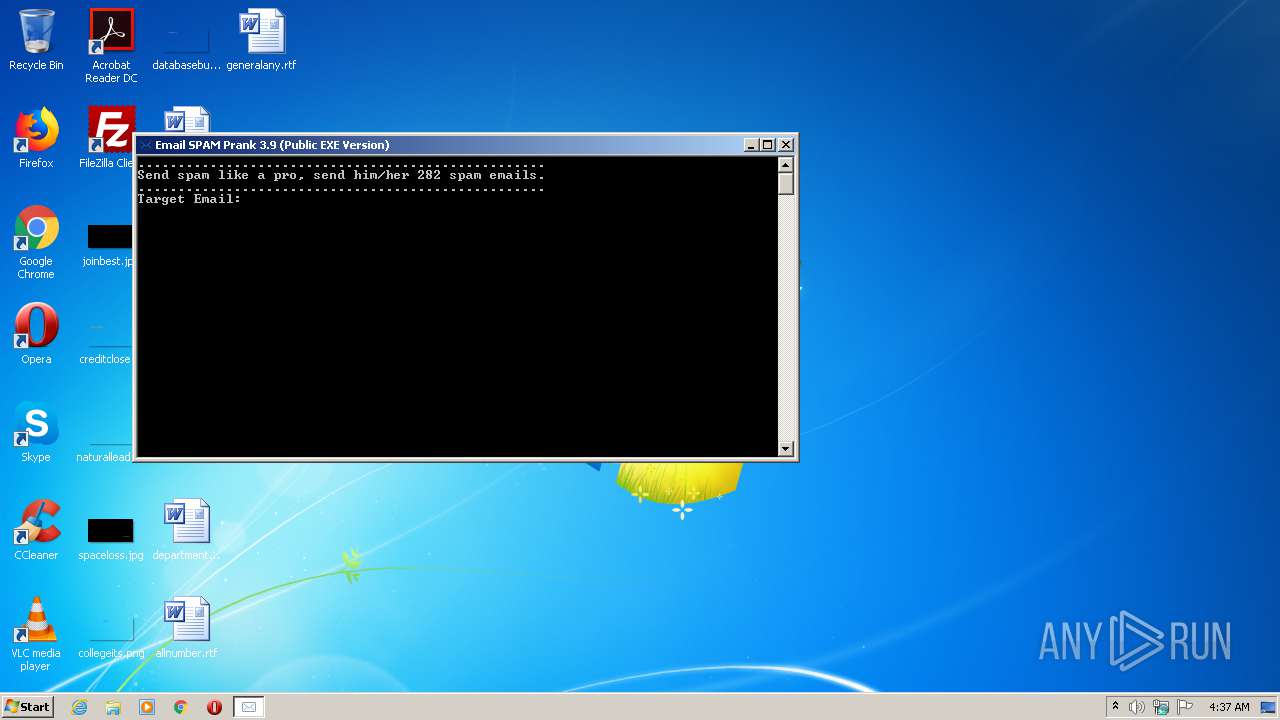
| File name: | Email SPAM Prank 3.9 (Public EXE Version).exe |
| Full analysis: | https://app.any.run/tasks/64076c8d-16be-4e72-ba1a-f39b86e5fe9d |
| Verdict: | Malicious activity |
| Analysis date: | February 13, 2021, 04:37:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | A86C725261A8135417CDE9419771A7D7 |
| SHA1: | D5E5D37EF1C6012D4B2CD5389A0AD513EA08BB6F |
| SHA256: | BE66246373FDFE1AE0FE70D1415F95734611CF76BABF2E226DEE816B6577F7C3 |
| SSDEEP: | 24576:cfU2UXJSCaOVIFHKkNsWG4GExr7bXqJo+vKpOLGl5Njw5+HypM:s2SCaOVIeF4Gir+zUDjw5ZC |
MALICIOUS
Application was dropped or rewritten from another process
- curl.exe (PID: 840)
- curl.exe (PID: 2524)
- curl.exe (PID: 4016)
- curl.exe (PID: 3620)
- curl.exe (PID: 2288)
SUSPICIOUS
Executable content was dropped or overwritten
- Email SPAM Prank 3.9 (Public EXE Version).exe (PID: 1044)
Starts CMD.EXE for commands execution
- Email SPAM Prank 3.9 (Public EXE Version).exe (PID: 1044)
Drops a file that was compiled in debug mode
- Email SPAM Prank 3.9 (Public EXE Version).exe (PID: 1044)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:05:11 00:18:20+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 86528 |
| InitializedDataSize: | 1847808 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x162c8 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 3.0.0.9 |
| ProductVersionNumber: | 3.0.0.9 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Microtech, LLC |
| FileDescription: | Send spam like a pro, send him/her 282 spam emails |
| FileVersion: | 3. 0. 0. 9 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| ProductName: | Email SPAM Prank 3.9 |
| ProductVersion: | 3. 0. 0. 9 |
| Comments: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 10-May-2016 22:18:20 |
| Detected languages: |
|
| CompanyName: | Microtech, LLC |
| FileDescription: | Send spam like a pro, send him/her 282 spam emails |
| FileVersion: | 3. 0. 0. 9 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | - |
| ProductName: | Email SPAM Prank 3.9 |
| ProductVersion: | 3. 0. 0. 9 |
| Comments: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 10-May-2016 22:18:20 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001448C | 0x00014600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50768 |
.itext | 0x00016000 | 0x00000A4C | 0x00000C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.57139 |
.data | 0x00017000 | 0x00000CAC | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.42854 |
.bss | 0x00018000 | 0x00005A60 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0001E000 | 0x00000D0E | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.74926 |
.tls | 0x0001F000 | 0x0000000C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00020000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.190489 |
.reloc | 0x00021000 | 0x00001A58 | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.50899 |
.rsrc | 0x00023000 | 0x001BF6D0 | 0x001BF800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.02113 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.30159 | 812 | Latin 1 / Western European | English - United States | RT_VERSION |
2 | 7.91664 | 8216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 2.08557 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 2.44637 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 1.29852 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 1.69999 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
99 | 2.75 | 8 | Latin 1 / Western European | UNKNOWN | UNKNOWN |
4090 | 3.38731 | 1732 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4091 | 3.34063 | 508 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.36196 | 204 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
SHFolder.dll |
advapi32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
40
Monitored processes
7
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
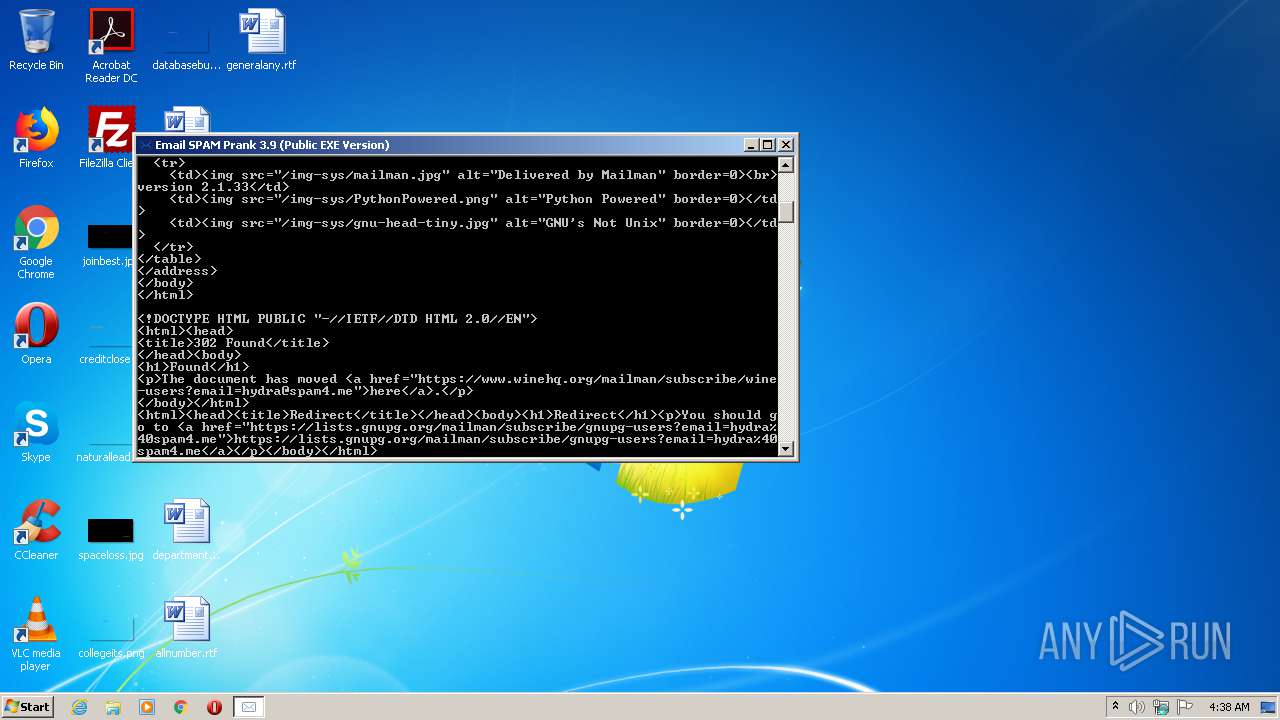
| 840 | C:\Users\admin\AppData\Local\qb129FB3.CC/curl.exe --get --insecure http://ml.ci.uc.pt/mailman/subscribe/archport?email=hydra@spam4.me | C:\Users\admin\AppData\Local\qb129FB3.CC\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.haxx.se/ Integrity Level: MEDIUM Description: The curl executable Exit code: 0 Version: 7.53.1 Modules
| |||||||||||||||
| 1044 | "C:\Users\admin\AppData\Local\Temp\Email SPAM Prank 3.9 (Public EXE Version).exe" | C:\Users\admin\AppData\Local\Temp\Email SPAM Prank 3.9 (Public EXE Version).exe | explorer.exe | ||||||||||||
User: admin Company: Microtech, LLC Integrity Level: MEDIUM Description: Send spam like a pro, send him/her 282 spam emails Exit code: 0 Version: 3. 0. 0. 9 Modules
| |||||||||||||||
| 2288 | C:\Users\admin\AppData\Local\qb129FB3.CC/curl.exe --get --insecure http://mailman.acomp.usf.edu/mailman/subscribe/lacsf?email=hydra@spam4.me | C:\Users\admin\AppData\Local\qb129FB3.CC\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.haxx.se/ Integrity Level: MEDIUM Description: The curl executable Exit code: 0 Version: 7.53.1 Modules
| |||||||||||||||
| 2524 | C:\Users\admin\AppData\Local\qb129FB3.CC/curl.exe --get --insecure http://flybynews.com/mailman/subscribe/flybynews_flybynews.com?email=hydra@spam4.me | C:\Users\admin\AppData\Local\qb129FB3.CC\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.haxx.se/ Integrity Level: MEDIUM Description: The curl executable Exit code: 0 Version: 7.53.1 Modules
| |||||||||||||||
| 2980 | cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\4OWPCYQM.bat" "C:\Users\admin\AppData\Local\Temp\Email SPAM Prank 3.9 (Public EXE Version).exe" " | C:\Windows\system32\cmd.exe | — | Email SPAM Prank 3.9 (Public EXE Version).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3620 | C:\Users\admin\AppData\Local\qb129FB3.CC/curl.exe --get --insecure http://lists.gnupg.org/mailman/subscribe/gnupg-users?email=hydra@spam4.me | C:\Users\admin\AppData\Local\qb129FB3.CC\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.haxx.se/ Integrity Level: MEDIUM Description: The curl executable Exit code: 0 Version: 7.53.1 Modules
| |||||||||||||||
| 4016 | C:\Users\admin\AppData\Local\qb129FB3.CC/curl.exe --get --insecure http://www.winehq.org/mailman/subscribe/wine-users?email=hydra@spam4.me | C:\Users\admin\AppData\Local\qb129FB3.CC\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.haxx.se/ Integrity Level: MEDIUM Description: The curl executable Exit code: 0 Version: 7.53.1 Modules
| |||||||||||||||
Total events
44
Read events
44
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1044 | Email SPAM Prank 3.9 (Public EXE Version).exe | C:\Users\admin\AppData\Local\Temp\4OWPCYQM.bat | text | |
MD5:— | SHA256:— | |||
| 1044 | Email SPAM Prank 3.9 (Public EXE Version).exe | C:\Users\admin\AppData\Local\qb129FB3.CC\curl.exe | executable | |
MD5:6149AF05AD1F5984CCC38A7A38E5127E | SHA256:FBF5A2417837819297A35CF0B63D684E95530BEFE137377E8CFE81E77A8F752C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
5
DNS requests
6
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | — | 131.247.250.88:80 | http://mailman.acomp.usf.edu/mailman/subscribe/lacsf?email=hydra@spam4.me | US | — | — | unknown |
840 | curl.exe | GET | 404 | 193.137.200.156:80 | http://ml.ci.uc.pt/mailman/subscribe/archport?email=hydra@spam4.me | PT | html | 300 b | suspicious |
2524 | curl.exe | GET | 200 | 216.37.42.100:80 | http://flybynews.com/mailman/subscribe/flybynews_flybynews.com?email=hydra@spam4.me | US | html | 1.17 Kb | suspicious |
3620 | curl.exe | GET | 307 | 217.69.76.57:80 | http://lists.gnupg.org/mailman/subscribe/gnupg-users?email=hydra@spam4.me | DE | html | 270 b | suspicious |
4016 | curl.exe | GET | 302 | 4.4.81.124:80 | http://www.winehq.org/mailman/subscribe/wine-users?email=hydra@spam4.me | US | html | 256 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
840 | curl.exe | 193.137.200.156:80 | ml.ci.uc.pt | Fundacao para a Ciencia e a Tecnologia, I.P. | PT | suspicious |
2524 | curl.exe | 216.37.42.100:80 | flybynews.com | CONTINENTAL BROADBAND PENNSYLVANIA, INC. | US | suspicious |
4016 | curl.exe | 4.4.81.124:80 | www.winehq.org | Level 3 Communications, Inc. | US | suspicious |
3620 | curl.exe | 217.69.76.57:80 | lists.gnupg.org | PlusServer GmbH | DE | suspicious |
— | — | 131.247.250.88:80 | mailman.acomp.usf.edu | UNIVERSITY OF SOUTH FLORIDA | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ml.ci.uc.pt |
| suspicious |
flybynews.com |
| suspicious |
www.winehq.org |
| suspicious |
lists.gnupg.org |
| suspicious |
mailman.acomp.usf.edu |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
840 | curl.exe | Attempted Information Leak | ET POLICY curl User-Agent Outbound |
2524 | curl.exe | Attempted Information Leak | ET POLICY curl User-Agent Outbound |
4016 | curl.exe | Attempted Information Leak | ET POLICY curl User-Agent Outbound |
3620 | curl.exe | Attempted Information Leak | ET POLICY curl User-Agent Outbound |