| File name: | 4kvideodownloaderplus_25.1.2_x64_online.exe |
| Full analysis: | https://app.any.run/tasks/2e49d874-248d-401c-8e94-75cee720dcbd |
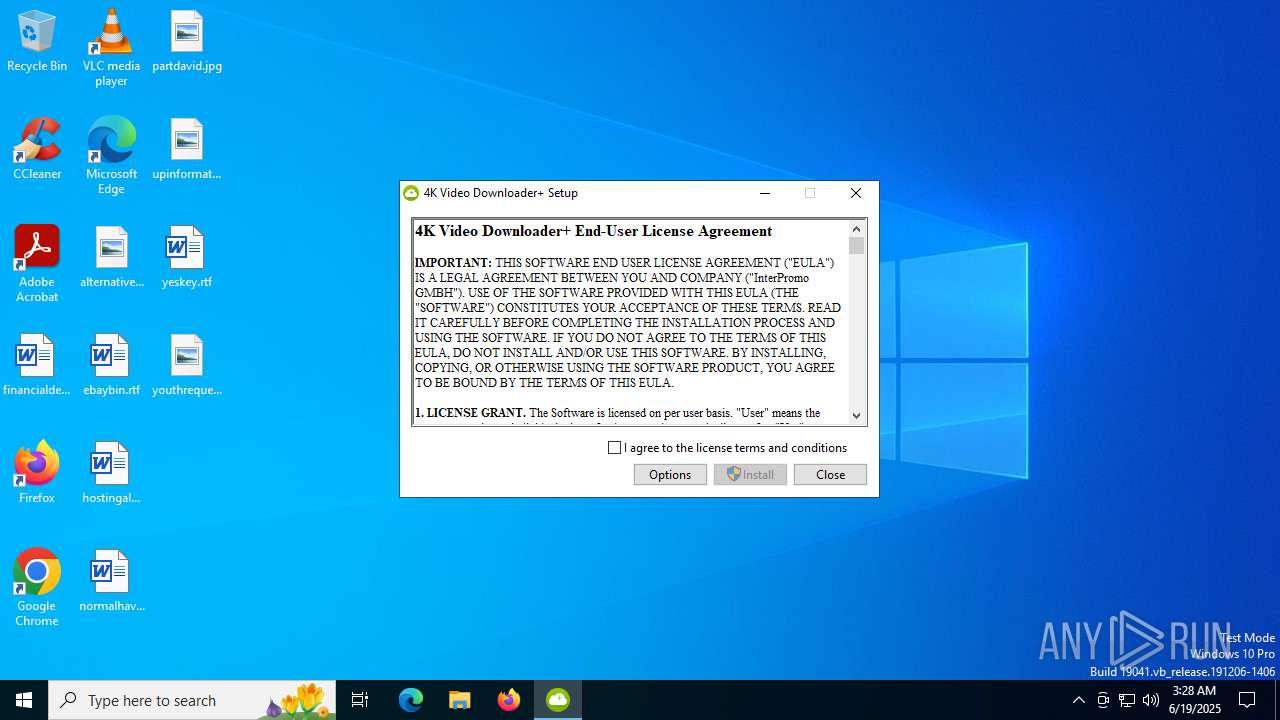
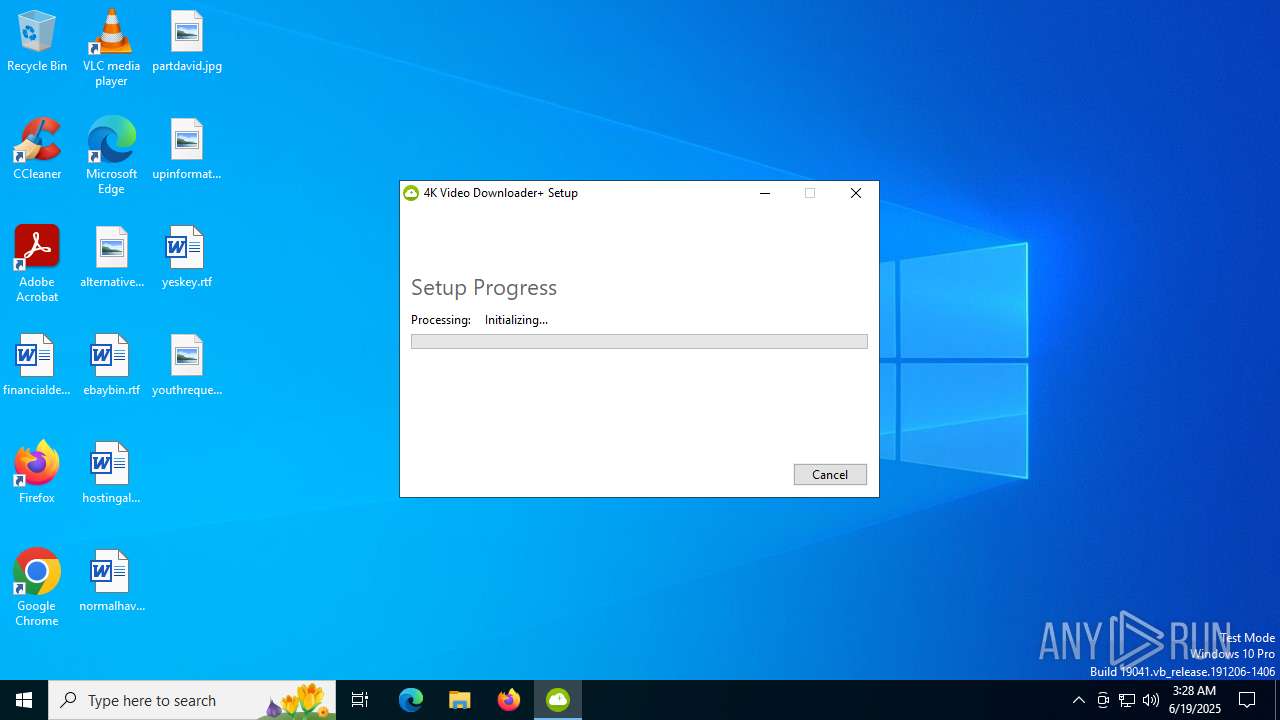
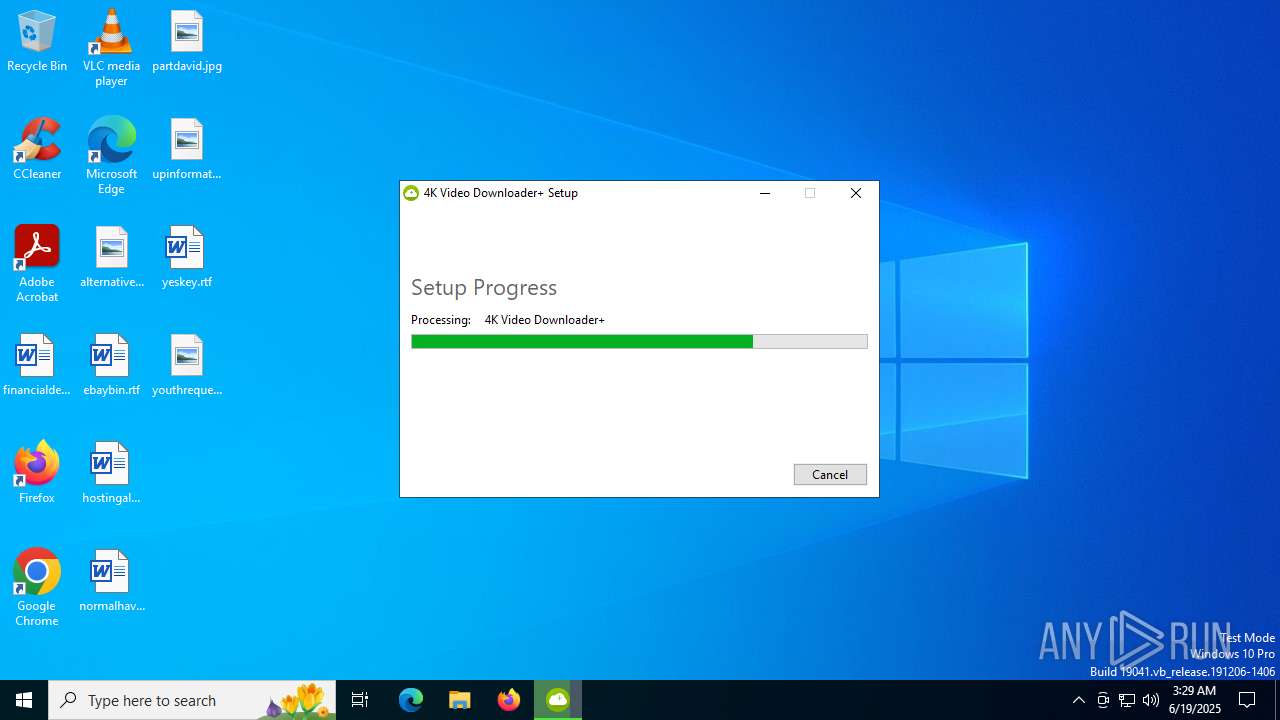
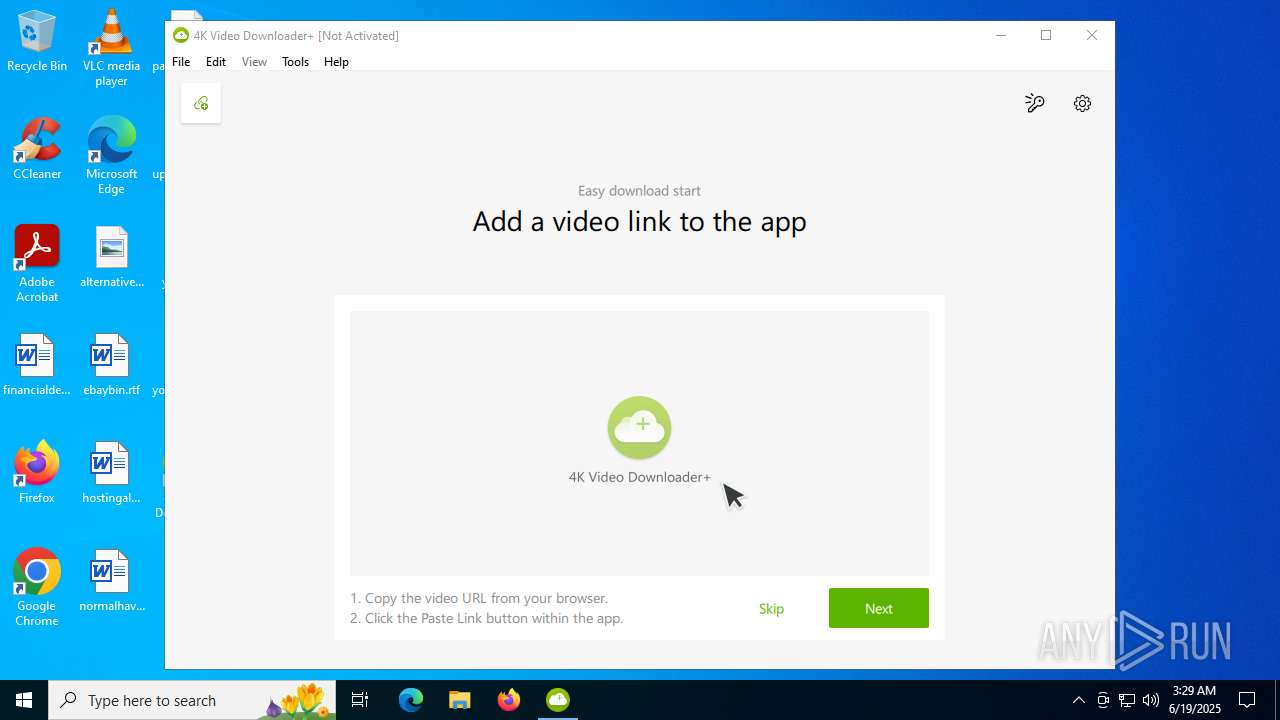
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2025, 03:28:46 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | F3F86E2536943EC6329E01937CDEBB0F |
| SHA1: | BC0426BA0951720C92DB8BFCDE1314F127E49CB4 |
| SHA256: | BE5422C810391D5C5C4CE7EAA6619B63131FDE342D9E56A596374CC865A9E5CE |
| SSDEEP: | 24576:pLN9pggkHLWqnivnuhHqaEVYSprkjrBN6r0UYq0EJV0yHXj:pLN9SgkHLWqnivnuhHqvVYSprurH6r08 |
MALICIOUS
Changes the autorun value in the registry
- 4kvideodownloaderplus_25.1.2_x64_online.exe (PID: 7048)
SUSPICIOUS
Starts itself from another location
- 4kvideodownloaderplus_25.1.2_x64_online.exe (PID: 3888)
Searches for installed software
- dllhost.exe (PID: 5612)
- 4kvideodownloaderplus_25.1.2_x64_online.exe (PID: 3888)
Executable content was dropped or overwritten
- 4kvideodownloaderplus_25.1.2_x64_online.exe (PID: 7048)
- 4kvideodownloaderplus_25.1.2_x64_online.exe (PID: 1568)
- 4kvideodownloaderplus_25.1.2_x64_online.exe (PID: 3888)
Reads security settings of Internet Explorer
- 4kvideodownloaderplus_25.1.2_x64_online.exe (PID: 3888)
- msi_analytics-1.2.exe (PID: 3092)
- msi_analytics-1.2.exe (PID: 4860)
- 4kvideodownloaderplus.exe (PID: 4892)
Creates a software uninstall entry
- 4kvideodownloaderplus_25.1.2_x64_online.exe (PID: 7048)
Adds/modifies Windows certificates
- msiexec.exe (PID: 6376)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6376)
The process drops C-runtime libraries
- msiexec.exe (PID: 6376)
Connects to unusual port
- msi_analytics-1.2.exe (PID: 3092)
- msi_analytics-1.2.exe (PID: 4860)
- 4kvideodownloaderplus.exe (PID: 4892)
Process drops legitimate windows executable
- msiexec.exe (PID: 6376)
Detected use of alternative data streams (AltDS)
- 4kvideodownloaderplus.exe (PID: 4892)
Executes as Windows Service
- VSSVC.exe (PID: 2520)
INFO
Create files in a temporary directory
- 4kvideodownloaderplus_25.1.2_x64_online.exe (PID: 1568)
- 4kvideodownloaderplus_25.1.2_x64_online.exe (PID: 3888)
- 4kvideodownloaderplus_25.1.2_x64_online.exe (PID: 7048)
- 4kvideodownloaderplus.exe (PID: 4892)
Manages system restore points
- SrTasks.exe (PID: 2188)
Checks supported languages
- 4kvideodownloaderplus_25.1.2_x64_online.exe (PID: 3888)
- 4kvideodownloaderplus_25.1.2_x64_online.exe (PID: 1568)
- msi_analytics-1.2.exe (PID: 3092)
- msiexec.exe (PID: 6376)
- msiexec.exe (PID: 2664)
- msi_analytics-1.2.exe (PID: 4860)
- 4kvideodownloaderplus.exe (PID: 4892)
- crashpad_handler.exe (PID: 3576)
- QtWebEngineProcess.exe (PID: 7056)
- QtWebEngineProcess.exe (PID: 4688)
- QtWebEngineProcess.exe (PID: 316)
- identity_helper.exe (PID: 8072)
- 4kvideodownloaderplus_25.1.2_x64_online.exe (PID: 7048)
The sample compiled with english language support
- 4kvideodownloaderplus_25.1.2_x64_online.exe (PID: 1568)
- 4kvideodownloaderplus_25.1.2_x64_online.exe (PID: 7048)
- msiexec.exe (PID: 6376)
- 4kvideodownloaderplus_25.1.2_x64_online.exe (PID: 3888)
Reads the computer name
- 4kvideodownloaderplus_25.1.2_x64_online.exe (PID: 3888)
- 4kvideodownloaderplus_25.1.2_x64_online.exe (PID: 7048)
- msi_analytics-1.2.exe (PID: 3092)
- msiexec.exe (PID: 6376)
- msiexec.exe (PID: 2664)
- msi_analytics-1.2.exe (PID: 4860)
- 4kvideodownloaderplus.exe (PID: 4892)
- QtWebEngineProcess.exe (PID: 7056)
- QtWebEngineProcess.exe (PID: 4688)
- QtWebEngineProcess.exe (PID: 316)
- identity_helper.exe (PID: 8072)
Creates files in the program directory
- 4kvideodownloaderplus_25.1.2_x64_online.exe (PID: 7048)
Reads the machine GUID from the registry
- 4kvideodownloaderplus_25.1.2_x64_online.exe (PID: 7048)
- 4kvideodownloaderplus_25.1.2_x64_online.exe (PID: 3888)
- msiexec.exe (PID: 6376)
- 4kvideodownloaderplus.exe (PID: 4892)
Creates files or folders in the user directory
- 4kvideodownloaderplus_25.1.2_x64_online.exe (PID: 3888)
- msiexec.exe (PID: 6376)
- 4kvideodownloaderplus.exe (PID: 4892)
Reads the software policy settings
- 4kvideodownloaderplus_25.1.2_x64_online.exe (PID: 3888)
- msiexec.exe (PID: 6376)
- 4kvideodownloaderplus.exe (PID: 4892)
Checks proxy server information
- 4kvideodownloaderplus_25.1.2_x64_online.exe (PID: 3888)
- msi_analytics-1.2.exe (PID: 3092)
- msi_analytics-1.2.exe (PID: 4860)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6376)
Creates a software uninstall entry
- msiexec.exe (PID: 6376)
Process checks computer location settings
- 4kvideodownloaderplus.exe (PID: 4892)
- QtWebEngineProcess.exe (PID: 7056)
- QtWebEngineProcess.exe (PID: 316)
- QtWebEngineProcess.exe (PID: 4688)
- 4kvideodownloaderplus_25.1.2_x64_online.exe (PID: 3888)
Application launched itself
- msedge.exe (PID: 3760)
- msedge.exe (PID: 5436)
Reads Environment values
- identity_helper.exe (PID: 8072)
Launching a file from a Registry key
- 4kvideodownloaderplus_25.1.2_x64_online.exe (PID: 7048)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:09:17 05:33:38+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit, Removable run from swap, Net run from swap |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 299008 |
| InitializedDataSize: | 352256 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2df71 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 25.1.2.198 |
| ProductVersionNumber: | 25.1.2.198 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
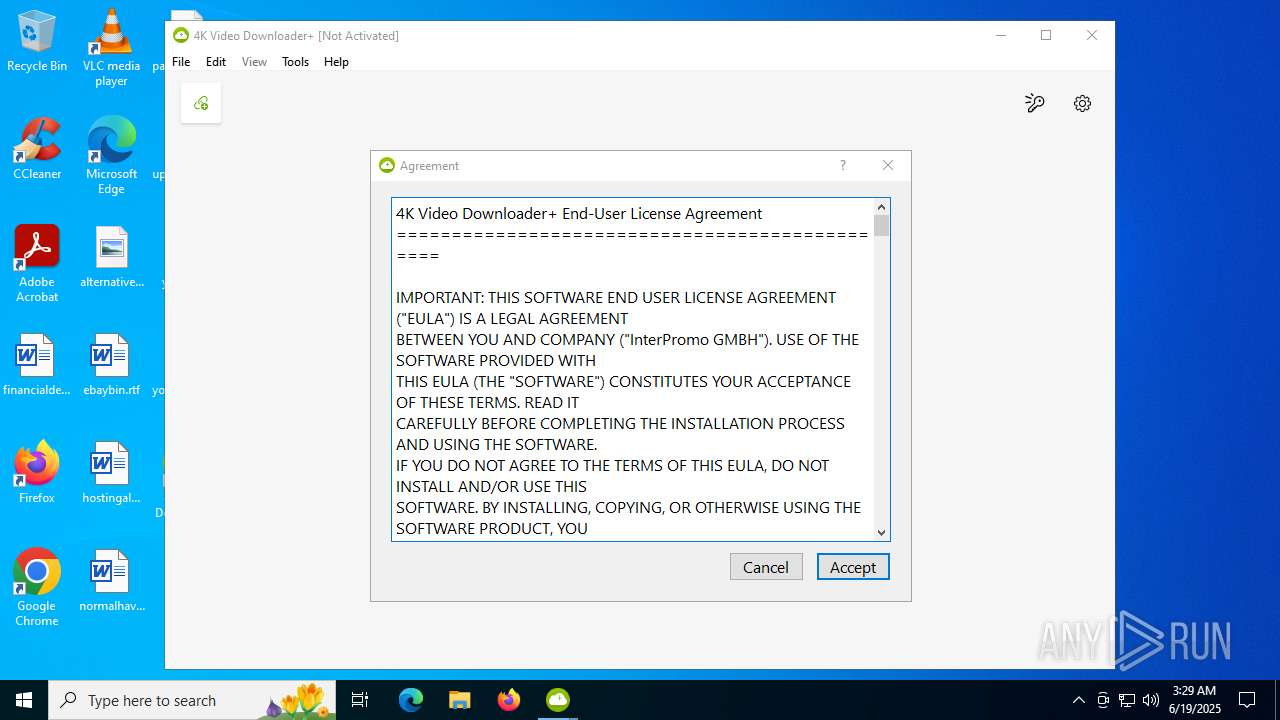
| CompanyName: | InterPromo GMBH |
| FileDescription: | 4K Video Downloader+ |
| FileVersion: | 25.1.2.198 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) InterPromo GMBH. All rights reserved. |
| OriginalFileName: | 4kvideodownloaderplus_25.1.2_x64_online.exe |
| ProductName: | 4K Video Downloader+ |
| ProductVersion: | 25.1.2.198 |
Total processes
175
Monitored processes
35
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Program Files\4KDownload\4kvideodownloaderplus\QtWebEngineProcess.exe" --type=renderer --disable-speech-api --enable-threaded-compositing --enable-features=AllowContentInitiatedDataUrlNavigations,NetworkServiceInProcess,TracingServiceInProcess --disable-features=BackgroundFetch,ConsolidatedMovementXY,DnsOverHttpsUpgrade,InstalledApp,MojoVideoCapture,PictureInPicture,SmsReceiver,UseSkiaRenderer,WebPayments,WebUSB --disable-gpu-compositing --lang=en --webengine-schemes=qrc:sLV --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=4112 /prefetch:1 | C:\Program Files\4KDownload\4kvideodownloaderplus\QtWebEngineProcess.exe | — | 4kvideodownloaderplus.exe | |||||||||||
User: admin Company: The Qt Company Ltd. Integrity Level: LOW Description: C++ Application Development Framework Exit code: 0 Version: 5.15.13.0 Modules
| |||||||||||||||
| 768 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | msi_analytics-1.2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1136 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | msi_analytics-1.2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1568 | "C:\Users\admin\AppData\Local\Temp\4kvideodownloaderplus_25.1.2_x64_online.exe" | C:\Users\admin\AppData\Local\Temp\4kvideodownloaderplus_25.1.2_x64_online.exe | explorer.exe | ||||||||||||
User: admin Company: InterPromo GMBH Integrity Level: MEDIUM Description: 4K Video Downloader+ Exit code: 0 Version: 25.1.2.198 Modules
| |||||||||||||||
| 1944 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2472,i,7998241219320808759,11954076649403566979,262144 --variations-seed-version --mojo-platform-channel-handle=2468 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2188 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2520 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2664 | C:\Windows\syswow64\MsiExec.exe -Embedding 12053882404333C1AF701314EB60601D | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3092 | "C:\ProgramData\Package Cache\BC8605C2DE03AE5CEB6BC09A1F25F20D1C49CF7B\msi_analytics-1.2.exe" --regkey "Software\4kdownload.com\4K Video Downloader+\Analytics" --an Wix --av 2 --ec "4K Video Downloader+" --ea "before-install" --el "x64" --af "" | C:\ProgramData\Package Cache\BC8605C2DE03AE5CEB6BC09A1F25F20D1C49CF7B\msi_analytics-1.2.exe | 4kvideodownloaderplus_25.1.2_x64_online.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3576 | "C:/Program Files/4KDownload/4kvideodownloaderplus/crashpad_handler.exe" "--database=C:/Users/admin/AppData/Local/4kdownload.com/4K Video Downloader+/4K Video Downloader+/../crashdb" "--metrics-dir=C:/Users/admin/AppData/Local/4kdownload.com/4K Video Downloader+/4K Video Downloader+/../crashdb" --url=https://o354938.ingest.sentry.io/api/4505076032667648/minidump/?sentry_key=1a7e5dd848a445bd99b93ea2e155896c --annotation=format=minidump --annotation=sentry[release]=25.1.2.0198 --initial-client-data=0x5a8,0x5ac,0x5b0,0x584,0x5b4,0x7ff7f7fc6a48,0x7ff7f7fc6a60,0x7ff7f7fc6a78 | C:\Program Files\4KDownload\4kvideodownloaderplus\crashpad_handler.exe | — | 4kvideodownloaderplus.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
17 907
Read events
17 043
Write events
830
Delete events
34
Modification events
| (PID) Process: | (7048) 4kvideodownloaderplus_25.1.2_x64_online.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000EEAC824ACAE0DB01881B0000B00D0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5612) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000EEAC824ACAE0DB01EC150000E4050000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5612) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 48000000000000001E70A64ACAE0DB01EC150000E4050000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5612) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000008FFEAF4ACAE0DB01EC150000E4050000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2520) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000005401014BCAE0DB01D80900005C080000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2520) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2520) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | write | Name: | Element |
Value: 0000000000000000000000000000000006000000000000004800000000000000715E5C2FA985EB1190A89A9B763584210000000000000000745E5C2FA985EB1190A89A9B7635842100000000000000000000000000000000 | |||
| (PID) Process: | (2520) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\12000002 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2520) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\12000002 |
| Operation: | write | Name: | Element |
Value: \EFI\Microsoft\Boot\bootmgfw.efi | |||
| (PID) Process: | (2520) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{5b970157-8568-11eb-b45c-806e6f6e6963}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
87
Suspicious files
721
Text files
379
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1568 | 4kvideodownloaderplus_25.1.2_x64_online.exe | C:\Users\admin\AppData\Local\Temp\{9F7107FC-8166-4DFC-9308-CEE6BB541F23}\.cr\4kvideodownloaderplus_25.1.2_x64_online.exe | executable | |
MD5:917A70191643F1E7B52B3B35228EFAB0 | SHA256:85F55EB3C705F0940C309A35EFC2850C9CC09A48B232B010B0725A429D89BB32 | |||
| 3888 | 4kvideodownloaderplus_25.1.2_x64_online.exe | C:\Users\admin\AppData\Local\Temp\{EFCC4C9D-E2CF-4F47-A7F0-E6C7B58FD6F7}\.ba\thm.wxl | xml | |
MD5:4D10FF1DF3576D52D4AA0F17C804A7EA | SHA256:D702A93B21B7513F84E132608E89099B13BF0618A8F2EDC673DF3592B5AB3C00 | |||
| 3888 | 4kvideodownloaderplus_25.1.2_x64_online.exe | C:\Users\admin\AppData\Local\Temp\{EFCC4C9D-E2CF-4F47-A7F0-E6C7B58FD6F7}\.ba\license.rtf | text | |
MD5:9987DADE9C6F9849EA4E84F8F57868F0 | SHA256:FCC8CC303EC23C2961512A892126405C4925D4961AEDA9BB7BE183F60709DECF | |||
| 3888 | 4kvideodownloaderplus_25.1.2_x64_online.exe | C:\Users\admin\AppData\Local\Temp\{EFCC4C9D-E2CF-4F47-A7F0-E6C7B58FD6F7}\.ba\thm.xml | xml | |
MD5:3443F15AB01877208AC563C323E6C216 | SHA256:1FA4A4B8FBE8444B3BD8C86E5B2897CF876E768F2083F224934C9D44DFEA69D7 | |||
| 3888 | 4kvideodownloaderplus_25.1.2_x64_online.exe | C:\Users\admin\AppData\Local\Temp\{EFCC4C9D-E2CF-4F47-A7F0-E6C7B58FD6F7}\.ba\wixstdba.dll | executable | |
MD5:FE7E0BD53F52E6630473C31299A49FDD | SHA256:2BEA14D70943A42D344E09B7C9DE5562FA7E109946E1C615DD584DA30D06CC80 | |||
| 3888 | 4kvideodownloaderplus_25.1.2_x64_online.exe | C:\Users\admin\AppData\Local\Temp\{EFCC4C9D-E2CF-4F47-A7F0-E6C7B58FD6F7}\.ba\1036\thm.wxl | xml | |
MD5:B08C2F7DCCDF1F702A1B952883332A9A | SHA256:25A6E9696F911B7B3D4F9D261C2D5C59A7C89C34D900317E1D7636827C5B6A9E | |||
| 3888 | 4kvideodownloaderplus_25.1.2_x64_online.exe | C:\Users\admin\AppData\Local\Temp\{EFCC4C9D-E2CF-4F47-A7F0-E6C7B58FD6F7}\.ba\1029\thm.wxl | xml | |
MD5:8B2AE816E0397D01709E7827347AFD75 | SHA256:98A8F5E72B3C7AED578E0D953D7512A8B92A9BA67DC2345A34716DFEB9375D51 | |||
| 3888 | 4kvideodownloaderplus_25.1.2_x64_online.exe | C:\Users\admin\AppData\Local\Temp\{EFCC4C9D-E2CF-4F47-A7F0-E6C7B58FD6F7}\.ba\1035\thm.wxl | xml | |
MD5:42972279B89654046D58504AC67E8044 | SHA256:012688F8DCA0B3EDEAB13103AD2993B2A903E1C0335A3FFD491F5B5BA4246AFA | |||
| 5612 | dllhost.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3888 | 4kvideodownloaderplus_25.1.2_x64_online.exe | C:\Users\admin\AppData\Local\Temp\{EFCC4C9D-E2CF-4F47-A7F0-E6C7B58FD6F7}\.ba\1046\thm.wxl | xml | |
MD5:EF78C2634C544DA4CC1E179EB17F9770 | SHA256:F48046595897CDC59E0D51BE9E7CA308FEBEC313751AEF14E1A466994E5B57A6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
108
DNS requests
74
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5012 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3888 | 4kvideodownloaderplus_25.1.2_x64_online.exe | GET | 200 | 104.18.21.213:80 | http://e5.c.lencr.org/113.crl | unknown | — | — | whitelisted |
3092 | msi_analytics-1.2.exe | GET | 200 | 34.213.215.111:8018 | http://sa.openmedia.co:8018/collect?an=Wix&av=2&cid=cdf9de7e-b20a-4a41-9e43-8908883c908f&ec=4K%20Video%20Downloader%2B&ea=before-install&el=windows%206.2.9200%20|%20x64 | unknown | — | — | unknown |
6376 | msiexec.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBTDHsfuqfubd3pihvq4mgQVWgHWNwQUyH7SaoUqG8oZmAQHJ89QEE9oqKICEzMAAAAHh6M0o3uljhwAAAAAAAc%3D | unknown | — | — | whitelisted |
6376 | msiexec.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBTOQYLFSE5GO%2FpaRVfYu7d9gZEbQAQU2UEpsA8PY2zvadf1zSmepEhqMOYCEzMAAAAF%2B3pcMhNh310AAAAAAAU%3D | unknown | — | — | whitelisted |
6376 | msiexec.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBTh4QXD3xfHaxna9yfH20h%2Ft5LfbQQUZZ9RzoVofy%2BKRYiq3acxux4NAF4CEzMAAx%2BBMldmm0P6vI4AAAADH4E%3D | unknown | — | — | whitelisted |
6376 | msiexec.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBTh4QXD3xfHaxna9yfH20h%2Ft5LfbQQUZZ9RzoVofy%2BKRYiq3acxux4NAF4CEzMAAx%2BBMldmm0P6vI4AAAADH4E%3D | unknown | — | — | whitelisted |
6376 | msiexec.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ID%20Verified%20CS%20EOC%20CA%2002.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6876 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2336 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
5012 | svchost.exe | 20.190.159.129:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5012 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 23.216.77.42:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
dl.4kdownload.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6212 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6212 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6212 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6212 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6212 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6212 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6212 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6212 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6212 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6212 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
Process | Message |
|---|---|
4kvideodownloaderplus.exe | QEventLoop: Cannot be used without QApplication
|