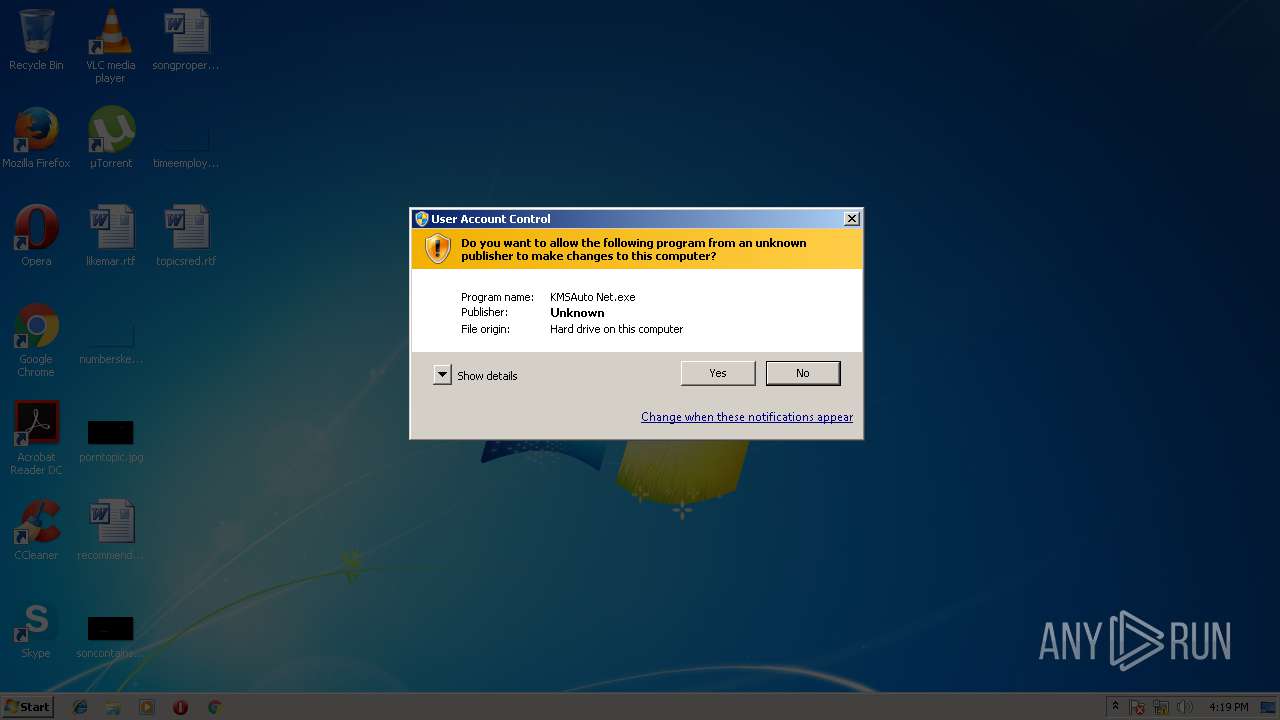
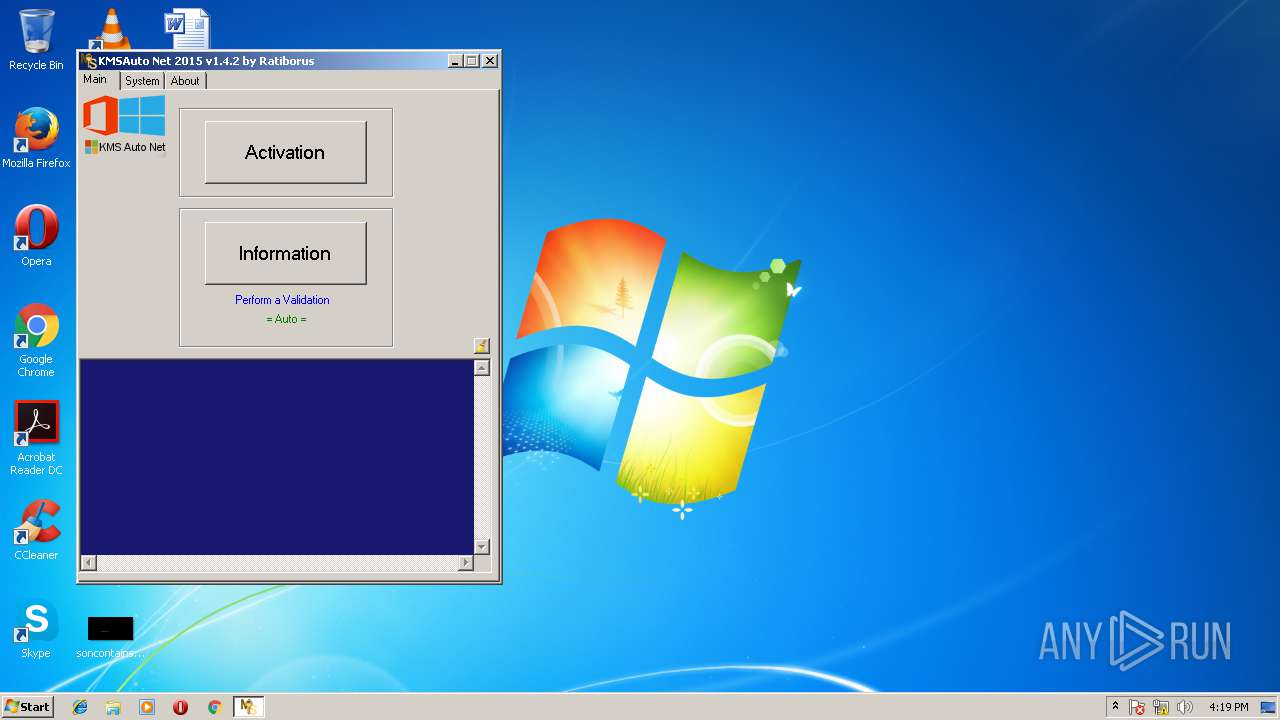
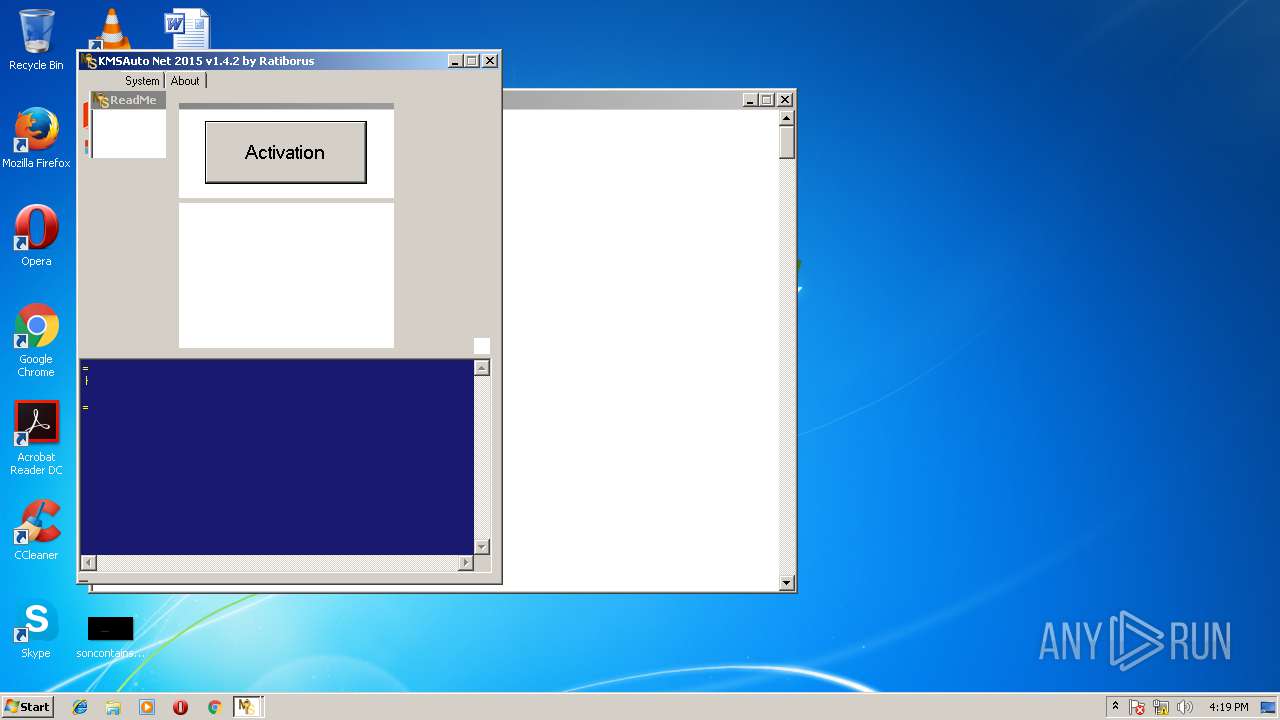
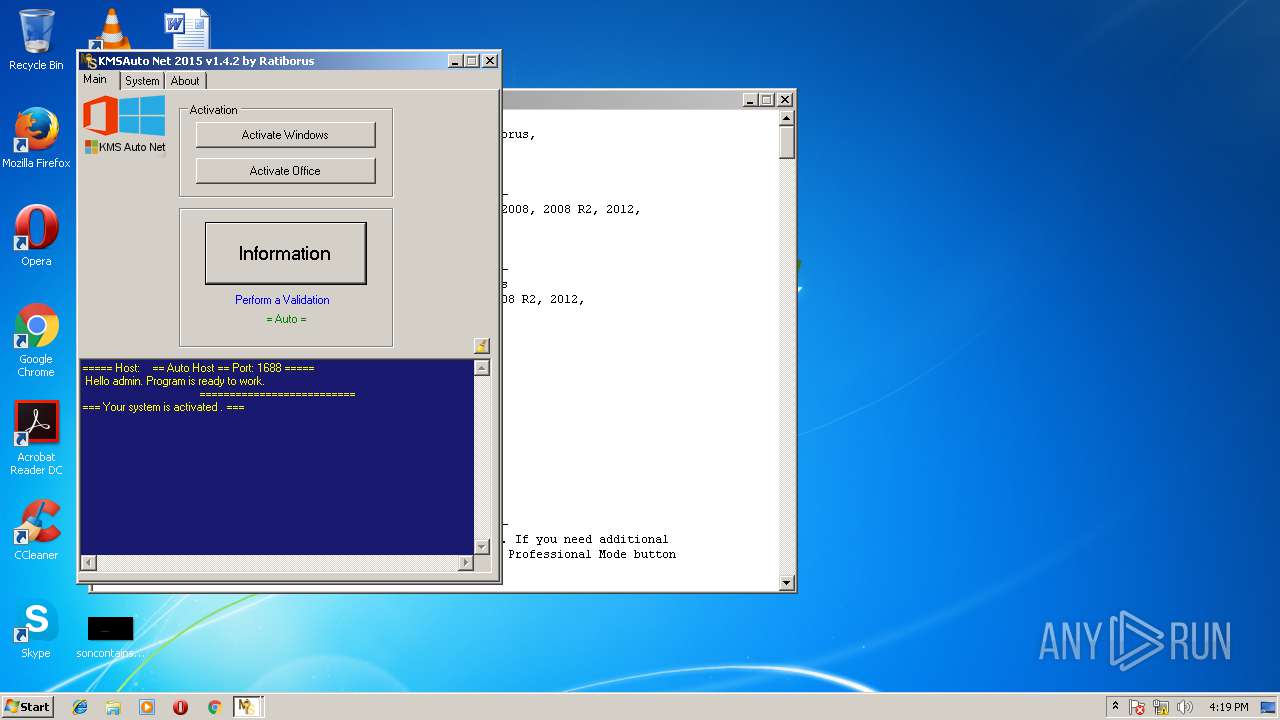
| File name: | KMSAuto Net.exe |
| Full analysis: | https://app.any.run/tasks/1d93ba94-d4c4-4496-aeae-c1fc2e55bcfb |
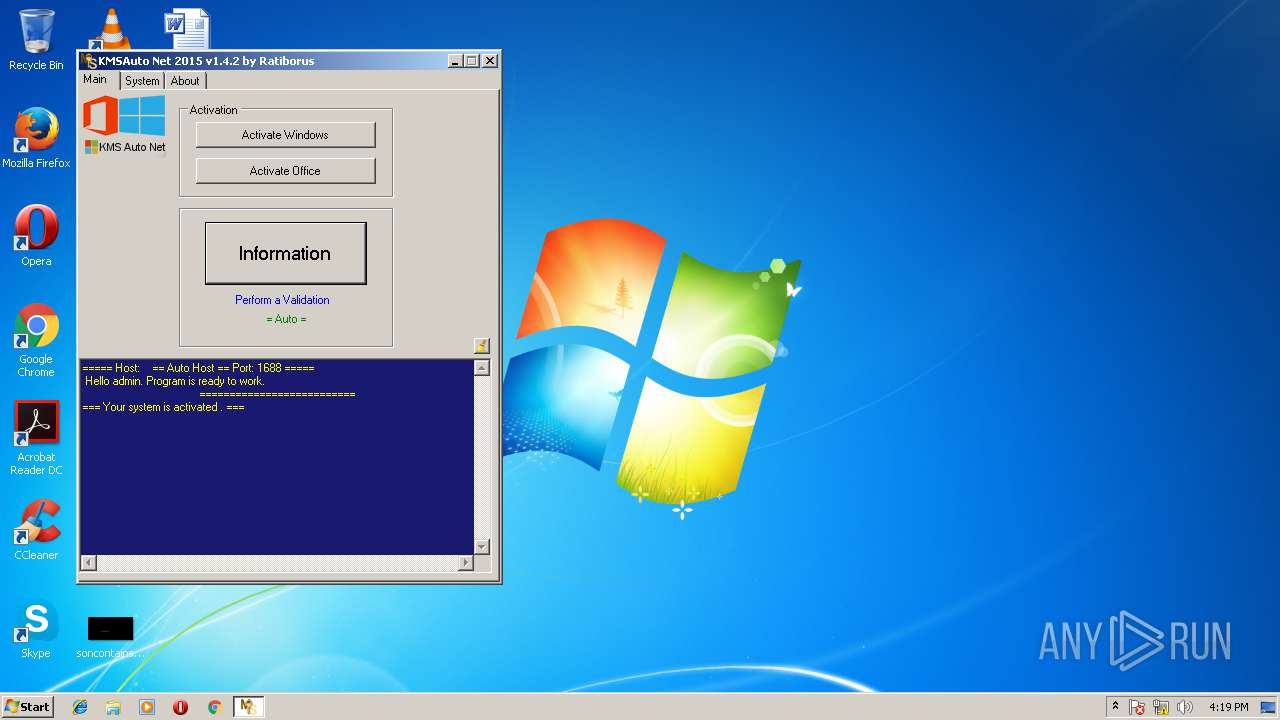
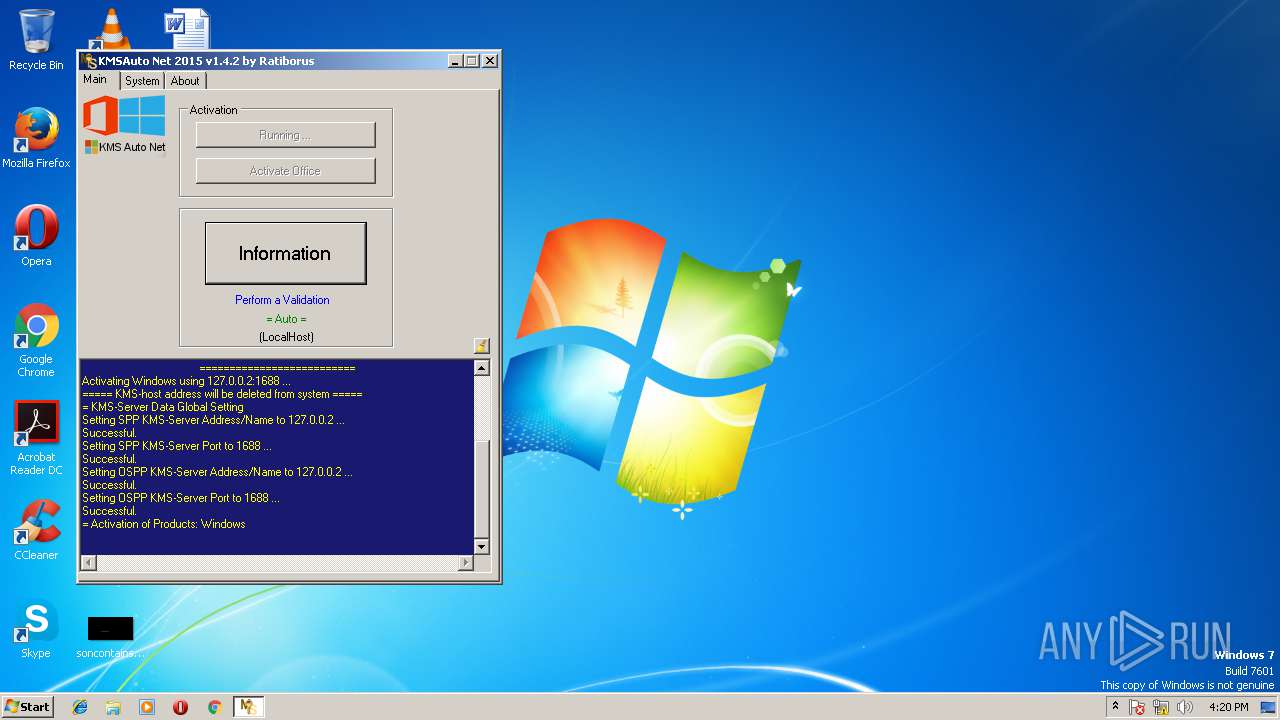
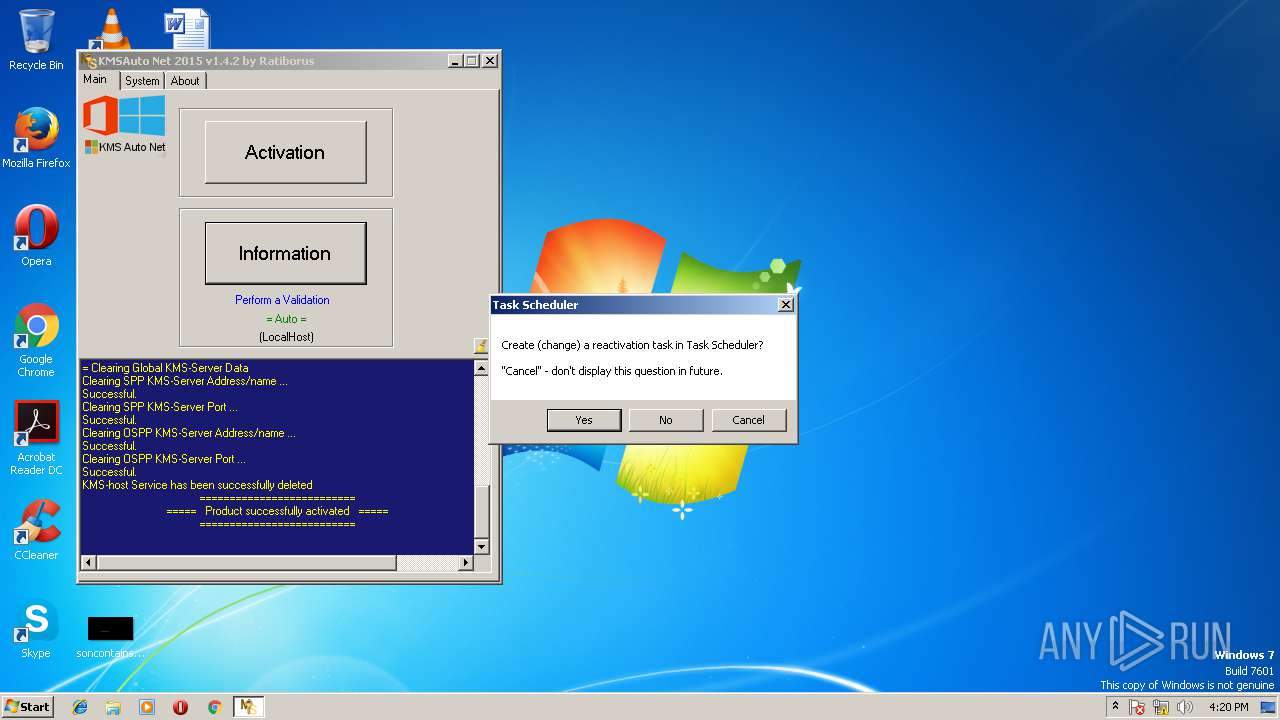
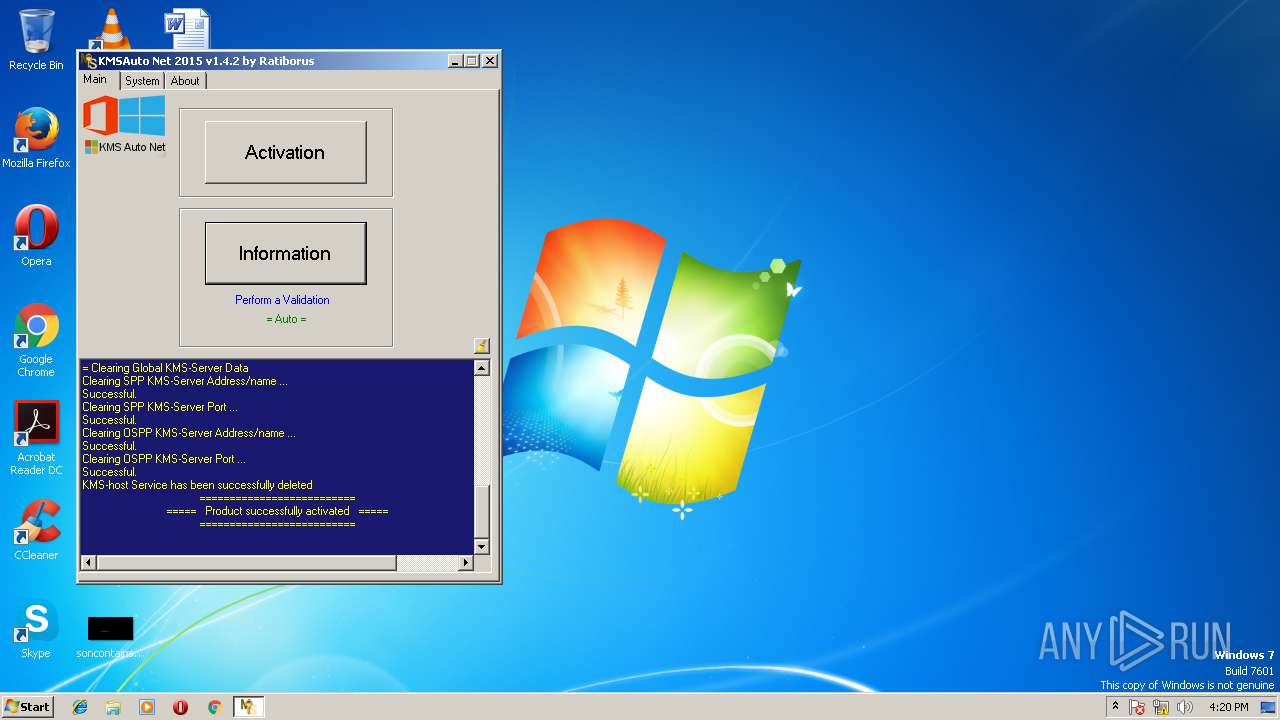
| Verdict: | Malicious activity |
| Analysis date: | March 12, 2018, 16:18:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 311F3BAA9BFA5B2364FEA8B254D15EB9 |
| SHA1: | 992585B81ACACCDB5C89361CDD1C1FD25E0C5CA1 |
| SHA256: | BEA219F0F08ED083677A0B869E658BA09785F470668EADC659DB2885FA89F3B9 |
| SSDEEP: | 196608:OwywCAfywOwe/3ywuywQywTyw3ywsywsywPbywgsywZywtywRywZywBywFywUywO:owCAqwUqwjwNw2wiwxwxwPewgxwUwQwN |
MALICIOUS
Changes settings of System certificates
- certmgr.exe (PID: 4080)
- certmgr.exe (PID: 2064)
Application was dropped or rewritten from another process
- certmgr.exe (PID: 2064)
- certmgr.exe (PID: 4080)
- wzt.dat (PID: 3024)
- bin.dat (PID: 3748)
- bin_x86.dat (PID: 3528)
- KMSSS.exe (PID: 3576)
Uses NETSH.EXE for network configuration
- KMSAuto Net.exe (PID: 3268)
SUSPICIOUS
Creates files in the program directory
- wzt.dat (PID: 3024)
- KMSAuto Net.exe (PID: 3268)
- AESDecoder.exe (PID: 2960)
- bin_x86.dat (PID: 3528)
- bin.dat (PID: 3748)
- KMSSS.exe (PID: 3576)
Starts application with an unusual extension
- cmd.exe (PID: 2524)
- cmd.exe (PID: 3364)
- cmd.exe (PID: 2384)
Reads internet explorer settings
- KMSAuto Net.exe (PID: 3268)
Starts CMD.EXE for commands execution
- KMSAuto Net.exe (PID: 3268)
- cmd.exe (PID: 2920)
Executes Visual Basic scripts
- KMSAuto Net.exe (PID: 3268)
Creates or modifies windows services
- KMSAuto Net.exe (PID: 3268)
Starts SC.EXE for service management
- KMSAuto Net.exe (PID: 3268)
Uses REG.EXE to modify Windows registry
- KMSAuto Net.exe (PID: 3268)
- cmd.exe (PID: 3980)
INFO
Loads the .NET runtime environment
- KMSAuto Net.exe (PID: 3268)
Dropped object may contain URL's
- wzt.dat (PID: 3024)
- AESDecoder.exe (PID: 2960)
- bin_x86.dat (PID: 3528)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .ocx | | | Windows ActiveX control (67.6) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (16) |
| .scr | | | Windows screen saver (7.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.8) |
| .exe | | | Win32 Executable (generic) (2.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:11:12 14:50:41+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 8968704 |
| InitializedDataSize: | 49152 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x88f916 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.4.2.0 |
| ProductVersionNumber: | 1.4.2.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | MSFree Inc. |
| FileDescription: | KMSAuto Net |
| FileVersion: | 1.4.2 |
| InternalName: | KMSAuto Net.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | KMSAuto Net.exe |
| ProductName: | KMSAuto Net |
| ProductVersion: | 1.4.2 |
| AssemblyVersion: | 1.4.2.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Nov-2015 13:50:41 |
| Comments: | - |
| CompanyName: | MSFree Inc. |
| FileDescription: | KMSAuto Net |
| FileVersion: | 1.4.2 |
| InternalName: | KMSAuto Net.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | KMSAuto Net.exe |
| ProductName: | KMSAuto Net |
| ProductVersion: | 1.4.2 |
| Assembly Version: | 1.4.2.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 12-Nov-2015 13:50:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0088D91C | 0x0088DA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.10189 |
.rsrc | 0x00890000 | 0x0000BC3C | 0x0000BE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.62503 |
.reloc | 0x0089C000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.41186 | 3073 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 5.29604 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.35071 | 1736 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.03007 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 3.79019 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 4.1678 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 4.32586 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 4.672 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 5.05539 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.96193 | 132 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
116
Monitored processes
45
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 908 | C:\Windows\System32\cmd.exe /D /c del /F /Q "AESDecoder.exe" | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2064 | certmgr.exe -add wzt.cer -n wzt -s -r localMachine ROOT | C:\ProgramData\KMSAuto\wzt\certmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ECM Certificate Manager Exit code: 0 Version: 6.3.9600.17298 (winblue.141024-1500) Modules
| |||||||||||||||
| 2128 | "C:\Windows\System32\cmd.exe" /c rd "C:\ProgramData\KMSAuto" /S /Q | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2224 | C:\Windows\System32\cmd.exe /D /c del /F /Q "bin_x86.dat" | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2320 | C:\Windows\System32\reg delete "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\0FF1CE15-A989-479D-AF46-F275C6370663" /f | C:\Windows\System32\reg.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2328 | C:\Windows\System32\cmd.exe /D /c certmgr.exe -add wzt.cer -n wzt -s -r localMachine ROOT | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2336 | reg.exe DELETE HKLM\SYSTEM\CurrentControlSet\Services\KMSEmulator /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2384 | C:\Windows\System32\cmd.exe /D /c bin_x86.dat -y -pkmsauto | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2384 | C:\Windows\System32\cmd.exe /D /c del /F /Q "test.test" | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2416 | C:\Windows\System32\cmd.exe /D /c AESDecoder.exe | C:\Windows\System32\cmd.exe | — | KMSAuto Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
347
Read events
185
Write events
158
Delete events
4
Modification events
| (PID) Process: | (4080) certmgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\TrustedPublisher\Certificates\F81F111D0E5AB58D396F7BF525577FD30FDC95AA |
| Operation: | write | Name: | Blob |
Value: 030000000100000014000000F81F111D0E5AB58D396F7BF525577FD30FDC95AA2000000001000000E8010000308201E43082014DA003020102021008A8E826950F1A9940262589FCAF0B8F300D06092A864886F70D0101040500300E310C300A06035504031303575A54301E170D3135313130383038313534395A170D3339313233313233353935395A300E310C300A06035504031303575A5430819F300D06092A864886F70D010101050003818D0030818902818100A3B38E6E8CD01F282D0872986D29BF5F0EAAD61A32C045D9B23DB1C221C3679770C401DE98695E88CAD621B319730DCABEDF4C4709EEBE8126DD567A9AB387DAB7EA13B3665166464D1B8EFFFED8BC4225515A9AAA170E595EB348A496309110C8EB66D0490F113A3C79A508058448B0398BE6F9D34F84C60E694C472C72F9B70203010001A3433041303F0603551D01043830368010E4E11038D29FC50F20A0C1914BBEFF0BA110300E310C300A06035504031303575A54821008A8E826950F1A9940262589FCAF0B8F300D06092A864886F70D01010405000381810054C251E1B9CDCA11ADE10887278347C178233BFFB85A6D692CA235D68AFE76D59F2113E7C3016AC0347E7131D590047A877083536F61D90FCB2BF95856952ABD4F63DACCFCCC840950667CC68F7513F8AE72DC7676E94B61FA169158457EA2B8531A593671E79D886743E24EDDF7141E0443E22F1F6B16B0A76D720466E4B8E8 | |||
| (PID) Process: | (2064) certmgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\F81F111D0E5AB58D396F7BF525577FD30FDC95AA |
| Operation: | write | Name: | Blob |
Value: 030000000100000014000000F81F111D0E5AB58D396F7BF525577FD30FDC95AA2000000001000000E8010000308201E43082014DA003020102021008A8E826950F1A9940262589FCAF0B8F300D06092A864886F70D0101040500300E310C300A06035504031303575A54301E170D3135313130383038313534395A170D3339313233313233353935395A300E310C300A06035504031303575A5430819F300D06092A864886F70D010101050003818D0030818902818100A3B38E6E8CD01F282D0872986D29BF5F0EAAD61A32C045D9B23DB1C221C3679770C401DE98695E88CAD621B319730DCABEDF4C4709EEBE8126DD567A9AB387DAB7EA13B3665166464D1B8EFFFED8BC4225515A9AAA170E595EB348A496309110C8EB66D0490F113A3C79A508058448B0398BE6F9D34F84C60E694C472C72F9B70203010001A3433041303F0603551D01043830368010E4E11038D29FC50F20A0C1914BBEFF0BA110300E310C300A06035504031303575A54821008A8E826950F1A9940262589FCAF0B8F300D06092A864886F70D01010405000381810054C251E1B9CDCA11ADE10887278347C178233BFFB85A6D692CA235D68AFE76D59F2113E7C3016AC0347E7131D590047A877083536F61D90FCB2BF95856952ABD4F63DACCFCCC840950667CC68F7513F8AE72DC7676E94B61FA169158457EA2B8531A593671E79D886743E24EDDF7141E0443E22F1F6B16B0A76D720466E4B8E8 | |||
| (PID) Process: | (3368) NETSTAT.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\RFC1156Agent\CurrentVersion\Parameters |
| Operation: | write | Name: | TrapPollTimeMilliSecs |
Value: 15000 | |||
| (PID) Process: | (2992) Netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2992) Netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (2992) Netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (2992) Netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (2992) Netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
| (PID) Process: | (2992) Netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-1 |
Value: IPsec Relying Party | |||
| (PID) Process: | (2992) Netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-2 |
Value: Provides IPsec based enforcement for Network Access Protection | |||
Executable files
15
Suspicious files
2
Text files
7
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3268 | KMSAuto Net.exe | C:\ProgramData\KMSAuto\wzt.dat | — | |
MD5:— | SHA256:— | |||
| 3748 | bin.dat | C:\ProgramData\KMSAuto\bin\KMSSS.exe.aes | — | |
MD5:— | SHA256:— | |||
| 3748 | bin.dat | C:\ProgramData\KMSAuto\bin\TunMirror.exe.aes | — | |
MD5:— | SHA256:— | |||
| 3748 | bin.dat | C:\ProgramData\KMSAuto\bin\TunMirror2.exe.aes | — | |
MD5:— | SHA256:— | |||
| 3748 | bin.dat | C:\ProgramData\KMSAuto\bin\AESDecoder.exe | — | |
MD5:— | SHA256:— | |||
| 3024 | wzt.dat | C:\ProgramData\KMSAuto\wzt\wzt.cer | der | |
MD5:4BF5BFBB3CAF16C6125DF0E10EE60D18 | SHA256:B3DB601B90499D6D5D7CD954CA36A907ABB6AE649B5439AB2BCA93E2E026FE9F | |||
| 3528 | bin_x86.dat | C:\ProgramData\KMSAuto\bin\driver\x86TAP1\ptun0901.cat | cat | |
MD5:B95669F68EE952F31F1F2C9D59D9A74B | SHA256:3BB447D3F5C41AA835D4510CFE9D89107B0614206E176C7E796F94A469FD51CE | |||
| 2960 | AESDecoder.exe | C:\ProgramData\KMSAuto\bin\TunMirror.exe | executable | |
MD5:FB5F055633E4F7890004972E108A07CD | SHA256:02145C3F60E704DF17919CD26CB79BD31A12B98D66B0B7FD1CF7EA894AD1F871 | |||
| 3528 | bin_x86.dat | C:\ProgramData\KMSAuto\bin\driver\x86TAP2\tapoas.cat | cat | |
MD5:F06DEB48D9149B3227C09FE4B9C3615E | SHA256:EC8A15EBD17E56F60851C557119E81A7F6EAAAB871ABFE9685926DF0C7AA6D4E | |||
| 3780 | cmd.exe | C:\Users\admin\AppData\Local\Temp\test.test | text | |
MD5:9F06243ABCB89C70E0C331C61D871FA7 | SHA256:837CCB607E312B170FAC7383D7CCFD61FA5072793F19A25E75FBACB56539B86B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report