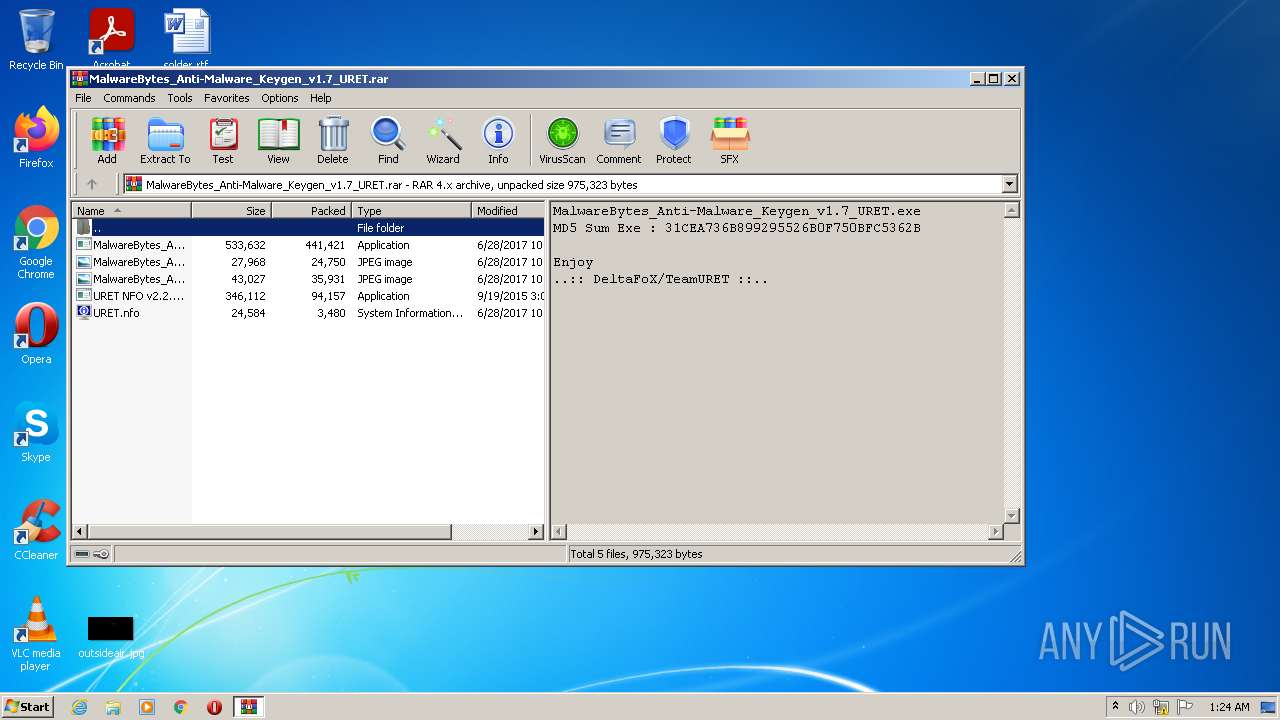
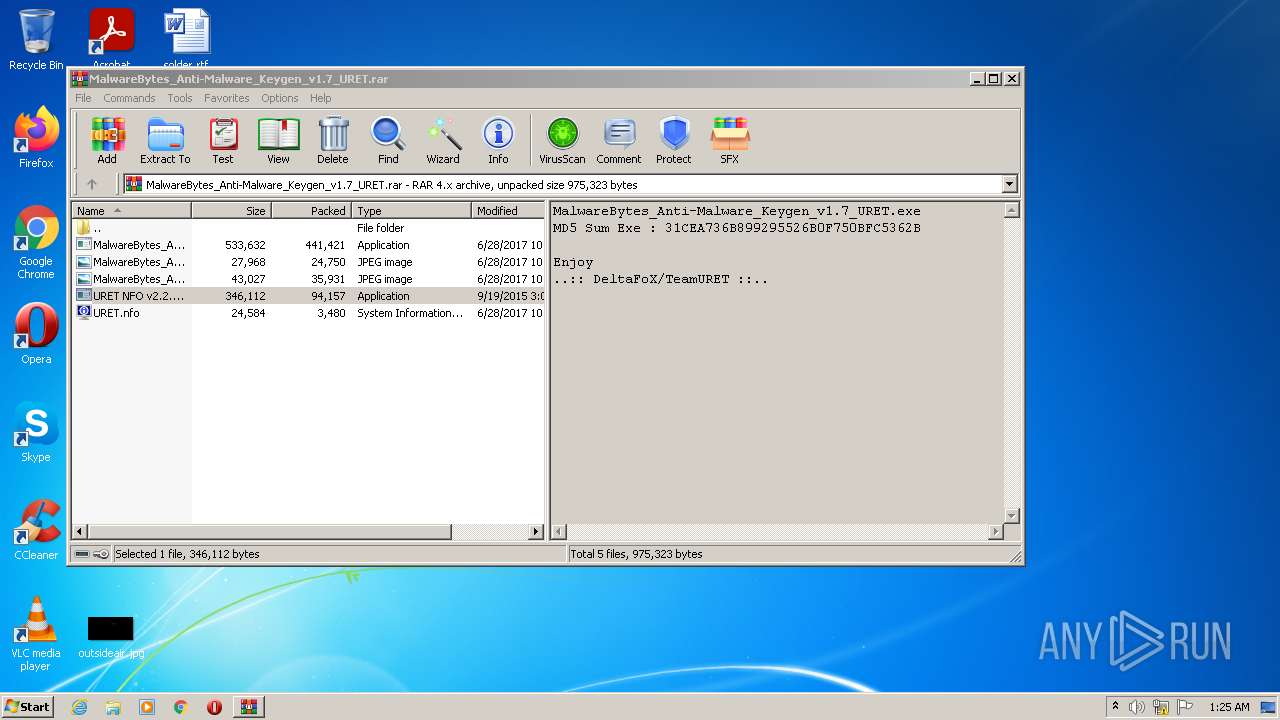
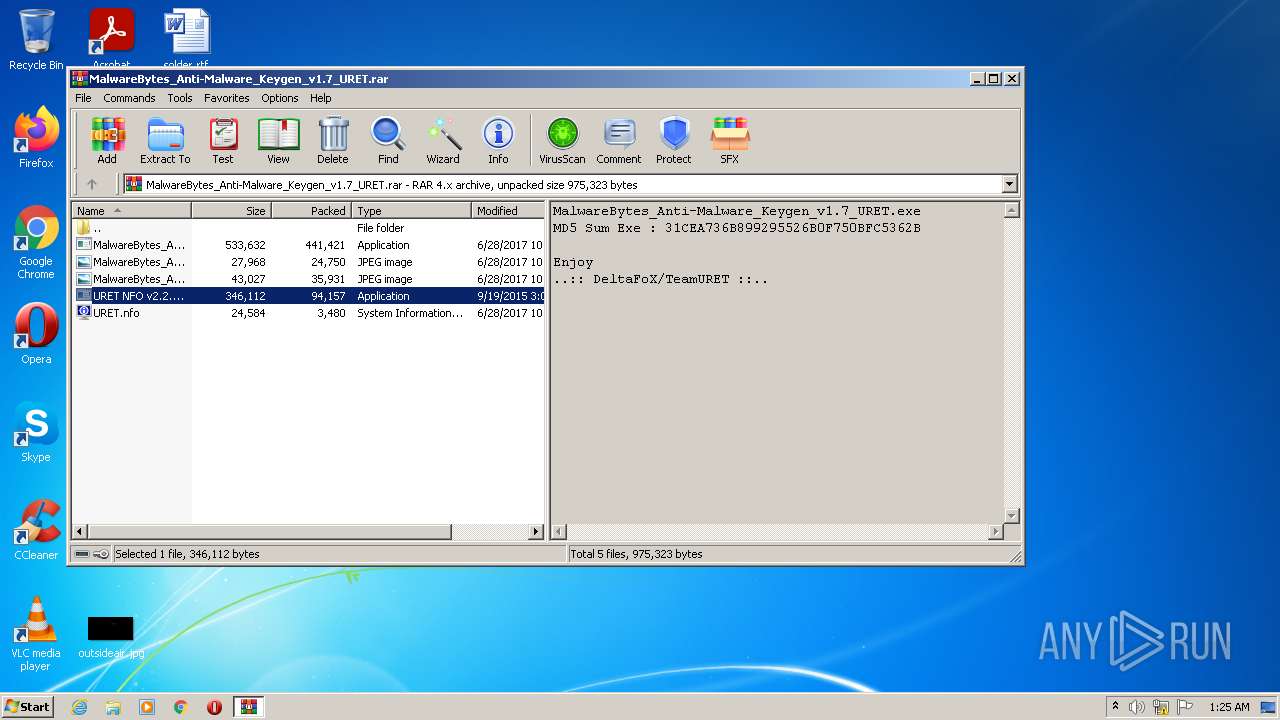
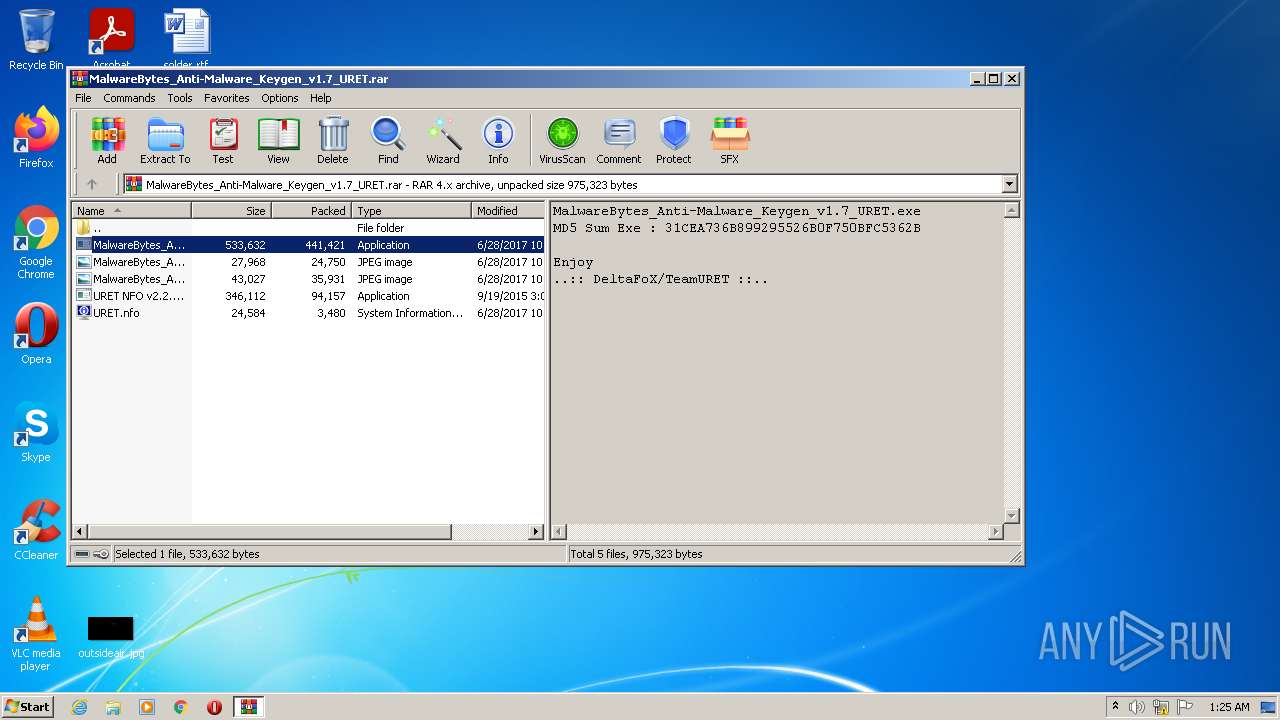
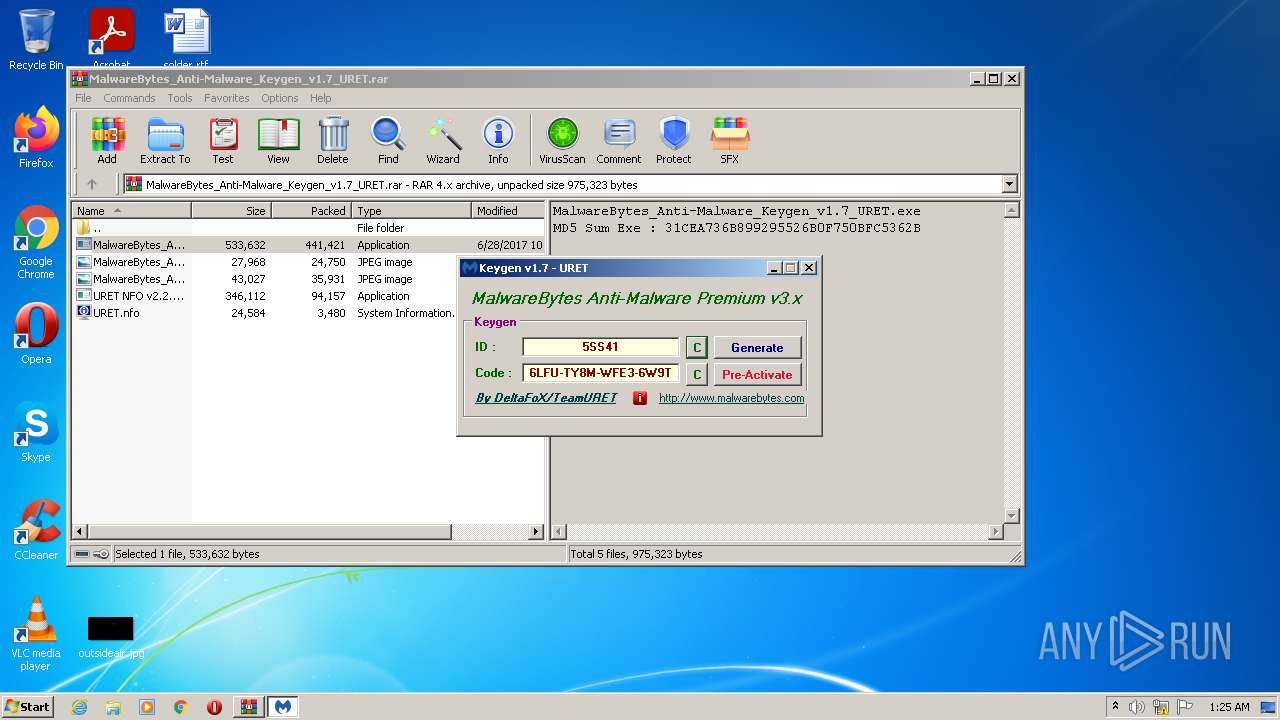
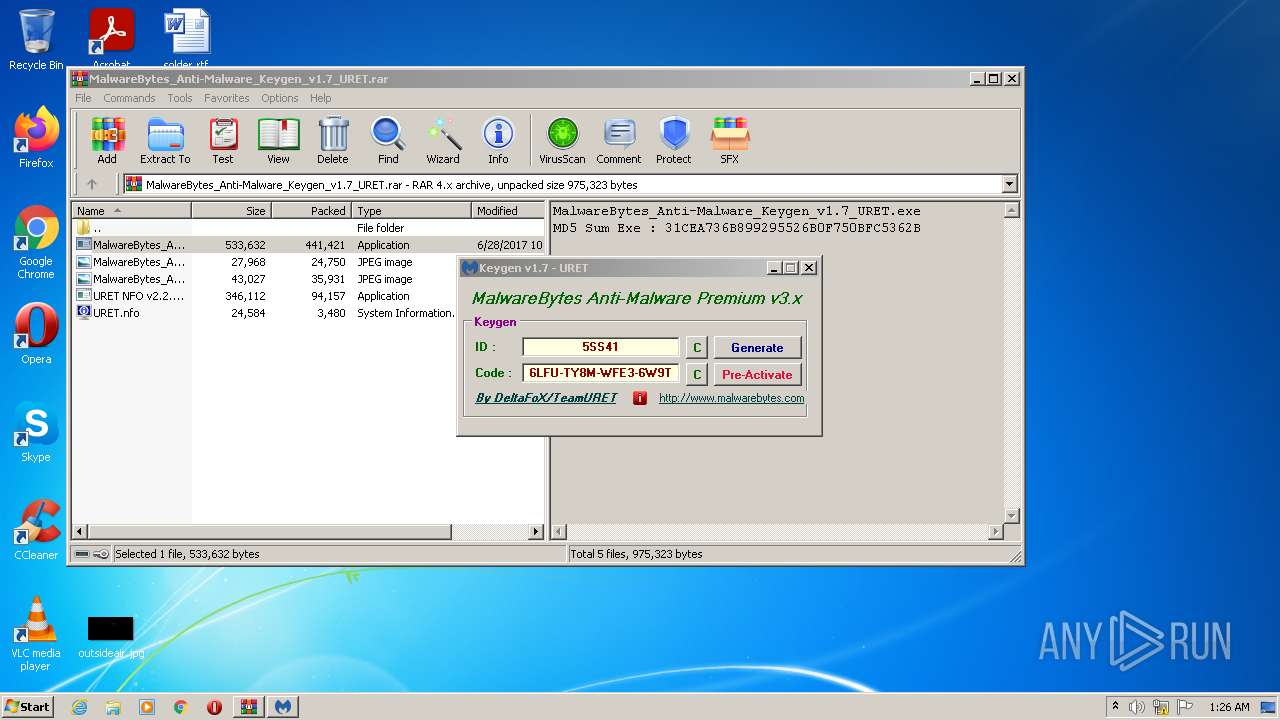
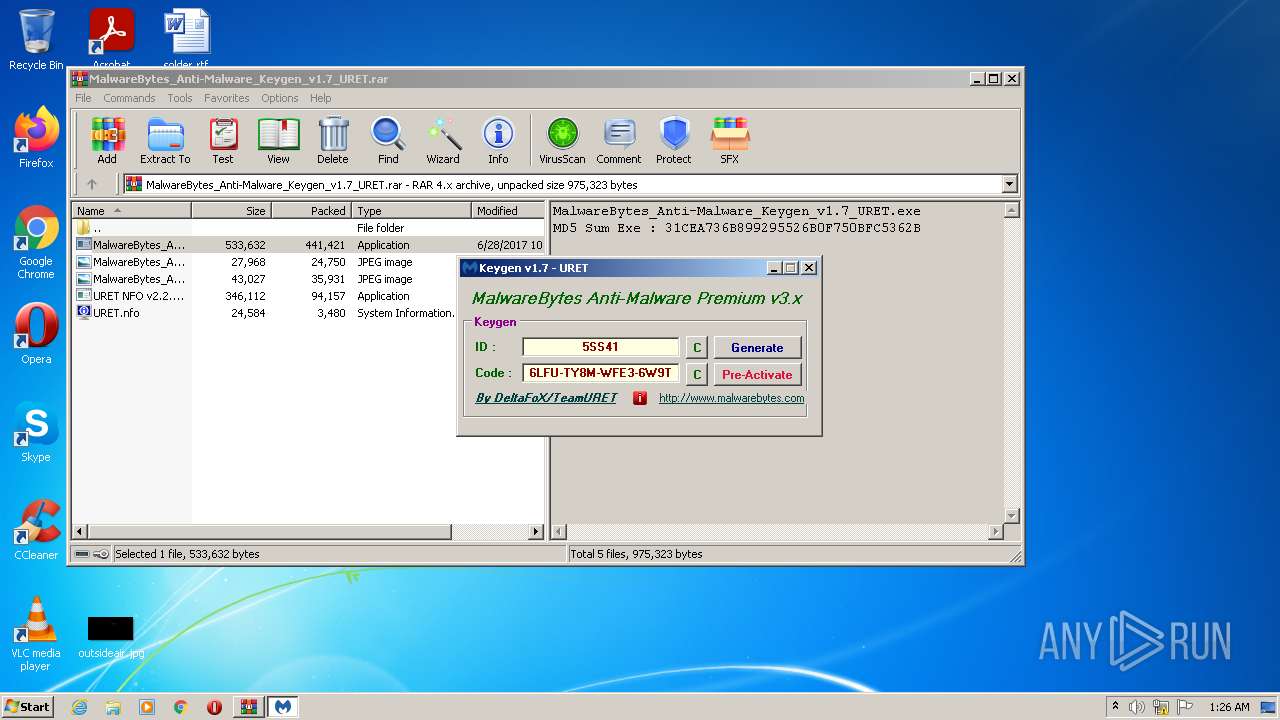
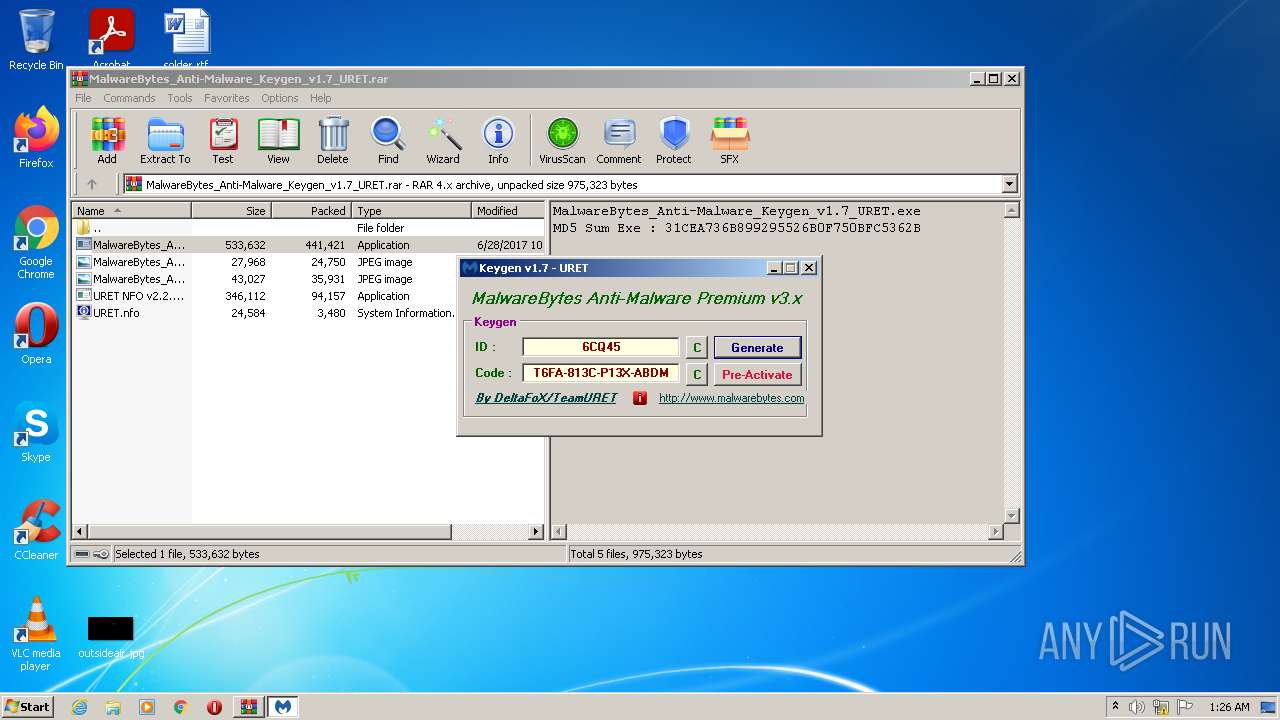
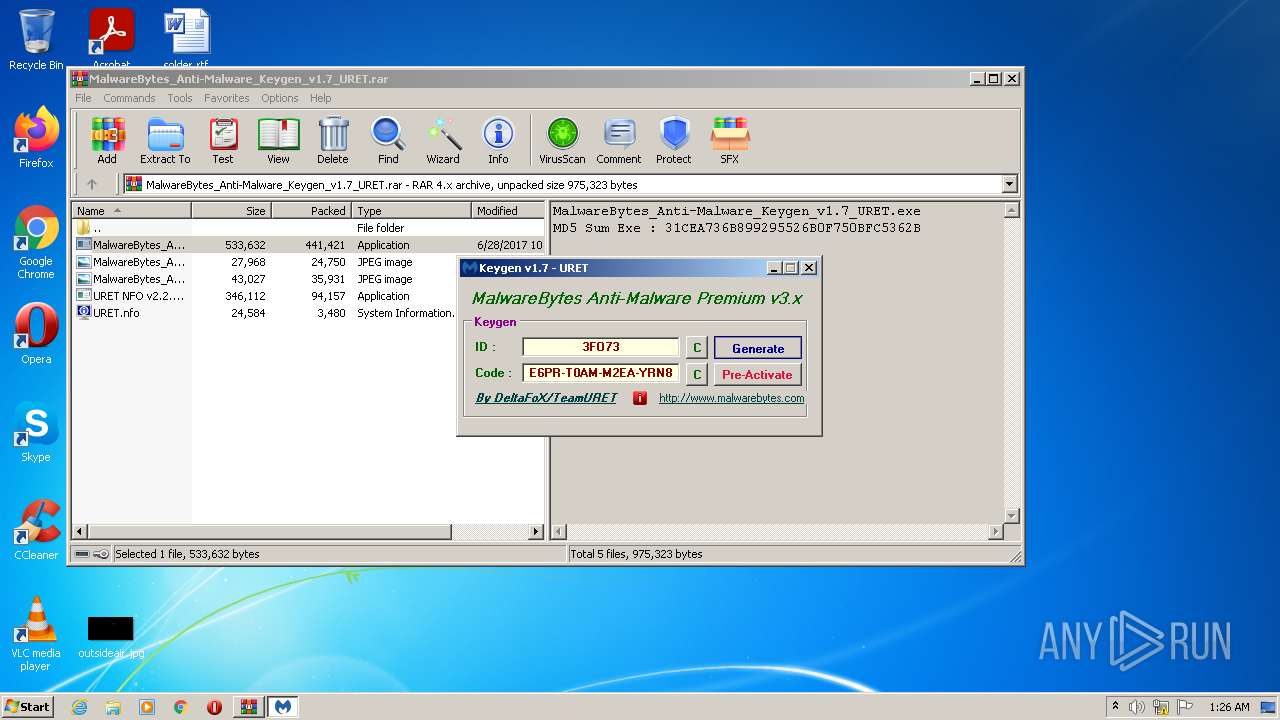
| File name: | MalwareBytes_Anti-Malware_Keygen_v1.7_URET.rar |
| Full analysis: | https://app.any.run/tasks/40cff82f-c84c-43e5-9c7a-6afbc226306d |
| Verdict: | Malicious activity |
| Analysis date: | November 23, 2022, 01:24:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | FDE304C3B1324162DBF213CC32A319D3 |
| SHA1: | 221C26D07FA708CF79618ACEF7C4A75C70CDB167 |
| SHA256: | BE6A6F1BE835EF70675A684AA49A3DCC0AA691BF8B2AB8EE6C872BD3A3E4D1D3 |
| SSDEEP: | 12288:si/5DK1S1VOP9tWqB0lFwCwOGmPTYvAtUA/YGwREXj:si/ptVmLlBY+mPTY4tUhVyj |
MALICIOUS
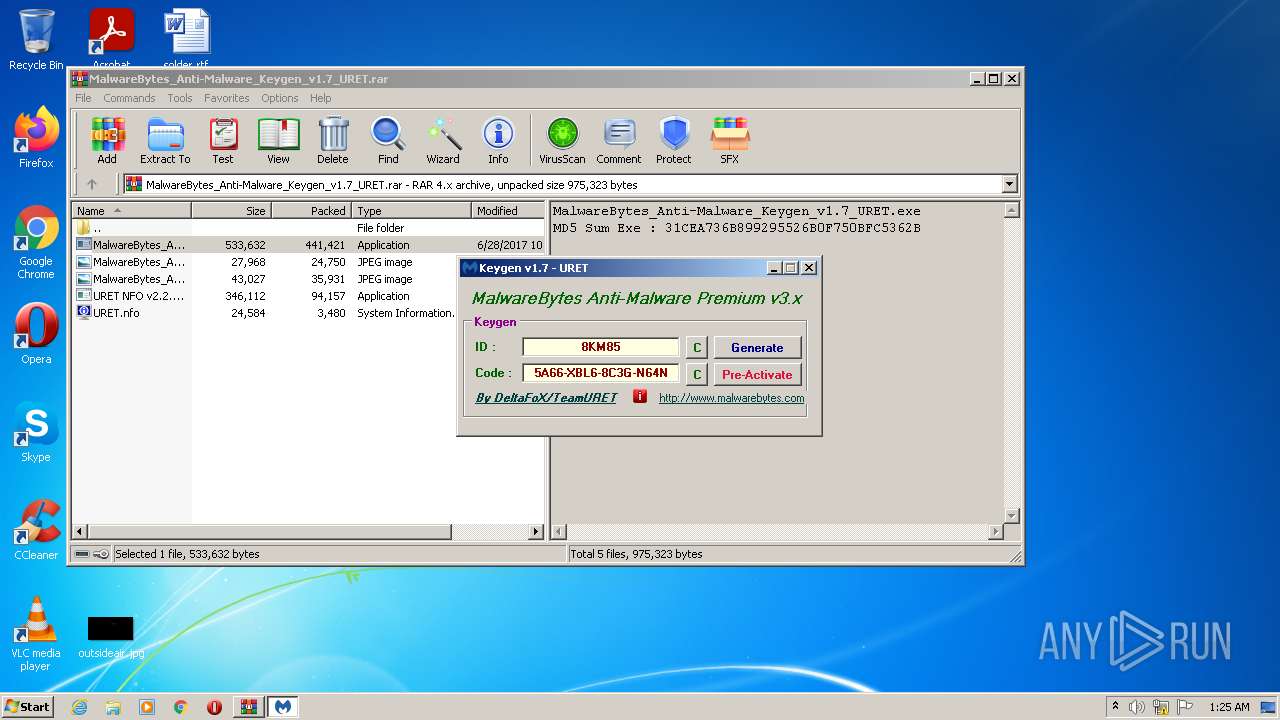
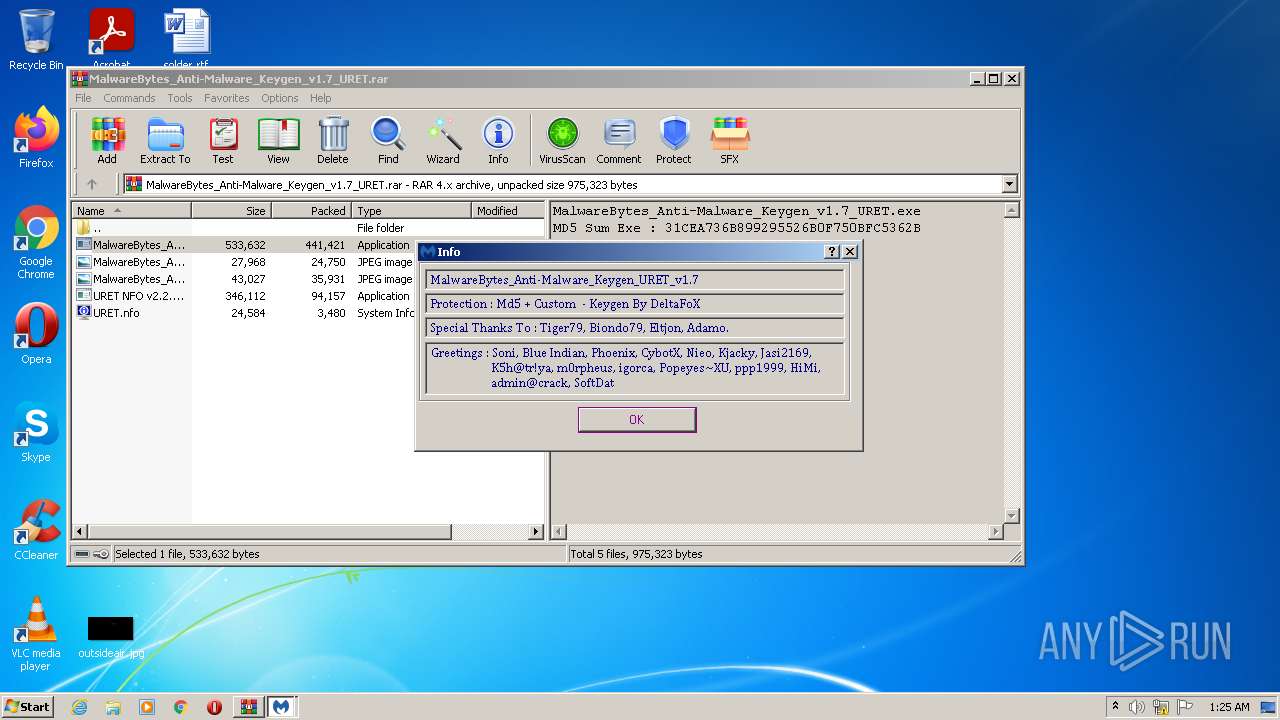
Application was dropped or rewritten from another process
- MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe (PID: 1976)
- URET NFO v2.2.exe (PID: 1568)
- MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe (PID: 3732)
Writes to the hosts file
- MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe (PID: 3732)
SUSPICIOUS
Reads the Windows owner or organization settings
- MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe (PID: 3732)
Reads Internet Settings
- MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe (PID: 3732)
Creates a software uninstall entry
- MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe (PID: 3732)
Searches for installed software
- MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe (PID: 3732)
INFO
Checks supported languages
- URET NFO v2.2.exe (PID: 1568)
- MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe (PID: 3732)
Creates files in the user directory
- MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe (PID: 3732)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 2968)
Application launched itself
- iexplore.exe (PID: 2296)
Reads the computer name
- URET NFO v2.2.exe (PID: 1568)
- MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe (PID: 3732)
Creates files in the program directory
- MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe (PID: 3732)
Process checks LSA protection
- MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe (PID: 3732)
Reads the machine GUID from the registry
- MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe (PID: 3732)
Starts Internet Explorer
- MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe (PID: 3732)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2968)
Reads the hosts file
- MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe (PID: 3732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
Total processes
48
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1568 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2968.35013\URET NFO v2.2.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2968.35013\URET NFO v2.2.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225725 Modules
| |||||||||||||||
| 1976 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2968.36519\MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2968.36519\MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe | — | WinRAR.exe | |||||||||||
User: admin Company: URET Integrity Level: MEDIUM Description: MalwareBytes_Anti-Malware_DFoX Exit code: 3221226540 Version: 1.7.0.0 Modules
| |||||||||||||||
| 2296 | "C:\program files\internet explorer\iexplore.exe" http://www.uret.in | C:\program files\internet explorer\iexplore.exe | MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2464 | "C:\program files\internet explorer\iexplore.exe" SCODEF:2296 CREDAT:275457 /prefetch:2 | C:\program files\internet explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2968 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\MalwareBytes_Anti-Malware_Keygen_v1.7_URET.rar" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3732 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2968.36519\MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2968.36519\MalwareBytes_Anti-Malware_Keygen_v1.7_URET.exe | WinRAR.exe | ||||||||||||
User: admin Company: URET Integrity Level: HIGH Description: MalwareBytes_Anti-Malware_DFoX Exit code: 0 Version: 1.7.0.0 Modules
| |||||||||||||||
Total events
15 228
Read events
15 012
Write events
215
Delete events
1
Modification events
| (PID) Process: | (2968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2968) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\MalwareBytes_Anti-Malware_Keygen_v1.7_URET.rar | |||
| (PID) Process: | (2968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
4
Suspicious files
16
Text files
28
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2968 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2968.35013\MalwareBytes_Anti-Malware_Keygen_v1.7_URET.jpg | image | |
MD5:— | SHA256:— | |||
| 2968 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2968.35013\URET.nfo | text | |
MD5:— | SHA256:— | |||
| 2968 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2968.36519\MalwareBytes_Anti-Malware_Keygen_v1.7_URET.jpg | image | |
MD5:— | SHA256:— | |||
| 2968 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2968.36519\MalwareBytes_Anti-Malware_Keygen_v1.7_URET_I.jpg | image | |
MD5:— | SHA256:— | |||
| 2464 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\style[1].css | text | |
MD5:— | SHA256:— | |||
| 2464 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\maincaf[1].js | text | |
MD5:— | SHA256:— | |||
| 2464 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Z9S4GZT0.txt | text | |
MD5:— | SHA256:— | |||
| 2968 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2968.36519\URET.nfo | text | |
MD5:— | SHA256:— | |||
| 2968 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2968.35013\MalwareBytes_Anti-Malware_Keygen_v1.7_URET_I.jpg | image | |
MD5:— | SHA256:— | |||
| 2464 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\SQ95GP24.htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
25
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2464 | iexplore.exe | GET | 200 | 142.250.185.100:80 | http://www.google.com/adsense/domains/caf.js | US | text | 52.2 Kb | malicious |
2464 | iexplore.exe | GET | 200 | 65.9.191.50:80 | http://d38psrni17bvxu.cloudfront.net/themes/cleanPeppermintBlack_657d9013/style.css | US | text | 648 b | suspicious |
2464 | iexplore.exe | GET | 200 | 185.53.177.50:80 | http://www.uret.in/ | DE | html | 4.73 Kb | malicious |
2464 | iexplore.exe | GET | 200 | 65.9.191.50:80 | http://d38psrni17bvxu.cloudfront.net/scripts/maincaf.js | US | text | 6.84 Kb | suspicious |
2464 | iexplore.exe | GET | 200 | 172.217.16.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2464 | iexplore.exe | GET | 200 | 65.9.191.50:80 | http://d38psrni17bvxu.cloudfront.net/themes/assets/style.css | US | text | 343 b | suspicious |
2296 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
2464 | iexplore.exe | GET | 200 | 172.217.16.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCG89in4JgGCxLKfewQn1bO | US | der | 472 b | whitelisted |
2464 | iexplore.exe | GET | 200 | 172.217.16.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDbyHvBeZtpOQpKuNstwnpv | US | der | 472 b | whitelisted |
2464 | iexplore.exe | GET | 200 | 172.217.16.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDZJO6dlgsrcRKeDfRzpInH | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2464 | iexplore.exe | 185.53.177.50:80 | www.uret.in | Team Internet AG | DE | malicious |
2464 | iexplore.exe | 65.9.191.50:80 | d38psrni17bvxu.cloudfront.net | — | US | unknown |
2464 | iexplore.exe | 142.250.186.66:443 | partner.googleadservices.com | GOOGLE | US | whitelisted |
2464 | iexplore.exe | 142.250.185.100:443 | www.google.com | GOOGLE | US | whitelisted |
2464 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
2464 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
2464 | iexplore.exe | 172.217.16.195:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
2464 | iexplore.exe | 172.217.16.193:443 | afs.googleusercontent.com | GOOGLE | US | whitelisted |
2296 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
2296 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.uret.in |
| malicious |
www.google.com |
| malicious |
d38psrni17bvxu.cloudfront.net |
| suspicious |
partner.googleadservices.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
afs.googleusercontent.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |