| File name: | hd.sentinel.pro.4.x-5.x-patch.exe |
| Full analysis: | https://app.any.run/tasks/0918590a-e409-4cbf-a53e-7c6ddaedb578 |
| Verdict: | No threats detected |
| Analysis date: | August 17, 2019, 22:43:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 57824ABBB9AFE394C8A17A410E60C6FD |
| SHA1: | CDB3FE63C22E7D93D4A47BDB966B09F1B478F19F |
| SHA256: | BECB4E1EAA4FBD915241F1138E2ED7B9833DC1CF66D6DA25F9FAC1A3E317C3EE |
| SSDEEP: | 1536:0mckPxiT0Vvh5yPBHqO/S8XA8UgEAK3ptUVJWf3GzR8IaUF+vBIuUMltn:DckPxiT0VvbuqT8Q8UNJZtUnW/yyIaPj |
MALICIOUS
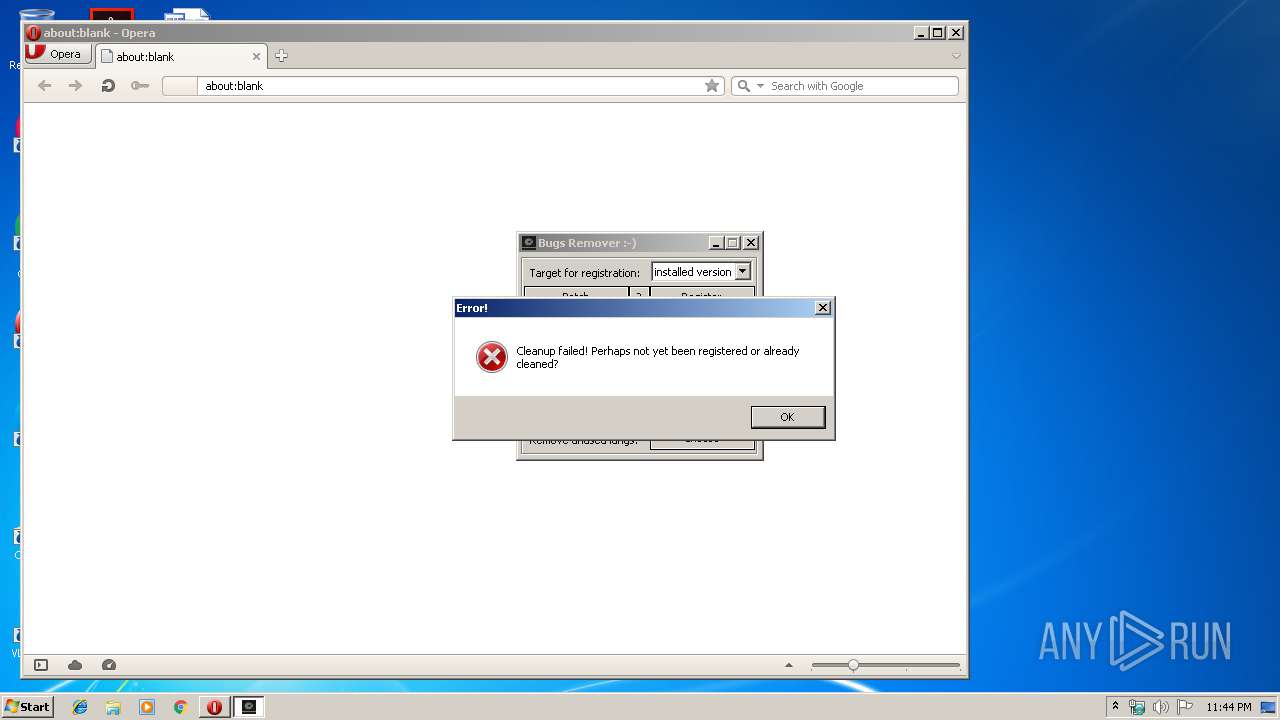
No malicious indicators.SUSPICIOUS
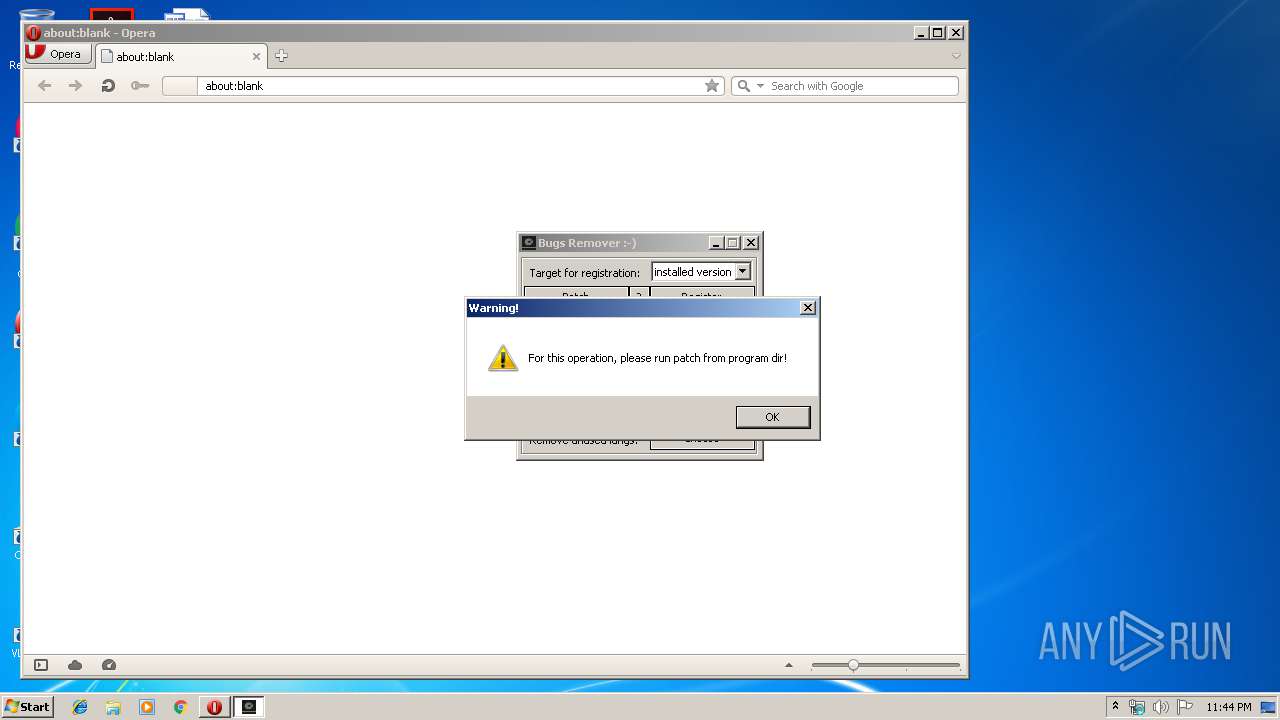
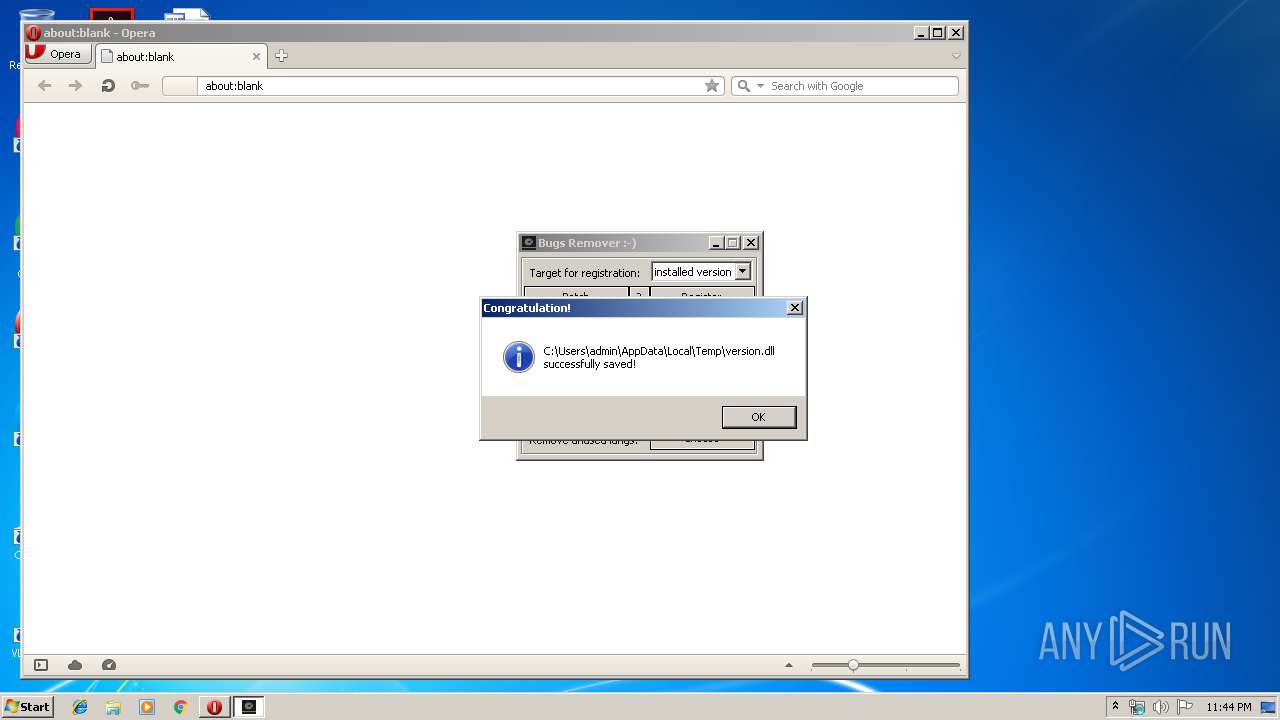
Executable content was dropped or overwritten
- hd.sentinel.pro.4.x-5.x-patch.exe (PID: 2296)
INFO
Creates files in the user directory
- opera.exe (PID: 3312)
Manual execution by user
- opera.exe (PID: 3312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Clipper DOS Executable (33.5) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (33.2) |
| .exe | | | DOS Executable Generic (33.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:11:16 16:25:52+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.1 |
| CodeSize: | 51712 |
| InitializedDataSize: | 6144 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xd6f4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.0.1.0 |
| ProductVersionNumber: | 5.0.1.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| CompanyName: | JUNLAJUBALAM/MPT & addhaloka |
| FileVersion: | 5.0.1 |
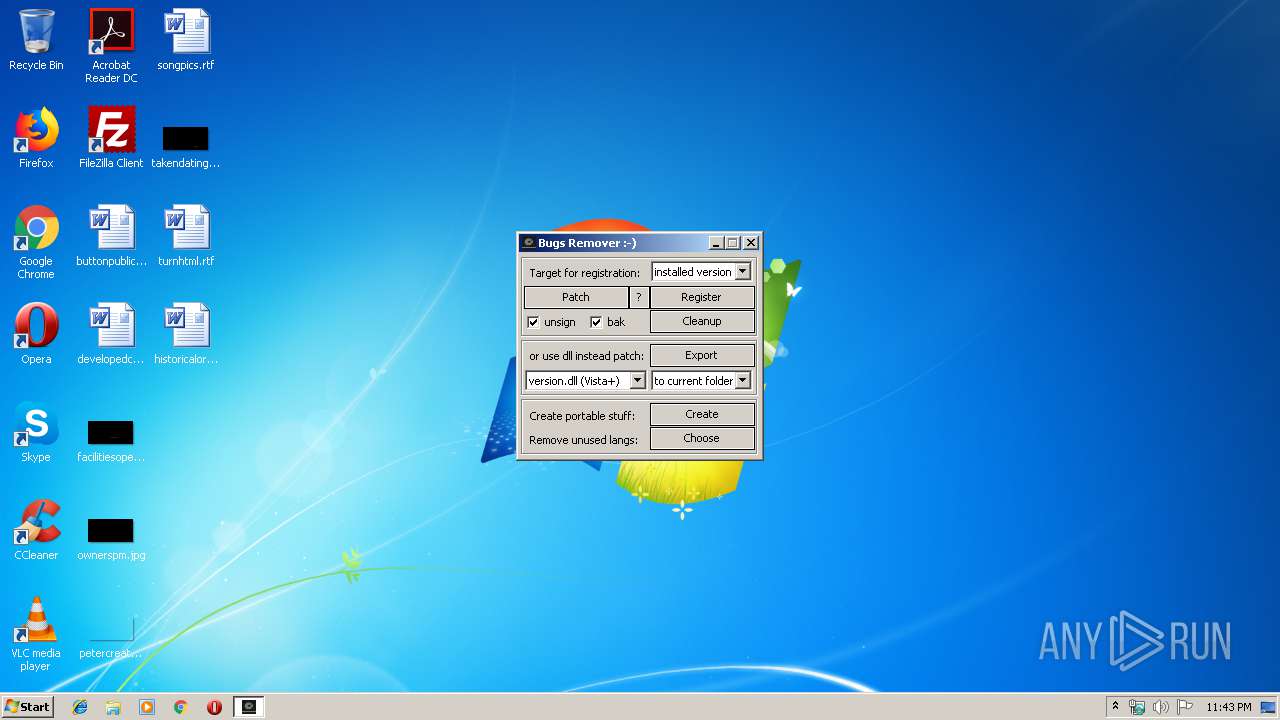
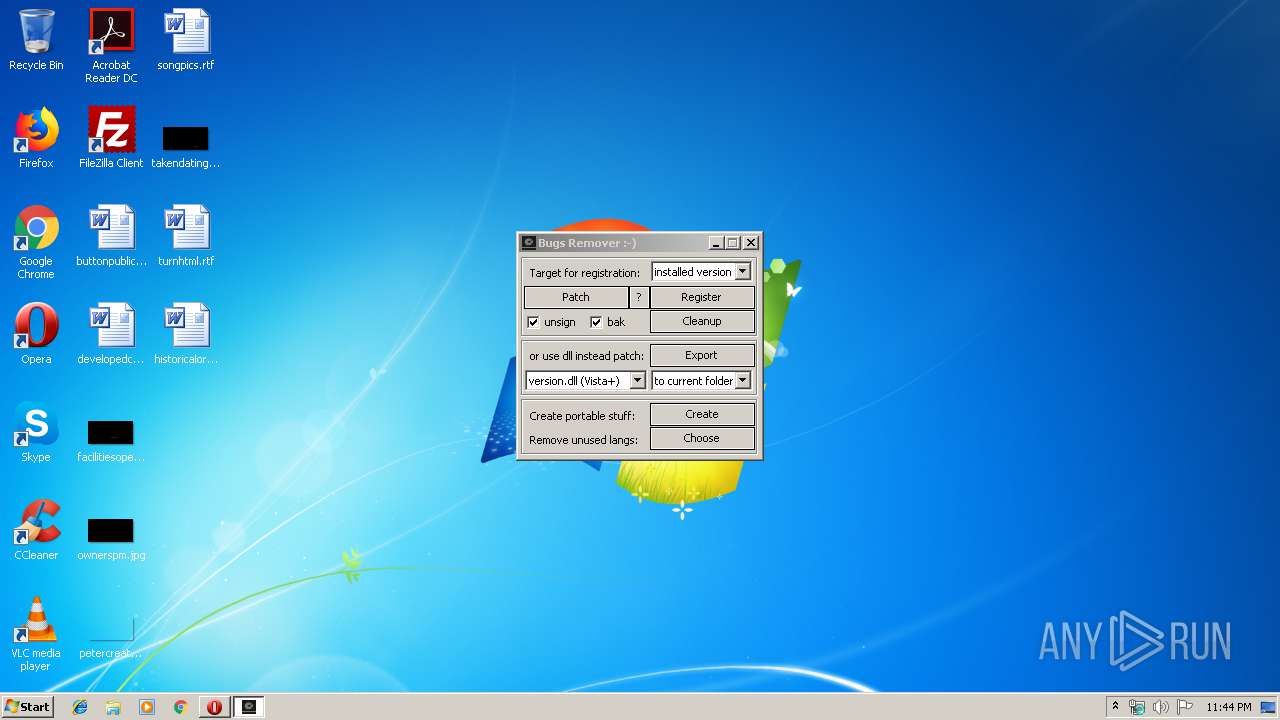
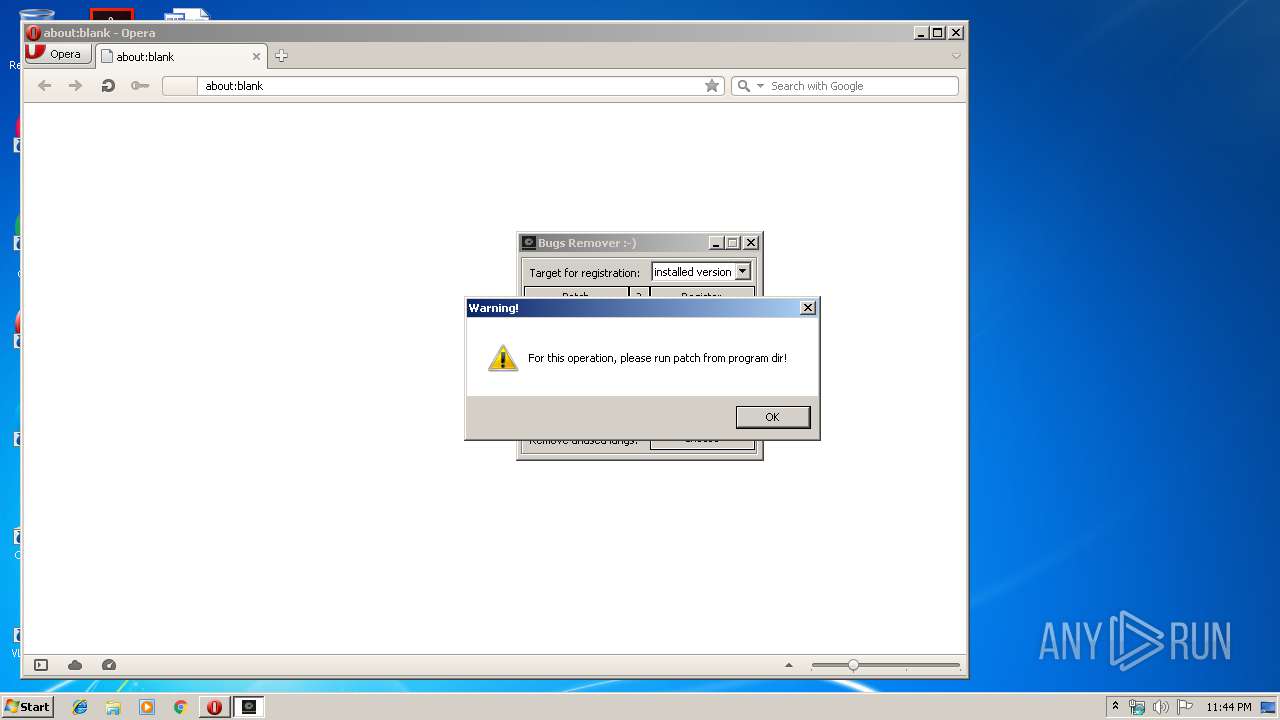
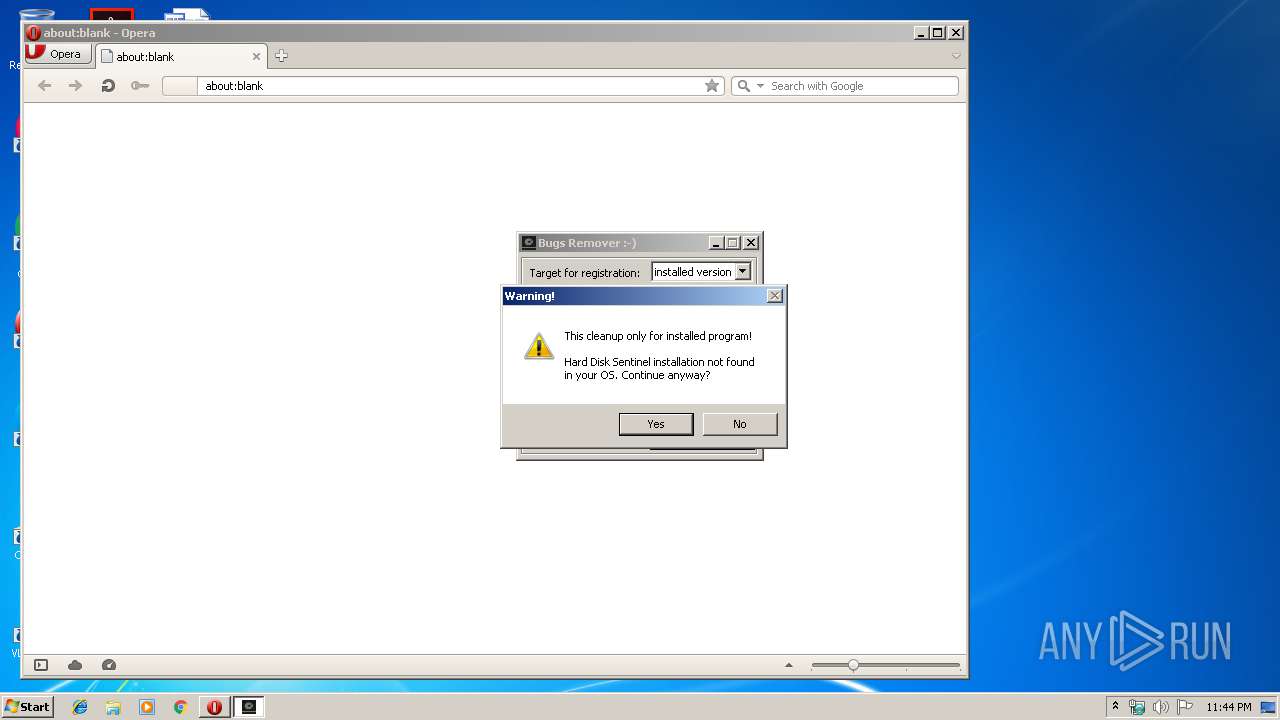
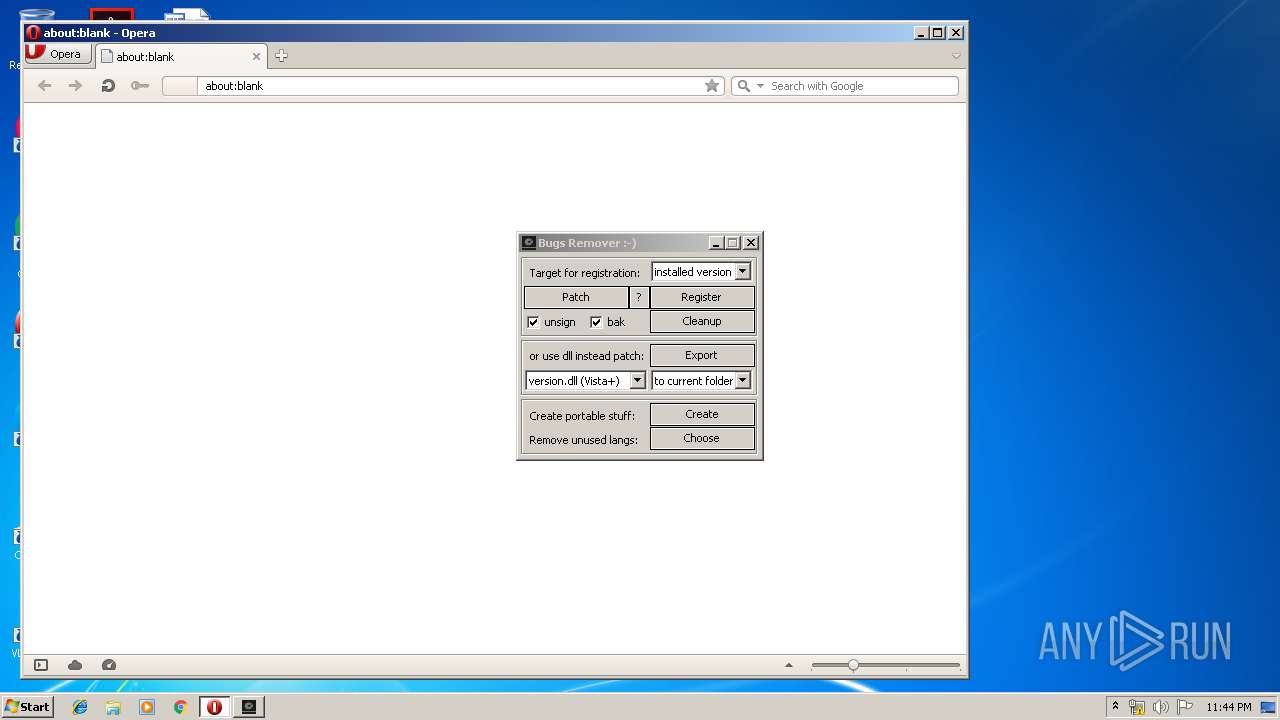
| FileDescription: | Bugs Remover :-) |
| LegalCopyright: | © 2017. No rights reserved. |
| ProductName: | Hard Disk Sentinel |
| ProductVersion: | 5 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Nov-2017 15:25:52 |
| Detected languages: |
|
| CompanyName: | JUNLAJUBALAM/MPT & addhaloka |
| FileVersion: | 5.0.1 |
| FileDescription: | Bugs Remover :-) |
| LegalCopyright: | © 2017. No rights reserved. |
| ProductName: | Hard Disk Sentinel |
| ProductVersion: | 5 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0080 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000068 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 16-Nov-2017 15:25:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000C980 | 0x0000CA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59175 |
.rdata | 0x0000E000 | 0x0000152A | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.21259 |
.idata | 0x00010000 | 0x00000AED | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.82255 |
.rsrc | 0x00011000 | 0x000071D0 | 0x00007200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.61087 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.04889 | 701 | UNKNOWN | Chinese - PRC | RT_MANIFEST |
2 | 2.25197 | 4264 | UNKNOWN | Chinese - PRC | RT_ICON |
3 | 2.40845 | 2664 | UNKNOWN | Chinese - PRC | RT_ICON |
4 | 2.82187 | 1640 | UNKNOWN | Chinese - PRC | RT_ICON |
5 | 2.79233 | 1224 | UNKNOWN | Chinese - PRC | RT_ICON |
6 | 3.06601 | 744 | UNKNOWN | Chinese - PRC | RT_ICON |
7 | 3.18395 | 488 | UNKNOWN | Chinese - PRC | RT_ICON |
8 | 3.84411 | 424 | UNKNOWN | Chinese - PRC | RT_ICON |
9 | 3.70007 | 296 | UNKNOWN | Chinese - PRC | RT_ICON |
10 | 7.86671 | 6329 | UNKNOWN | Chinese - PRC | RT_ICON |
Imports
advapi32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
gdiplus.dll |
imagehlp.dll |
kernel32.dll |
ole32.dll |
shell32.dll |
shlwapi.dll |
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
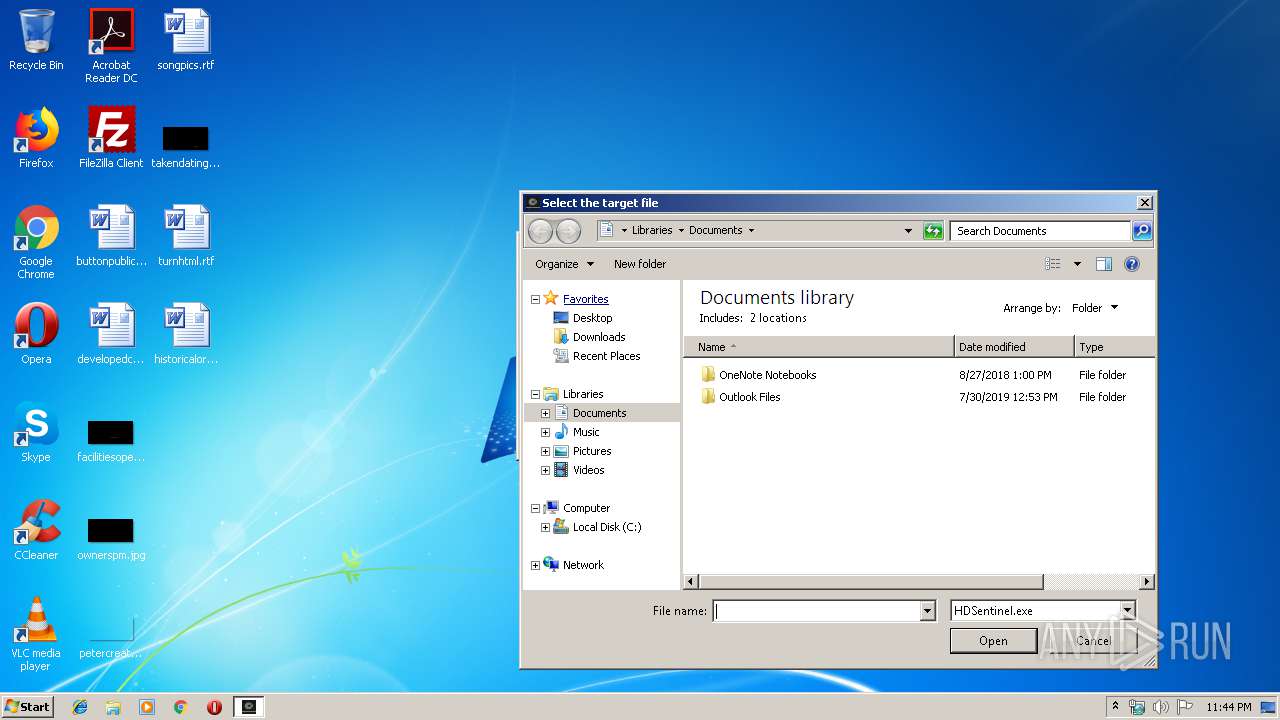
| 2296 | "C:\Users\admin\AppData\Local\Temp\hd.sentinel.pro.4.x-5.x-patch.exe" | C:\Users\admin\AppData\Local\Temp\hd.sentinel.pro.4.x-5.x-patch.exe | explorer.exe | ||||||||||||
User: admin Company: JUNLAJUBALAM/MPT & addhaloka Integrity Level: HIGH Description: Bugs Remover :-) Exit code: 0 Version: 5.0.1 Modules
| |||||||||||||||
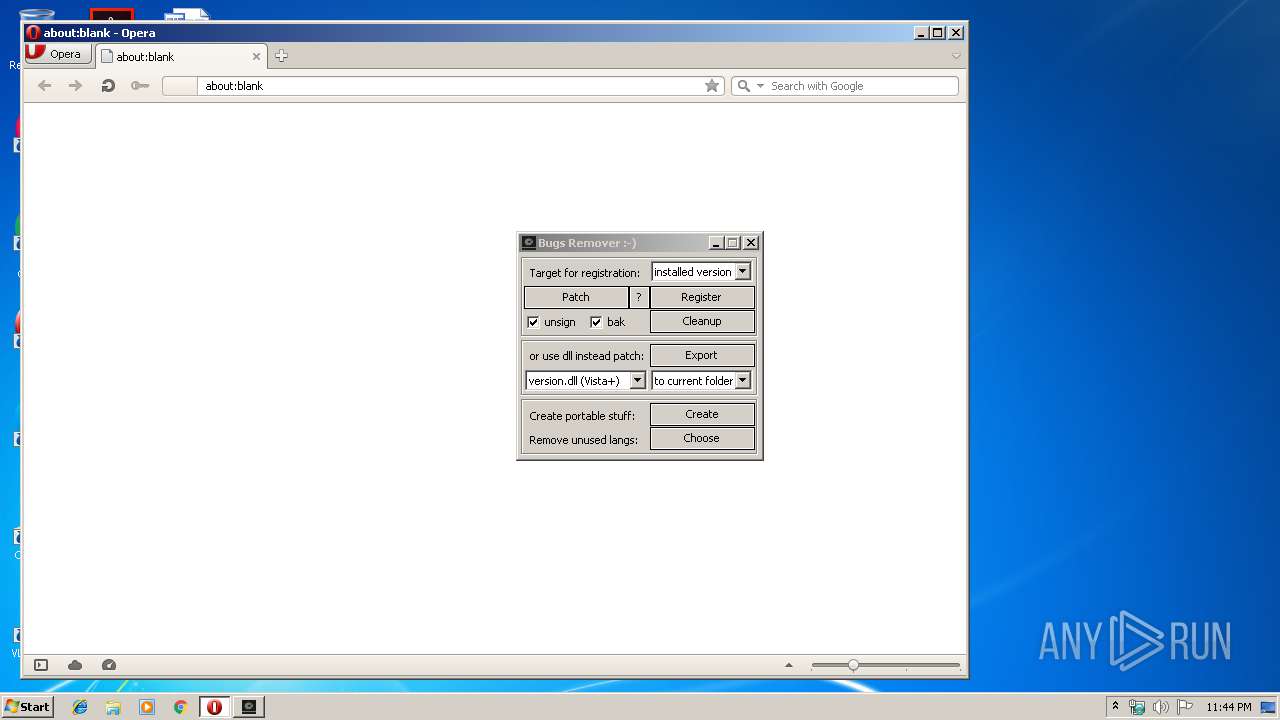
| 3312 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 3568 | "C:\Users\admin\AppData\Local\Temp\hd.sentinel.pro.4.x-5.x-patch.exe" | C:\Users\admin\AppData\Local\Temp\hd.sentinel.pro.4.x-5.x-patch.exe | — | explorer.exe | |||||||||||
User: admin Company: JUNLAJUBALAM/MPT & addhaloka Integrity Level: MEDIUM Description: Bugs Remover :-) Exit code: 3221226540 Version: 5.0.1 Modules
| |||||||||||||||
Total events
696
Read events
609
Write events
85
Delete events
2
Modification events
| (PID) Process: | (2296) hd.sentinel.pro.4.x-5.x-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2296) hd.sentinel.pro.4.x-5.x-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0200000001000000000000000700000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2296) hd.sentinel.pro.4.x-5.x-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (2296) hd.sentinel.pro.4.x-5.x-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (2296) hd.sentinel.pro.4.x-5.x-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (2296) hd.sentinel.pro.4.x-5.x-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2296) hd.sentinel.pro.4.x-5.x-patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | 1 |
Value: 680064002E00730065006E00740069006E0065006C002E00700072006F002E0034002E0078002D0035002E0078002D00700061007400630068002E0065007800650000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000007020000BE000000870400009E020000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (2296) hd.sentinel.pro.4.x-5.x-patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | delete value | Name: | 1 |
Value: 680064002E00730065006E00740069006E0065006C002E00700072006F002E0034002E0078002D0035002E0078002D00700061007400630068002E0065007800650000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000007020000BE000000870400009E020000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (2296) hd.sentinel.pro.4.x-5.x-patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | 1 |
Value: 680064002E00730065006E00740069006E0065006C002E00700072006F002E0034002E0078002D0035002E0078002D00700061007400630068002E006500780065000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000004020000E7000000FC020000CD0100000000000000000000000000000000000007020000BE000000870400009E020000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (2296) hd.sentinel.pro.4.x-5.x-patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0100000000000000FFFFFFFF | |||
Executable files
1
Suspicious files
23
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2296 | hd.sentinel.pro.4.x-5.x-patch.exe | C:\Users\admin\AppData\Local\Temp\~e0itht0i-t0t.tmp | — | |
MD5:— | SHA256:— | |||
| 3312 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr7C0.tmp | — | |
MD5:— | SHA256:— | |||
| 3312 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr7F0.tmp | — | |
MD5:— | SHA256:— | |||
| 3312 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00001.tmp | — | |
MD5:— | SHA256:— | |||
| 3312 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\QNIVGNAIHXENZBXSCS4M.temp | — | |
MD5:— | SHA256:— | |||
| 3312 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opssl6.dat | binary | |
MD5:— | SHA256:— | |||
| 3312 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
| 3312 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:— | SHA256:— | |||
| 3312 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\CACHEDIR.TAG | text | |
MD5:E717F92FA29AE97DBE4F6F5C04B7A3D9 | SHA256:5BBD5DCBF87FD8CD7544C522BADF22A2951CF010AD9F25C40F9726F09EA2B552 | |||
| 3312 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opcert6.dat | binary | |
MD5:1AA8644C9261DC10F7247F6A145C1DD2 | SHA256:58A8933F65361633C6AB194000D312DC9D566F717B1A16814A0DBEE24A60EBE3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3312 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 528 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3312 | opera.exe | 185.26.182.94:443 | certs.opera.com | Opera Software AS | — | whitelisted |
3312 | opera.exe | 93.184.220.29:80 | crl4.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |