| File name: | utorrent_installer.exe |
| Full analysis: | https://app.any.run/tasks/bb728c81-195a-4664-8b64-f5accb2bdf6d |
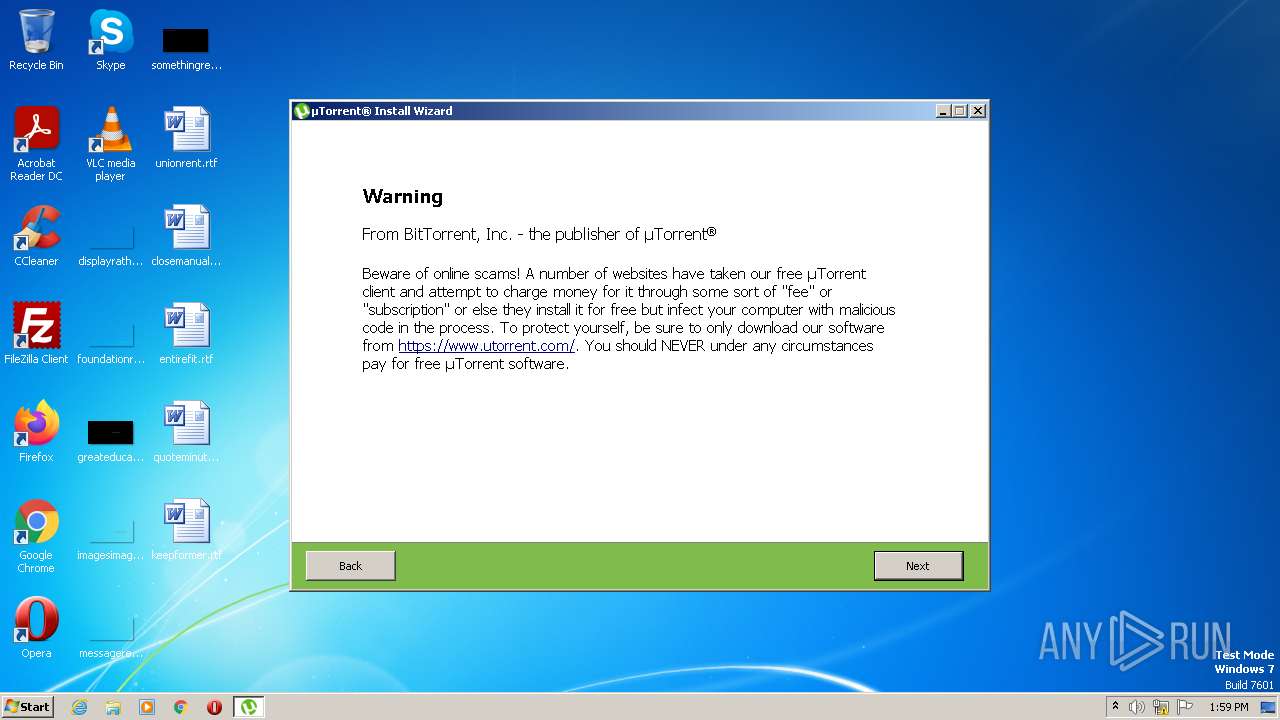
| Verdict: | Malicious activity |
| Analysis date: | April 04, 2023, 12:59:21 |
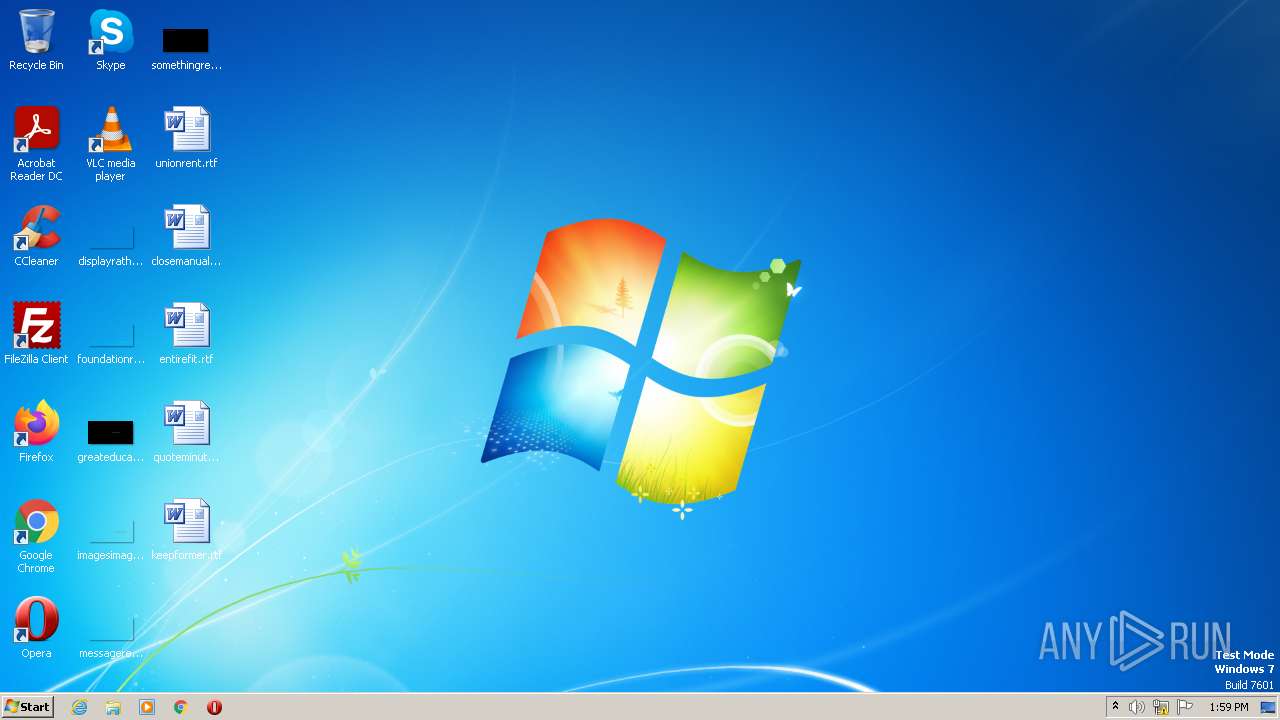
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | BB58FD279A1B991E2BEBB1941BB64905 |
| SHA1: | 71F48CFC2AD7F6FAA0CFB9B9424E5564E215A9B0 |
| SHA256: | BE91A0635CAB8BE4952C30398671617F9E548F30451172ED0ECD416FDC0AA998 |
| SSDEEP: | 24576:a4nXubIQGyxbPV0db26sdRr9IThAZymuz7lnAjEHLcfVLKswfsl:aqe3f6e9Zyh71SaLcfxOfsl |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- utorrent_installer.exe (PID: 2368)
- utorrent_installer.exe (PID: 3760)
- utorrent_installer.tmp (PID: 3936)
Reads the Windows owner or organization settings
- utorrent_installer.tmp (PID: 3936)
Reads settings of System Certificates
- utorrent_installer.tmp (PID: 3936)
Reads the Internet Settings
- utorrent_installer.tmp (PID: 3936)
INFO
Create files in a temporary directory
- utorrent_installer.exe (PID: 2368)
- utorrent_installer.exe (PID: 3760)
- utorrent_installer.tmp (PID: 3936)
Checks supported languages
- utorrent_installer.exe (PID: 2368)
- utorrent_installer.tmp (PID: 920)
- utorrent_installer.exe (PID: 3760)
- utorrent_installer.tmp (PID: 3936)
Reads the computer name
- utorrent_installer.tmp (PID: 920)
- utorrent_installer.tmp (PID: 3936)
Application was dropped or rewritten from another process
- utorrent_installer.tmp (PID: 920)
- utorrent_installer.tmp (PID: 3936)
The process checks LSA protection
- utorrent_installer.tmp (PID: 920)
- utorrent_installer.tmp (PID: 3936)
Reads the machine GUID from the registry
- utorrent_installer.tmp (PID: 3936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (65.1) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (24.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.9) |
| .exe | | | Win32 Executable (generic) (2.6) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
EXIF
EXE
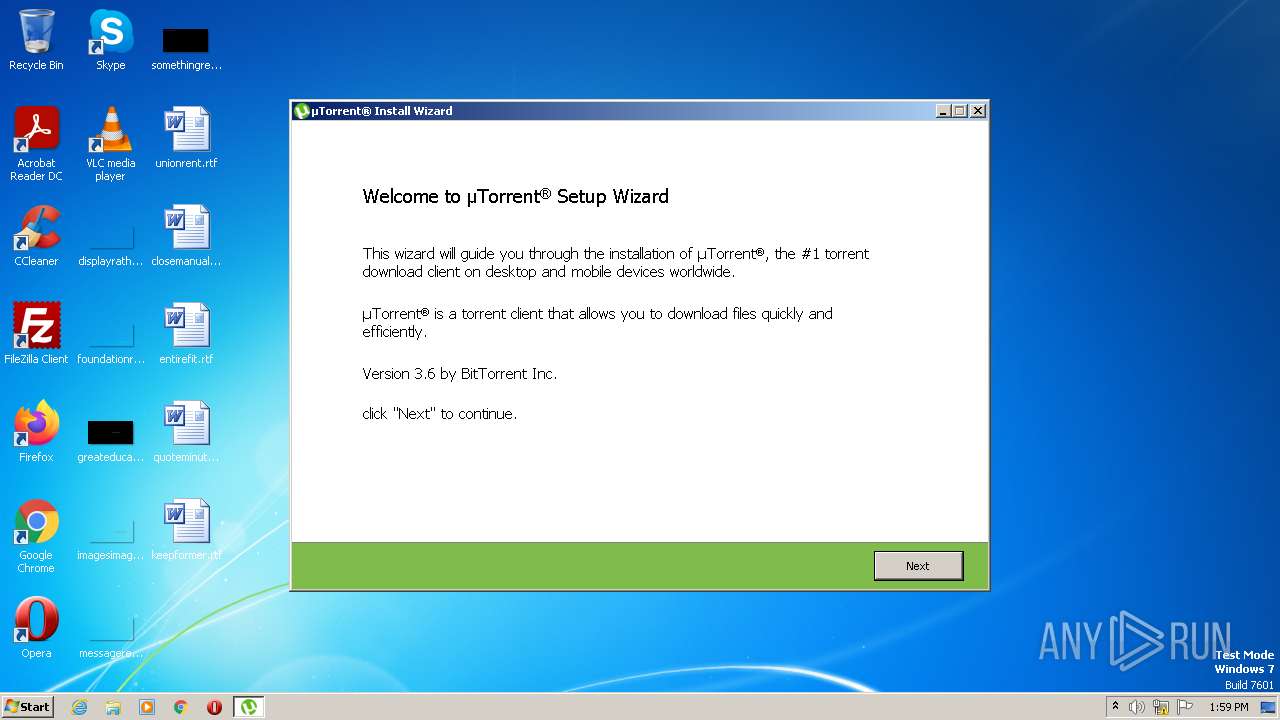
| ProductVersion: | 3.6 |
|---|---|
| ProductName: | uTorrent® Classic |
| OriginalFileName: | |
| LegalCopyright: | ©2022 RainBerry Inc. All Rights Reserved |
| FileVersion: | 3.6 |
| FileDescription: | uTorrent® Classic |
| CompanyName: | |
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 3.6.0.0 |
| FileVersionNumber: | 3.6.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6.1 |
| ImageVersion: | 6 |
| OSVersion: | 6.1 |
| EntryPoint: | 0xb5eec |
| UninitializedDataSize: | - |
| InitializedDataSize: | 72704 |
| CodeSize: | 741376 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| TimeStamp: | 2021:06:03 08:09:11+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Jun-2021 08:09:11 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | uTorrent® Classic |
| FileVersion: | 3.6 |
| LegalCopyright: | ©2022 RainBerry Inc. All Rights Reserved |
| OriginalFileName: | - |
| ProductName: | uTorrent® Classic |
| ProductVersion: | 3.6 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 03-Jun-2021 08:09:11 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000B361C | 0x000B3800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.35606 |
.itext | 0x000B5000 | 0x00001688 | 0x00001800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.97275 |
.data | 0x000B7000 | 0x000037A4 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.0444 |
.bss | 0x000BB000 | 0x00006DE8 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x000C2000 | 0x00000F36 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.8987 |
.didata | 0x000C3000 | 0x000001A4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75636 |
.edata | 0x000C4000 | 0x0000009A | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.87222 |
.tls | 0x000C5000 | 0x00000018 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x000C6000 | 0x0000005D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.38389 |
.rsrc | 0x000C7000 | 0x0000CCE8 | 0x0000CE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.7055 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.18295 | 1830 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.46918 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.0586 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.54687 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 7.96969 | 21583 | Latin 1 / Western European | English - United States | RT_ICON |
4086 | 3.16547 | 864 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4087 | 3.40938 | 608 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4088 | 3.31153 | 1116 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4089 | 3.33977 | 1036 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.36723 | 724 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
netapi32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x000BE63C |
__dbk_fcall_wrapper | 2 | 0x0000D0A0 |
TMethodImplementationIntercept | 3 | 0x00054060 |
Total processes
41
Monitored processes
4
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 920 | "C:\Users\admin\AppData\Local\Temp\is-9Q5BG.tmp\utorrent_installer.tmp" /SL5="$8012E,874637,815104,C:\Users\admin\AppData\Local\Temp\utorrent_installer.exe" | C:\Users\admin\AppData\Local\Temp\is-9Q5BG.tmp\utorrent_installer.tmp | — | utorrent_installer.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 2 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2368 | "C:\Users\admin\AppData\Local\Temp\utorrent_installer.exe" | C:\Users\admin\AppData\Local\Temp\utorrent_installer.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: uTorrent® Classic Exit code: 2 Version: 3.6 Modules
| |||||||||||||||
| 3760 | "C:\Users\admin\AppData\Local\Temp\utorrent_installer.exe" /SPAWNWND=$70134 /NOTIFYWND=$8012E | C:\Users\admin\AppData\Local\Temp\utorrent_installer.exe | utorrent_installer.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: uTorrent® Classic Exit code: 2 Version: 3.6 Modules
| |||||||||||||||
| 3936 | "C:\Users\admin\AppData\Local\Temp\is-EAFM8.tmp\utorrent_installer.tmp" /SL5="$5012A,874637,815104,C:\Users\admin\AppData\Local\Temp\utorrent_installer.exe" /SPAWNWND=$70134 /NOTIFYWND=$8012E | C:\Users\admin\AppData\Local\Temp\is-EAFM8.tmp\utorrent_installer.tmp | utorrent_installer.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Setup/Uninstall Exit code: 2 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
7 620
Read events
7 584
Write events
28
Delete events
8
Modification events
| (PID) Process: | (3936) utorrent_installer.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3936) utorrent_installer.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3936) utorrent_installer.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | SessionHash |
Value: 068626E3D4F896107DE865960B9A24BDE2CE9550F0155C45AB3EC4C15E4C5214 | |||
| (PID) Process: | (3936) utorrent_installer.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Owner |
Value: 600F0000F01AB34BF566D901 | |||
| (PID) Process: | (3936) utorrent_installer.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
6
Suspicious files
0
Text files
12
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3936 | utorrent_installer.tmp | C:\Users\admin\AppData\Local\Temp\is-DNEL1.tmp\is-U2VQL.tmp | — | |
MD5:— | SHA256:— | |||
| 3936 | utorrent_installer.tmp | C:\Users\admin\AppData\Local\Temp\is-DNEL1.tmp\license.rtf | text | |
MD5:D88780E16B98ABD0E73EE15D2AC5FE46 | SHA256:89FE20D3C918FB515E63E632E325ED93618DAB8C00D39074594D466C978B9868 | |||
| 3936 | utorrent_installer.tmp | C:\Users\admin\AppData\Local\Temp\is-DNEL1.tmp\is-1MAAE.tmp | image | |
MD5:F1F21BE822C2E22934C88478DDA2FD74 | SHA256:5F3223DBFD67DC3BA0E0A3C23F5294258251272E06A66FDEE6416DACC160FAD4 | |||
| 3936 | utorrent_installer.tmp | C:\Users\admin\AppData\Local\Temp\is-DNEL1.tmp\Logo.png | image | |
MD5:5424804C80DB74E1304535141A5392C6 | SHA256:9B7E2EA77E518B50E5DD78E0FAEC509E791949A7C7F360A967C9EE204A8F1412 | |||
| 3936 | utorrent_installer.tmp | C:\Users\admin\AppData\Local\Temp\is-DNEL1.tmp\WebAdvisor.png | image | |
MD5:4CFFF8DC30D353CD3D215FD3A5DBAC24 | SHA256:0C430E56D69435D8AB31CBB5916A73A47D11EF65B37D289EE7D11130ADF25856 | |||
| 3760 | utorrent_installer.exe | C:\Users\admin\AppData\Local\Temp\is-EAFM8.tmp\utorrent_installer.tmp | executable | |
MD5:BEE3A3AE058047DBE5D147B30D11C331 | SHA256:1FF0CEFBFE0905F845EF0E0F2F2B20D5F131AE126BA4ACFBD368A6BE879DD5C7 | |||
| 3936 | utorrent_installer.tmp | C:\Users\admin\AppData\Local\Temp\is-DNEL1.tmp\AVG_AV.png | image | |
MD5:F1F21BE822C2E22934C88478DDA2FD74 | SHA256:5F3223DBFD67DC3BA0E0A3C23F5294258251272E06A66FDEE6416DACC160FAD4 | |||
| 3936 | utorrent_installer.tmp | C:\Users\admin\AppData\Local\Temp\is-DNEL1.tmp\is-ICSS4.tmp | image | |
MD5:4CFFF8DC30D353CD3D215FD3A5DBAC24 | SHA256:0C430E56D69435D8AB31CBB5916A73A47D11EF65B37D289EE7D11130ADF25856 | |||
| 3936 | utorrent_installer.tmp | C:\Users\admin\AppData\Local\Temp\is-DNEL1.tmp\botva2.dll | executable | |
MD5:67965A5957A61867D661F05AE1F4773E | SHA256:450B9B0BA25BF068AFBC2B23D252585A19E282939BF38326384EA9112DFD0105 | |||
| 2368 | utorrent_installer.exe | C:\Users\admin\AppData\Local\Temp\is-9Q5BG.tmp\utorrent_installer.tmp | executable | |
MD5:BEE3A3AE058047DBE5D147B30D11C331 | SHA256:1FF0CEFBFE0905F845EF0E0F2F2B20D5F131AE126BA4ACFBD368A6BE879DD5C7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
11
DNS requests
6
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3936 | utorrent_installer.tmp | GET | — | 82.221.103.243:80 | http://download-new.utorrent.com/endpoint/utorrent/os/riserollout/track/stable | IS | — | — | whitelisted |
3936 | utorrent_installer.tmp | HEAD | 200 | 82.221.103.242:80 | http://download-new.utorrent.com/endpoint/utorrent/os/riserollout/track/stable | IS | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3936 | utorrent_installer.tmp | 52.222.232.181:443 | d4w1kp01cnm54.cloudfront.net | AMAZON-02 | US | unknown |
3936 | utorrent_installer.tmp | 18.66.107.12:443 | d3cfdnjelz8u20.cloudfront.net | AMAZON-02 | US | unknown |
3936 | utorrent_installer.tmp | 18.66.97.48:443 | api.playanext.com | — | US | suspicious |
3936 | utorrent_installer.tmp | 52.222.206.112:443 | d4bohzj3dmv4j.cloudfront.net | AMAZON-02 | US | unknown |
3936 | utorrent_installer.tmp | 82.221.103.243:80 | download-new.utorrent.com | Advania Island ehf | IS | suspicious |
3936 | utorrent_installer.tmp | 82.221.103.242:80 | download-new.utorrent.com | Advania Island ehf | IS | suspicious |
3936 | utorrent_installer.tmp | 18.66.97.82:443 | api.playanext.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
d4w1kp01cnm54.cloudfront.net |
| whitelisted |
d3cfdnjelz8u20.cloudfront.net |
| whitelisted |
api.playanext.com |
| whitelisted |
d4bohzj3dmv4j.cloudfront.net |
| whitelisted |
download-new.utorrent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3936 | utorrent_installer.tmp | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3936 | utorrent_installer.tmp | Potentially Bad Traffic | ET INFO TLS Handshake Failure |