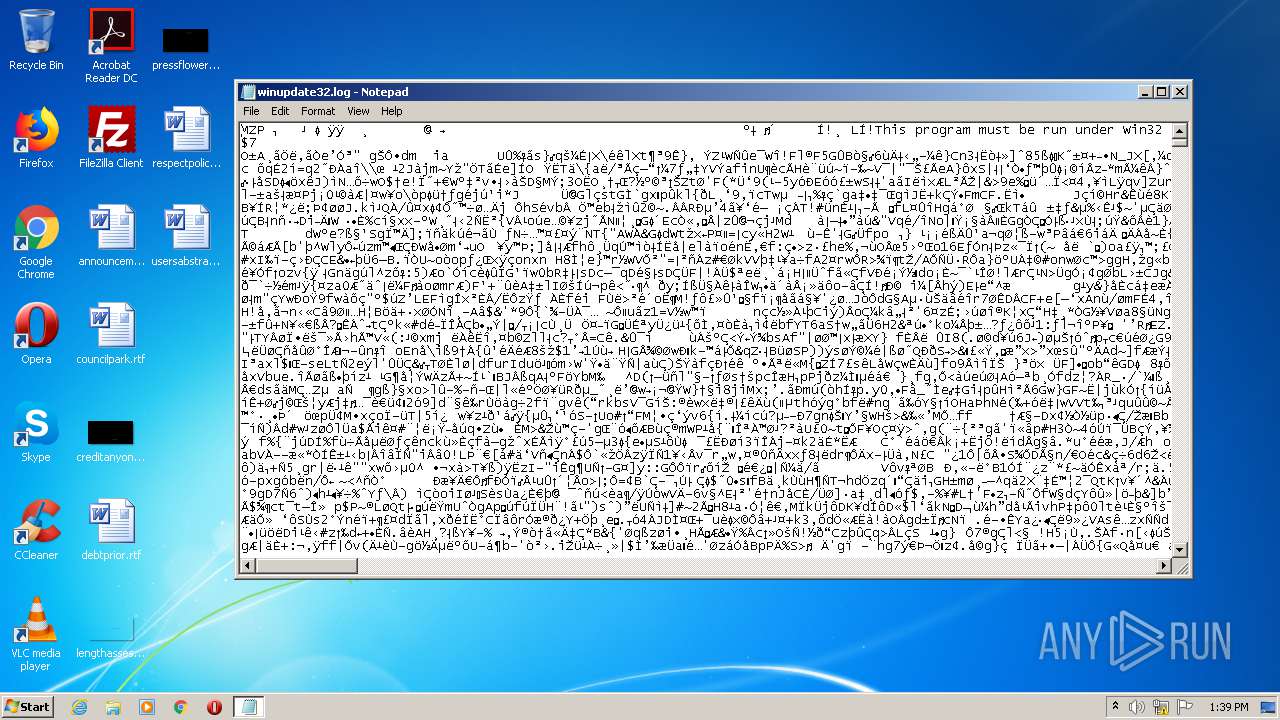
| File name: | C:\Windows\winupdate32.log |
| Full analysis: | https://app.any.run/tasks/6a2b946d-1444-4c12-a4a8-5bf58899f22a |
| Verdict: | Malicious activity |
| Analysis date: | August 10, 2020, 12:38:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | 9310708F07B27AF4CA85EA961D780793 |
| SHA1: | 9522ED207E7BEDC1537D81DAEA50DE42DED9063A |
| SHA256: | BE9C01236581A499C76567F6D72769F6B7C7D4ABBEDFB8D43D510A11331BF8FB |
| SSDEEP: | 12288:0q+kSVmWZ5f7z7mZyjXrwN/E7BdPgGH8G6qNoP4qN:0F/5jz7g+7kE7fPJ8lqNoPf |
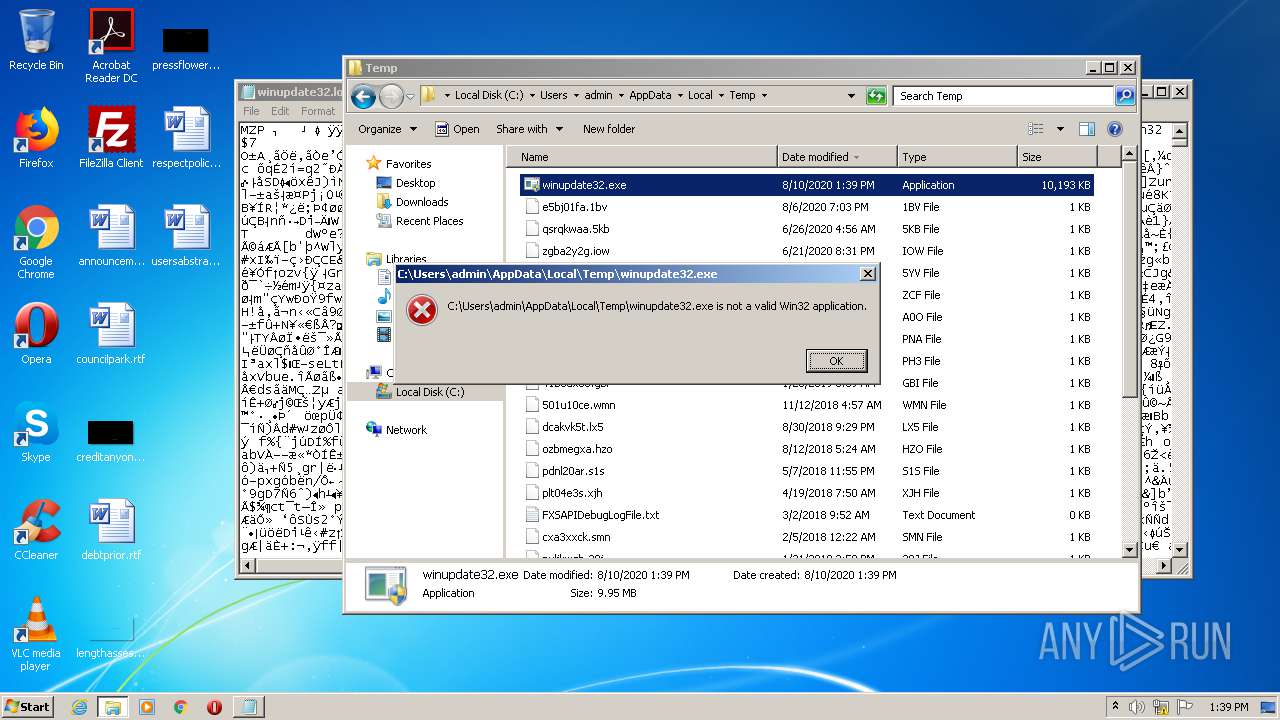
MALICIOUS
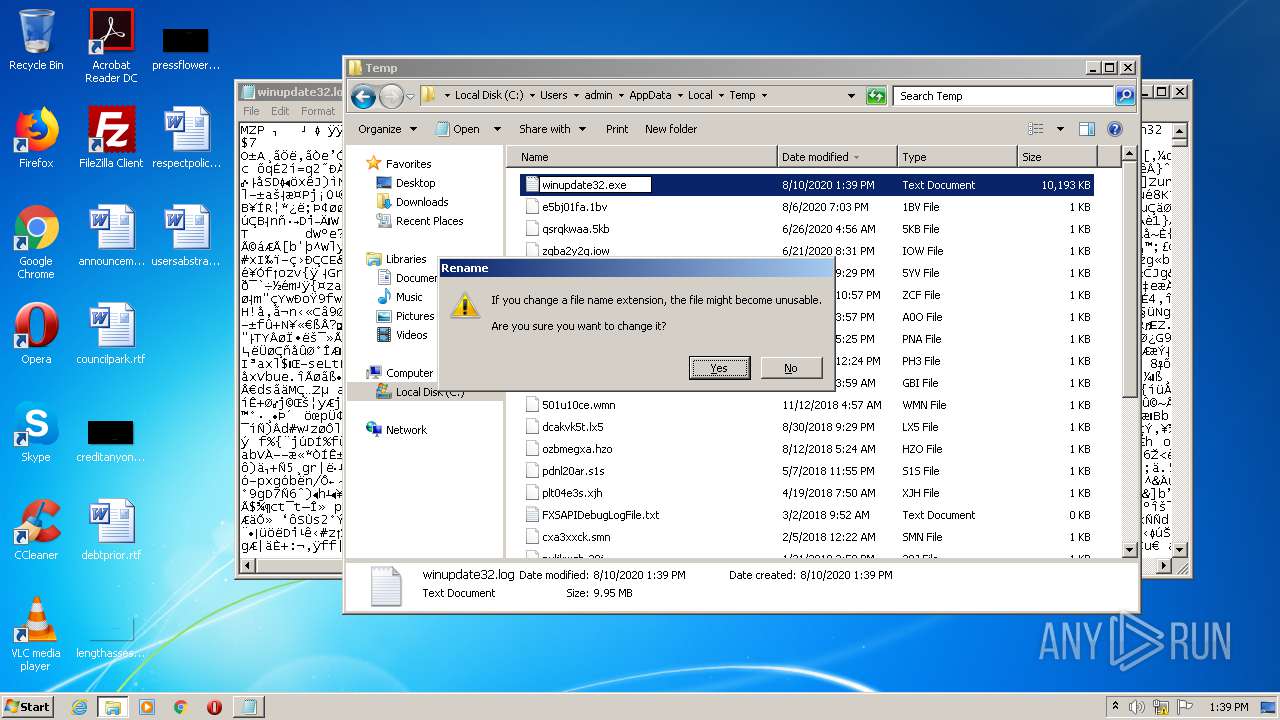
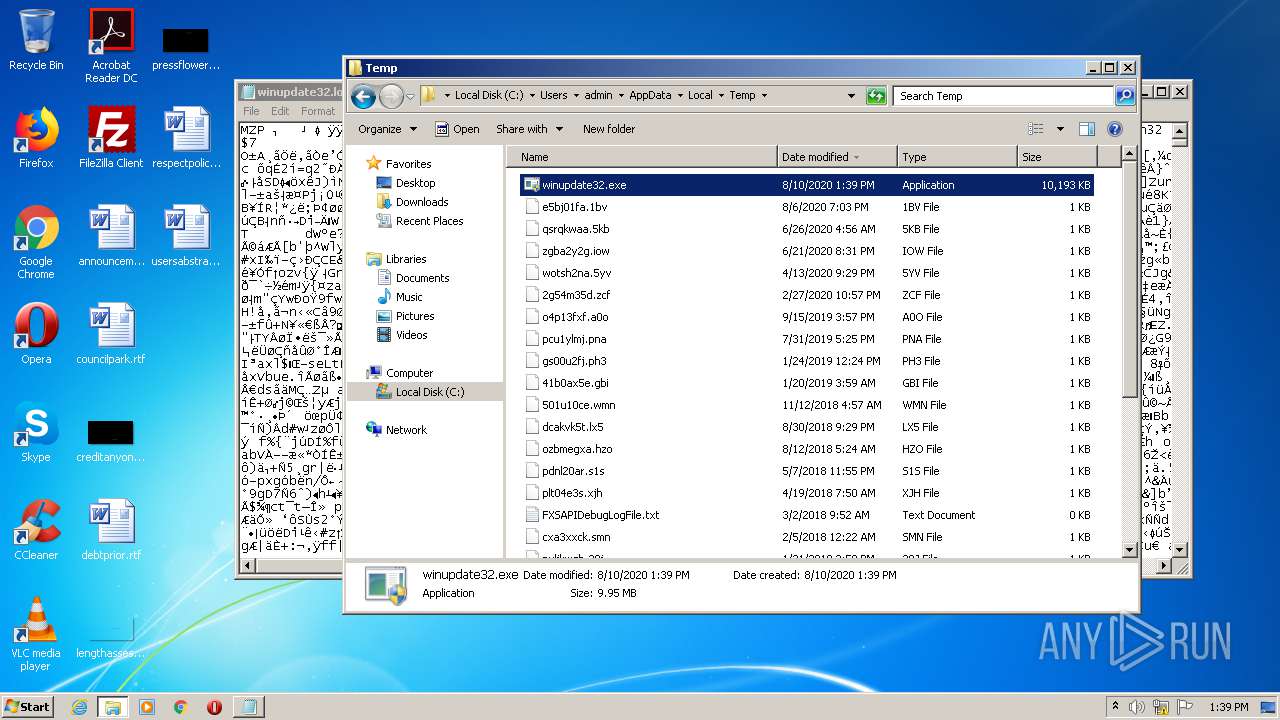
Loads dropped or rewritten executable
- explorer.exe (PID: 352)
SUSPICIOUS
Executable content was dropped or overwritten
- explorer.exe (PID: 352)
INFO
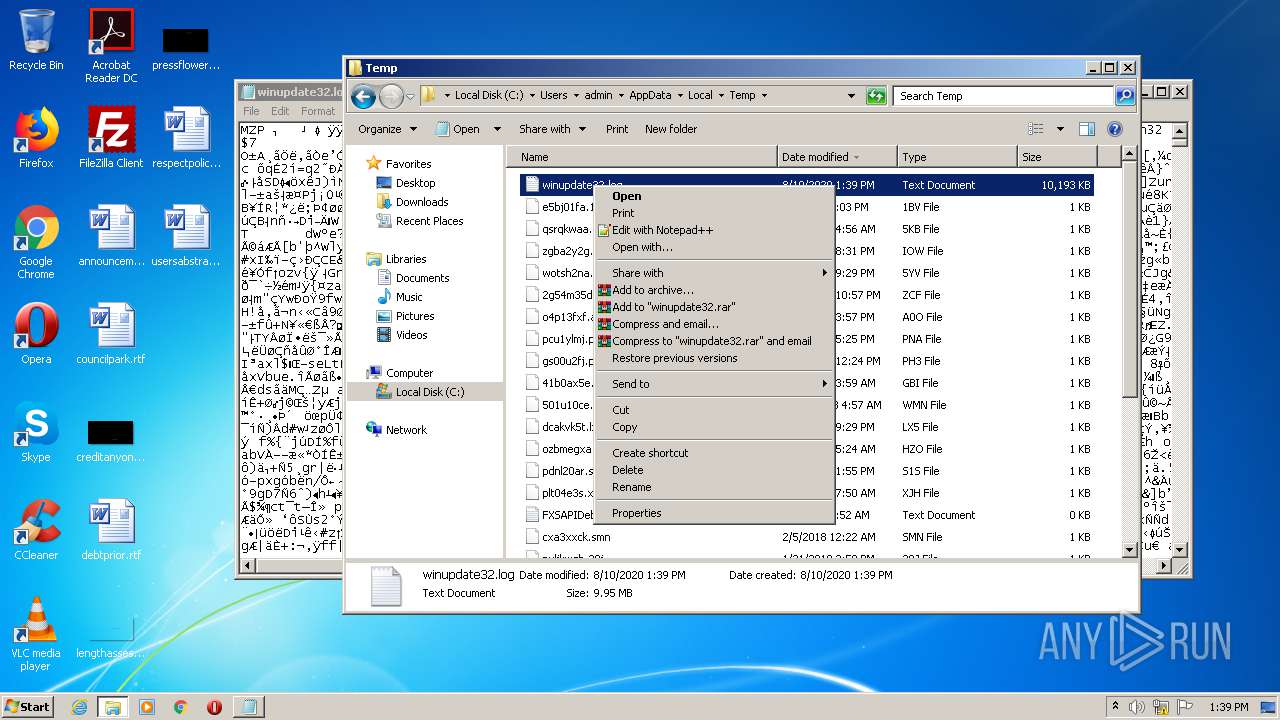
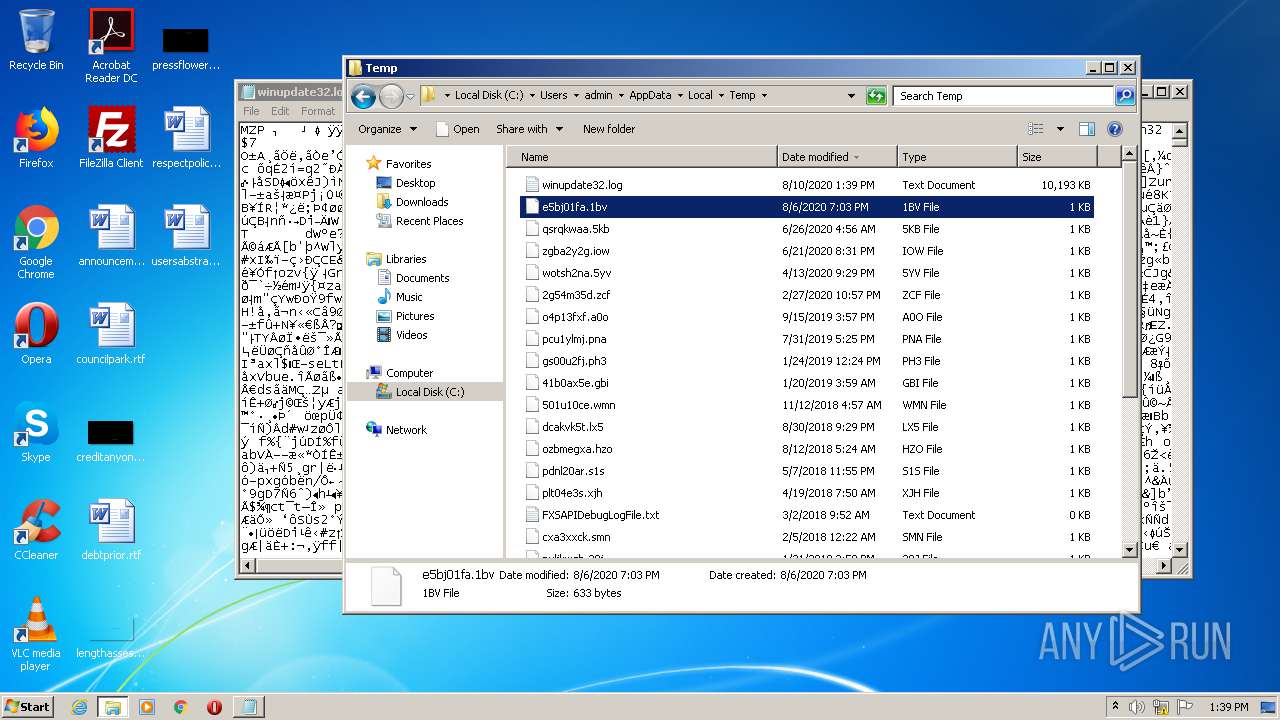
Manual execution by user
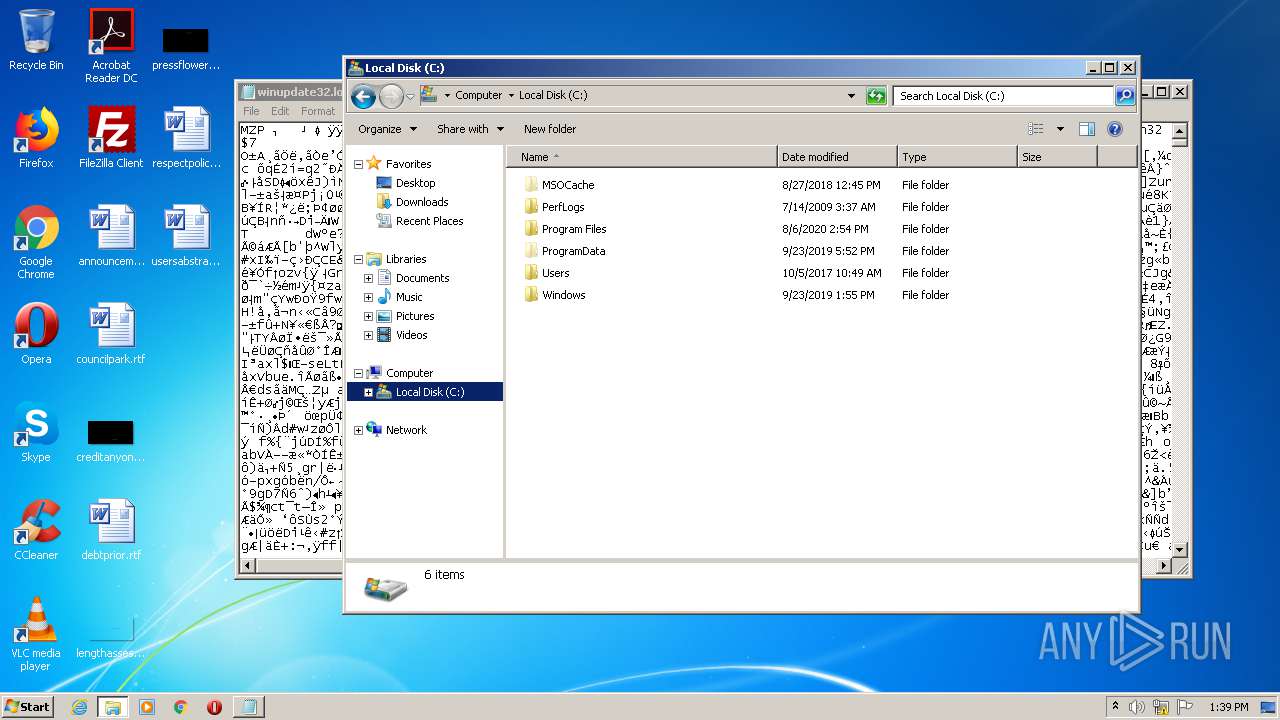
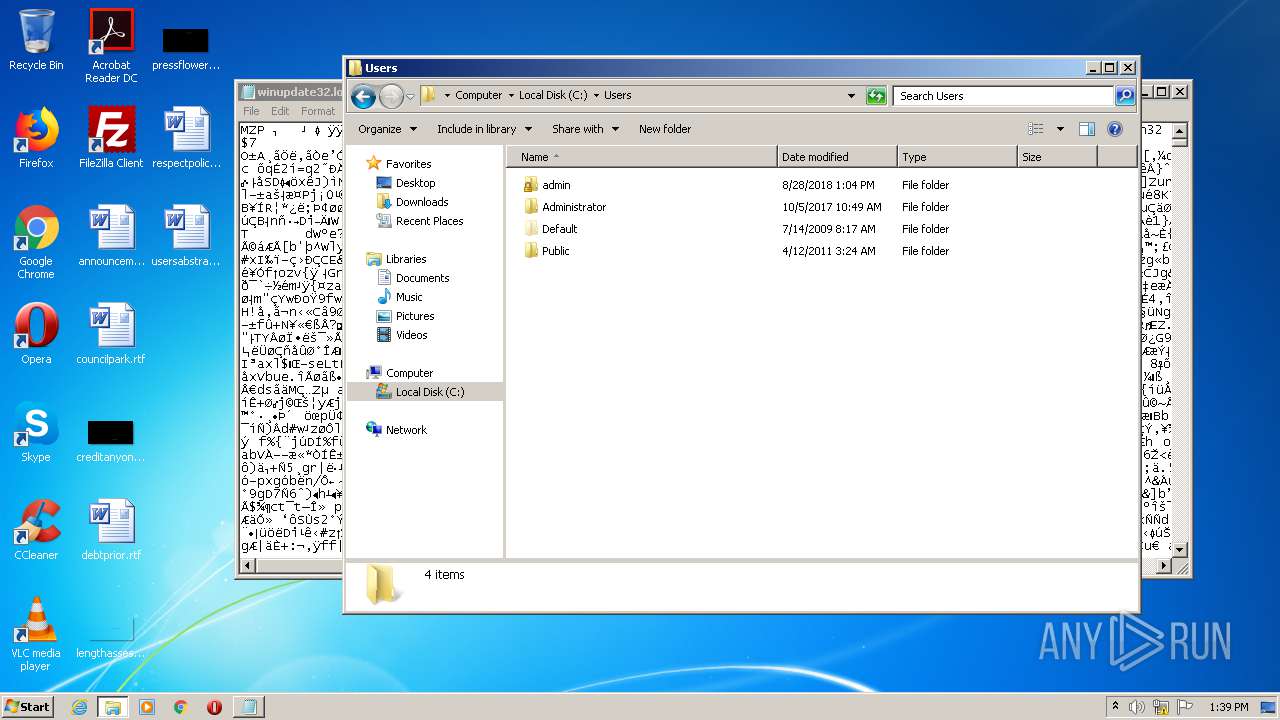
- explorer.exe (PID: 2876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:05:31 04:09:05+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 155136 |
| InitializedDataSize: | 334848 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xcc42a |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 31-May-2020 02:09:05 |
DOS Header
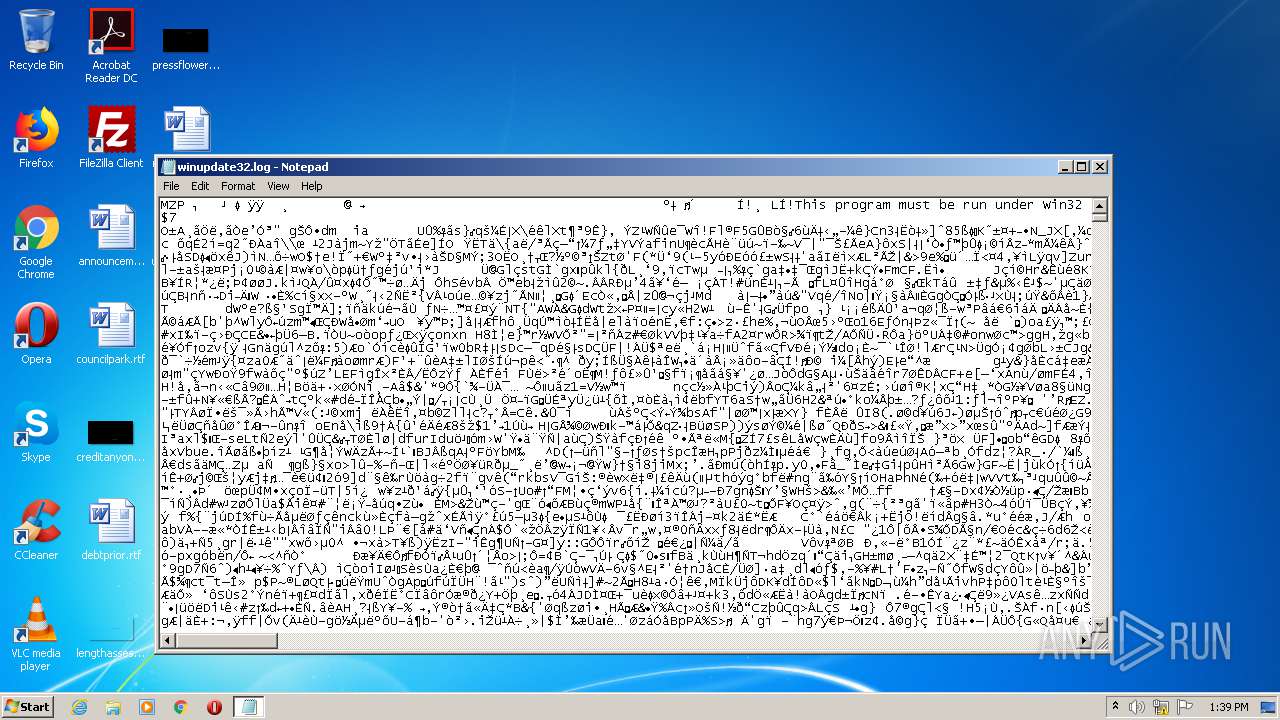
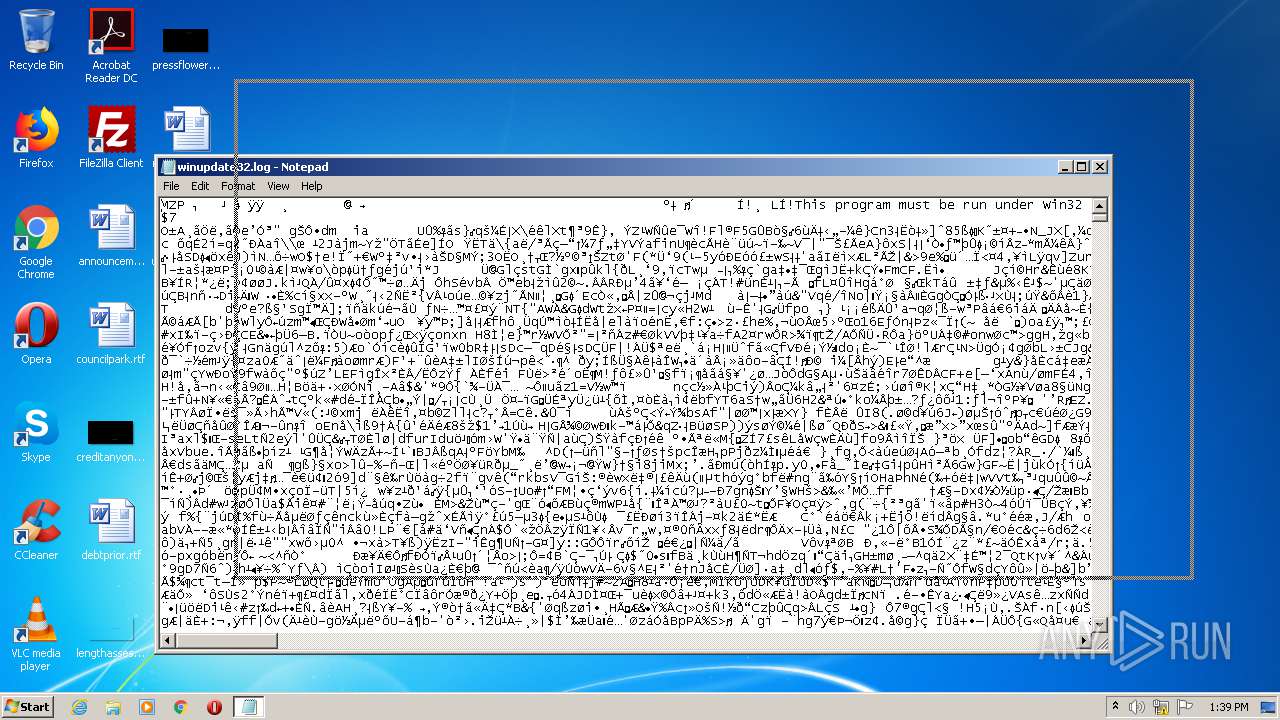
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 11 |
| Time date stamp: | 31-May-2020 02:09:05 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00025764 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0 |
.itext | 0x00027000 | 0x00000408 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0 |
.data | 0x00028000 | 0x0004CF9C | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.bss | 0x00075000 | 0x00004368 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0007A000 | 0x000010E4 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.didata | 0x0007C000 | 0x00000098 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.edata | 0x0007D000 | 0x0000004C | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0 |
.rdata | 0x0007E000 | 0x00000044 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0 |
.vmp0 | 0x0007F000 | 0x0001A3A9 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.vmp1 | 0x0009A000 | 0x0006A1DE | 0x0006A200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.9197 |
Imports
advapi32.dll |
kernel32.dll |
ntdll.dll |
oleaut32.dll |
user32.dll |
version.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
ServiceMain | 1 | 0x0002424C |
Total processes
41
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
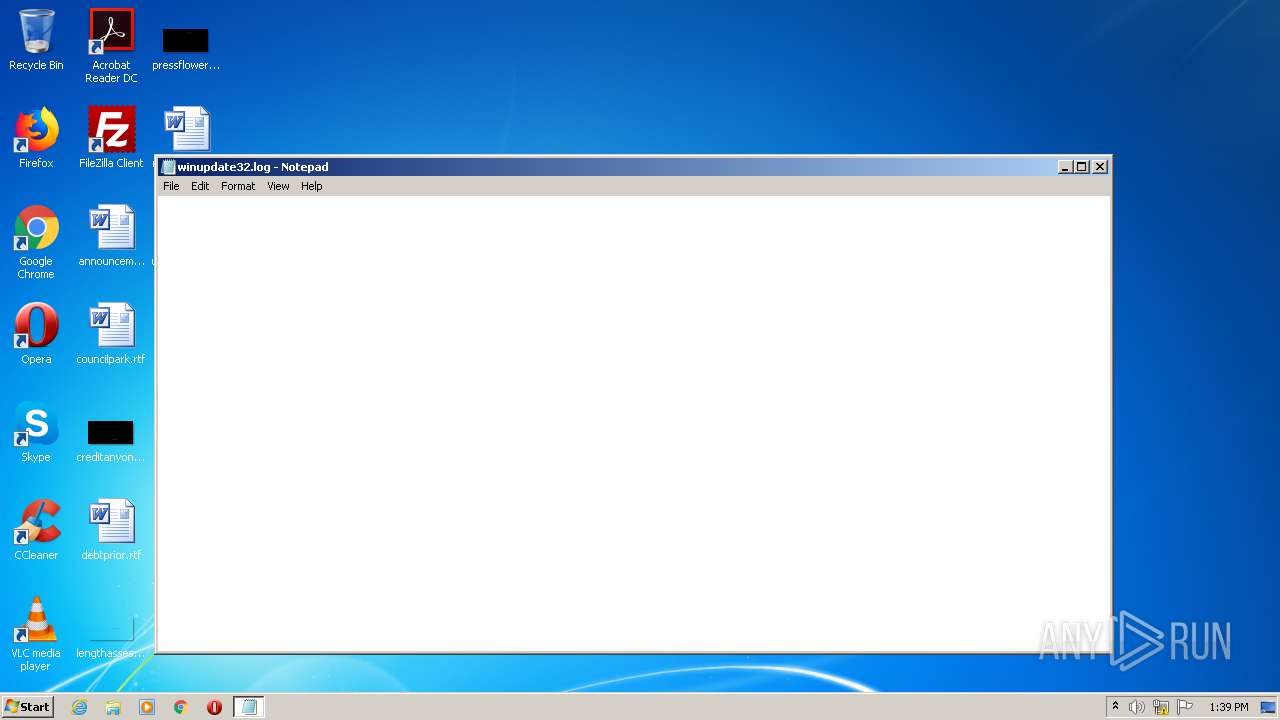
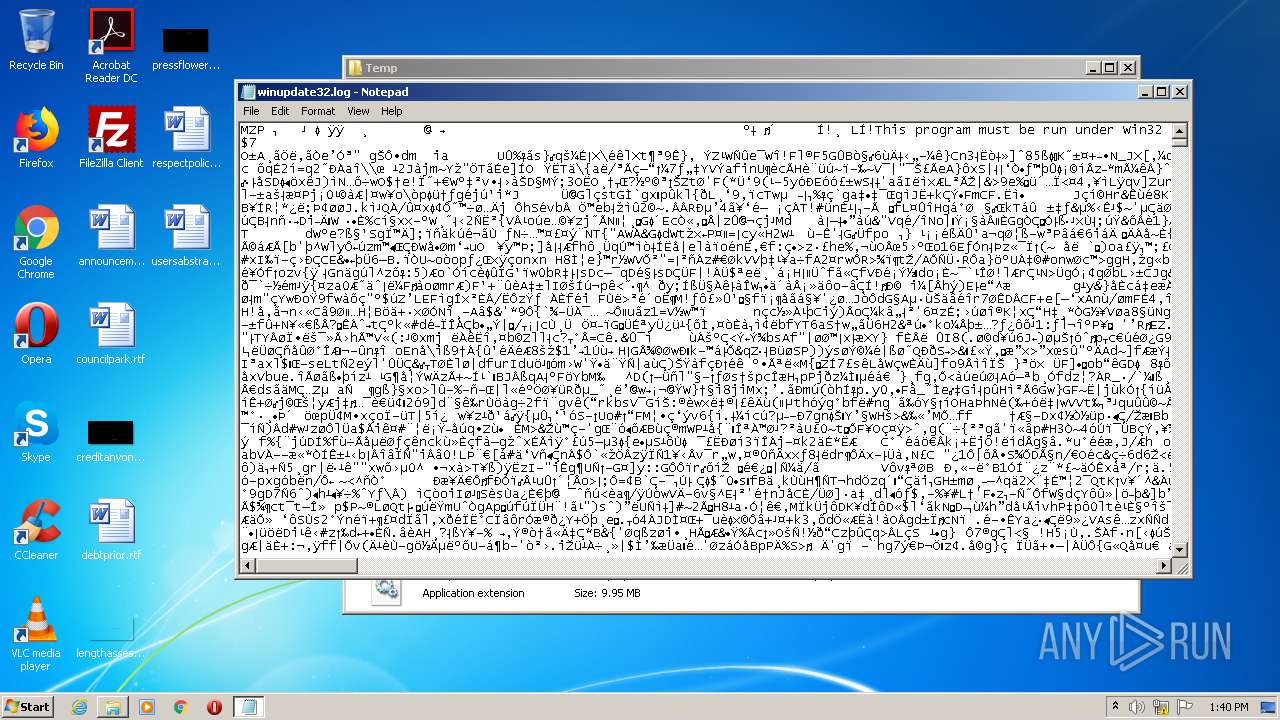
| 2656 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\winupdate32.log | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2876 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 236
Read events
931
Write events
305
Delete events
0
Modification events
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {Q65231O0-O2S1-4857-N4PR-N8R7P6RN7Q27}\abgrcnq.rkr |
Value: 00000000000000000100000000000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000004A000000720000007C7532000C00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF7059F6740000000000000000B4E91D028575F274000400000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF18323B001C333B0078D93A00E4E91D022FB19C7580B0CF7524F71D02381E9D7514639D75A017380018EA1D02B87A390070000000AEE04A38F8E91D02BE6A9D75A017380018EA1D020000000024EC1D026F629D75A017380018EA1D0200000400000000807C629D75A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630068005C007500730011000000483D3800403D38006E00650064005C0030EB000082E34A38E0EA1D0282919D7530EB1D02E4EA1D0227959D75000000009C01D8020CEB1D02CD949D759C01D802B8EB1D0210FDD702E1949D750000000010FDD702B8EB1D0214EB1D020C00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF7059F6740000000000000000B4E91D028575F274000400000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF18323B001C333B0078D93A00E4E91D022FB19C7580B0CF7524F71D02381E9D7514639D75A017380018EA1D02B87A390070000000AEE04A38F8E91D02BE6A9D75A017380018EA1D020000000024EC1D026F629D75A017380018EA1D0200000400000000807C629D75A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630068005C007500730011000000483D3800403D38006E00650064005C0030EB000082E34A38E0EA1D0282919D7530EB1D02E4EA1D0227959D75000000009C01D8020CEB1D02CD949D759C01D802B8EB1D0210FDD702E1949D750000000010FDD702B8EB1D0214EB1D020C00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF7059F6740000000000000000B4E91D028575F274000400000000000018EA1D02FFFFFFFF80D93A00FFFFFFFF18323B001C333B0078D93A00E4E91D022FB19C7580B0CF7524F71D02381E9D7514639D75A017380018EA1D02B87A390070000000AEE04A38F8E91D02BE6A9D75A017380018EA1D020000000024EC1D026F629D75A017380018EA1D0200000400000000807C629D75A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E0067005C006D006900630072006F0073006F00660074005C0069006E007400650072006E006500740020006500780070006C006F007200650072005C0071007500690063006B0020006C00610075006E00630068005C007500730011000000483D3800403D38006E00650064005C0030EB000082E34A38E0EA1D0282919D7530EB1D02E4EA1D0227959D75000000009C01D8020CEB1D02CD949D759C01D802B8EB1D0210FDD702E1949D750000000010FDD702B8EB1D0214EB1D02 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {S38OS404-1Q43-42S2-9305-67QR0O28SP23}\rkcybere.rkr |
Value: 000000000D00000025000000D79E1300000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF605AE541136FD60100000000 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000004B000000720000007C7532000D00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000B22BE903B02BE903B8F9B87551020000600000000000000002000000000000000000000000D46505399C4A777059D40300030000000000000D000000705CD403AF0200007059D40330D465054319B9751F5CD403D845D7035E0000007059D403782EE903AF020000B8F9B875D023E903D023E90340D465056419B975782EE903D845D703D8D86505BF43B975782EE9030000000000000000FFFFFFFF000000000000000000000000D845D703F045D703D845D7031A46D7030000000000000000000000000000B975781DE9037045D70324D96505BF43B975781DE9030000000000000000FFFFFFFF0000000000000000000000007045D7038845D7037045D703B245D70363010000061FB702E4D4650533AB8377063718090B0C00001027000009000000AA56020018D56505F8AA8377AA560200061FB70238D56505B874D403B8D5650500000000A4010000CE0100000F000000270000000E00000040D56505FDE19E75E407000038D56505E40708000A000C0027000F00CE010F00605AE541136FD60168D5650557C1BC7554D56505B8D5650562C1BC75E407080001000A000D00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000B22BE903B02BE903B8F9B87551020000600000000000000002000000000000000000000000D46505399C4A777059D40300030000000000000D000000705CD403AF0200007059D40330D465054319B9751F5CD403D845D7035E0000007059D403782EE903AF020000B8F9B875D023E903D023E90340D465056419B975782EE903D845D703D8D86505BF43B975782EE9030000000000000000FFFFFFFF000000000000000000000000D845D703F045D703D845D7031A46D7030000000000000000000000000000B975781DE9037045D70324D96505BF43B975781DE9030000000000000000FFFFFFFF0000000000000000000000007045D7038845D7037045D703B245D70363010000061FB702E4D4650533AB8377063718090B0C00001027000009000000AA56020018D56505F8AA8377AA560200061FB70238D56505B874D403B8D5650500000000A4010000CE0100000F000000270000000E00000040D56505FDE19E75E407000038D56505E40708000A000C0027000F00CE010F00605AE541136FD60168D5650557C1BC7554D56505B8D5650562C1BC75E407080001000A000D00000025000000D79E13007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000B22BE903B02BE903B8F9B87551020000600000000000000002000000000000000000000000D46505399C4A777059D40300030000000000000D000000705CD403AF0200007059D40330D465054319B9751F5CD403D845D7035E0000007059D403782EE903AF020000B8F9B875D023E903D023E90340D465056419B975782EE903D845D703D8D86505BF43B975782EE9030000000000000000FFFFFFFF000000000000000000000000D845D703F045D703D845D7031A46D7030000000000000000000000000000B975781DE9037045D70324D96505BF43B975781DE9030000000000000000FFFFFFFF0000000000000000000000007045D7038845D7037045D703B245D70363010000061FB702E4D4650533AB8377063718090B0C00001027000009000000AA56020018D56505F8AA8377AA560200061FB70238D56505B874D403B8D5650500000000A4010000CE0100000F000000270000000E00000040D56505FDE19E75E407000038D56505E40708000A000C0027000F00CE010F00605AE541136FD60168D5650557C1BC7554D56505B8D5650562C1BC75E407080001000A00 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | {9R3995NO-1S9P-4S13-O827-48O24O6P7174}\GnfxOne\Jvaqbjf Rkcybere.yax |
Value: 000000000D000000000000000C000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF605AE541136FD60100000000 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000002600000000000000250000000D000000000000000C0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000000000000000D46505399C4A777059D40300030000000000000D000000705CD403AF0200007059D40330D465054319B9751F5CD403D845D7035E0000007059D403782EE903AF020000B8F9B875D023E903D023E90340D465056419B975782EE903D845D703D8D86505BF43B975782EE9030000000000000000FFFFFFFF000000000000000000000000D845D703F045D703D845D7031A46D7030000000000000000000000000000B975781DE9037045D70324D96505BF43B975781DE9030000000000000000FFFFFFFF0000000000000000000000007045D7038845D7037045D703B245D70363010000061FB702E4D4650533AB8377063718090B0C00001027000009000000AA56020018D56505F8AA8377AA560200061FB70238D56505A07FD403B8D5650500000000A4010000CE0100000F000000270000000E00000040D56505FDE19E75E407000038D56505E40708000A000C0027000F00CE010F00605AE541136FD60168D5650557C1BC7554D56505B8D5650562C1BC75E407080001000A000D000000000000000C0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000000000000000D46505399C4A777059D40300030000000000000D000000705CD403AF0200007059D40330D465054319B9751F5CD403D845D7035E0000007059D403782EE903AF020000B8F9B875D023E903D023E90340D465056419B975782EE903D845D703D8D86505BF43B975782EE9030000000000000000FFFFFFFF000000000000000000000000D845D703F045D703D845D7031A46D7030000000000000000000000000000B975781DE9037045D70324D96505BF43B975781DE9030000000000000000FFFFFFFF0000000000000000000000007045D7038845D7037045D703B245D70363010000061FB702E4D4650533AB8377063718090B0C00001027000009000000AA56020018D56505F8AA8377AA560200061FB70238D56505A07FD403B8D5650500000000A4010000CE0100000F000000270000000E00000040D56505FDE19E75E407000038D56505E40708000A000C0027000F00CE010F00605AE541136FD60168D5650557C1BC7554D56505B8D5650562C1BC75E407080001000A000D000000000000000C0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000000000000000D46505399C4A777059D40300030000000000000D000000705CD403AF0200007059D40330D465054319B9751F5CD403D845D7035E0000007059D403782EE903AF020000B8F9B875D023E903D023E90340D465056419B975782EE903D845D703D8D86505BF43B975782EE9030000000000000000FFFFFFFF000000000000000000000000D845D703F045D703D845D7031A46D7030000000000000000000000000000B975781DE9037045D70324D96505BF43B975781DE9030000000000000000FFFFFFFF0000000000000000000000007045D7038845D7037045D703B245D70363010000061FB702E4D4650533AB8377063718090B0C00001027000009000000AA56020018D56505F8AA8377AA560200061FB70238D56505A07FD403B8D5650500000000A4010000CE0100000F000000270000000E00000040D56505FDE19E75E407000038D56505E40708000A000C0027000F00CE010F00605AE541136FD60168D5650557C1BC7554D56505B8D5650562C1BC75E407080001000A00 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | {9R3995NO-1S9P-4S13-O827-48O24O6P7174}\GnfxOne\Jvaqbjf Rkcybere.yax |
Value: 000000000D000000000000000D000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF605AE541136FD60100000000 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000002600000000000000260000000D000000000000000D0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B0000000000000000D46505399C4A777059D40300030000000000000D000000705CD403AF0200007059D40330D465054319B9751F5CD403D845D7035E0000007059D403782EE903AF020000B8F9B875D023E903D023E90340D465056419B975782EE903D845D703D8D86505BF43B975782EE9030000000000000000FFFFFFFF000000000000000000000000D845D703F045D703D845D7031A46D7030000000000000000000000000000B975781DE9037045D70324D96505BF43B975781DE9030000000000000000FFFFFFFF0000000000000000000000007045D7038845D7037045D703B245D70363010000061FB702E4D4650533AB8377063718090B0C00001027000009000000AA56020018D56505F8AA8377AA560200061FB70238D56505A07FD403B8D5650500000000A401000078D50000CBBBA11C28D565058291B97578D565052CD565052795B975000000002C84D40354D56505CD94B9752C84D40300D66505A07FD403E194B97500000000A07FD40300D665055CD565050D000000000000000D0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B0000000000000000D46505399C4A777059D40300030000000000000D000000705CD403AF0200007059D40330D465054319B9751F5CD403D845D7035E0000007059D403782EE903AF020000B8F9B875D023E903D023E90340D465056419B975782EE903D845D703D8D86505BF43B975782EE9030000000000000000FFFFFFFF000000000000000000000000D845D703F045D703D845D7031A46D7030000000000000000000000000000B975781DE9037045D70324D96505BF43B975781DE9030000000000000000FFFFFFFF0000000000000000000000007045D7038845D7037045D703B245D70363010000061FB702E4D4650533AB8377063718090B0C00001027000009000000AA56020018D56505F8AA8377AA560200061FB70238D56505A07FD403B8D5650500000000A401000078D50000CBBBA11C28D565058291B97578D565052CD565052795B975000000002C84D40354D56505CD94B9752C84D40300D66505A07FD403E194B97500000000A07FD40300D665055CD565050D000000000000000D0000007B00390045003300390039003500410042002D0031004600390043002D0034004600310033002D0042003800320037002D003400380042003200340042003600430037003100370034007D005C005400610073006B004200610072005C00570069006E0064006F007700730020004500780070006C006F007200650072002E006C006E006B0000006C006E006B0000000000000000D46505399C4A777059D40300030000000000000D000000705CD403AF0200007059D40330D465054319B9751F5CD403D845D7035E0000007059D403782EE903AF020000B8F9B875D023E903D023E90340D465056419B975782EE903D845D703D8D86505BF43B975782EE9030000000000000000FFFFFFFF000000000000000000000000D845D703F045D703D845D7031A46D7030000000000000000000000000000B975781DE9037045D70324D96505BF43B975781DE9030000000000000000FFFFFFFF0000000000000000000000007045D7038845D7037045D703B245D70363010000061FB702E4D4650533AB8377063718090B0C00001027000009000000AA56020018D56505F8AA8377AA560200061FB70238D56505A07FD403B8D5650500000000A401000078D50000CBBBA11C28D565058291B97578D565052CD565052795B975000000002C84D40354D56505CD94B9752C84D40300D66505A07FD403E194B97500000000A07FD40300D665055CD56505 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 020000000B0000000100000000000000070000000A000000090000000800000006000000030000000500000004000000FFFFFFFF | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
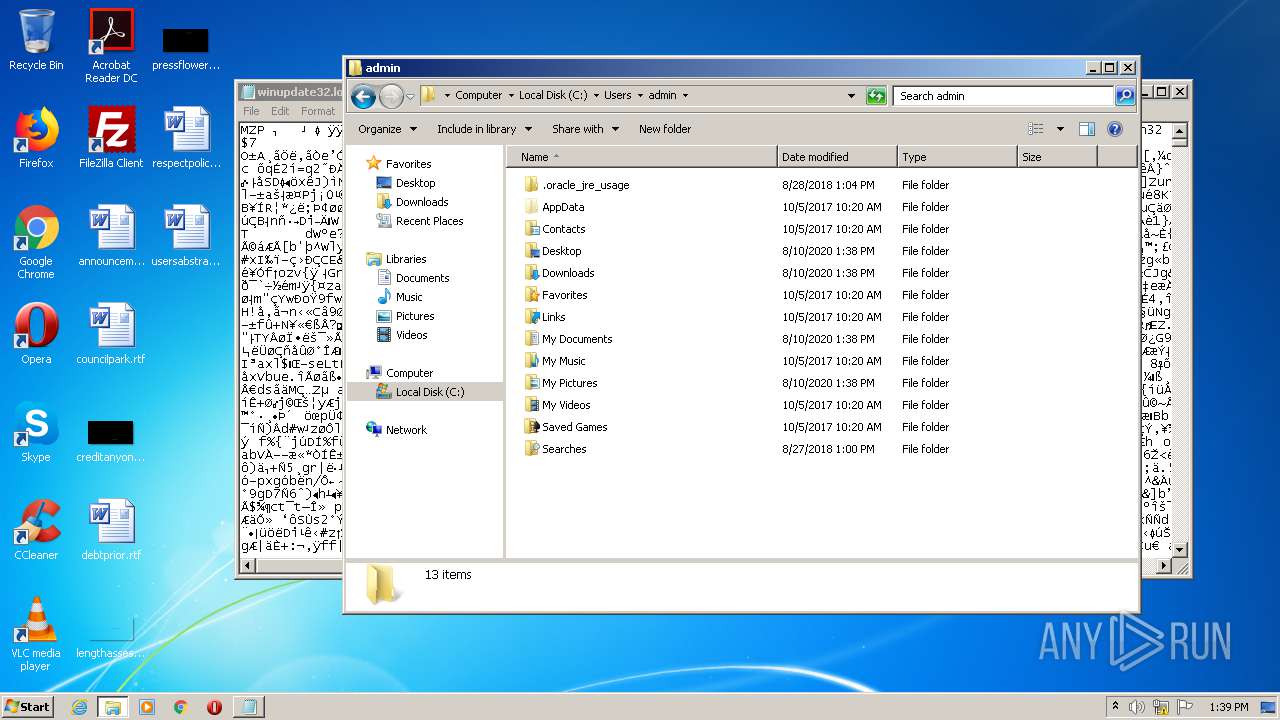
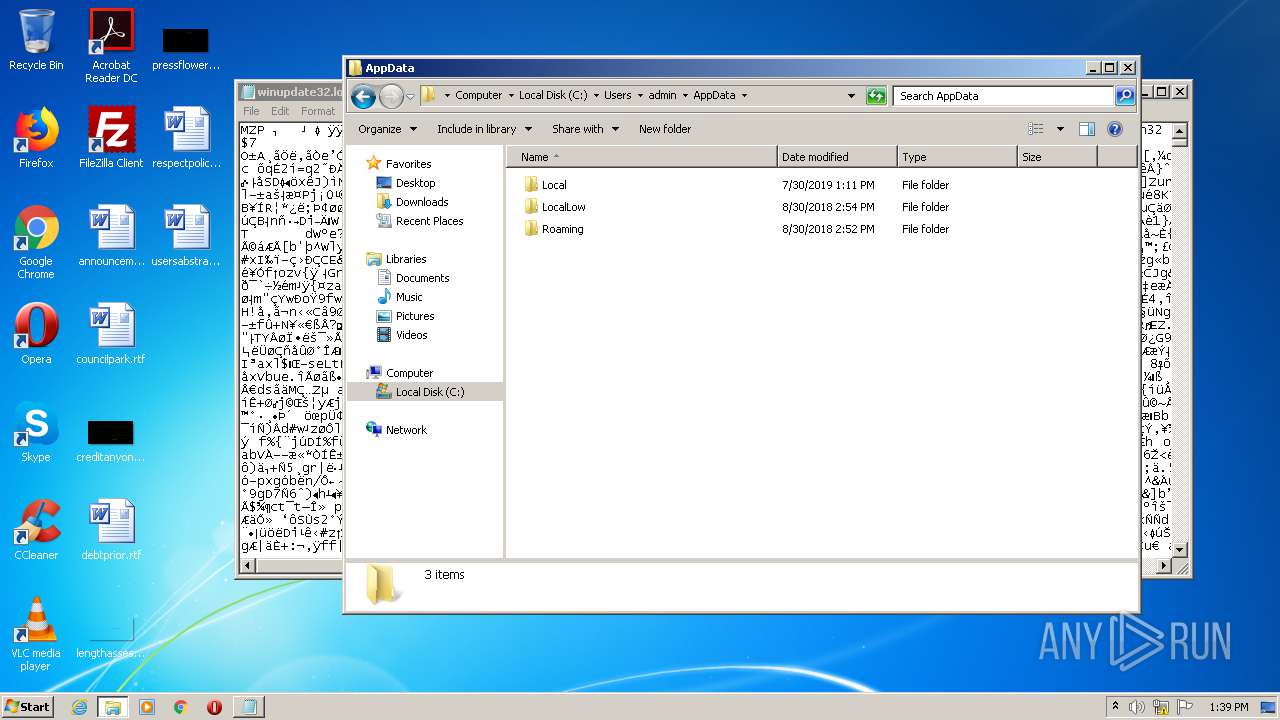
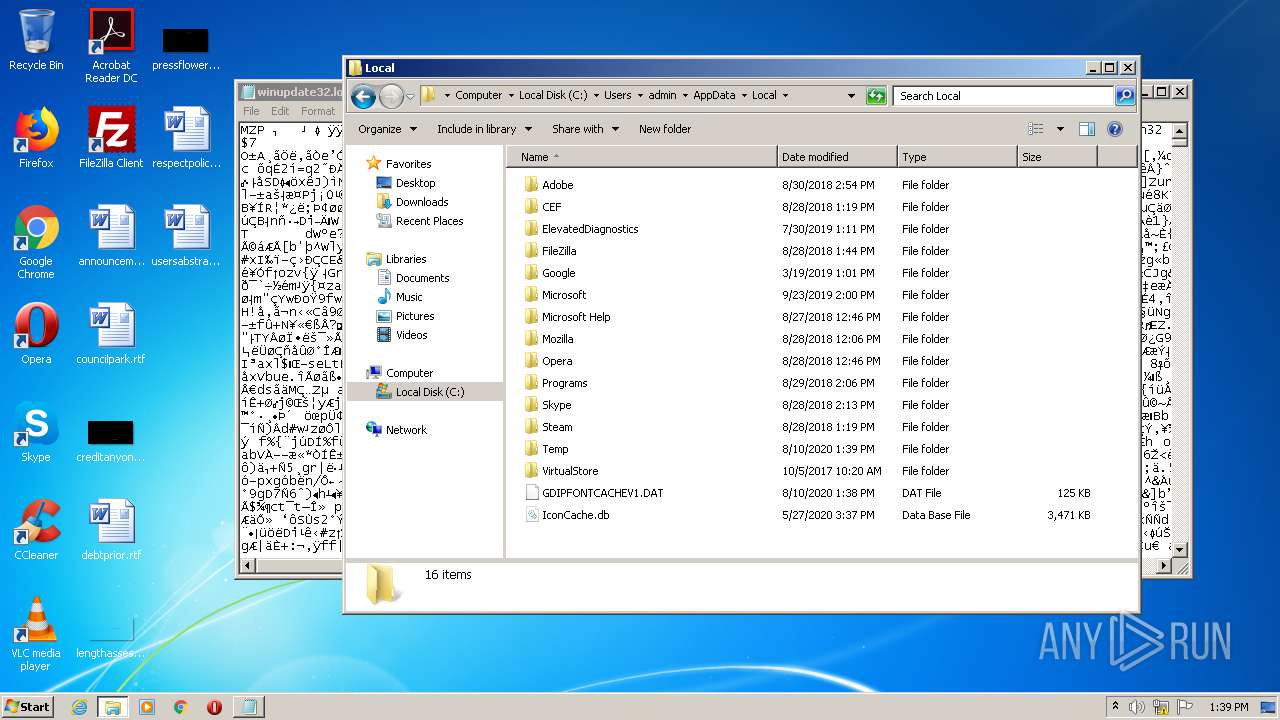
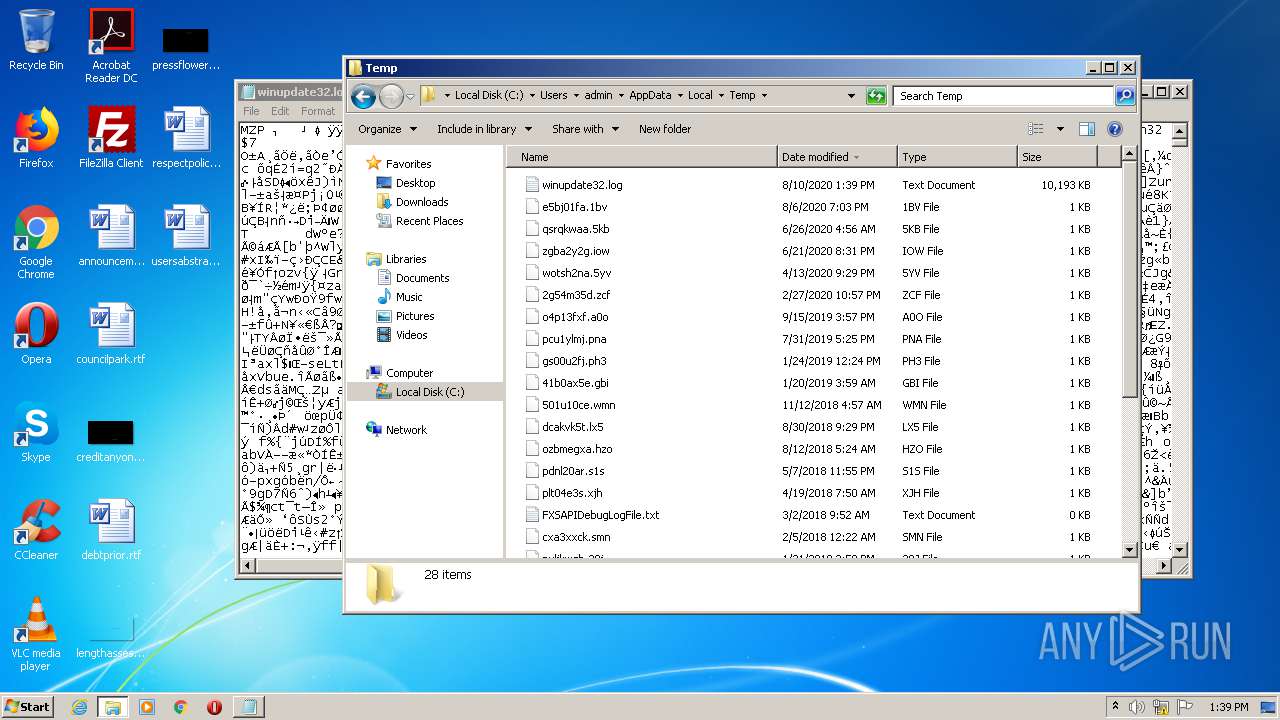
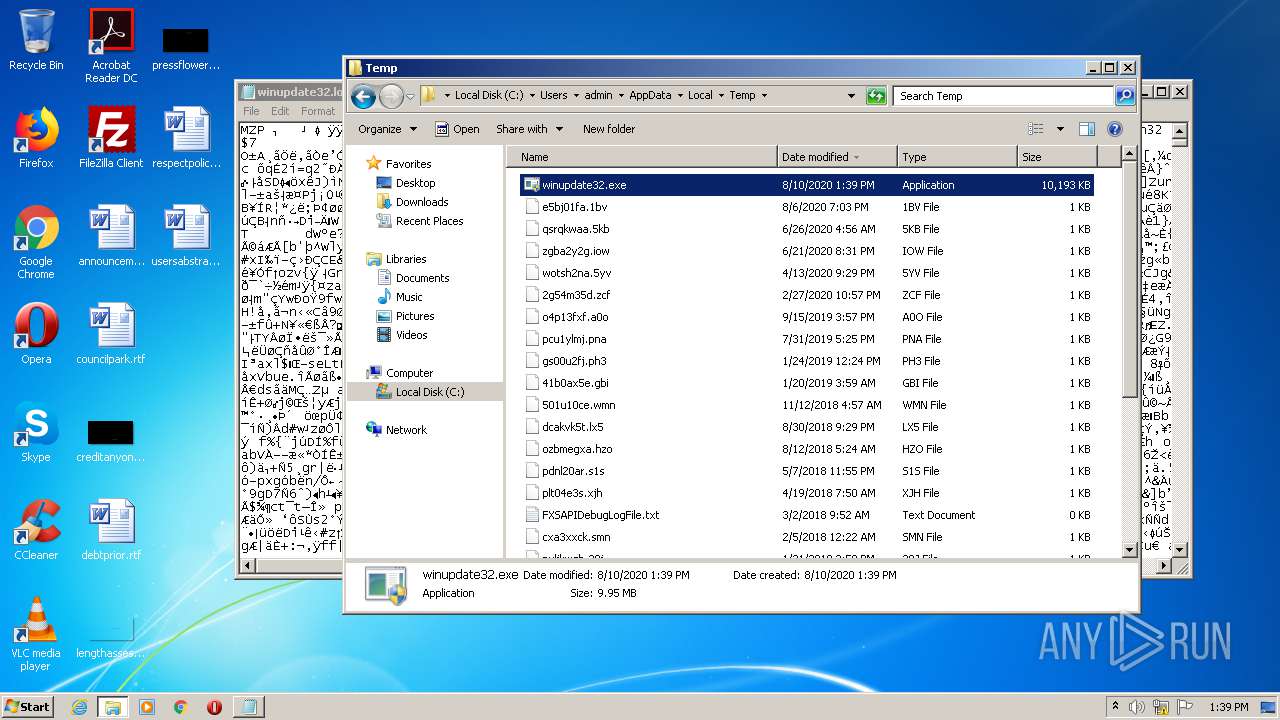
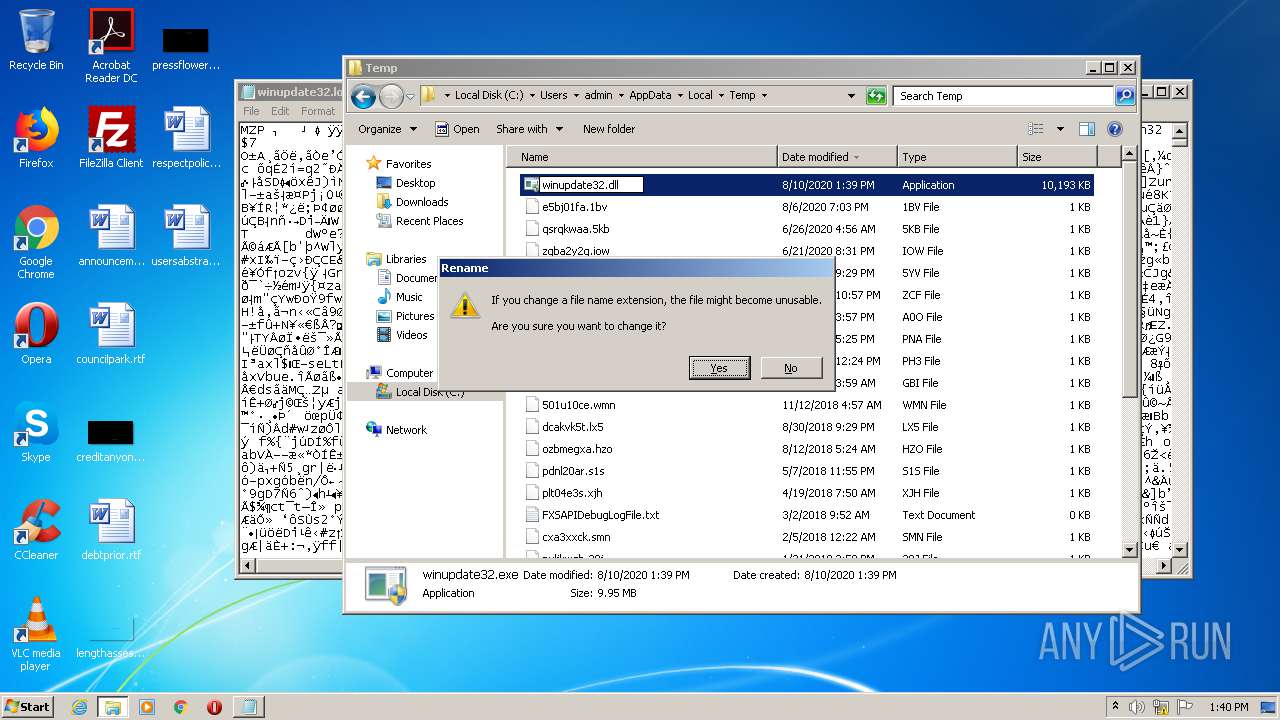
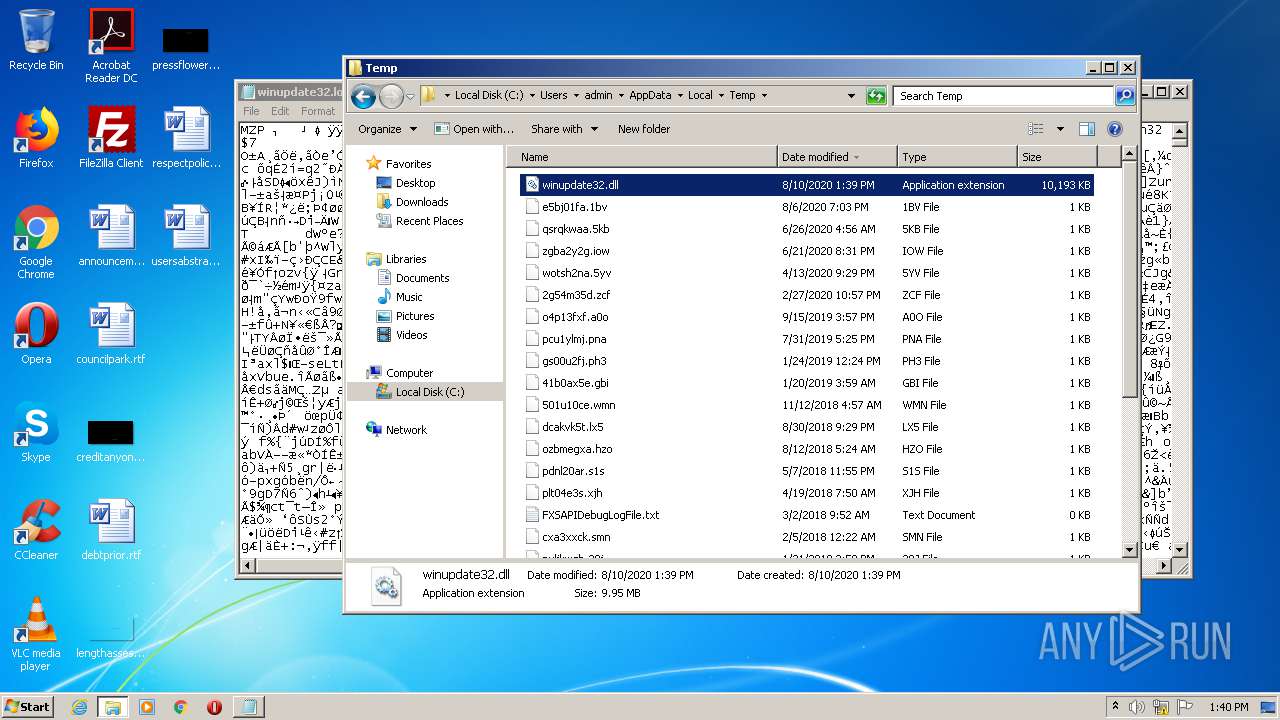
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 352 | explorer.exe | C:\Users\admin\AppData\Local\Temp\winupdate32.exe | executable | |
MD5:— | SHA256:— | |||
| 352 | explorer.exe | C:\Users\admin\AppData\Local\Temp\winupdate32.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report