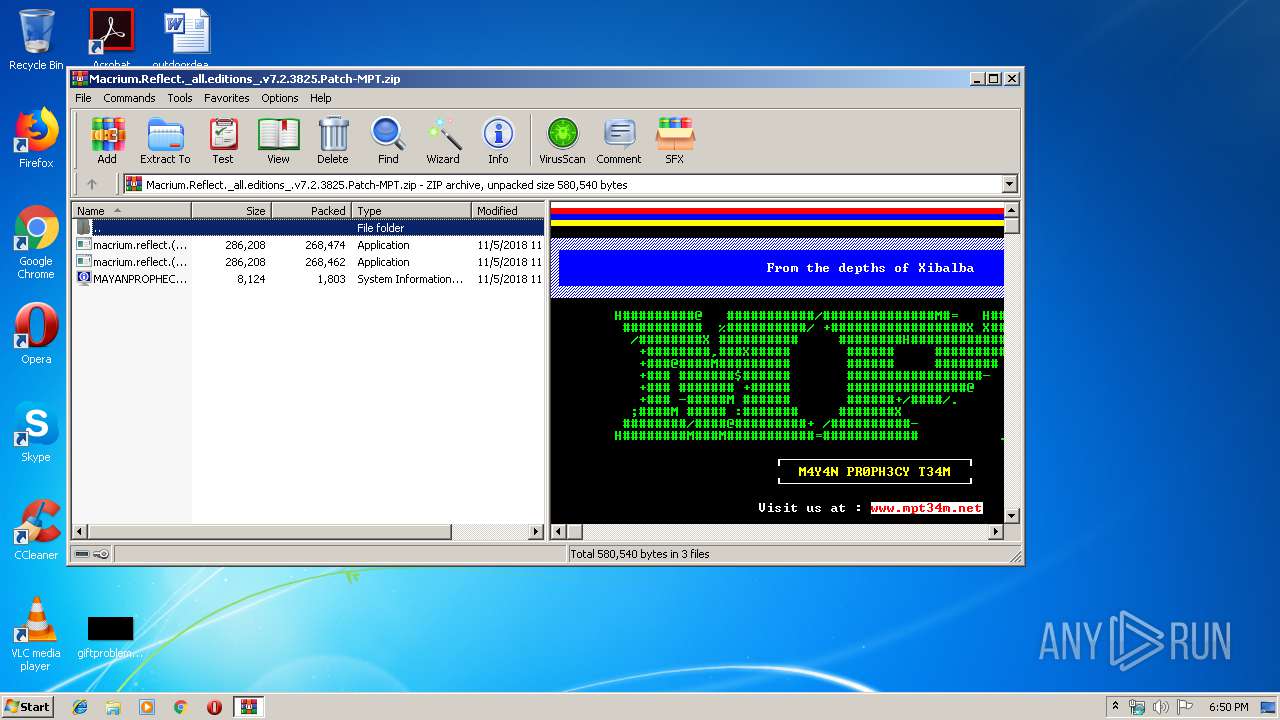
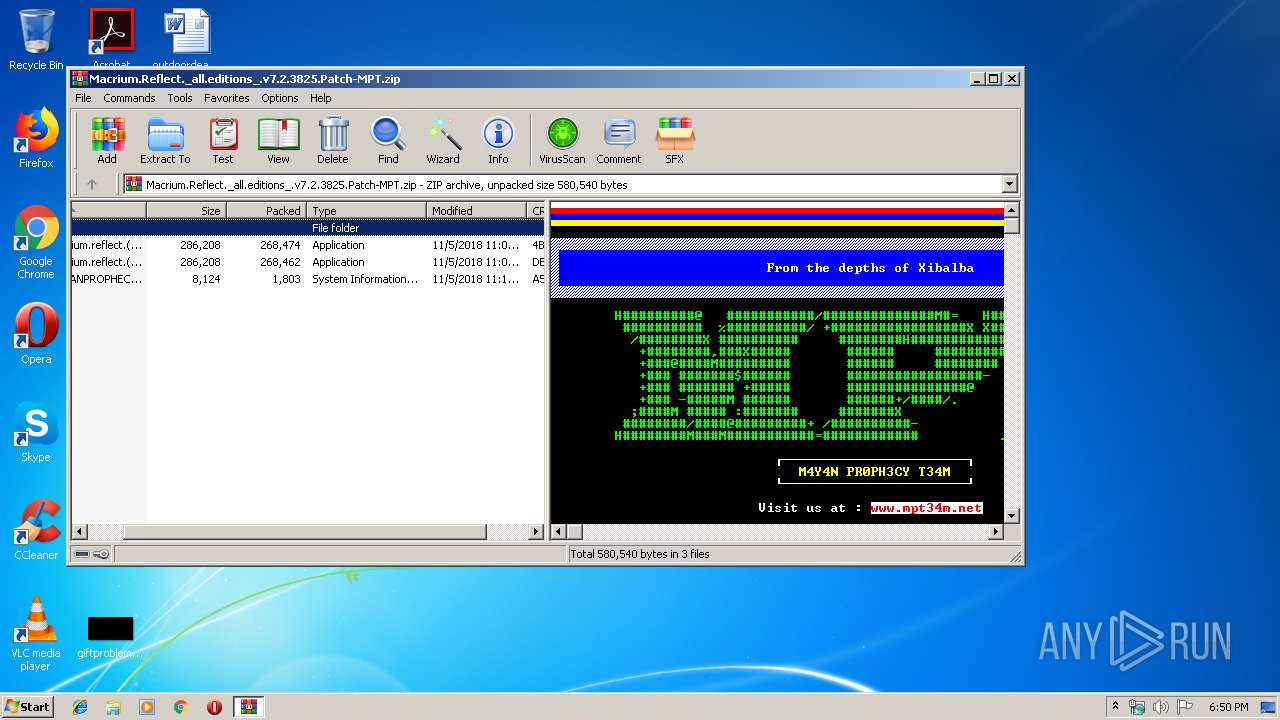
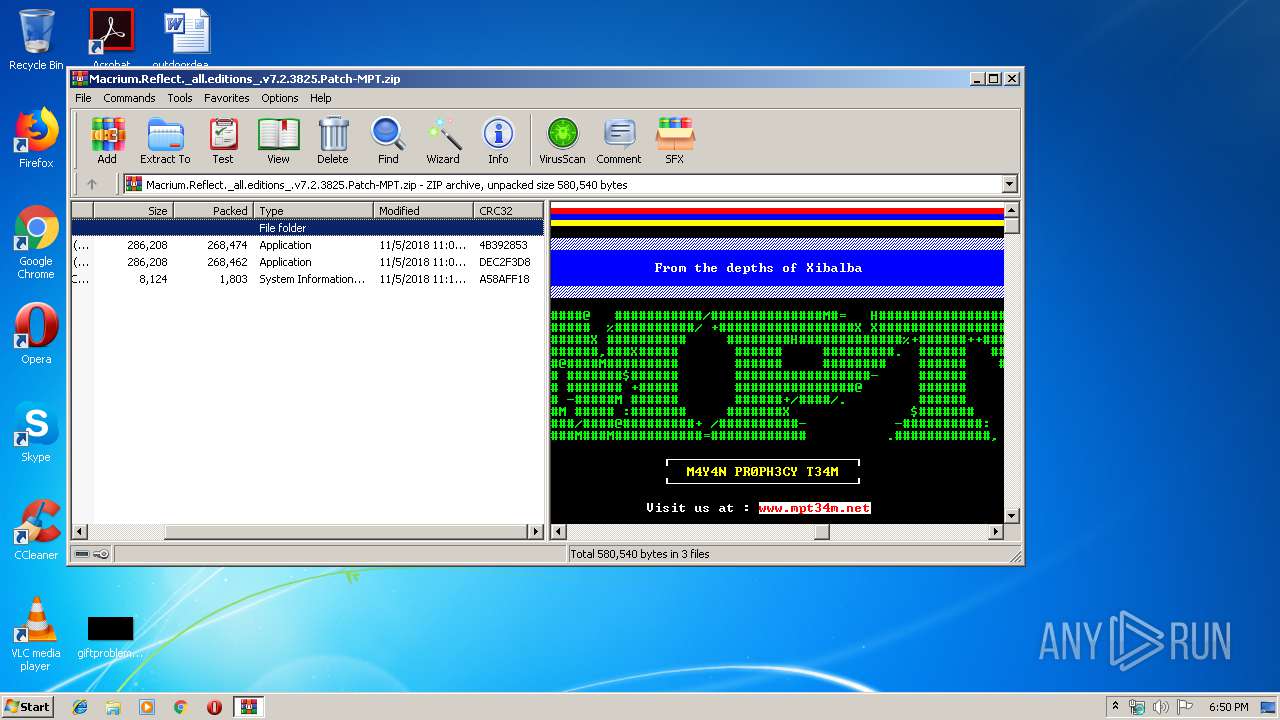
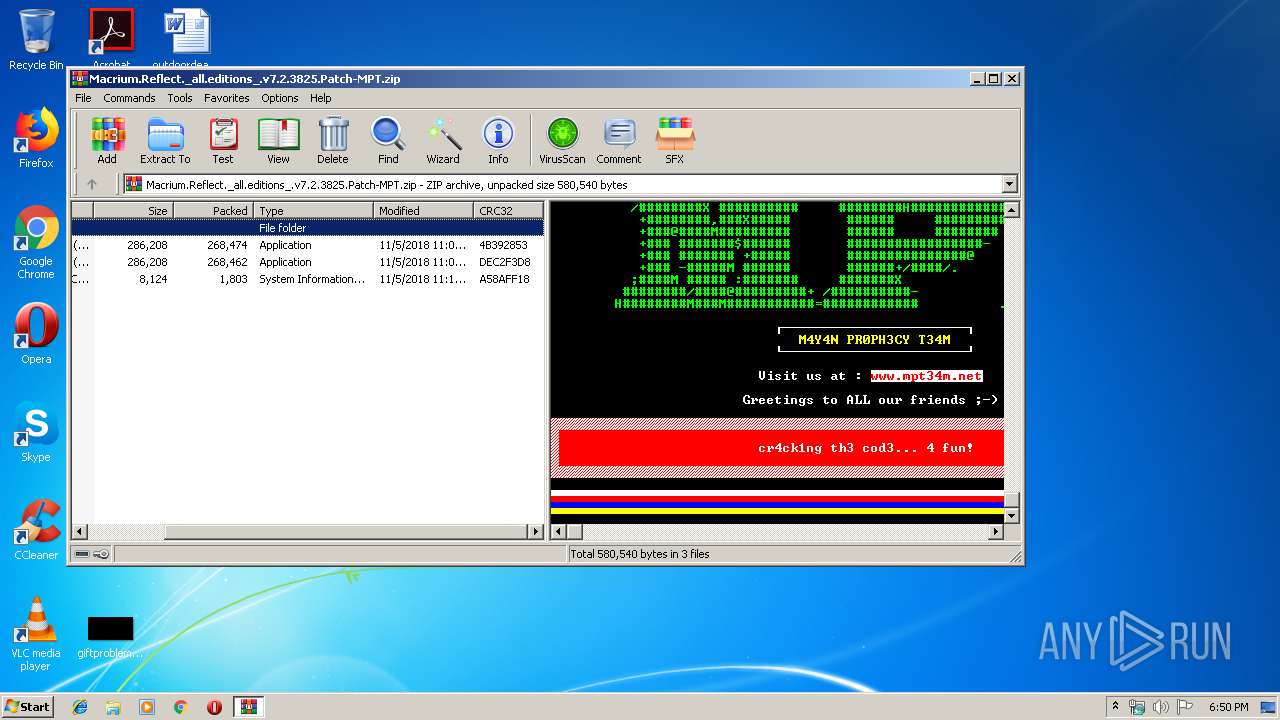
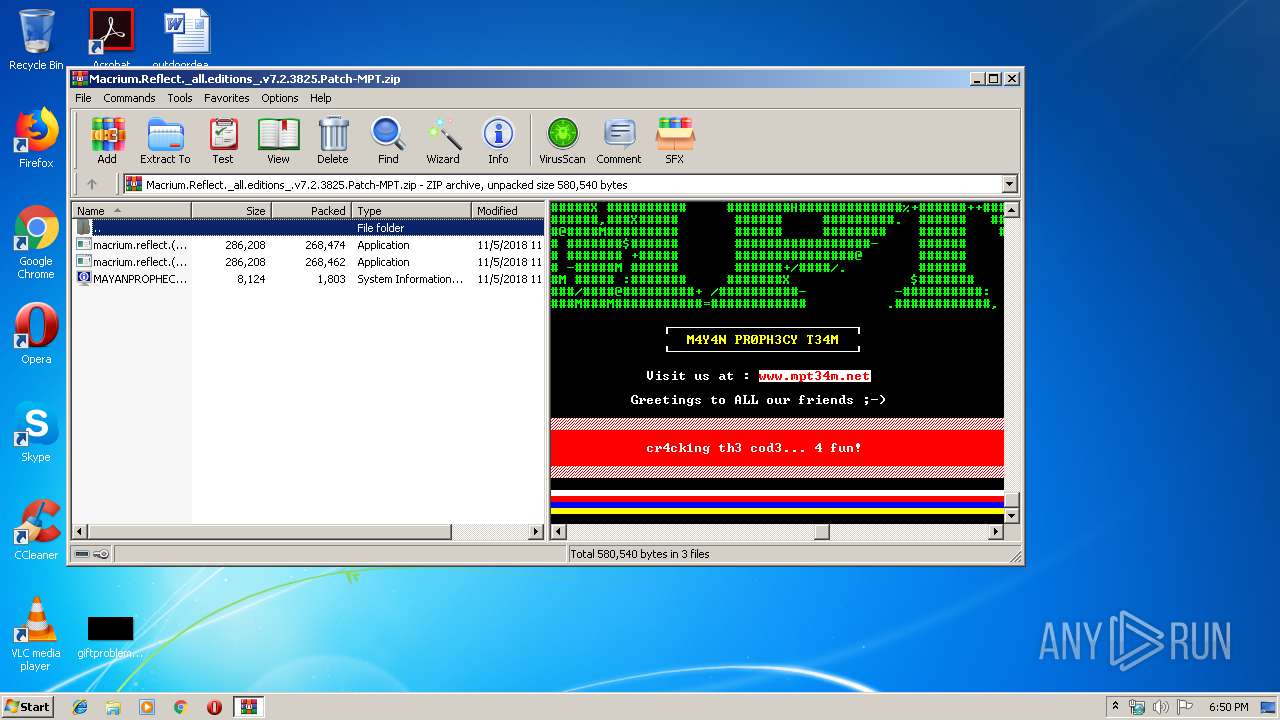
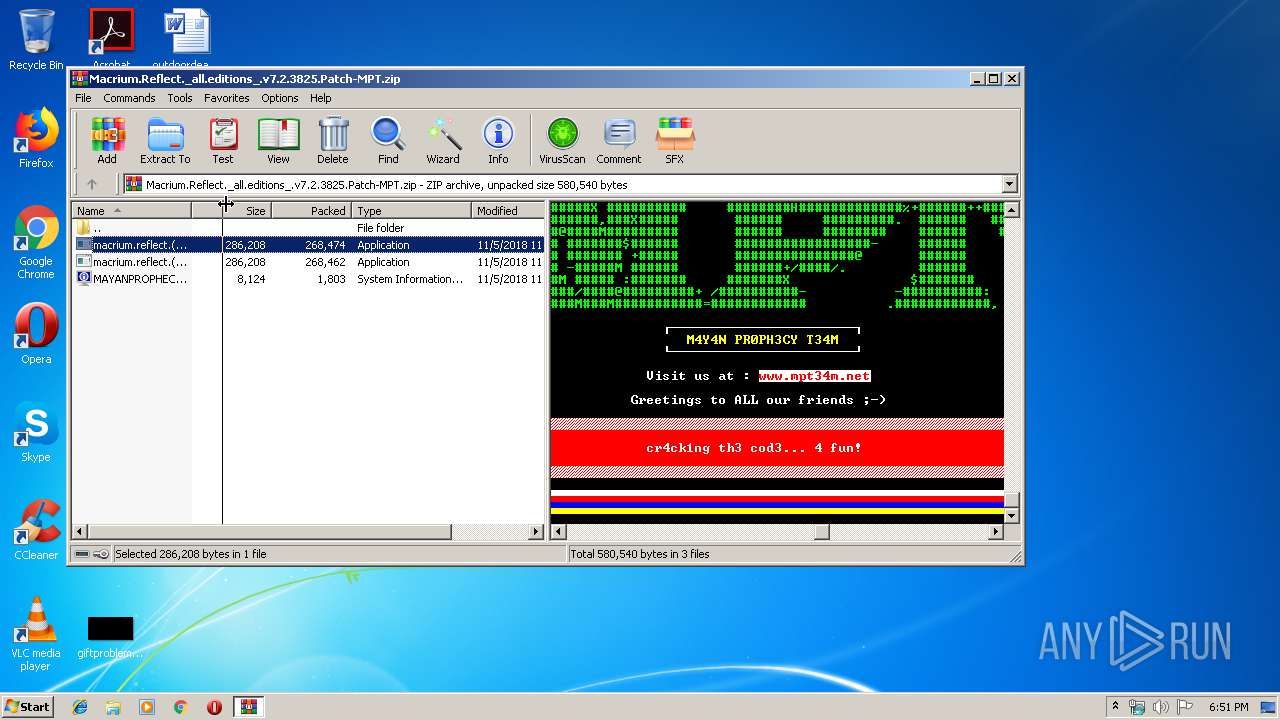
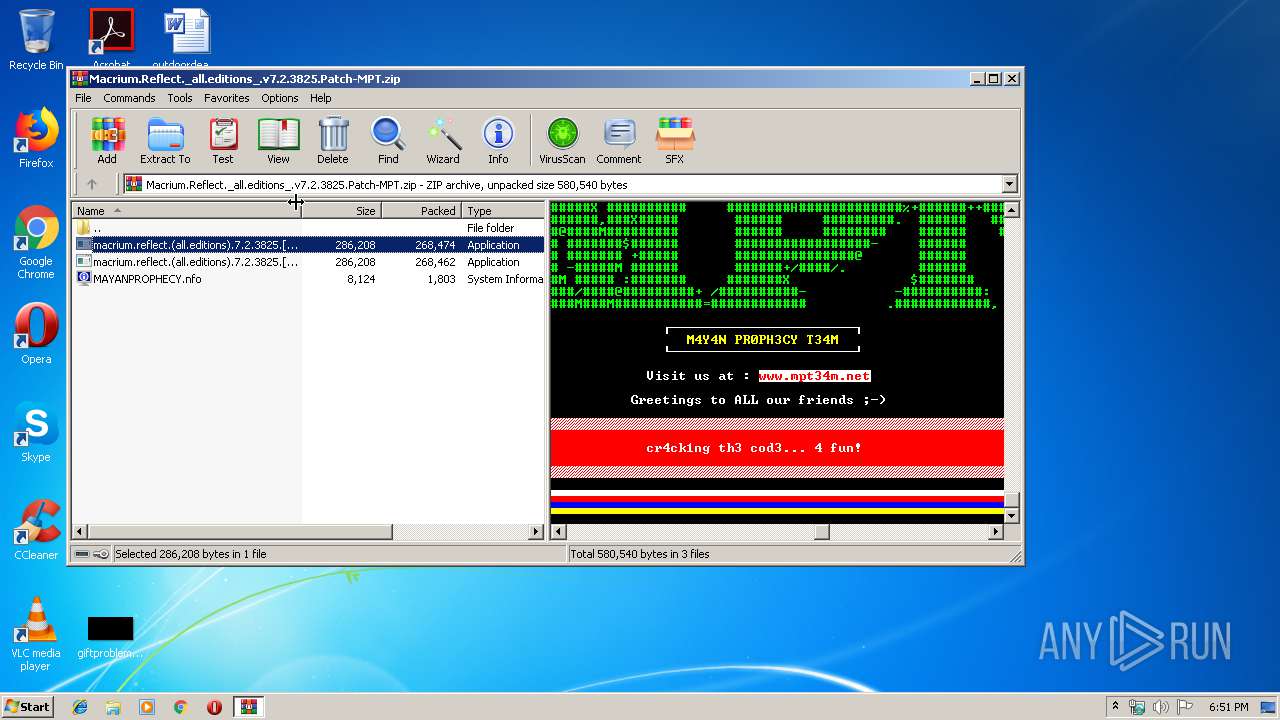
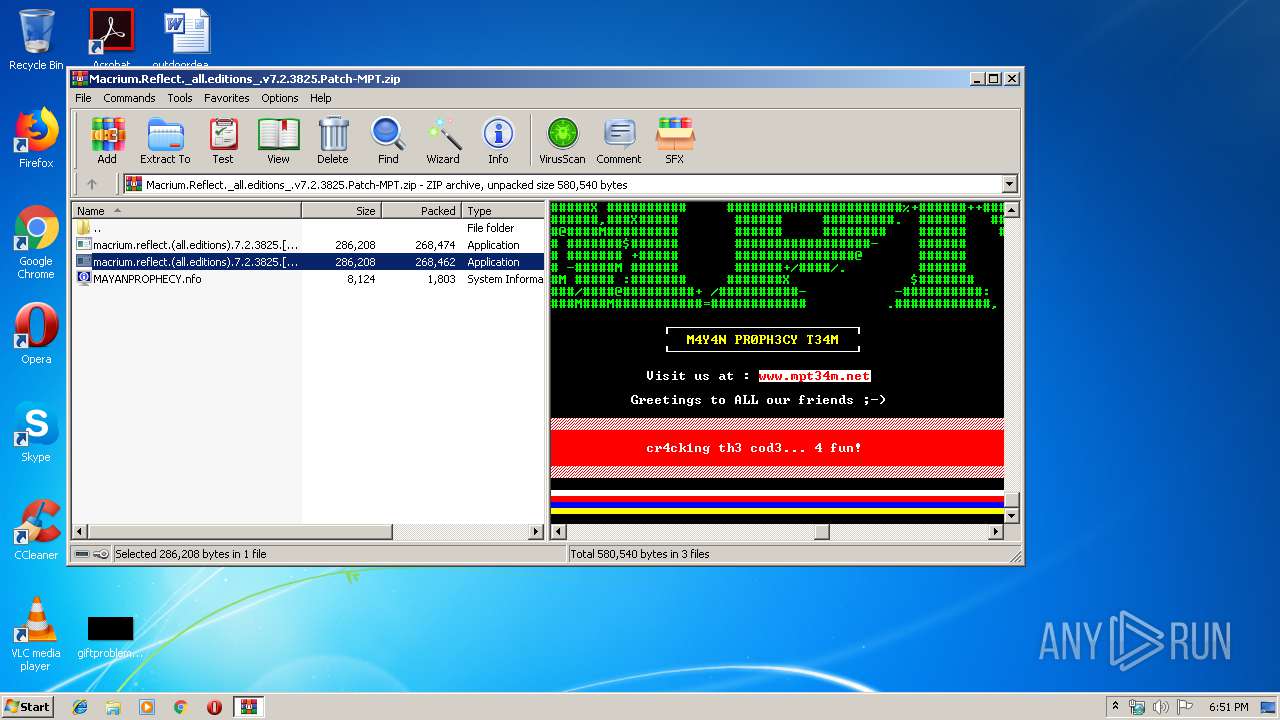
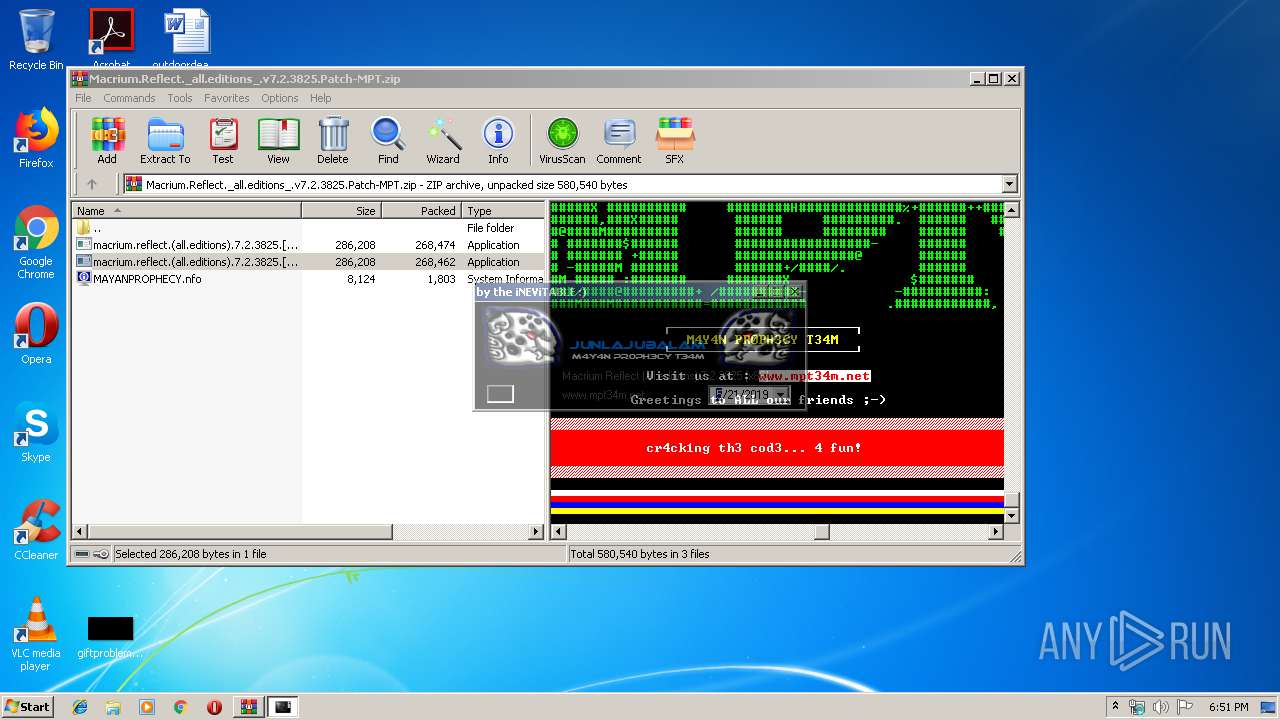
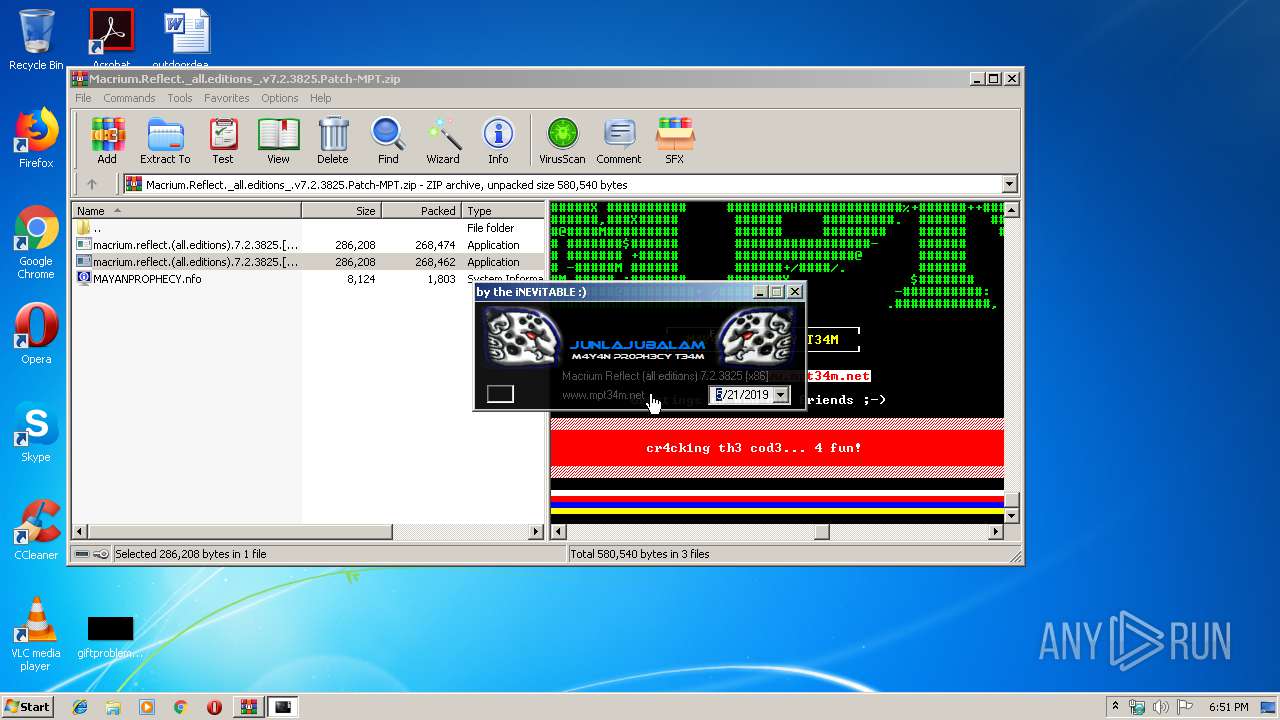
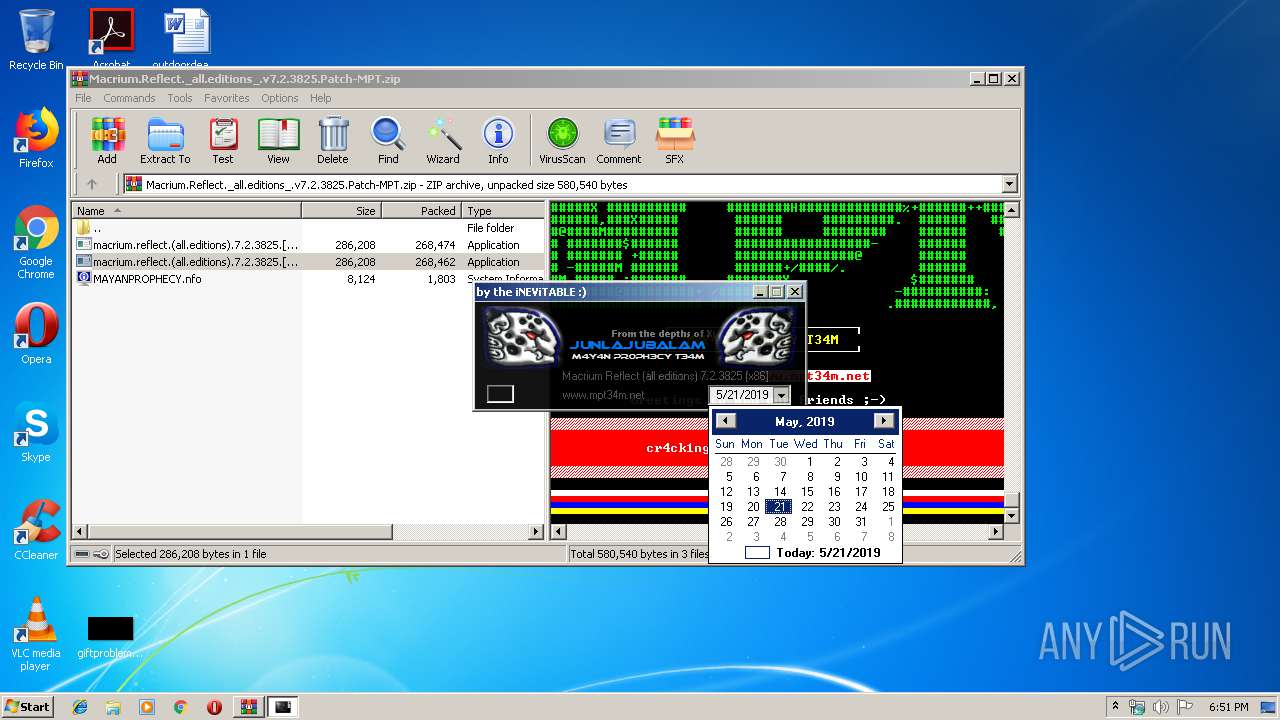
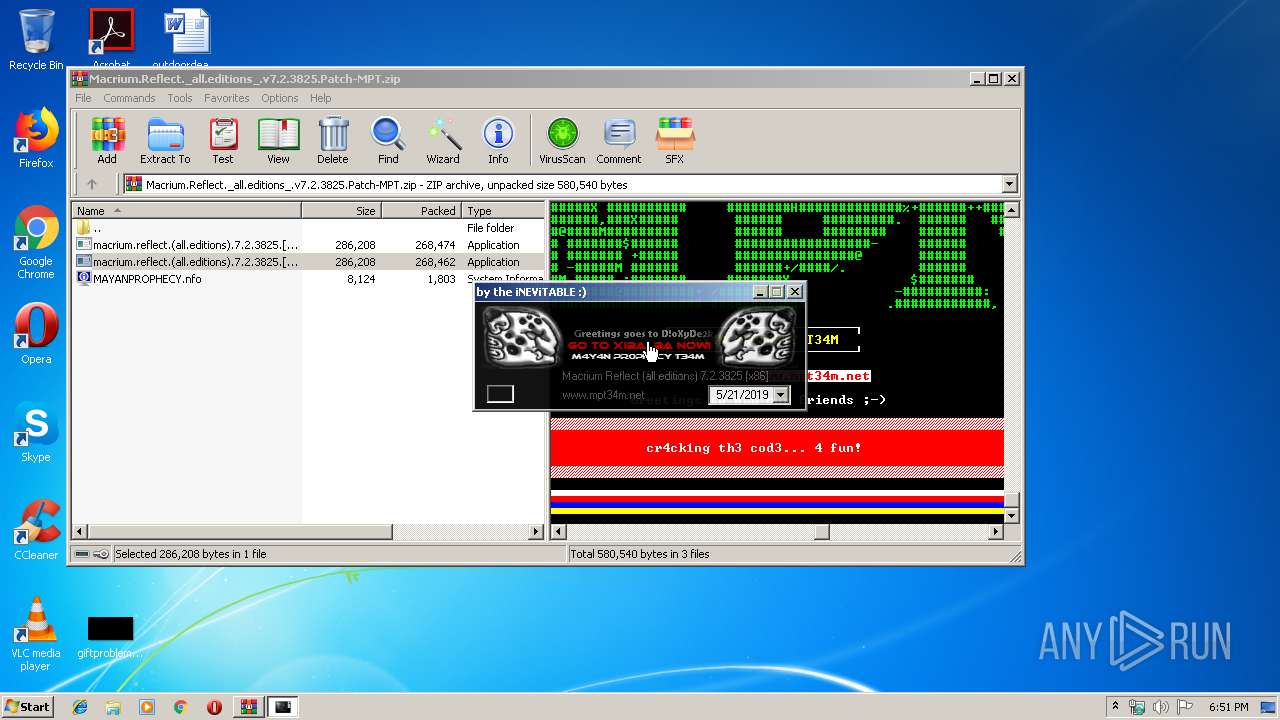
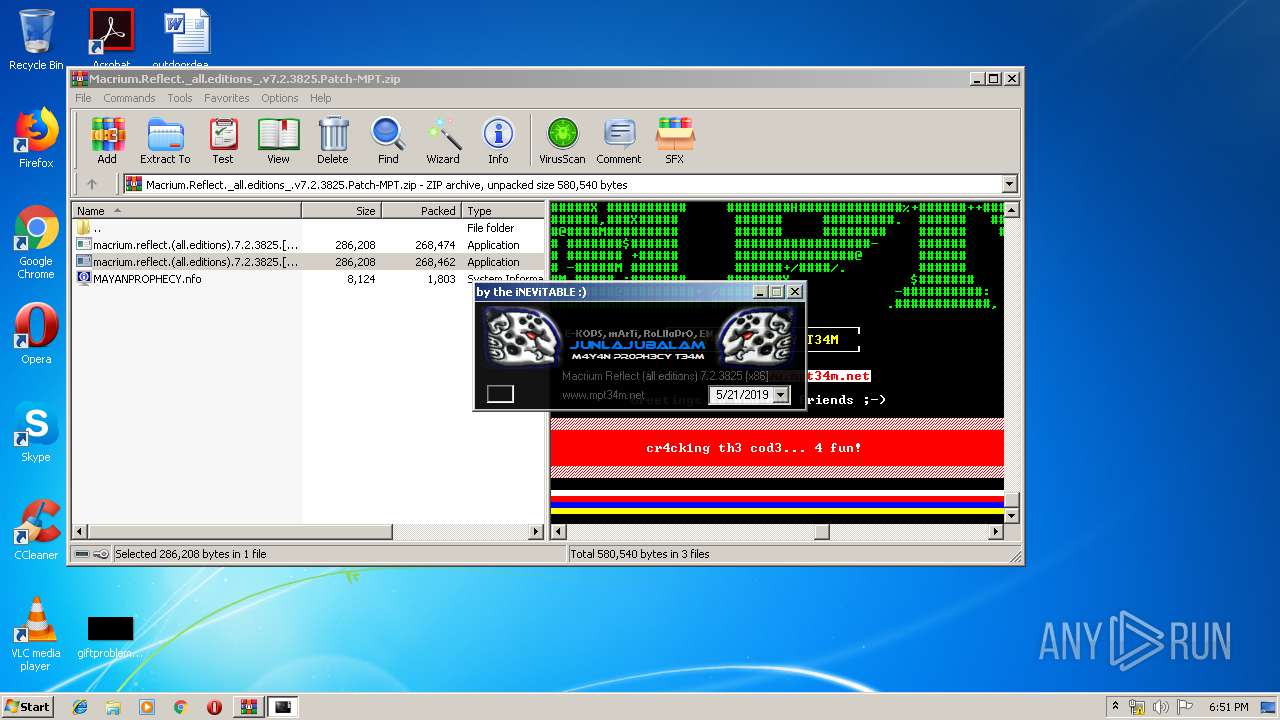
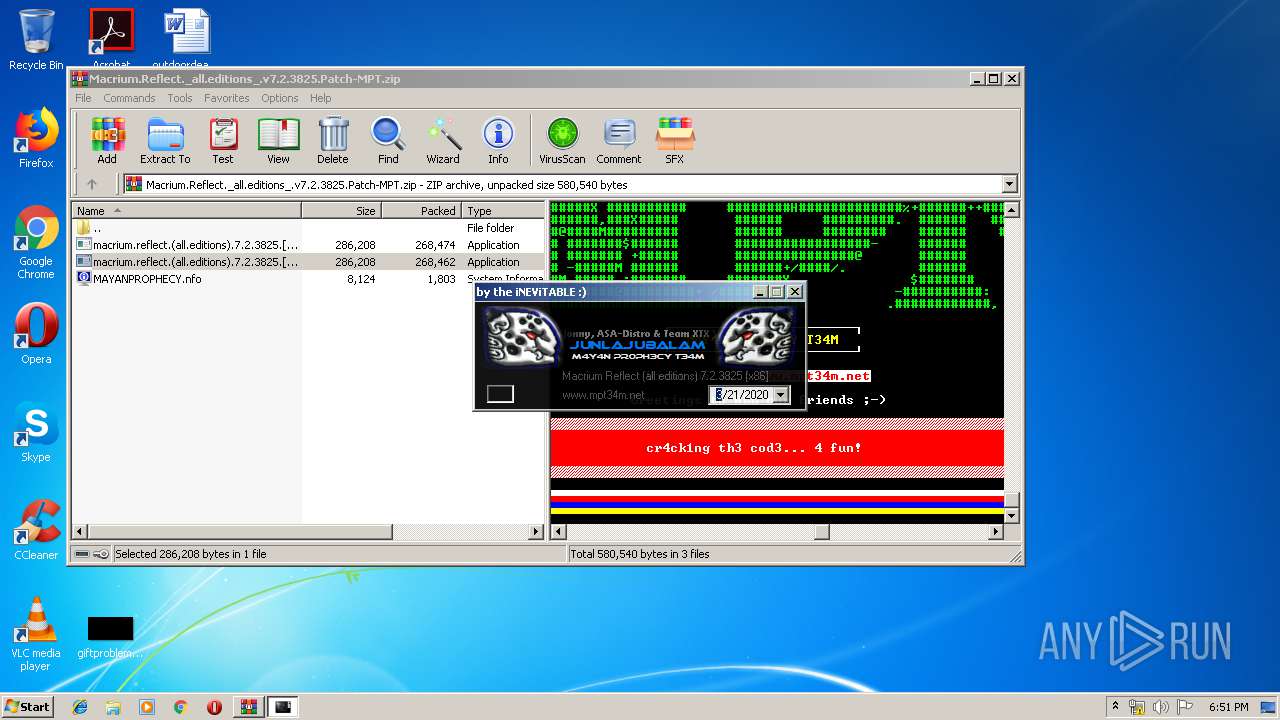
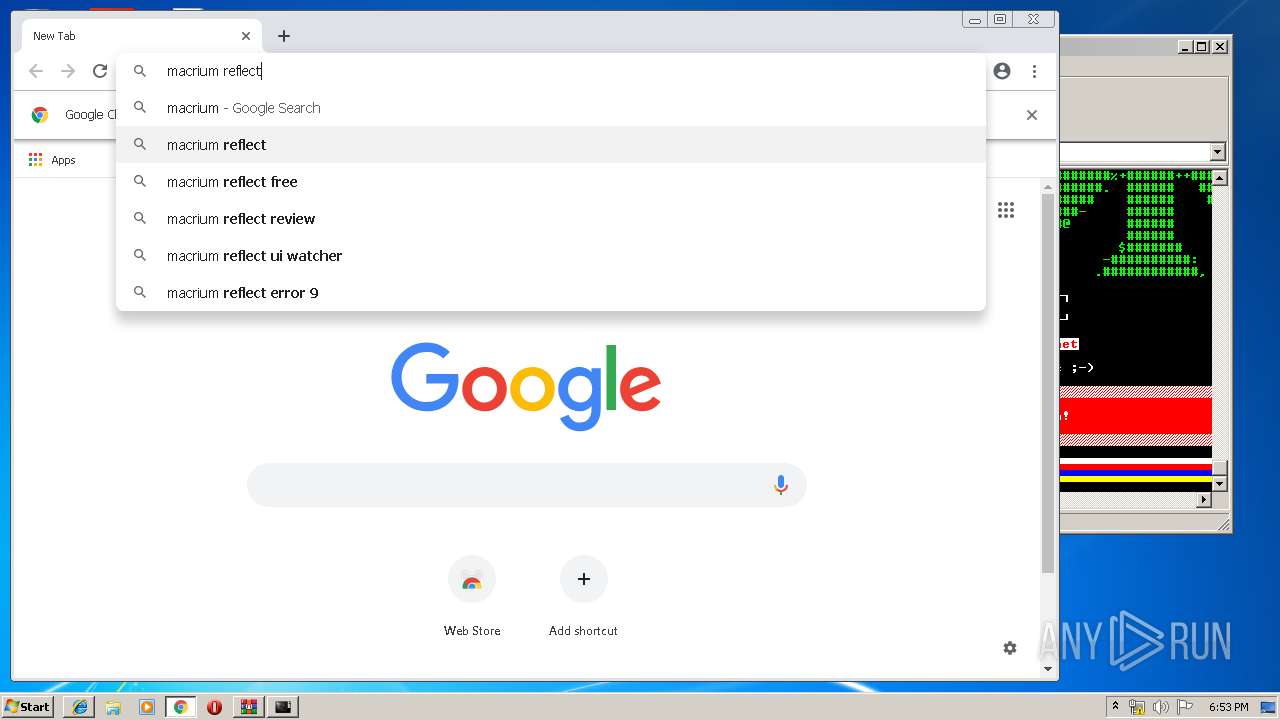
| File name: | Macrium.Reflect._all.editions_.v7.2.3825.Patch-MPT.zip |
| Full analysis: | https://app.any.run/tasks/044266eb-3fcb-4329-9fbf-cf7a7be7a5cf |
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2019, 17:50:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 0B5C64766821AE2C3B539E7E43D6BB05 |
| SHA1: | 10A2A2A754783B65C7213610816629720D9AB070 |
| SHA256: | BE55BB445DEB38C7AAA2F6ABF00F9F7321A903B54BA6FCB71AFC6976E080DA70 |
| SSDEEP: | 12288:XCtGq+jpN2/B0VCMR7q2o28S1M2p4a1JPO/u8vJbk:3DVp5D/1M2pp1JPOmkJQ |
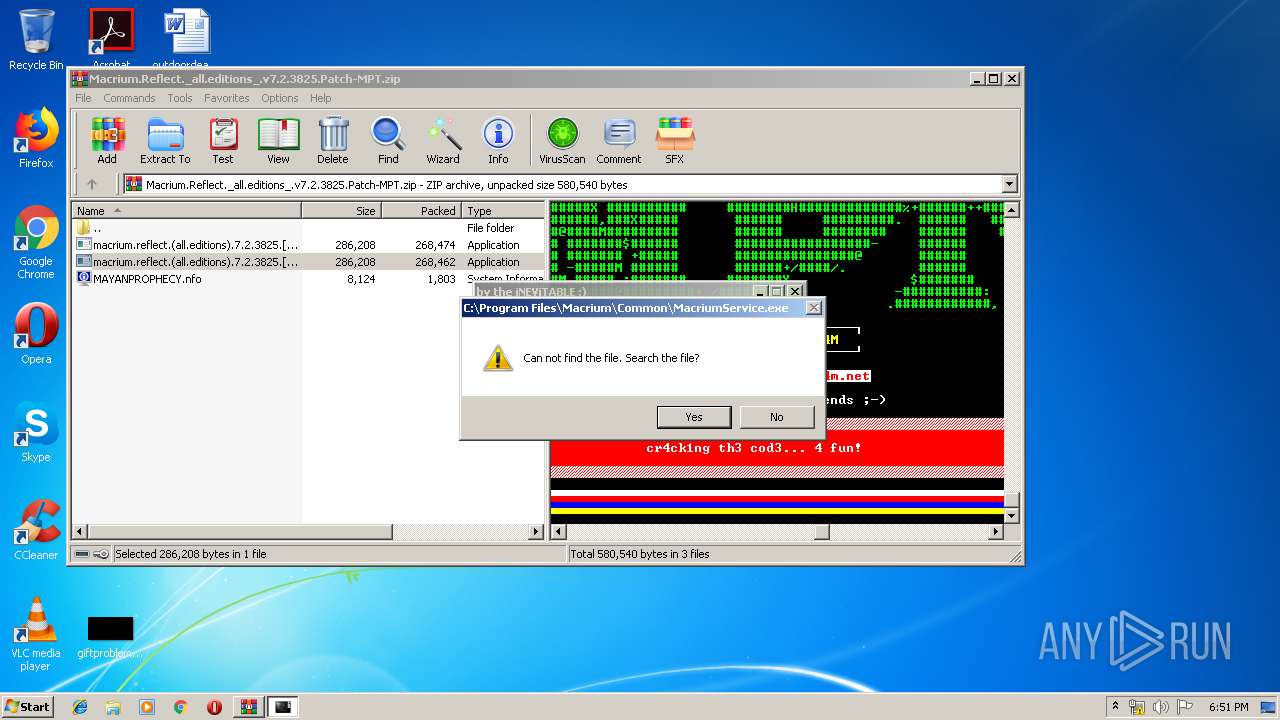
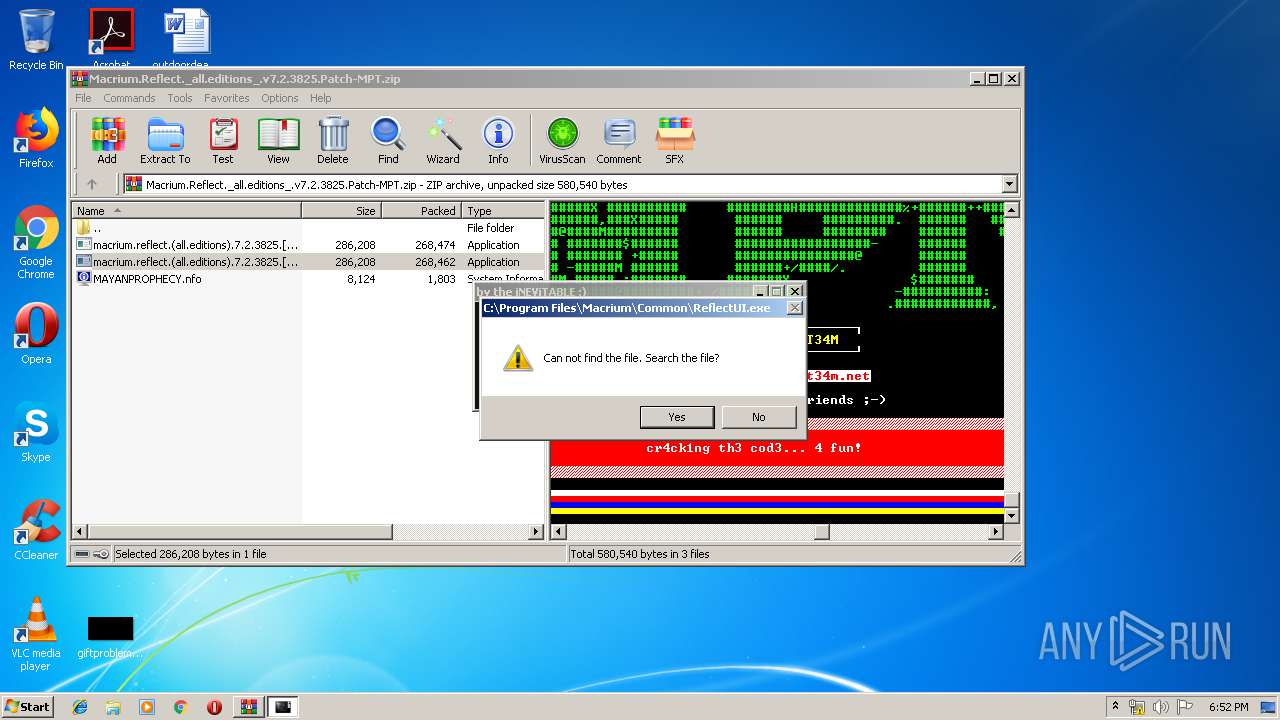
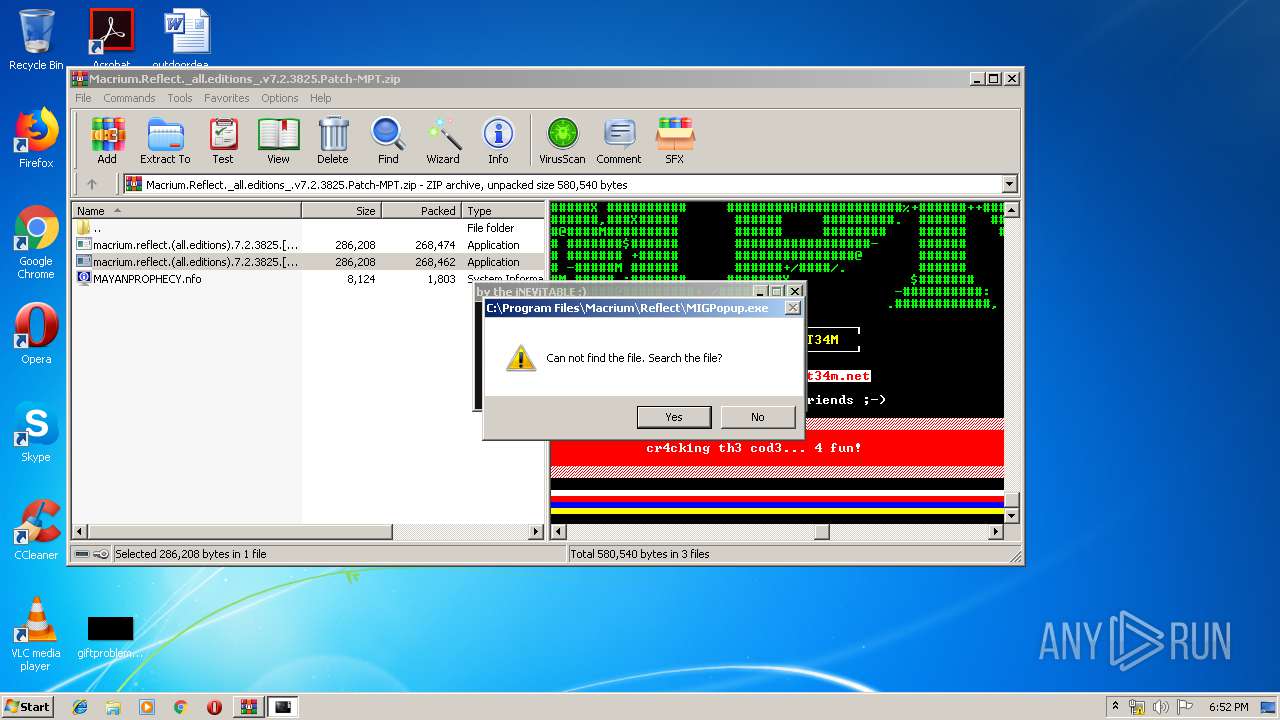
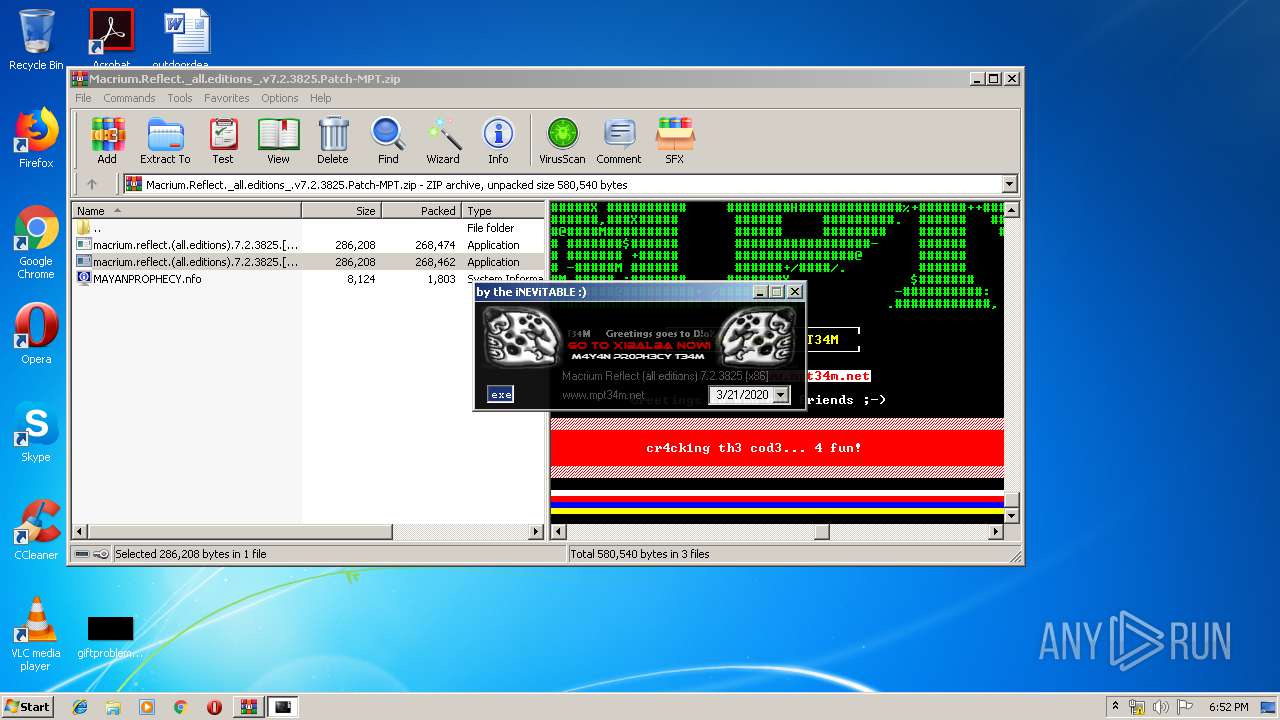
MALICIOUS
Starts NET.EXE for service management
- cmd.exe (PID: 2368)
- cmd.exe (PID: 936)
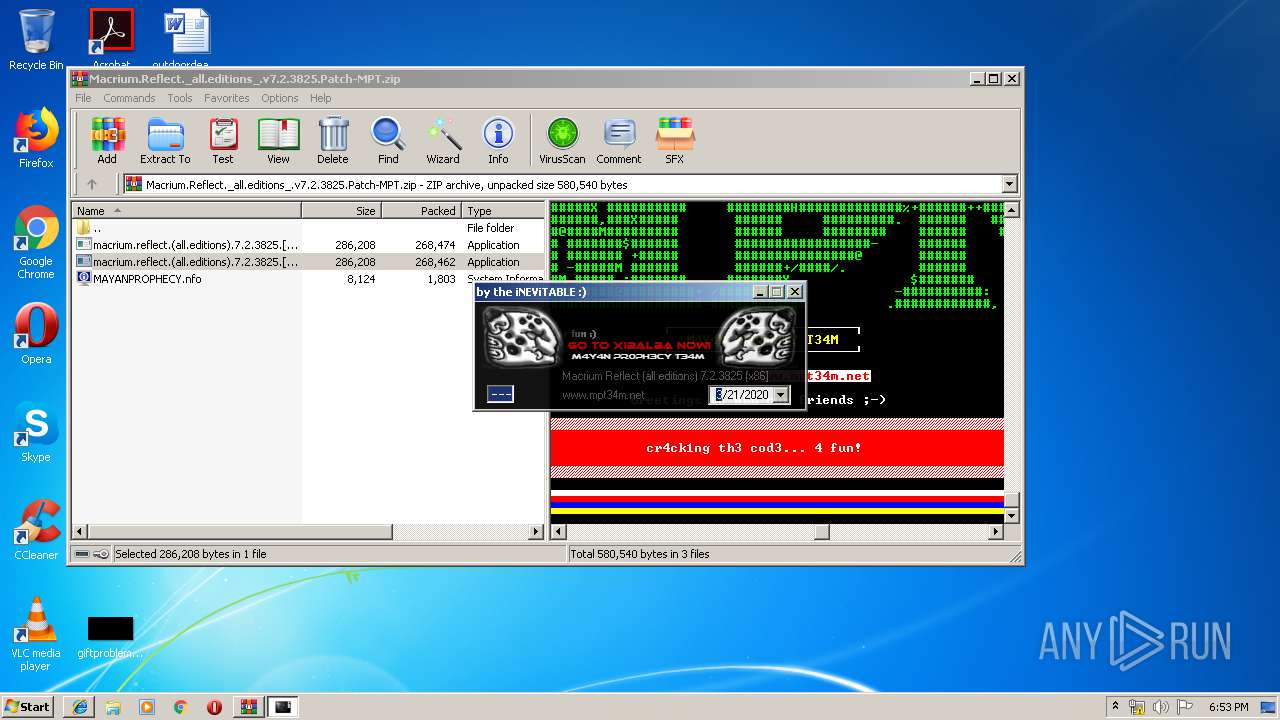
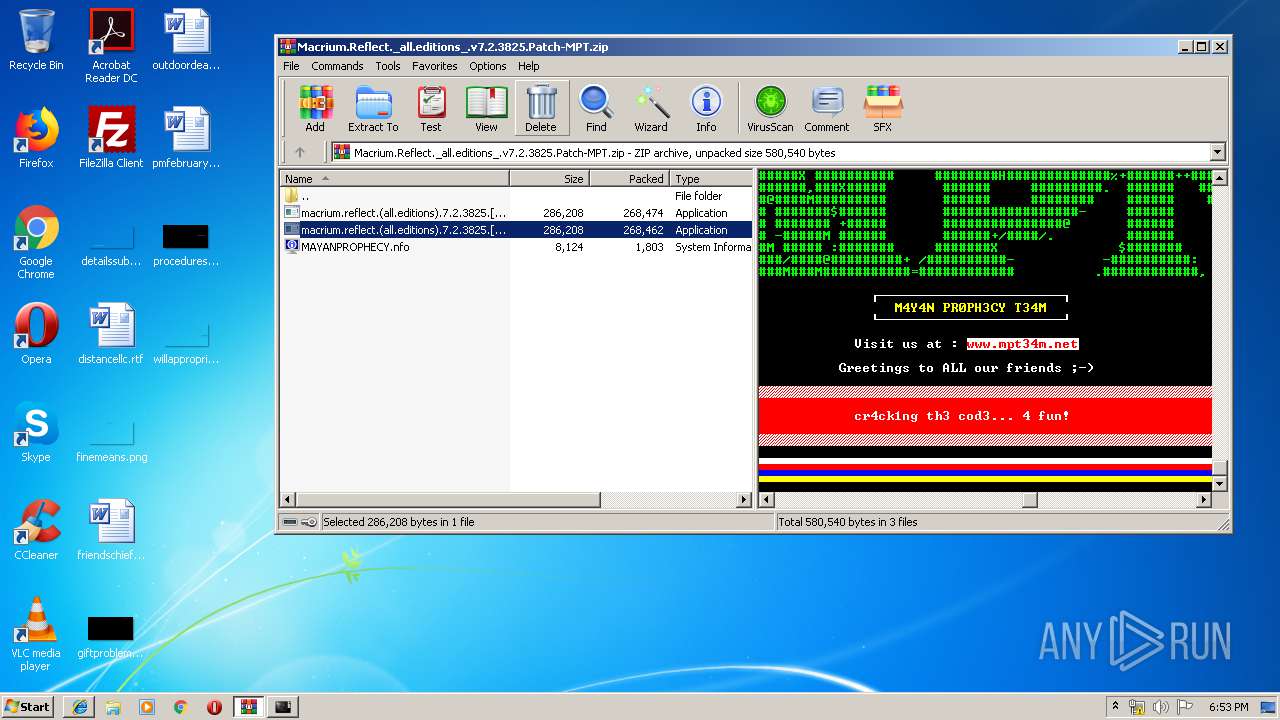
Loads dropped or rewritten executable
- macrium.reflect.(all.editions).7.2.3825.[x86]-MPT.exe (PID: 2400)
Application was dropped or rewritten from another process
- macrium.reflect.(all.editions).7.2.3825.[x86]-MPT.exe (PID: 4060)
- macrium.reflect.(all.editions).7.2.3825.[x86]-MPT.exe (PID: 2400)
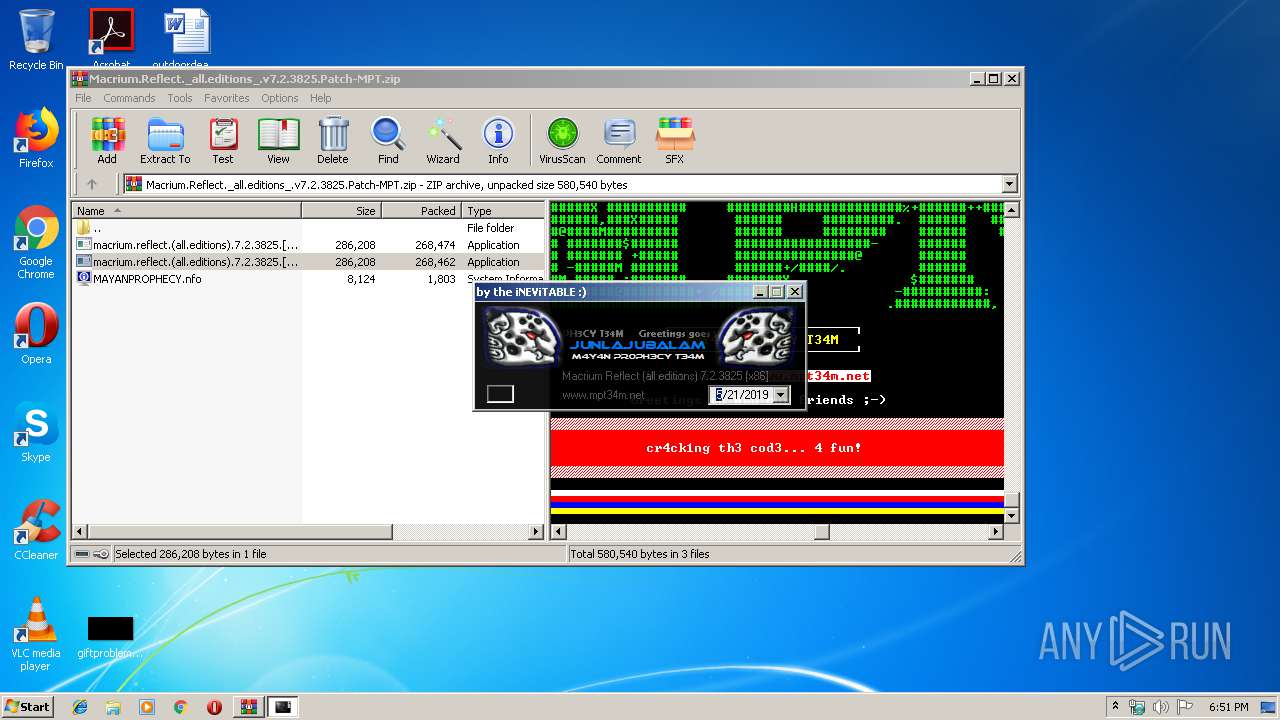
SUSPICIOUS
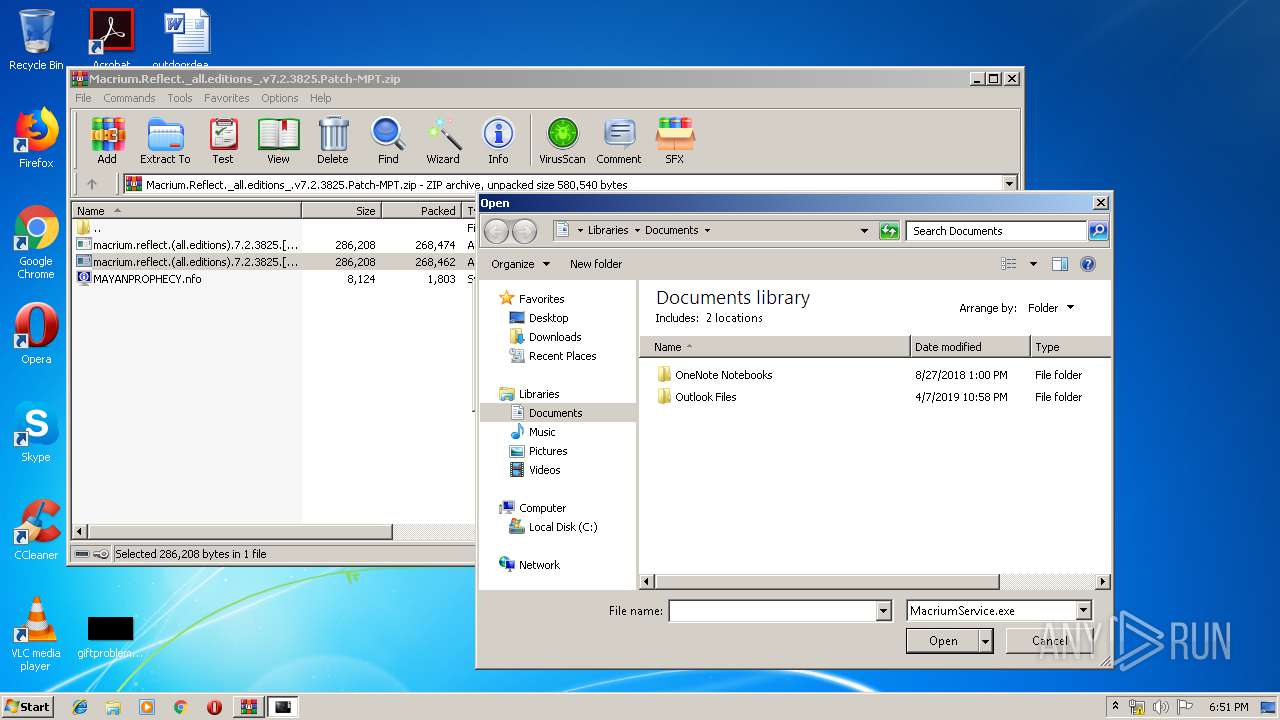
Executable content was dropped or overwritten
- macrium.reflect.(all.editions).7.2.3825.[x86]-MPT.exe (PID: 2400)
- WinRAR.exe (PID: 2944)
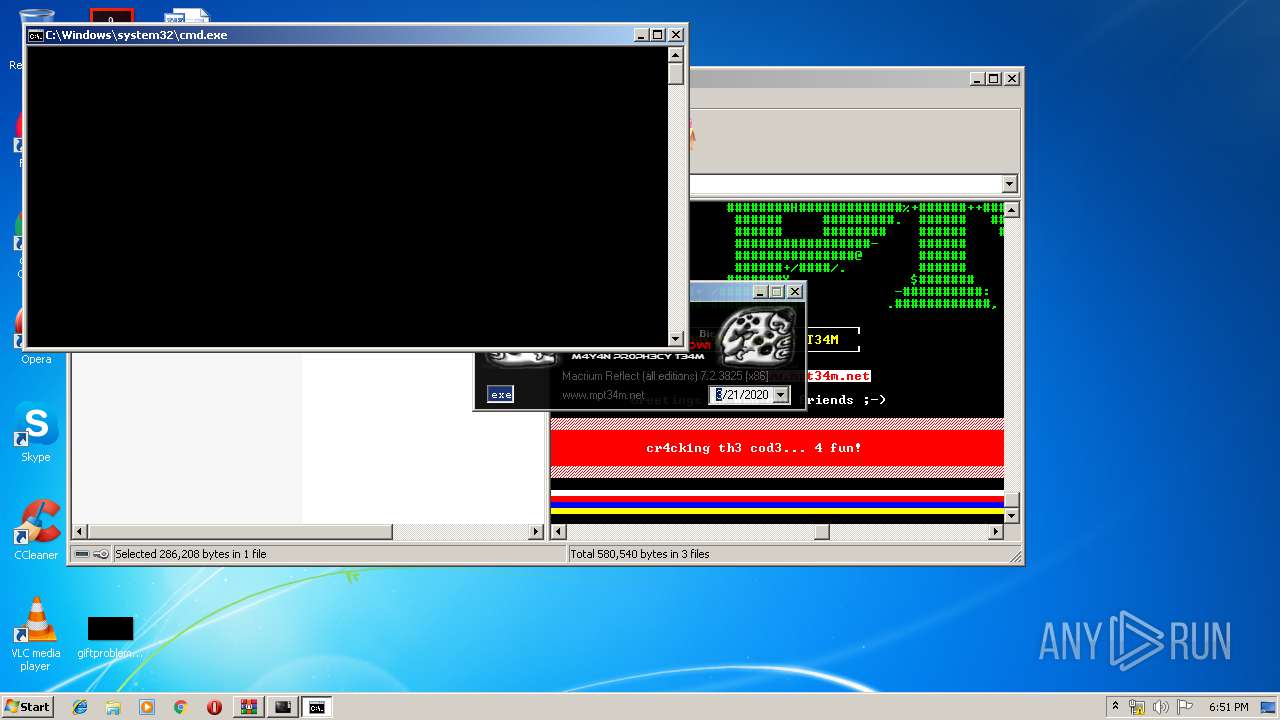
Starts CMD.EXE for commands execution
- macrium.reflect.(all.editions).7.2.3825.[x86]-MPT.exe (PID: 2400)
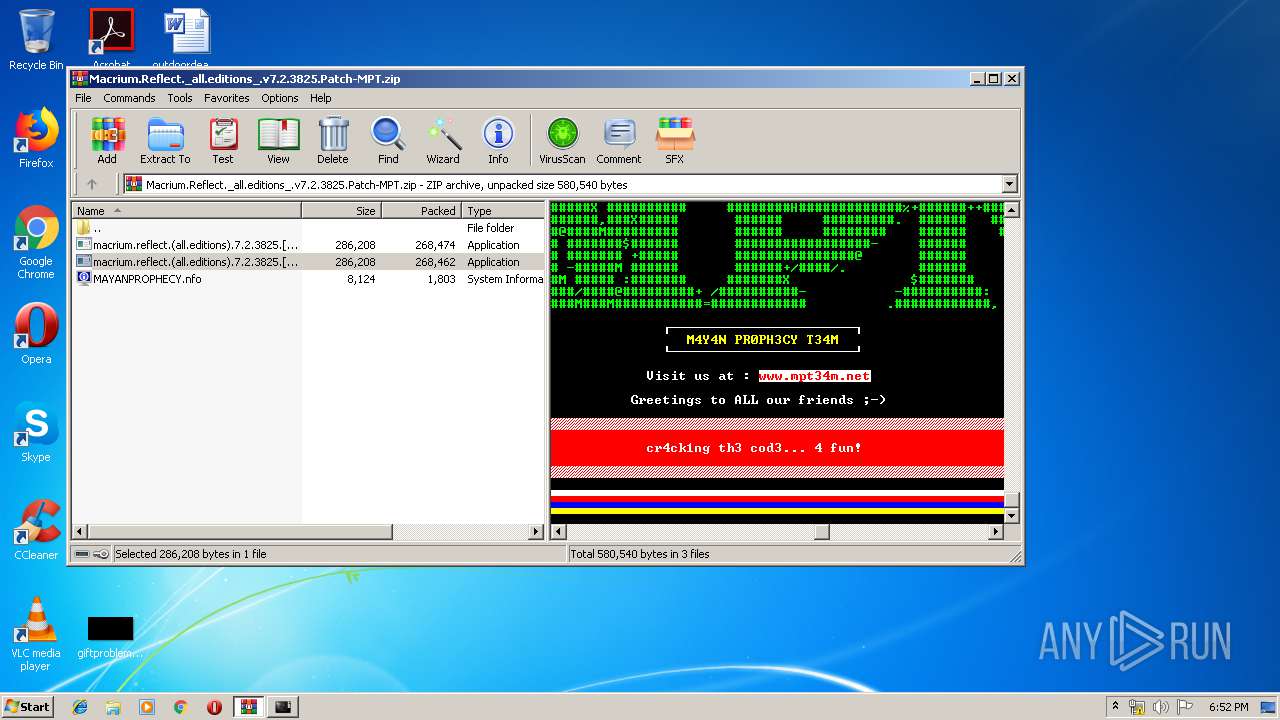
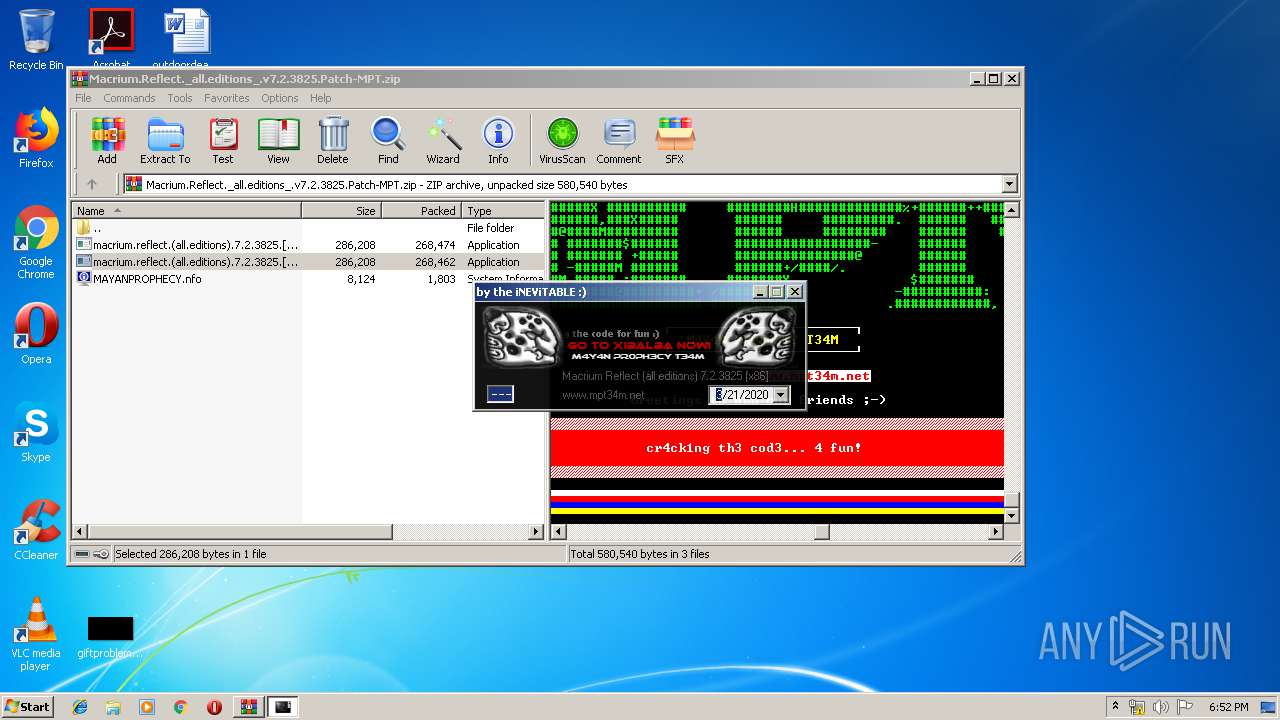
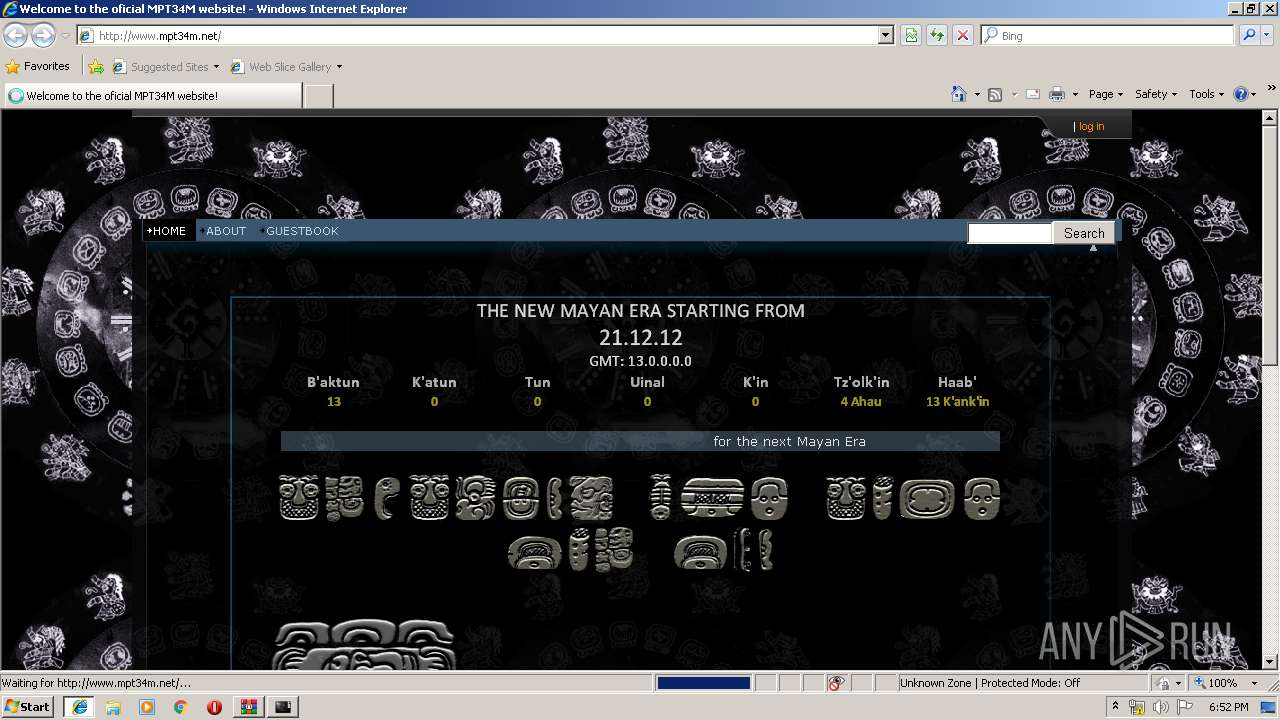
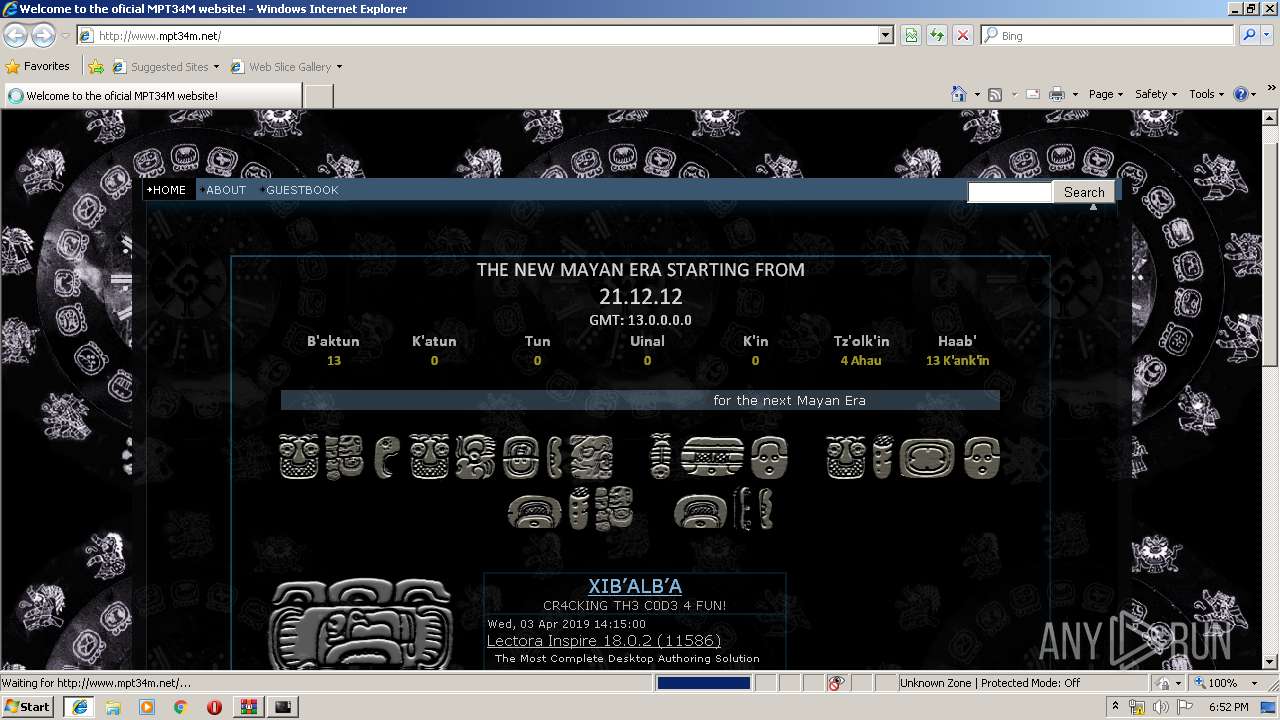
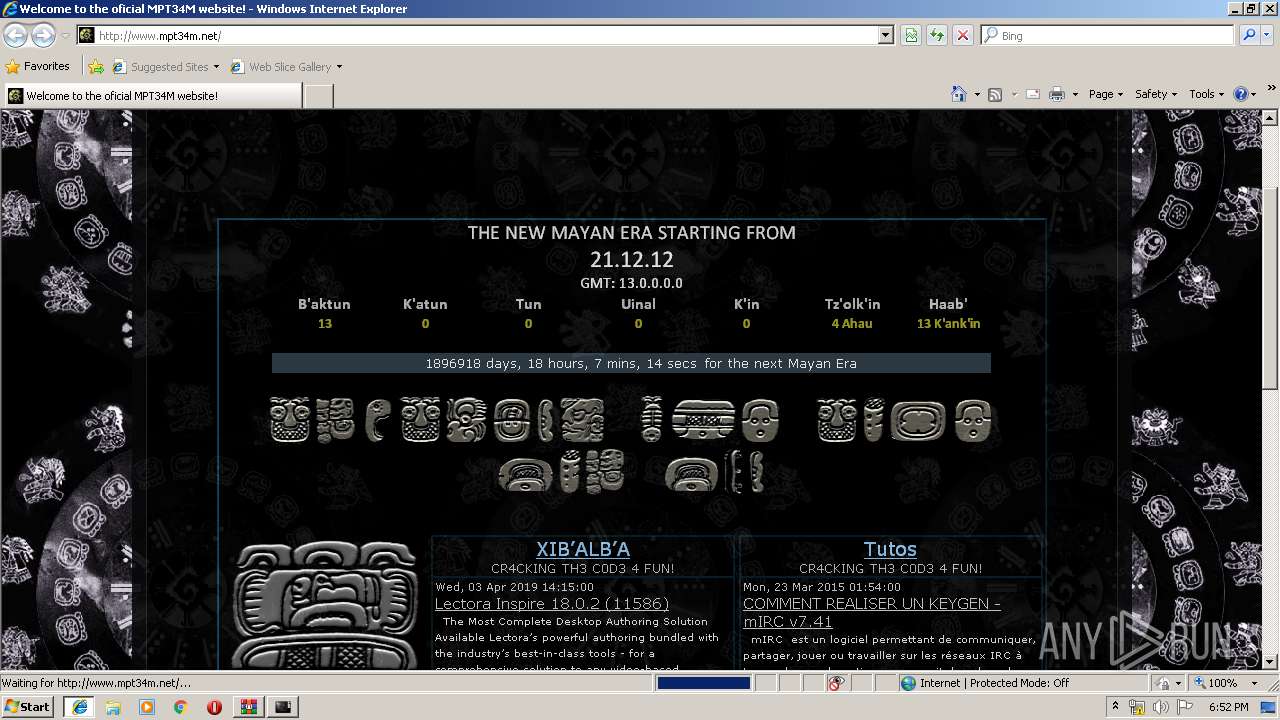
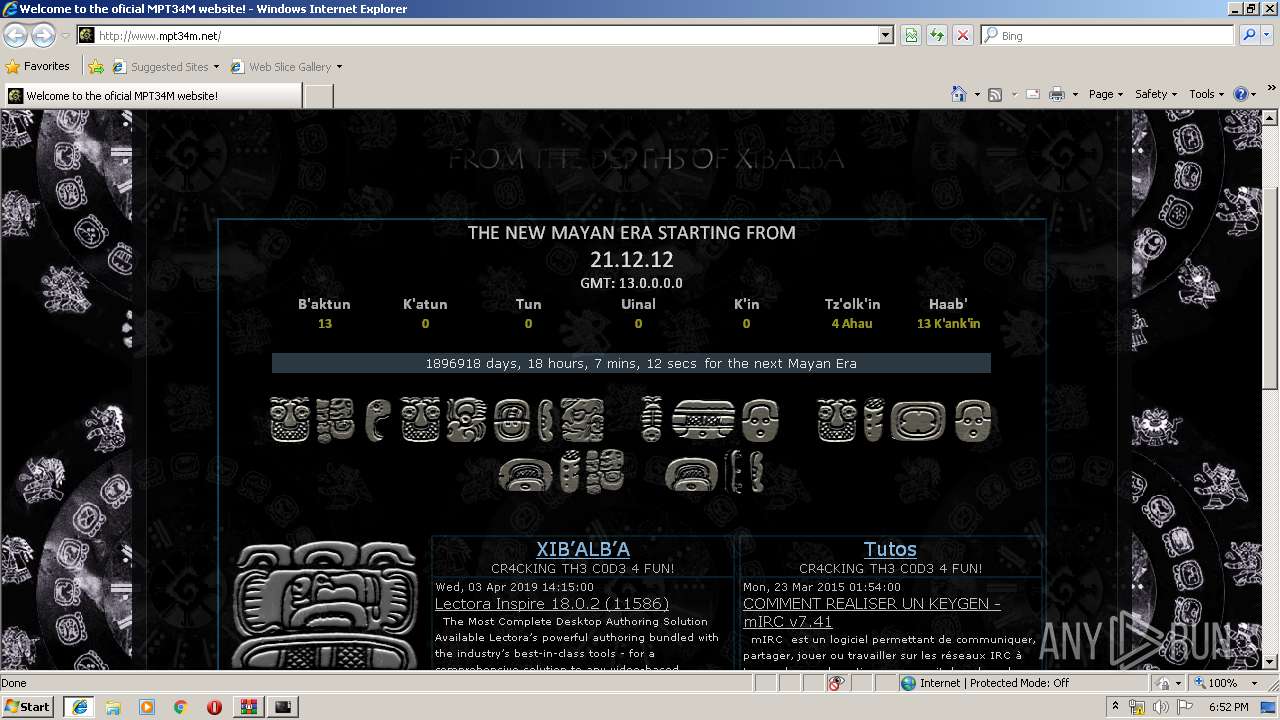
Starts Internet Explorer
- macrium.reflect.(all.editions).7.2.3825.[x86]-MPT.exe (PID: 2400)
Reads Internet Cache Settings
- macrium.reflect.(all.editions).7.2.3825.[x86]-MPT.exe (PID: 2400)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2320)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2644)
Application launched itself
- iexplore.exe (PID: 2320)
- chrome.exe (PID: 2460)
Reads Internet Cache Settings
- iexplore.exe (PID: 2644)
- iexplore.exe (PID: 2320)
Reads internet explorer settings
- iexplore.exe (PID: 2644)
Creates files in the user directory
- iexplore.exe (PID: 2644)
Manual execution by user
- chrome.exe (PID: 2460)
Changes settings of System certificates
- iexplore.exe (PID: 2644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:11:05 12:11:15 |
| ZipCRC: | 0xa58aff18 |
| ZipCompressedSize: | 1803 |
| ZipUncompressedSize: | 8124 |
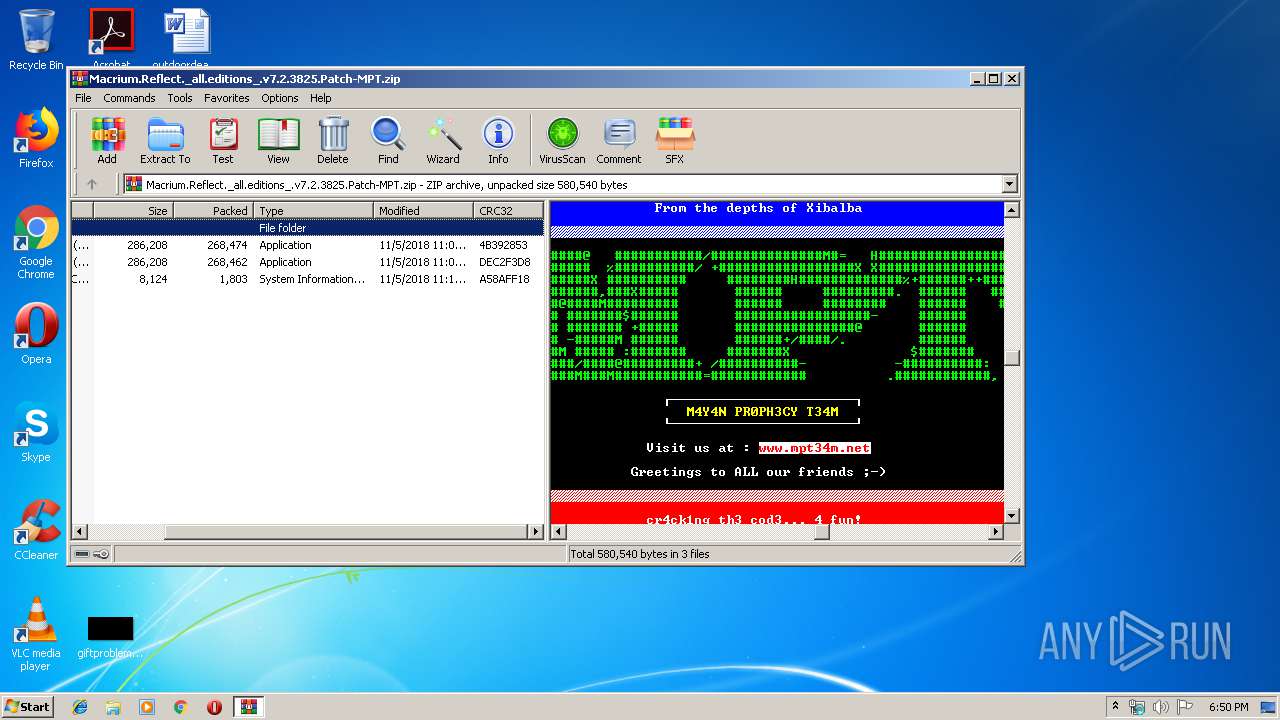
| ZipFileName: | MAYANPROPHECY.nfo |
Total processes
63
Monitored processes
23
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 936 | cmd /c "C:\Users\admin\AppData\Local\Temp\mptstart.bat" | C:\Windows\system32\cmd.exe | — | macrium.reflect.(all.editions).7.2.3825.[x86]-MPT.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,14854289295169909423,13871215889692877150,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3381567905716081753 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3381567905716081753 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4064 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,14854289295169909423,13871215889692877150,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=11514519782408711728 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11514519782408711728 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3844 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 | |||||||||||||||
| 1836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,14854289295169909423,13871215889692877150,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=13432964848190705523 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13432964848190705523 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3744 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2320 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | macrium.reflect.(all.editions).7.2.3825.[x86]-MPT.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2368 | cmd /c "C:\Users\admin\AppData\Local\Temp\mptstop.bat" | C:\Windows\system32\cmd.exe | — | macrium.reflect.(all.editions).7.2.3825.[x86]-MPT.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=956,14854289295169909423,13871215889692877150,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15951484882494600464 --mojo-platform-channel-handle=944 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
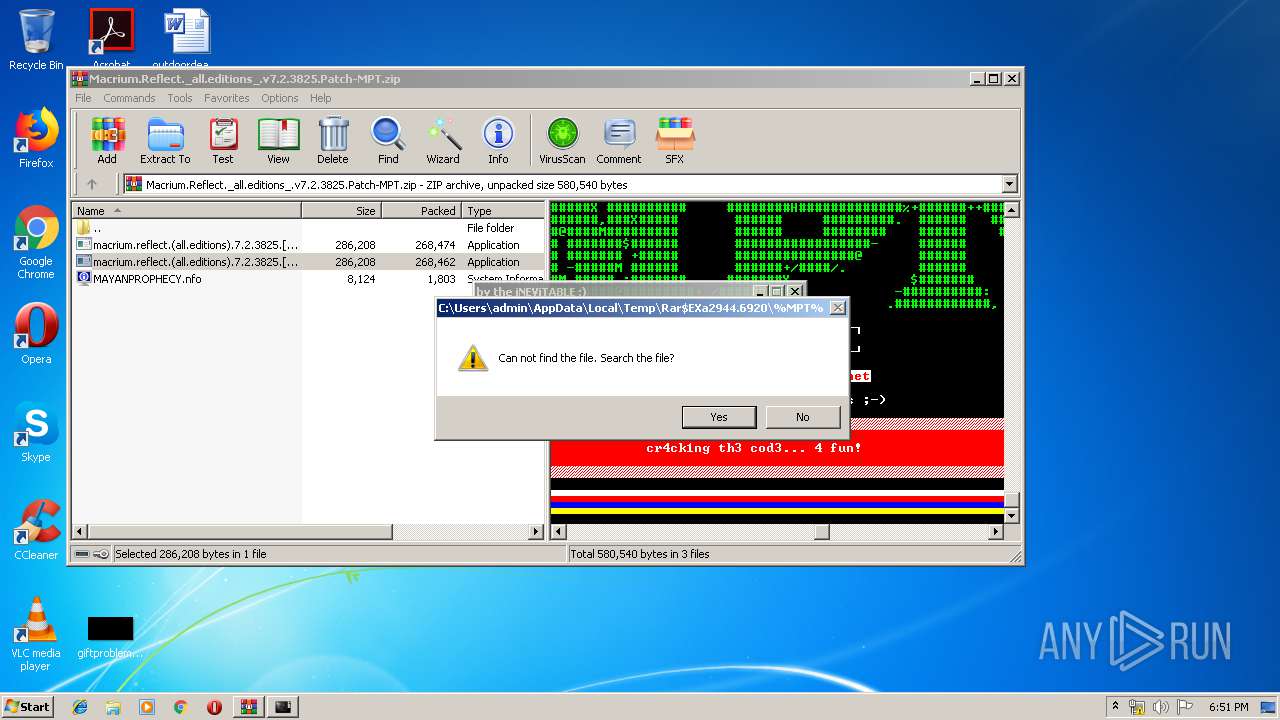
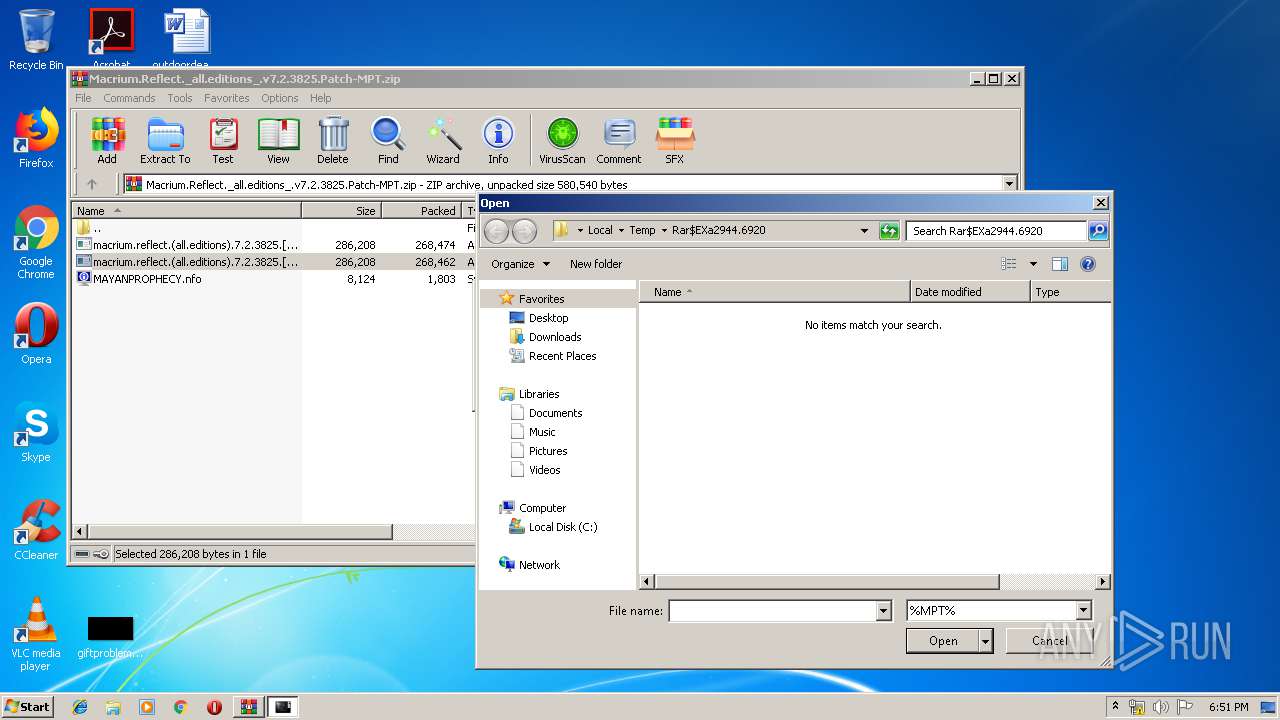
| 2400 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2944.6920\macrium.reflect.(all.editions).7.2.3825.[x86]-MPT.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2944.6920\macrium.reflect.(all.editions).7.2.3825.[x86]-MPT.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2404 | C:\Windows\system32\net1 stop "MacriumService" | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
1 690
Read events
1 427
Write events
256
Delete events
7
Modification events
| (PID) Process: | (2944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2944) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Macrium.Reflect._all.editions_.v7.2.3825.Patch-MPT.zip | |||
| (PID) Process: | (2944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2944) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\msinfo32.exe,-10001 |
Value: System Information File | |||
| (PID) Process: | (2944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
6
Suspicious files
52
Text files
65
Unknown types
25
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2400 | macrium.reflect.(all.editions).7.2.3825.[x86]-MPT.exe | C:\Users\admin\AppData\Local\Temp\mptstop.bat | — | |
MD5:— | SHA256:— | |||
| 2400 | macrium.reflect.(all.editions).7.2.3825.[x86]-MPT.exe | C:\Users\admin\AppData\Local\Temp\mptstart.bat | — | |
MD5:— | SHA256:— | |||
| 2320 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2320 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2644 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\mpt34m_net[1].htm | html | |
MD5:— | SHA256:— | |||
| 2644 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\PrivacIE\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2644 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\textstyles_nf[1].css | text | |
MD5:— | SHA256:— | |||
| 2944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2944.6920\macrium.reflect.(all.editions).7.2.3825.[x64]-MPT.exe | executable | |
MD5:9EC06E71C956C414C278C67F69564CD9 | SHA256:FE511ACB318D59F80D753EE9300B4CF937E25C4B1980A07F60B45DC1C3B12C8D | |||
| 2400 | macrium.reflect.(all.editions).7.2.3825.[x86]-MPT.exe | C:\Users\admin\AppData\Local\Temp\Berlin Sans FB.TTF | odttf | |
MD5:FE2027C27B6A24505F548C6FD2E1076D | SHA256:0B6044C72E67AAAE9C2AE3C8B4BB06D066FDBC02779C68E3883984ACBBE24CB8 | |||
| 2944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2944.6920\MAYANPROPHECY.nfo | text | |
MD5:AD107E1FDC5DACAC61093A3A41F52818 | SHA256:6E85B92368A28D2526742F0F049651895E0BEDE080358424E2B0859C1E72C572 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
45
DNS requests
32
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
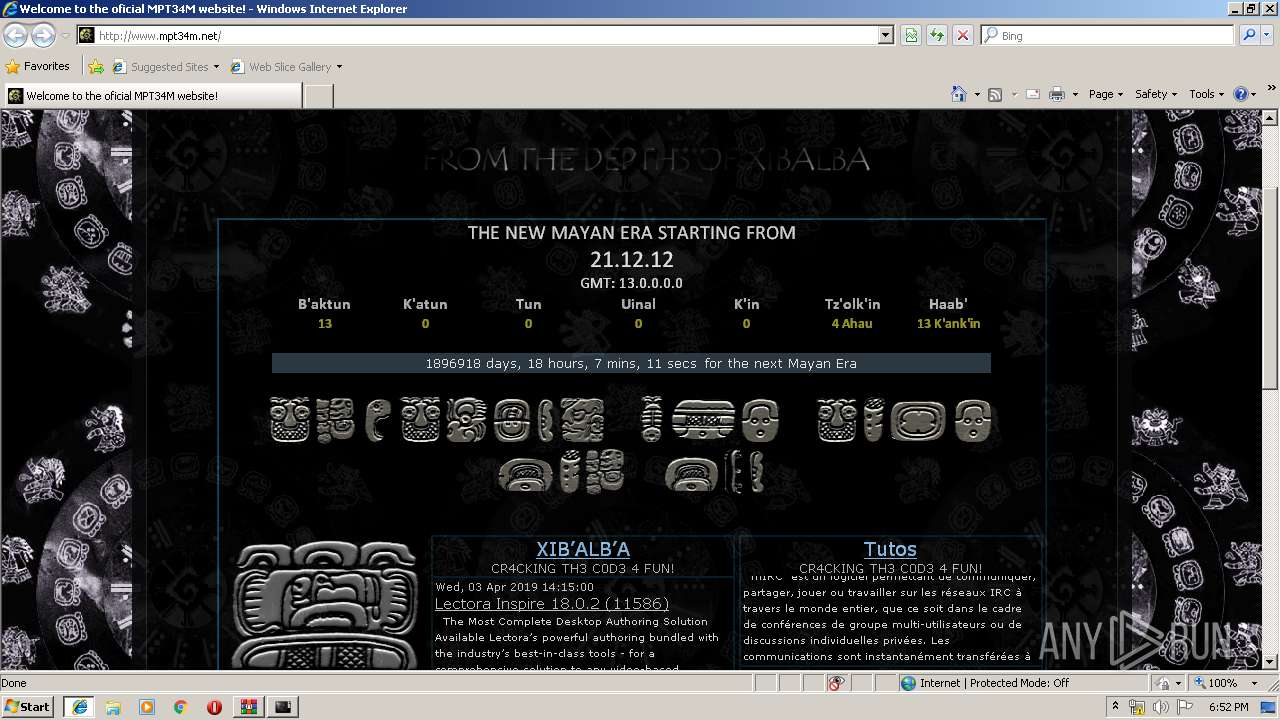
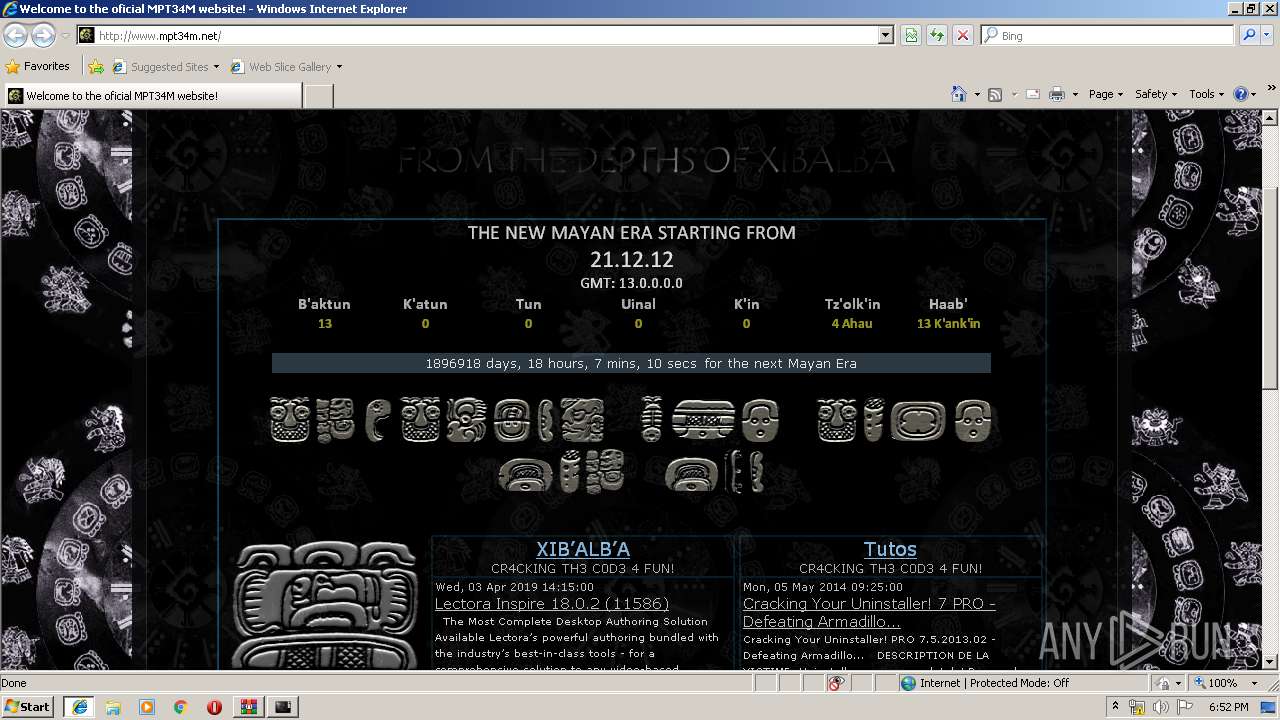
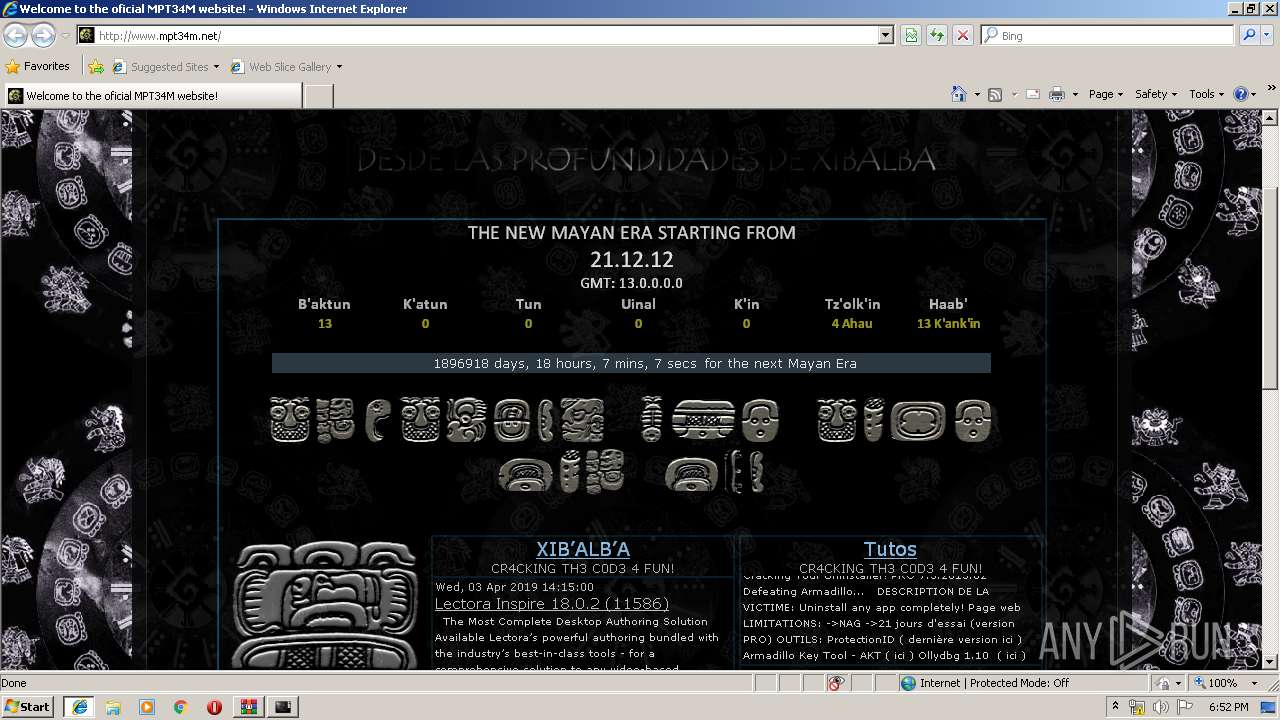
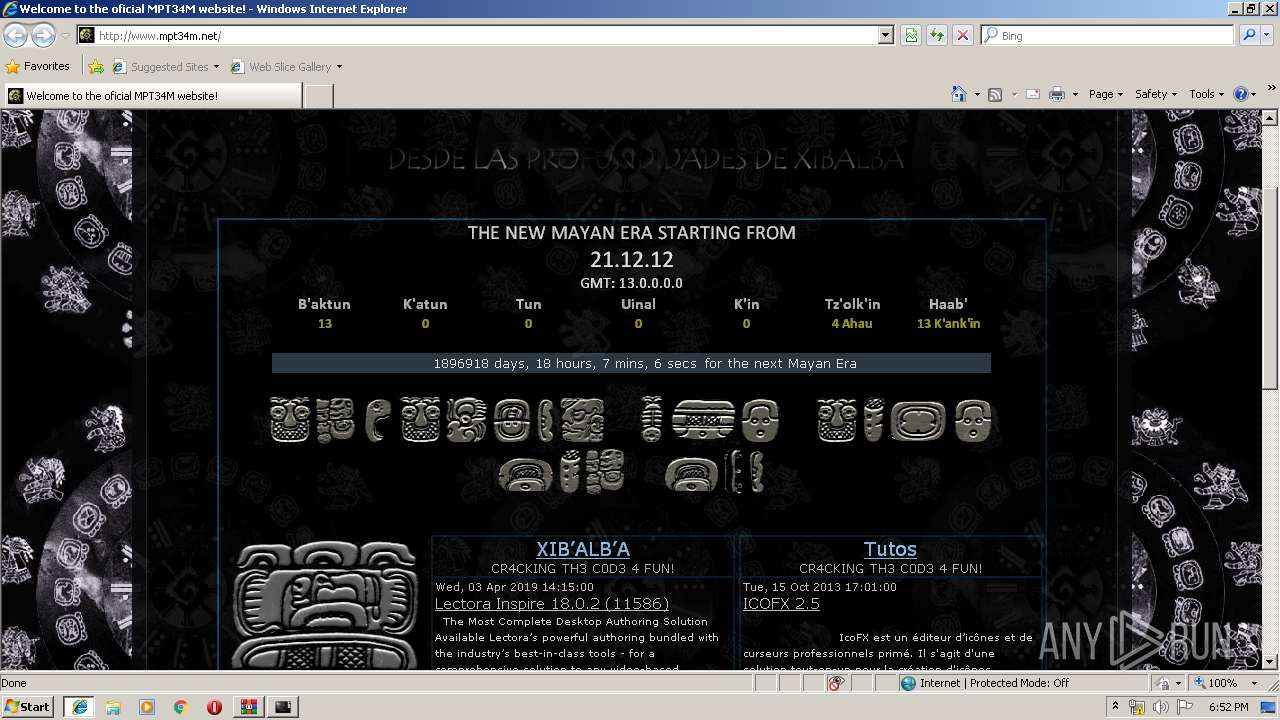
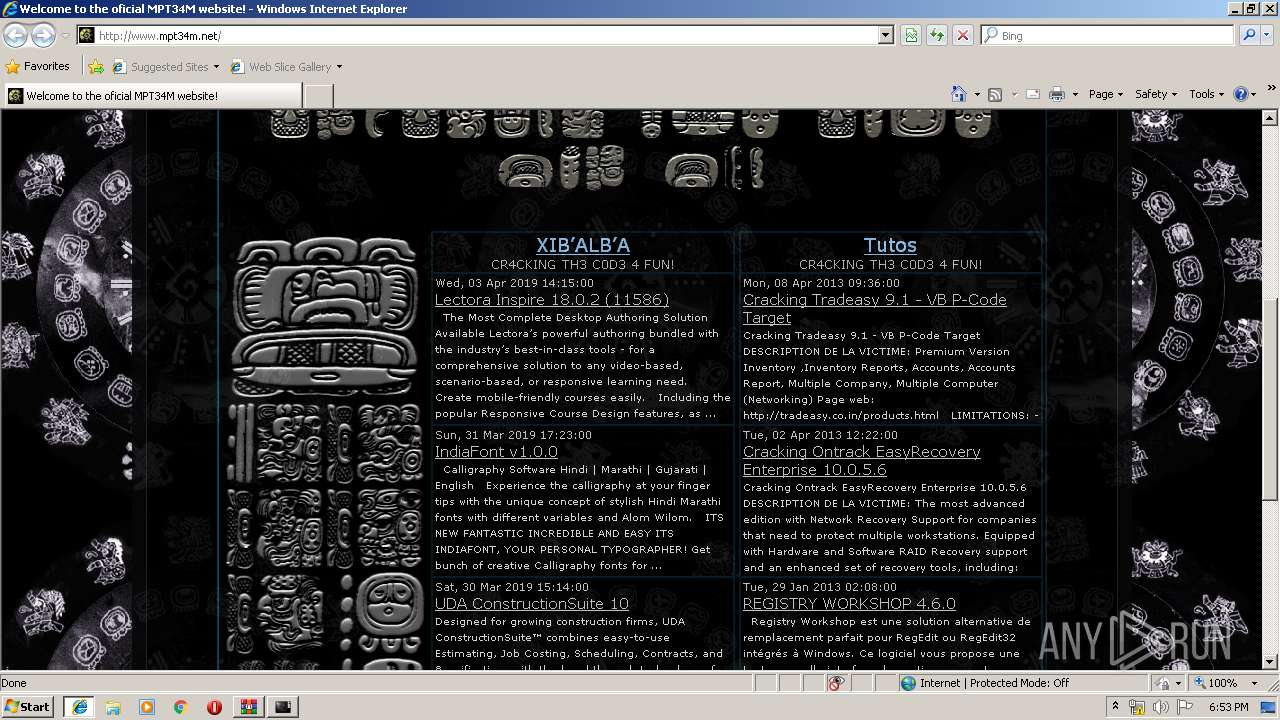
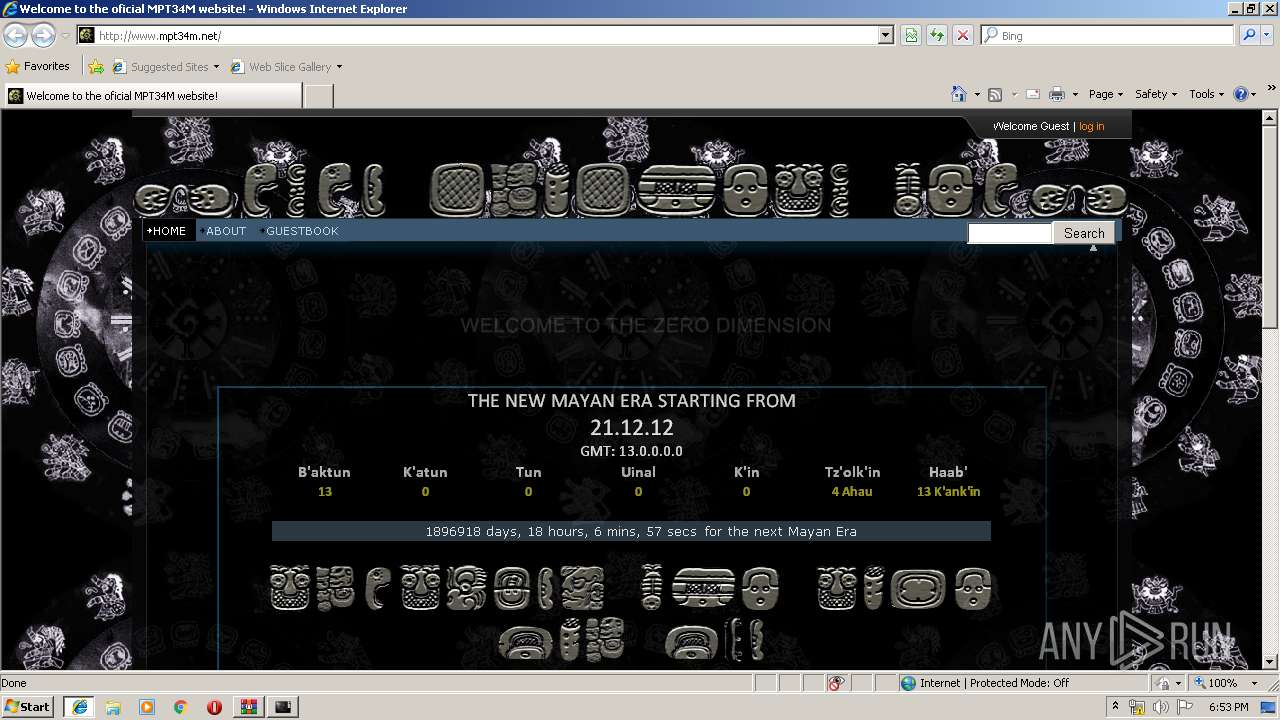
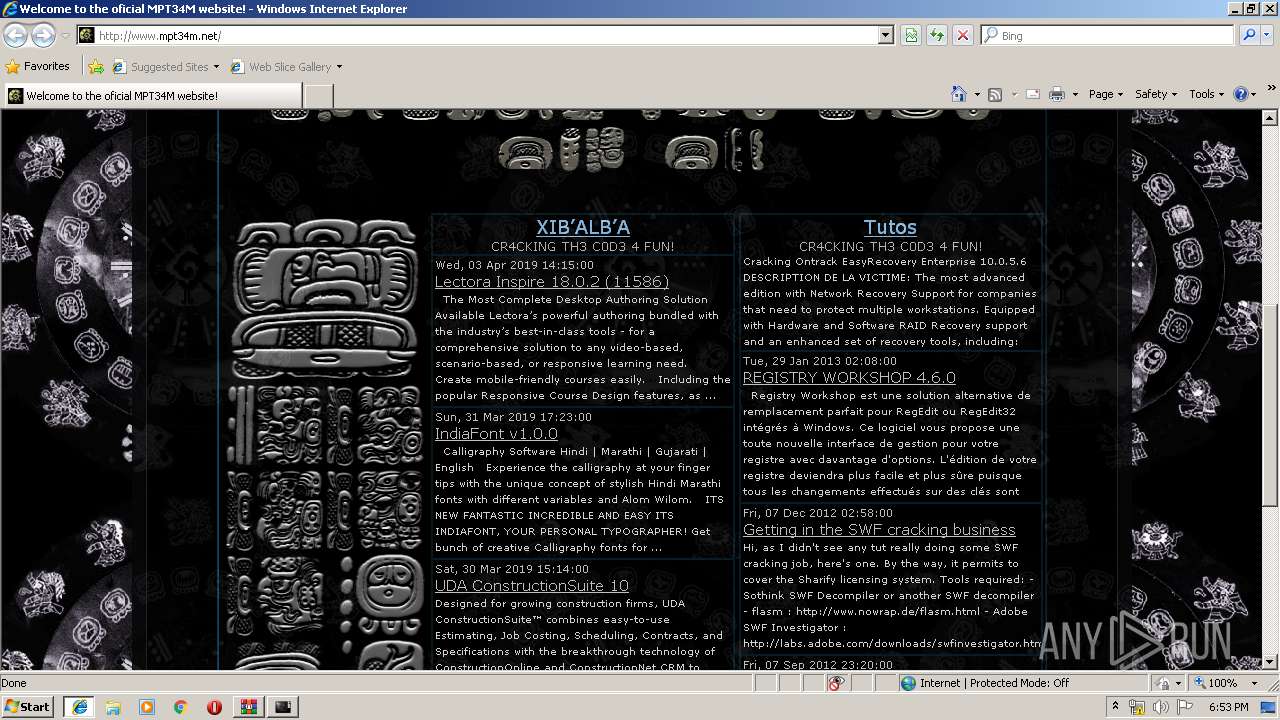
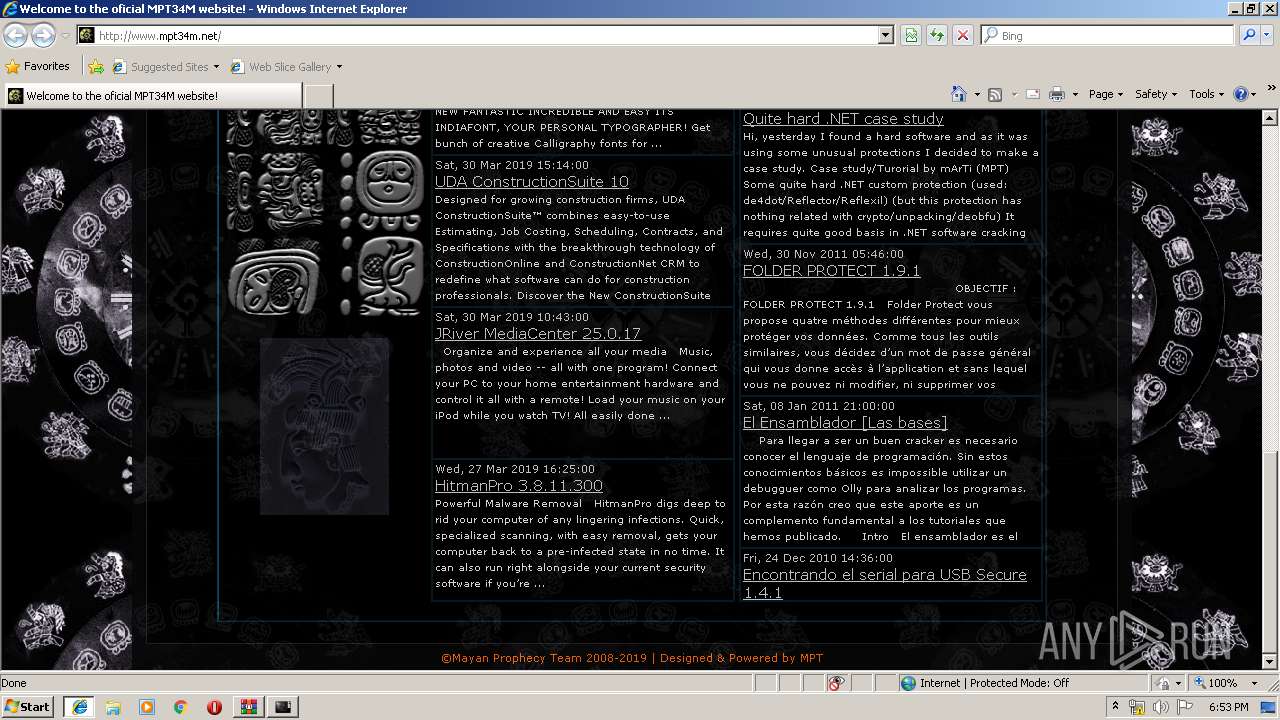
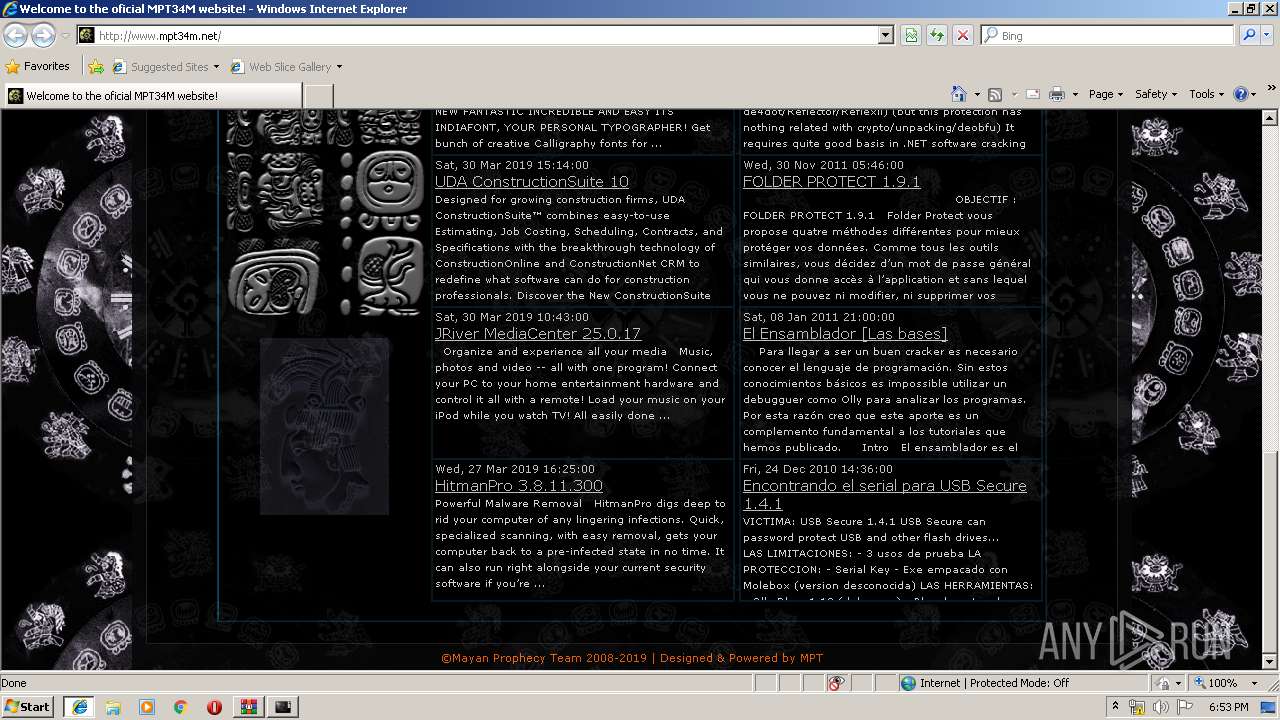
2644 | iexplore.exe | GET | 200 | 91.223.82.39:80 | http://www.mpt34m.net/documents/textstyles_nf.css | NL | text | 32.9 Kb | malicious |
2644 | iexplore.exe | GET | 200 | 185.60.216.19:80 | http://connect.facebook.net/en_US/all.js | IE | text | 1.74 Kb | whitelisted |
2644 | iexplore.exe | GET | 200 | 91.223.82.39:80 | http://www.mpt34m.net/extimages/scripts/login_l.png | NL | image | 541 b | malicious |
2644 | iexplore.exe | GET | 200 | 91.223.82.39:80 | http://www.mpt34m.net/ | NL | html | 17.3 Kb | malicious |
2644 | iexplore.exe | GET | 200 | 91.223.82.39:80 | http://www.mpt34m.net/extimages/scripts/login_m.png | NL | image | 195 b | malicious |
2644 | iexplore.exe | GET | 301 | 104.108.60.31:80 | http://www.adobe.com/images/shared/download_buttons/get_flash_player.gif | NL | html | 281 b | whitelisted |
2644 | iexplore.exe | GET | 200 | 91.223.82.39:80 | http://www.mpt34m.net/images/topbar.gif | NL | image | 56 b | malicious |
2644 | iexplore.exe | GET | 200 | 91.223.82.39:80 | http://www.mpt34m.net/extimages/scripts/detect.js | NL | text | 8.13 Kb | malicious |
2644 | iexplore.exe | GET | 200 | 91.223.82.39:80 | http://www.mpt34m.net/images/mb.gif | NL | image | 775 b | malicious |
2644 | iexplore.exe | GET | 200 | 91.223.82.39:80 | http://www.mpt34m.net/documents/scripts.js | NL | text | 90 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2644 | iexplore.exe | 91.223.82.39:80 | www.mpt34m.net | Iws Networks LLC | NL | malicious |
2320 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 64.233.167.82:443 | html5shiv.googlecode.com | Google Inc. | US | whitelisted |
2644 | iexplore.exe | 104.18.62.204:443 | anonymizer.info | Cloudflare Inc | US | shared |
2644 | iexplore.exe | 185.60.216.35:443 | www.facebook.com | Facebook, Inc. | IE | whitelisted |
2644 | iexplore.exe | 104.108.60.31:443 | www.adobe.com | Akamai Technologies, Inc. | NL | whitelisted |
2460 | chrome.exe | 172.217.16.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2460 | chrome.exe | 172.217.23.174:443 | clients1.google.com | Google Inc. | US | whitelisted |
2460 | chrome.exe | 216.58.206.14:443 | apis.google.com | Google Inc. | US | whitelisted |
2460 | chrome.exe | 216.58.206.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mpt34m.net |
| malicious |
www.bing.com |
| whitelisted |
html5shiv.googlecode.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
anonymizer.info |
| suspicious |
connect.facebook.net |
| whitelisted |
www.adobe.com |
| whitelisted |
www.facebook.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2644 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Outdated Flash Version M1 |