| File name: | R_NA CL_ENT.exe |
| Full analysis: | https://app.any.run/tasks/cf979e67-af78-4198-9c6f-2e7fa937ffce |
| Verdict: | Malicious activity |
| Analysis date: | December 21, 2020, 12:04:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E7775EC363BDB9F104252745E3011E4C |
| SHA1: | FF8393602C1F3629B5F25BFE3452D2F4919D0A07 |
| SHA256: | BEBBD722E3C388FC743F7C0B719A32AD6B30D6FA619A701345EDE57DE732EE2C |
| SSDEEP: | 6144:smcD66RRjv5JGmrpQsK3RD2u270jupCJsCxCv:dcD663OZ2zkPaCxi |
MALICIOUS
Application was injected by another process
- explorer.exe (PID: 1724)
- taskeng.exe (PID: 1532)
- dwm.exe (PID: 1608)
- DllHost.exe (PID: 4076)
- ctfmon.exe (PID: 1656)
- host.exe (PID: 600)
Runs injected code in another process
- R_NA CL_ENT.exe (PID: 2864)
- explorer.exe (PID: 2912)
Changes the autorun value in the registry
- R_NA CL_ENT.exe (PID: 2864)
SUSPICIOUS
Executable content was dropped or overwritten
- R_NA CL_ENT.exe (PID: 2864)
Creates files in the user directory
- explorer.exe (PID: 2912)
Creates executable files which already exist in Windows
- R_NA CL_ENT.exe (PID: 2864)
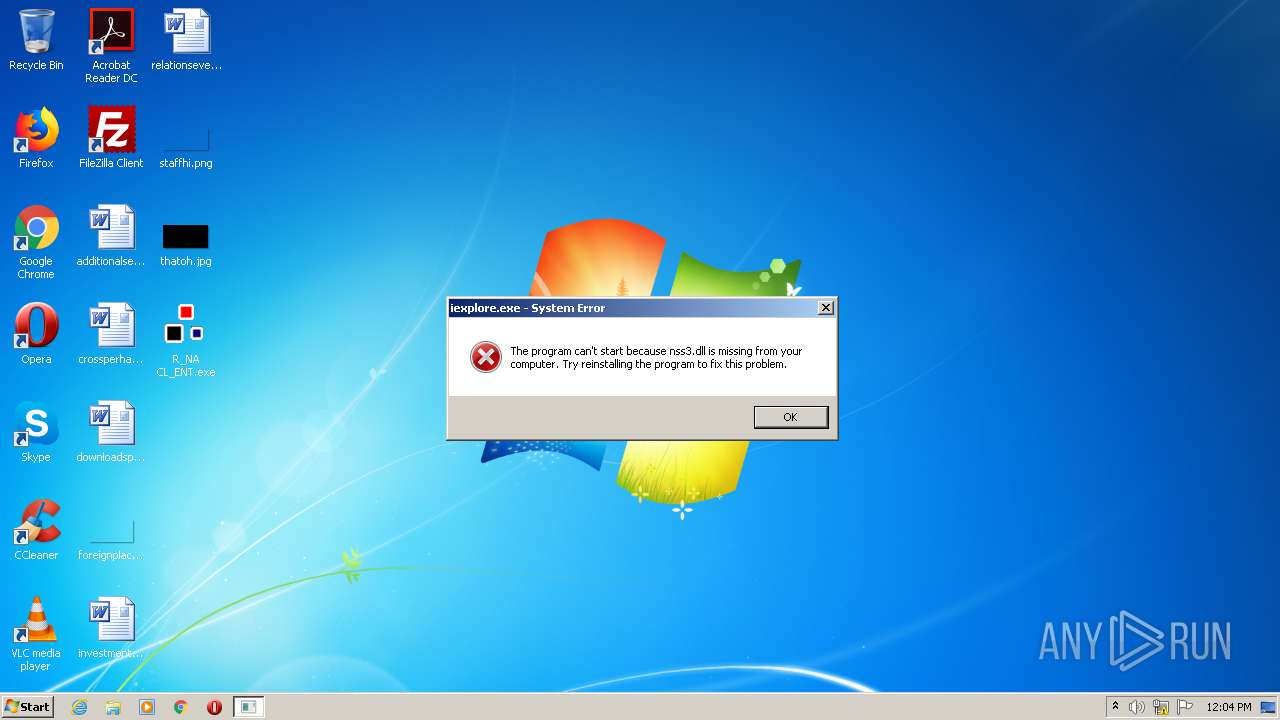
Loads DLL from Mozilla Firefox
- iexplore.exe (PID: 2992)
Drops a file with too old compile date
- R_NA CL_ENT.exe (PID: 2864)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (42.6) |
|---|---|---|
| .exe | | | Win16/32 Executable Delphi generic (19.5) |
| .exe | | | Generic Win/DOS Executable (18.9) |
| .exe | | | DOS Executable Generic (18.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 45568 |
| InitializedDataSize: | 261632 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xbbf4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0000B1C8 | 0x0000B200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.41418 |
DATA | 0x0000D000 | 0x00000220 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.76426 |
BSS | 0x0000E000 | 0x000011F1 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00010000 | 0x00000BE4 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.77096 |
.tls | 0x00011000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00012000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.205446 |
.reloc | 0x00013000 | 0x00000A60 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.2459 |
.rsrc | 0x00014000 | 0x0003DF3C | 0x0003E000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 7.90402 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 1.14666 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
50 | 1.14666 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
51 | 1.14666 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
DVCLAL | 4 | 16 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 5.0948 | 388 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
XX-XX-XX-XX | 7.94418 | 246083 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
ICON_STANDARD | 1.9815 | 20 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
MAINICON | 1.9815 | 20 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
advapi32.dll |
crypt32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
pstorec.dll |
rasapi32.dll |
shell32.dll |
user32.dll |
Total processes
37
Monitored processes
9
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 600 | "host.exe" | C:\Windows\system32\host.exe | srvpost.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1532 | taskeng.exe {63C85A42-5597-452E-ABD1-EF9D4EDAB4D8} | C:\Windows\System32\taskeng.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Engine Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1608 | "C:\Windows\system32\Dwm.exe" | C:\Windows\System32\dwm.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Desktop Window Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1656 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1724 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2864 | "C:\Users\admin\Desktop\R_NA CL_ENT.exe" | C:\Users\admin\Desktop\R_NA CL_ENT.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2912 | explorer.exe | C:\Windows\explorer.exe | — | R_NA CL_ENT.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2992 | "C:\install\iexplore.exe" | C:\install\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4076 | C:\Windows\system32\DllHost.exe /Processid:{AB8902B4-09CA-4BB6-B78D-A8F59079A8D5} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 402
Read events
1 321
Write events
81
Delete events
0
Modification events
| (PID) Process: | (600) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | APPSTARTING |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (600) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | ARROW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (600) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | CROSS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (600) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HAND |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (600) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HELP |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (600) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | IBEAM |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (600) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | NO |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (600) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZEALL |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (600) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENESW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (600) host.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
Executable files
1
Suspicious files
1
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2864 | R_NA CL_ENT.exe | C:\install\iexplore.exe | executable | |
MD5:— | SHA256:— | |||
| 2864 | R_NA CL_ENT.exe | C:\Users\admin\AppData\Local\Temp\XX--XX--XX.txt | binary | |
MD5:— | SHA256:— | |||
| 2912 | explorer.exe | C:\Users\admin\AppData\Local\Temp\UuU.uUu | text | |
MD5:— | SHA256:— | |||
| 2912 | explorer.exe | C:\Users\admin\AppData\Local\Temp\XxX.xXx | text | |
MD5:— | SHA256:— | |||
| 2912 | explorer.exe | C:\Users\admin\AppData\Roaming\logs.dat | text | |
MD5:E21BD9604EFE8EE9B59DC7605B927A2A | SHA256:51A3FE220229AA3FDDDC909E20A4B107E7497320A00792A280A03389F2EACB46 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |