| File name: | Contract.pptx |
| Full analysis: | https://app.any.run/tasks/765fdd8e-c4c8-4430-bd06-083a74b39f60 |
| Verdict: | Malicious activity |
| Analysis date: | April 14, 2025, 22:00:27 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | Microsoft OOXML |
| MD5: | 71143DBCC5B53ABD5CAD89D51D3C911B |
| SHA1: | F22257852BFDA65B0E0DA3253960562F9E985ACD |
| SHA256: | BE81589D48C1F392E033985989C4A283E234B354626C8482EA166A690D3EB01A |
| SSDEEP: | 6144:G37HcMX7zMmzQOLexD3Q29fWYpVvZ6NIS:AHcMXPNLed3Nf5VvEIS |
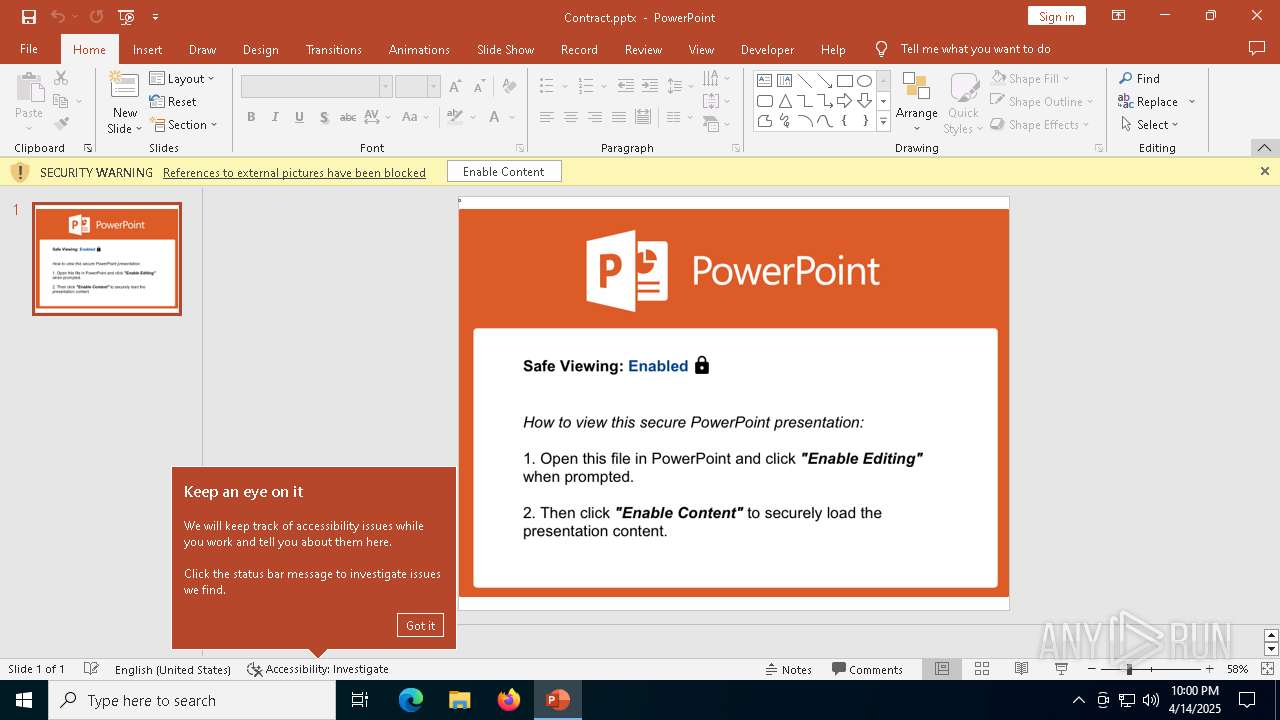
MALICIOUS
KNOWBE4 has been detected (SURICATA)
- svchost.exe (PID: 2196)
PHISHING has been detected (SURICATA)
- svchost.exe (PID: 2196)
SUSPICIOUS
The process connected to a server suspected of theft
- svchost.exe (PID: 2196)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .pptx | | | PowerPoint Microsoft Office Open XML Format document (87) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (10.5) |
| .zip | | | ZIP compressed archive (2.4) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:04:14 12:49:50 |
| ZipCRC: | 0xdd1cce94 |
| ZipCompressedSize: | 425 |
| ZipUncompressedSize: | 3193 |
| ZipFileName: | [Content_Types].xml |
XML
| TotalEditTime: | 33 minutes |
|---|---|
| Words: | 7 |
| Application: | Microsoft Macintosh PowerPoint |
| PresentationFormat: | On-screen Show (4:3) |
| Paragraphs: | 1 |
| Slides: | 1 |
| Notes: | - |
| HiddenSlides: | - |
| MMClips: | - |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: |
|
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16.0014 |
| LastModifiedBy: | KB4 |
| RevisionNumber: | 7 |
| CreateDate: | 2014:07:08 19:45:52Z |
| ModifyDate: | 2018:06:21 08:42:27Z |
XMP
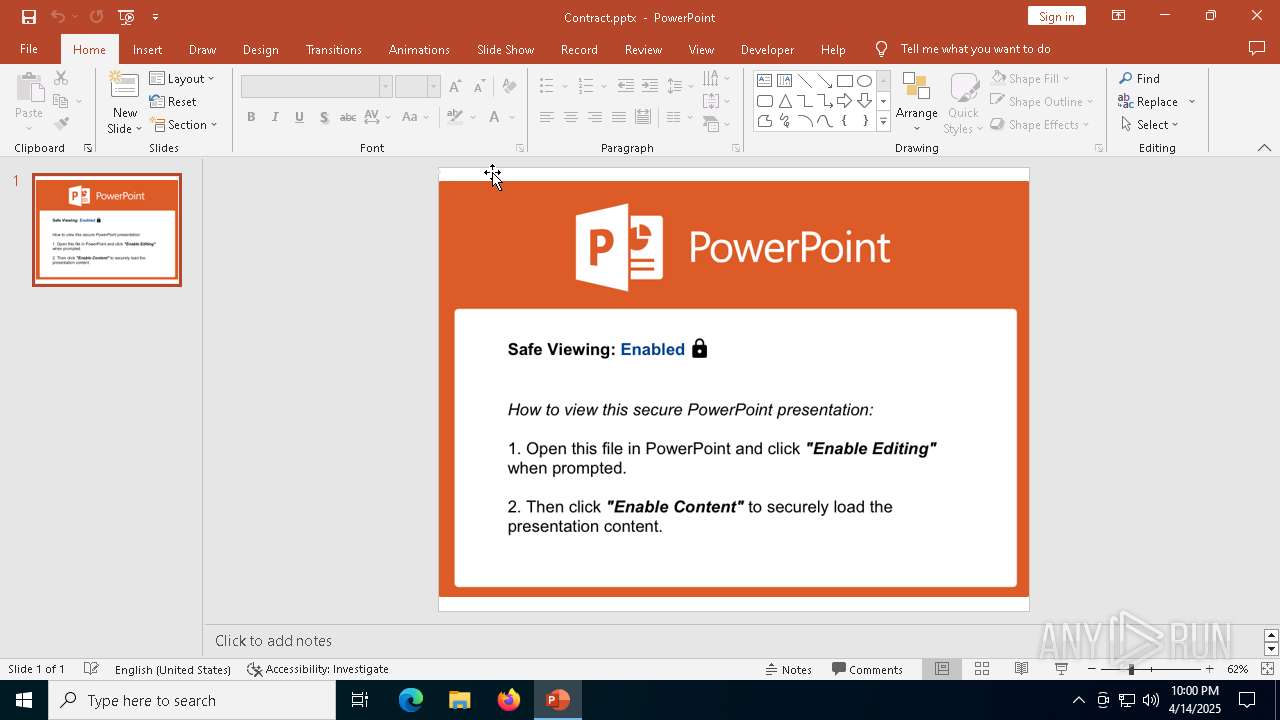
| Title: | YOU MUST OPEN THIS FILE IN POWERPOINT AND ENABLE EDITING TO VIEW THIS PRESENTATION |
|---|---|
| Creator: | KnowBe4 |
Total processes
134
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7412 | "C:\Program Files\Microsoft Office\Root\Office16\POWERPNT.EXE" C:\Users\admin\AppData\Local\Temp\Contract.pptx /ou "" | C:\Program Files\Microsoft Office\root\Office16\POWERPNT.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft PowerPoint Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 7928 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7960 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 863
Read events
11 515
Write events
330
Delete events
18
Modification events
| (PID) Process: | (7412) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 3 |
Value: 011C08000000001000B24E9A3E01000000000000000300000000000000 | |||
| (PID) Process: | (7412) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\POWERPNT\7412 |
| Operation: | write | Name: | 0 |
Value: 0B0E10C54A1AA772814247A73DB27386420EC7230046E2E58BA78AB1EBED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C511F439D2120C70006F0077006500720070006E0074002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (7412) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (7412) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (7412) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (7412) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (7412) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
| (PID) Process: | (7412) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 2 | |||
| (PID) Process: | (7412) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ko-kr |
Value: 2 | |||
| (PID) Process: | (7412) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | pt-br |
Value: 2 | |||
Executable files
17
Suspicious files
108
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7412 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\986CA3B9-F0CF-4D83-BD31-1113ED625A03 | xml | |
MD5:9C706C2F685D36B28A466DDE6F68BA47 | SHA256:1C992270DDF42A3CDE521D9DCA6F606B9C6F2848E6A5051D2AF7E11CC49B4CD8 | |||
| 7412 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntities.bin | text | |
MD5:CC90D669144261B198DEAD45AA266572 | SHA256:89C701EEFF939A44F28921FD85365ECD87041935DCD0FE0BAF04957DA12C9899 | |||
| 7412 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:E37774E519779C05844FCD16536CFF58 | SHA256:43A68C16804B8B272047F96D4801FC165F92B678916675954F46E7FEDC36FFFA | |||
| 7412 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\UsageMetricsStore\FileActivityStoreV3\PowerPoint\ASkwMDAwMDAwMC0wMDAwLTAwMDAtMDAwMC0wMDAwMDAwMDAwMDBfTnVsbAA.S | binary | |
MD5:7B9C2CA1B0EA8BF830F3628F147186AE | SHA256:14EA3E532CFD59FF3862842FFD25CBD3FF2C2D2CAD083D1046C207698ABE5291 | |||
| 7412 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntitiesUpdated.bin | text | |
MD5:F6AB2A0F972E1CD9463524B3857D6B73 | SHA256:B4FCF845D2BABC281610624BFBC029EF9913C7A3C1A0D45A7F5702DBD23FDF5E | |||
| 7412 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\Personalization\Governance\Anonymous\floodgatecampaigns.json.tmp | binary | |
MD5:1F34250CA1E4935554880767652EB906 | SHA256:E61547E4C8D9223A4EAE972863B6954344906EB7DBDECB3F8CC0E74019190AA3 | |||
| 7412 | POWERPNT.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_6372E0472AFF76BB926C97818BC773B9 | binary | |
MD5:F30F89FE1B1C4296F169F81879D4201C | SHA256:666EE5F3EB6E244ED30FE32F963A1C2E5E0D6EEF65FEC02A50F6AAFD2758A155 | |||
| 7412 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\Personalization\Governance\Anonymous\floodgatecampaigns.json | binary | |
MD5:1F34250CA1E4935554880767652EB906 | SHA256:E61547E4C8D9223A4EAE972863B6954344906EB7DBDECB3F8CC0E74019190AA3 | |||
| 7412 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Temp\cab127D.tmp | compressed | |
MD5:EF9CB8BDFBC08F03BEF519AD66BA642F | SHA256:93A2F873ACF5BEAD4BC0D1CC17B5E89A928D63619F70A1918B29E5230ABEAD8E | |||
| 7412 | POWERPNT.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\W4I0BIF94NXU7J8FFCI5.temp | binary | |
MD5:4FCB2A3EE025E4A10D21E1B154873FE2 | SHA256:90BF6BAA6F968A285F88620FBF91E1F5AA3E66E2BAD50FD16F37913280AD8228 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
65
DNS requests
25
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.141:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7412 | POWERPNT.EXE | GET | 200 | 23.48.23.147:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | unknown | — | — | whitelisted |
7412 | POWERPNT.EXE | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
7412 | POWERPNT.EXE | GET | 200 | 23.48.23.147:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | — | — | whitelisted |
7412 | POWERPNT.EXE | GET | 200 | 23.48.23.147:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7412 | POWERPNT.EXE | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
7412 | POWERPNT.EXE | GET | 200 | 23.48.23.147:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
7412 | POWERPNT.EXE | GET | 200 | 23.48.23.147:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | — | — | whitelisted |
7152 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.141:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7412 | POWERPNT.EXE | 52.109.28.46:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
7412 | POWERPNT.EXE | 52.123.129.14:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7412 | POWERPNT.EXE | 23.48.23.18:443 | omex.cdn.office.net | Akamai International B.V. | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7412 | POWERPNT.EXE | 52.111.236.4:443 | messaging.engagement.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
client.wns.windows.com |
| whitelisted |
messaging.engagement.office.com |
| whitelisted |
login.live.com |
| whitelisted |
messaging.lifecycle.office.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Successful Credential Theft Detected | ET INFO Observed DNS Query to KnowBe4 Simulated Phish Domain |
2196 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Training domain ( .phish .farm) |