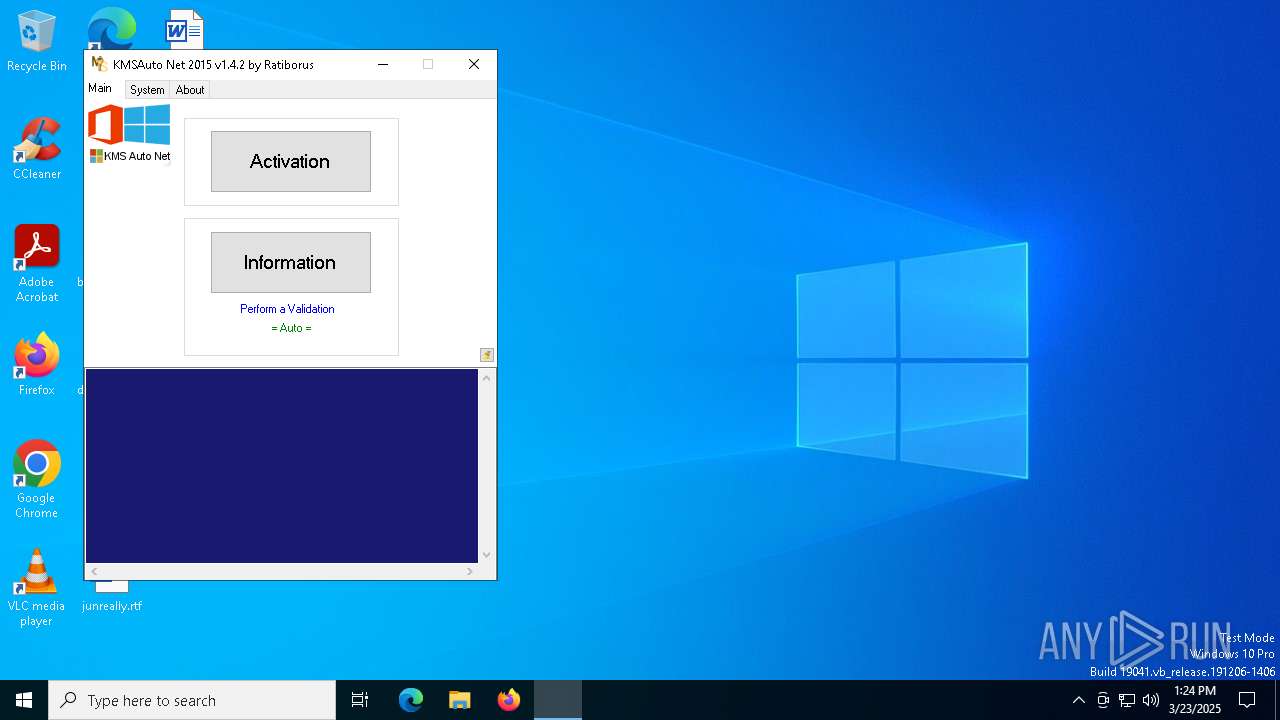
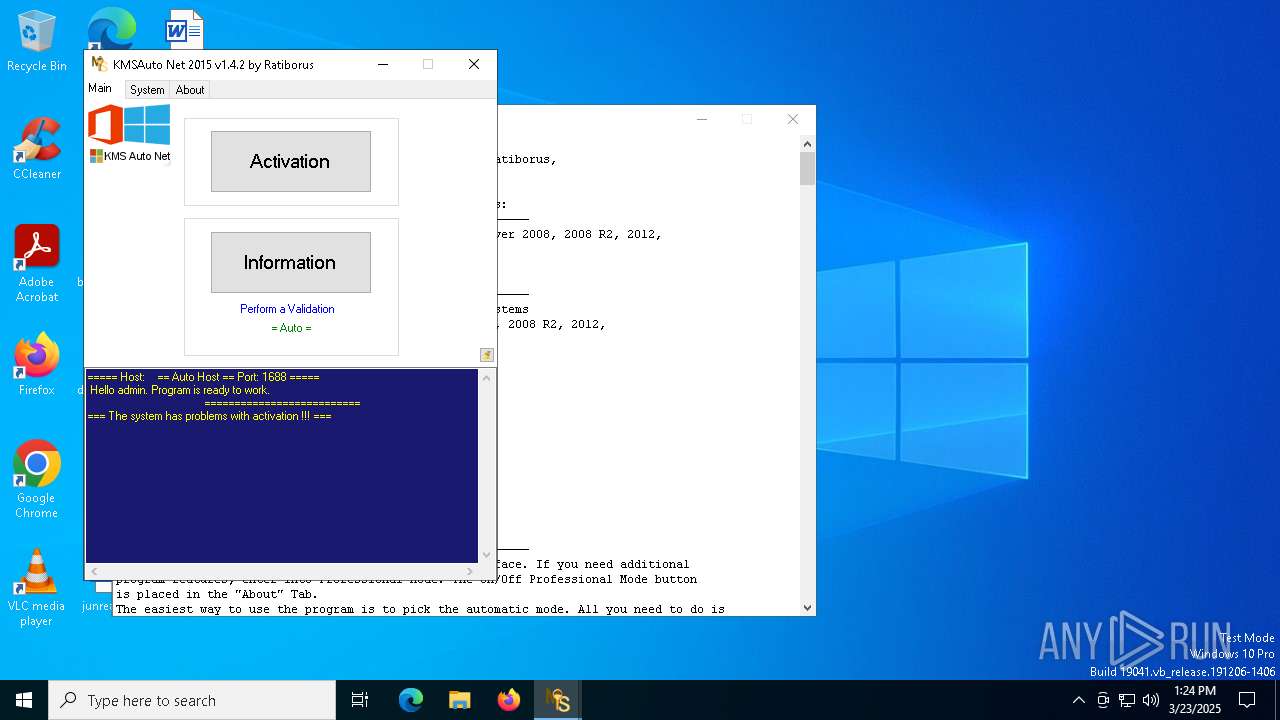
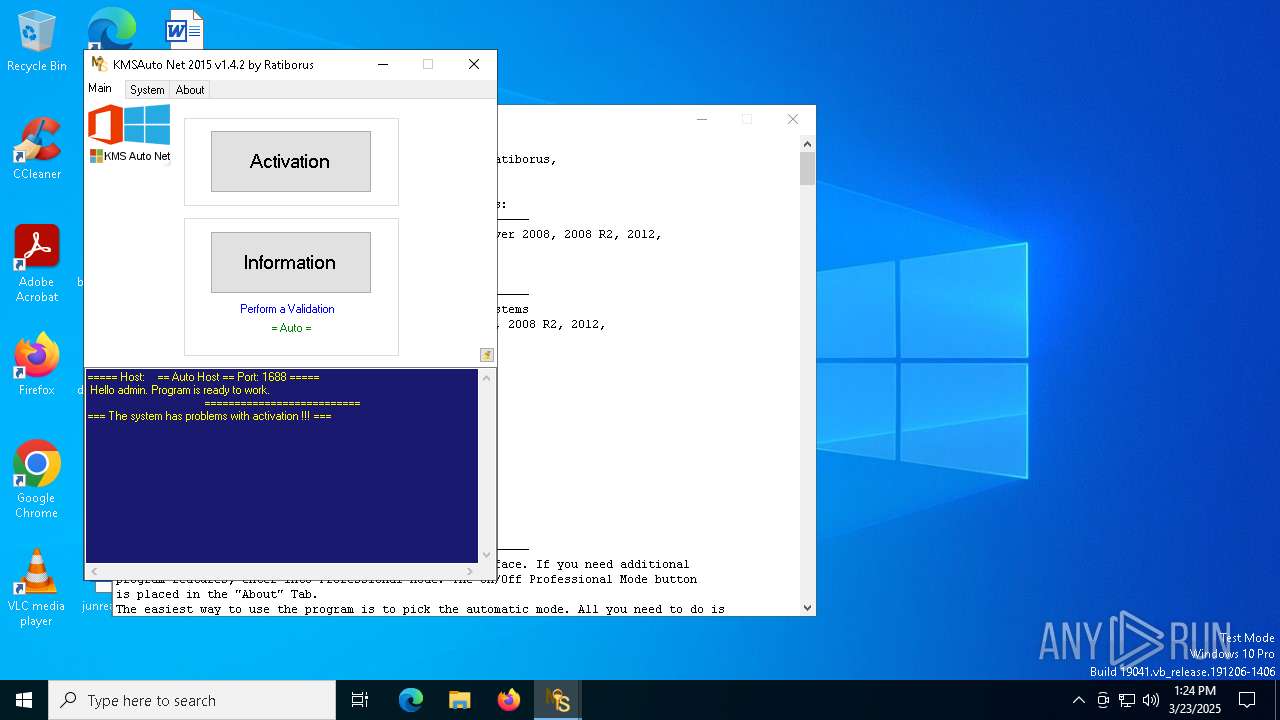
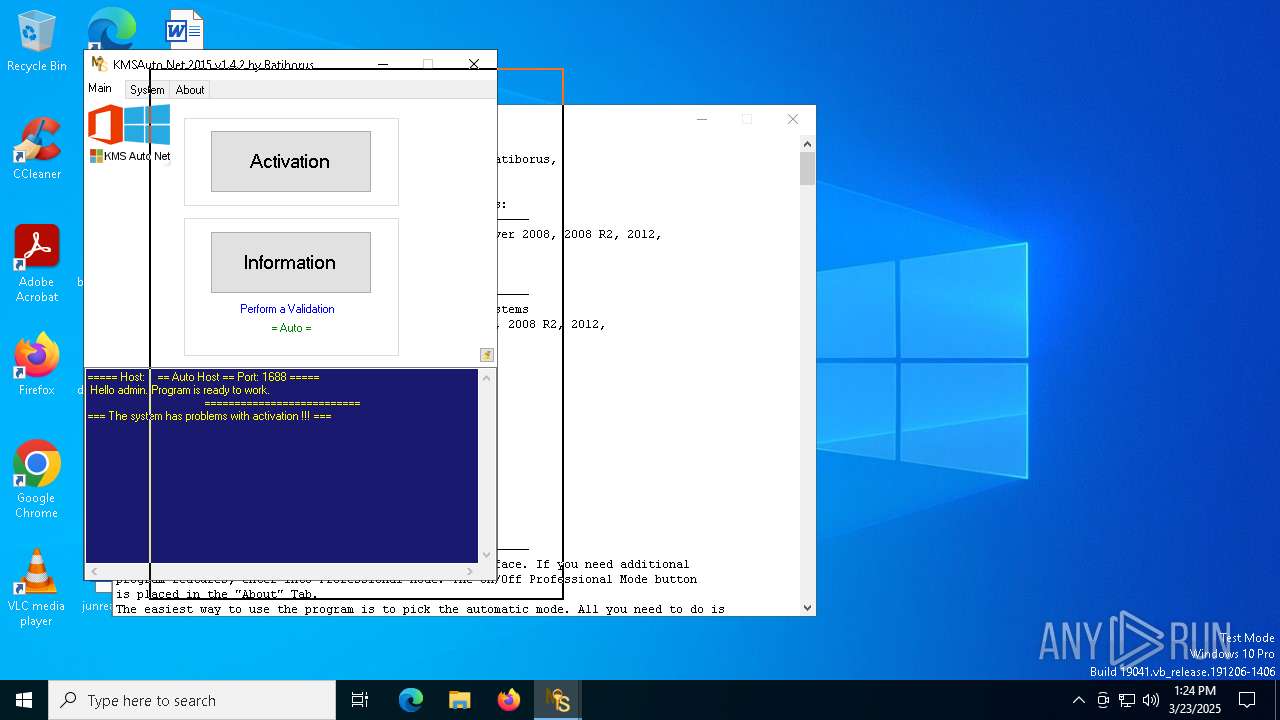
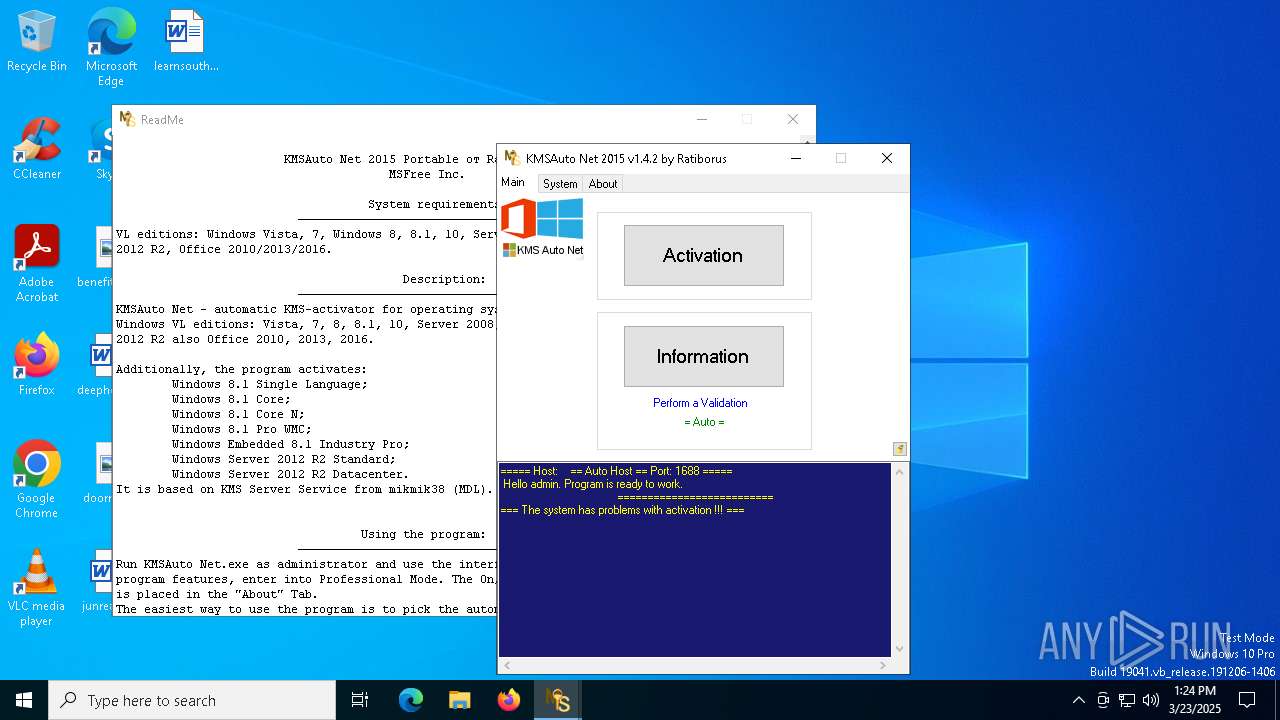
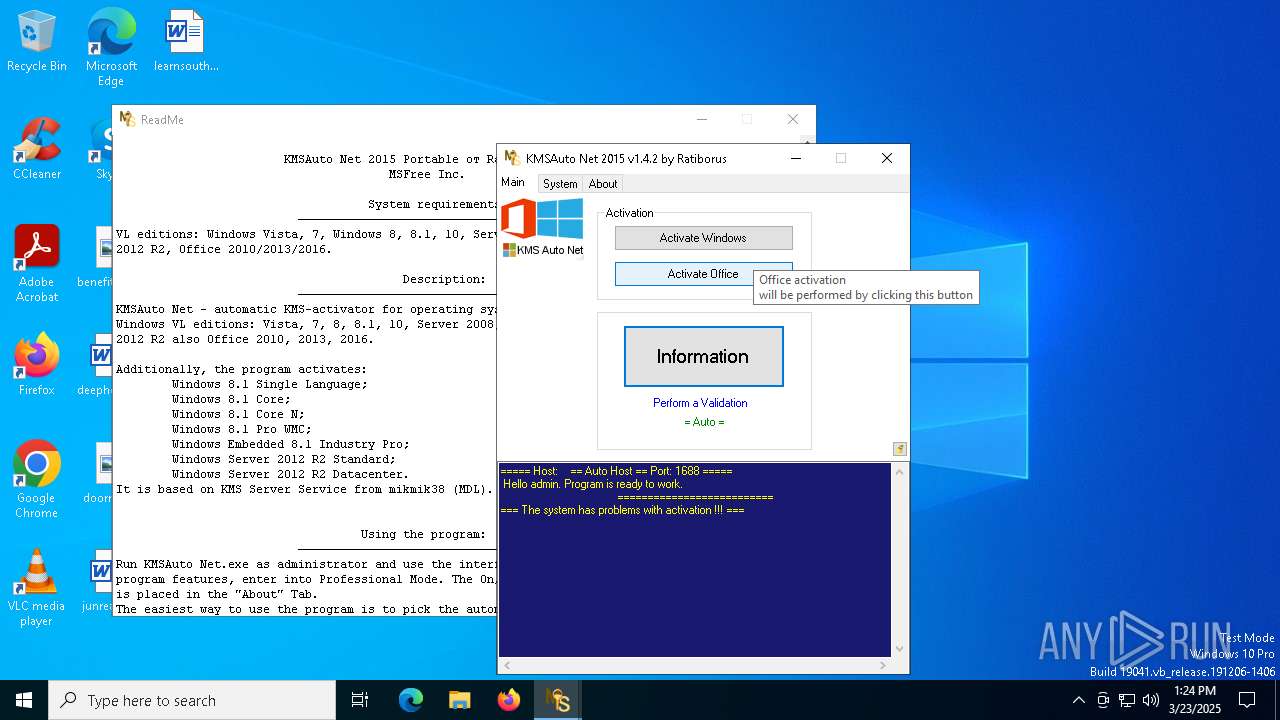
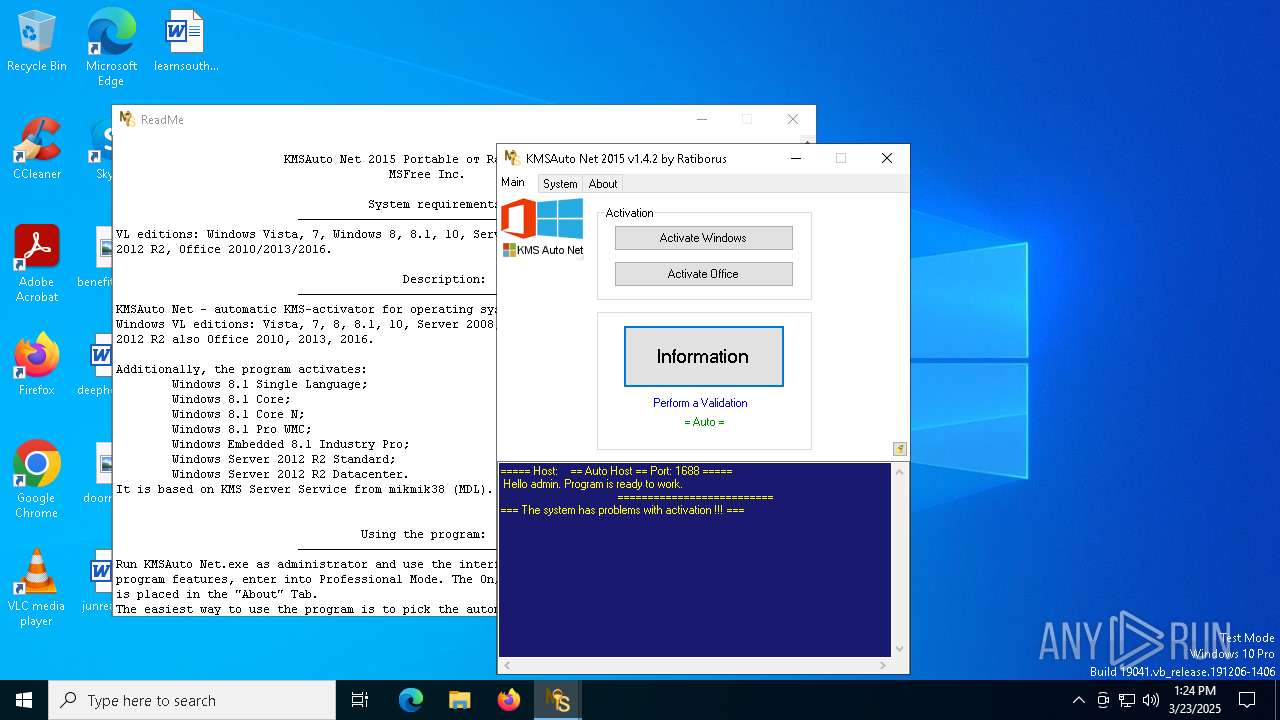
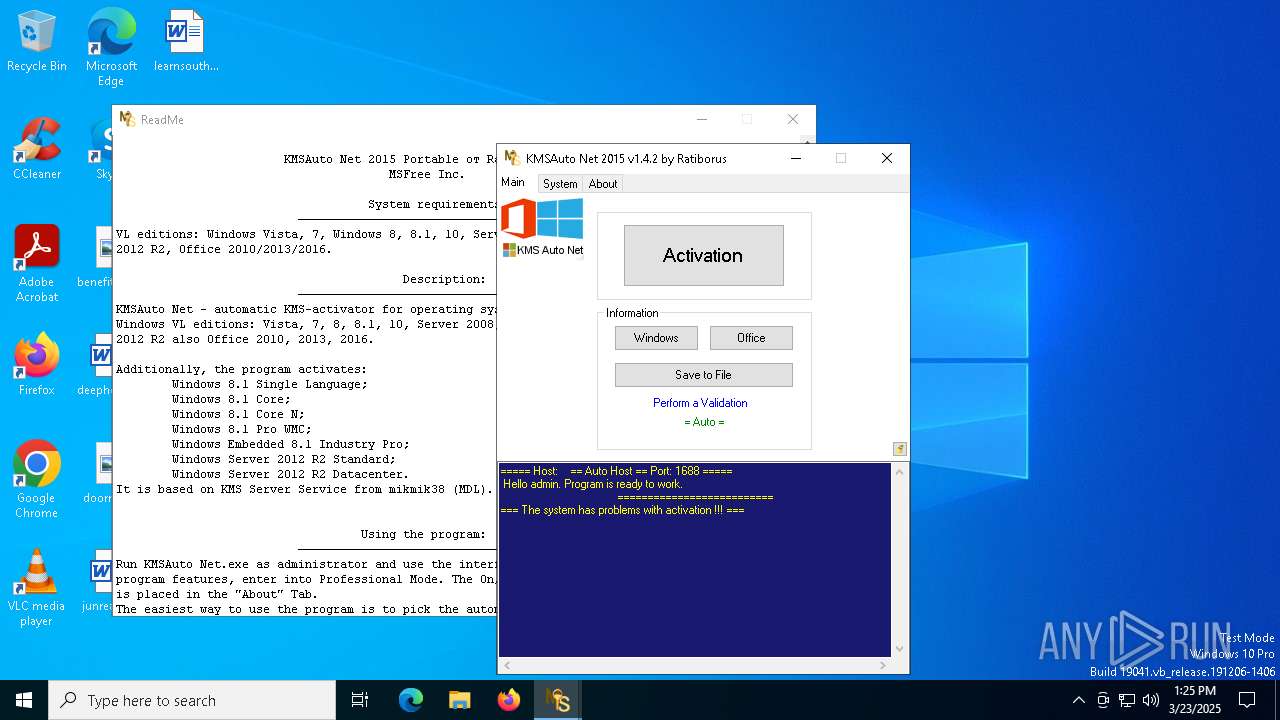
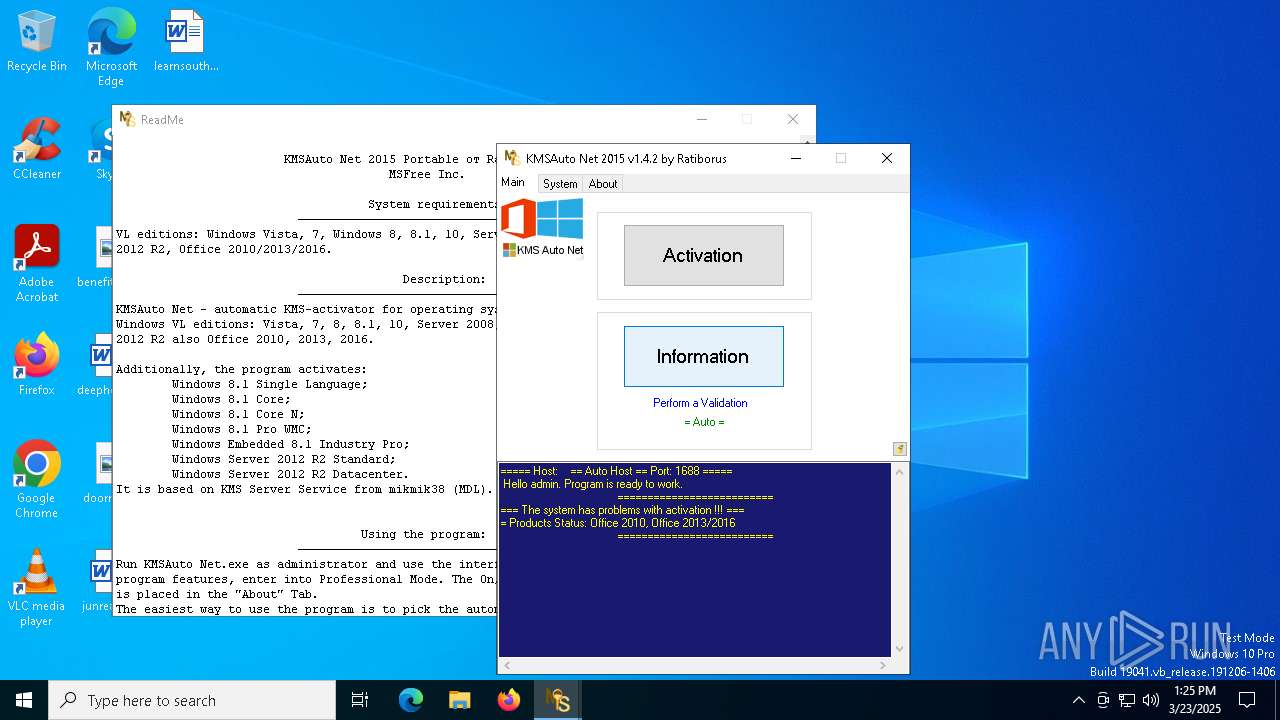
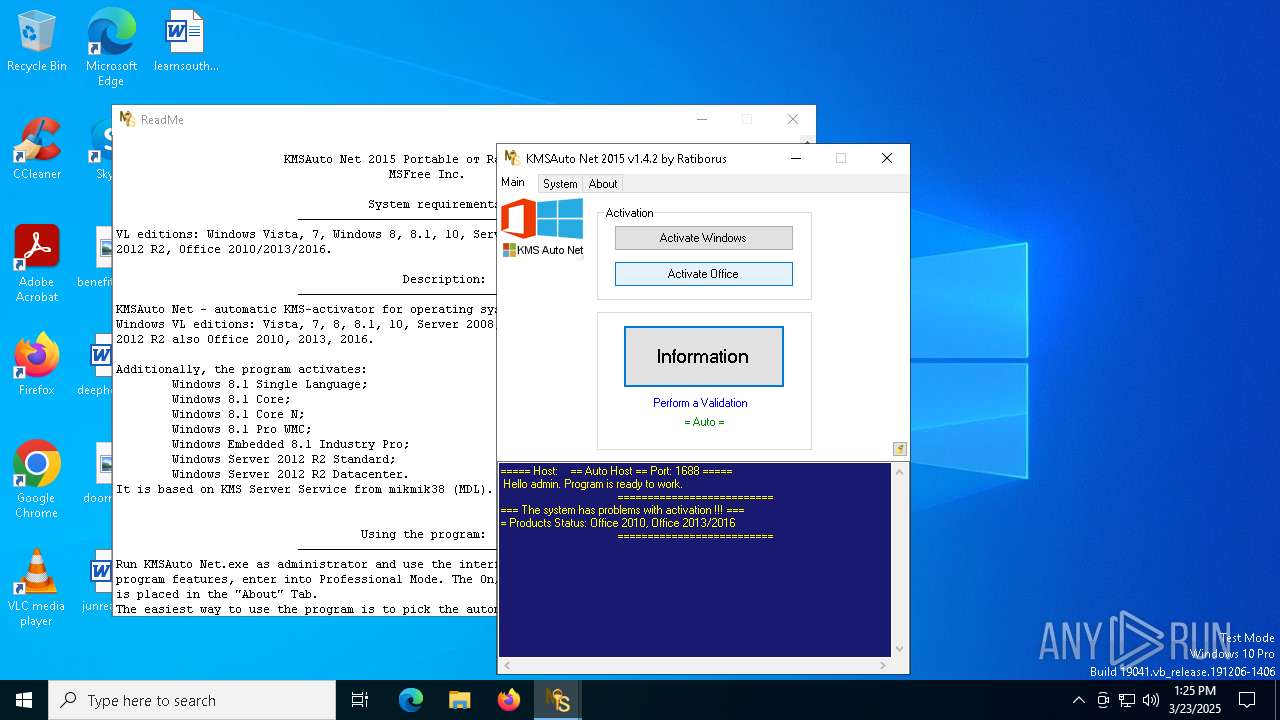
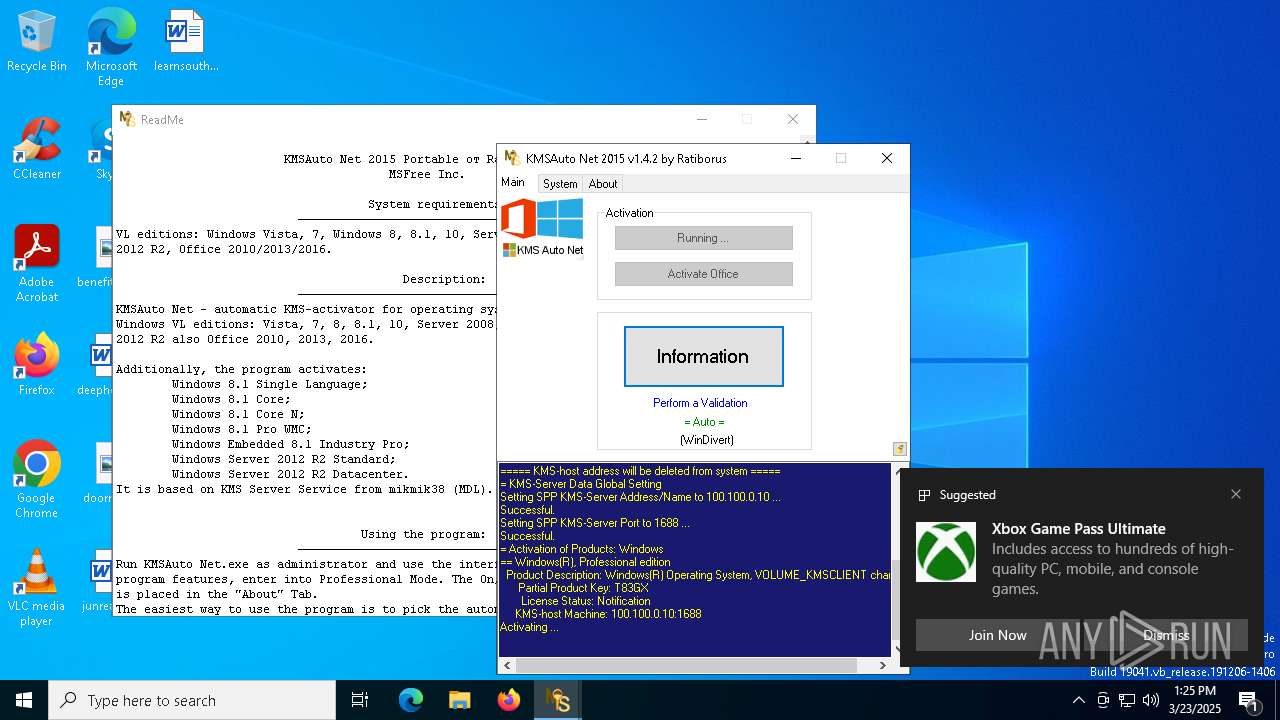
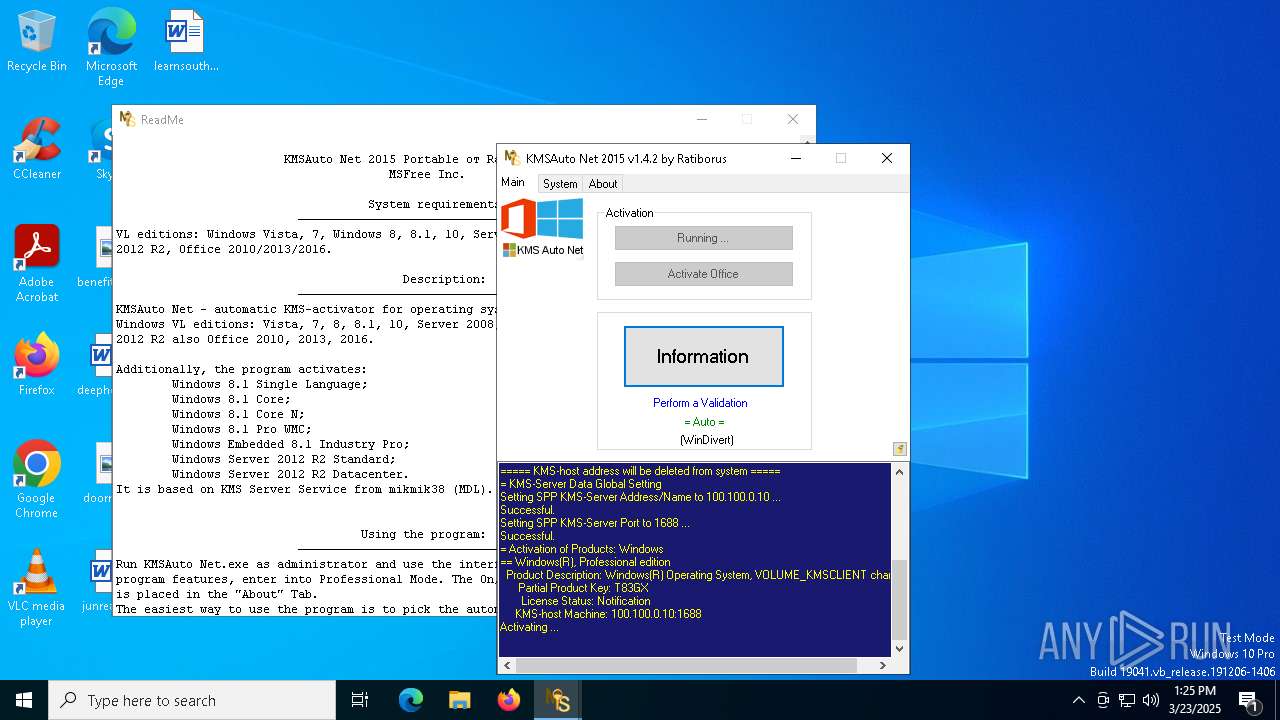
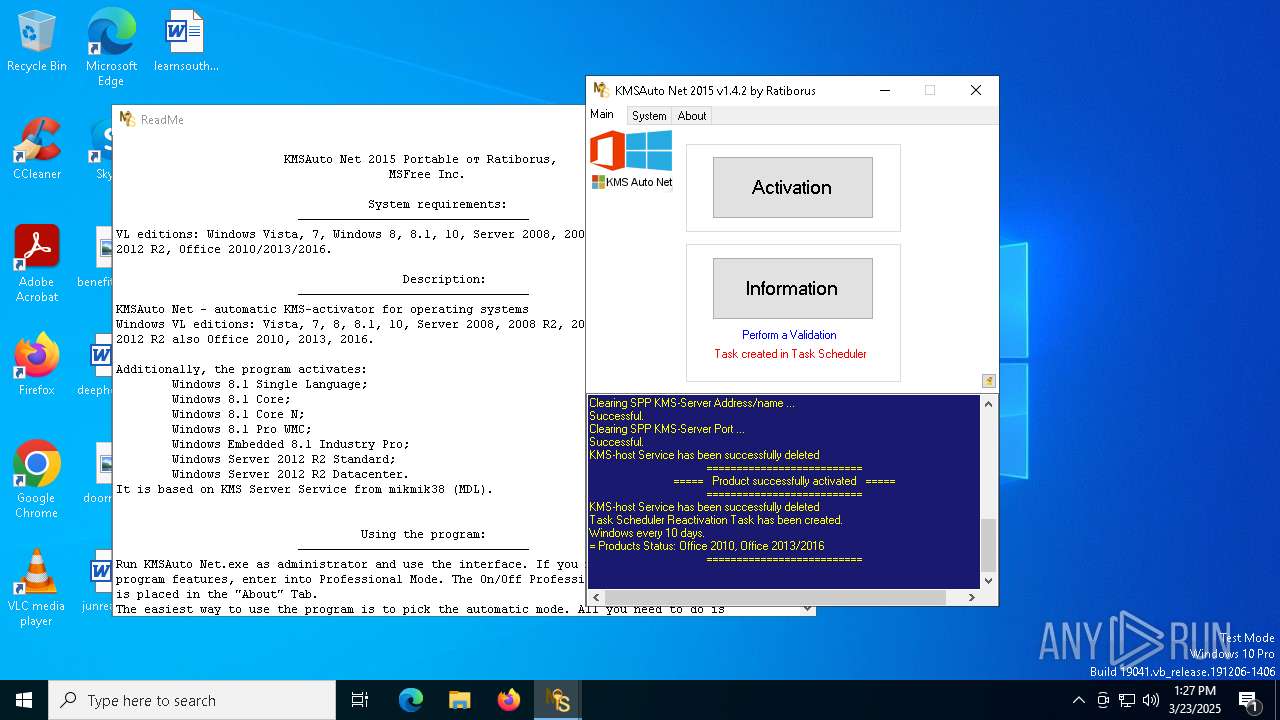
| File name: | KMSAuto Net.exe |
| Full analysis: | https://app.any.run/tasks/793309c4-27fc-4b7b-8286-6816557f5a1a |
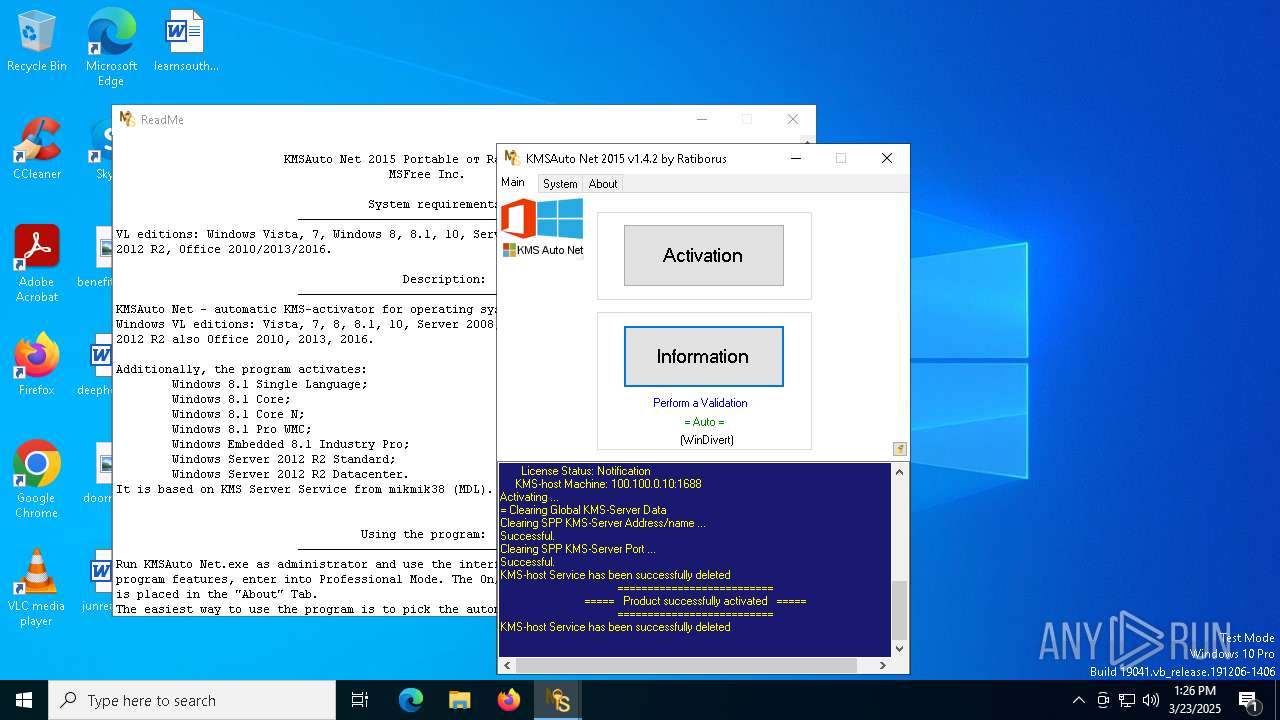
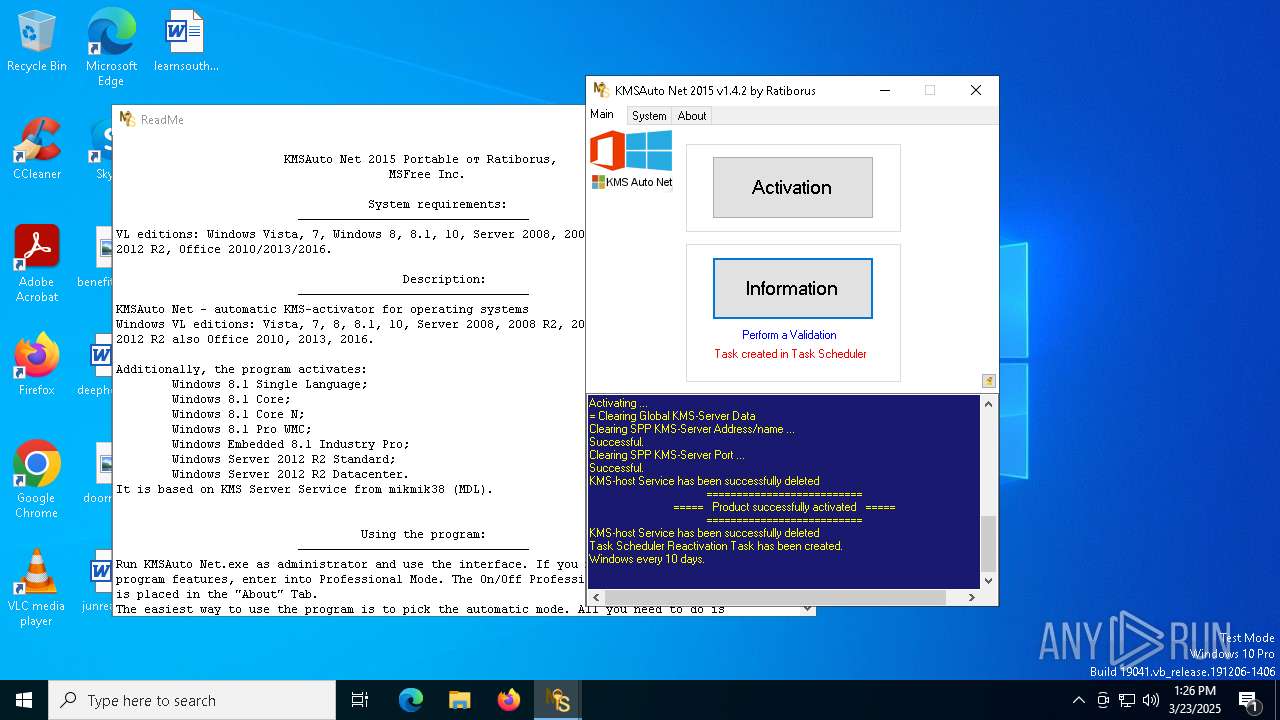
| Verdict: | Malicious activity |
| Analysis date: | March 23, 2025, 13:24:22 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 311F3BAA9BFA5B2364FEA8B254D15EB9 |
| SHA1: | 992585B81ACACCDB5C89361CDD1C1FD25E0C5CA1 |
| SHA256: | BEA219F0F08ED083677A0B869E658BA09785F470668EADC659DB2885FA89F3B9 |
| SSDEEP: | 196608:OwywCAfywOwe/3ywuywQywTyw3ywsywsywPbywgsywZywtywRywZywBywFywUywO:owCAqwUqwjwNw2wiwxwxwPewgxwUwQwN |
MALICIOUS
Executing a file with an untrusted certificate
- KMSAuto Net.exe (PID: 2284)
- certmgr.exe (PID: 5780)
- certmgr.exe (PID: 1168)
- KMSSS.exe (PID: 7084)
- FakeClient.exe (PID: 2984)
- certmgr.exe (PID: 2852)
- certmgr.exe (PID: 2092)
- certmgr.exe (PID: 4348)
- certmgr.exe (PID: 6960)
- KMSSS.exe (PID: 5780)
- FakeClient.exe (PID: 3300)
Opens a text file (SCRIPT)
- cscript.exe (PID: 2980)
- cscript.exe (PID: 2384)
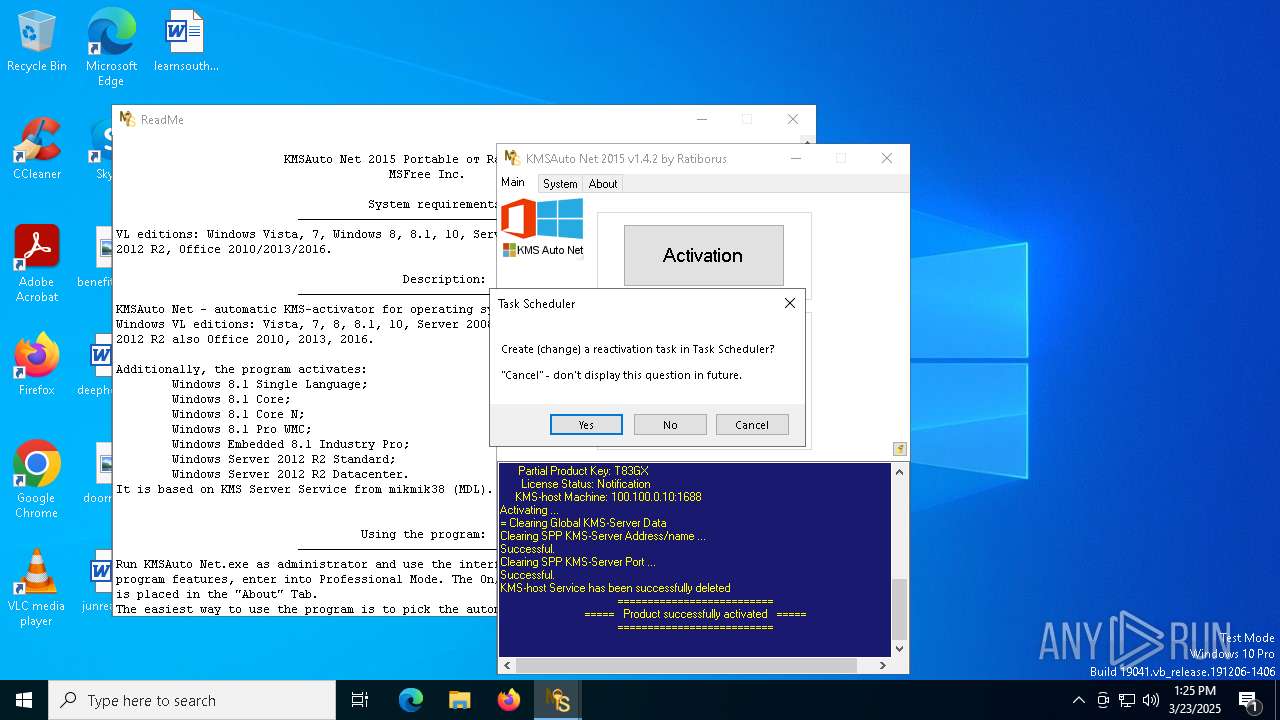
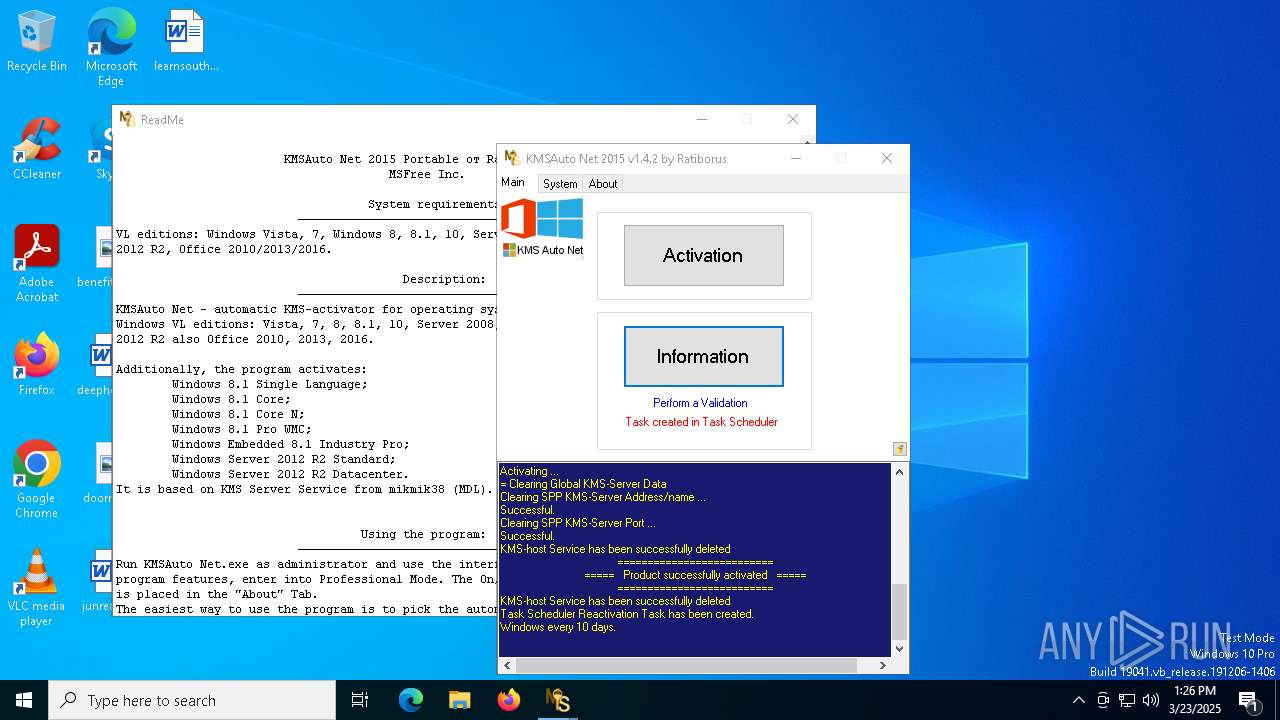
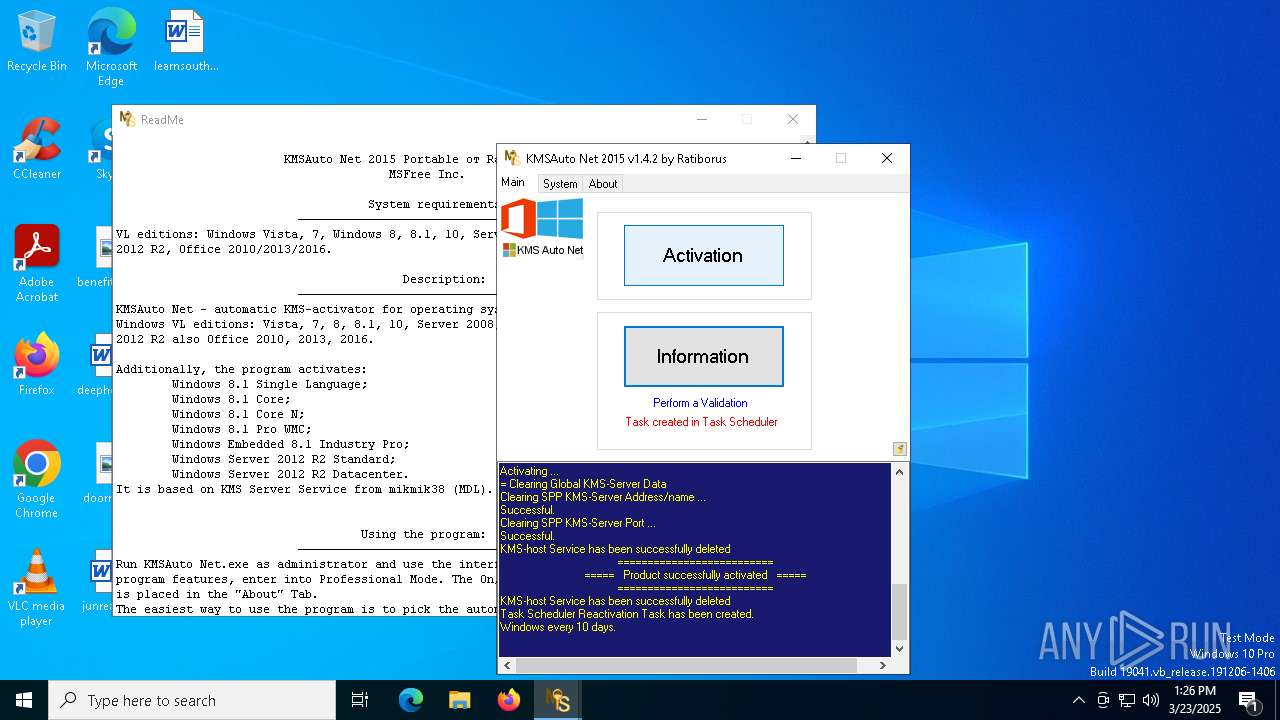
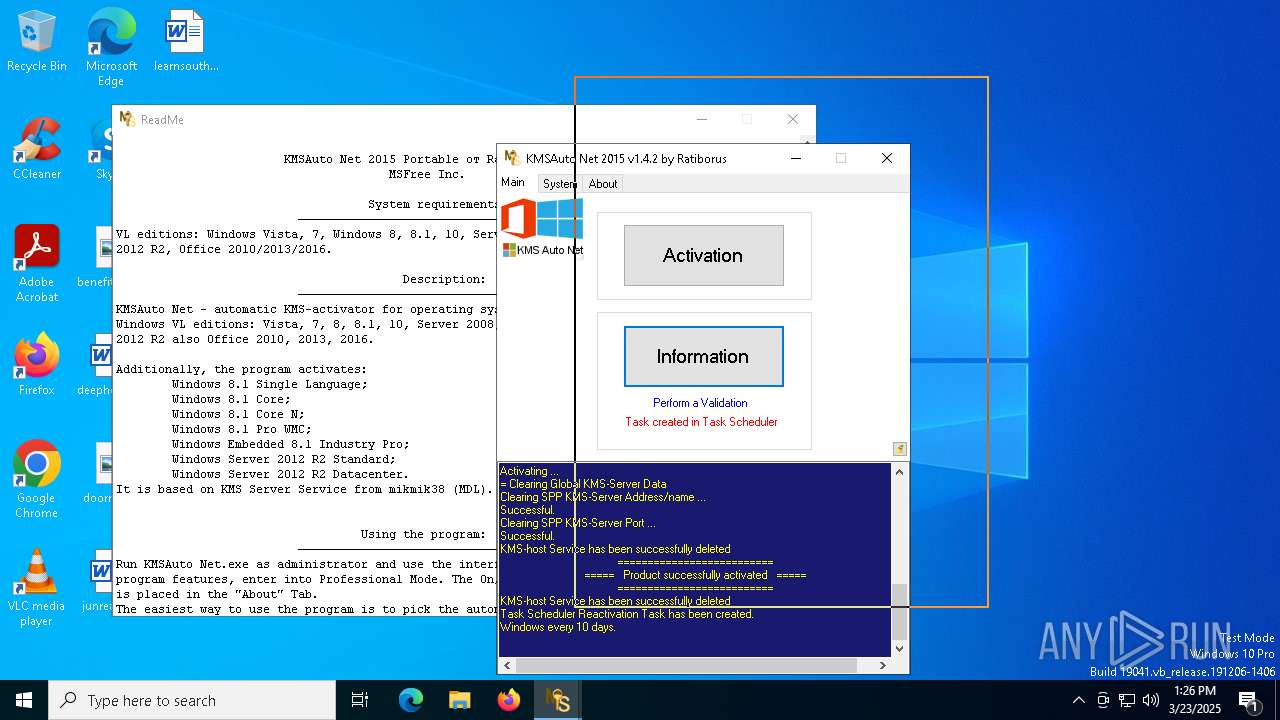
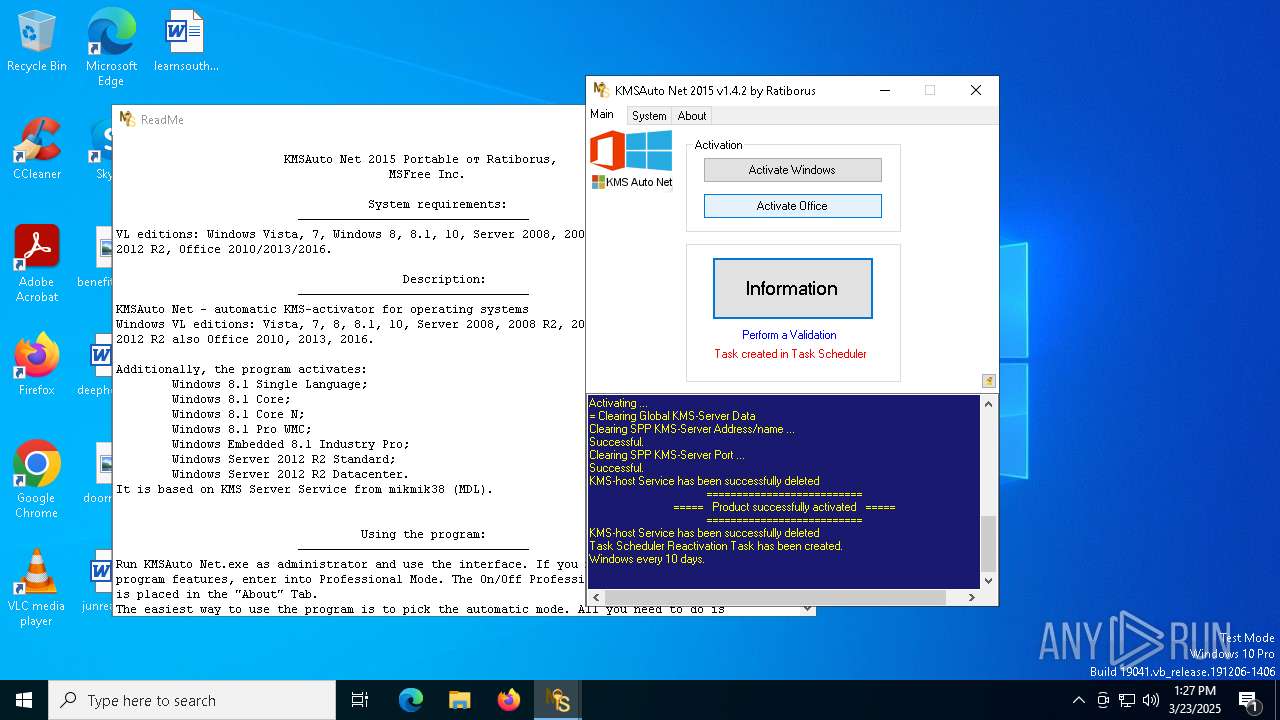
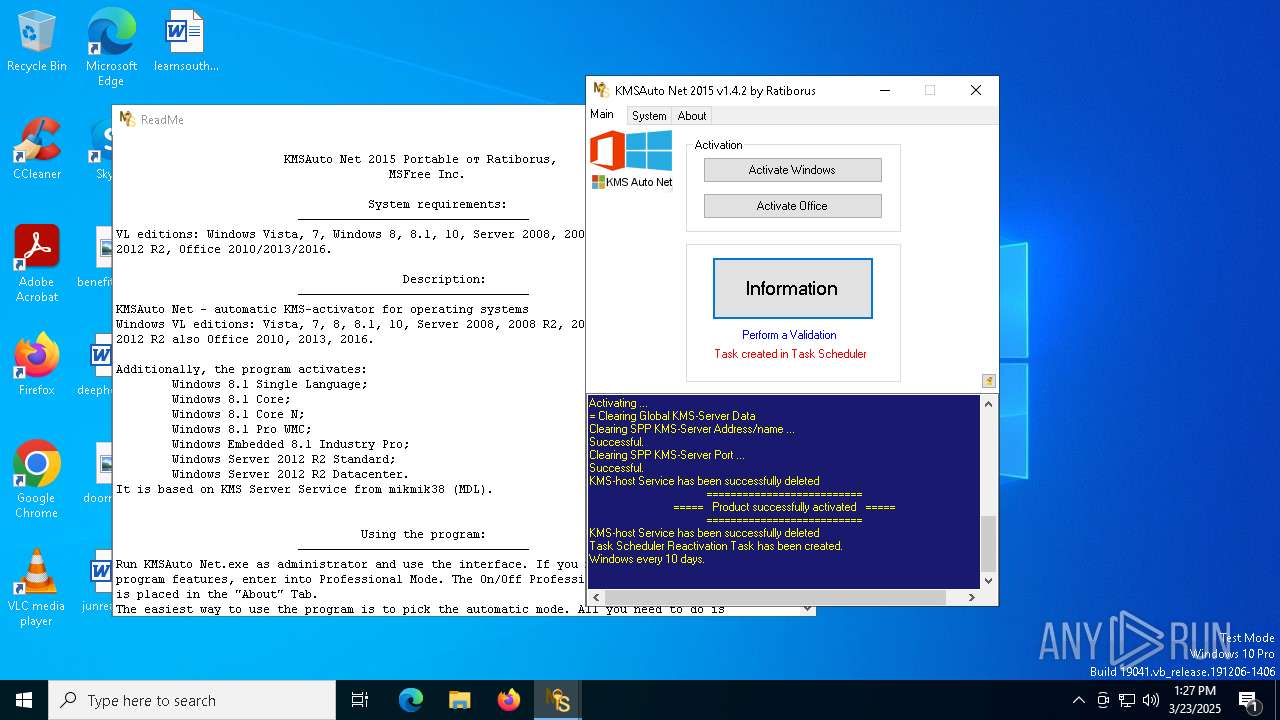
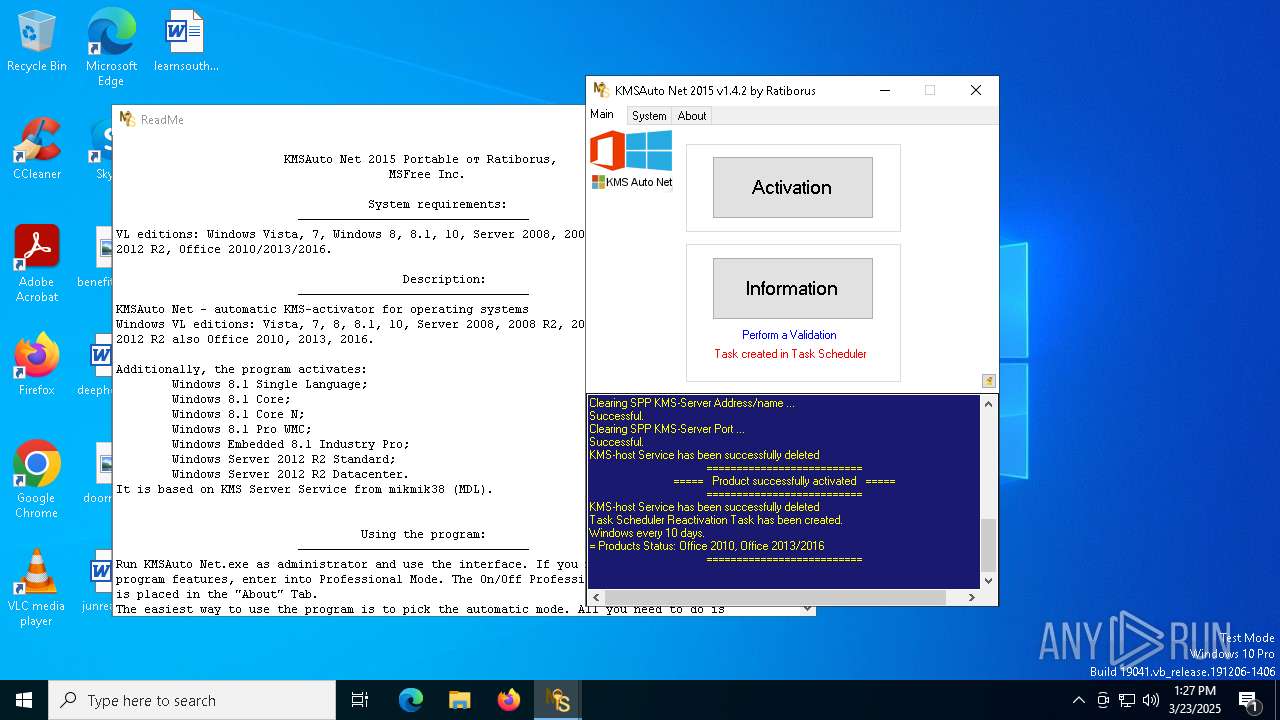
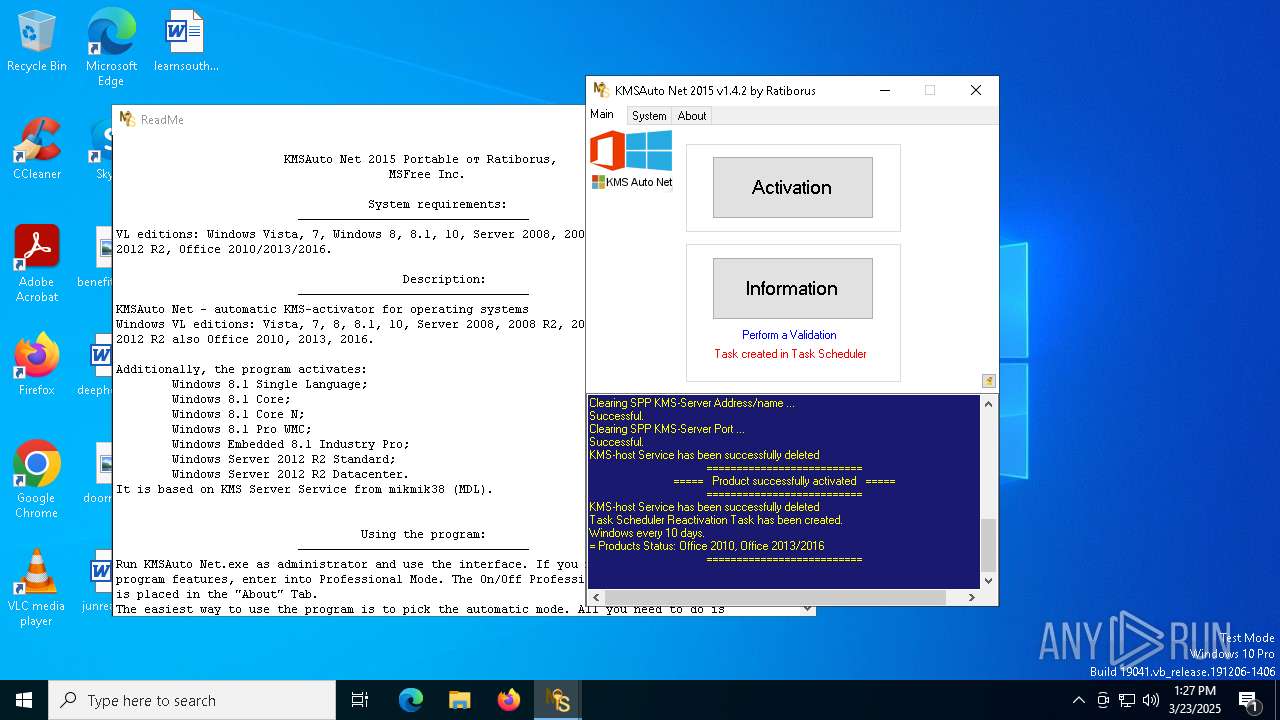
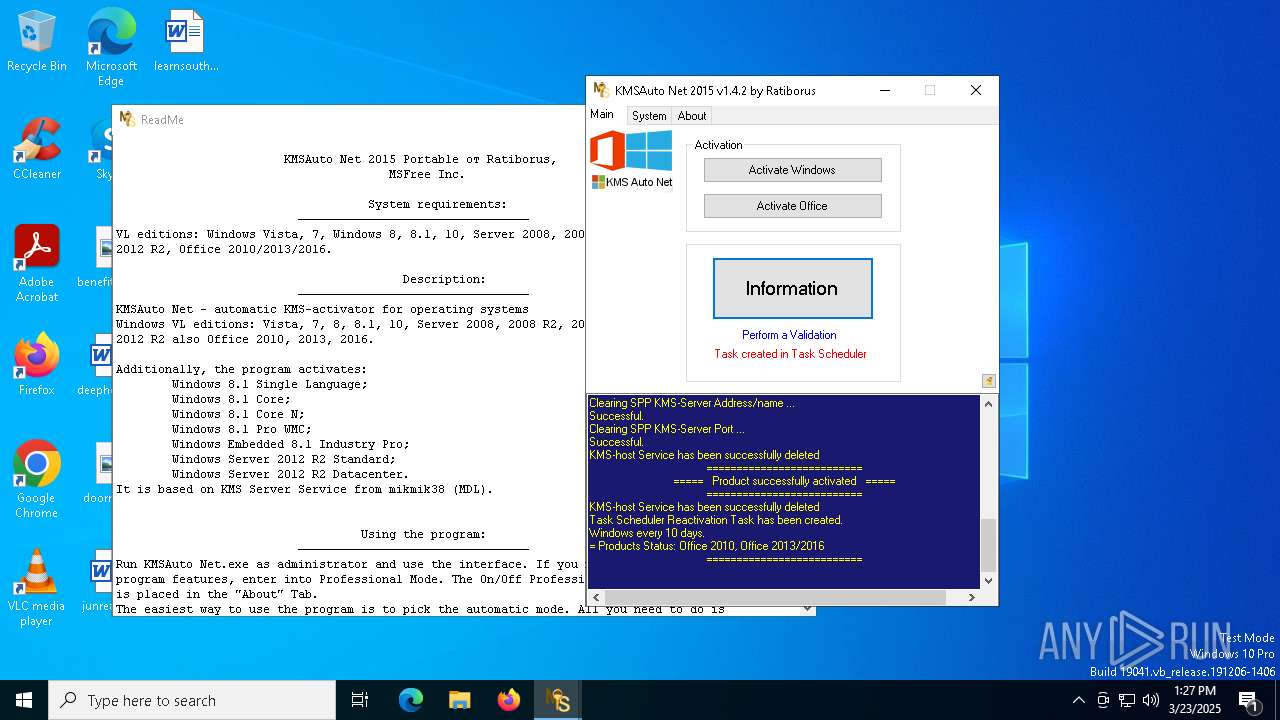
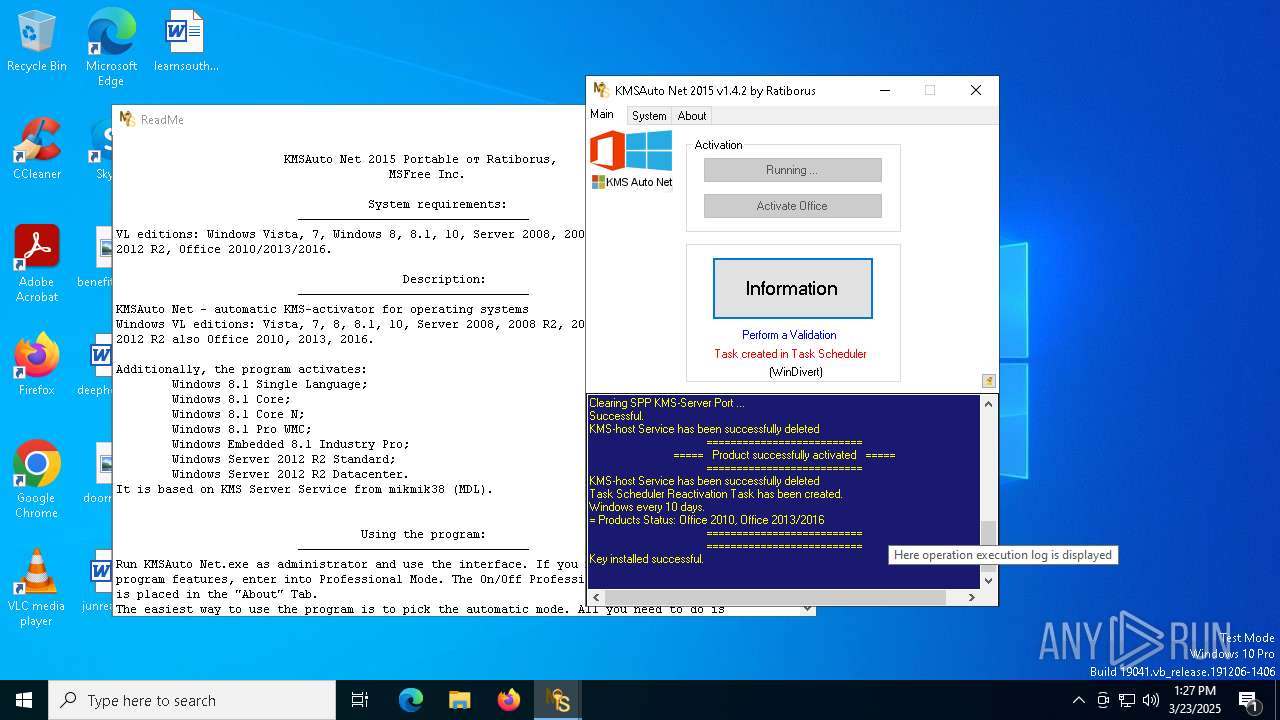
Uses Task Scheduler to run other applications
- cmd.exe (PID: 1512)
SUSPICIOUS
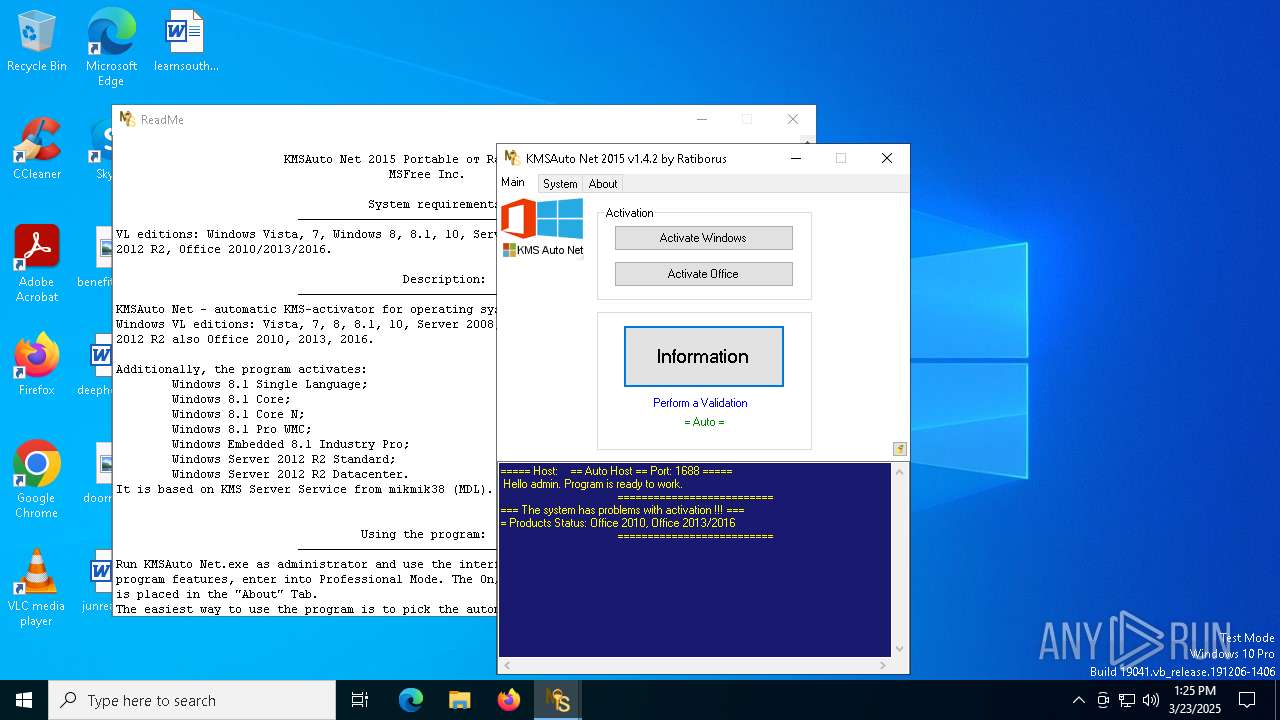
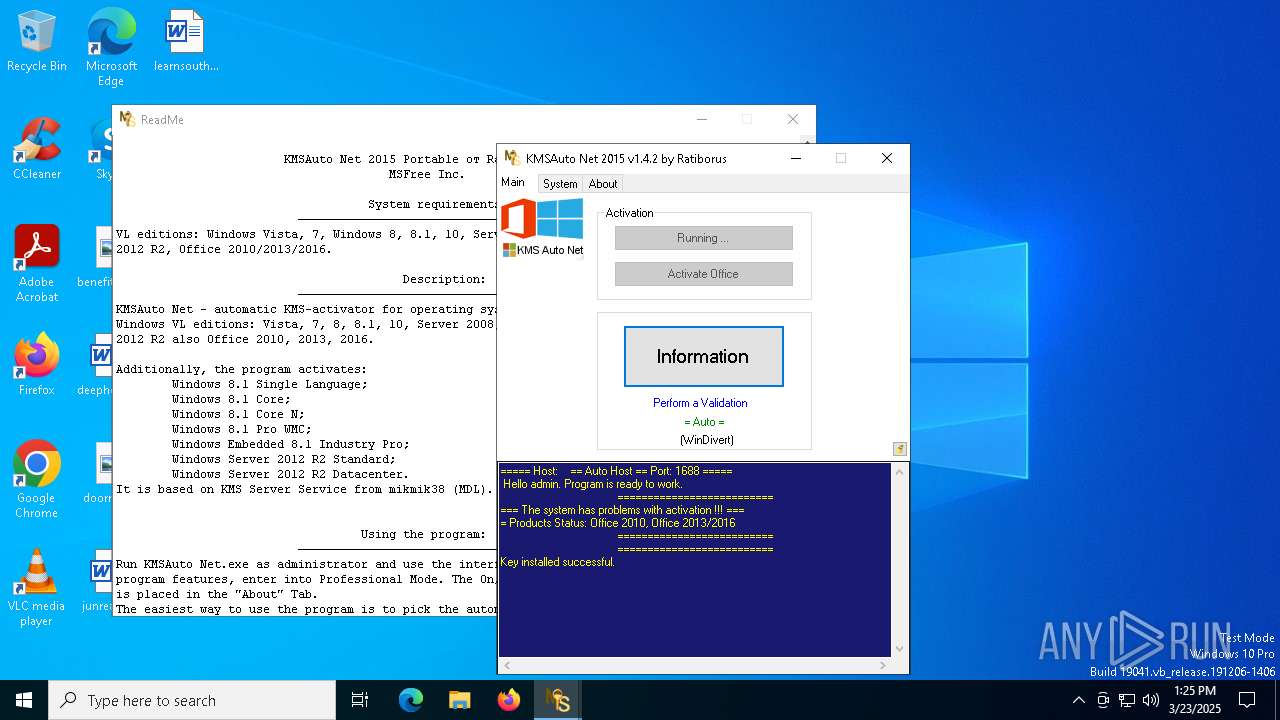
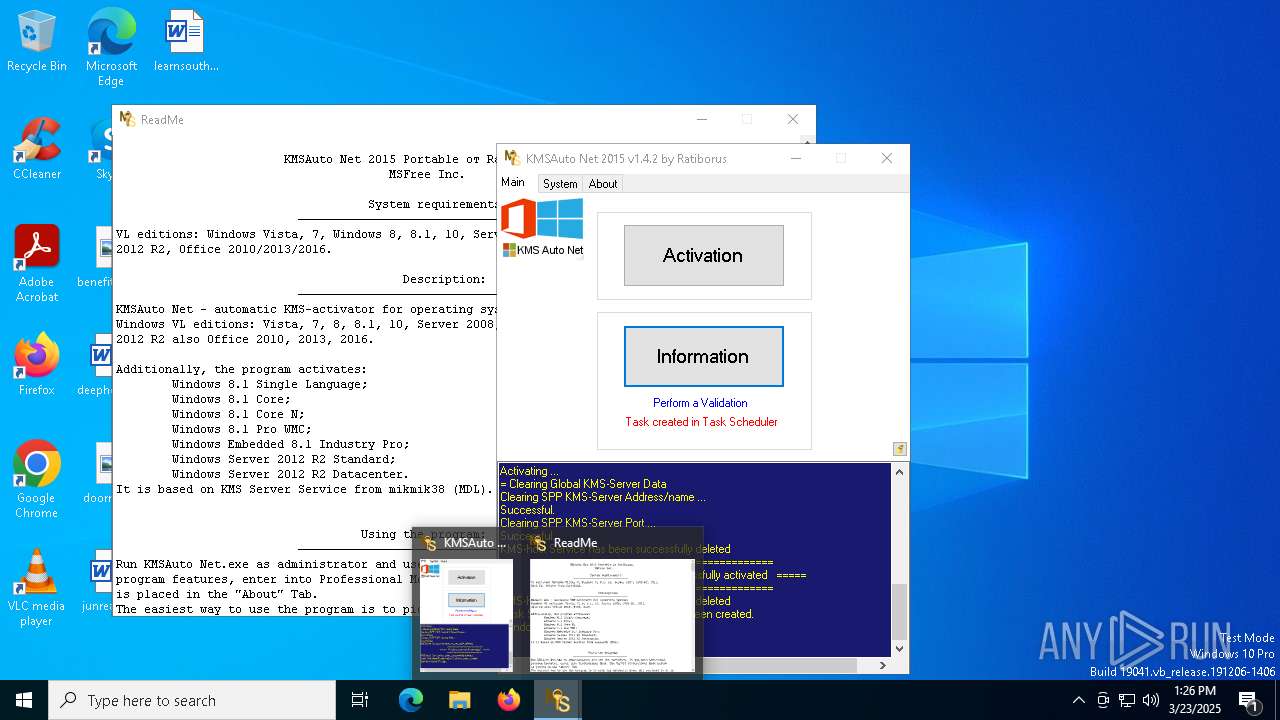
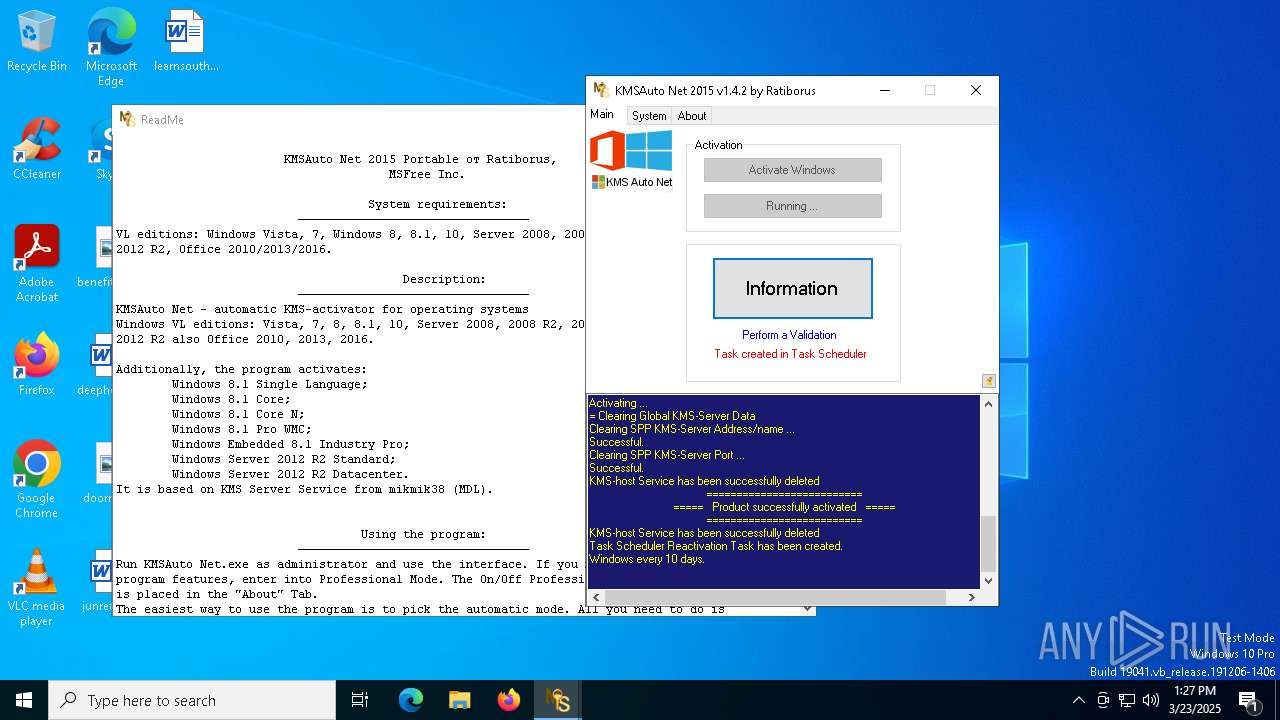
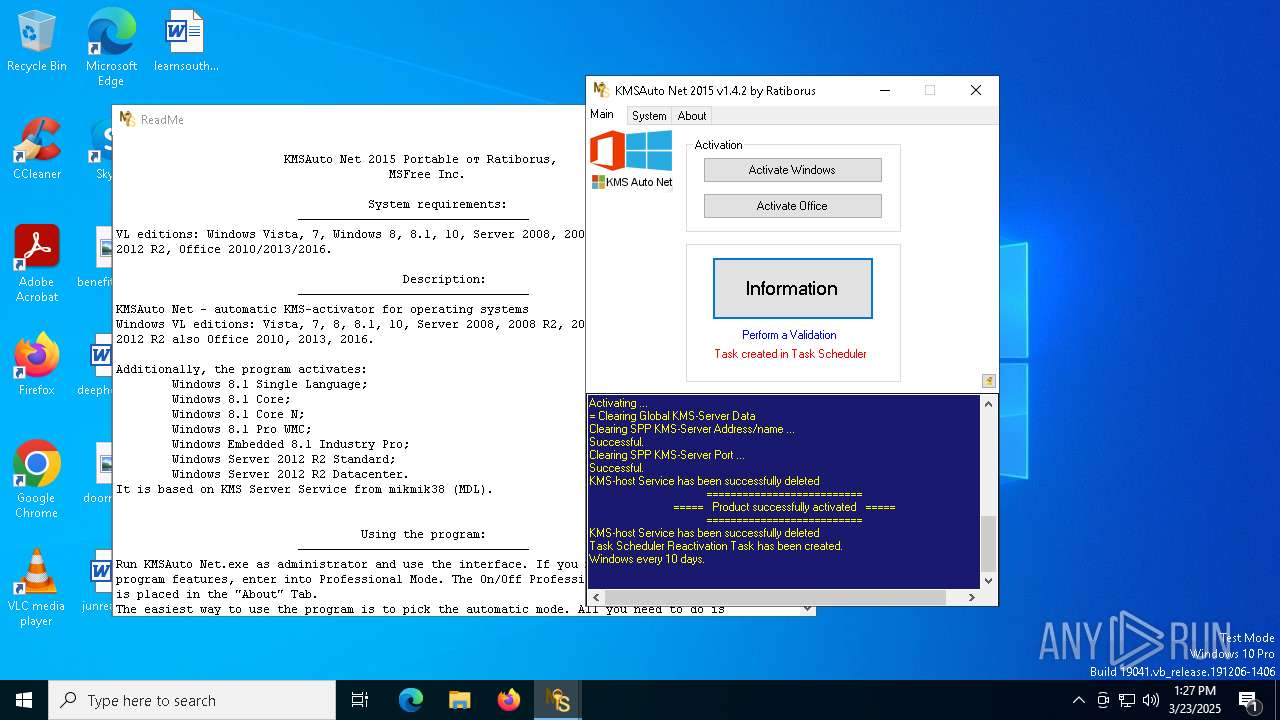
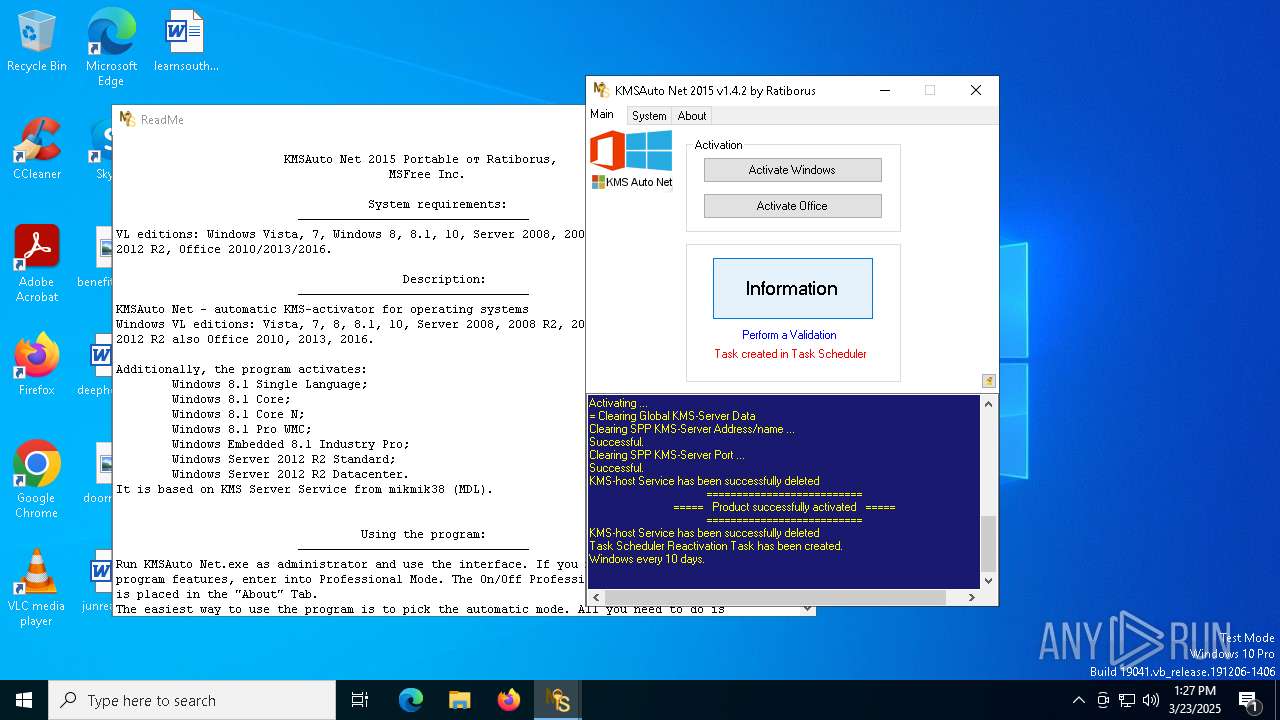
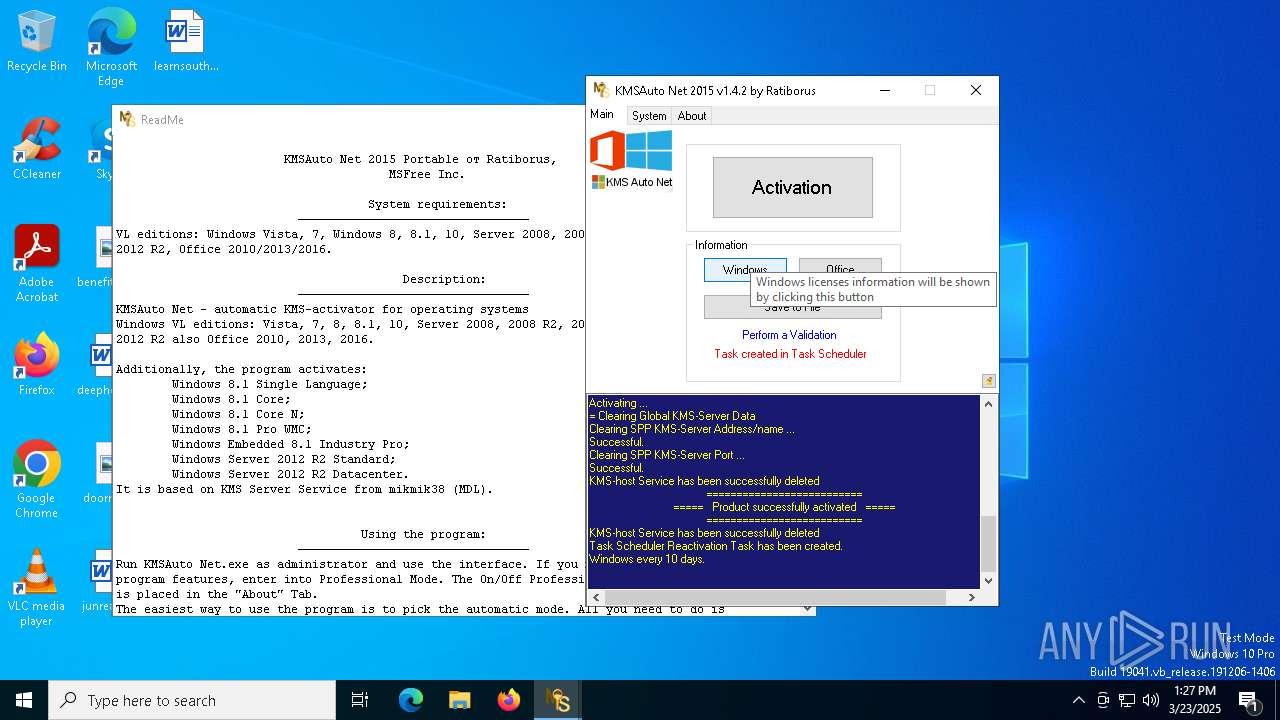
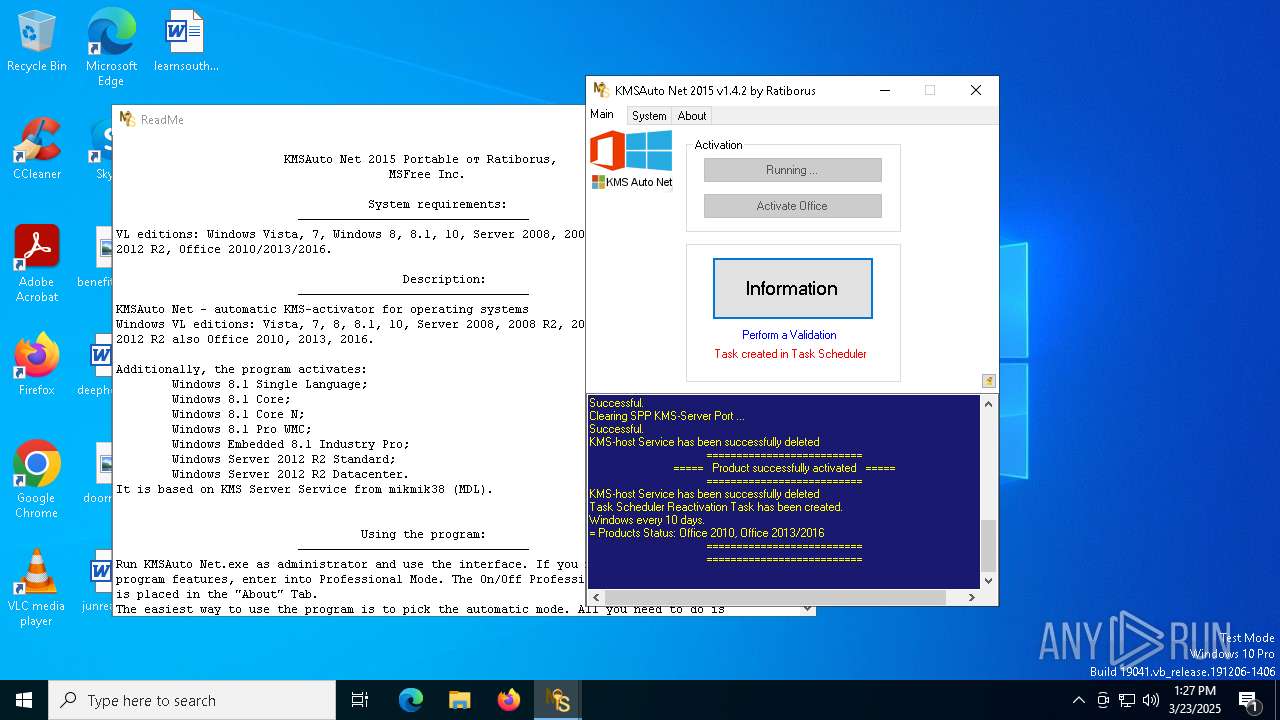
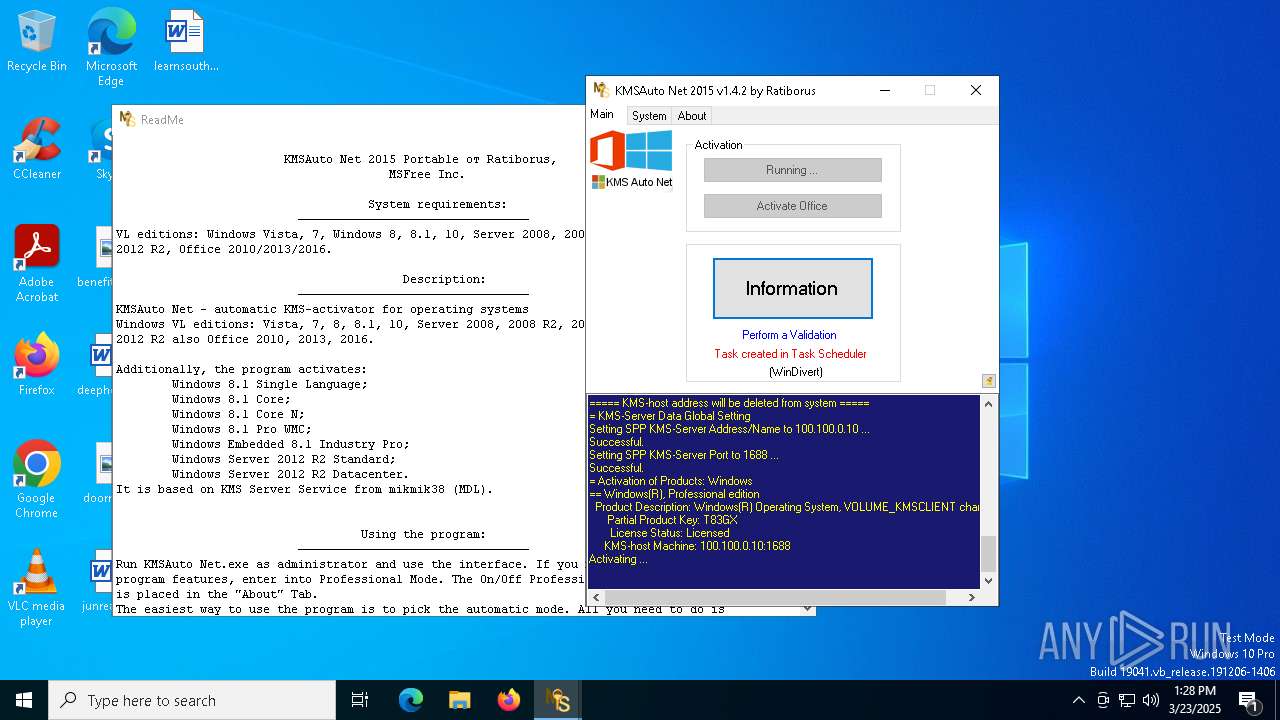
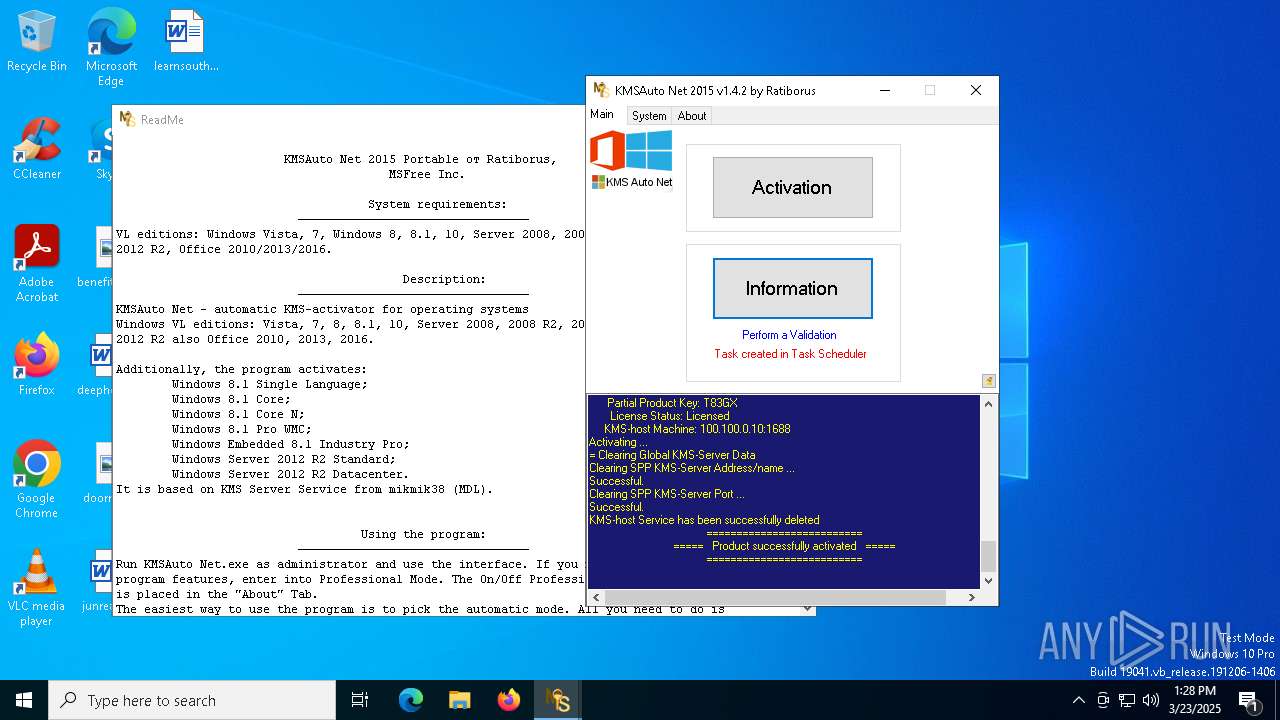
KMS tool has been detected
- KMSAuto Net.exe (PID: 5304)
- KMSAuto Net.exe (PID: 2284)
- KMSAuto Net.exe (PID: 5304)
There is functionality for taking screenshot (YARA)
- KMSAuto Net.exe (PID: 5304)
Gets full path of the running script (SCRIPT)
- cscript.exe (PID: 2980)
- cscript.exe (PID: 2384)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 2980)
- cscript.exe (PID: 2384)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- cscript.exe (PID: 2980)
- cscript.exe (PID: 2384)
The process executes VB scripts
- KMSAuto Net.exe (PID: 5304)
Checks whether a specific file exists (SCRIPT)
- cscript.exe (PID: 2980)
- cscript.exe (PID: 2384)
Reads data from a binary Stream object (SCRIPT)
- cscript.exe (PID: 2980)
- cscript.exe (PID: 2384)
Executes WMI query (SCRIPT)
- cscript.exe (PID: 2980)
- cscript.exe (PID: 2384)
Executable content was dropped or overwritten
- wzt.dat (PID: 2332)
- KMSAuto Net.exe (PID: 5304)
- AESDecoder.exe (PID: 5988)
- bin.dat (PID: 1272)
- bin_x64.dat (PID: 3968)
- wzt.dat (PID: 5172)
- bin.dat (PID: 132)
- bin_x64.dat (PID: 5728)
- AESDecoder.exe (PID: 4268)
- AESDecoder.exe (PID: 5232)
- bin.dat (PID: 5796)
- wzt.dat (PID: 6480)
- bin_x64.dat (PID: 5328)
Starts CMD.EXE for commands execution
- KMSAuto Net.exe (PID: 5304)
- cmd.exe (PID: 5968)
- cmd.exe (PID: 1184)
Starts application with an unusual extension
- cmd.exe (PID: 6712)
- cmd.exe (PID: 6708)
- cmd.exe (PID: 5116)
- cmd.exe (PID: 4268)
- cmd.exe (PID: 2096)
- cmd.exe (PID: 5216)
- cmd.exe (PID: 1056)
- cmd.exe (PID: 2552)
- cmd.exe (PID: 6944)
Process drops legitimate windows executable
- wzt.dat (PID: 2332)
- bin_x64.dat (PID: 3968)
- wzt.dat (PID: 5172)
- bin_x64.dat (PID: 5728)
- wzt.dat (PID: 6480)
- bin_x64.dat (PID: 5328)
Drops 7-zip archiver for unpacking
- KMSAuto Net.exe (PID: 5304)
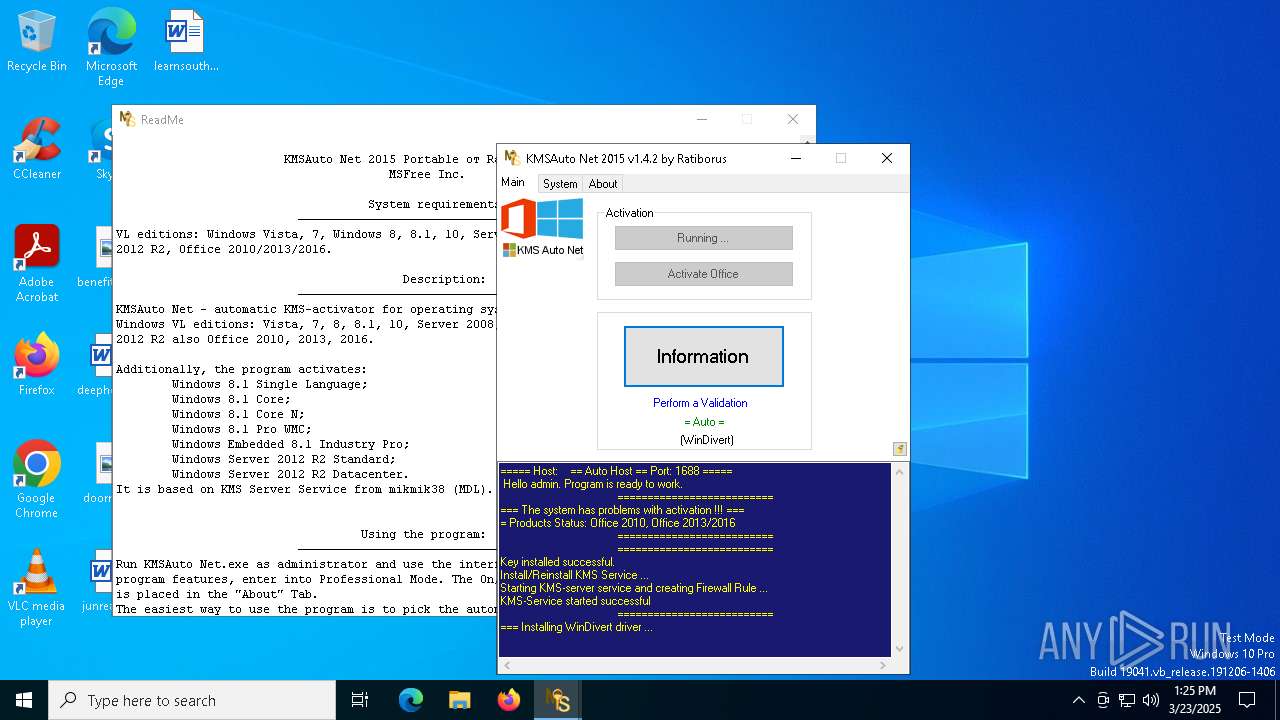
Drops a system driver (possible attempt to evade defenses)
- bin_x64.dat (PID: 3968)
- bin_x64.dat (PID: 5728)
- bin_x64.dat (PID: 5328)
Adds/modifies Windows certificates
- certmgr.exe (PID: 5780)
- certmgr.exe (PID: 1168)
- certmgr.exe (PID: 2852)
- certmgr.exe (PID: 2092)
- certmgr.exe (PID: 6960)
- certmgr.exe (PID: 4348)
Application launched itself
- cmd.exe (PID: 5968)
- cmd.exe (PID: 1184)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- KMSAuto Net.exe (PID: 5304)
Uses ROUTE.EXE to modify routing table
- cmd.exe (PID: 3888)
- cmd.exe (PID: 6080)
Uses NETSH.EXE to add a firewall rule or allowed programs
- KMSAuto Net.exe (PID: 5304)
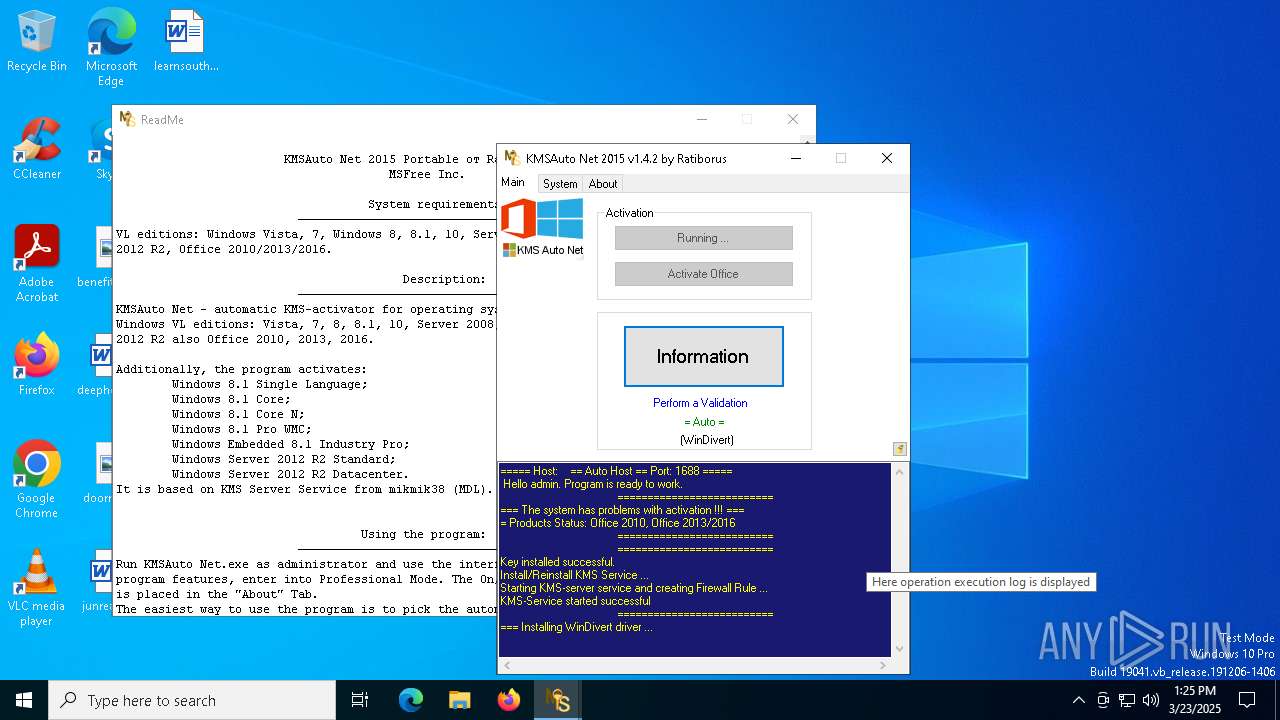
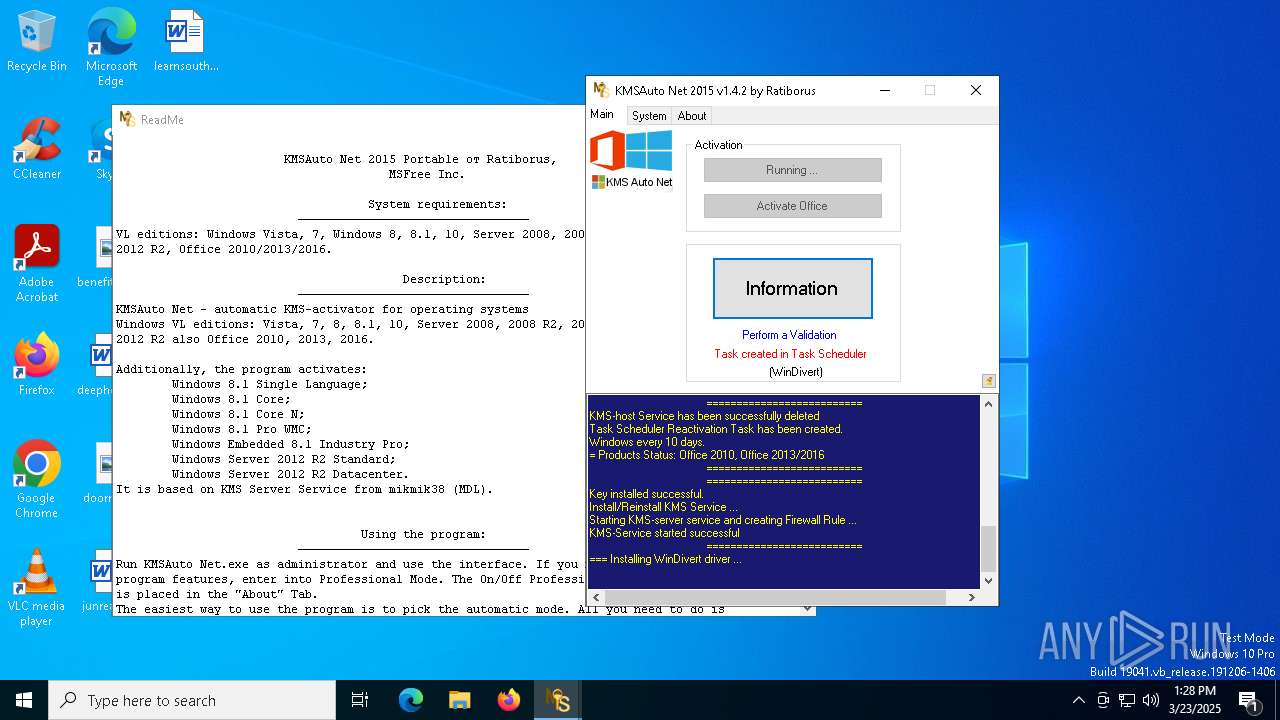
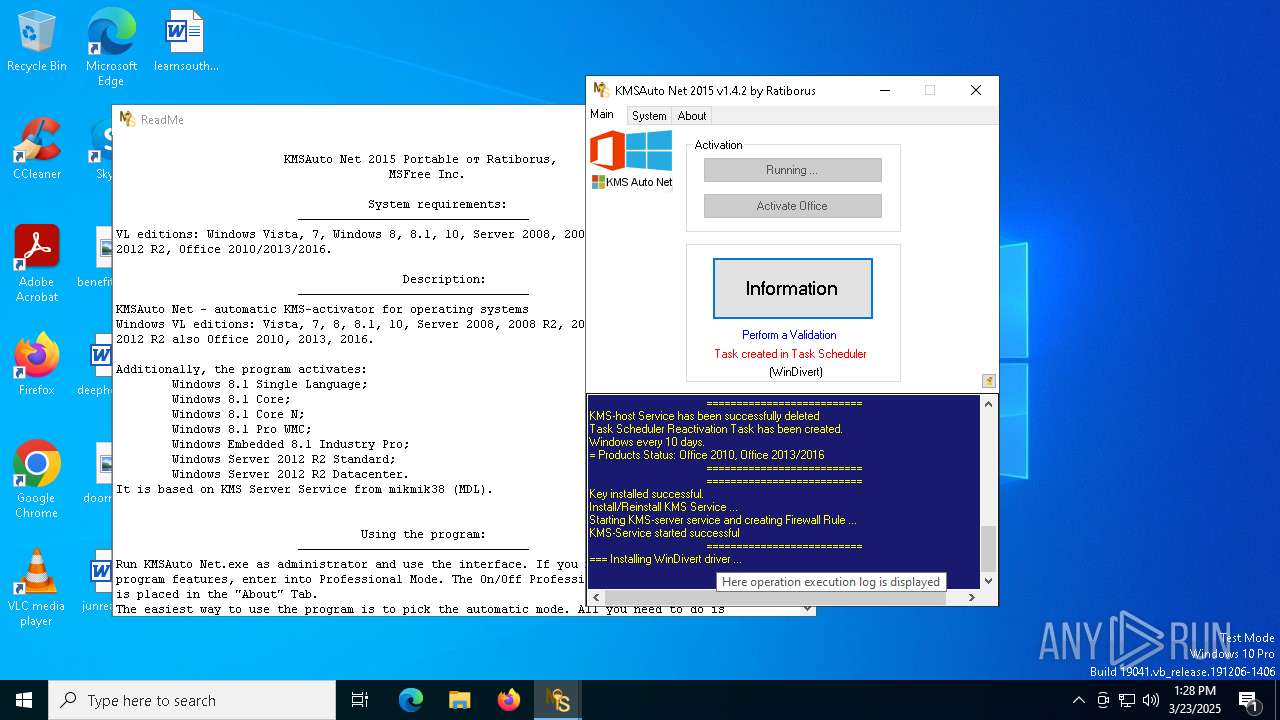
Creates a new Windows service
- sc.exe (PID: 4844)
- sc.exe (PID: 6904)
Windows service management via SC.EXE
- sc.exe (PID: 6036)
- sc.exe (PID: 5796)
- sc.exe (PID: 5332)
- sc.exe (PID: 3304)
- sc.exe (PID: 6268)
- sc.exe (PID: 6592)
Executes as Windows Service
- KMSSS.exe (PID: 7084)
- KMSSS.exe (PID: 5780)
Creates or modifies Windows services
- KMSAuto Net.exe (PID: 5304)
Uses REG/REGEDIT.EXE to modify registry
- KMSAuto Net.exe (PID: 5304)
- cmd.exe (PID: 4040)
- cmd.exe (PID: 4212)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 3024)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2288)
- cmd.exe (PID: 6900)
Uses ROUTE.EXE to obtain the routing table information
- cmd.exe (PID: 5204)
- cmd.exe (PID: 5360)
Stops a currently running service
- sc.exe (PID: 2096)
- sc.exe (PID: 968)
- sc.exe (PID: 3028)
- sc.exe (PID: 644)
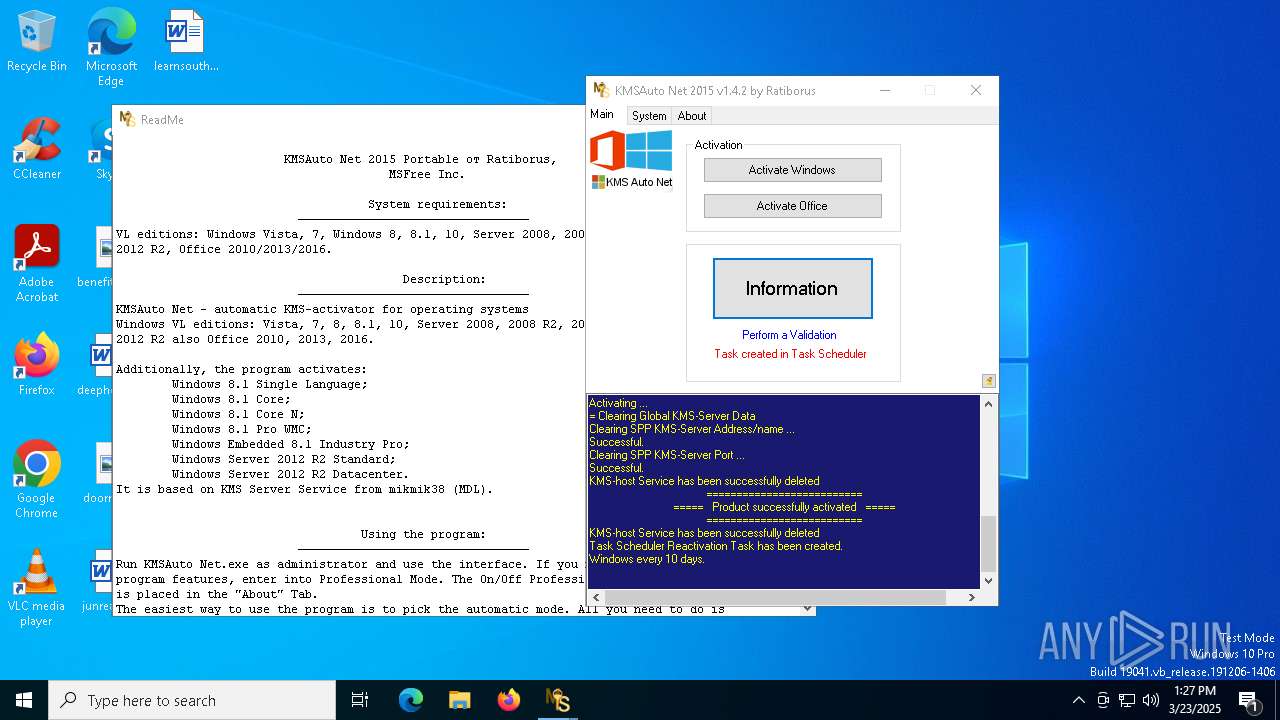
Deletes scheduled task without confirmation
- schtasks.exe (PID: 1628)
Modifies existing scheduled task
- schtasks.exe (PID: 6264)
INFO
Reads product name
- KMSAuto Net.exe (PID: 5304)
Reads Environment values
- KMSAuto Net.exe (PID: 5304)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 1328)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 1328)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 4040)
- BackgroundTransferHost.exe (PID: 1328)
- BackgroundTransferHost.exe (PID: 5960)
- BackgroundTransferHost.exe (PID: 6080)
- BackgroundTransferHost.exe (PID: 5756)
- BackgroundTransferHost.exe (PID: 4776)
- cscript.exe (PID: 2980)
- cscript.exe (PID: 2384)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 1328)
- KMSAuto Net.exe (PID: 5304)
Creates files in the program directory
- cmd.exe (PID: 1012)
- wzt.dat (PID: 2332)
- KMSAuto Net.exe (PID: 5304)
- bin.dat (PID: 1272)
- AESDecoder.exe (PID: 5988)
- bin_x64.dat (PID: 3968)
- KMSSS.exe (PID: 7084)
- wzt.dat (PID: 5172)
- cmd.exe (PID: 3800)
- bin.dat (PID: 132)
- AESDecoder.exe (PID: 4268)
- bin_x64.dat (PID: 5728)
- wzt.dat (PID: 6480)
- cmd.exe (PID: 5952)
- bin.dat (PID: 5796)
- AESDecoder.exe (PID: 5232)
- bin_x64.dat (PID: 5328)
- KMSSS.exe (PID: 5780)
Creates a new folder
- cmd.exe (PID: 1012)
- cmd.exe (PID: 3800)
- cmd.exe (PID: 5952)
Checks supported languages
- wzt.dat (PID: 2332)
- certmgr.exe (PID: 5780)
- certmgr.exe (PID: 1168)
- bin.dat (PID: 1272)
- AESDecoder.exe (PID: 5988)
- bin_x64.dat (PID: 3968)
- KMSSS.exe (PID: 7084)
- FakeClient.exe (PID: 2984)
- ShellExperienceHost.exe (PID: 3024)
- certmgr.exe (PID: 2852)
- wzt.dat (PID: 5172)
- AESDecoder.exe (PID: 4268)
- certmgr.exe (PID: 2092)
- bin.dat (PID: 132)
- bin_x64.dat (PID: 5728)
- wzt.dat (PID: 6480)
- certmgr.exe (PID: 4348)
- bin.dat (PID: 5796)
- AESDecoder.exe (PID: 5232)
- certmgr.exe (PID: 6960)
- bin_x64.dat (PID: 5328)
- KMSSS.exe (PID: 5780)
- FakeClient.exe (PID: 3300)
The sample compiled with english language support
- wzt.dat (PID: 2332)
- AESDecoder.exe (PID: 5988)
- KMSAuto Net.exe (PID: 5304)
- bin_x64.dat (PID: 3968)
- wzt.dat (PID: 5172)
- bin_x64.dat (PID: 5728)
- AESDecoder.exe (PID: 4268)
- wzt.dat (PID: 6480)
- AESDecoder.exe (PID: 5232)
- bin_x64.dat (PID: 5328)
Reads the computer name
- KMSSS.exe (PID: 7084)
- FakeClient.exe (PID: 2984)
- ShellExperienceHost.exe (PID: 3024)
- KMSSS.exe (PID: 5780)
- FakeClient.exe (PID: 3300)
Adds a route via ROUTE.EXE
- ROUTE.EXE (PID: 5232)
- ROUTE.EXE (PID: 7104)
Reads the machine GUID from the registry
- KMSSS.exe (PID: 7084)
- KMSSS.exe (PID: 5780)
Deletes a route via ROUTE.EXE
- ROUTE.EXE (PID: 6108)
- ROUTE.EXE (PID: 732)
Create files in a temporary directory
- KMSAuto Net.exe (PID: 5304)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (16) |
|---|---|---|
| .scr | | | Windows screen saver (7.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.8) |
| .exe | | | Win32 Executable (generic) (2.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:11:12 13:50:41+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 8968704 |
| InitializedDataSize: | 49152 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x88f916 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.4.2.0 |
| ProductVersionNumber: | 1.4.2.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | MSFree Inc. |
| FileDescription: | KMSAuto Net |
| FileVersion: | 1.4.2 |
| InternalName: | KMSAuto Net.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | KMSAuto Net.exe |
| ProductName: | KMSAuto Net |
| ProductVersion: | 1.4.2 |
| AssemblyVersion: | 1.4.2.0 |
Total processes
385
Monitored processes
234
Malicious processes
9
Suspicious processes
12
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | C:\WINDOWS\Sysnative\cmd.exe /D /c del /F /Q "kmsauto.ini" | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 132 | bin.dat -y -pkmsauto | C:\ProgramData\KMSAutoS\bin.dat | cmd.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7z Console SFX Exit code: 0 Version: 15.09 beta Modules
| |||||||||||||||
| 208 | C:\WINDOWS\Sysnative\cmd.exe /D /c del /F /Q "bin_x64.dat" | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | reg.exe DELETE HKLM\SYSTEM\CurrentControlSet\Services\KMSEmulator /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | C:\WINDOWS\Sysnative\cmd.exe /D /c del /F /Q "bin_x64.dat" | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | C:\WINDOWS\Sysnative\cmd.exe /D /c certmgr.exe -add wzt.cer -n wzt -s -r localMachine TRUSTEDPUBLISHER | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
15 345
Read events
15 296
Write events
35
Delete events
14
Modification events
| (PID) Process: | (4040) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4040) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4040) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1328) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1328) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1328) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6080) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6080) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6080) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5960) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
50
Suspicious files
31
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1328 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | — | |
MD5:— | SHA256:— | |||
| 1328 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | — | |
MD5:— | SHA256:— | |||
| 1328 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\489f16cc-0562-4a35-8fcc-4d9648806e72.down_data | — | |
MD5:— | SHA256:— | |||
| 1328 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\489f16cc-0562-4a35-8fcc-4d9648806e72.67eff38c-9c41-4d3d-8f19-fc3ad565d726.down_meta | — | |
MD5:— | SHA256:— | |||
| 1328 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\901e0f11-ce72-46d2-af2b-6ed13f11b5f3.67eff38c-9c41-4d3d-8f19-fc3ad565d726.down_meta | — | |
MD5:— | SHA256:— | |||
| 5304 | KMSAuto Net.exe | C:\Users\admin\AppData\Local\MSfree Inc\kmsauto.ini | text | |
MD5:B22721ECC7249380EF3032685ED19A5A | SHA256:2AC517A3388939951E5BC81489A251193C4BCB4620A9968BA0EC8F34594952D8 | |||
| 1328 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\901e0f11-ce72-46d2-af2b-6ed13f11b5f3.up_meta_secure | binary | |
MD5:AC83CE38587C9F8D8E47476F133D71ED | SHA256:C5A007FFCE08CC55D7ABCED0E6BC4D58310A7FE13859E59DB0863856DDCCE2F2 | |||
| 1272 | bin.dat | C:\ProgramData\KMSAuto\bin\TunMirror.exe.aes | binary | |
MD5:A59C42386E14D73EC83CC01A4AF1551B | SHA256:8751A3C6CF2E3A1CD8E9C7B63BB3CBA177476319A67AA766F317151C9CA83AEC | |||
| 5988 | AESDecoder.exe | C:\ProgramData\KMSAuto\bin\TunMirror.exe | executable | |
MD5:FB5F055633E4F7890004972E108A07CD | SHA256:02145C3F60E704DF17919CD26CB79BD31A12B98D66B0B7FD1CF7EA894AD1F871 | |||
| 3968 | bin_x64.dat | C:\ProgramData\KMSAuto\bin\driver\x64TAP2\tapoas.inf | binary | |
MD5:61243CB103543EE3163BF16DF69BCB54 | SHA256:1652B1DE2F15EEACBD06E0AB14ADA5A466316FFD3AB88D4A2A46CFCBD25FDFA1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
26
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1328 | BackgroundTransferHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6736 | backgroundTaskHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5384 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5384 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 40.126.31.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 40.126.31.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6736 | backgroundTaskHost.exe | 20.31.169.57:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6736 | backgroundTaskHost.exe | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |