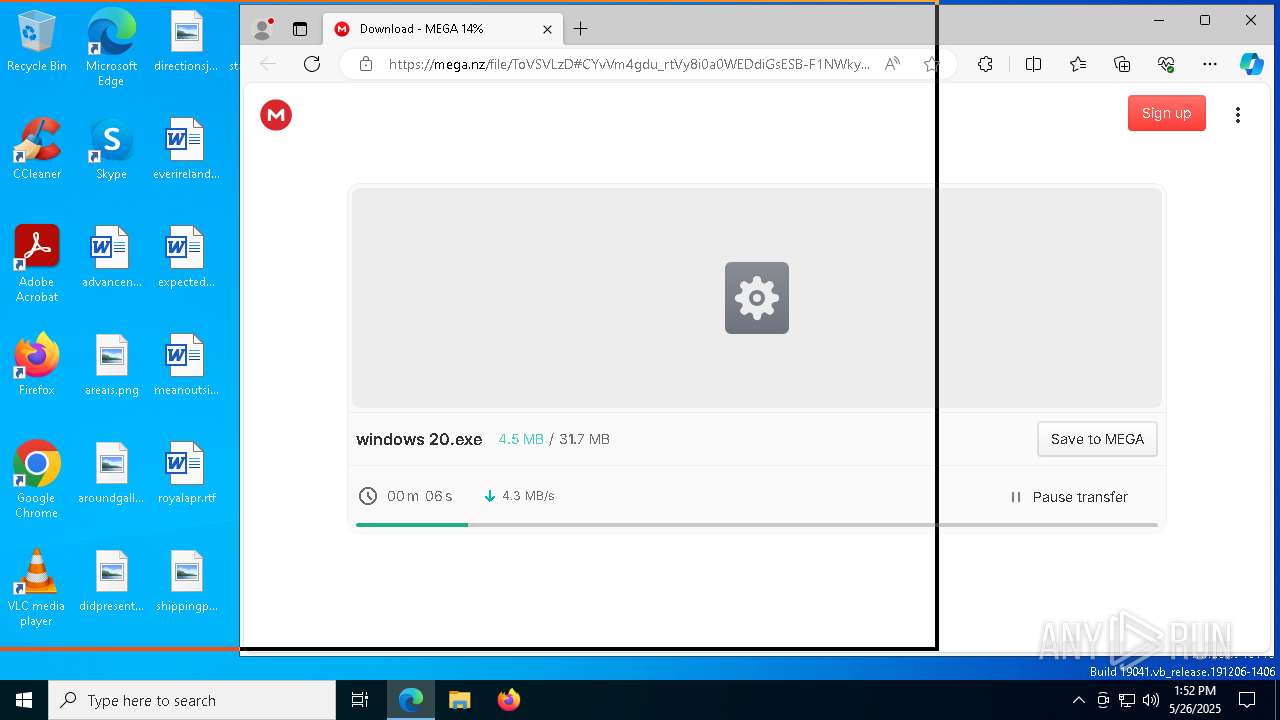
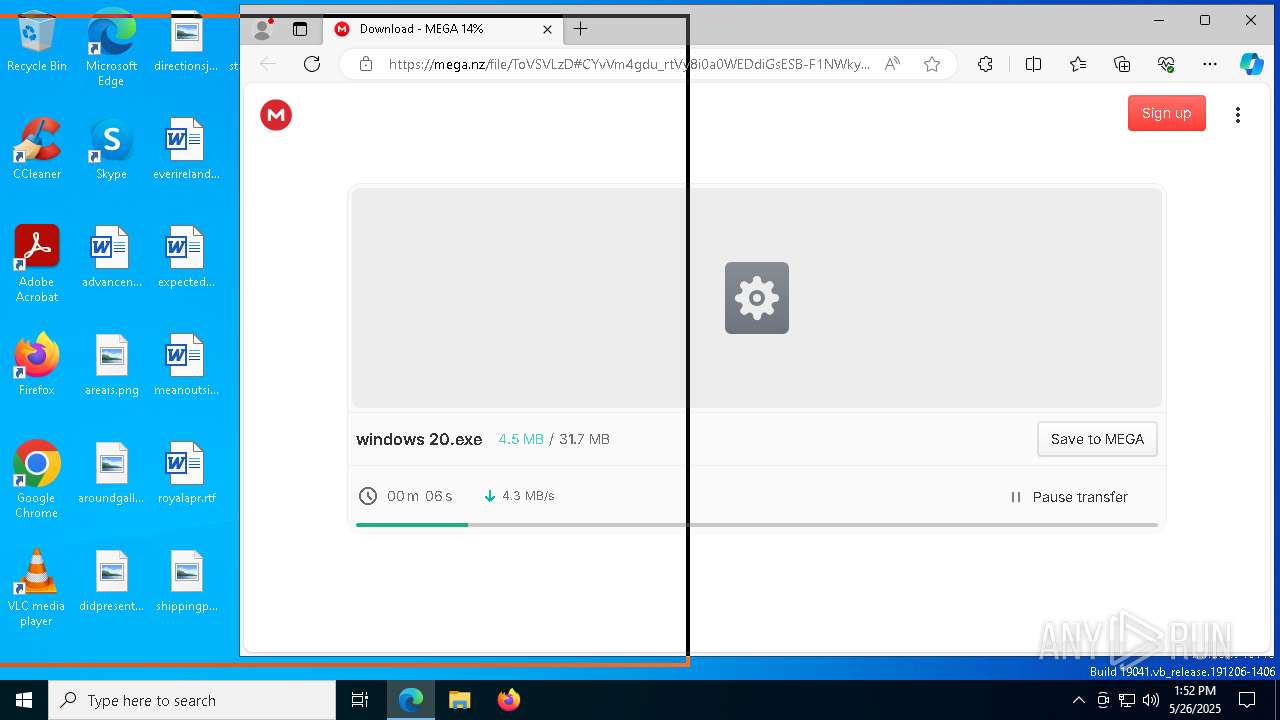
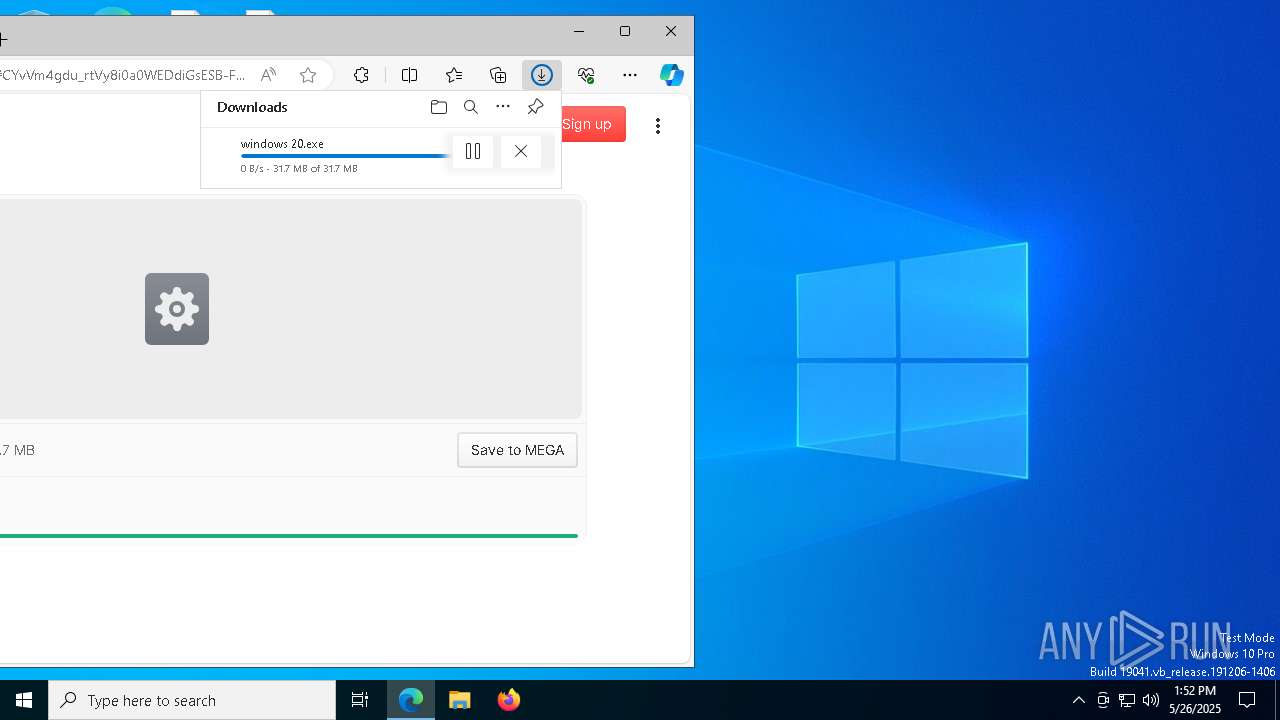
| URL: | https://mega.nz/file/ToVSVLzD#CYvVm4gdu_rtVy8i0a0WEDdiGsESB-F1NWkyGB3jXa4 |
| Full analysis: | https://app.any.run/tasks/a7785f49-56c6-42f6-af55-91e032b632fc |
| Verdict: | Malicious activity |
| Analysis date: | May 26, 2025, 13:51:48 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 097D5450CC1166B06060279370C8C36A |
| SHA1: | F3C7DDE8947EF21B8AAFE81A4264E0DF40809C3C |
| SHA256: | BE913D2DB2996DCD1841F29468CA65C3867759129C3A1CBD6CD3F637148D310F |
| SSDEEP: | 3:N8X/i/zUxQTtayIMNNhRn:284YtayLfRn |
MALICIOUS
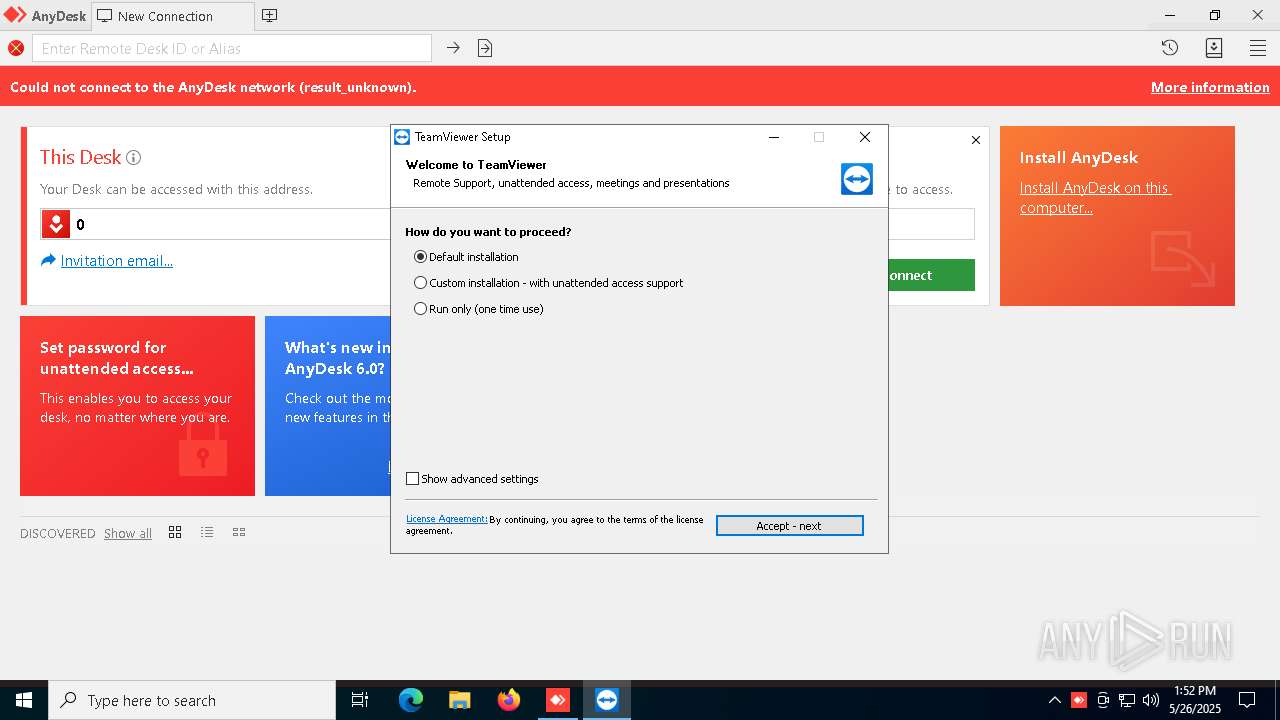
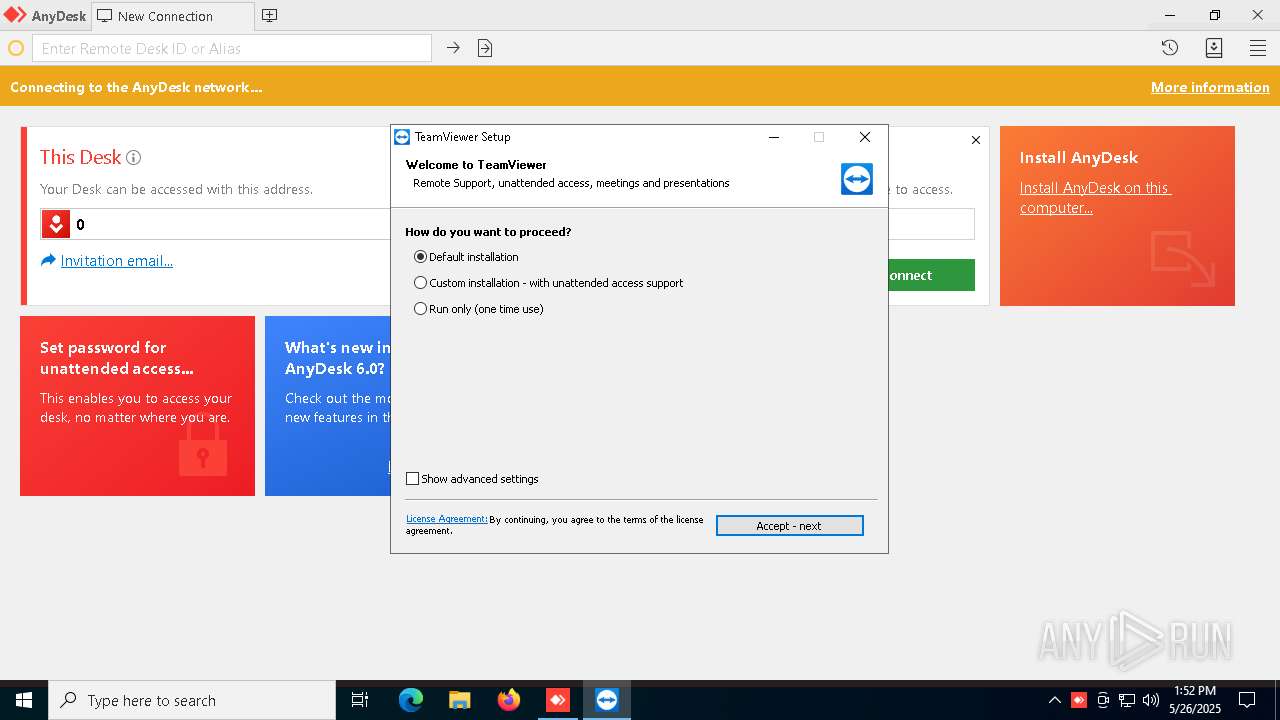
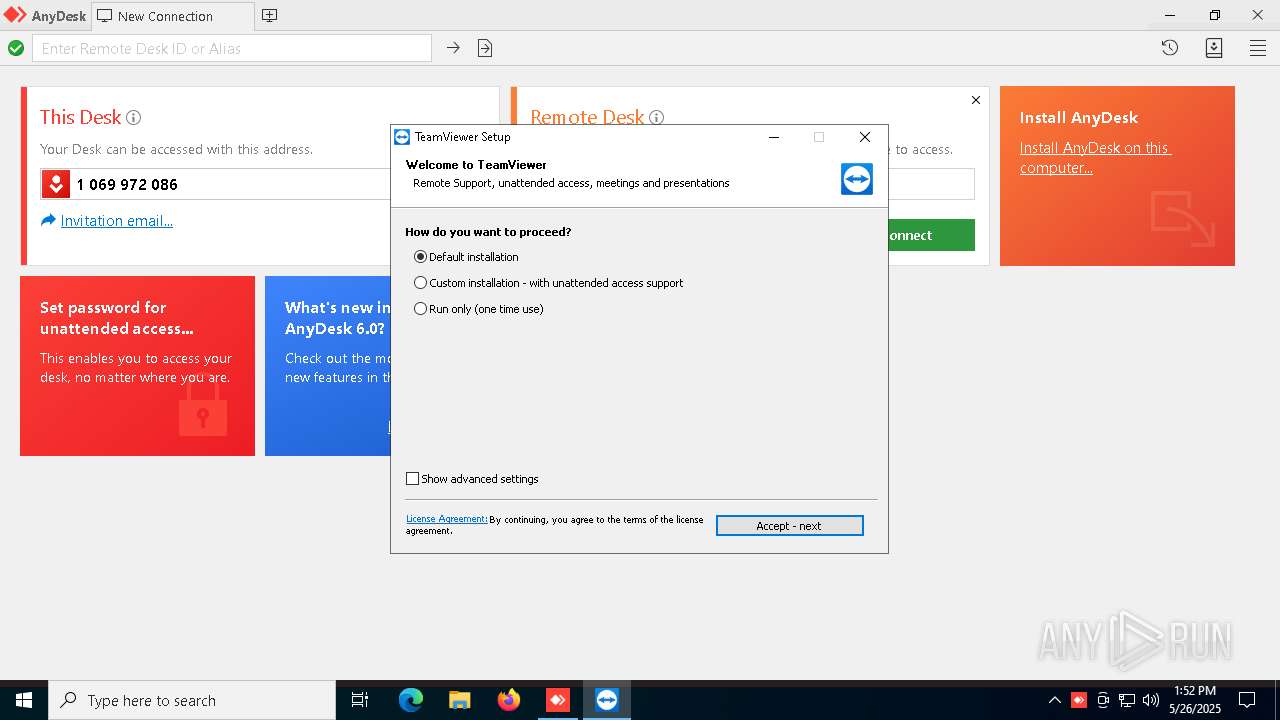
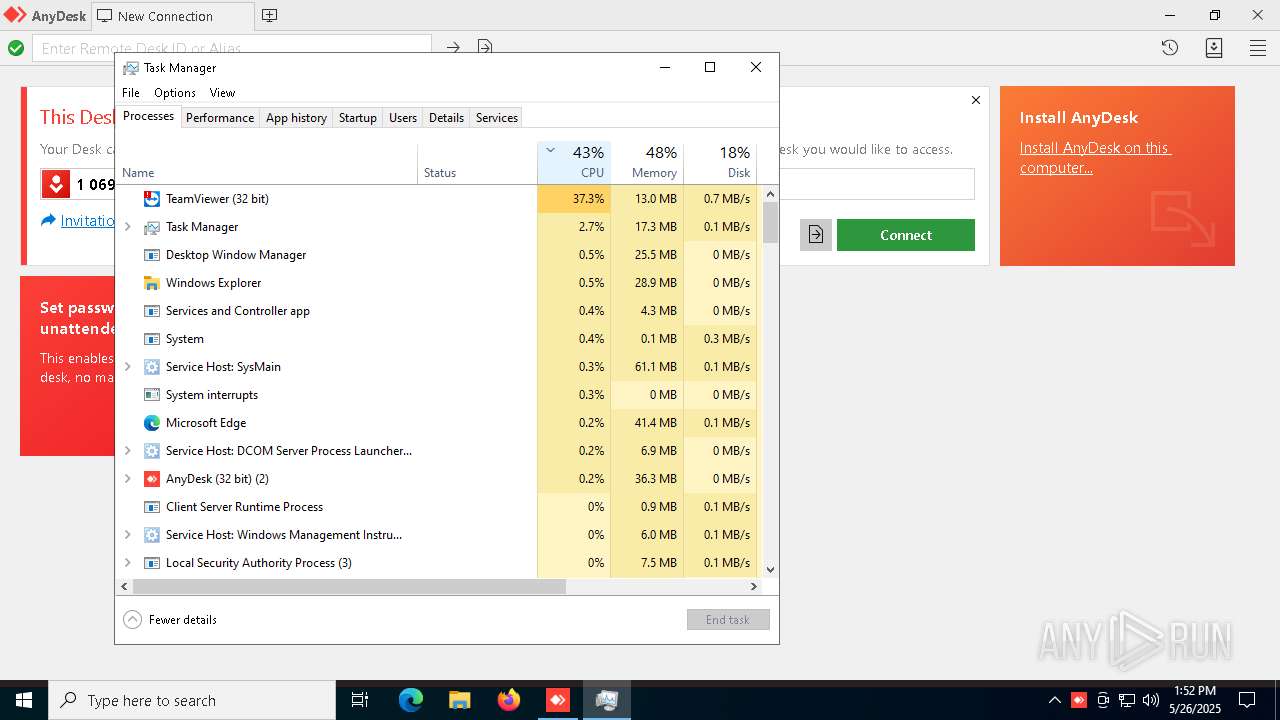
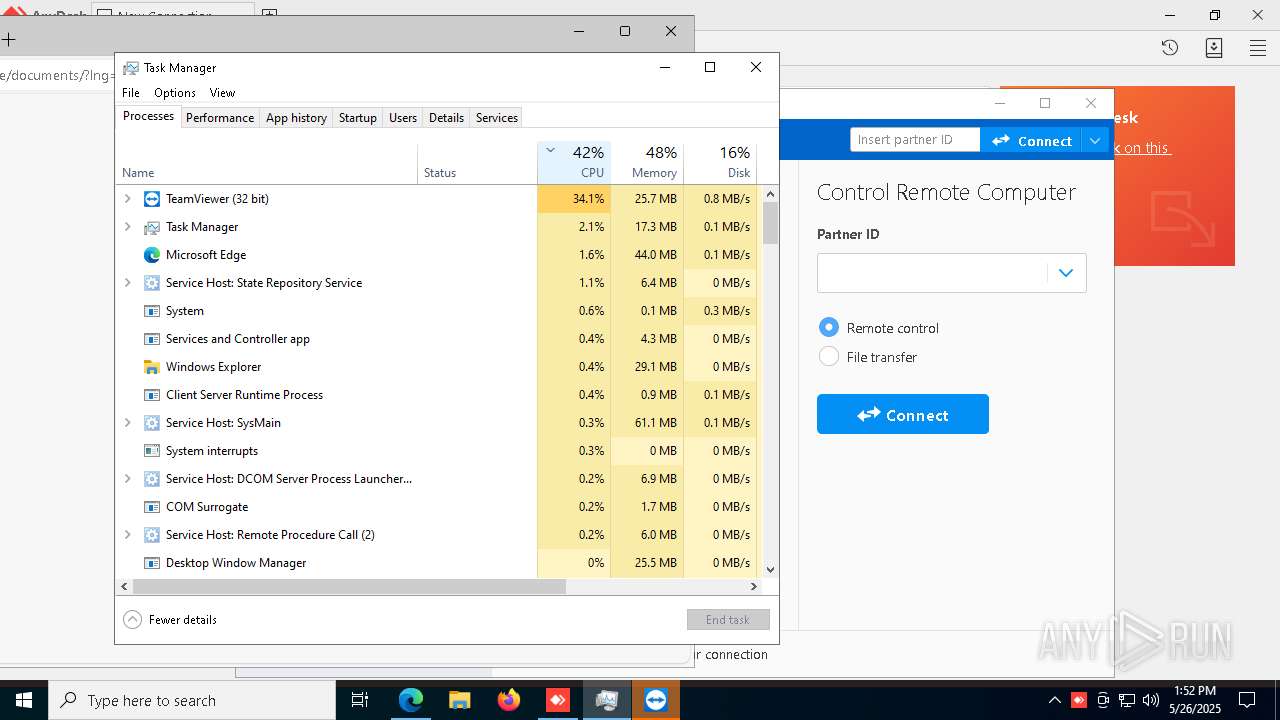
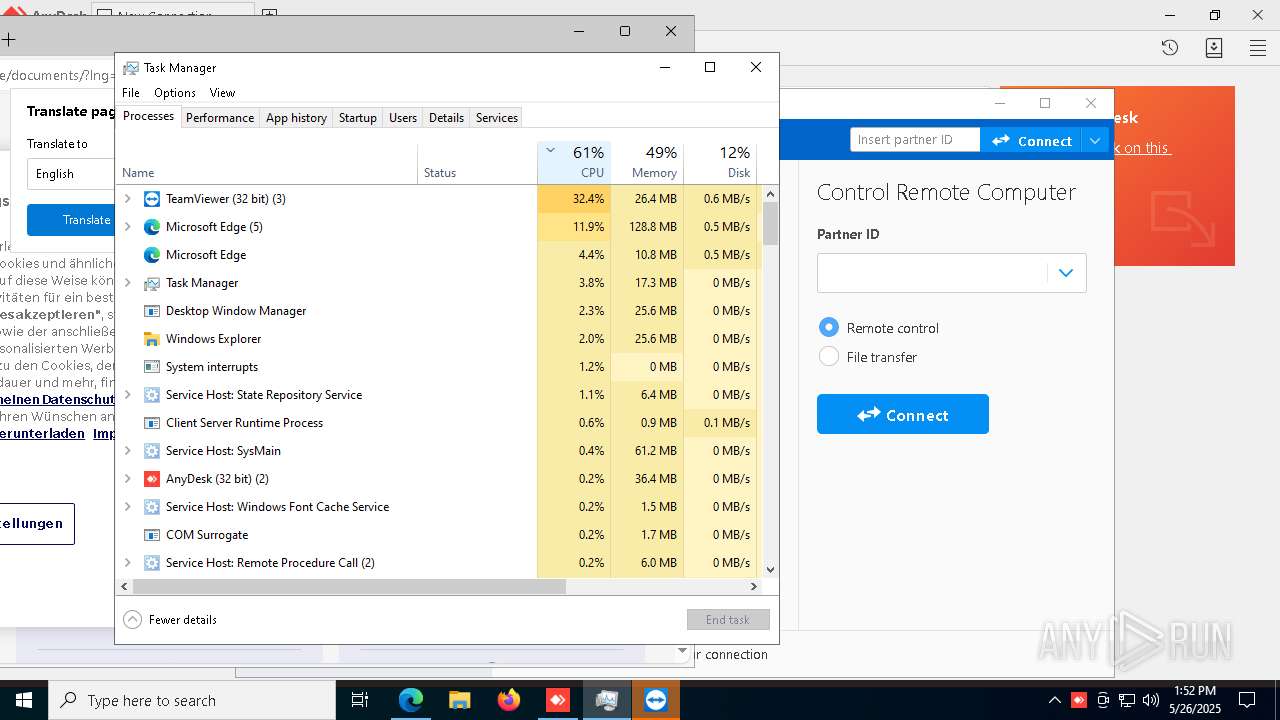
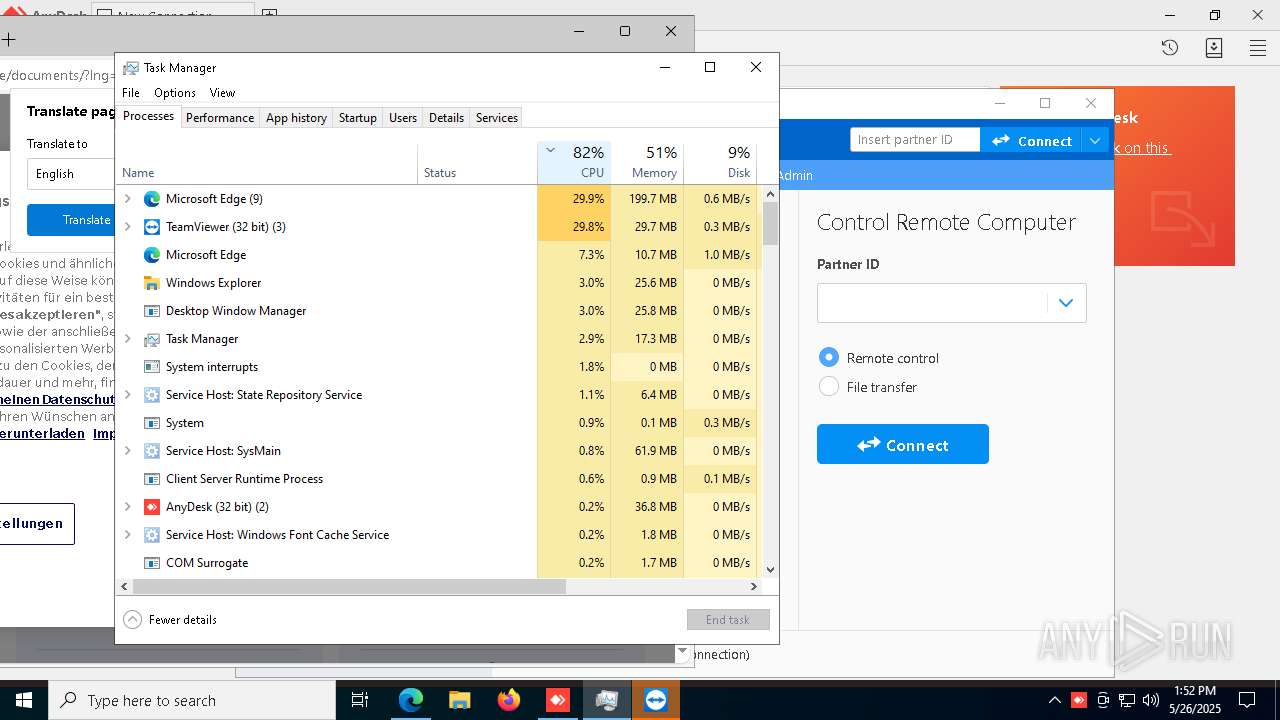
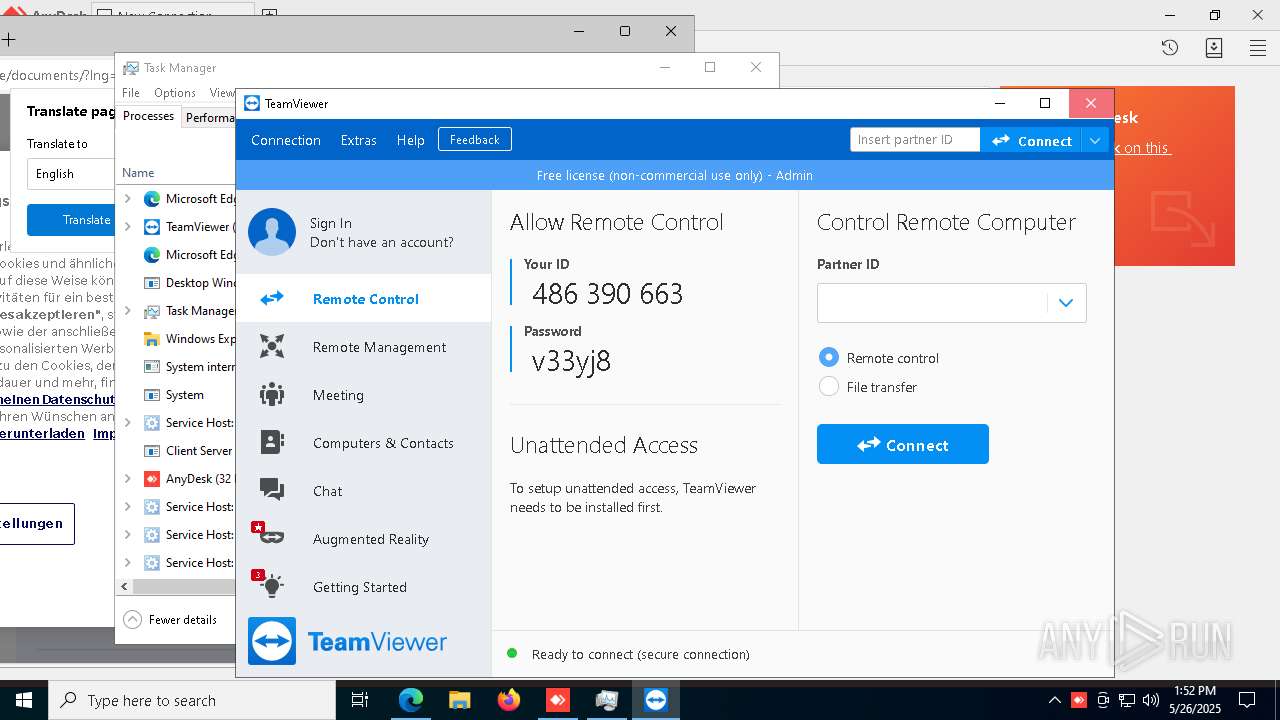
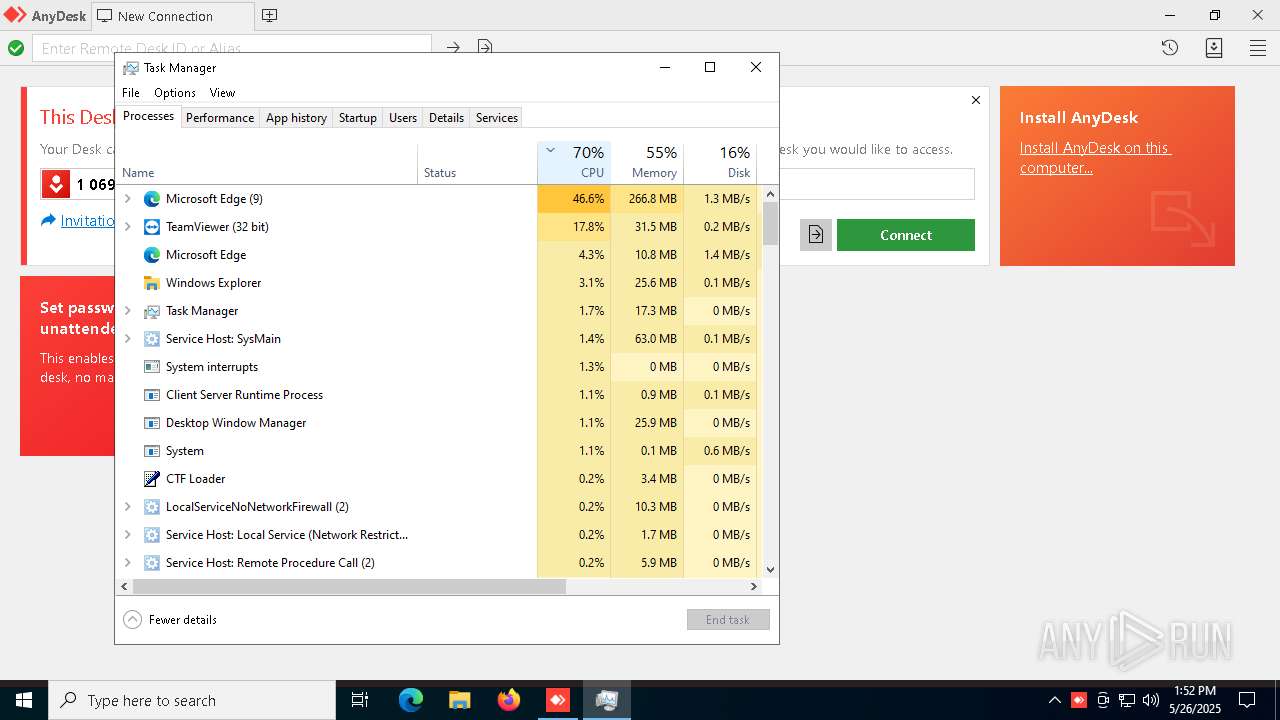
TEAMVIEWER has been detected (SURICATA)
- TeamViewer.exe (PID: 8080)
SUSPICIOUS
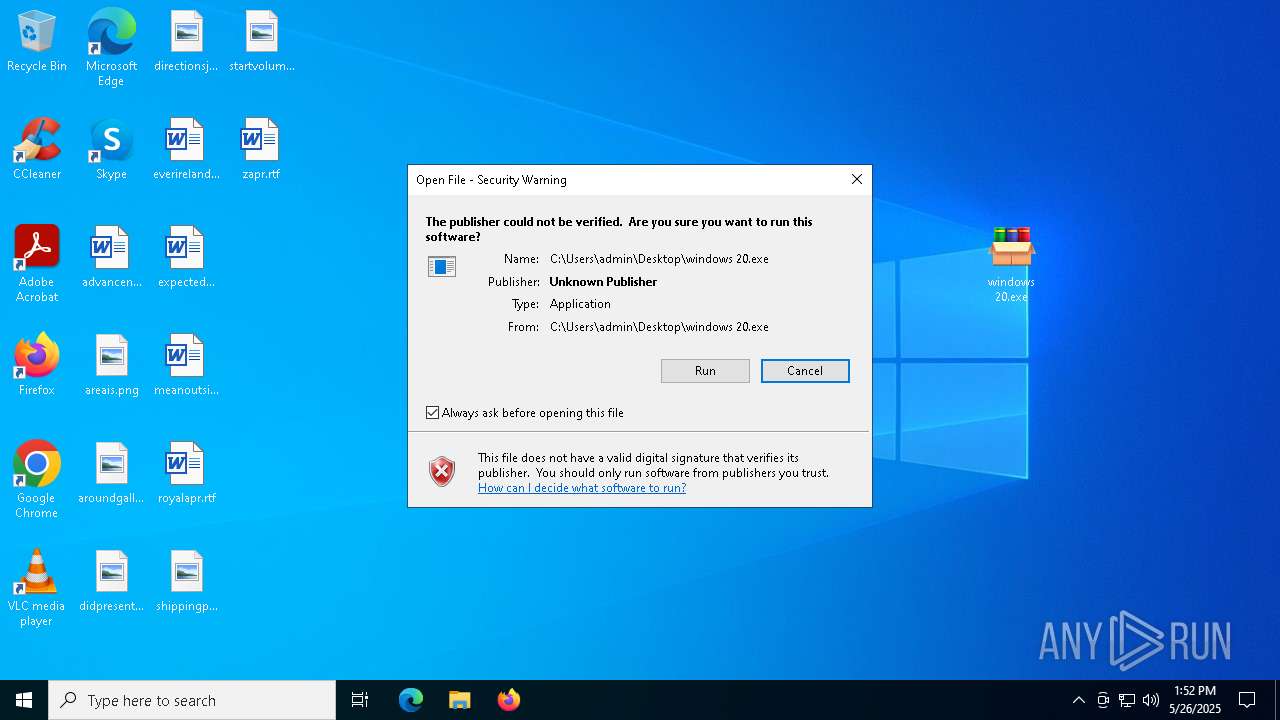
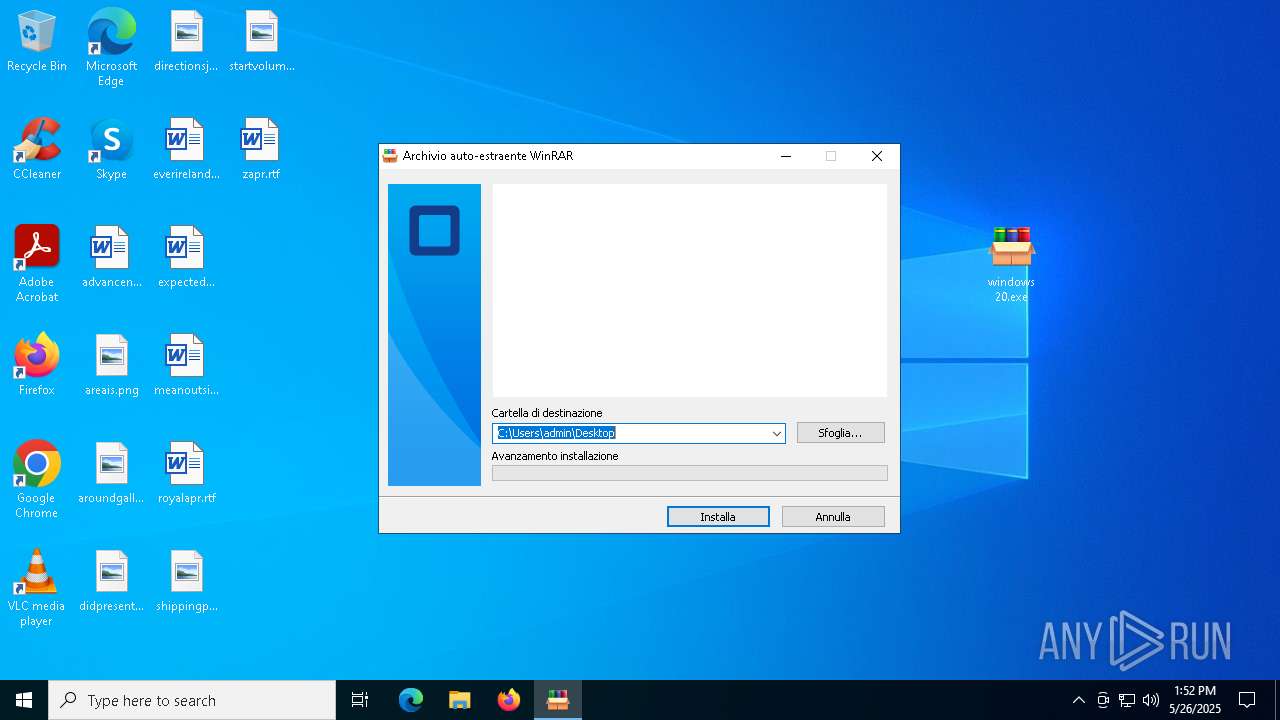
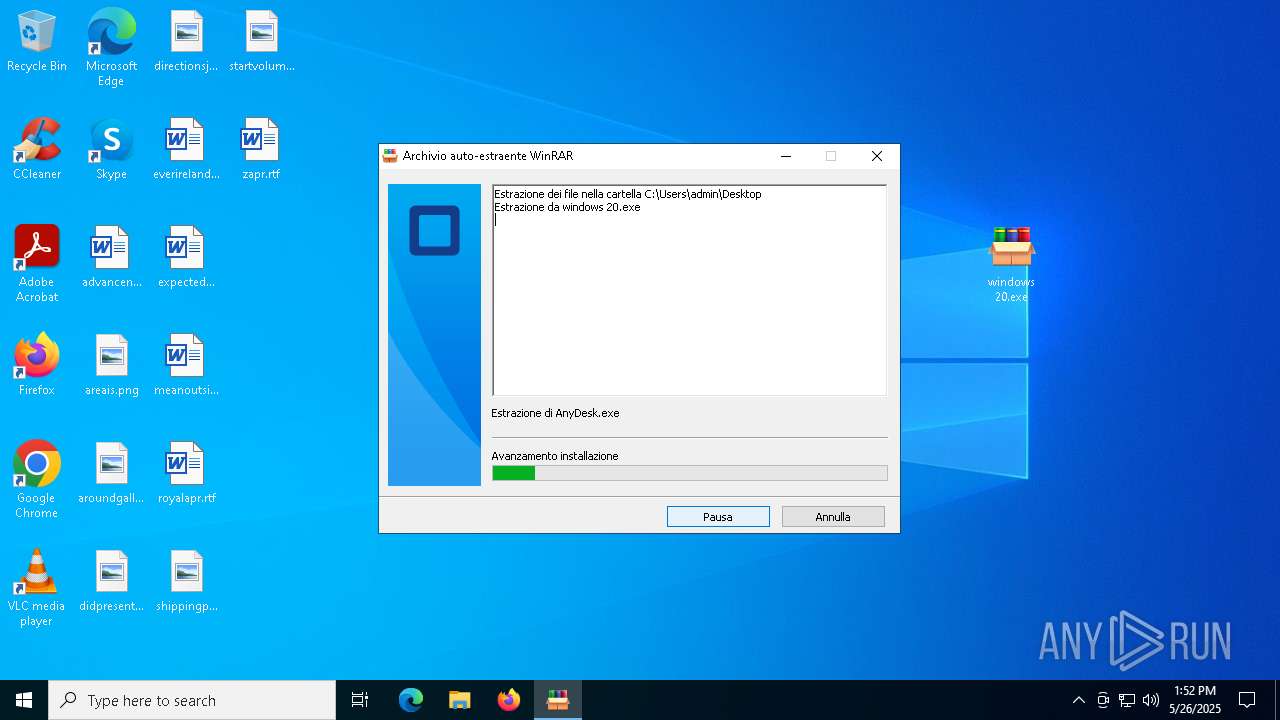
Executable content was dropped or overwritten
- TeamViewer_Setup.exe (PID: 7216)
- windows 20.exe (PID: 7020)
- TeamViewer_.exe (PID: 6028)
- TeamViewer_.exe (PID: 7644)
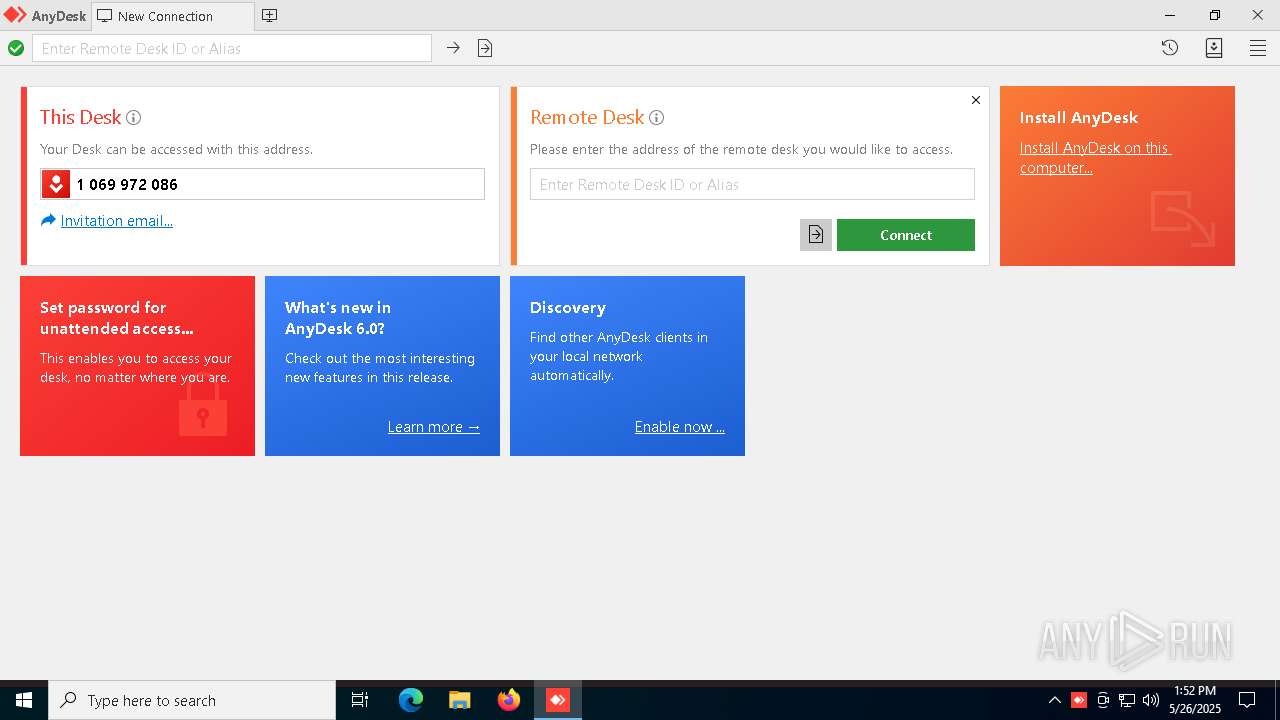
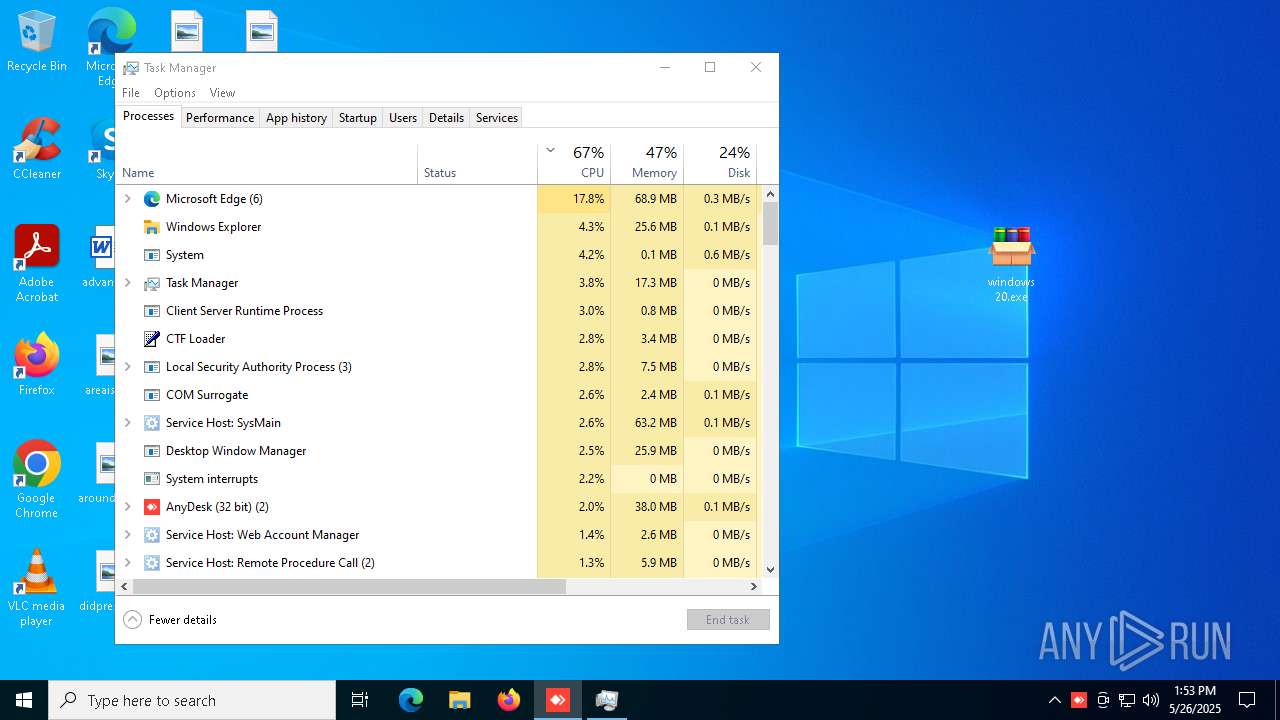
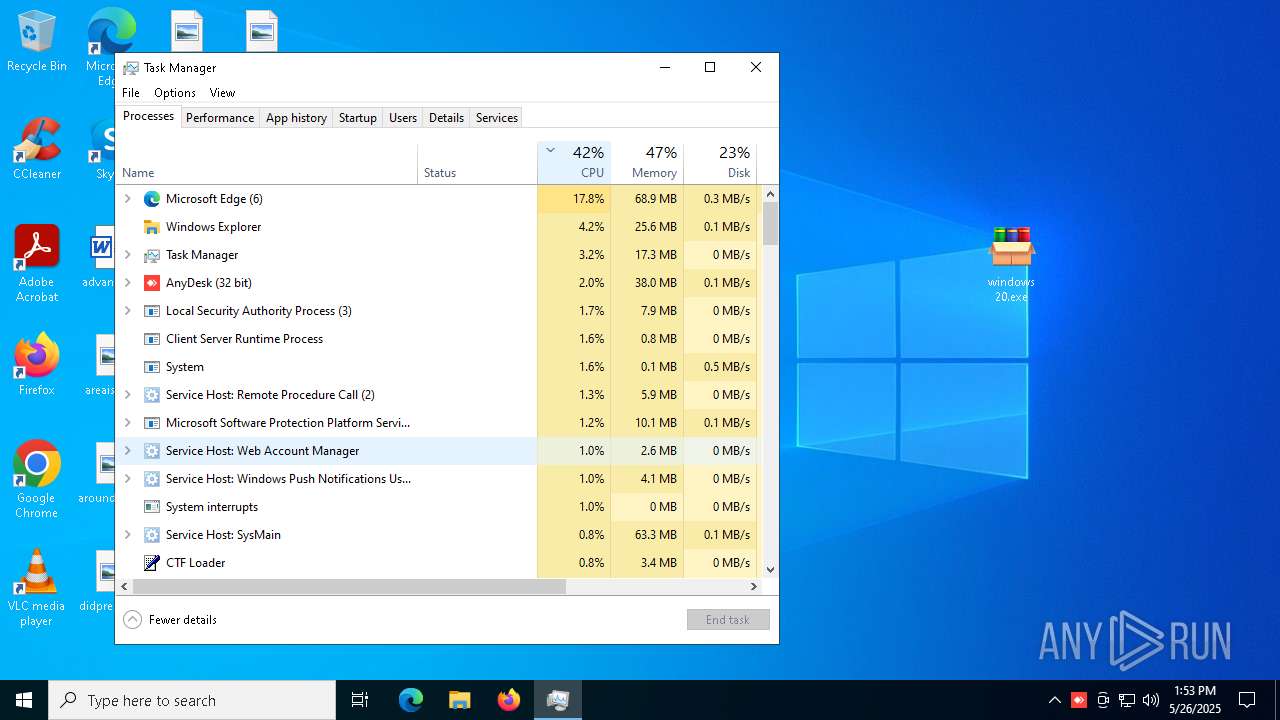
ANYDESK mutex has been found
- AnyDesk.exe (PID: 8036)
- AnyDesk.exe (PID: 7180)
- AnyDesk.exe (PID: 7244)
Reads Microsoft Outlook installation path
- windows 20.exe (PID: 7020)
Reads security settings of Internet Explorer
- windows 20.exe (PID: 7020)
- TeamViewer_.exe (PID: 7644)
- TeamViewer.exe (PID: 5956)
Reads Internet Explorer settings
- windows 20.exe (PID: 7020)
Application launched itself
- AnyDesk.exe (PID: 8036)
- TeamViewer_.exe (PID: 6028)
- TeamViewer.exe (PID: 5956)
The process creates files with name similar to system file names
- TeamViewer_.exe (PID: 6028)
- TeamViewer_.exe (PID: 7644)
Malware-specific behavior (creating "System.dll" in Temp)
- TeamViewer_.exe (PID: 6028)
- TeamViewer_.exe (PID: 7644)
Process drops legitimate windows executable
- TeamViewer_.exe (PID: 7644)
Drops 7-zip archiver for unpacking
- TeamViewer_.exe (PID: 7644)
Potential Corporate Privacy Violation
- TeamViewer.exe (PID: 8080)
Connects to unusual port
- TeamViewer.exe (PID: 8080)
INFO
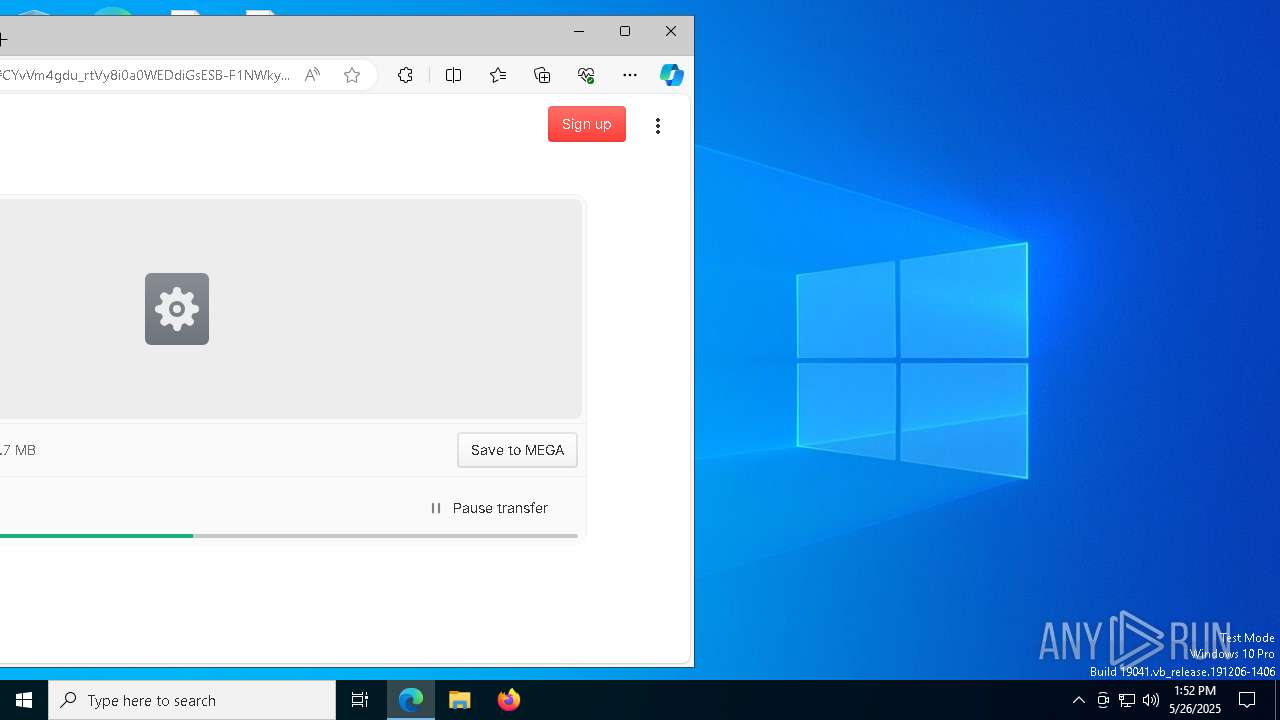
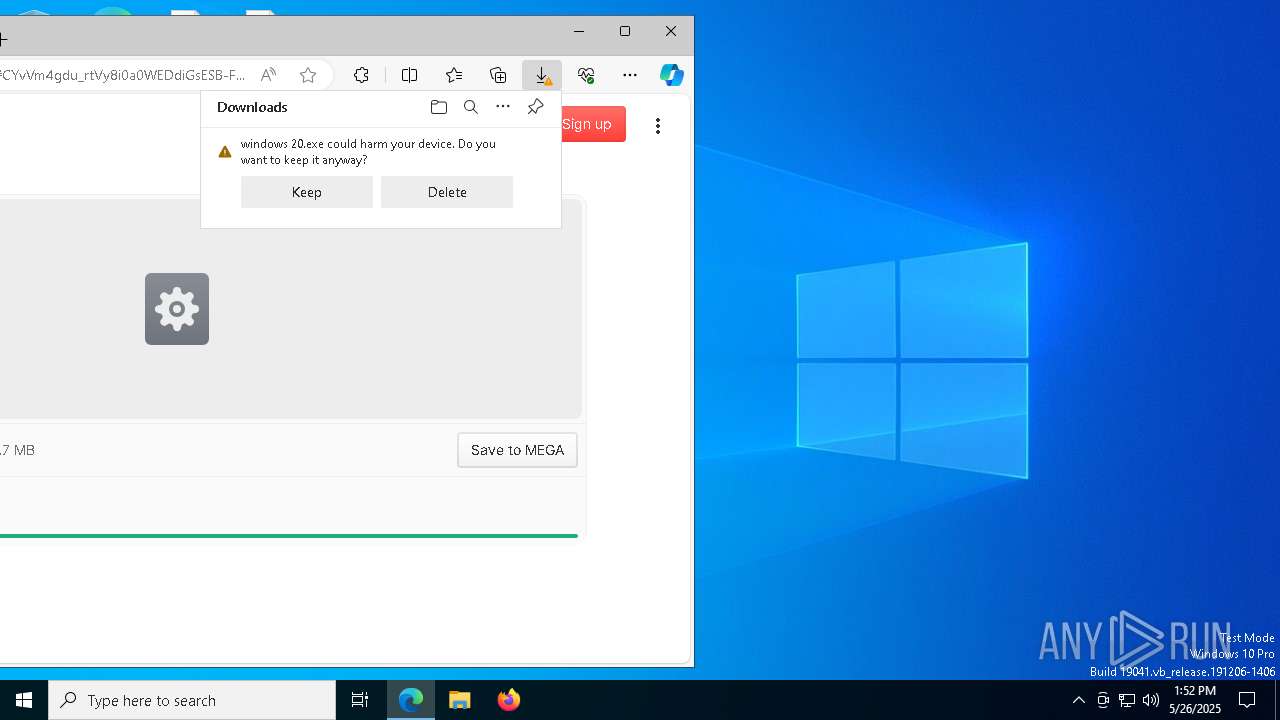
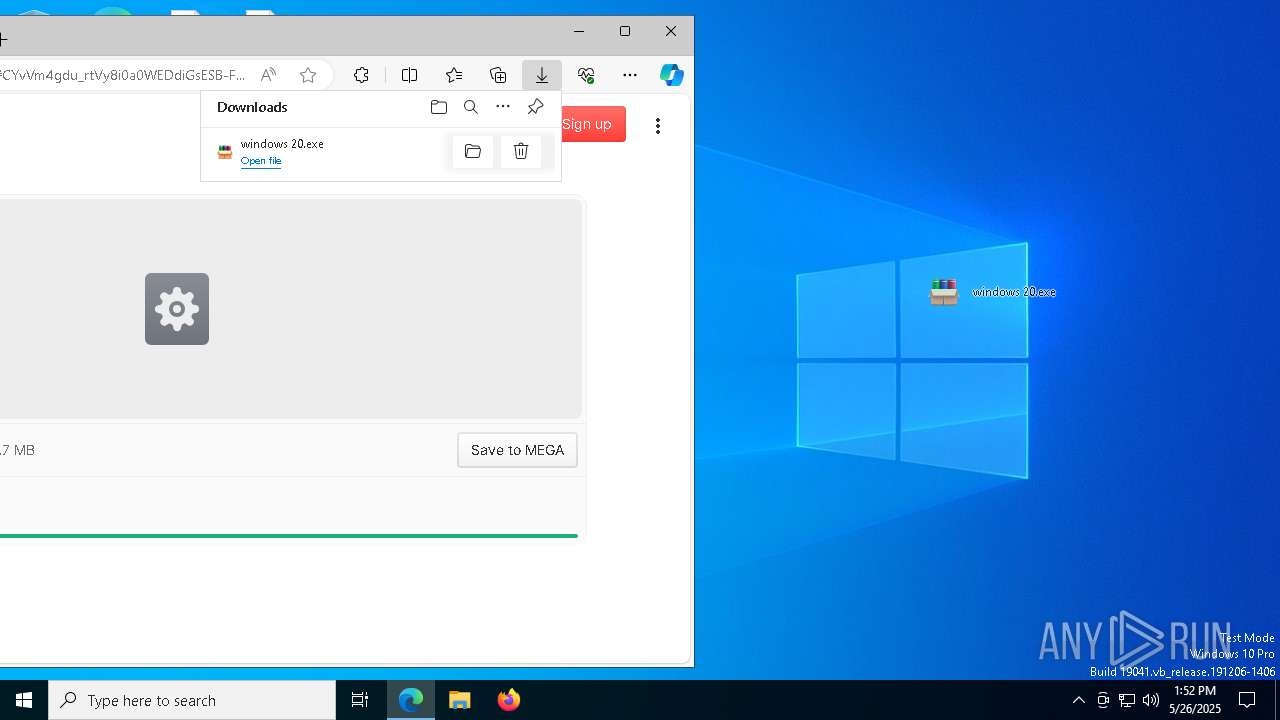
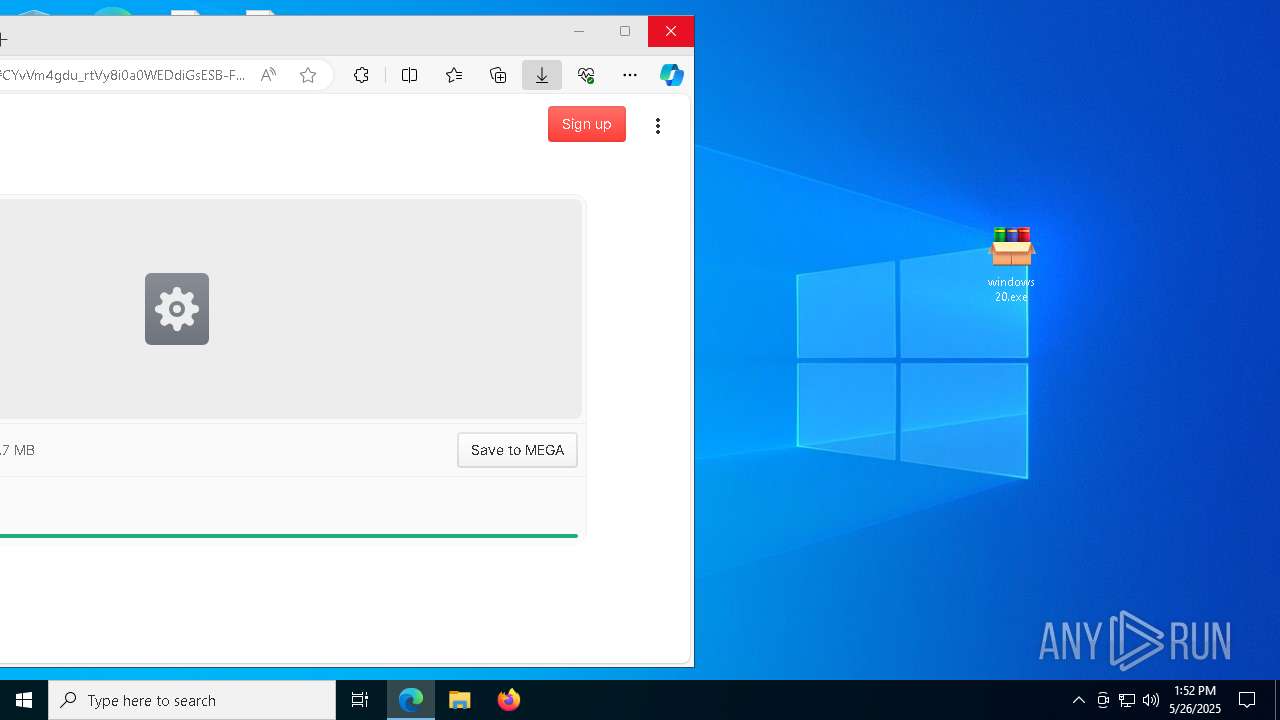
Launch of the file from Downloads directory
- msedge.exe (PID: 3100)
- msedge.exe (PID: 1116)
Application launched itself
- msedge.exe (PID: 3100)
- msedge.exe (PID: 2772)
- msedge.exe (PID: 5868)
Executable content was dropped or overwritten
- msedge.exe (PID: 3100)
Reads the computer name
- identity_helper.exe (PID: 7736)
- identity_helper.exe (PID: 5228)
- AnyDesk.exe (PID: 8036)
- windows 20.exe (PID: 7020)
- AnyDesk.exe (PID: 7244)
- TeamViewer_.exe (PID: 6028)
- AnyDesk.exe (PID: 7180)
- TeamViewer_.exe (PID: 7644)
- TeamViewer.exe (PID: 5956)
Reads Environment values
- identity_helper.exe (PID: 7736)
- identity_helper.exe (PID: 5228)
Checks supported languages
- identity_helper.exe (PID: 7736)
- identity_helper.exe (PID: 5228)
- TeamViewer_Setup.exe (PID: 7216)
- windows 20.exe (PID: 7020)
- AnyDesk.exe (PID: 7244)
- AnyDesk.exe (PID: 8036)
- TeamViewer_.exe (PID: 6028)
- TeamViewer_.exe (PID: 7644)
- TeamViewer.exe (PID: 5956)
- AnyDesk.exe (PID: 7180)
Process checks computer location settings
- windows 20.exe (PID: 7020)
- TeamViewer_.exe (PID: 7644)
Create files in a temporary directory
- TeamViewer_Setup.exe (PID: 7216)
- TeamViewer_.exe (PID: 6028)
- TeamViewer_.exe (PID: 7644)
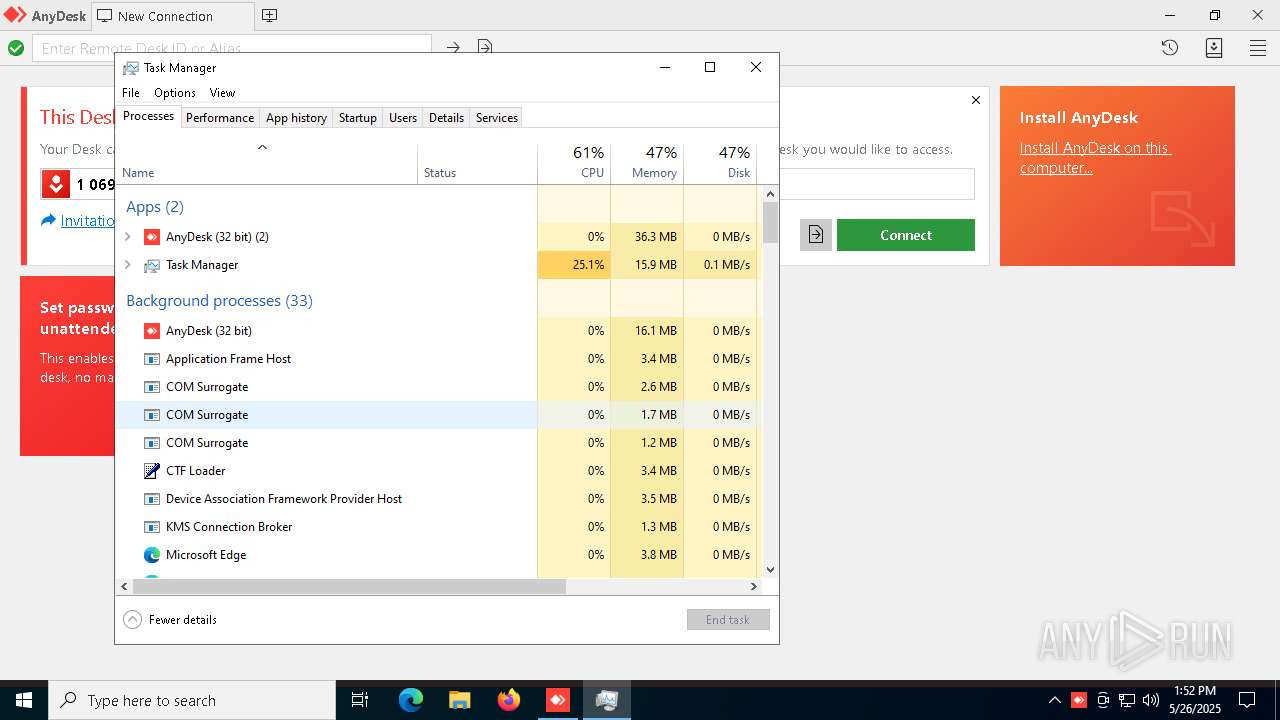
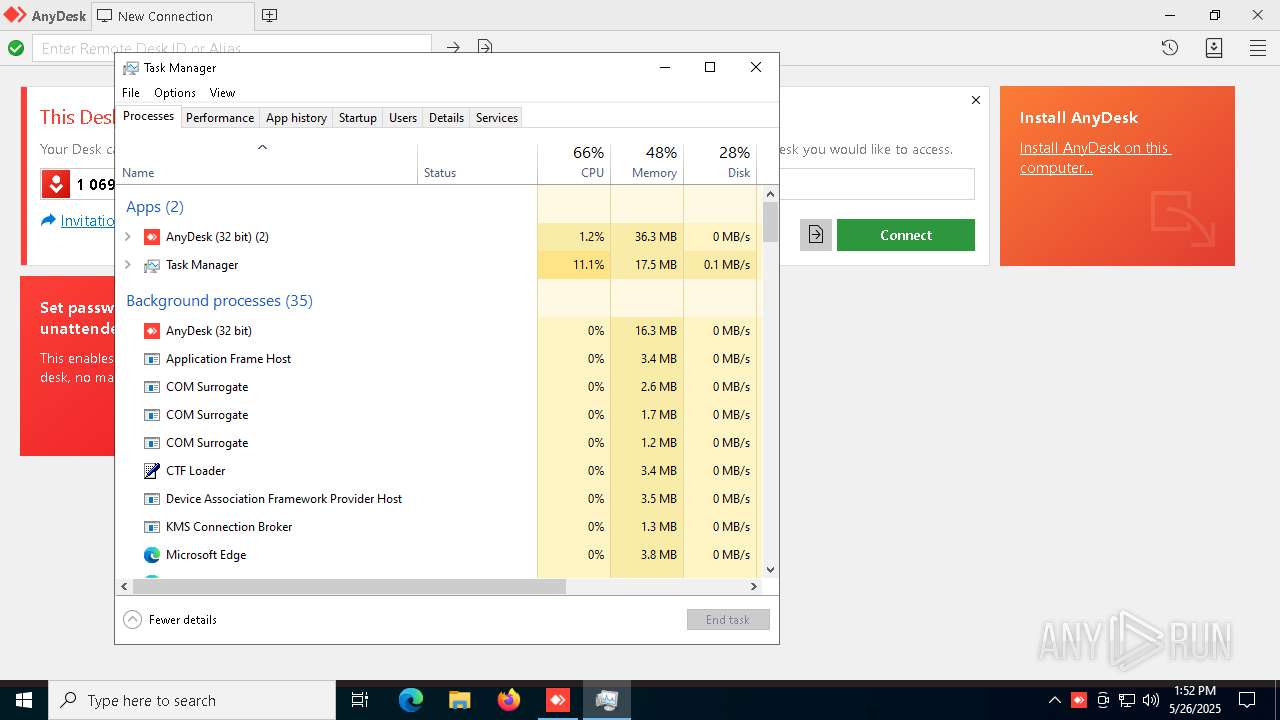
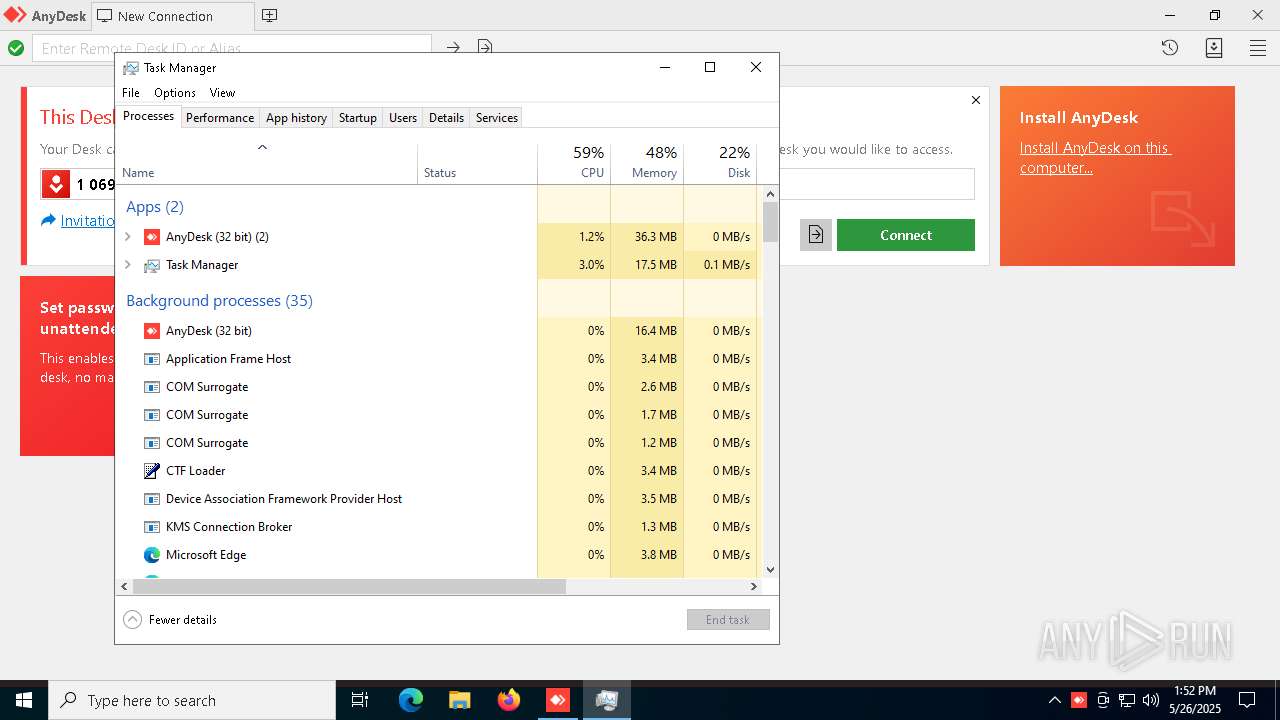
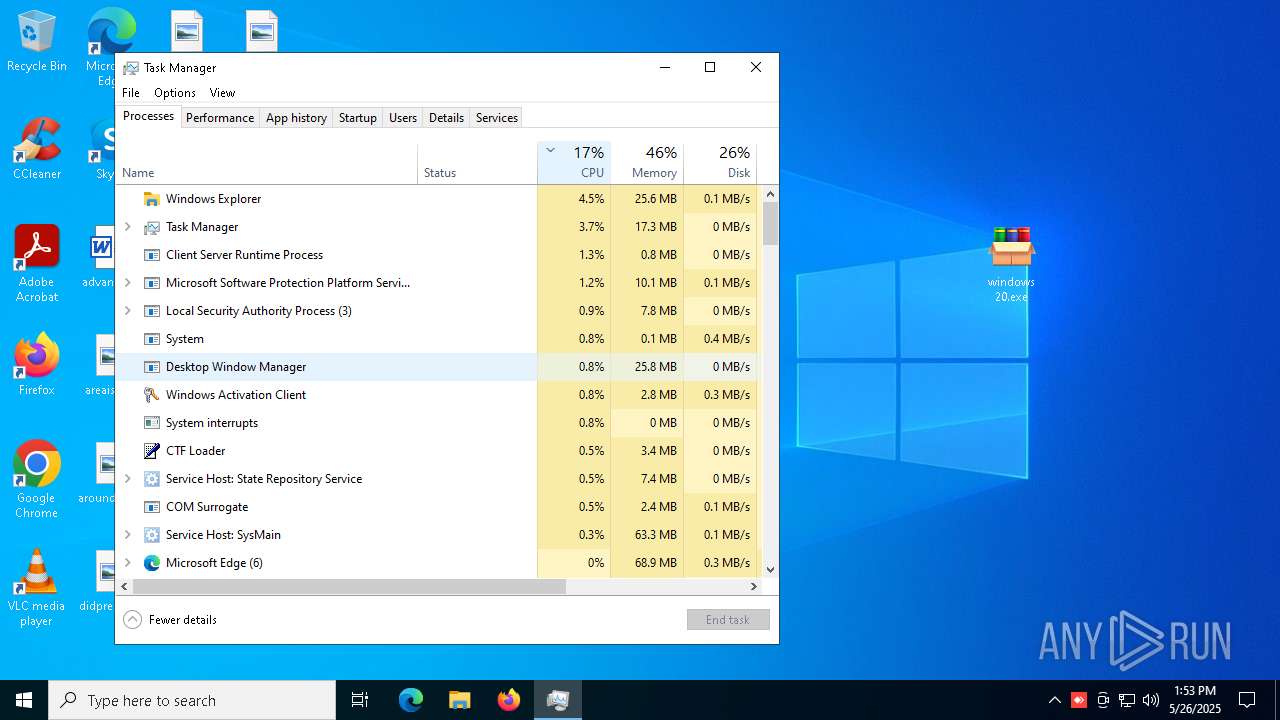
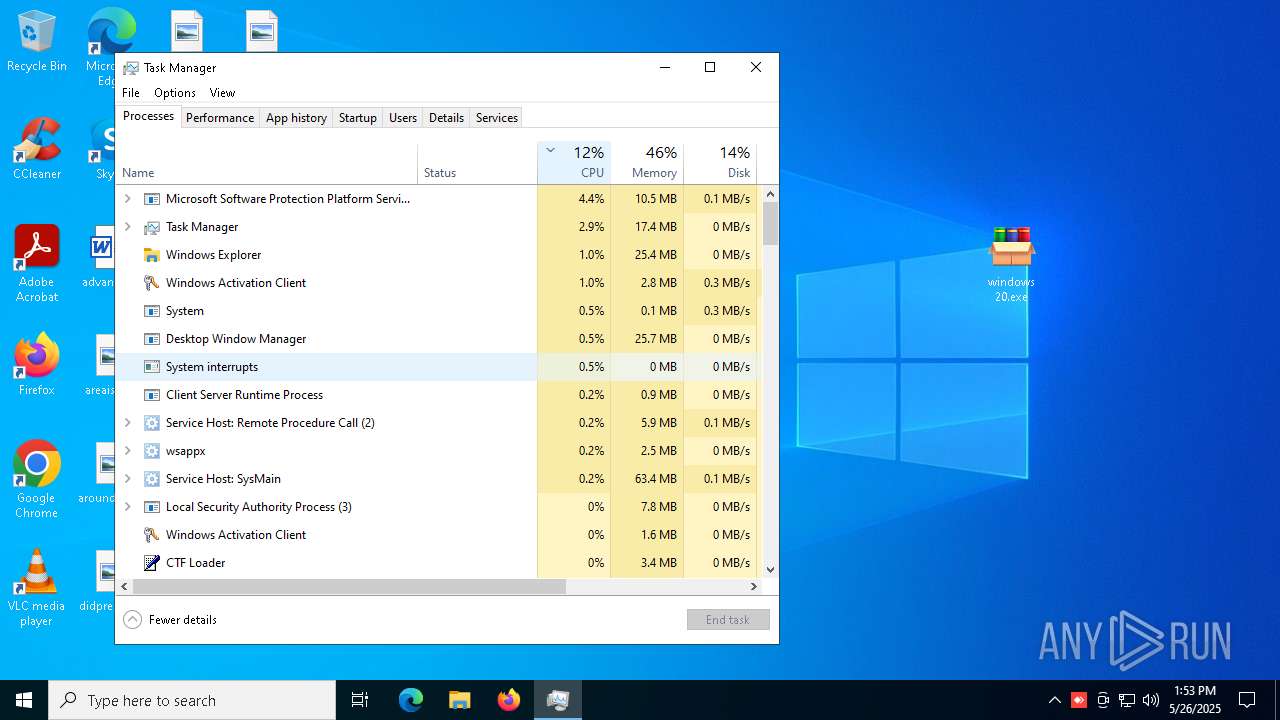
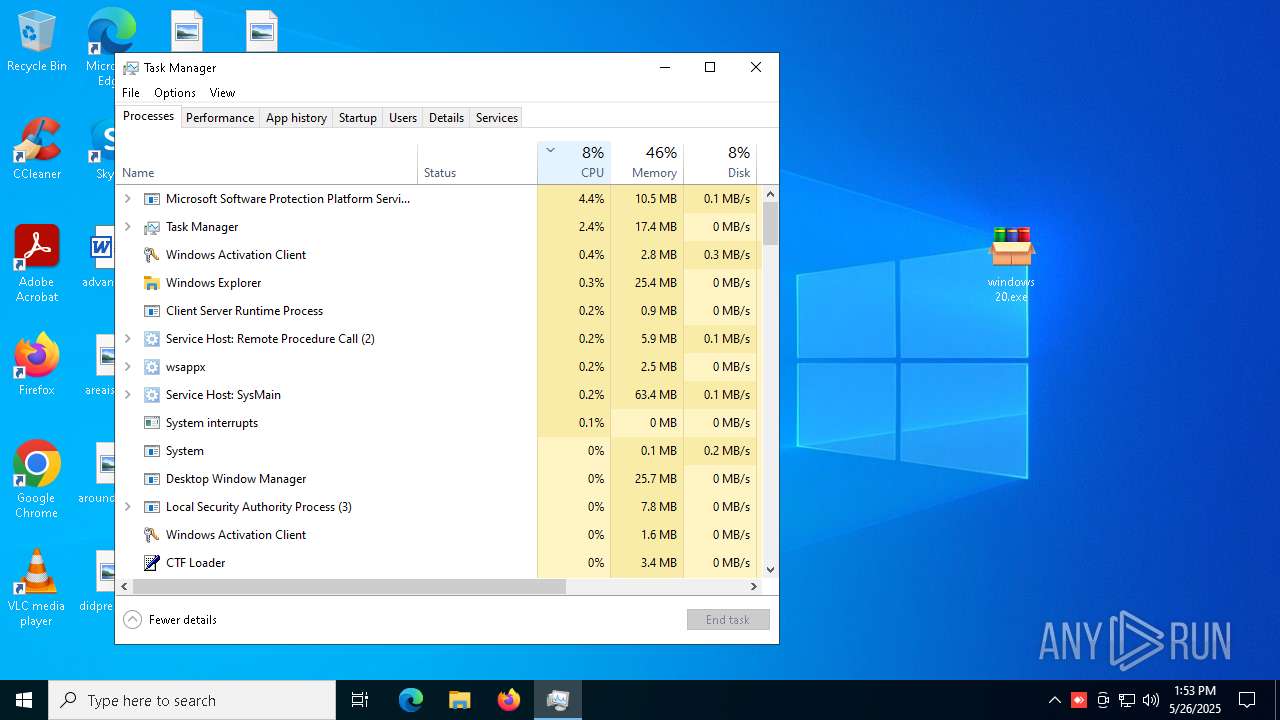
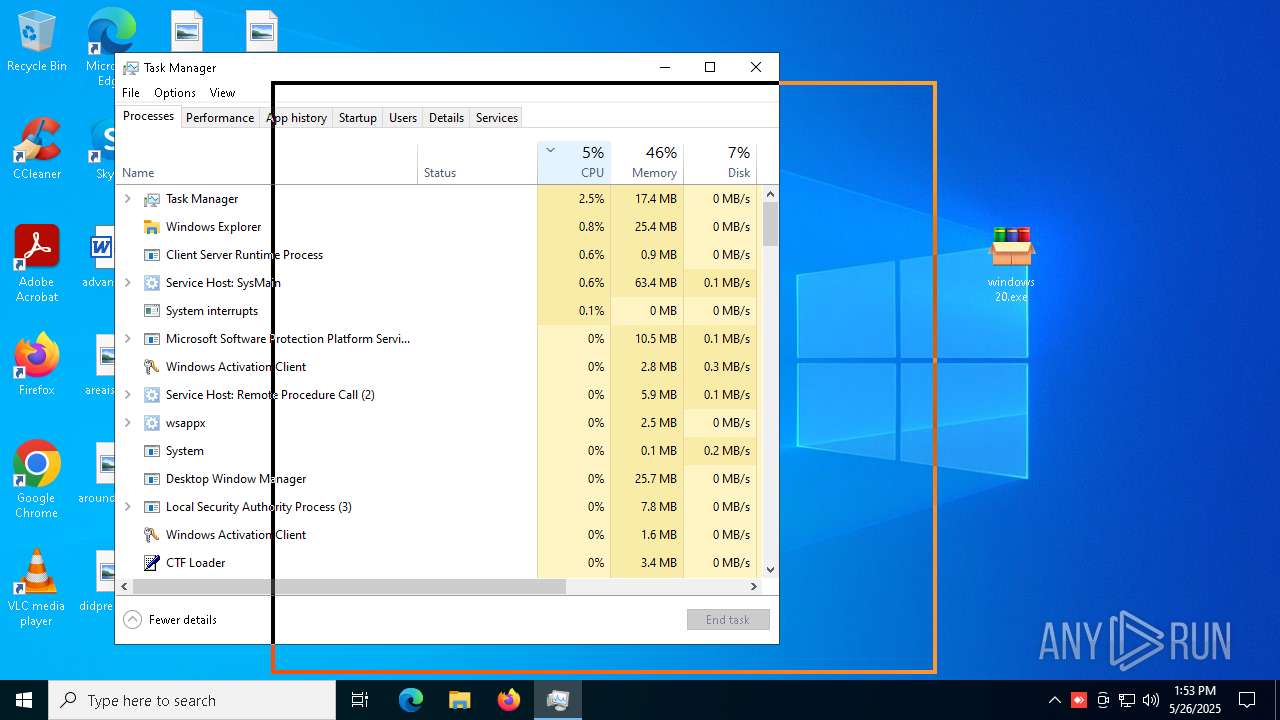
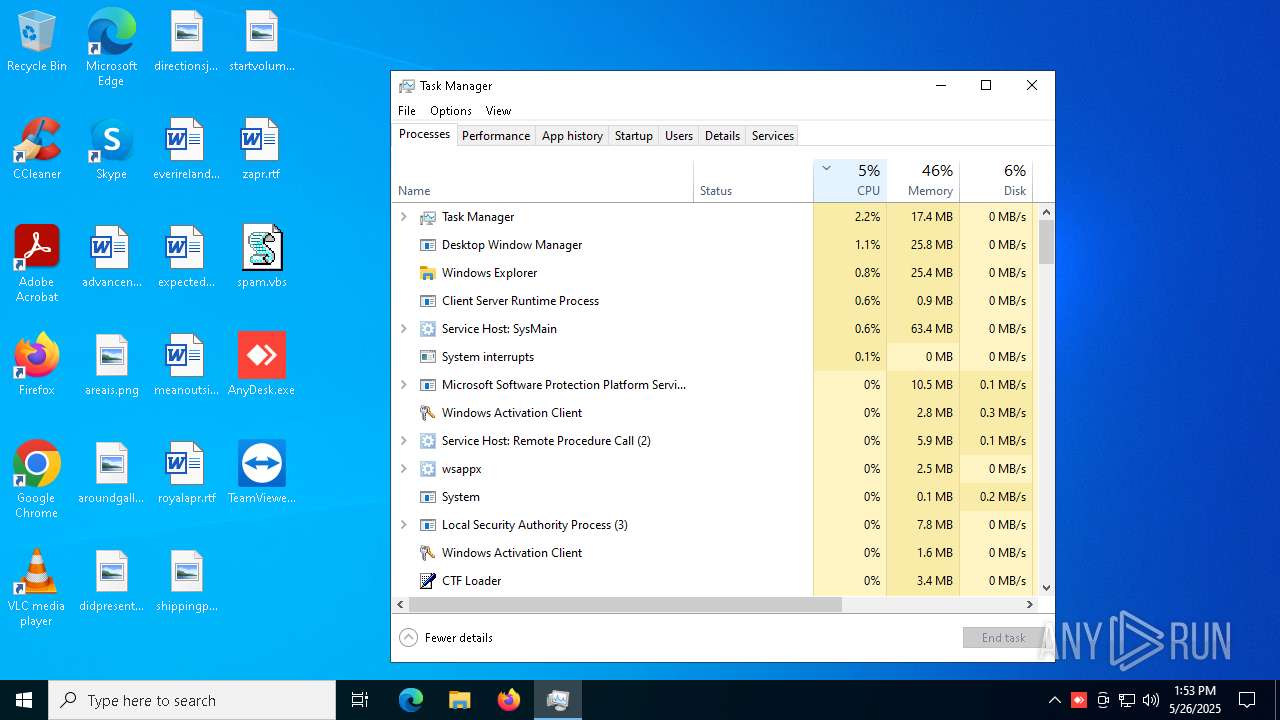
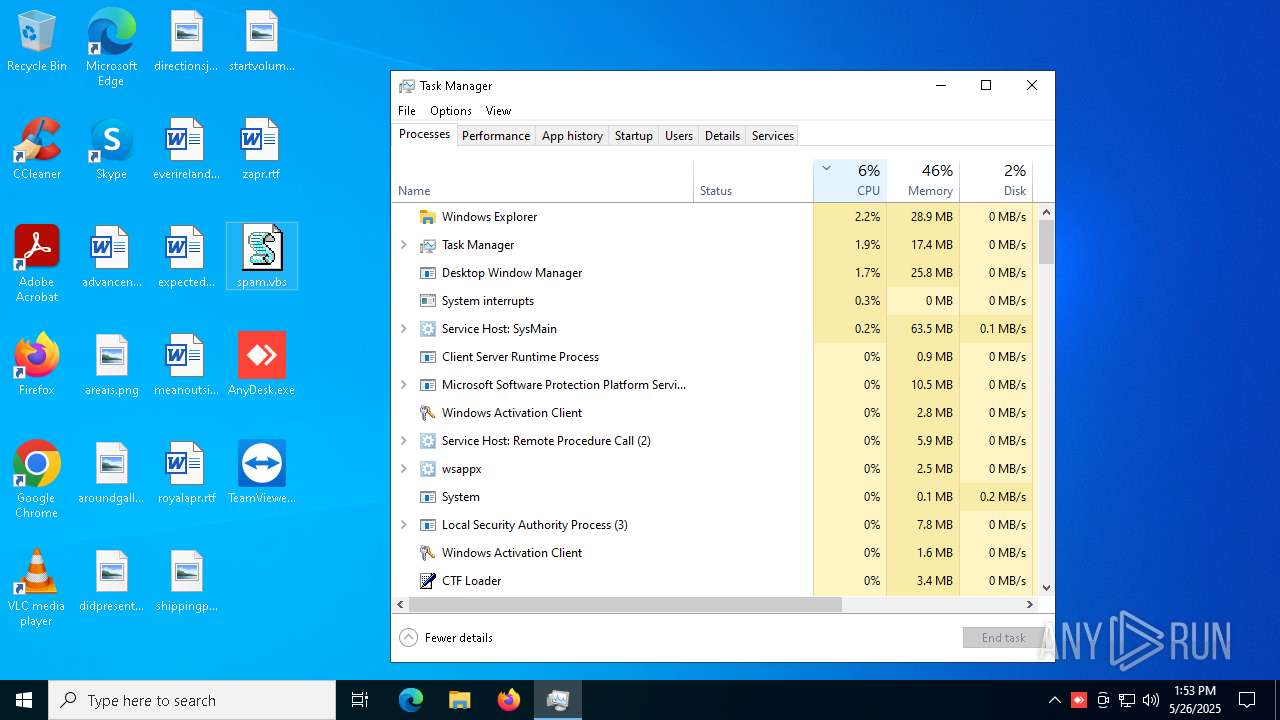
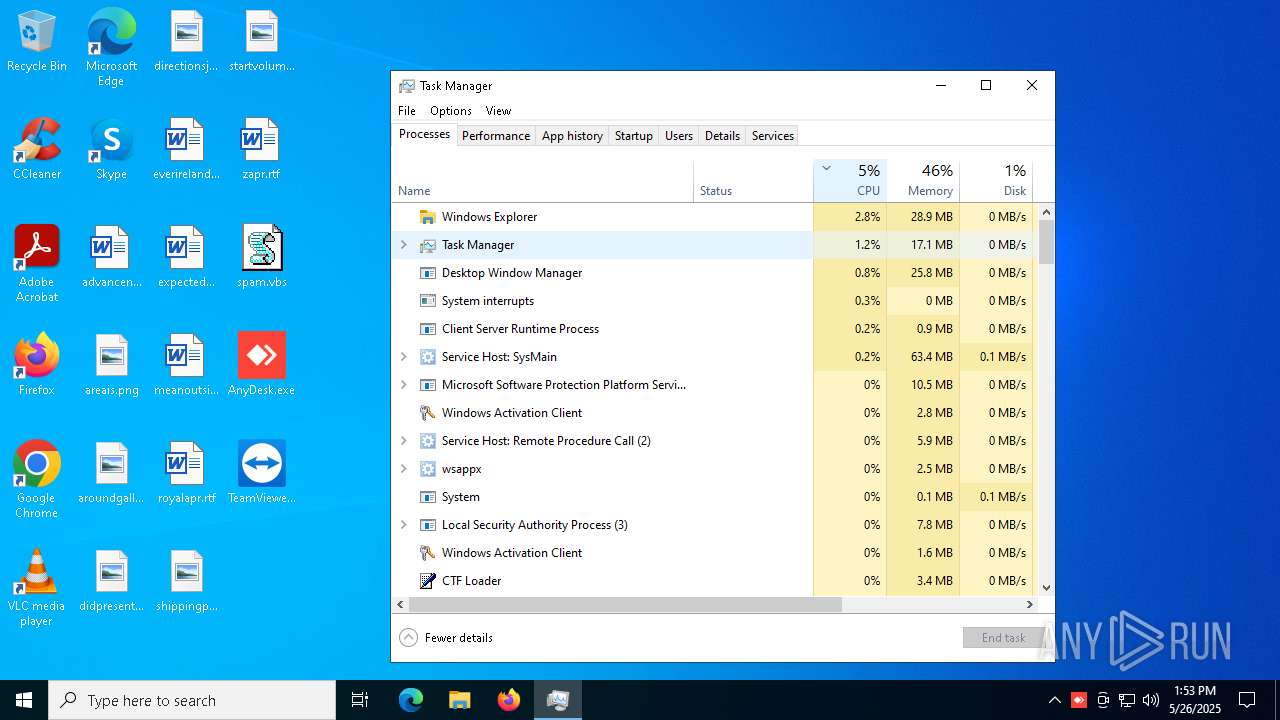
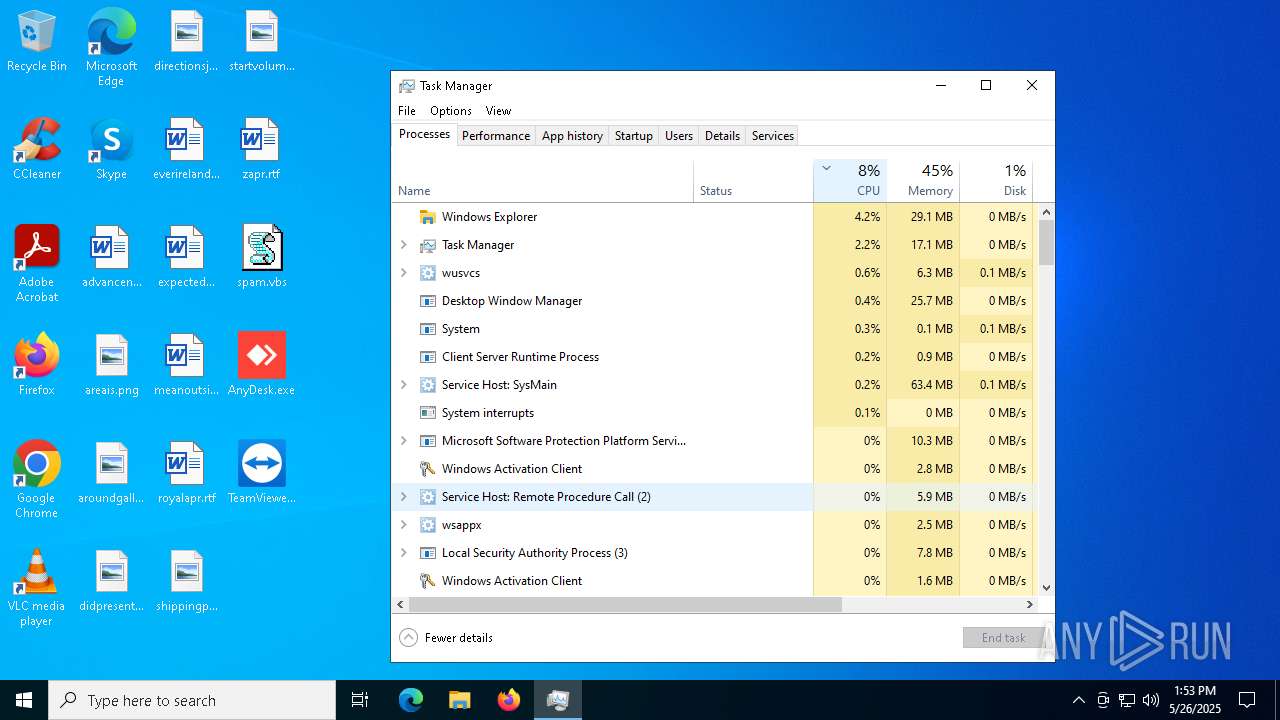
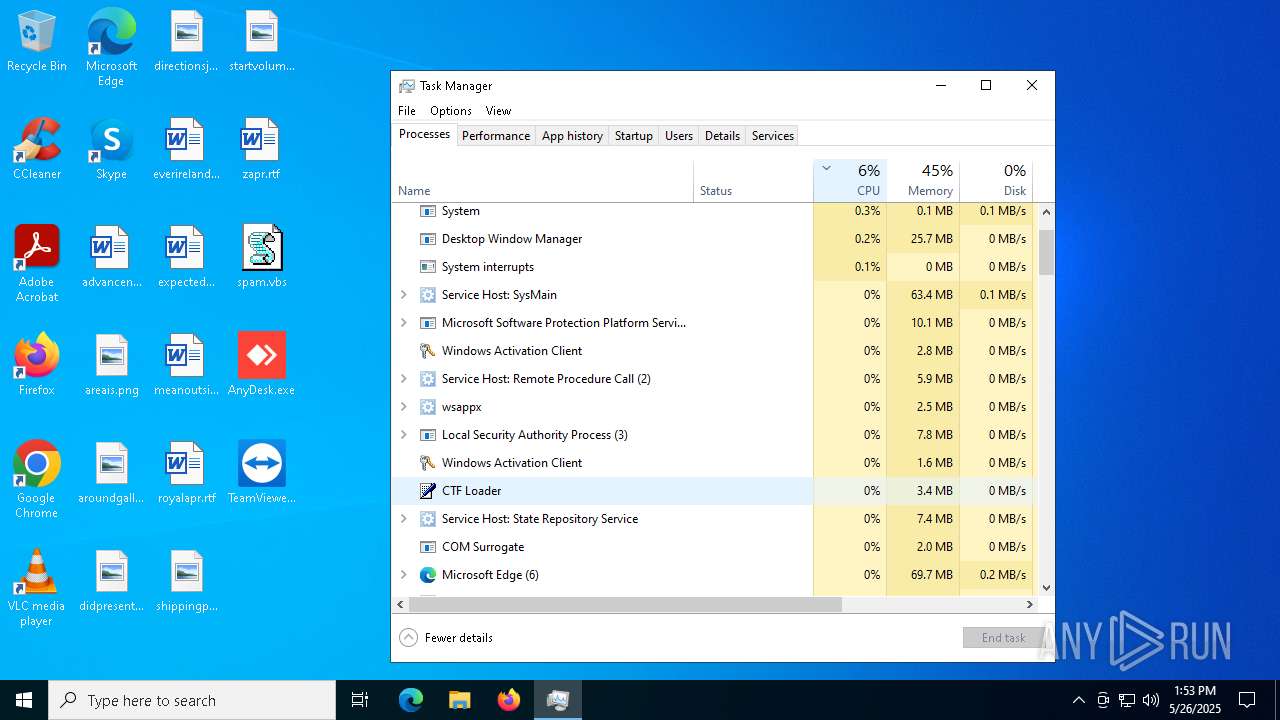
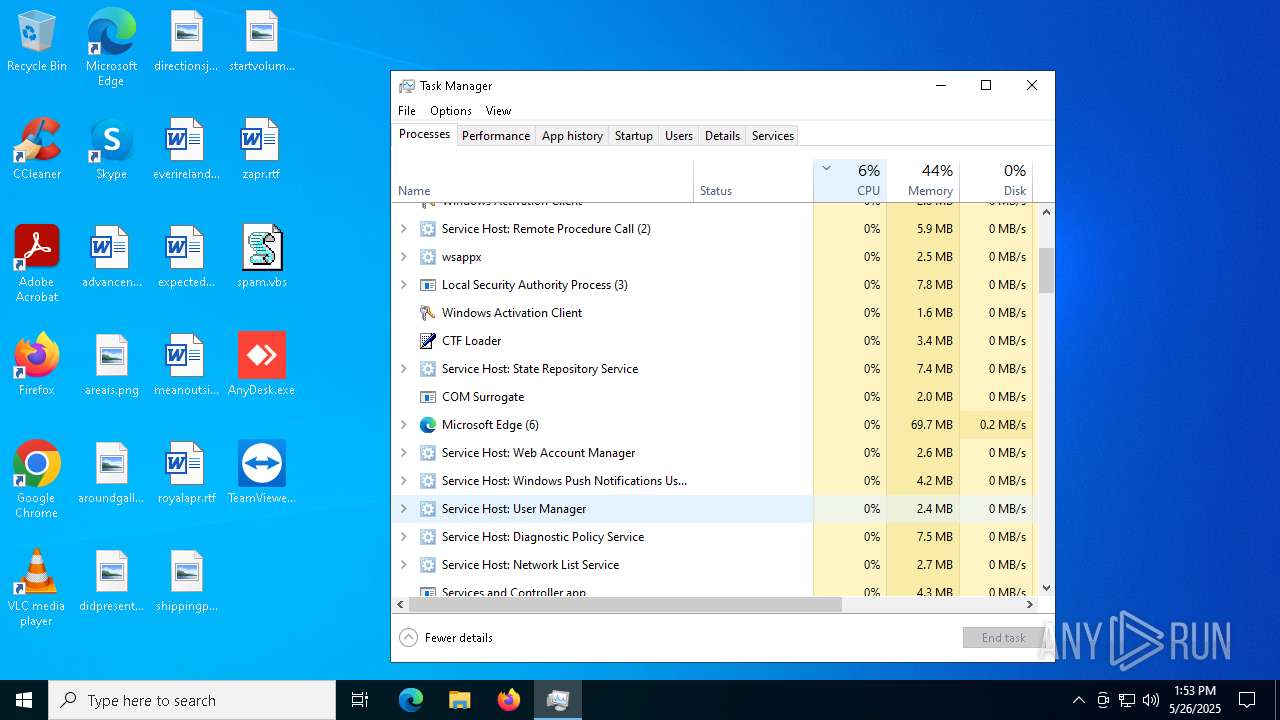
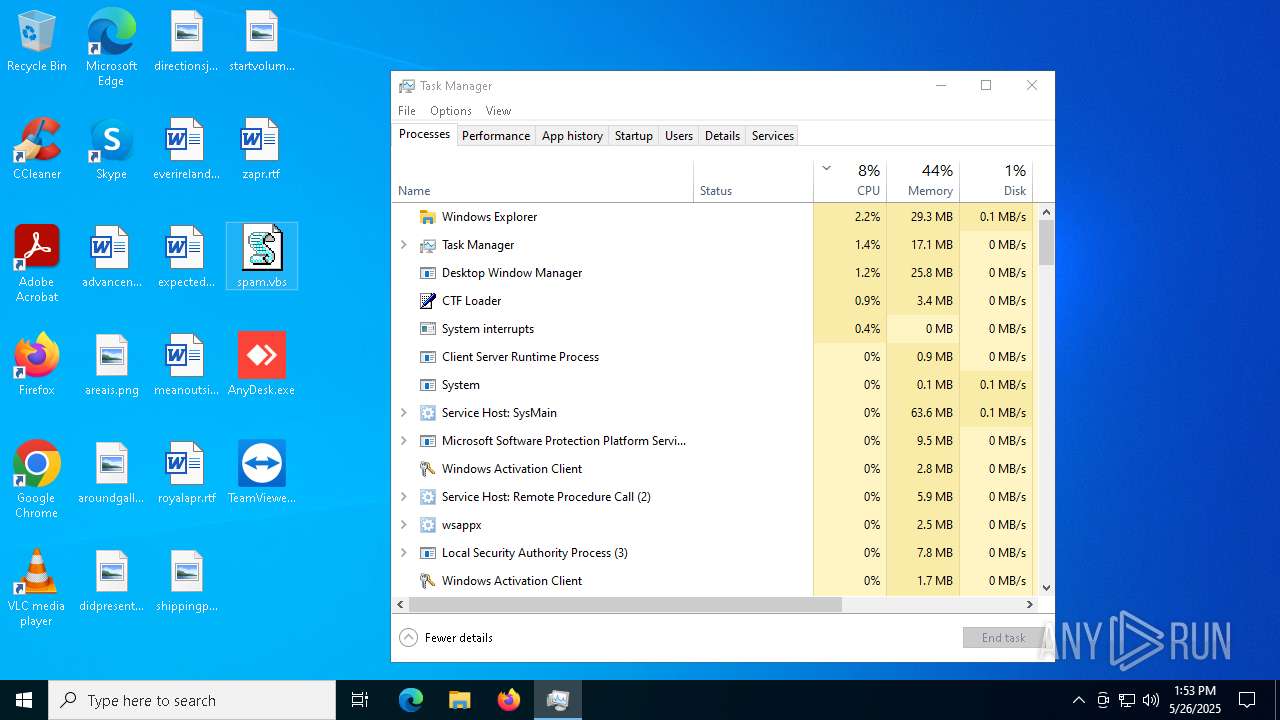
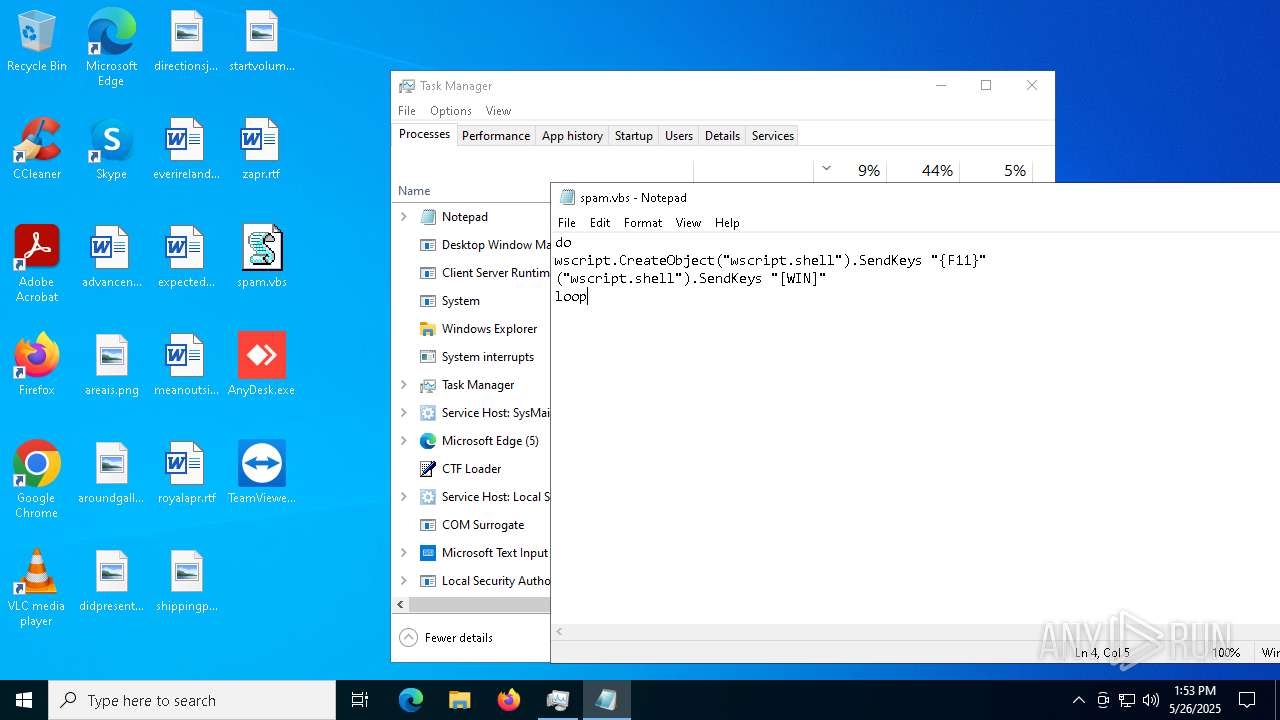
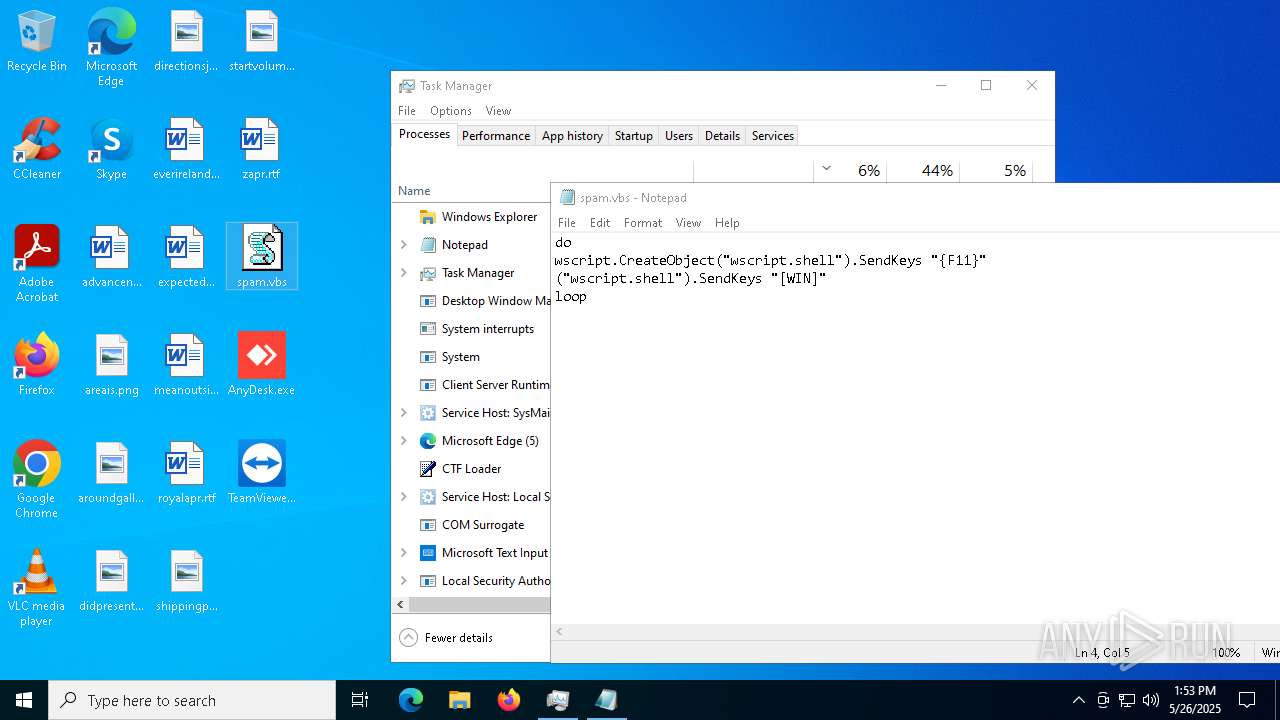
TEAMVIEWER has been detected
- TeamViewer_Setup.exe (PID: 7216)
- TeamViewer_.exe (PID: 6028)
- TeamViewer_.exe (PID: 7644)
- TeamViewer.exe (PID: 5956)
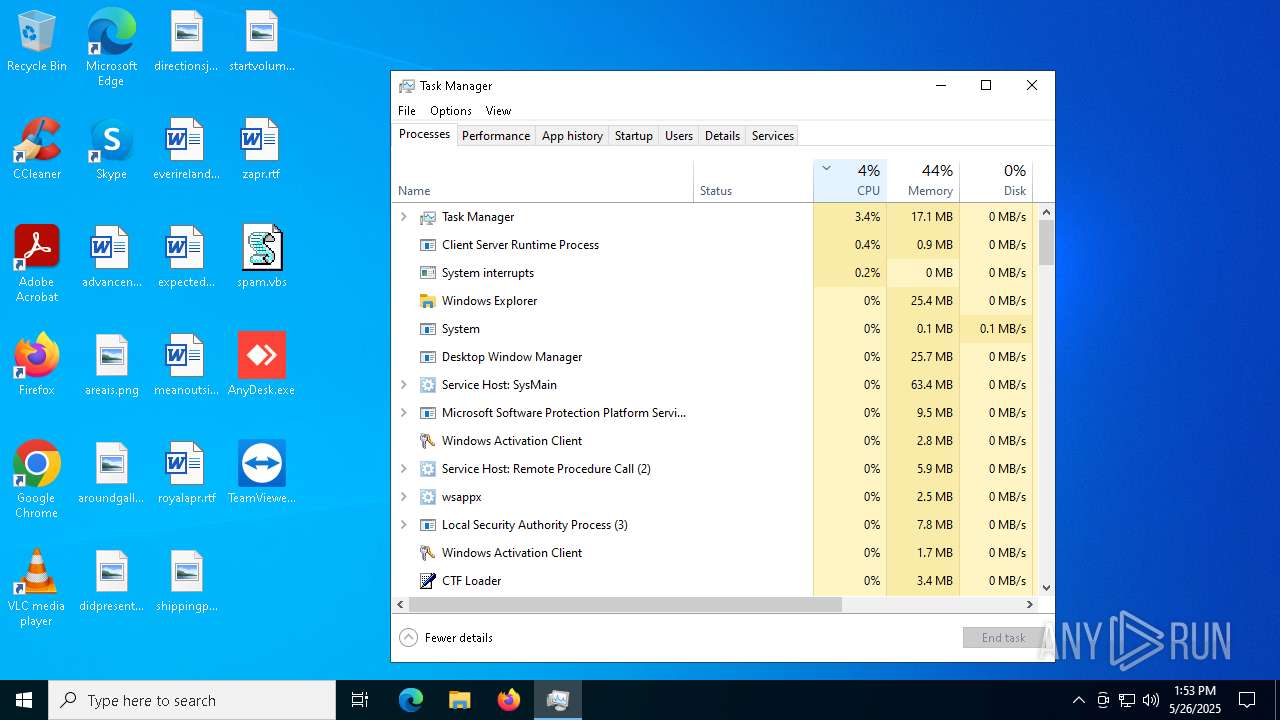
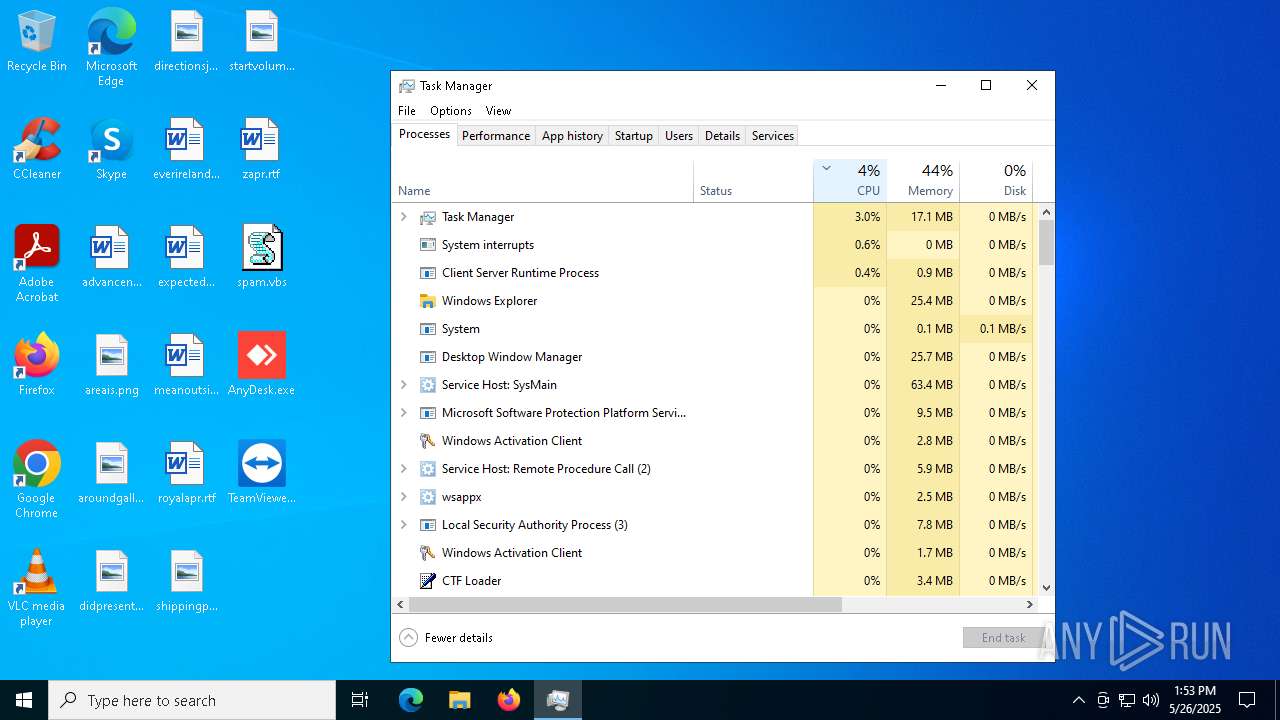
- Taskmgr.exe (PID: 8140)
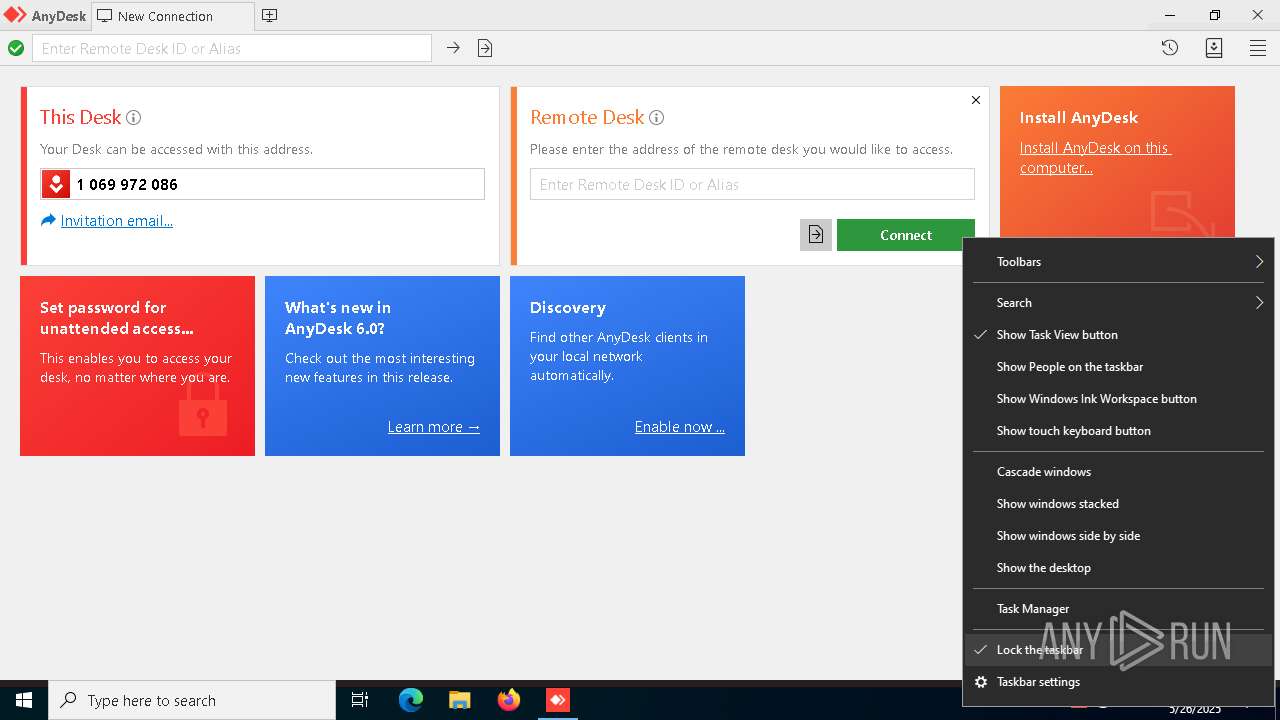
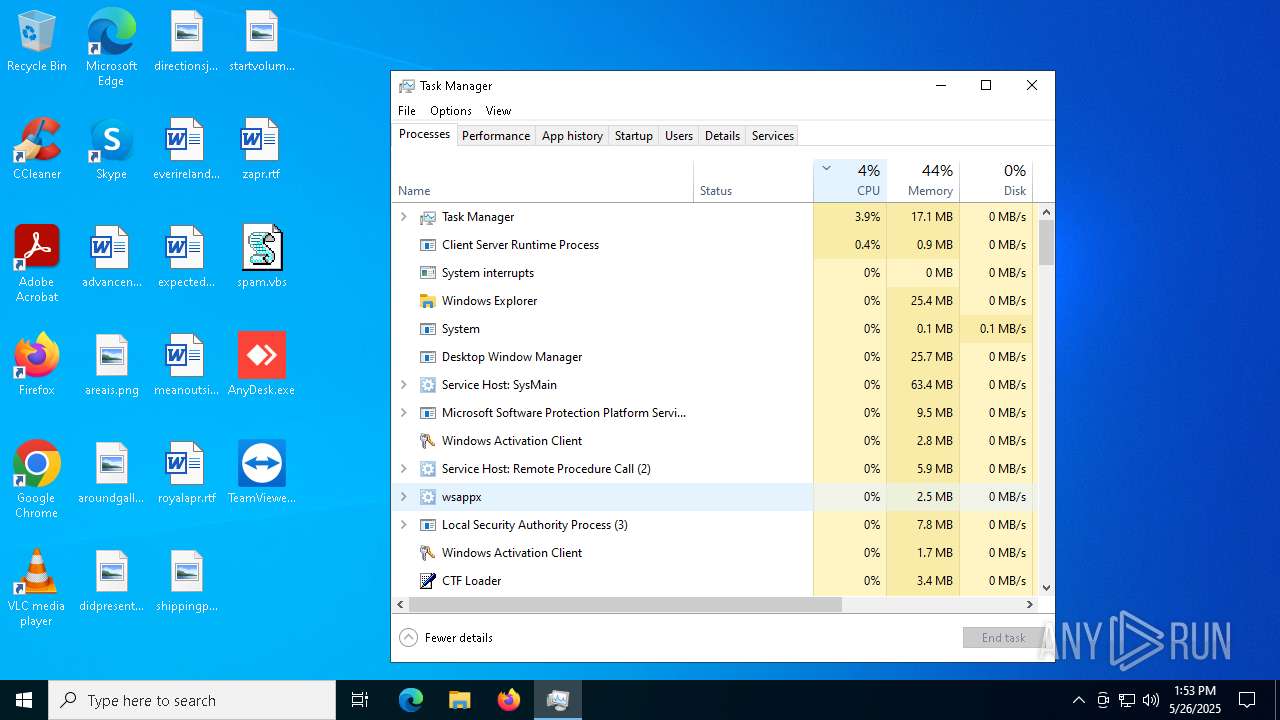
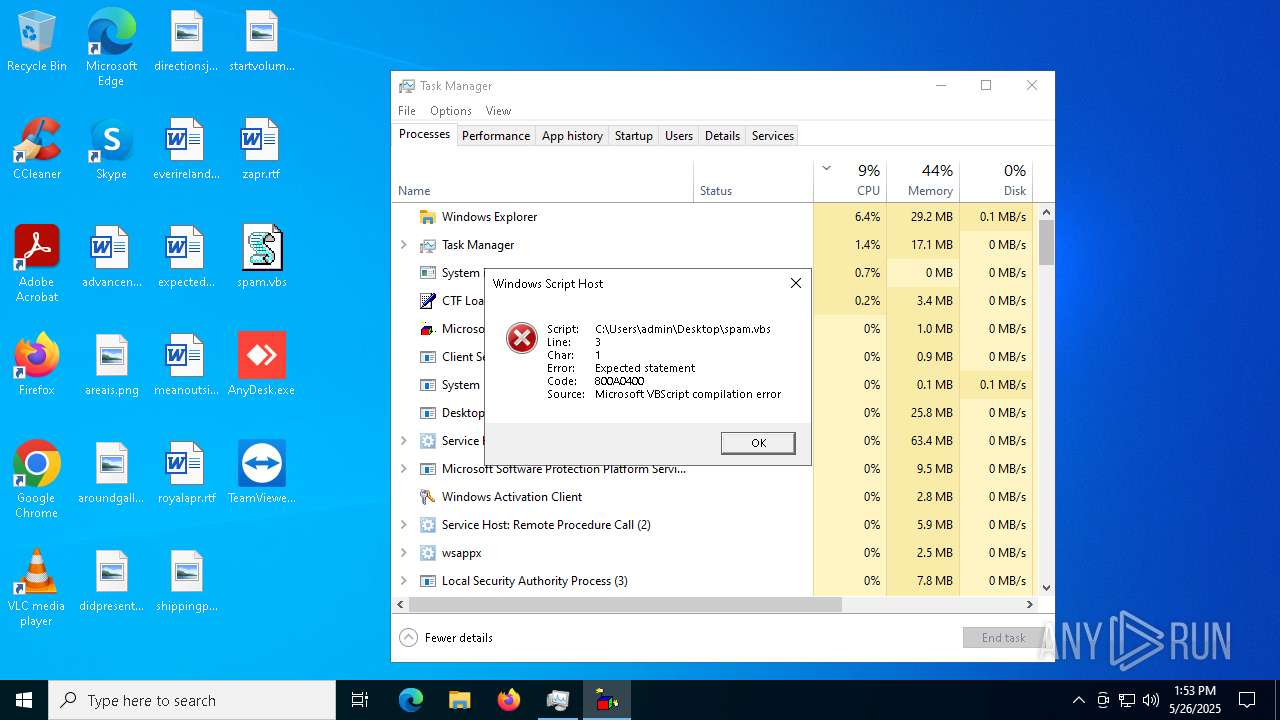
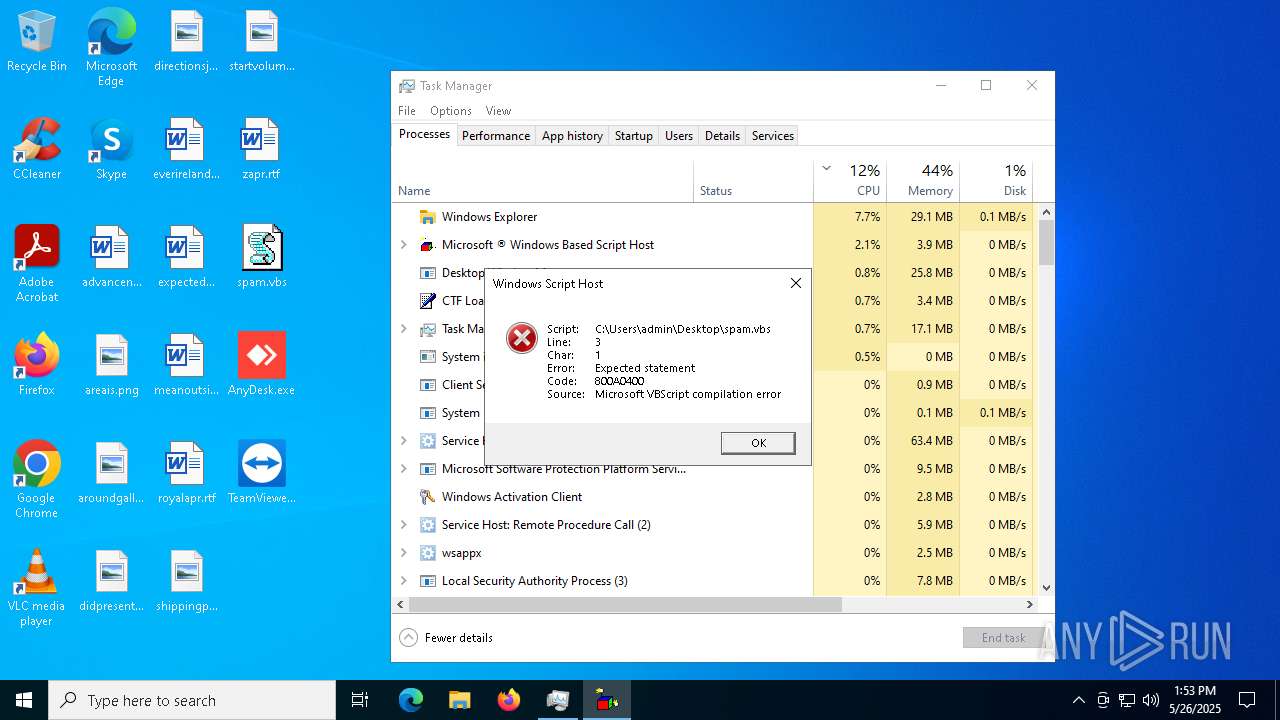
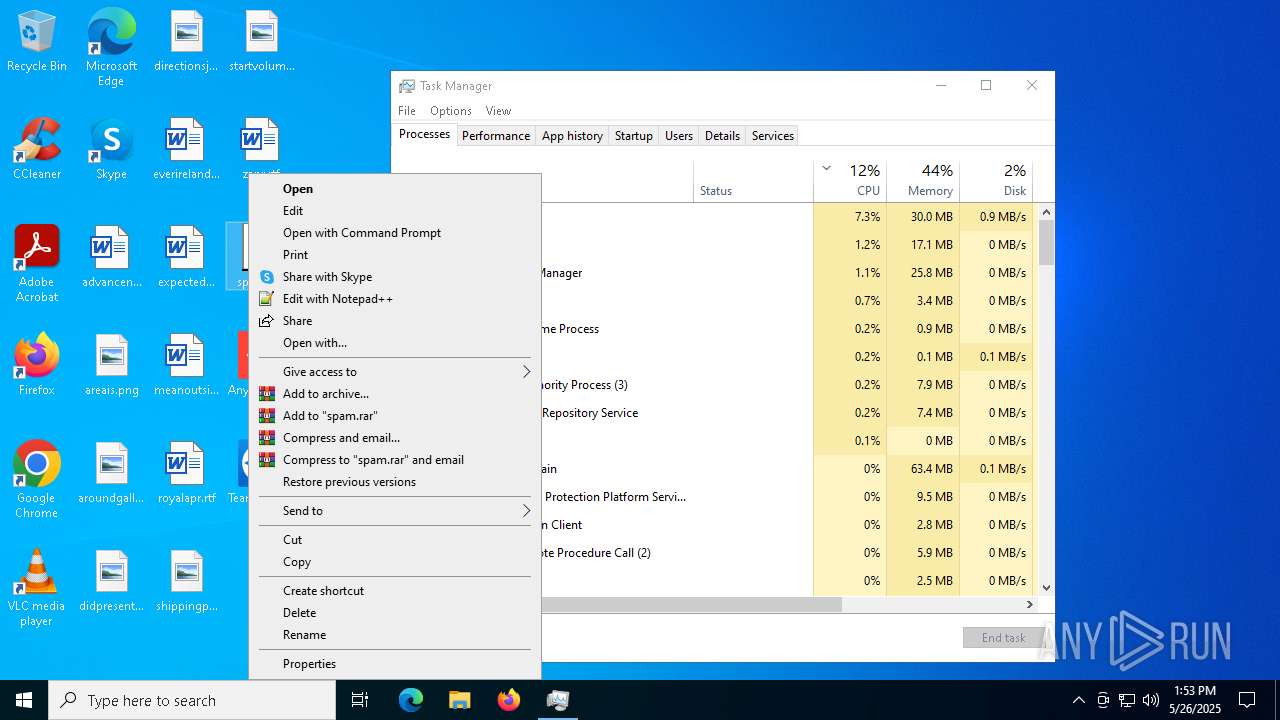
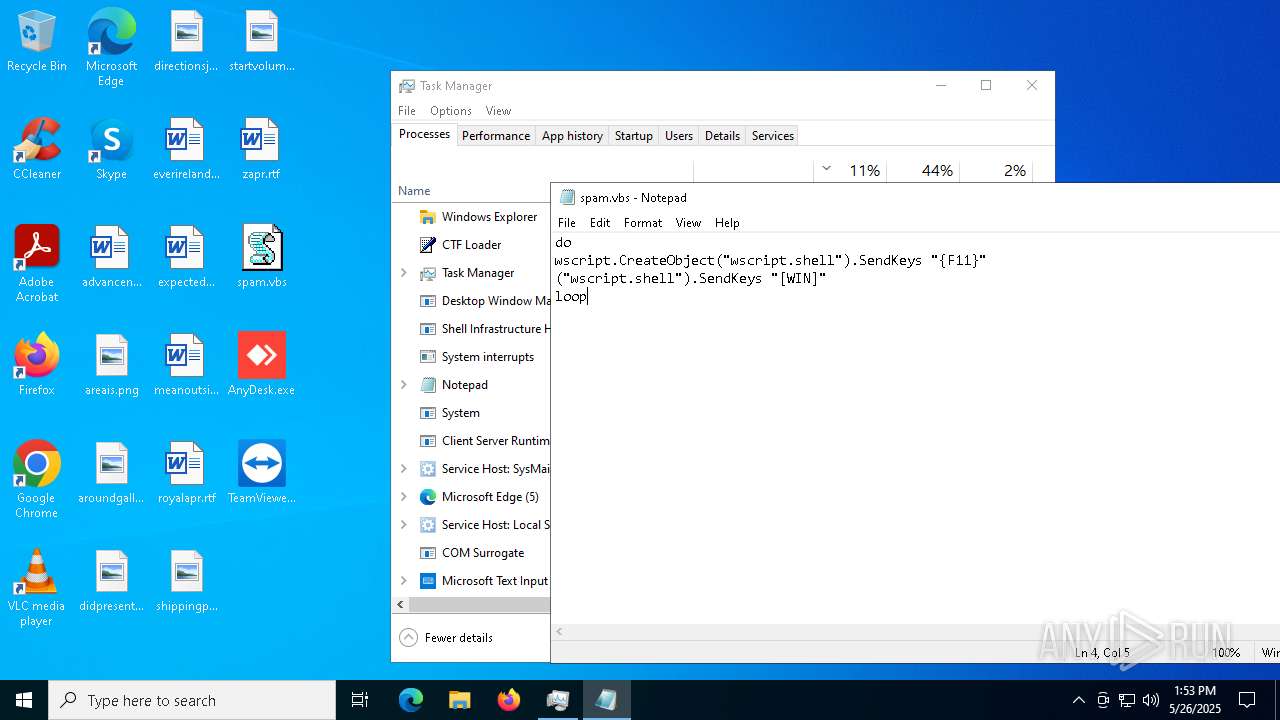
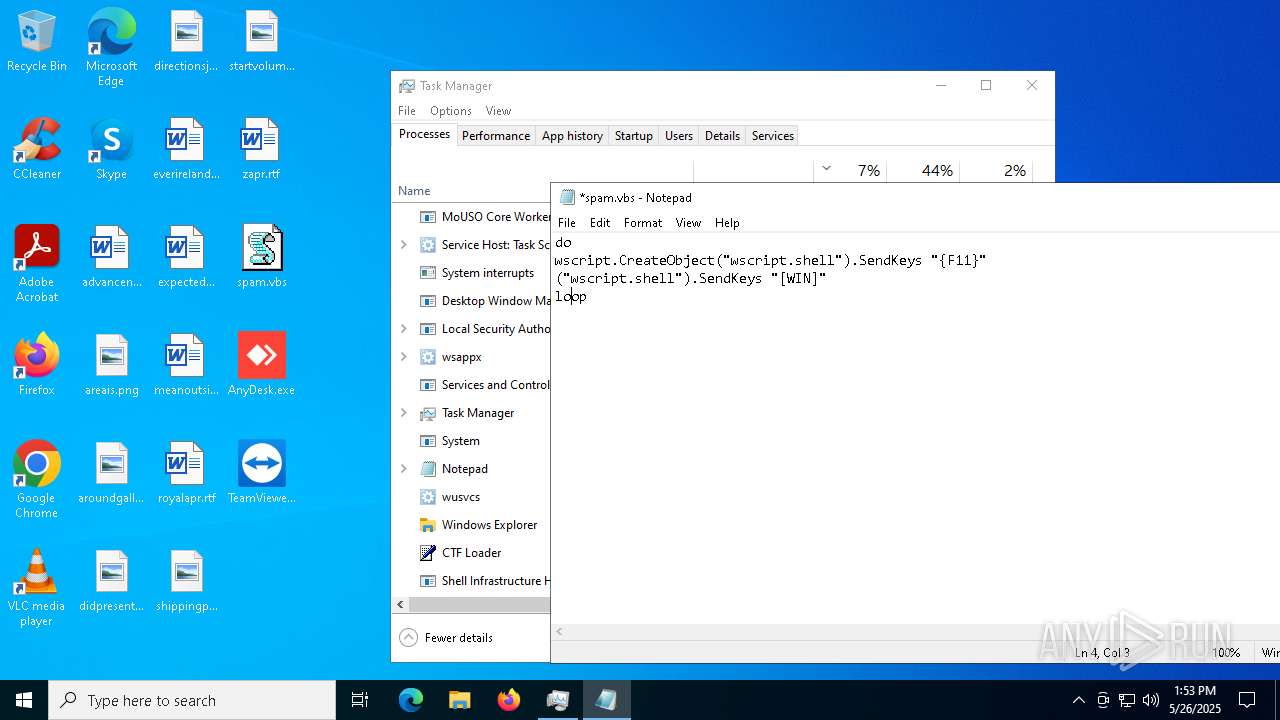
Manual execution by a user
- windows 20.exe (PID: 7020)
- Taskmgr.exe (PID: 6036)
- Taskmgr.exe (PID: 8140)
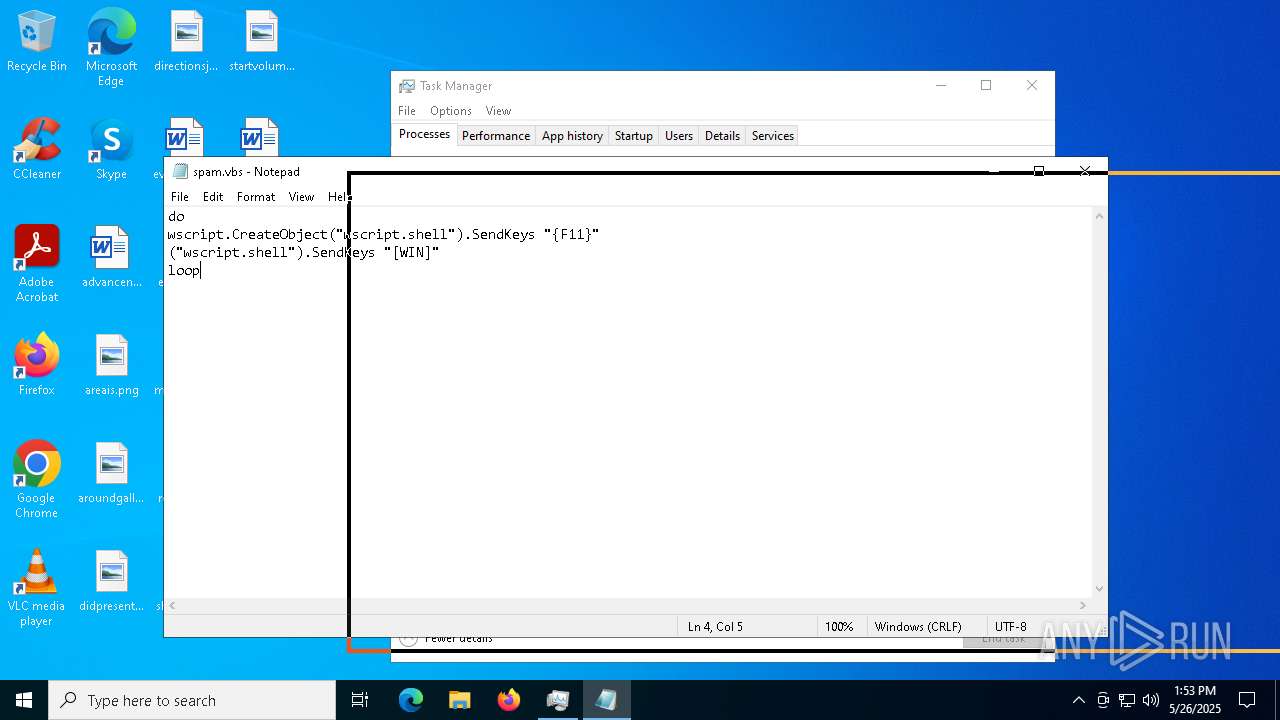
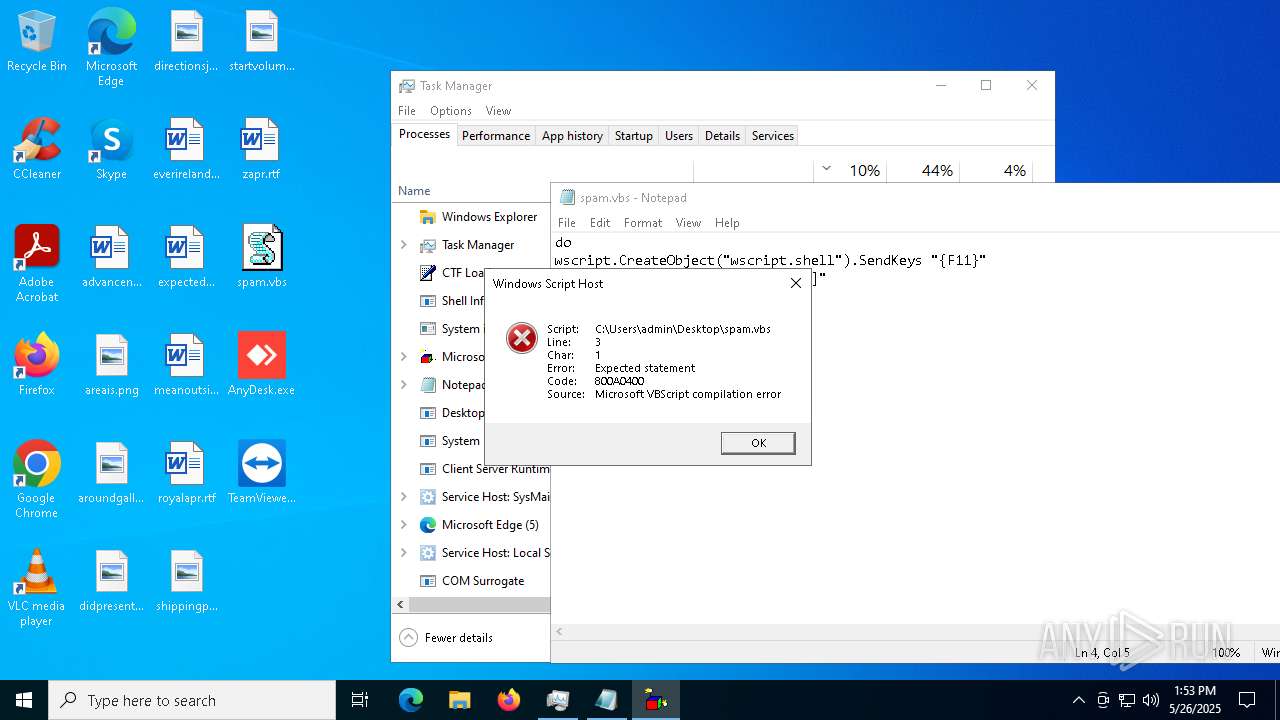
- wscript.exe (PID: 8032)
- notepad.exe (PID: 1812)
- wscript.exe (PID: 6728)
Checks proxy server information
- windows 20.exe (PID: 7020)
- AnyDesk.exe (PID: 7244)
The sample compiled with english language support
- windows 20.exe (PID: 7020)
- TeamViewer_.exe (PID: 6028)
- TeamViewer_Setup.exe (PID: 7216)
- TeamViewer_.exe (PID: 7644)
Process checks whether UAC notifications are on
- AnyDesk.exe (PID: 8036)
TeamViewer related mutex has been found
- TeamViewer_.exe (PID: 6028)
- TeamViewer.exe (PID: 5956)
Creates files or folders in the user directory
- AnyDesk.exe (PID: 8036)
- TeamViewer.exe (PID: 5956)
Reads Microsoft Office registry keys
- TeamViewer_.exe (PID: 6028)
- TeamViewer_.exe (PID: 7644)
Reads the machine GUID from the registry
- AnyDesk.exe (PID: 7244)
- TeamViewer.exe (PID: 5956)
Reads CPU info
- AnyDesk.exe (PID: 8036)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 8140)
Reads the software policy settings
- TeamViewer.exe (PID: 5956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
233
Monitored processes
99
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 900 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=22 --mojo-platform-channel-handle=5160 --field-trial-handle=2368,i,4204827591638590446,15752722378397599843,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5228 --field-trial-handle=2372,i,354645984857757959,10609861166633268046,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1116 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6972 --field-trial-handle=2380,i,15551917887322220753,6234744021405835056,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1272 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=29 --mojo-platform-channel-handle=6916 --field-trial-handle=2380,i,15551917887322220753,6234744021405835056,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=5964 --field-trial-handle=2368,i,4204827591638590446,15752722378397599843,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1660 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6648 --field-trial-handle=2380,i,15551917887322220753,6234744021405835056,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1660 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4744 --field-trial-handle=2368,i,4204827591638590446,15752722378397599843,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1672 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=17 --mojo-platform-channel-handle=5592 --field-trial-handle=2368,i,4204827591638590446,15752722378397599843,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
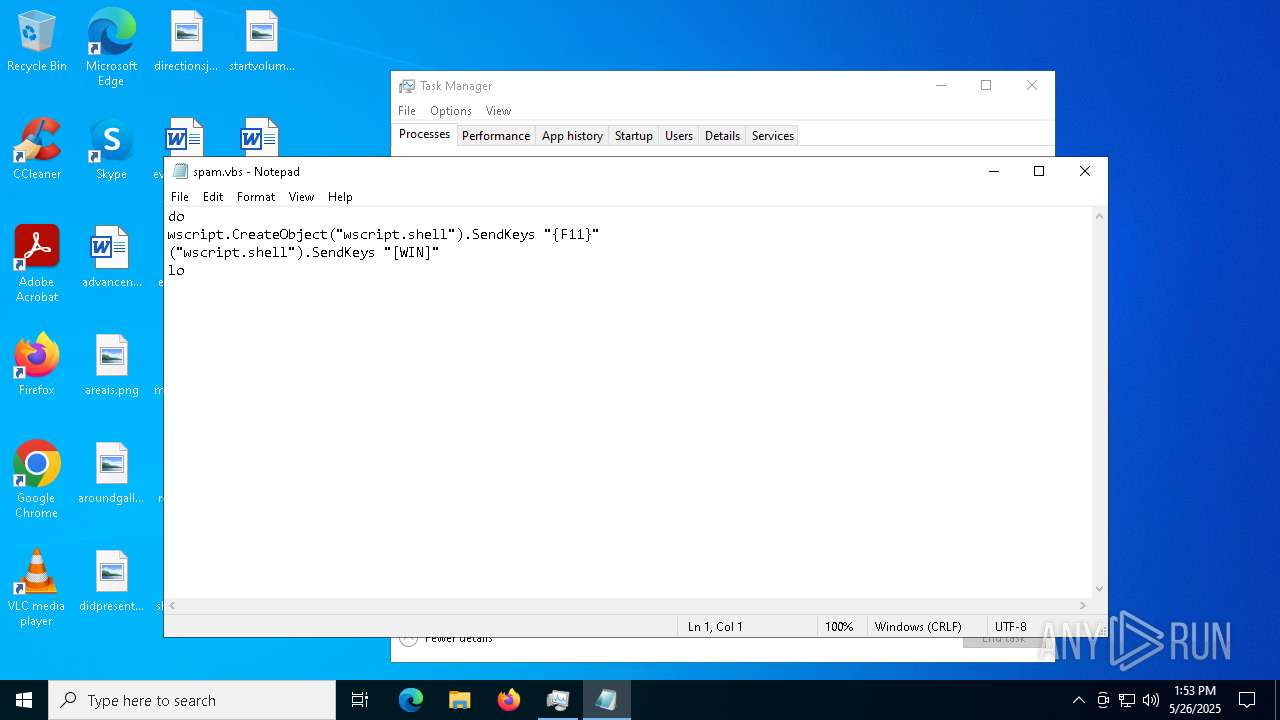
| 1812 | "C:\WINDOWS\System32\Notepad.exe" C:\Users\admin\Desktop\spam.vbs | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1912 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6228 --field-trial-handle=2368,i,4204827591638590446,15752722378397599843,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
32 138
Read events
31 745
Write events
386
Delete events
7
Modification events
| (PID) Process: | (3100) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3100) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3100) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3100) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3100) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D4B0C788A0942F00 | |||
| (PID) Process: | (3100) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A478D188A0942F00 | |||
| (PID) Process: | (3100) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459532 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3035E908-8BB7-401F-A46B-08349C81B885} | |||
| (PID) Process: | (3100) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459532 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9504BE63-C493-4E7A-BB2D-BB1D25B36B7B} | |||
| (PID) Process: | (3100) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459532 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {96C4BD09-E0A8-4D4C-A43C-462A6BFEBCC9} | |||
| (PID) Process: | (3100) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459532 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {60676C17-1F85-4F13-A1F8-57C290BD78B3} | |||
Executable files
141
Suspicious files
259
Text files
162
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3100 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10ce3f.TMP | — | |
MD5:— | SHA256:— | |||
| 3100 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3100 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10ce4e.TMP | — | |
MD5:— | SHA256:— | |||
| 3100 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10ce4e.TMP | — | |
MD5:— | SHA256:— | |||
| 3100 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3100 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3100 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10ce4e.TMP | — | |
MD5:— | SHA256:— | |||
| 3100 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3100 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10ce4e.TMP | — | |
MD5:— | SHA256:— | |||
| 3100 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
151
DNS requests
137
Threats
35
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
536 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
536 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
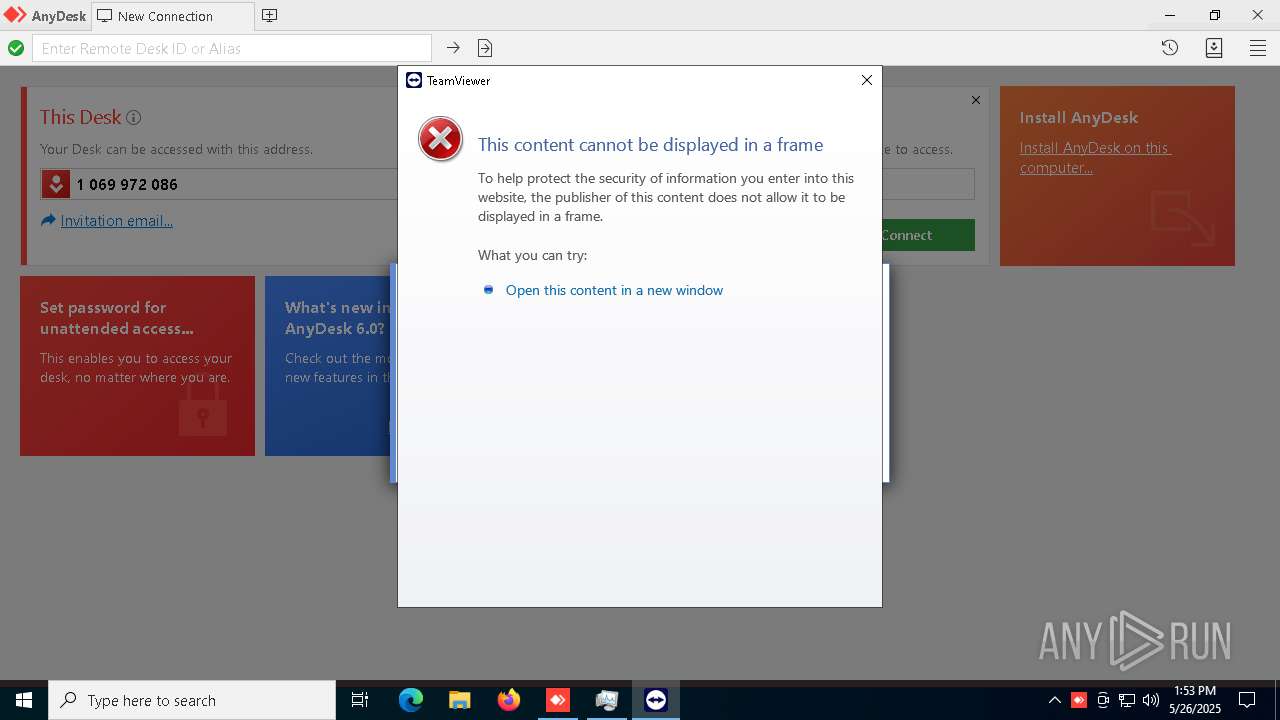
5328 | mshta.exe | GET | 301 | 20.79.107.7:80 | http://client.teamviewer.com/shutdown/index.aspx?lng=en | unknown | — | — | unknown |
5328 | mshta.exe | GET | 301 | 104.16.63.16:80 | http://www.teamviewer.com/favicon.ico | unknown | — | — | unknown |
5328 | mshta.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | unknown | — | — | whitelisted |
5328 | mshta.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECECO1SRtoRjdWzlsXC7yXMV0%3D | unknown | — | — | whitelisted |
5328 | mshta.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7232 | msedge.exe | 150.171.29.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7232 | msedge.exe | 31.216.145.5:443 | mega.nz | Datacenter Luxembourg S.A. | LU | whitelisted |
3100 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7232 | msedge.exe | 13.107.43.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
mega.nz |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7232 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7232 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7232 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
7232 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
7232 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
7232 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
7232 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
7232 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
7232 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7232 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |