| File name: | BLuecord.exe |
| Full analysis: | https://app.any.run/tasks/70d10b5f-0146-4627-8d73-80e1d491780a |
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2023, 14:32:05 |
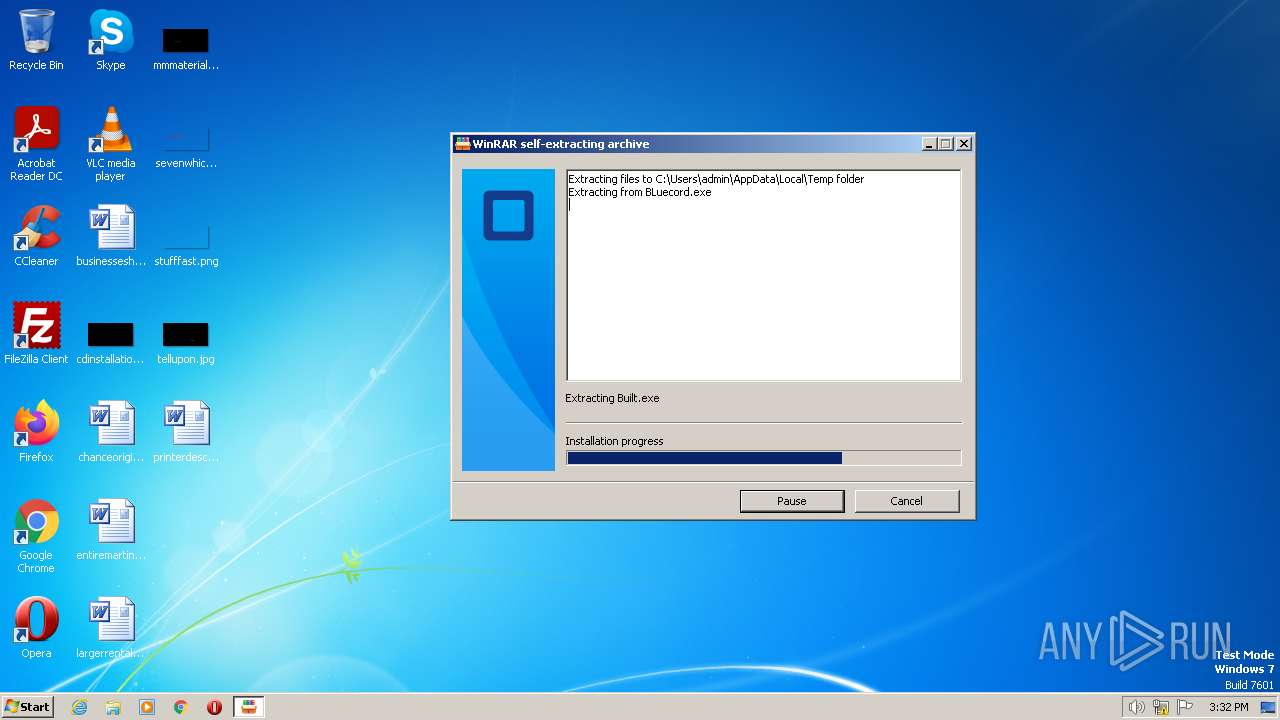
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 4B28101A9496EE4933486B1612E6B37D |
| SHA1: | 1AD83BE2E185EA7E8D8B2139885ABFD19AA8486E |
| SHA256: | BE6E41CB79CDAD91DC4BF6CBE2E133ECD452C47A94ABD79F05DAE80AEB29E897 |
| SSDEEP: | 98304:uYN8839InHHroDQqFh/rUJODRyVd8cwFZkMb8yG3C6S/Am0iyp7URBd8+3n:BHNI8kOxrUgRyVd8bkMAy56S/1OGnR3n |
MALICIOUS
Changes the login/logoff helper path in the registry
- hehehe.exe (PID: 3204)
Application was dropped or rewritten from another process
- svchost.exe (PID: 3924)
- weeew.exe (PID: 3168)
- qualcom2.exe (PID: 2884)
- weeew.exe (PID: 3100)
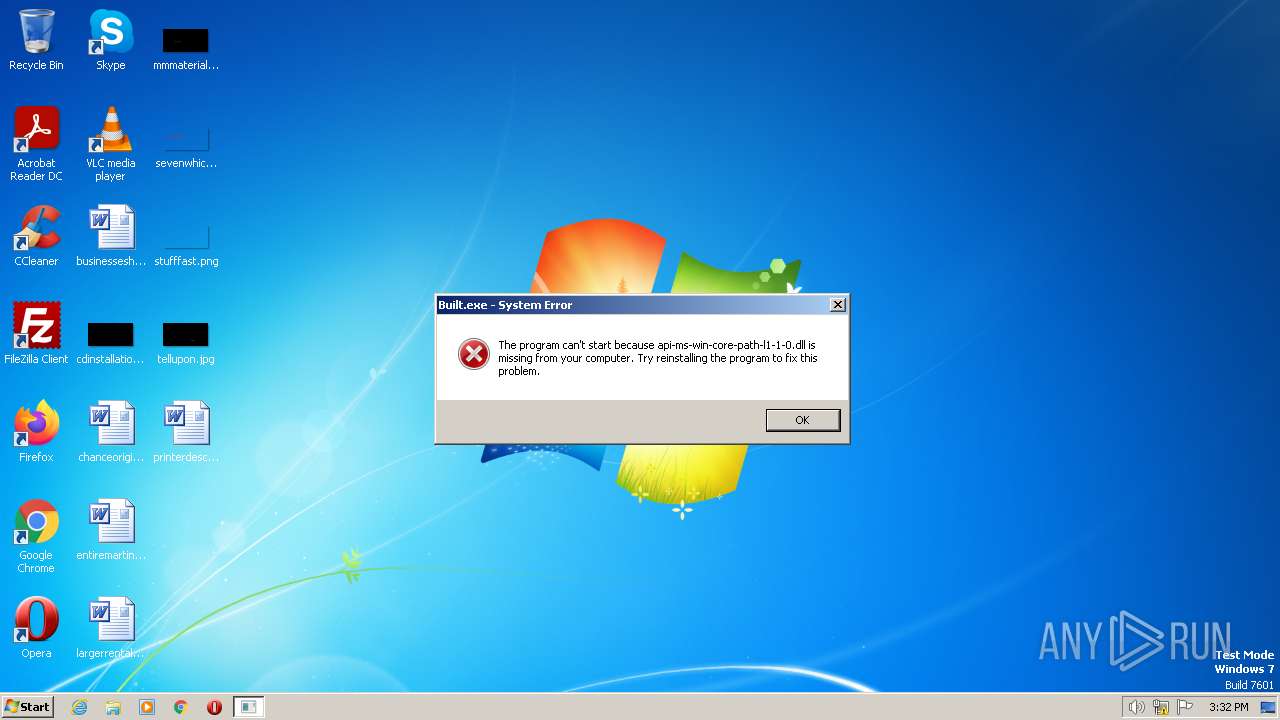
- Built.exe (PID: 2940)
- Built.exe (PID: 2168)
- hehehe.exe (PID: 3204)
- svchost.exe (PID: 940)
Create files in the Startup directory
- svchost.exe (PID: 940)
Loads dropped or rewritten executable
- Built.exe (PID: 2168)
Renames files like ransomware
- svchost.exe (PID: 940)
Steals credentials from Web Browsers
- svchost.exe (PID: 940)
Actions looks like stealing of personal data
- svchost.exe (PID: 940)
SUSPICIOUS
Reads the Internet Settings
- BLuecord.exe (PID: 3980)
- svchost.exe (PID: 3924)
- weeew.exe (PID: 3100)
Reads Internet Explorer settings
- BLuecord.exe (PID: 3980)
Creates executable files that already exist in Windows
- BLuecord.exe (PID: 3980)
- svchost.exe (PID: 3924)
Reads Microsoft Outlook installation path
- BLuecord.exe (PID: 3980)
The process creates files with name similar to system file names
- BLuecord.exe (PID: 3980)
- svchost.exe (PID: 3924)
Executable content was dropped or overwritten
- BLuecord.exe (PID: 3980)
- svchost.exe (PID: 3924)
- Built.exe (PID: 2940)
- qualcom2.exe (PID: 2884)
- weeew.exe (PID: 3100)
- weeew.exe (PID: 3168)
Application launched itself
- Built.exe (PID: 2940)
- weeew.exe (PID: 3100)
Loads Python modules
- Built.exe (PID: 2168)
Starts itself from another location
- svchost.exe (PID: 3924)
Write to the desktop.ini file (may be used to cloak folders)
- svchost.exe (PID: 940)
INFO
The process checks LSA protection
- BLuecord.exe (PID: 3980)
- svchost.exe (PID: 3924)
- weeew.exe (PID: 3100)
- svchost.exe (PID: 940)
- qualcom2.exe (PID: 2884)
- weeew.exe (PID: 3168)
Checks supported languages
- BLuecord.exe (PID: 3980)
- weeew.exe (PID: 3100)
- Built.exe (PID: 2940)
- qualcom2.exe (PID: 2884)
- hehehe.exe (PID: 3204)
- Built.exe (PID: 2168)
- svchost.exe (PID: 3924)
- weeew.exe (PID: 3168)
- svchost.exe (PID: 940)
Checks proxy server information
- BLuecord.exe (PID: 3980)
Reads the machine GUID from the registry
- BLuecord.exe (PID: 3980)
- weeew.exe (PID: 3100)
- weeew.exe (PID: 3168)
- svchost.exe (PID: 940)
- qualcom2.exe (PID: 2884)
Reads the computer name
- BLuecord.exe (PID: 3980)
- Built.exe (PID: 2940)
- svchost.exe (PID: 3924)
- weeew.exe (PID: 3100)
- svchost.exe (PID: 940)
- weeew.exe (PID: 3168)
- qualcom2.exe (PID: 2884)
Create files in a temporary directory
- BLuecord.exe (PID: 3980)
- Built.exe (PID: 2940)
- qualcom2.exe (PID: 2884)
Process checks are UAC notifies on
- weeew.exe (PID: 3100)
- weeew.exe (PID: 3168)
Creates files or folders in the user directory
- weeew.exe (PID: 3100)
- svchost.exe (PID: 940)
- svchost.exe (PID: 3924)
Reads Environment values
- weeew.exe (PID: 3168)
- qualcom2.exe (PID: 2884)
Creates files in the program directory
- weeew.exe (PID: 3168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x205e0 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 262144 |
| CodeSize: | 208384 |
| LinkerVersion: | 14.33 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2023:02:16 12:31:25+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Feb-2023 12:31:25 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 16-Feb-2023 12:31:25 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00032C1C | 0x00032E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.69711 |
.rdata | 0x00034000 | 0x0000B130 | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.25783 |
.data | 0x00040000 | 0x00024750 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.08398 |
.didat | 0x00065000 | 0x00000190 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.37276 |
.rsrc | 0x00066000 | 0x0000DFF8 | 0x0000E000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.63872 |
.reloc | 0x00074000 | 0x000023AC | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.64408 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.10026 | 2216 | UNKNOWN | English - United States | RT_ICON |
3 | 5.25868 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 5.02609 | 1128 | UNKNOWN | English - United States | RT_ICON |
5 | 5.18109 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 5.04307 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 3.1586 | 482 | UNKNOWN | English - United States | RT_STRING |
8 | 3.11685 | 460 | UNKNOWN | English - United States | RT_STRING |
9 | 3.11236 | 440 | UNKNOWN | English - United States | RT_STRING |
10 | 2.99727 | 326 | UNKNOWN | English - United States | RT_STRING |
Imports
KERNEL32.dll |
OLEAUT32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
49
Monitored processes
9
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 940 | "C:\Users\admin\AppData\Roaming\svchost.exe" | C:\Users\admin\AppData\Roaming\svchost.exe | svchost.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2168 | "C:\Users\admin\AppData\Local\Temp\Built.exe" | C:\Users\admin\AppData\Local\Temp\Built.exe | — | Built.exe | |||||||||||
User: admin Company: Windows (R) Win 7 DDK provider Integrity Level: MEDIUM Description: Microsoft (R) DirectX Control Panel Exit code: 0 Version: 6.3.9600.16384 Modules
| |||||||||||||||
| 2884 | "C:\Users\admin\AppData\Local\Temp\qualcom2.exe" | C:\Users\admin\AppData\Local\Temp\qualcom2.exe | BLuecord.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Remote Controler Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2940 | "C:\Users\admin\AppData\Local\Temp\Built.exe" | C:\Users\admin\AppData\Local\Temp\Built.exe | BLuecord.exe | ||||||||||||
User: admin Company: Windows (R) Win 7 DDK provider Integrity Level: MEDIUM Description: Microsoft (R) DirectX Control Panel Exit code: 0 Version: 6.3.9600.16384 Modules
| |||||||||||||||
| 3100 | "C:\Users\admin\AppData\Local\Temp\weeew.exe" | C:\Users\admin\AppData\Local\Temp\weeew.exe | BLuecord.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3168 | "C:\Users\admin\AppData\Local\Temp\weeew.exe" | C:\Users\admin\AppData\Local\Temp\weeew.exe | weeew.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3204 | "C:\Users\admin\AppData\Local\Temp\hehehe.exe" | C:\Users\admin\AppData\Local\Temp\hehehe.exe | BLuecord.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 3924 | "C:\Users\admin\AppData\Local\Temp\svchost.exe" | C:\Users\admin\AppData\Local\Temp\svchost.exe | BLuecord.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 1 Version: 0.0.0.0 Modules
| |||||||||||||||
| 3980 | "C:\Users\admin\AppData\Local\Temp\BLuecord.exe" | C:\Users\admin\AppData\Local\Temp\BLuecord.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
5 471
Read events
5 443
Write events
27
Delete events
1
Modification events
| (PID) Process: | (3980) BLuecord.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3980) BLuecord.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3980) BLuecord.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3980) BLuecord.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3980) BLuecord.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3980) BLuecord.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3204) hehehe.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Shell |
Value: explorer.exe | |||
| (PID) Process: | (3924) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3924) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3924) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
31
Suspicious files
2
Text files
508
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2940 | Built.exe | C:\Users\admin\AppData\Local\Temp\_MEI29402\VCRUNTIME140.dll | executable | |
MD5:1E6E97D60D411A2DEE8964D3D05ADB15 | SHA256:8598940E498271B542F2C04998626AA680F2172D0FF4F8DBD4FFEC1A196540F9 | |||
| 2940 | Built.exe | C:\Users\admin\AppData\Local\Temp\_MEI29402\PIL\_webp.cp310-win32.pyd | executable | |
MD5:9495F592D98677E1EEE41BFCB104D014 | SHA256:567887A304670D1D60BF9337A5D9D08AA9C4051148A42D8537234D8A4A071274 | |||
| 2940 | Built.exe | C:\Users\admin\AppData\Local\Temp\_MEI29402\_lzma.pyd | executable | |
MD5:A5E88E86D08F97E262ECC4F06FDEF890 | SHA256:D09C0F890C3329B5C65363D05C5492A03A1C69F05C88D185E7DD4D8A5B35E2A5 | |||
| 2940 | Built.exe | C:\Users\admin\AppData\Local\Temp\_MEI29402\_bz2.pyd | executable | |
MD5:1CCB079DE2131E28FC7E6BC00F21BF86 | SHA256:01101B4267278A4553DAA56AF5CD3F078B494DD22CDFD0BF8FE552743958BDD0 | |||
| 2940 | Built.exe | C:\Users\admin\AppData\Local\Temp\_MEI29402\_decimal.pyd | executable | |
MD5:06AB63CD64FB7A3F3356F843BB294072 | SHA256:5AEE22492C520A21292C84CBD0FE4B7E1038F73AE231809F18A8A7CF0097B48A | |||
| 2940 | Built.exe | C:\Users\admin\AppData\Local\Temp\_MEI29402\_ctypes.pyd | executable | |
MD5:6A64B32FF56498158110875DF5CF684F | SHA256:78F42580C9AD4DA257DA8AB8CC7A289EECFFD78CA754F8B582F63089EF3D762B | |||
| 2940 | Built.exe | C:\Users\admin\AppData\Local\Temp\_MEI29402\PIL\_imagingcms.cp310-win32.pyd | executable | |
MD5:F47756792144E3696BC72BCEE3E5D8A5 | SHA256:14E948F1797C70B7C4C42B27F95EFACDBC1E95EC95F06E0752A415025C60083E | |||
| 2940 | Built.exe | C:\Users\admin\AppData\Local\Temp\_MEI29402\_queue.pyd | executable | |
MD5:045E1030DA6356BCAA78E0AEB0C3A688 | SHA256:49DD7382D79D2DCFACBC65DEBBBD6BDD8854F42C04742F6DE3950A63A988DC5F | |||
| 2940 | Built.exe | C:\Users\admin\AppData\Local\Temp\_MEI29402\_ssl.pyd | executable | |
MD5:5C6DA86EE8D8AD64F9BD2B604E573D8B | SHA256:EB62826DFD0836A8583BFF2B6478FBD7A5DC51DFE51B4DF2A2D77115C8DA6019 | |||
| 2940 | Built.exe | C:\Users\admin\AppData\Local\Temp\_MEI29402\_socket.pyd | executable | |
MD5:7A74A69E9705FEE1AF987FE55434DE10 | SHA256:533CD2AD8AD7C14F7A5CED4EC4A582A3577BE113F914A93049548A4D93C8001C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
5
Threats
5
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3400 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
baggard477.ddns.net |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3168 | weeew.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
3168 | weeew.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
1076 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
3168 | weeew.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
3168 | weeew.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |