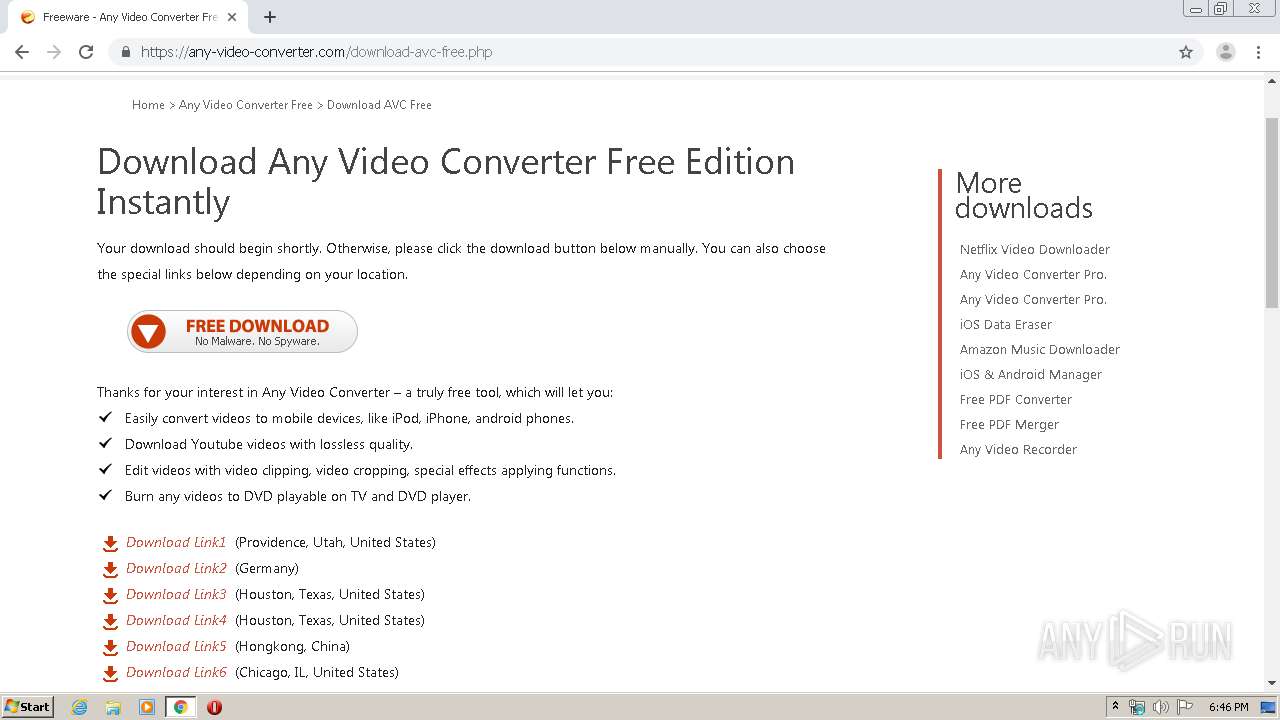
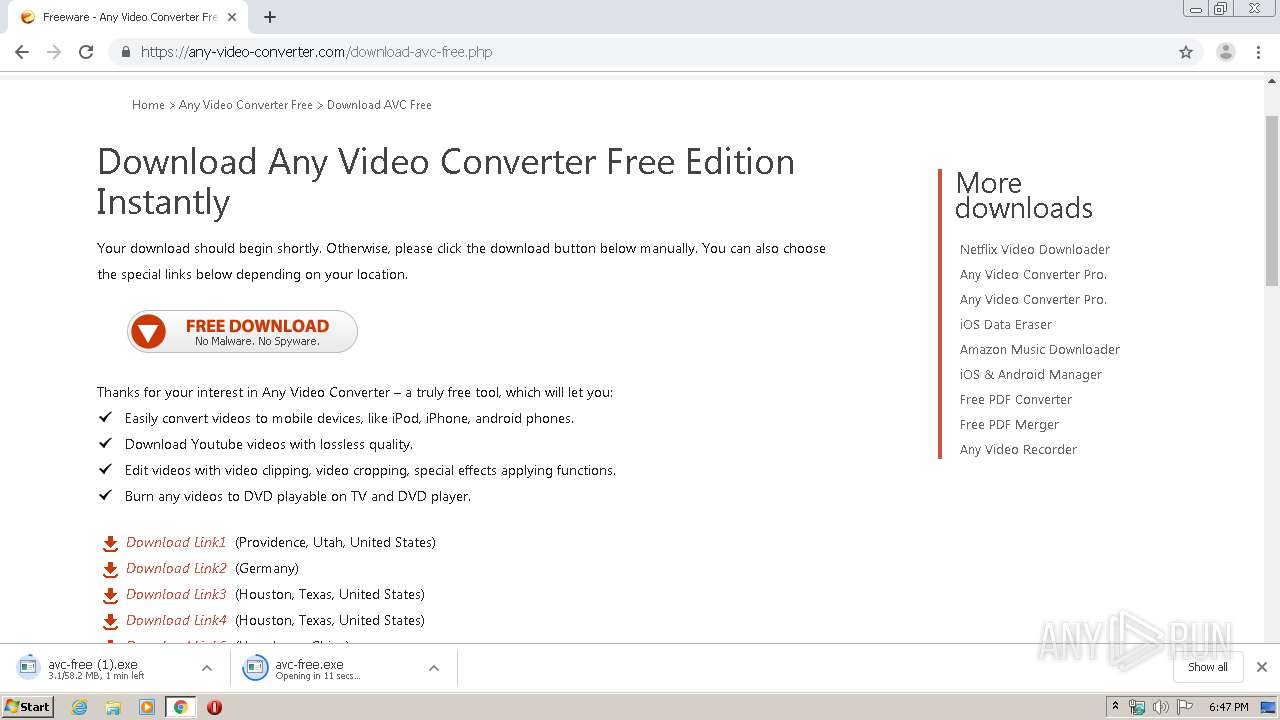
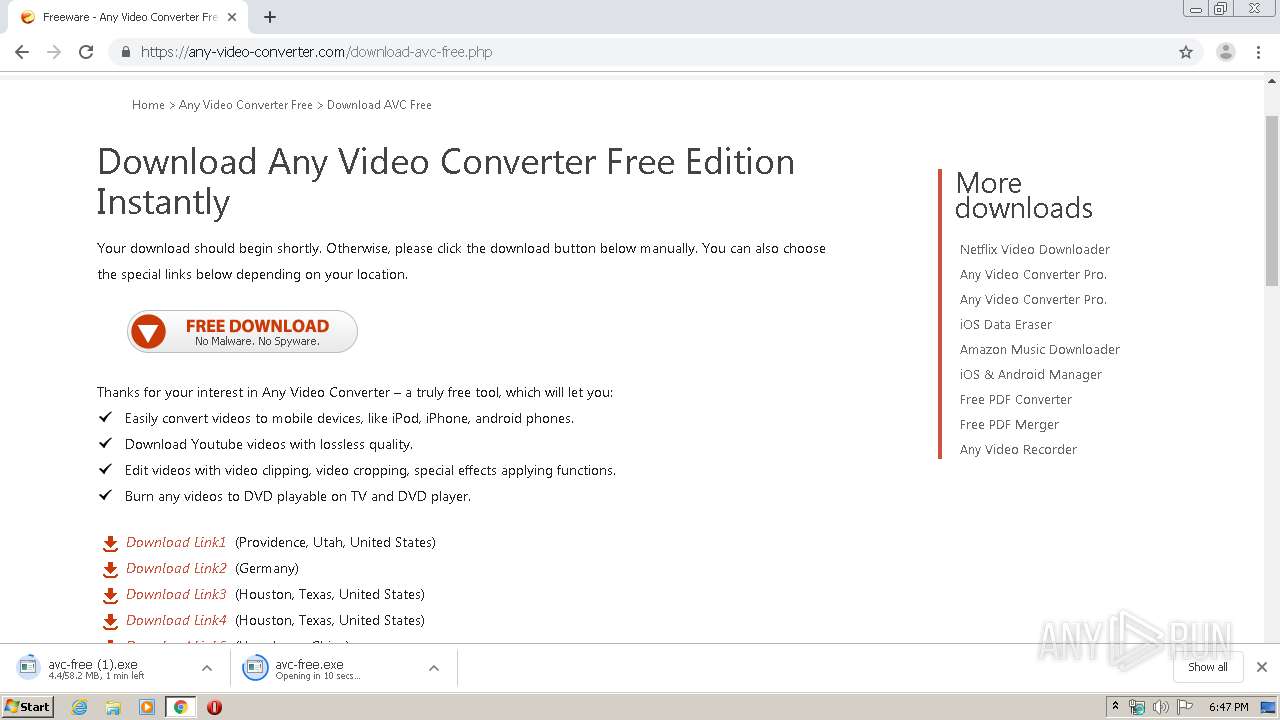
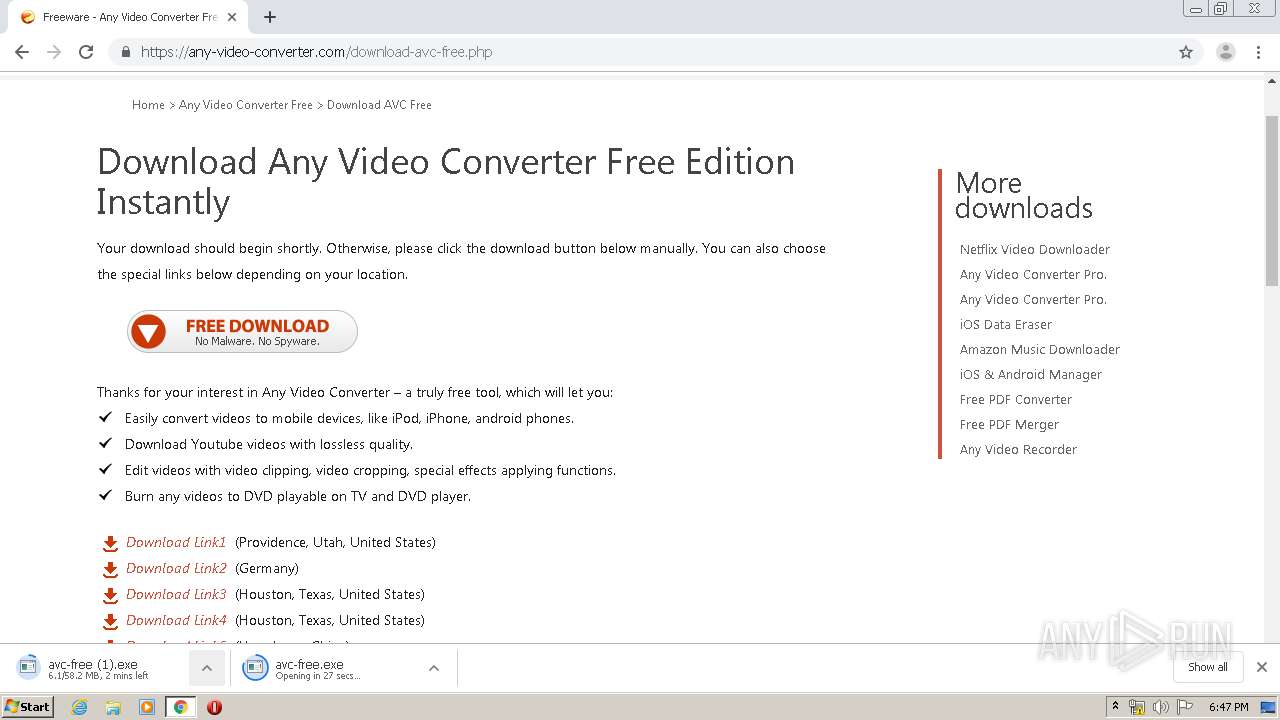
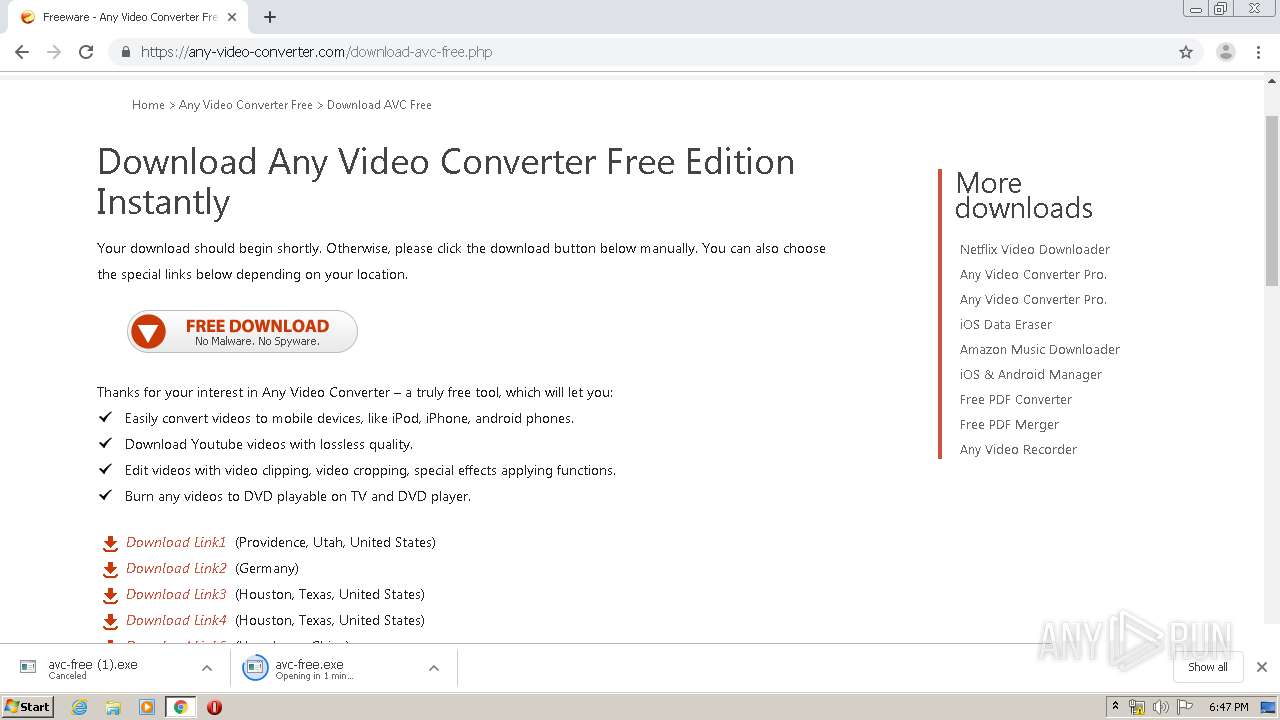
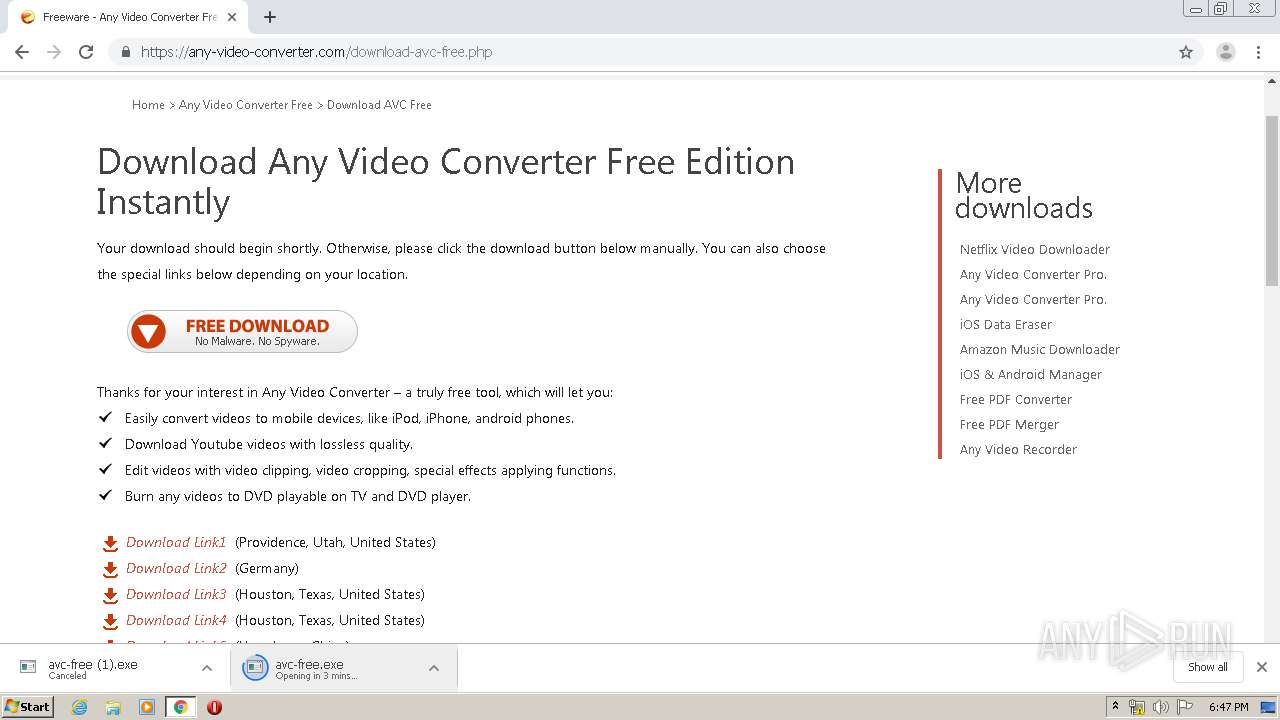
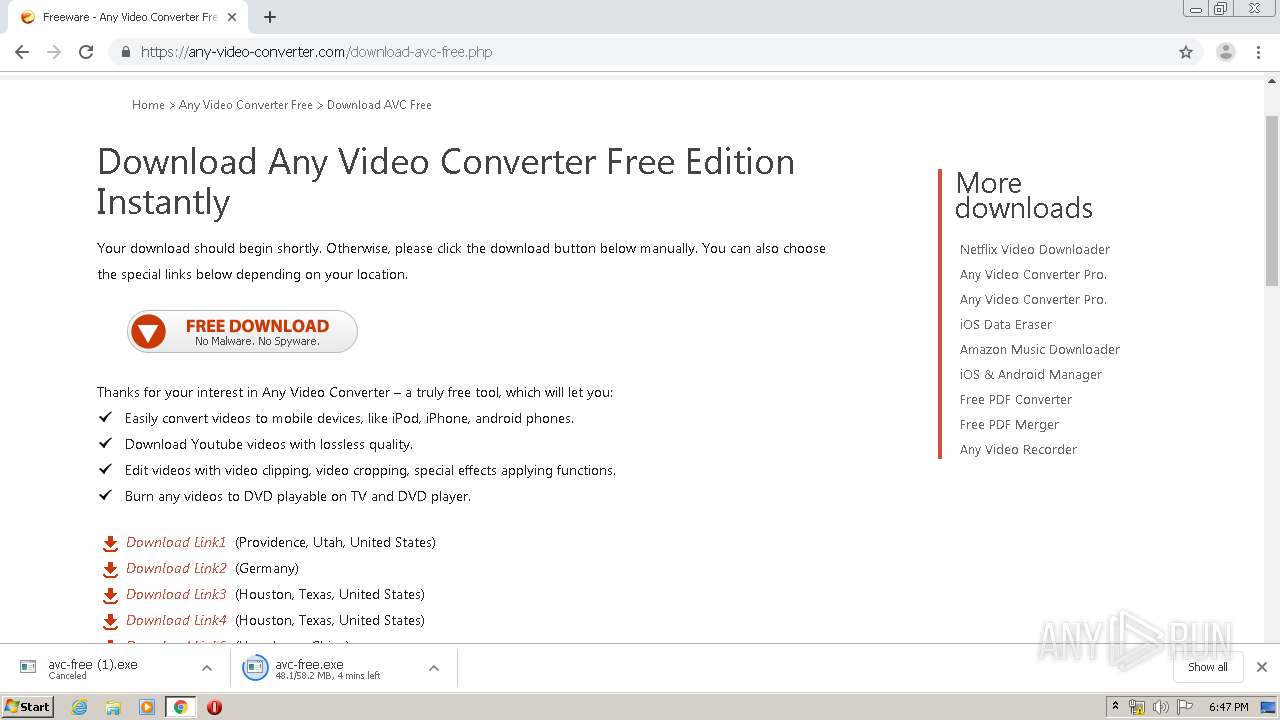
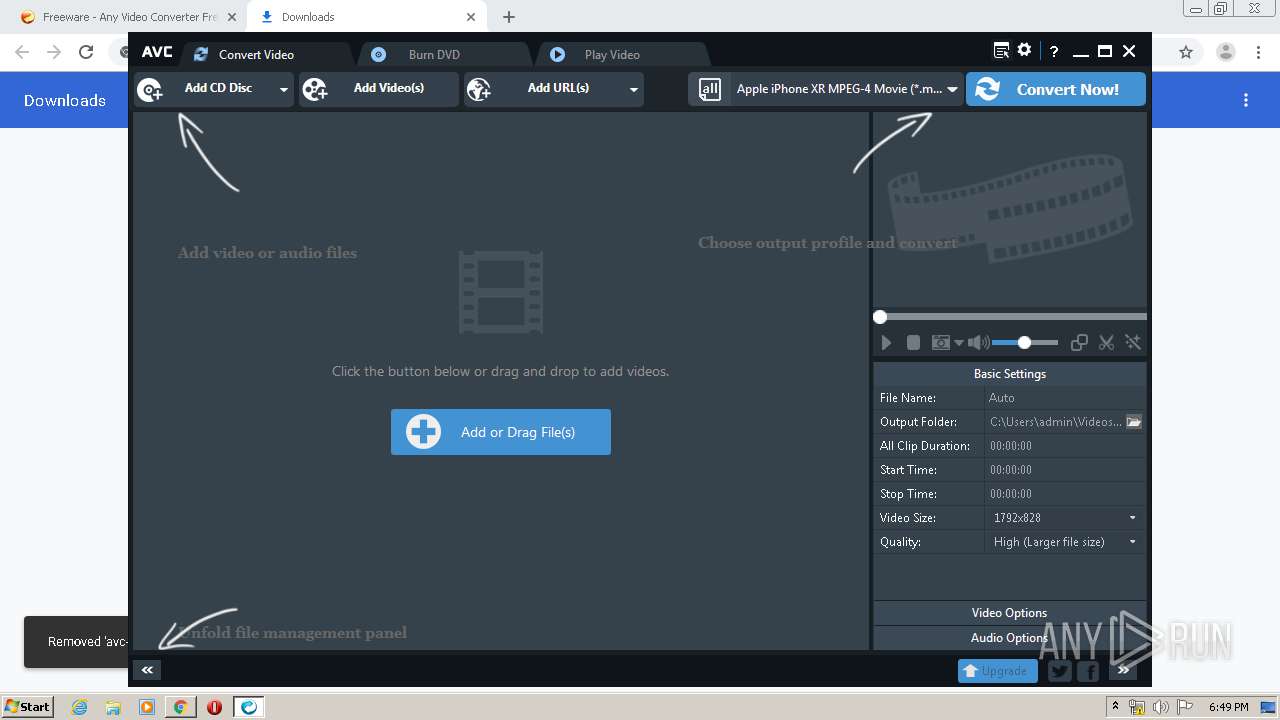
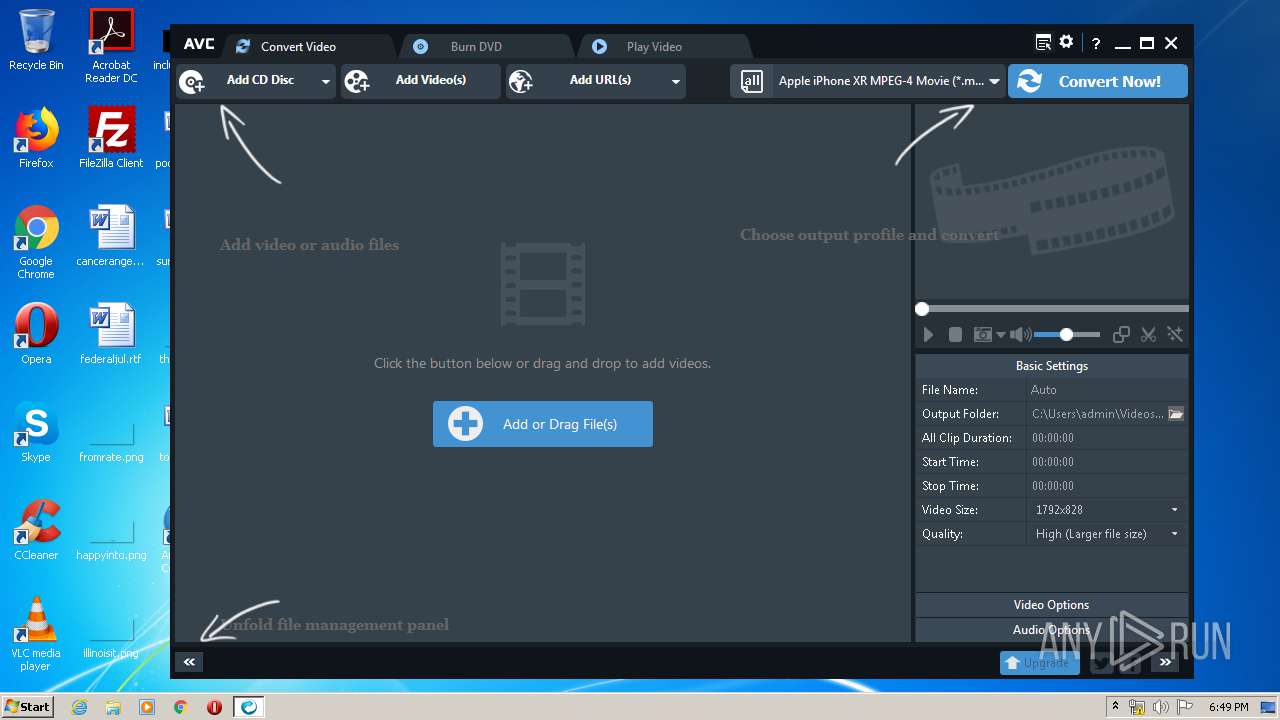
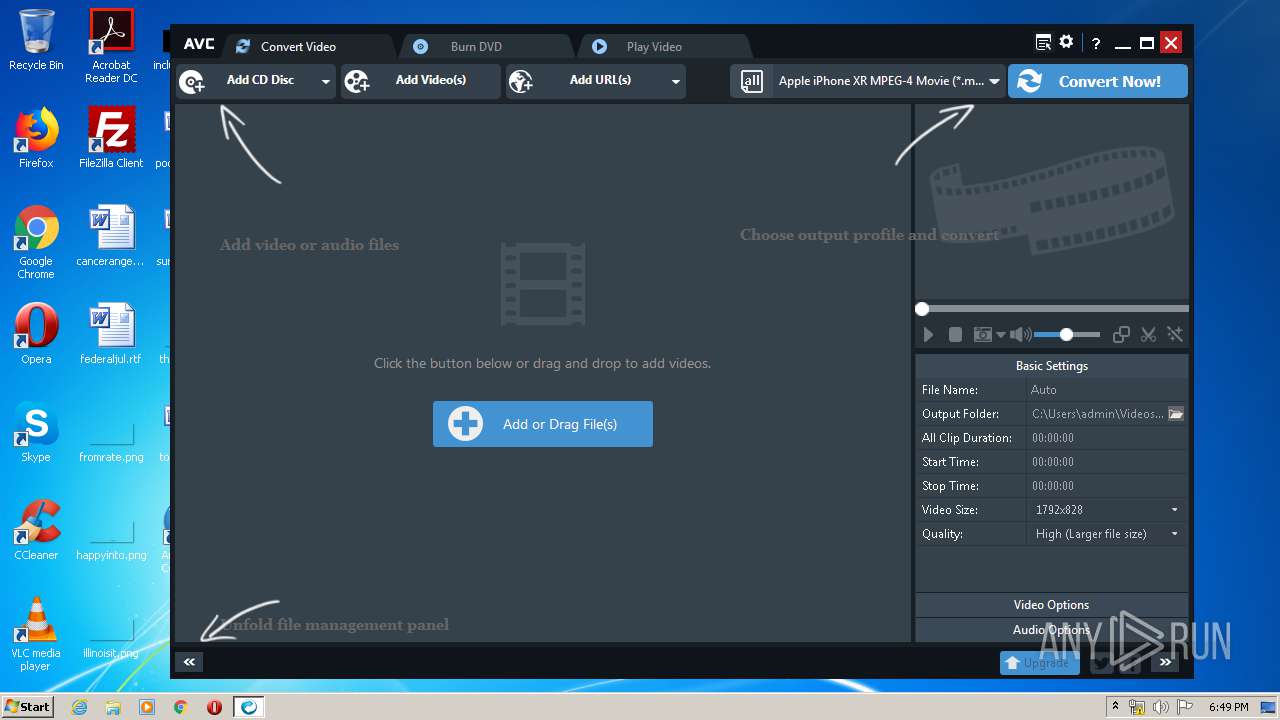
| URL: | https://any-video-converter.com/products/for_video_free/ |
| Full analysis: | https://app.any.run/tasks/78a4a865-98fb-49fc-8087-26a83b3503d3 |
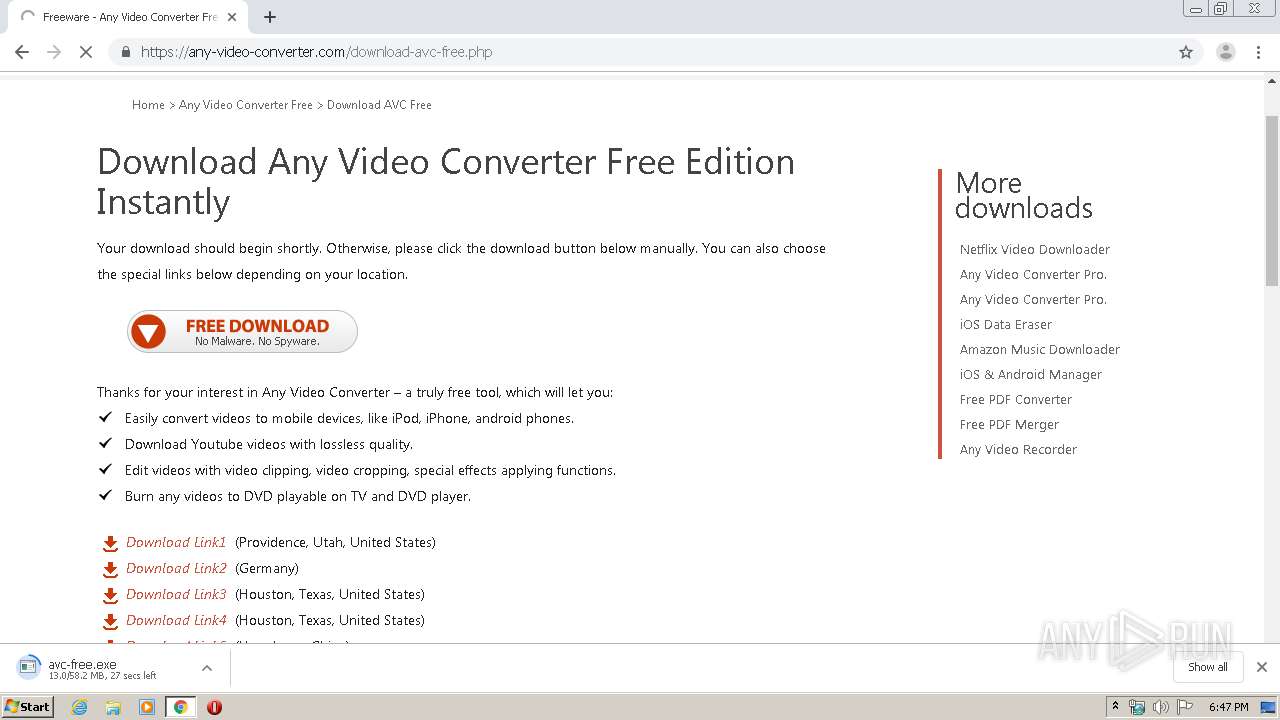
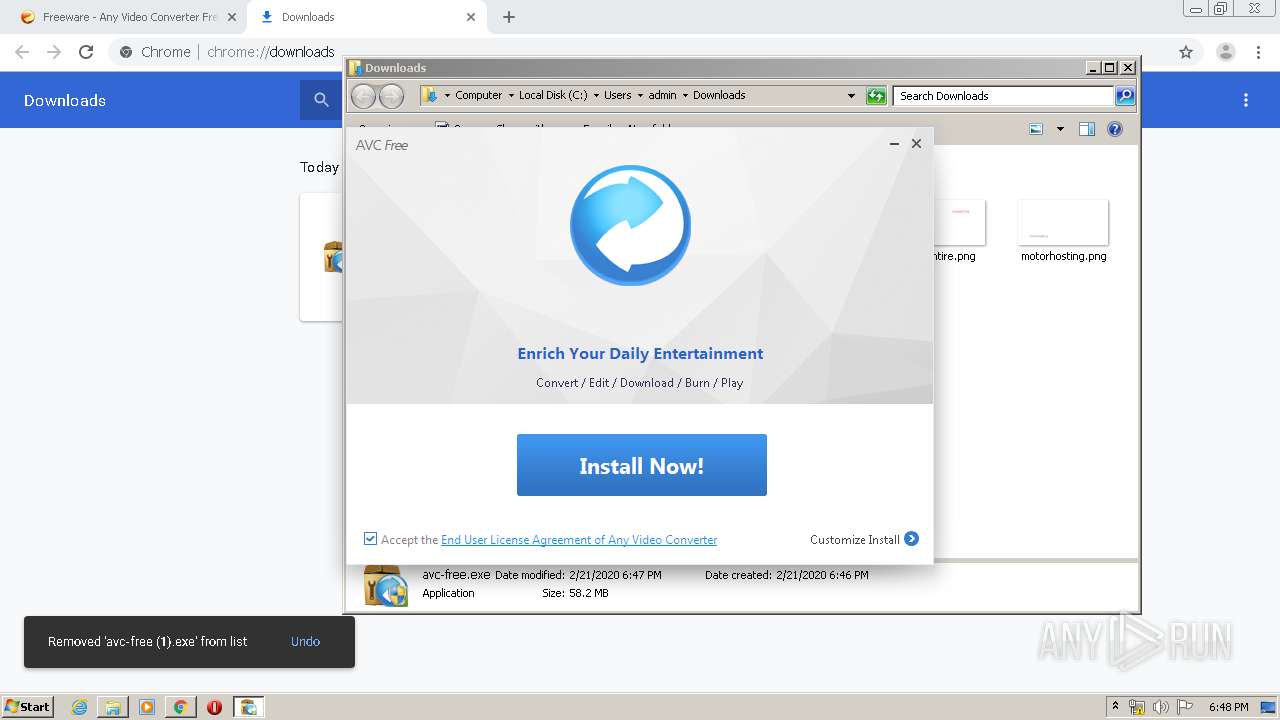
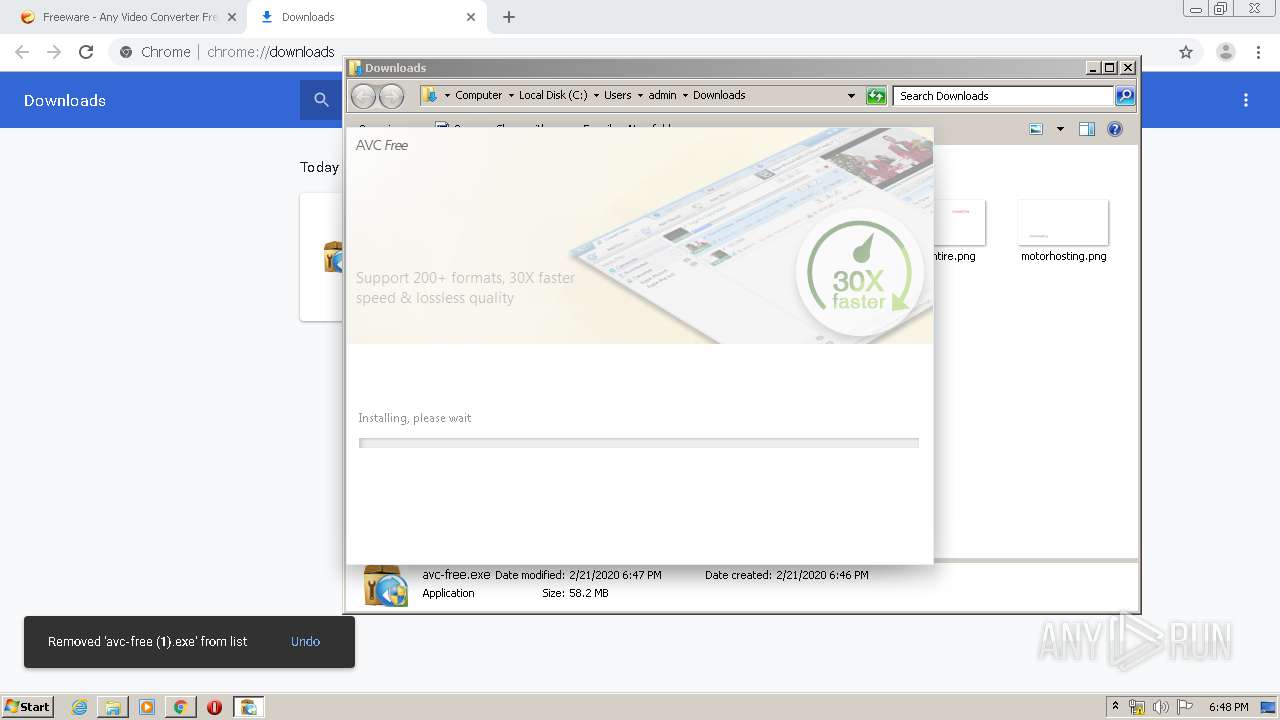
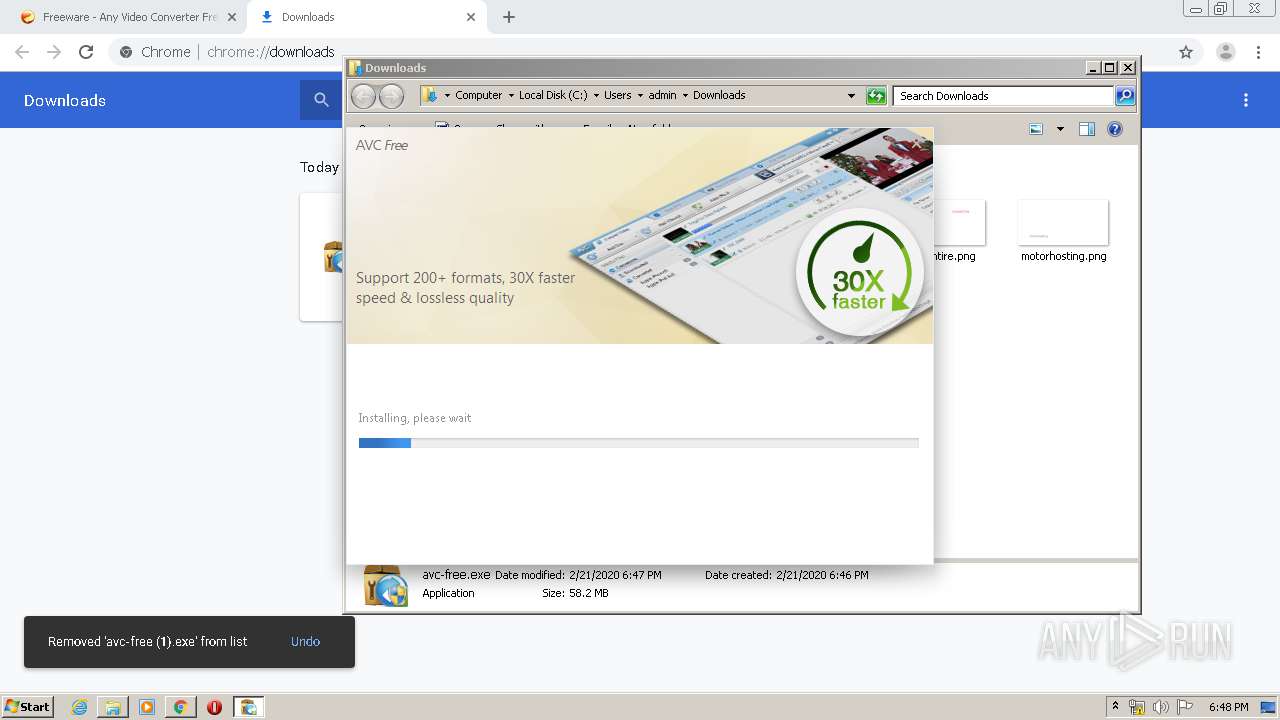
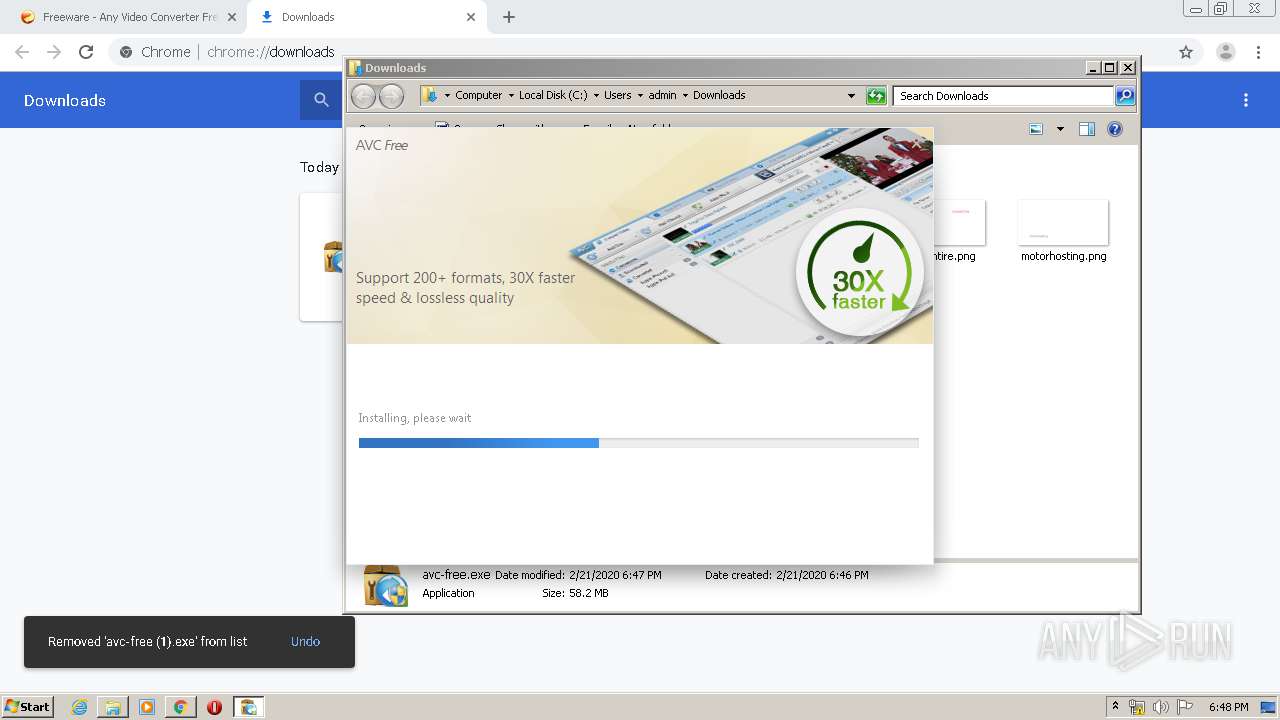
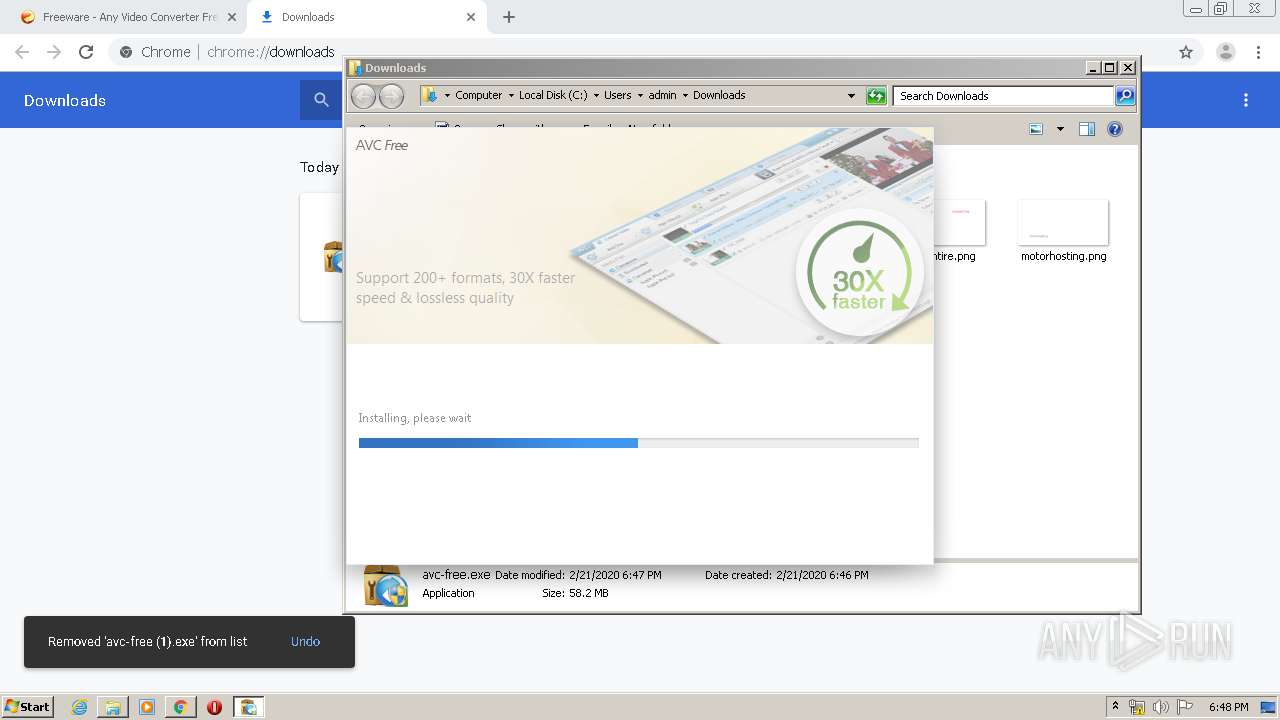
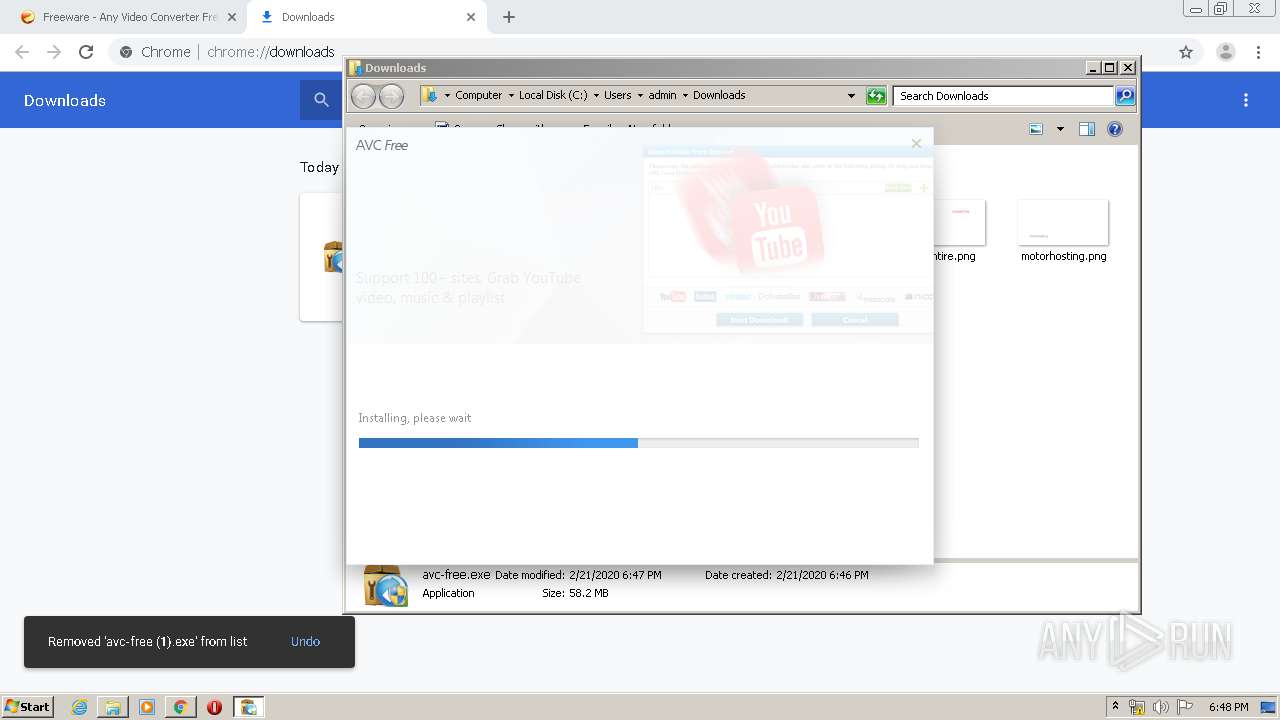
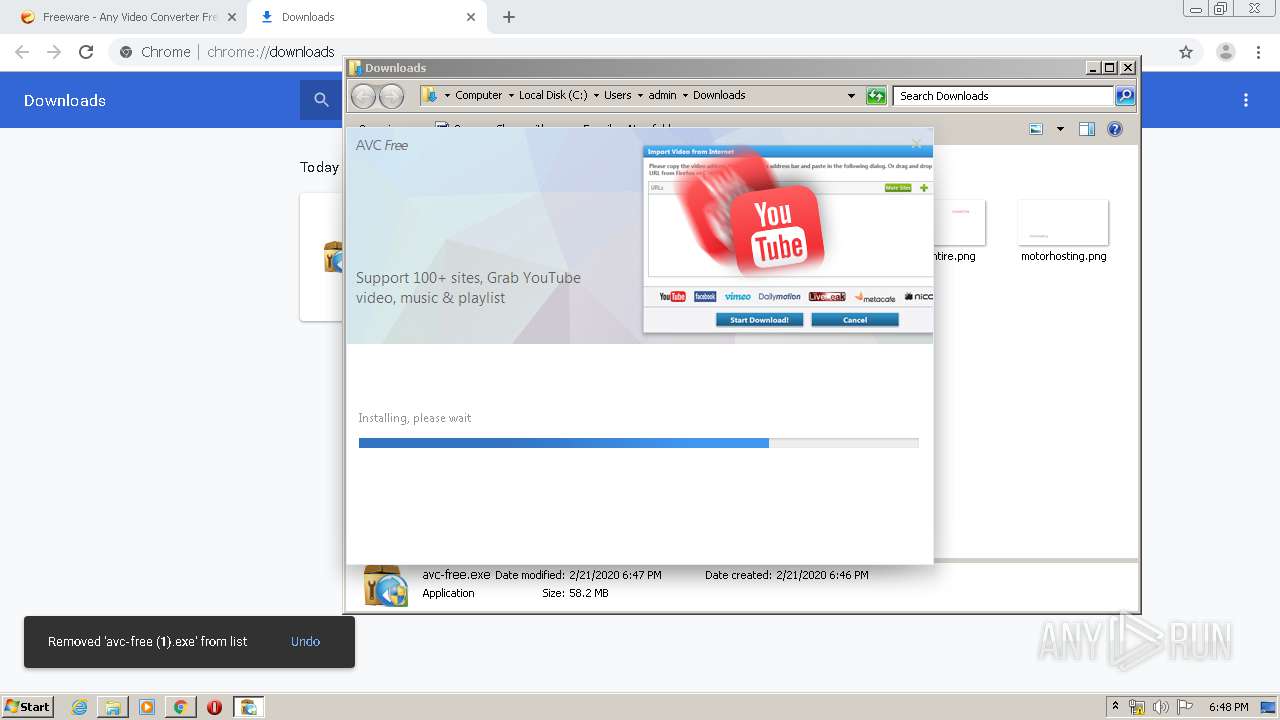
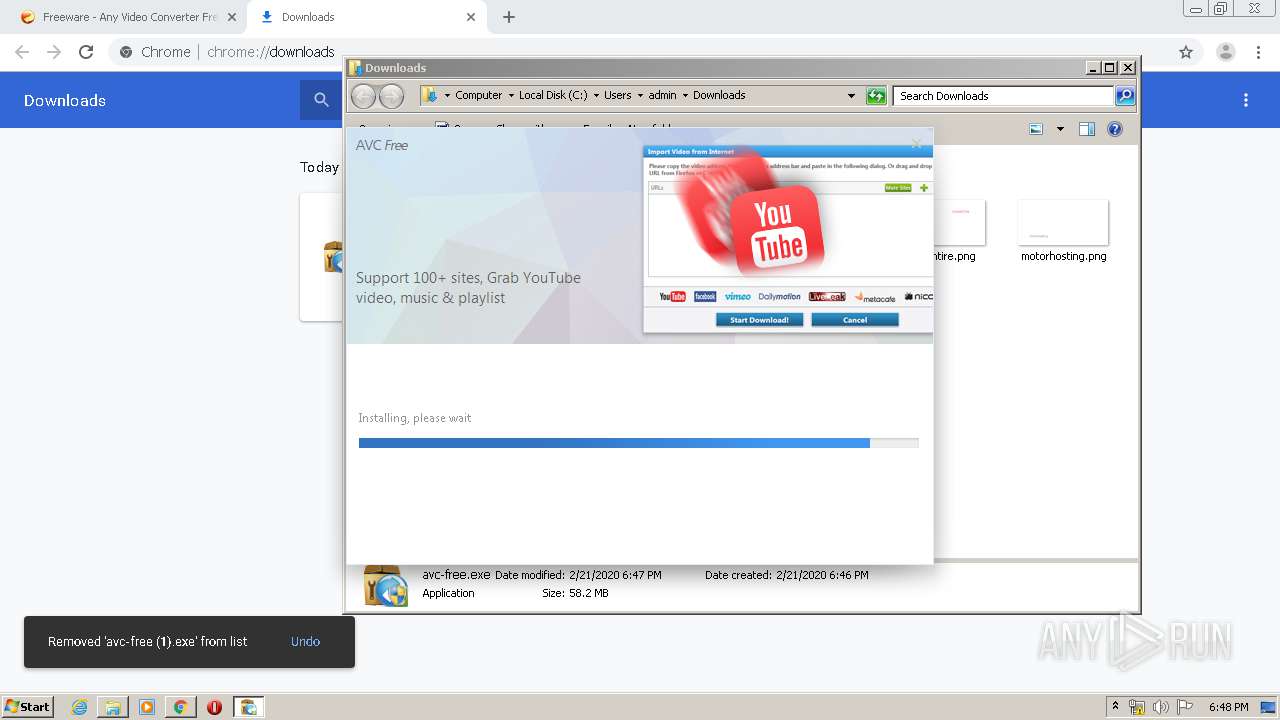
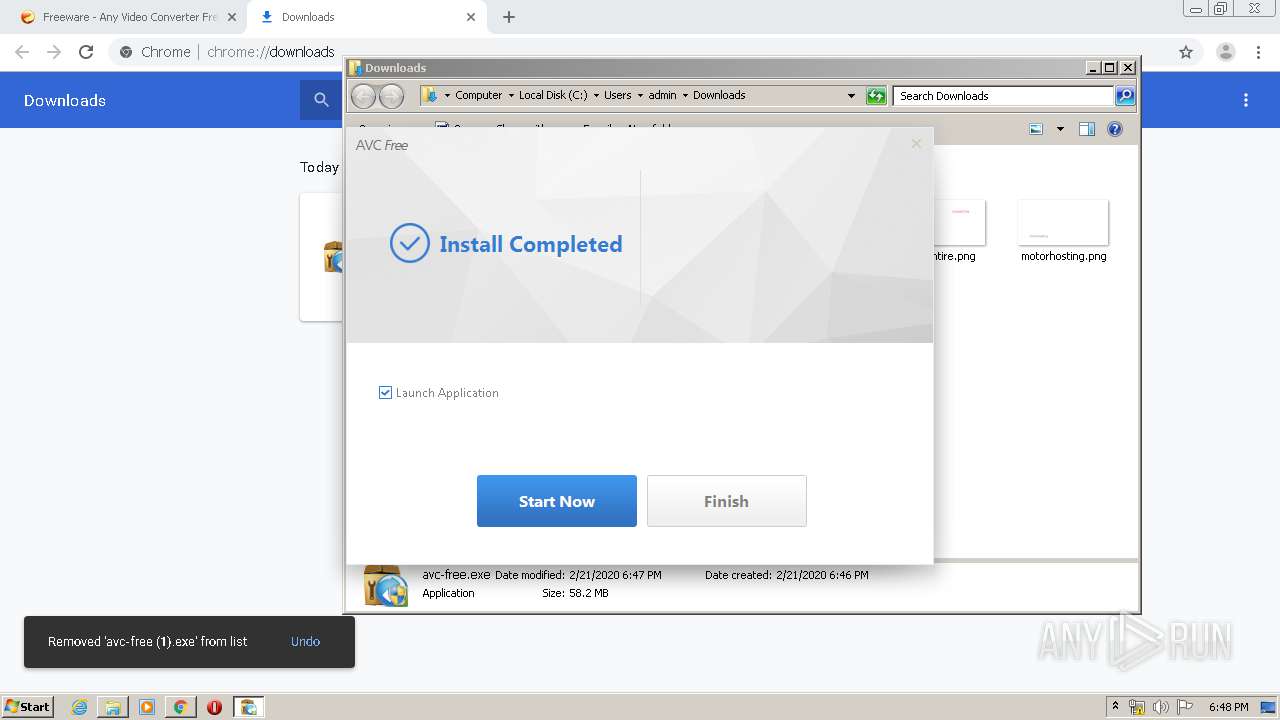
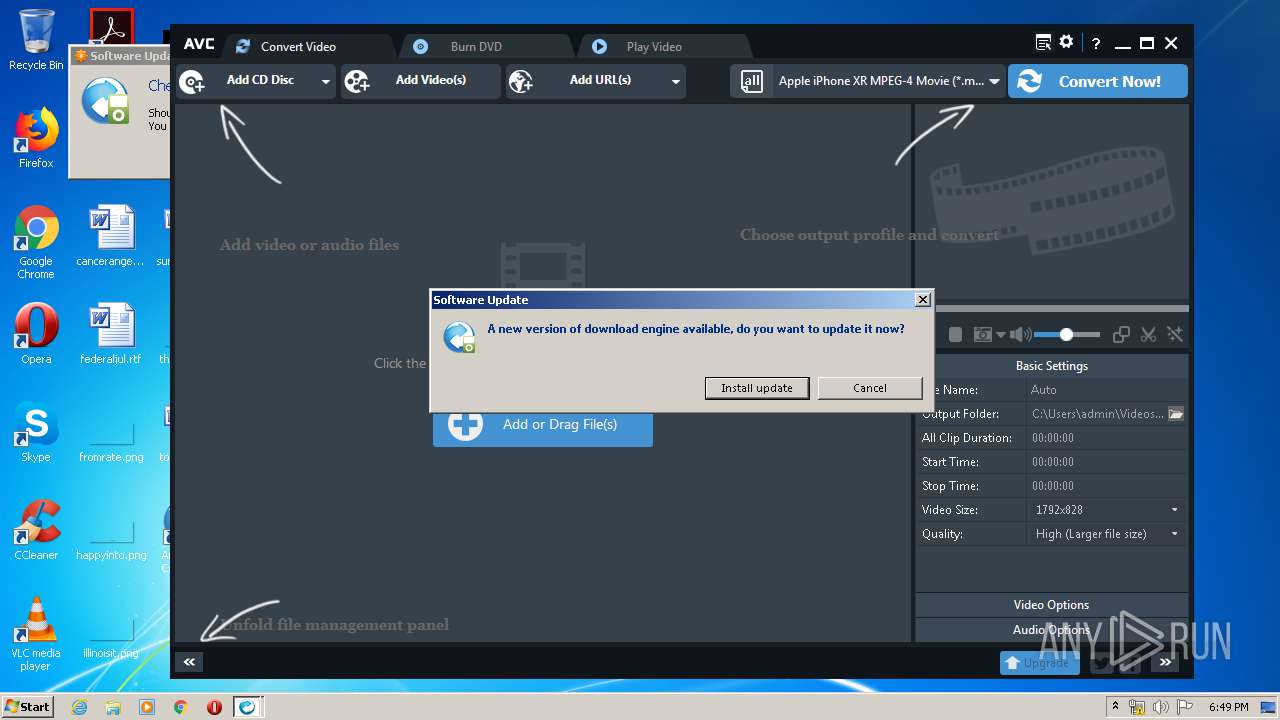
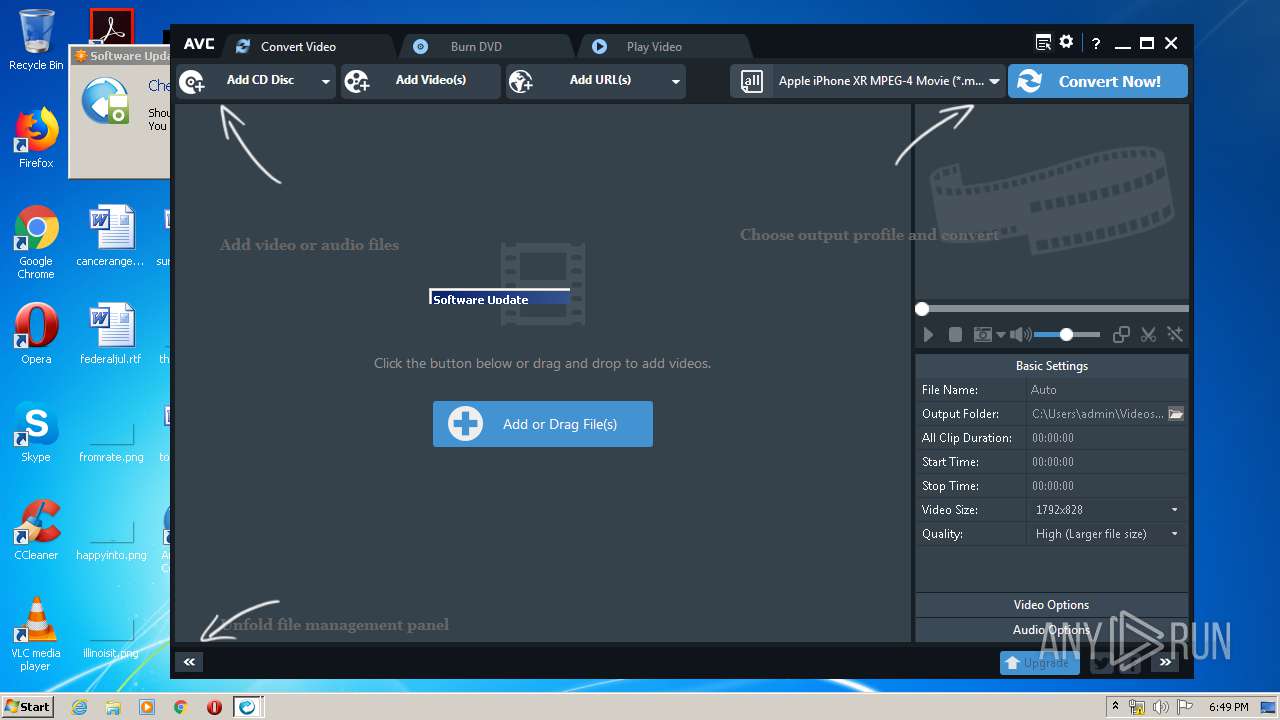
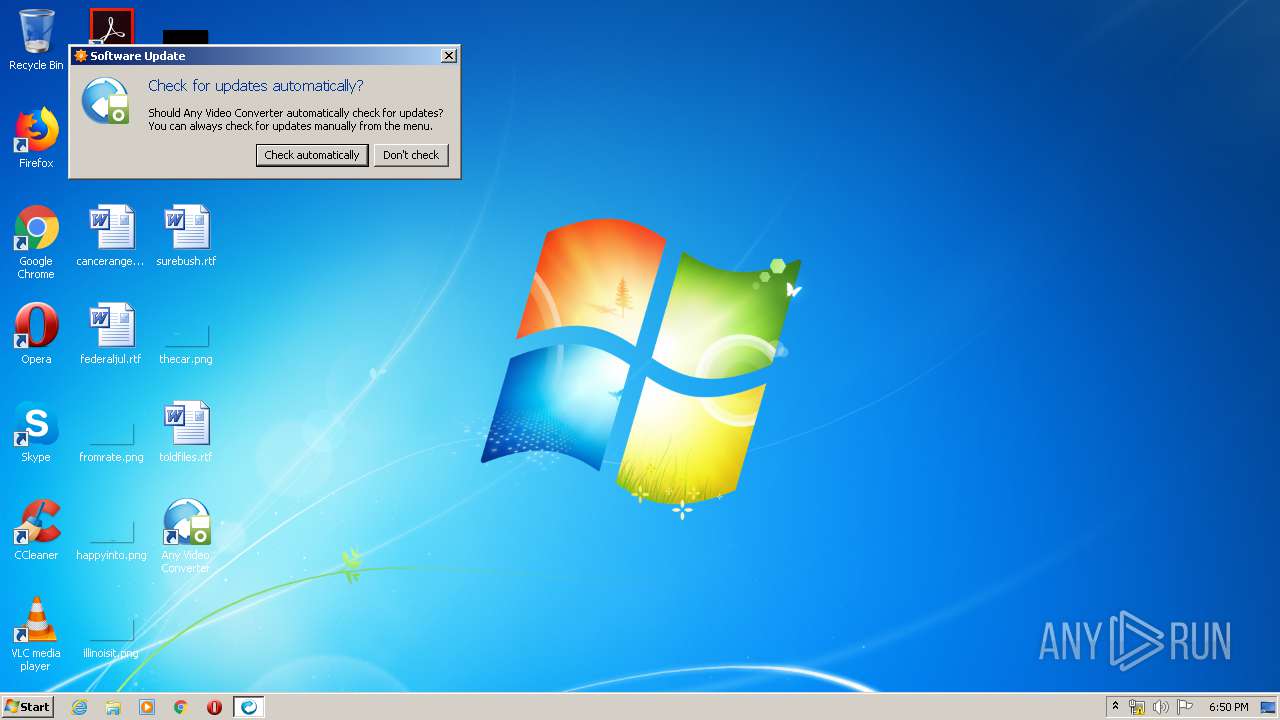
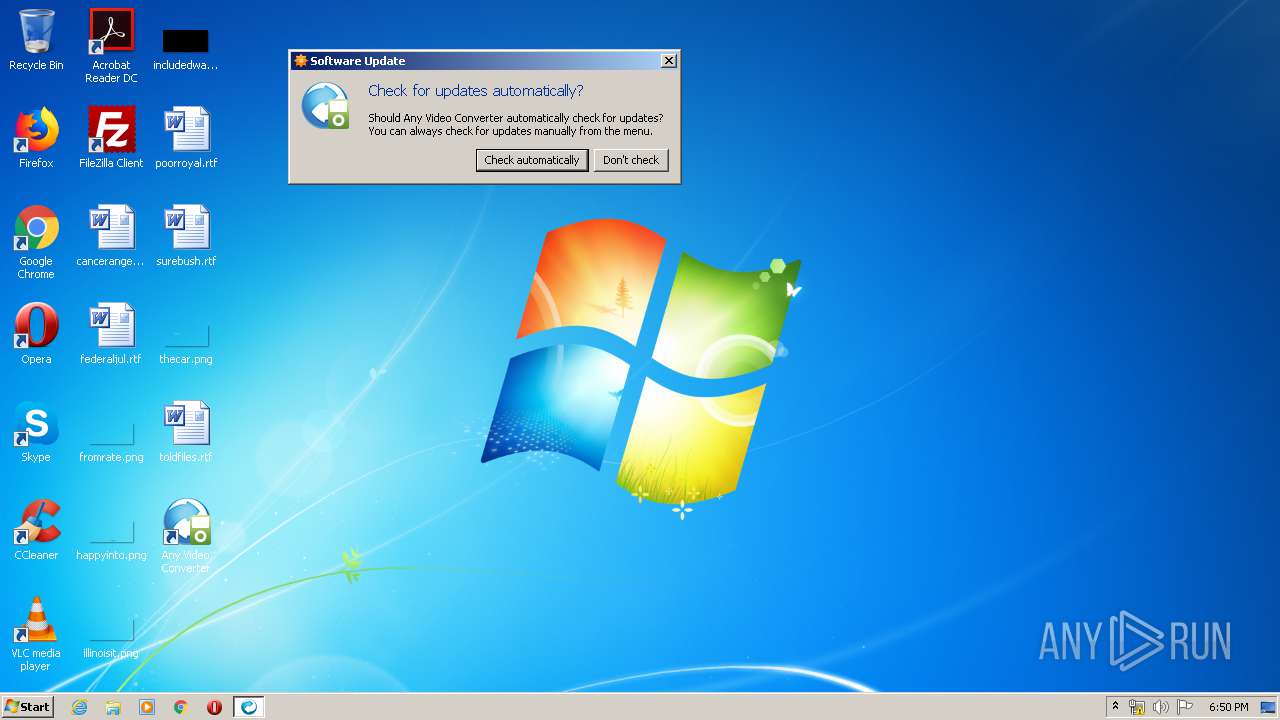
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2020, 18:46:11 |
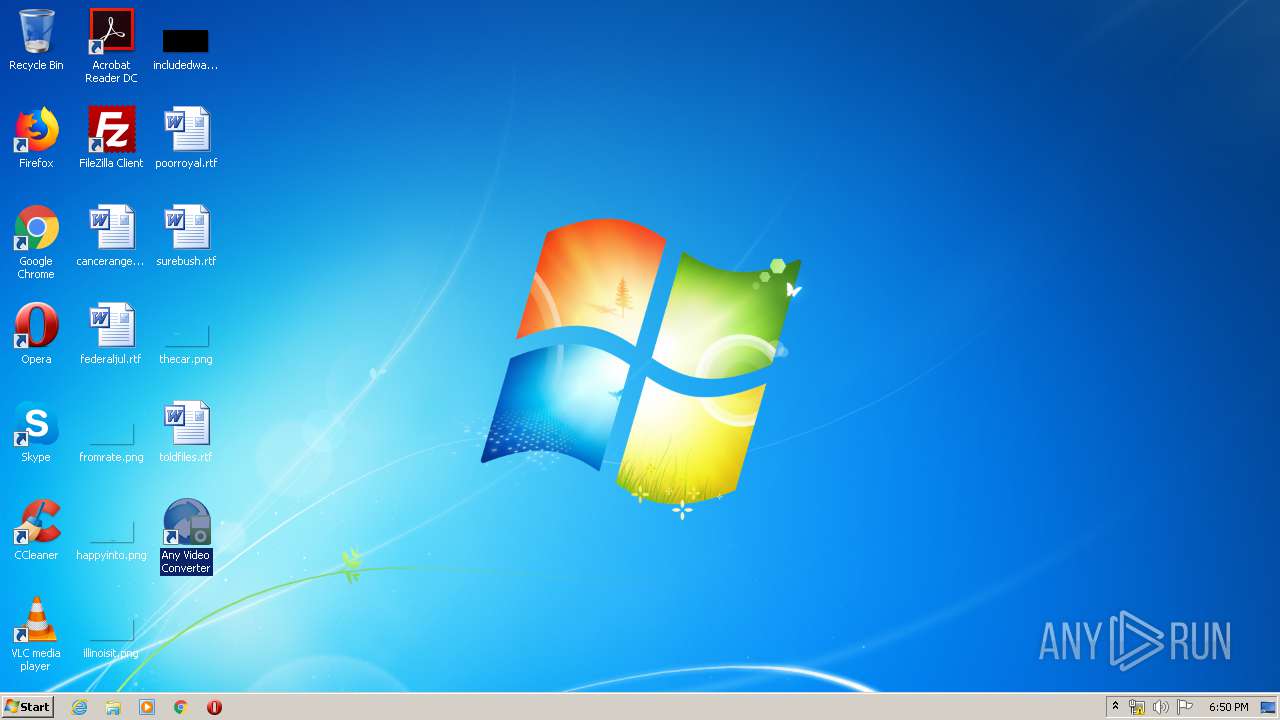
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BFDBB6EE5CAB79D4AA964CA38460B7F4 |
| SHA1: | 5ECE95725EFA376E424323C0AECB4C061A9B420C |
| SHA256: | BE6595ED07E4734B1770D3AFD95ECA35D5513FD7B81D9FBE18F94BE2BA440E3B |
| SSDEEP: | 3:N8mQQMuaQGRWYM6TlKDn:2IMfRWol2n |
MALICIOUS
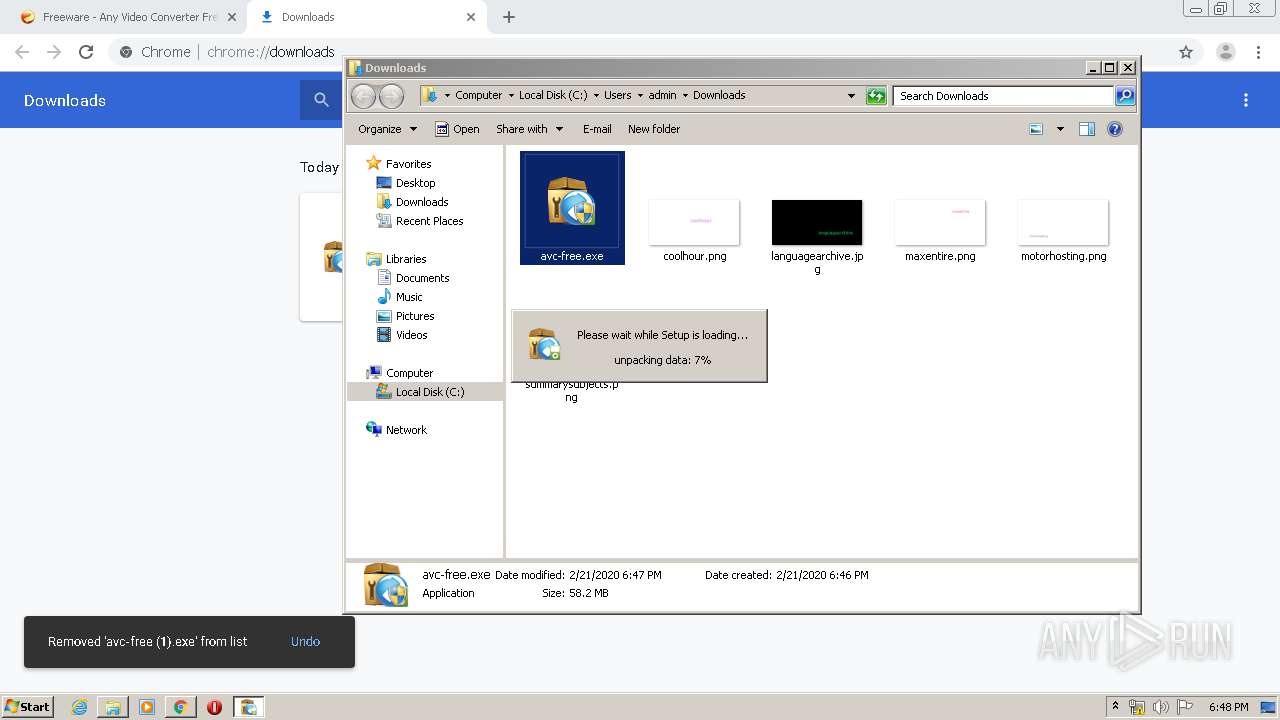
Application was dropped or rewritten from another process
- avc-free.exe (PID: 2960)
- avc-free.exe (PID: 3816)
- youtube-dl.exe (PID: 2928)
- AVCFree.exe (PID: 1932)
- AVCFree.exe (PID: 2856)
- youtube-dl.exe (PID: 2852)
Loads dropped or rewritten executable
- avc-free.exe (PID: 3816)
- AVCFree.exe (PID: 1932)
- youtube-dl.exe (PID: 2928)
- AVCFree.exe (PID: 2856)
- youtube-dl.exe (PID: 2852)
Detects Cygwin installation
- avc-free.exe (PID: 3816)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3852)
Executable content was dropped or overwritten
- chrome.exe (PID: 2740)
- chrome.exe (PID: 3852)
- avc-free.exe (PID: 3816)
- AVCFree.exe (PID: 1932)
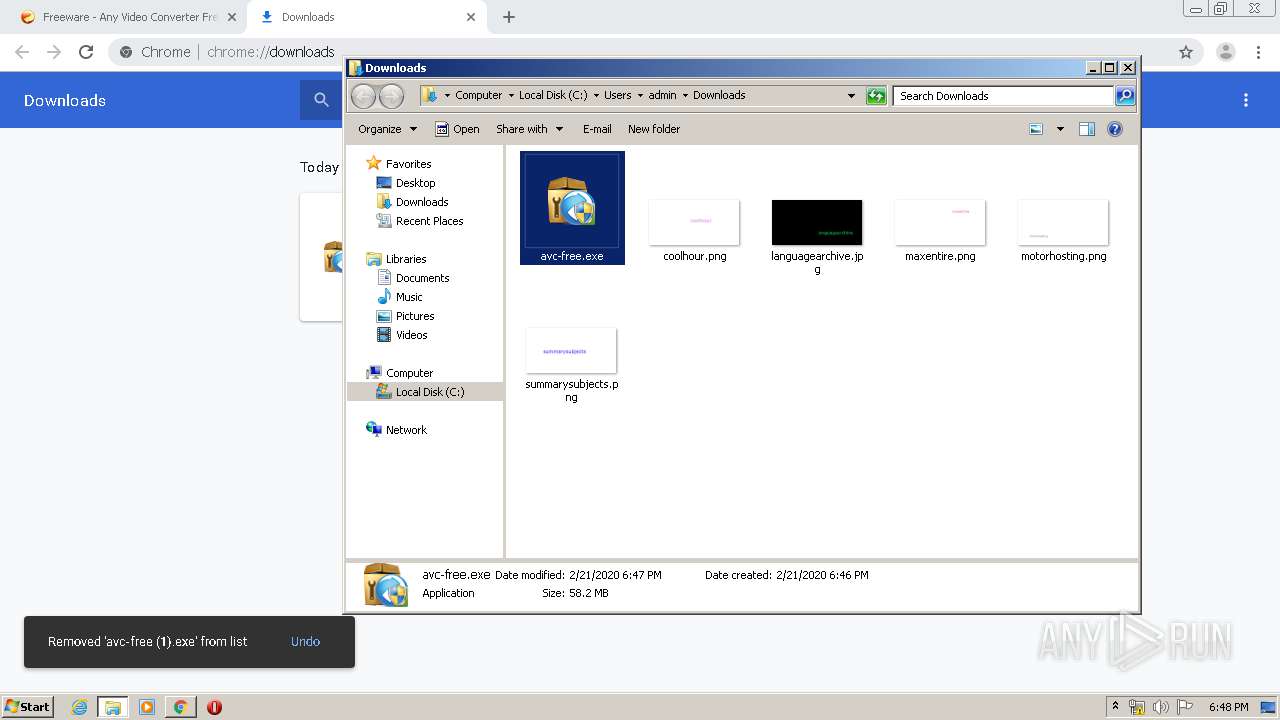
Creates files in the user directory
- avc-free.exe (PID: 3816)
- AVCFree.exe (PID: 1932)
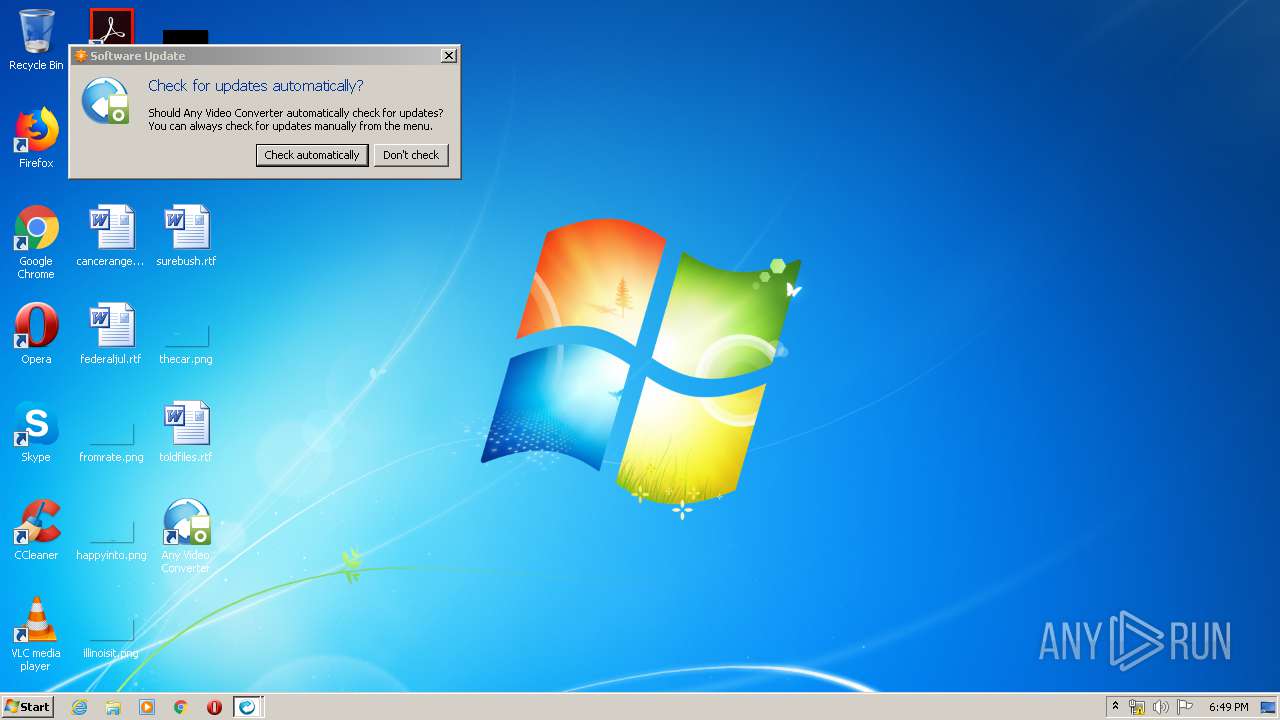
Creates a software uninstall entry
- avc-free.exe (PID: 3816)
Writes to a desktop.ini file (may be used to cloak folders)
- avc-free.exe (PID: 3816)
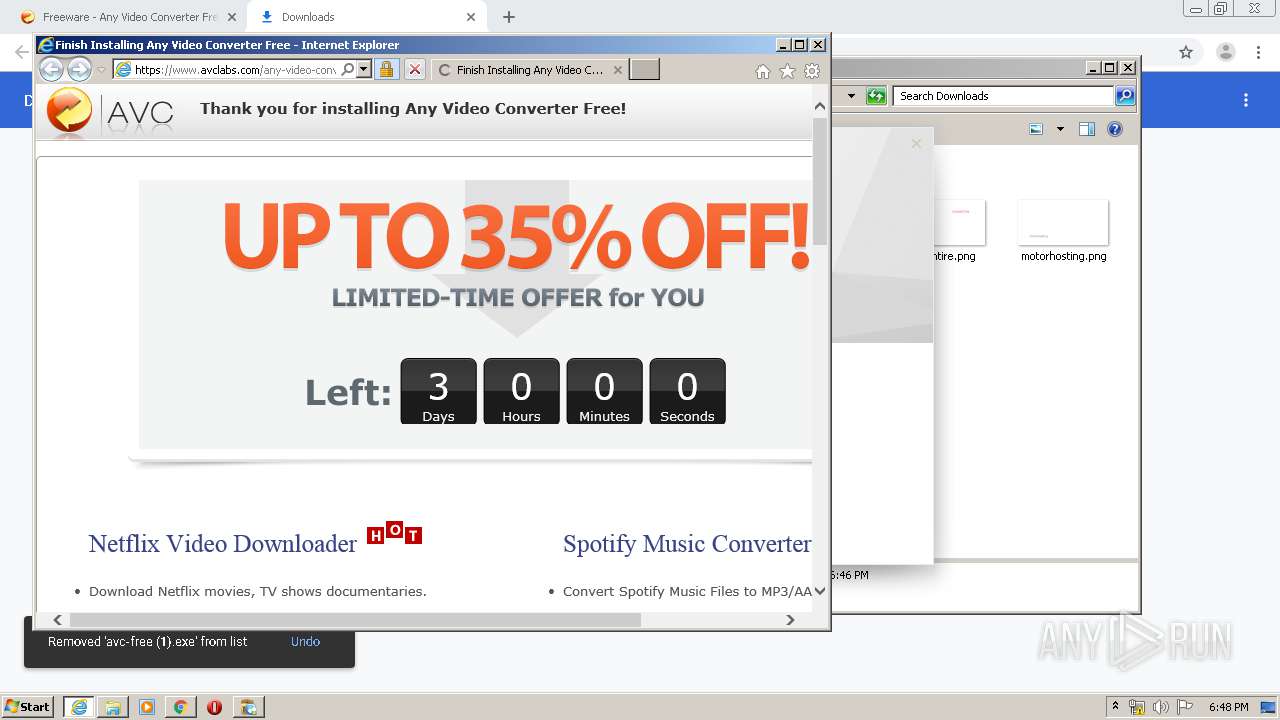
Starts Internet Explorer
- avc-free.exe (PID: 3816)
Starts CMD.EXE for commands execution
- AVCFree.exe (PID: 1932)
- AVCFree.exe (PID: 2856)
Reads Internet Cache Settings
- AVCFree.exe (PID: 1932)
- AVCFree.exe (PID: 2856)
Creates files in the program directory
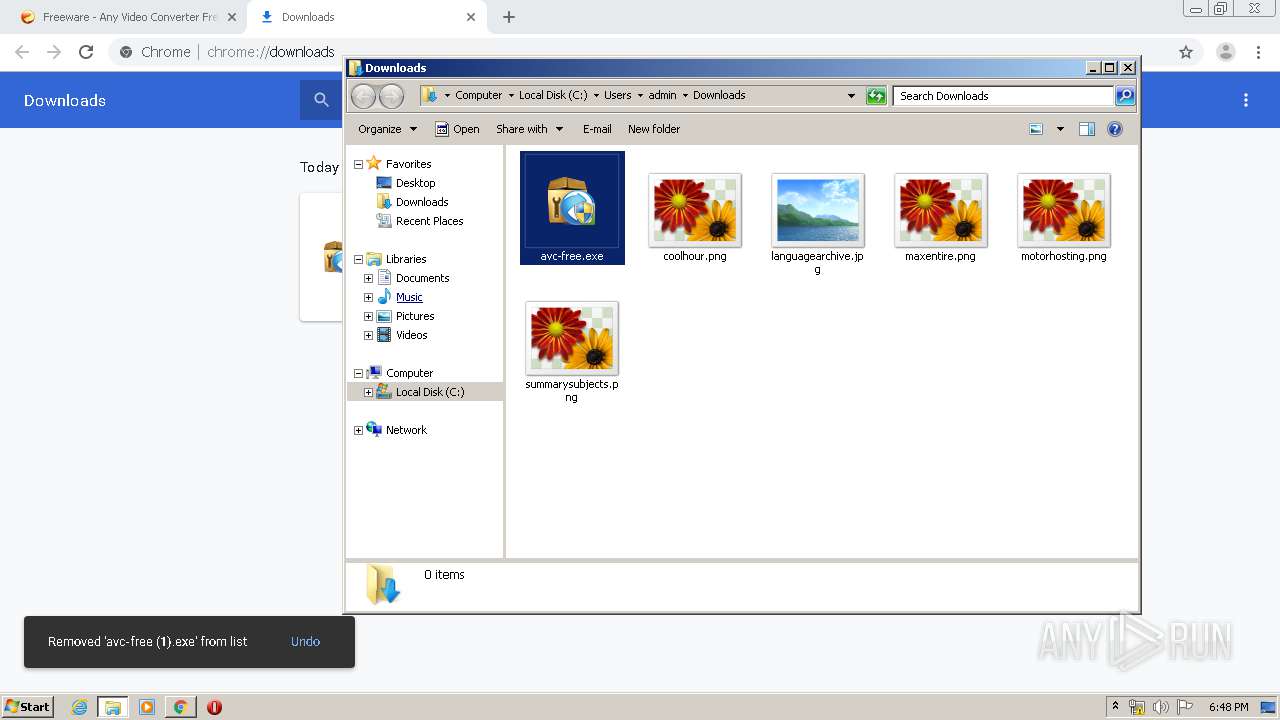
- avc-free.exe (PID: 3816)
INFO
Reads the hosts file
- chrome.exe (PID: 2740)
- chrome.exe (PID: 3852)
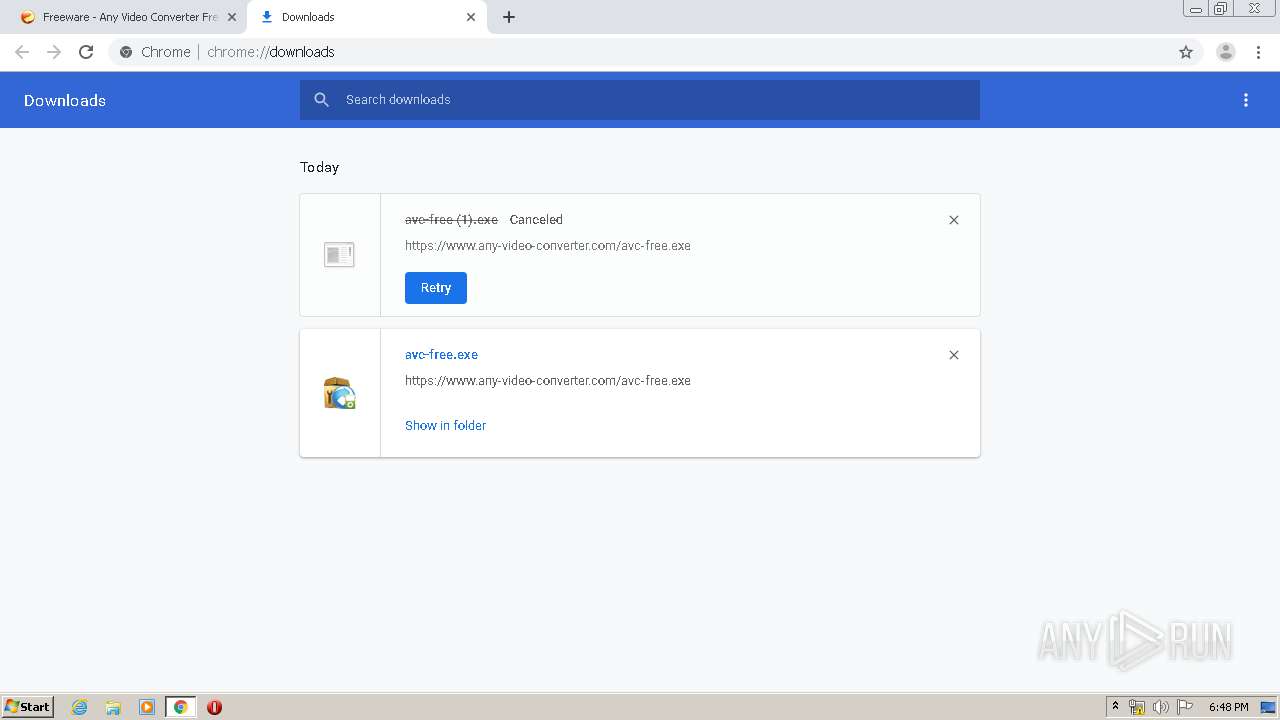
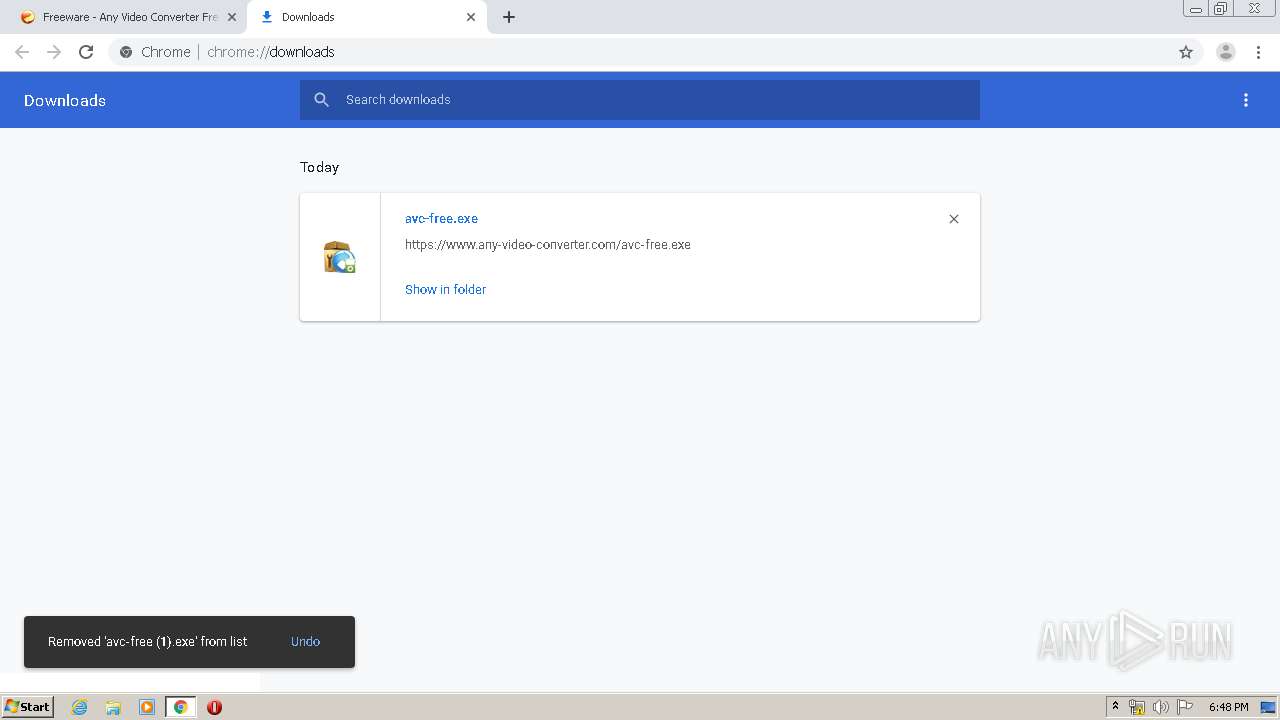
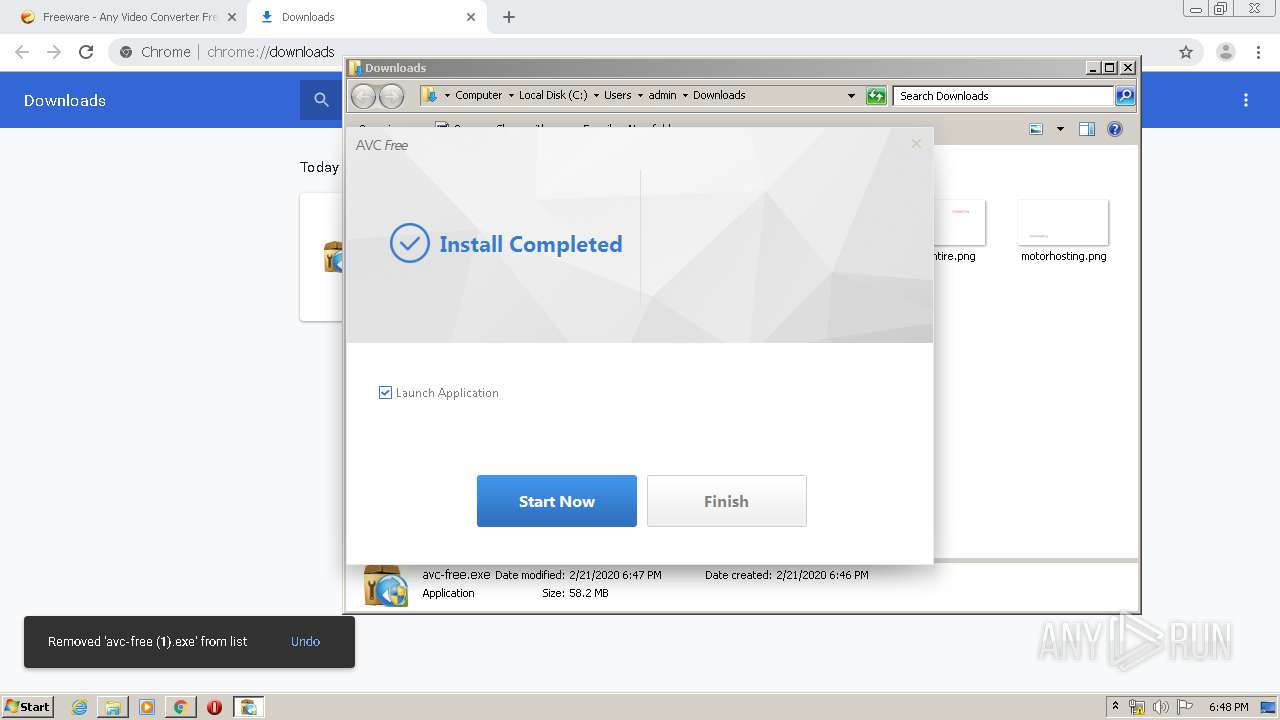
Manual execution by user
- avc-free.exe (PID: 3816)
- avc-free.exe (PID: 2960)
- AVCFree.exe (PID: 2856)
- explorer.exe (PID: 2004)
Reads Internet Cache Settings
- chrome.exe (PID: 3852)
- iexplore.exe (PID: 4072)
- iexplore.exe (PID: 3752)
Dropped object may contain Bitcoin addresses
- avc-free.exe (PID: 3816)
Reads settings of System Certificates
- chrome.exe (PID: 3852)
- iexplore.exe (PID: 3752)
- iexplore.exe (PID: 4072)
Changes internet zones settings
- iexplore.exe (PID: 4072)
Reads internet explorer settings
- iexplore.exe (PID: 3752)
Creates files in the user directory
- iexplore.exe (PID: 3752)
Application launched itself
- chrome.exe (PID: 3852)
Changes settings of System certificates
- iexplore.exe (PID: 4072)
- iexplore.exe (PID: 3752)
Adds / modifies Windows certificates
- iexplore.exe (PID: 4072)
- iexplore.exe (PID: 3752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
90
Monitored processes
45
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,15247345911486605719,12729289019760675271,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17227153454986651976 --mojo-platform-channel-handle=4740 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,15247345911486605719,12729289019760675271,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13760332036741529241 --mojo-platform-channel-handle=3892 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,15247345911486605719,12729289019760675271,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17036530253150889458 --mojo-platform-channel-handle=3696 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,15247345911486605719,12729289019760675271,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10468089787379789713 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3704 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,15247345911486605719,12729289019760675271,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16005427254784958711 --mojo-platform-channel-handle=2484 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1440 | cmd.exe /c ""C:\Users\admin\AppData\Roaming\Anvsoft\Common\youtube-dl.exe" --version " | C:\Windows\system32\cmd.exe | — | AVCFree.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa8a9d0,0x6fa8a9e0,0x6fa8a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,15247345911486605719,12729289019760675271,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1540979035305947781 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3100 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
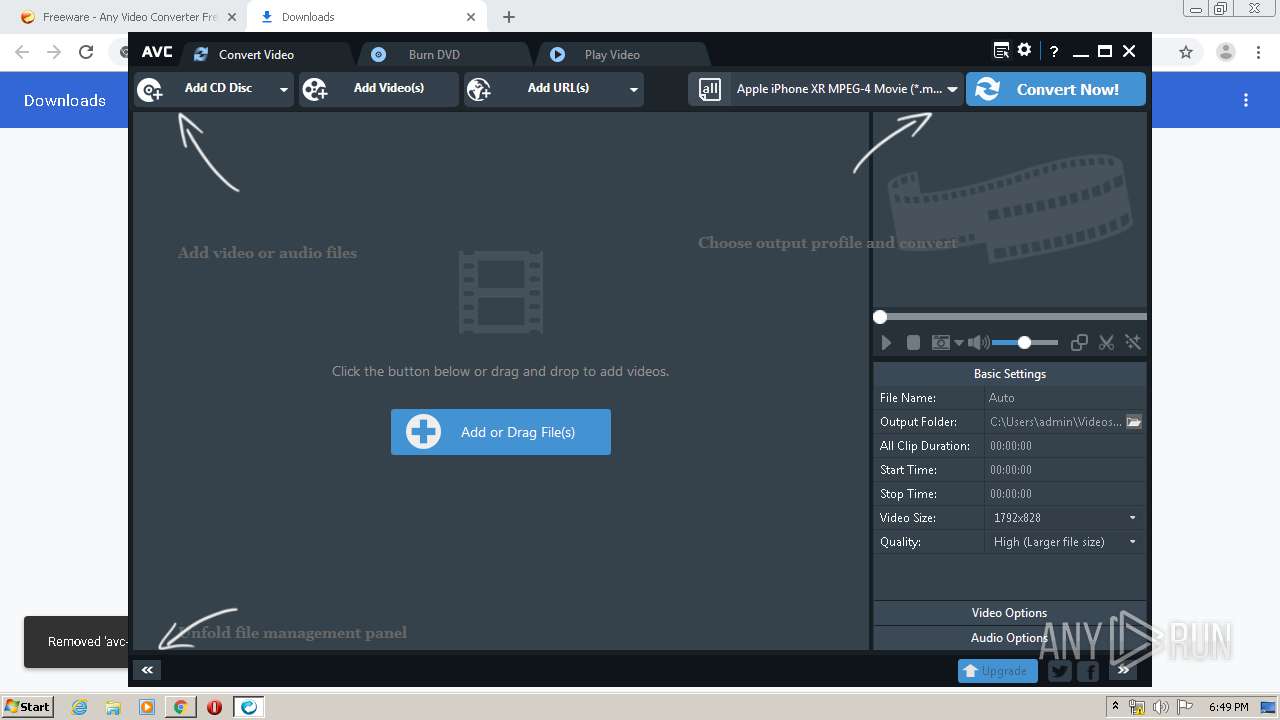
| 1932 | "C:\Program Files\Anvsoft\Any Video Converter\AVCFree.exe" | C:\Program Files\Anvsoft\Any Video Converter\AVCFree.exe | avc-free.exe | ||||||||||||
User: admin Company: Anvsoft Integrity Level: HIGH Description: Any Video Converter Exit code: 0 Version: 6.3.8.0 Modules
| |||||||||||||||
| 2004 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 914
Read events
2 170
Write events
1 734
Delete events
10
Modification events
| (PID) Process: | (3736) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3852-13226784387610625 |
Value: 259 | |||
| (PID) Process: | (3852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3852) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
130
Suspicious files
58
Text files
3 726
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E502583-F0C.pma | — | |
MD5:— | SHA256:— | |||
| 3852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\13bb6072-9e27-40d2-b297-4fdd38c24137.tmp | — | |
MD5:— | SHA256:— | |||
| 3852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFa663f2.TMP | text | |
MD5:— | SHA256:— | |||
| 3852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66588.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
57
DNS requests
41
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
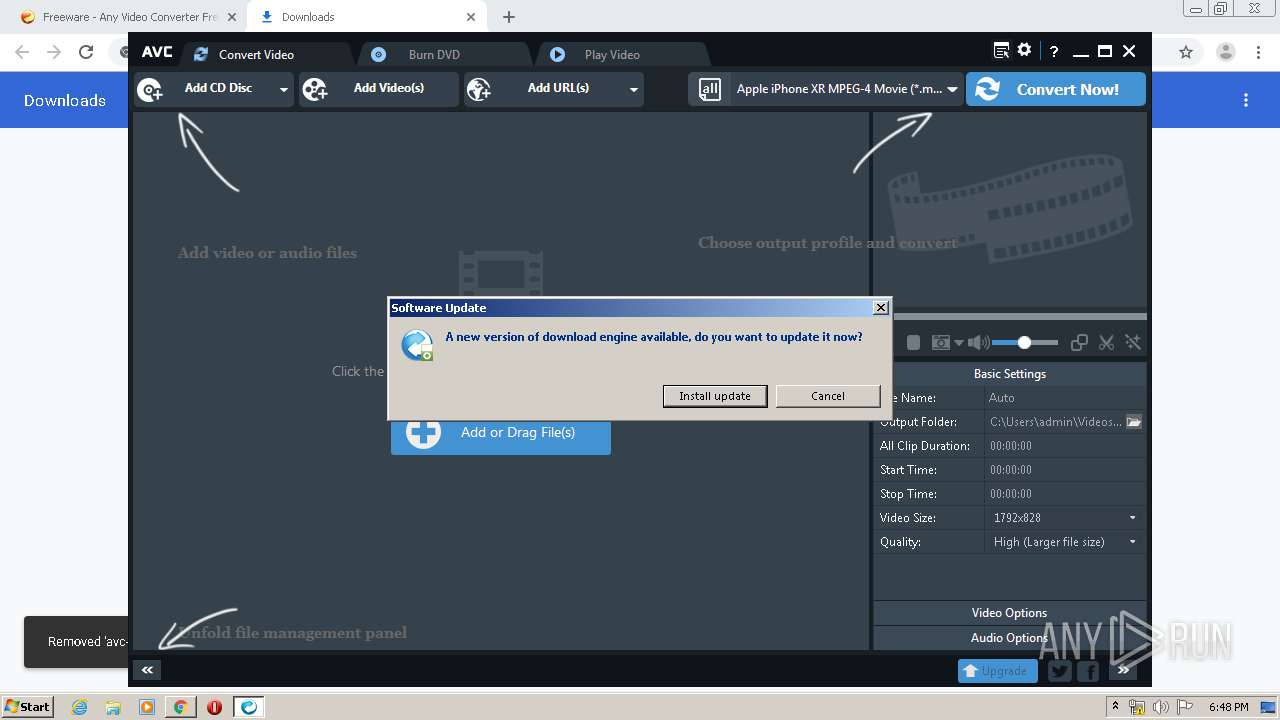
1932 | AVCFree.exe | HEAD | 200 | 104.20.146.79:80 | http://update.any-video-converter.com/ver_youtube-dl.ini | US | — | — | malicious |
1932 | AVCFree.exe | GET | — | 104.20.146.79:80 | http://update.any-video-converter.com/youtube-dl.exe | US | — | — | malicious |
3752 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | US | der | 471 b | whitelisted |
3752 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3752 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDx9it%2Fyk0DxwgAAAAALC4g | US | der | 472 b | whitelisted |
1932 | AVCFree.exe | GET | 200 | 104.20.146.79:80 | http://update.any-video-converter.com/ver_youtube-dl.ini | US | text | 29 b | malicious |
1932 | AVCFree.exe | HEAD | 200 | 104.20.146.79:80 | http://update.any-video-converter.com/youtube-dl.exe | US | text | 29 b | malicious |
2740 | chrome.exe | GET | 302 | 172.217.16.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 511 b | whitelisted |
3752 | iexplore.exe | GET | 200 | 195.138.255.24:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | DE | der | 1.37 Kb | whitelisted |
3752 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2740 | chrome.exe | 74.125.133.156:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
2740 | chrome.exe | 31.13.92.10:443 | graph.facebook.com | Facebook, Inc. | IE | whitelisted |
2740 | chrome.exe | 104.20.146.79:443 | any-video-converter.com | Cloudflare Inc | US | shared |
2740 | chrome.exe | 172.217.16.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2740 | chrome.exe | 172.217.23.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2740 | chrome.exe | 172.217.22.100:443 | www.google.com | Google Inc. | US | whitelisted |
2740 | chrome.exe | 23.210.248.44:443 | s7.addthis.com | Akamai International B.V. | NL | whitelisted |
2740 | chrome.exe | 172.217.18.14:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2740 | chrome.exe | 172.217.18.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2740 | chrome.exe | 172.217.22.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
any-video-converter.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
s7.addthis.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
z.moatads.com |
| whitelisted |
v1.addthisedge.com |
| shared |
m.addthis.com |
| shared |
stats.g.doubleclick.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1932 | AVCFree.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1932 | AVCFree.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
youtube-dl.exe | Py_Initialize: unable to load the file system codec |
youtube-dl.exe | Py_Initialize: unable to load the file system codec |
youtube-dl.exe |