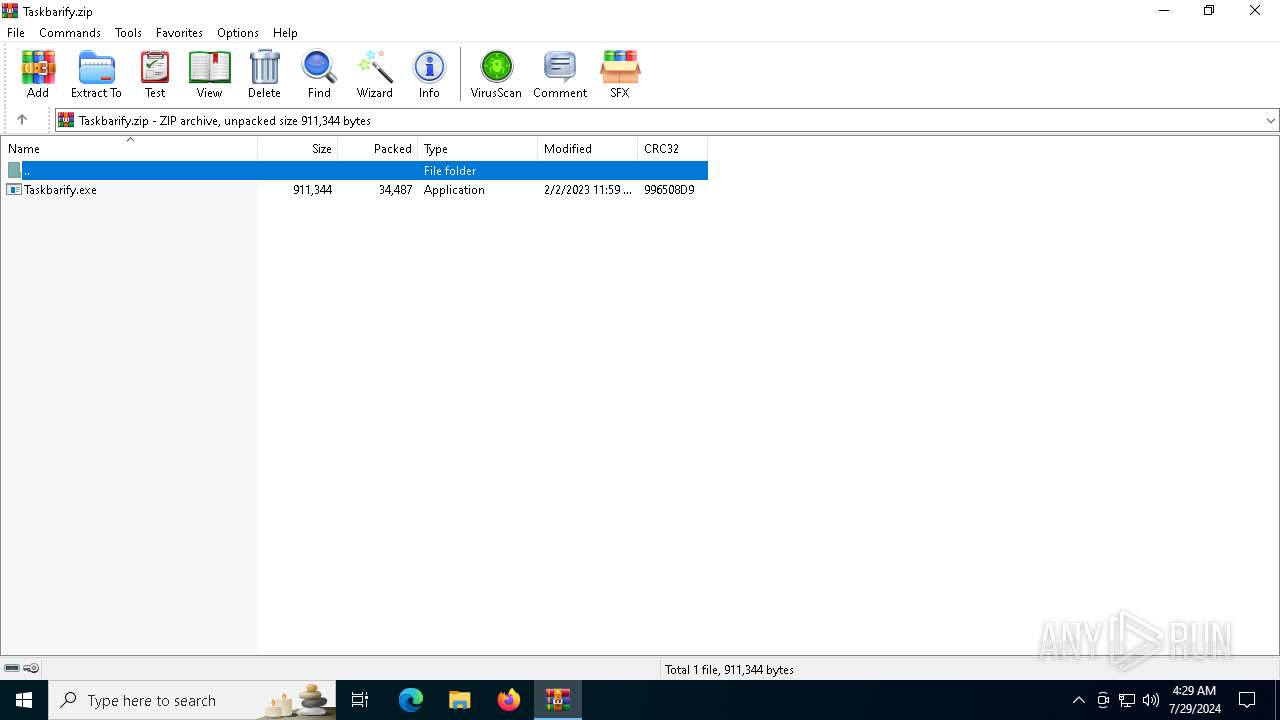
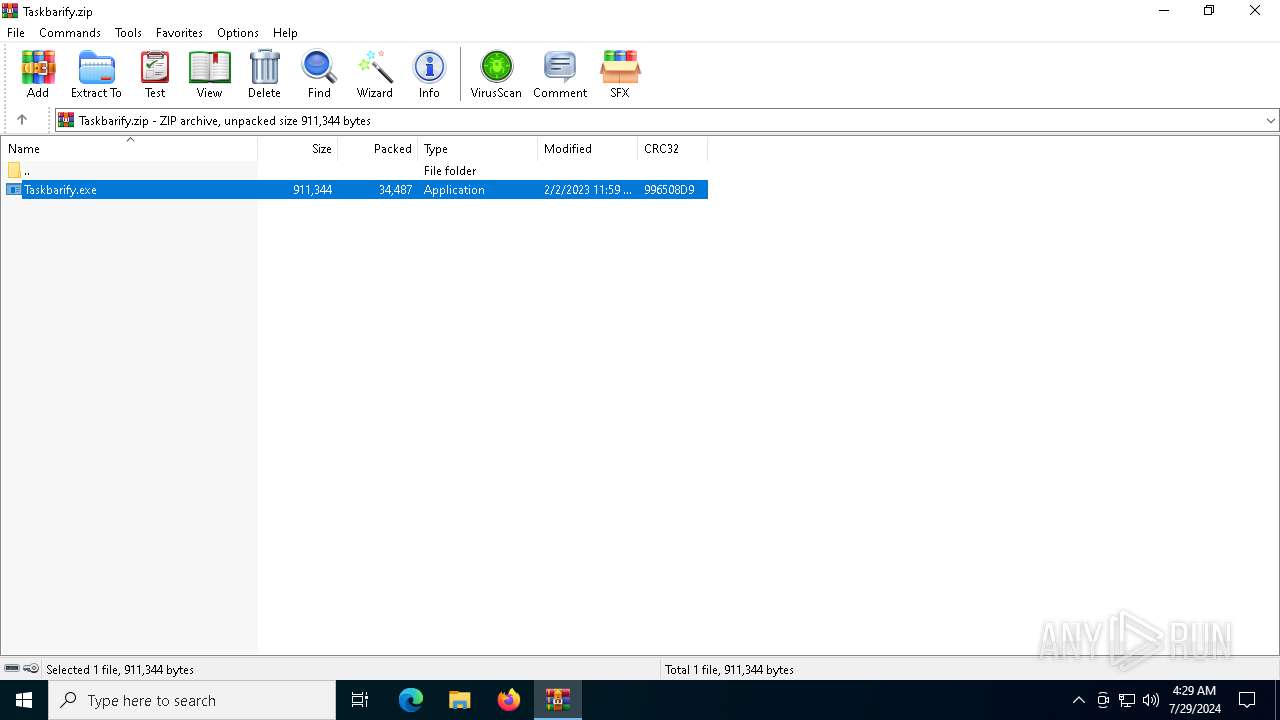
| File name: | Taskbarify.zip |
| Full analysis: | https://app.any.run/tasks/c4e9203b-ed21-441a-a5a1-d91a1b2c3eed |
| Verdict: | Malicious activity |
| Analysis date: | July 29, 2024, 04:29:16 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 611183EBE5CE8102F29001D88A8AD2AC |
| SHA1: | 3740F99EB01D3979FE75AEC95E6AAB9B72889A05 |
| SHA256: | BEAF90245A9715E05E7D0CA1C9AAD7C3973780CDC8427851EA7E5848AE9FD18D |
| SSDEEP: | 768:LP8xBOtOCvah2ZPFInYwaOh4rFr0YMN00UrLvns3gI89PgB+fStuz:LP86DSwZPuJaKYSdUrLv6dOPgB+fKuz |
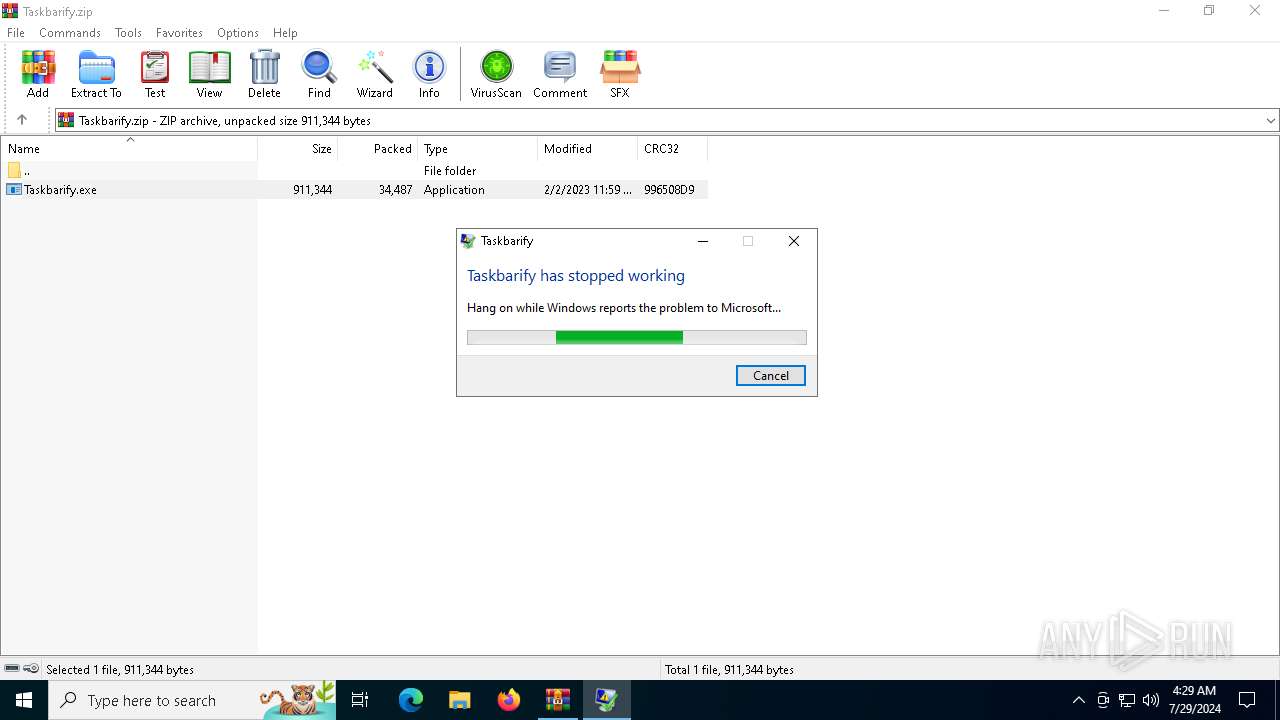
MALICIOUS
Drops the executable file immediately after the start
- WinRAR.exe (PID: 2120)
Scans artifacts that could help determine the target
- dw20.exe (PID: 5828)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2120)
- Taskbarify.exe (PID: 4316)
Checks Windows Trust Settings
- Taskbarify.exe (PID: 4316)
Reads the date of Windows installation
- dw20.exe (PID: 5828)
INFO
Reads the machine GUID from the registry
- Taskbarify.exe (PID: 4316)
- dw20.exe (PID: 5828)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2120)
Reads the computer name
- Taskbarify.exe (PID: 4316)
- dw20.exe (PID: 5828)
Checks supported languages
- Taskbarify.exe (PID: 4316)
- dw20.exe (PID: 5828)
Checks proxy server information
- Taskbarify.exe (PID: 4316)
- dw20.exe (PID: 5828)
- slui.exe (PID: 4468)
Reads the software policy settings
- Taskbarify.exe (PID: 4316)
- dw20.exe (PID: 5828)
Creates files or folders in the user directory
- Taskbarify.exe (PID: 4316)
Creates files in the program directory
- dw20.exe (PID: 5828)
Reads product name
- dw20.exe (PID: 5828)
Reads Environment values
- dw20.exe (PID: 5828)
Process checks computer location settings
- dw20.exe (PID: 5828)
Reads CPU info
- dw20.exe (PID: 5828)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2023:02:03 10:59:26 |
| ZipCRC: | 0x996508d9 |
| ZipCompressedSize: | 34487 |
| ZipUncompressedSize: | 911344 |
| ZipFileName: | Taskbarify.exe |
Total processes
147
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2120 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Taskbarify.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 4316 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2120.19203\Taskbarify.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2120.19203\Taskbarify.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Taskbarify Exit code: 3762507597 Version: 1.0.0.1 Modules
| |||||||||||||||
| 4468 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5828 | dw20.exe -x -s 1784 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\dw20.exe | Taskbarify.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Error Reporting Shim Exit code: 0 Version: 2.0.50727.9149 (WinRelRS6.050727-9100) Modules
| |||||||||||||||
Total events
12 365
Read events
12 343
Write events
22
Delete events
0
Modification events
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Taskbarify.zip | |||
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
1
Suspicious files
8
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5828 | dw20.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_Taskbarify.exe_39fedad0def74b2908ba76bff11e399e4966a6_00000000_629b0bbc-3437-41da-b2b2-dd652c0b94b9\Report.wer | — | |
MD5:— | SHA256:— | |||
| 2120 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2120.19203\Taskbarify.exe | executable | |
MD5:798A870C8D7C0027C829586BF63C2B4F | SHA256:741F68A10A6369D383BEEAB44596A33A919803CB061BEAAE48CDE8FB4B7EC037 | |||
| 4316 | Taskbarify.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_93702E680A5530C052C8D2BA33A2225F | binary | |
MD5:4F006E9E83BB461FC1D617A080540CDC | SHA256:91013D3F8B50D00B9B5F360A16F86F7F62149D720315C430EFE25AEA52A2659A | |||
| 4316 | Taskbarify.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_93702E680A5530C052C8D2BA33A2225F | binary | |
MD5:C1657C09CBF653085FE5977265C03E1D | SHA256:3E9B4E775C00A2FD2B1DB9D5C7B4E83D6DF7F3683AABA7283A8137248DAD751A | |||
| 4316 | Taskbarify.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\18E6B4A57A6BC7EC9B861CDF2D6D0D02_EF52C1EC85F21F31CC0157A5C8803013 | binary | |
MD5:6CA6059D607881E9BDCBEED15CD64D64 | SHA256:95EB48F29073CA36BE5E37B8B57B7EFE7C33F235873FB4CE8FF952B89EE69D7F | |||
| 4316 | Taskbarify.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\3AA0DCD5A74331FBD6F344550EC48B87_7902A748B8A9234885910B8C93165796 | binary | |
MD5:243B641FB24998C4274A05262A36FD1C | SHA256:0FD51BF0F58B04F736A8C001095FE23F2853D794FB15BB338B78E3CDF1E67938 | |||
| 4316 | Taskbarify.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\18E6B4A57A6BC7EC9B861CDF2D6D0D02_EF52C1EC85F21F31CC0157A5C8803013 | binary | |
MD5:95E810BC77F5755CBC10F421F82CFD7C | SHA256:229E21E94512D97795CCF3D626A3F3DA165C2CF2B957339D692323D3B266076A | |||
| 4316 | Taskbarify.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\3AA0DCD5A74331FBD6F344550EC48B87_7902A748B8A9234885910B8C93165796 | binary | |
MD5:905C14152E6DFB3C1355640FF0EE1746 | SHA256:9DB6A42918D13523C94DA2D0728384E188F3363394535AB1D9CD03C7E8D1741A | |||
| 5828 | dw20.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER549F.tmp.WERInternalMetadata.xml | xml | |
MD5:FAC45B4D432C8FEED605C5FDB106D027 | SHA256:2D30D56A5B923706339F3286710C26C136B28E4EA6D760A6991161912C428E67 | |||
| 5828 | dw20.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:FB64A9EBEDF48D3895381D5B7D80743D | SHA256:EA21D495930AD76F267A33A0F593DBF0C7EA75E457FCAE49A29DAAD8BD920F42 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
47
DNS requests
26
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4424 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5368 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4316 | Taskbarify.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEEj8k7RgVZSNNqfJionWlBY%3D | unknown | — | — | whitelisted |
4316 | Taskbarify.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSdE3gf41WAic8Uh9lF92%2BIJqh5qwQUMuuSmv81lkgvKEBCcCA2kVwXheYCEDPXCKiRQFMZ4qW70zm5rW4%3D | unknown | — | — | whitelisted |
4316 | Taskbarify.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRd0JozUYXMqqW4y4zJTrLcMCRSkAQUgTKSQSsozUbIxKLGKjkS7EipPxQCEEkUWgwqFu1ulbAVdWqzyDM%3D | unknown | — | — | whitelisted |
3676 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5368 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
2692 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4132 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5368 | SearchApp.exe | 131.253.33.254:443 | a-ring-fallback.msedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
3976 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5368 | SearchApp.exe | 95.100.146.34:443 | www.bing.com | Akamai International B.V. | CZ | unknown |
1736 | slui.exe | 40.91.76.224:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6012 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3332 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6564 | slui.exe | 40.91.76.224:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
t-ring-fdv2.msedge.net |
| unknown |
a-ring-fallback.msedge.net |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
fp-afd-nocache-ccp.azureedge.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |