| File name: | 𝗞𝗠𝗦𝗣𝗜𝗖𝗢.exe |
| Full analysis: | https://app.any.run/tasks/10d76e24-9647-47f6-b3c3-8ce7489e8b24 |
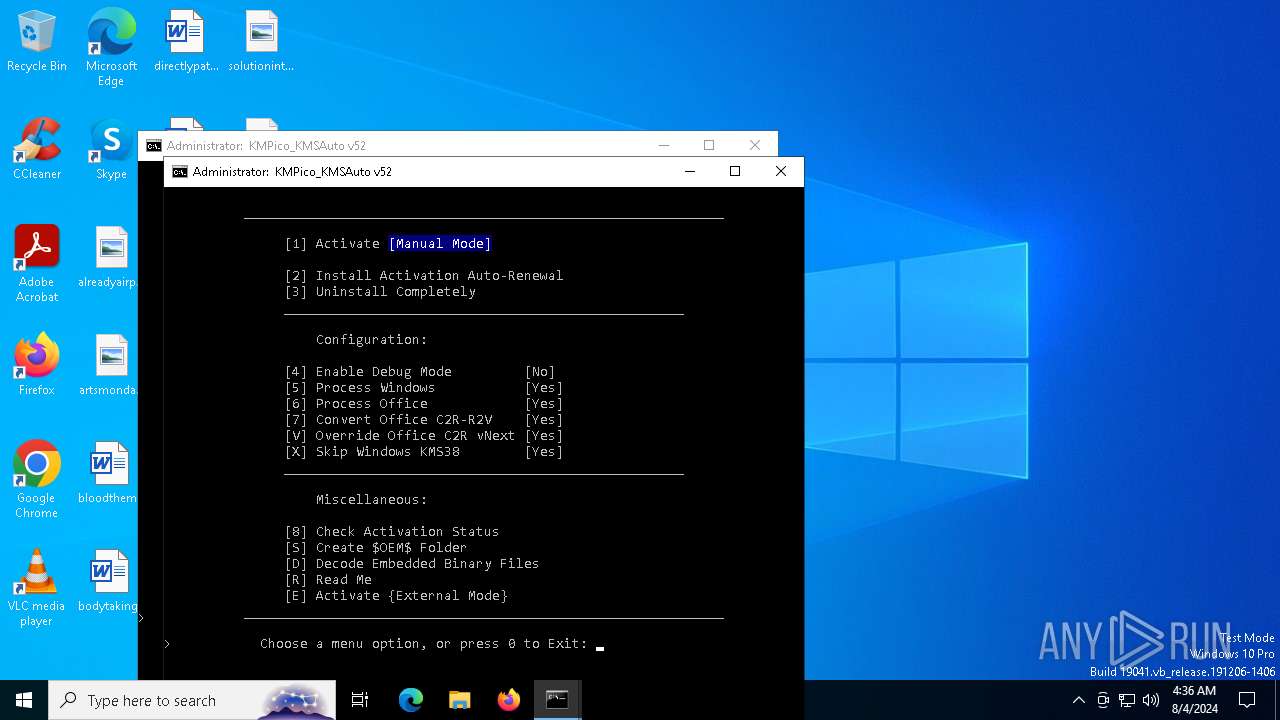
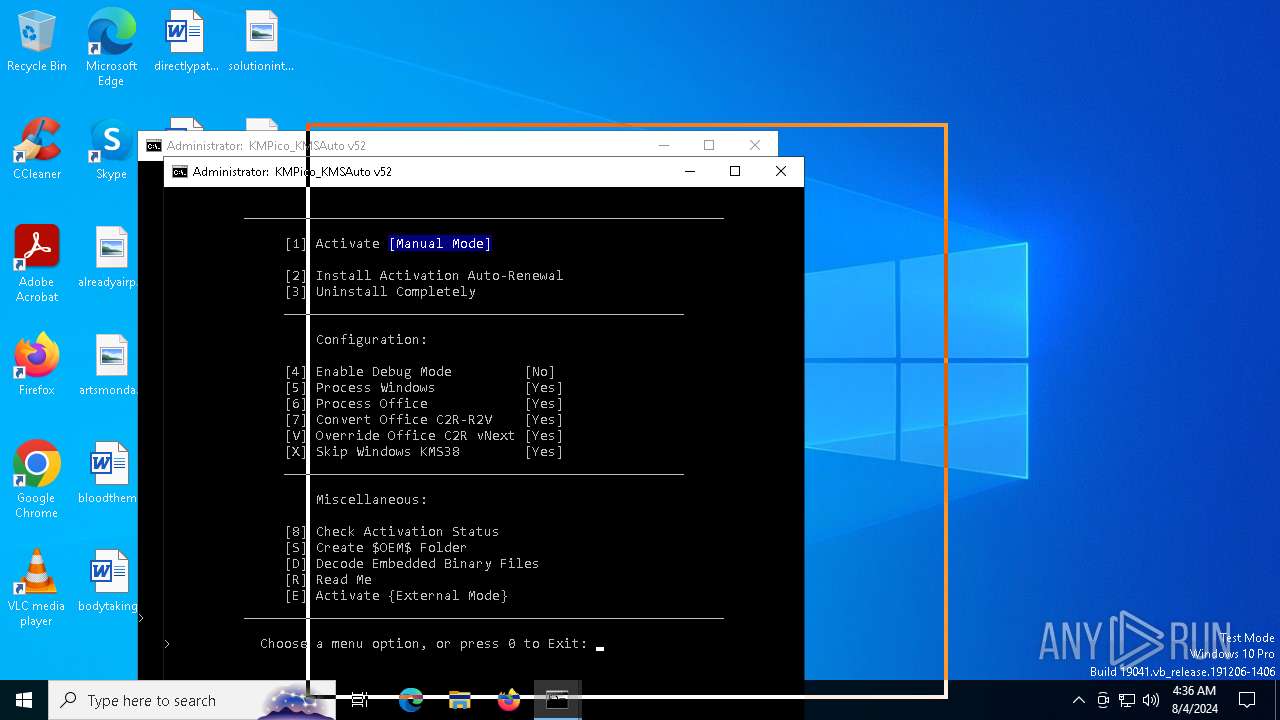
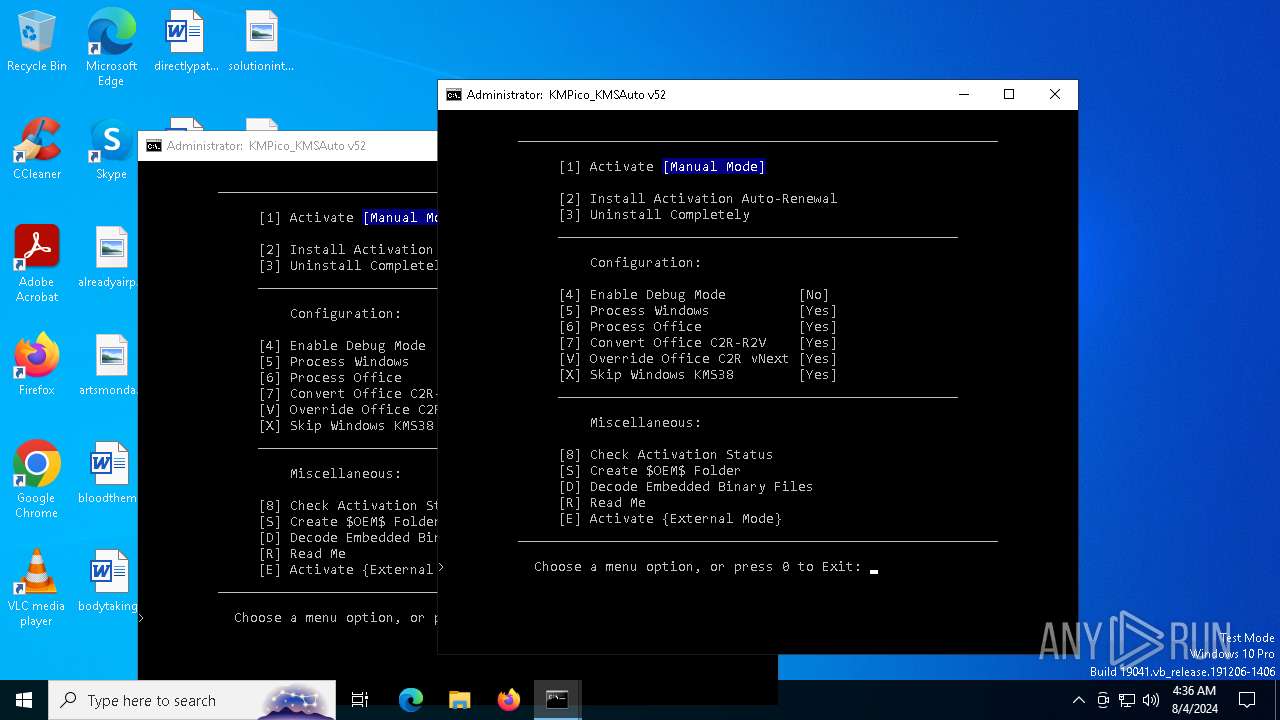
| Verdict: | Malicious activity |
| Analysis date: | August 04, 2024, 04:35:21 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64 (stripped to external PDB), for MS Windows |
| MD5: | 5D4FBA0B7799AFC9E6545B737A9C1233 |
| SHA1: | 350444CCA78E9B593F3E2CC5F4E49A3022CBC287 |
| SHA256: | BE944EEED71FBFAA27360FAF468A946D1899B287C9665F3543E3F30DFCDCD31E |
| SSDEEP: | 98304:of0BiPcJNdaBCv4UZ4dQ9sBCynSSDc+jDNqgb3TdQnZgsJdO8FJeecokJ+Jl+HzO:o5orjL |
MALICIOUS
Drops the executable file immediately after the start
- 𝗞𝗠𝗦𝗣𝗜𝗖𝗢.exe (PID: 6268)
Registers / Runs the DLL via REGSVR32.EXE
- 𝗞𝗠𝗦𝗣𝗜𝗖𝗢.exe (PID: 6268)
SUSPICIOUS
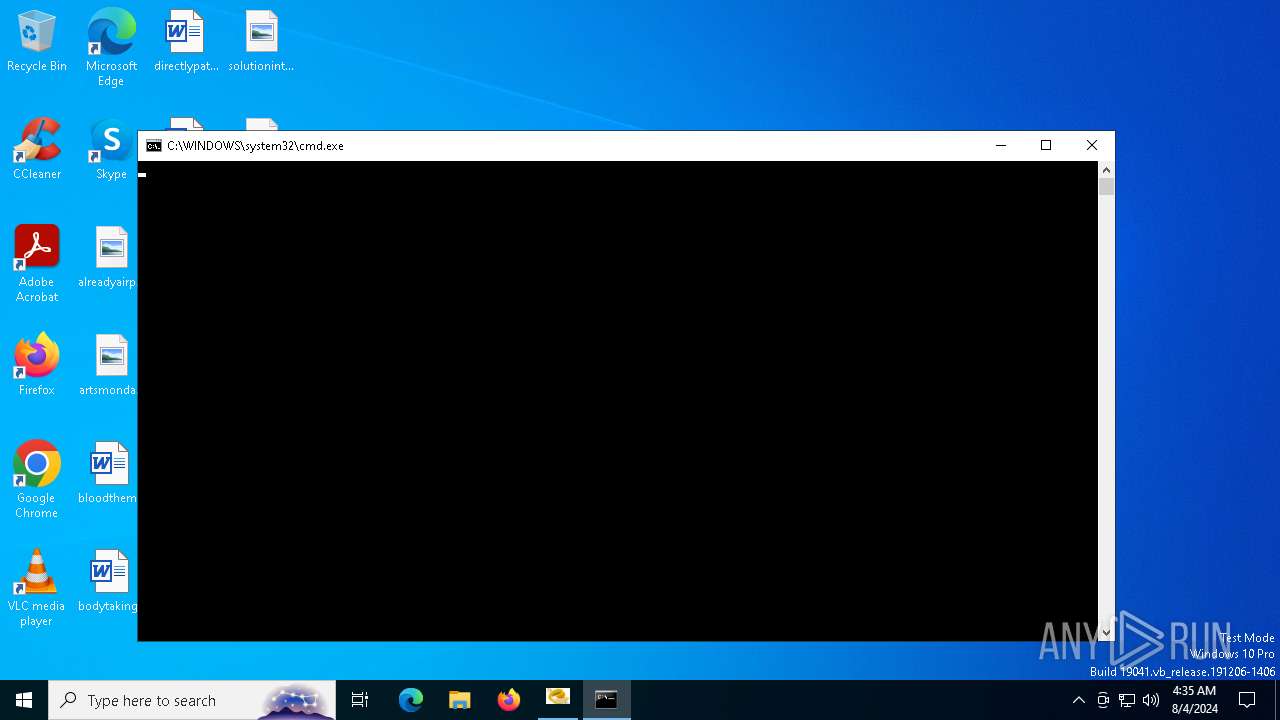
Starts CMD.EXE for commands execution
- 𝗞𝗠𝗦𝗣𝗜𝗖𝗢.exe (PID: 6268)
- cmd.exe (PID: 7016)
- cmd.exe (PID: 5500)
Executes application which crashes
- regsvr32.exe (PID: 2508)
- regsvr32.exe (PID: 1536)
Executable content was dropped or overwritten
- 𝗞𝗠𝗦𝗣𝗜𝗖𝗢.exe (PID: 6268)
Reads security settings of Internet Explorer
- 𝗞𝗠𝗦𝗣𝗜𝗖𝗢.exe (PID: 6268)
Reads the date of Windows installation
- 𝗞𝗠𝗦𝗣𝗜𝗖𝗢.exe (PID: 6268)
Executing commands from a ".bat" file
- 𝗞𝗠𝗦𝗣𝗜𝗖𝗢.exe (PID: 6268)
Application launched itself
- cmd.exe (PID: 7016)
- cmd.exe (PID: 5500)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 7016)
- cmd.exe (PID: 5500)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7016)
- cmd.exe (PID: 5500)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 7016)
- cmd.exe (PID: 5500)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7016)
- cmd.exe (PID: 5500)
Hides command output
- cmd.exe (PID: 5032)
- cmd.exe (PID: 6620)
- cmd.exe (PID: 5600)
- cmd.exe (PID: 6840)
Starts SC.EXE for service management
- cmd.exe (PID: 7016)
- cmd.exe (PID: 5500)
INFO
Found Base64 encoded text manipulation via PowerShell (YARA)
- 𝗞𝗠𝗦𝗣𝗜𝗖𝗢.exe (PID: 6268)
Found Base64 encoded access to UAC via PowerShell (YARA)
- 𝗞𝗠𝗦𝗣𝗜𝗖𝗢.exe (PID: 6268)
Found Base64 encoded file access via PowerShell (YARA)
- 𝗞𝗠𝗦𝗣𝗜𝗖𝗢.exe (PID: 6268)
Found Base64 encoded access to Windows Identity via PowerShell (YARA)
- 𝗞𝗠𝗦𝗣𝗜𝗖𝗢.exe (PID: 6268)
Found Base64 encoded reference to WMI classes (YARA)
- 𝗞𝗠𝗦𝗣𝗜𝗖𝗢.exe (PID: 6268)
Checks supported languages
- 𝗞𝗠𝗦𝗣𝗜𝗖𝗢.exe (PID: 6268)
- mode.com (PID: 3972)
- mode.com (PID: 4824)
Found Base64 encoded JSON usage via PowerShell (YARA)
- 𝗞𝗠𝗦𝗣𝗜𝗖𝗢.exe (PID: 6268)
Reads the computer name
- 𝗞𝗠𝗦𝗣𝗜𝗖𝗢.exe (PID: 6268)
Found Base64 encoded reflection usage via PowerShell (YARA)
- 𝗞𝗠𝗦𝗣𝗜𝗖𝗢.exe (PID: 6268)
Create files in a temporary directory
- 𝗞𝗠𝗦𝗣𝗜𝗖𝗢.exe (PID: 6268)
Creates files or folders in the user directory
- WerFault.exe (PID: 904)
- WerFault.exe (PID: 2468)
Process checks computer location settings
- 𝗞𝗠𝗦𝗣𝗜𝗖𝗢.exe (PID: 6268)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 2804)
- WMIC.exe (PID: 5292)
Reads Microsoft Office registry keys
- reg.exe (PID: 2228)
- reg.exe (PID: 4292)
- reg.exe (PID: 6188)
- reg.exe (PID: 1236)
- reg.exe (PID: 1356)
- reg.exe (PID: 376)
- reg.exe (PID: 1184)
- reg.exe (PID: 4160)
- reg.exe (PID: 6936)
- reg.exe (PID: 3984)
- reg.exe (PID: 5540)
- reg.exe (PID: 6040)
- reg.exe (PID: 1536)
- reg.exe (PID: 6604)
- reg.exe (PID: 6288)
- reg.exe (PID: 2396)
- reg.exe (PID: 6480)
- reg.exe (PID: 5796)
Checks operating system version
- cmd.exe (PID: 7016)
- cmd.exe (PID: 5500)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.2) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Large address aware, No debug |
| PEType: | PE32+ |
| LinkerVersion: | 3.22 |
| CodeSize: | 5884768 |
| InitializedDataSize: | 289700 |
| UninitializedDataSize: | 40952 |
| EntryPoint: | 0x3460 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.2.1.5 |
| ProductVersionNumber: | 3.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug, Pre-release, Patched, Private build, Special build |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | universal school app |
| CompanyName: | universal school app |
| FileDescription: | universal school app |
| FileVersion: | 4.2.1.5 |
| InternalName: | universal school app |
| LegalCopyright: | universal school app |
| LegalTrademarks: | universal school app |
| OriginalFileName: | universal school app |
| ProductName: | universal school app |
| ProductVersion: | 3 |
| PrivateBuild: | 2 |
| SpecialBuild: | 4 |
Total processes
256
Monitored processes
124
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | findstr /i /r "project.*" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 376 | findstr /i /r "project.*" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 376 | reg query HKCU\SOFTWARE\Microsoft\Office\16.0\Common\Licensing\LicensingNext | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | findstr /i /v "project visio" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 888 | reg query "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion" /v UBR | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 904 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 2508 -s 732 | C:\Windows\SysWOW64\WerFault.exe | — | regsvr32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1048 | findstr /i /r ".*volume" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1048 | C:\WINDOWS\system32\cmd.exe /c dir /b /ad C:\WINDOWS\System32\spp\tokens\skus | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1104 | find /i "0x0" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | find /i "Full" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
20 199
Read events
20 159
Write events
34
Delete events
6
Modification events
| (PID) Process: | (904) WerFault.exe | Key: | \REGISTRY\A\{dd3871ca-5951-872f-6b84-953fa2ce2785}\Root\InventoryApplicationFile |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (904) WerFault.exe | Key: | \REGISTRY\A\{dd3871ca-5951-872f-6b84-953fa2ce2785}\Root\InventoryApplicationFile\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (904) WerFault.exe | Key: | \REGISTRY\A\{dd3871ca-5951-872f-6b84-953fa2ce2785}\Root\InventoryApplicationFile\regsvr32.exe|8f2966bc37740081 |
| Operation: | write | Name: | ProgramId |
Value: 0000f519feec486de87ed73cb92d3cac802400000000 | |||
| (PID) Process: | (904) WerFault.exe | Key: | \REGISTRY\A\{dd3871ca-5951-872f-6b84-953fa2ce2785}\Root\InventoryApplicationFile\regsvr32.exe|8f2966bc37740081 |
| Operation: | write | Name: | FileId |
Value: 0000cb377e2ba78e131d7a1887c58c073e23d003454f | |||
| (PID) Process: | (904) WerFault.exe | Key: | \REGISTRY\A\{dd3871ca-5951-872f-6b84-953fa2ce2785}\Root\InventoryApplicationFile\regsvr32.exe|8f2966bc37740081 |
| Operation: | write | Name: | LowerCaseLongPath |
Value: c:\windows\syswow64\regsvr32.exe | |||
| (PID) Process: | (904) WerFault.exe | Key: | \REGISTRY\A\{dd3871ca-5951-872f-6b84-953fa2ce2785}\Root\InventoryApplicationFile\regsvr32.exe|8f2966bc37740081 |
| Operation: | write | Name: | LongPathHash |
Value: regsvr32.exe|8f2966bc37740081 | |||
| (PID) Process: | (904) WerFault.exe | Key: | \REGISTRY\A\{dd3871ca-5951-872f-6b84-953fa2ce2785}\Root\InventoryApplicationFile\regsvr32.exe|8f2966bc37740081 |
| Operation: | write | Name: | Name |
Value: regsvr32.exe | |||
| (PID) Process: | (904) WerFault.exe | Key: | \REGISTRY\A\{dd3871ca-5951-872f-6b84-953fa2ce2785}\Root\InventoryApplicationFile\regsvr32.exe|8f2966bc37740081 |
| Operation: | write | Name: | OriginalFileName |
Value: regsvr32.exe | |||
| (PID) Process: | (904) WerFault.exe | Key: | \REGISTRY\A\{dd3871ca-5951-872f-6b84-953fa2ce2785}\Root\InventoryApplicationFile\regsvr32.exe|8f2966bc37740081 |
| Operation: | write | Name: | Publisher |
Value: microsoft corporation | |||
| (PID) Process: | (904) WerFault.exe | Key: | \REGISTRY\A\{dd3871ca-5951-872f-6b84-953fa2ce2785}\Root\InventoryApplicationFile\regsvr32.exe|8f2966bc37740081 |
| Operation: | write | Name: | Version |
Value: 10.0.19041.1 (winbuild.160101.0800) | |||
Executable files
2
Suspicious files
6
Text files
12
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6268 | 𝗞𝗠𝗦𝗣𝗜𝗖𝗢.exe | C:\Users\admin\AppData\Local\Temp\963937.tmp | — | |
MD5:— | SHA256:— | |||
| 904 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_regsvr32.exe_dcfebec5cacfe697149c8c5334526b1dab6d33_ce3feb90_9fe73ade-5a71-44bd-b907-6c6aa98a6bb7\Report.wer | — | |
MD5:— | SHA256:— | |||
| 6268 | 𝗞𝗠𝗦𝗣𝗜𝗖𝗢.exe | C:\Users\admin\AppData\Local\Temp\965578.tmp | — | |
MD5:— | SHA256:— | |||
| 2468 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_regsvr32.exe_52c4d1b8eb5d1bfbc9a832b0a3dfcba115563_ce3feb90_5b58d4aa-1020-4c4e-9fdc-d082f92cb291\Report.wer | — | |
MD5:— | SHA256:— | |||
| 6268 | 𝗞𝗠𝗦𝗣𝗜𝗖𝗢.exe | C:\Users\admin\AppData\Local\Temp\964140.tmp | text | |
MD5:2066543D1C4B0648A58882AD2296F9AC | SHA256:8A3CCB0AC1C6ABE75EF5D0EEEFF03DE1027077D53086AFEE1E17C097F4DF7B73 | |||
| 4208 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_imdrlyd0.g4x.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6268 | 𝗞𝗠𝗦𝗣𝗜𝗖𝗢.exe | C:\Users\admin\AppData\Local\Temp\964093.dll | executable | |
MD5:EC1D3176604FEF69007926FE403428BB | SHA256:3DF3AB31CF95F300E4D45008CA2A3F960755B2000B2E80D0F562AACDAE206B5C | |||
| 2468 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERBF26.tmp.WERInternalMetadata.xml | xml | |
MD5:30B7947DD96817897C809C4DE7F44DDE | SHA256:4FD7D1AD09F1B453967A05E1DA39B326785B9362BB6548A18045B3394D5BF8F1 | |||
| 6268 | 𝗞𝗠𝗦𝗣𝗜𝗖𝗢.exe | C:\Users\admin\AppData\Local\Temp\964156.bat | text | |
MD5:60BC2CA75A2B765CA05D7C003F0AD810 | SHA256:E2E25982F731EFD36B7ADC00ACE02E9DDA001E4F84D625674D96939C39F63183 | |||
| 904 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERB997.tmp.dmp | binary | |
MD5:EB9A18DC42E3C20965DAE05E02A76037 | SHA256:C80DF4FB4E185D80CB195397E12E868E33E20FB5133A5FADE2F392FD1F6E0BFD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
36
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2616 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2616 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6544 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6600 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2536 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2804 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2536 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5336 | SearchApp.exe | 2.23.209.140:443 | www.bing.com | Akamai International B.V. | GB | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2616 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |