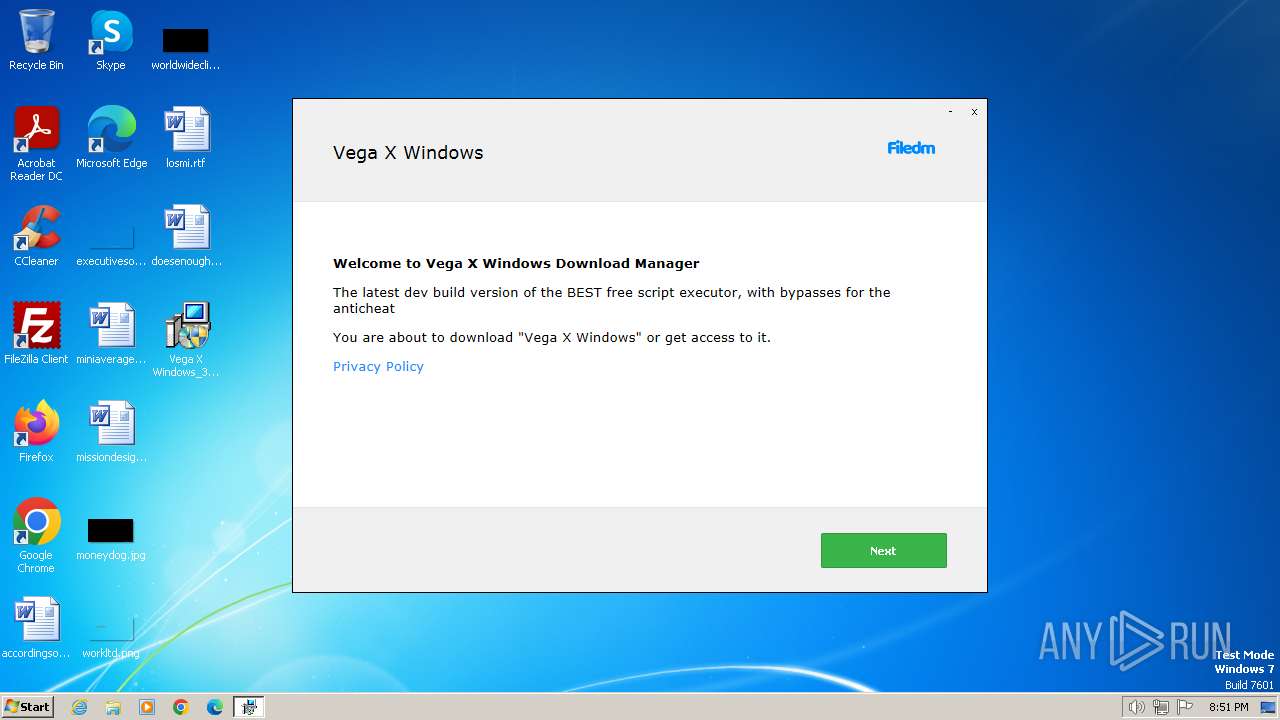
| File name: | Vega X Windows_38858099.exe |
| Full analysis: | https://app.any.run/tasks/ca5f8fdd-04a6-4a26-83ef-2bef4f2c5dcd |
| Verdict: | Malicious activity |
| Analysis date: | January 27, 2024, 20:51:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 93D16508432C3FF3512EB9DE584F48E6 |
| SHA1: | 6ED9FD4D190AFC6C5154730D85CF883FD3AD4D2E |
| SHA256: | BE5357F63B036DA79D198978CBC5B652EA02B1CCFCB1538352442CDC7F4D5549 |
| SSDEEP: | 98304:F7GowcdPyJC8JRlobIlEQBYIXwUOZkj0o14vZGcwhnVx/mp9814L/fKBUe3VBOUu:R/JiB |
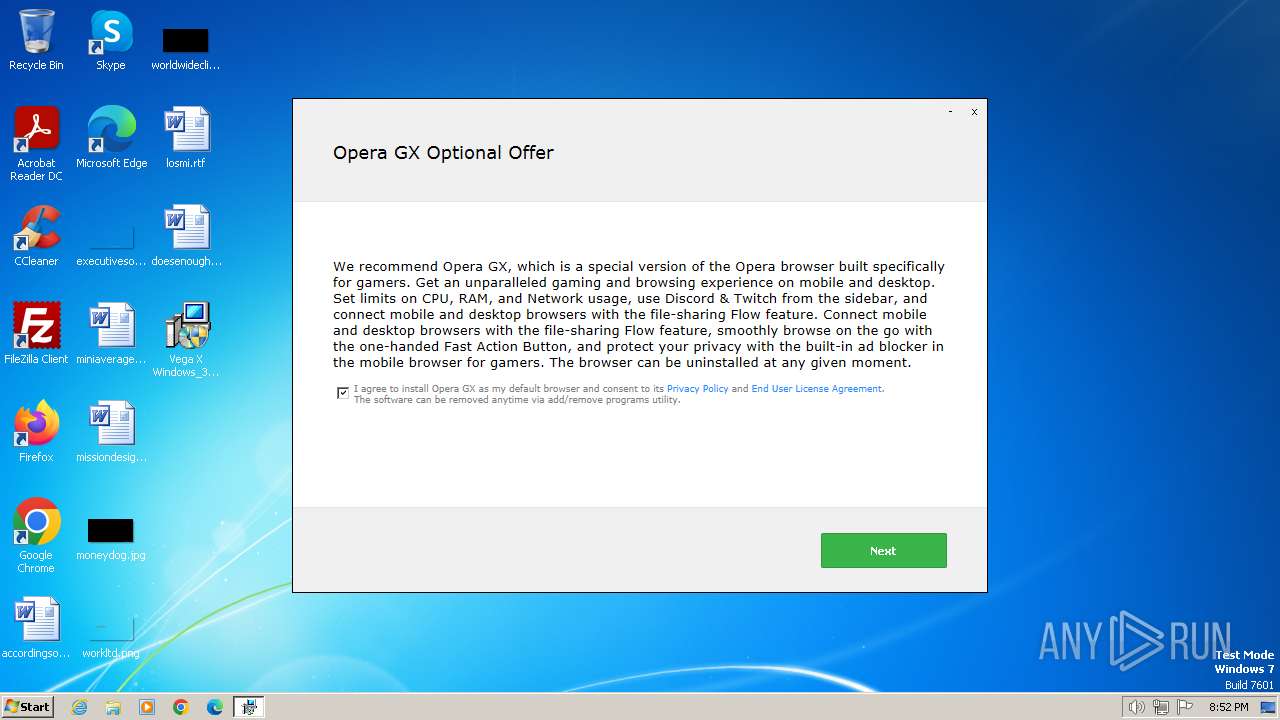
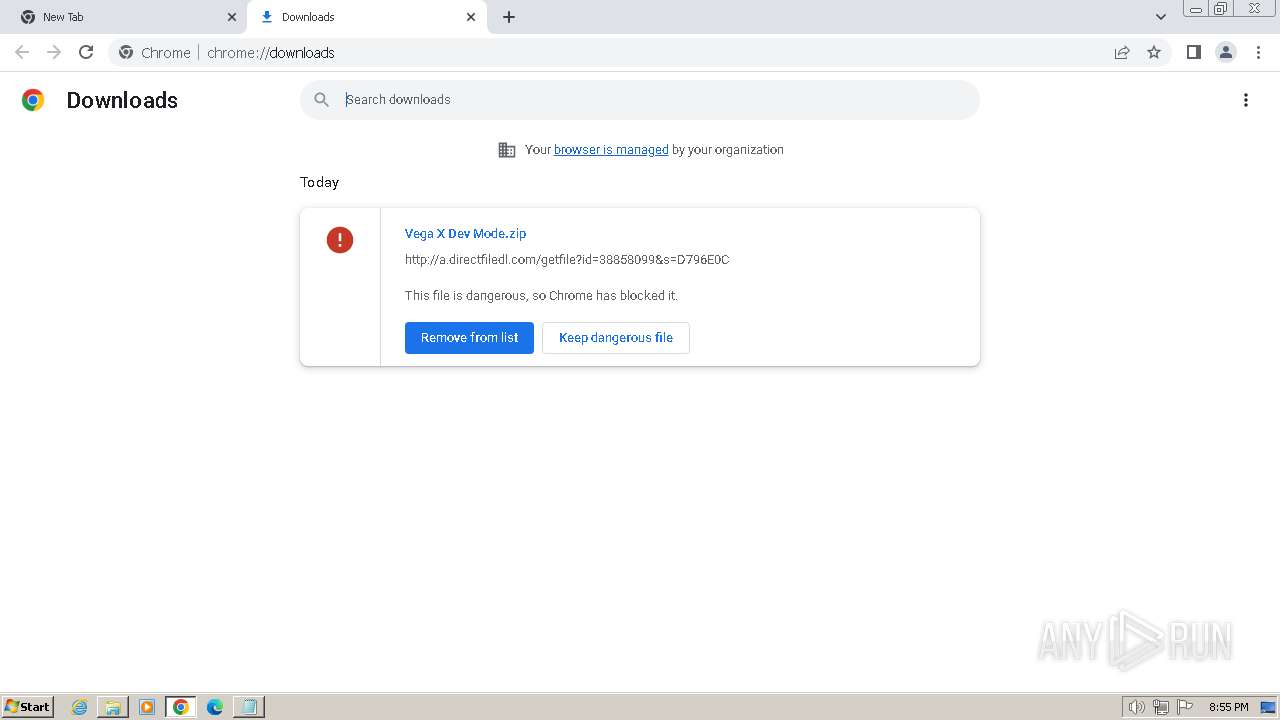
MALICIOUS
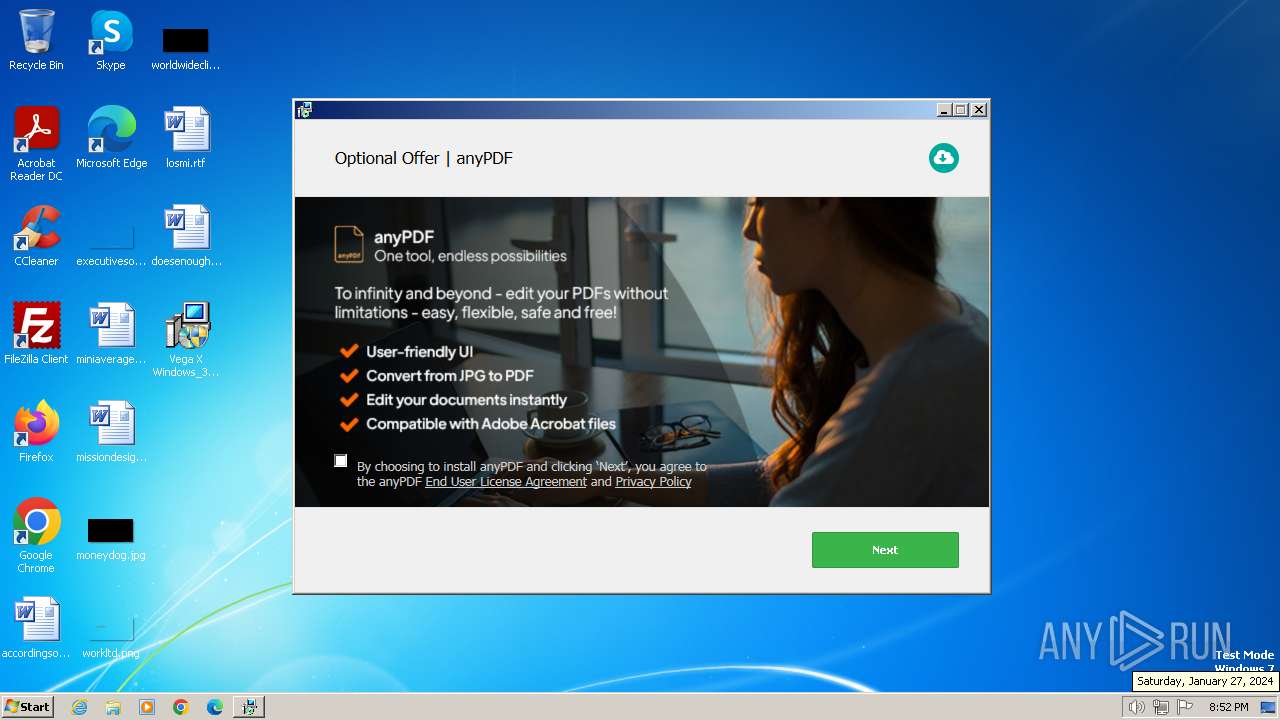
Drops the executable file immediately after the start
- Vega X Windows_38858099.exe (PID: 2260)
- setup38858099.exe (PID: 2420)
Actions looks like stealing of personal data
- setup38858099.exe (PID: 2420)
- OfferInstaller.exe (PID: 2528)
SUSPICIOUS
Reads settings of System Certificates
- Vega X Windows_38858099.exe (PID: 2260)
- OfferInstaller.exe (PID: 2528)
- setup38858099.exe (PID: 2420)
Reads the Internet Settings
- Vega X Windows_38858099.exe (PID: 2260)
- setup38858099.exe (PID: 2420)
- setup38858099.exe (PID: 968)
- cmd.exe (PID: 3732)
- OfferInstaller.exe (PID: 2528)
Reads security settings of Internet Explorer
- Vega X Windows_38858099.exe (PID: 2260)
- setup38858099.exe (PID: 2420)
Checks Windows Trust Settings
- Vega X Windows_38858099.exe (PID: 2260)
- setup38858099.exe (PID: 2420)
Executable content was dropped or overwritten
- Vega X Windows_38858099.exe (PID: 2260)
- setup38858099.exe (PID: 2420)
Process drops legitimate windows executable
- setup38858099.exe (PID: 2420)
The process drops C-runtime libraries
- setup38858099.exe (PID: 2420)
The process creates files with name similar to system file names
- setup38858099.exe (PID: 2420)
Reads the Windows owner or organization settings
- setup38858099.exe (PID: 2420)
- OfferInstaller.exe (PID: 2528)
Searches for installed software
- setup38858099.exe (PID: 2420)
Adds/modifies Windows certificates
- Vega X Windows_38858099.exe (PID: 2260)
- setup38858099.exe (PID: 2420)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 1376)
- cmd.exe (PID: 1492)
Get information on the list of running processes
- cmd.exe (PID: 1376)
- cmd.exe (PID: 1492)
Starts CMD.EXE for commands execution
- setup38858099.exe (PID: 2420)
- OfferInstaller.exe (PID: 2528)
Executing commands from a ".bat" file
- OfferInstaller.exe (PID: 2528)
- setup38858099.exe (PID: 2420)
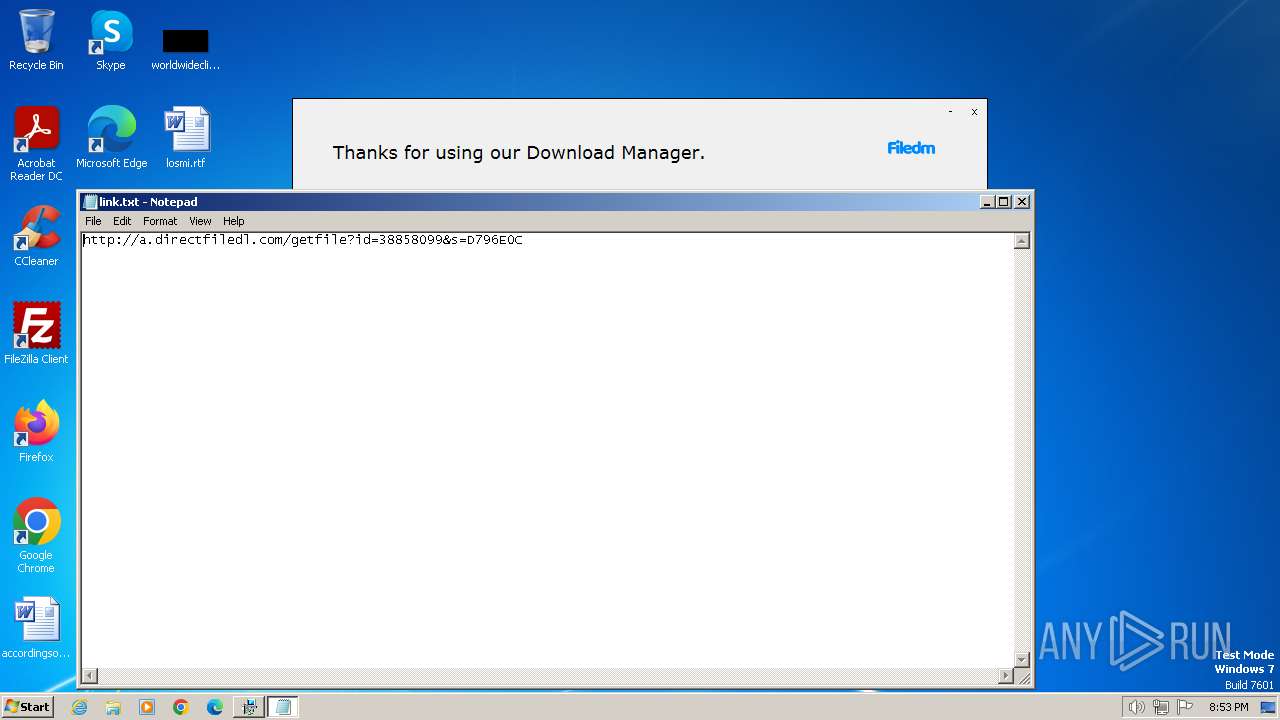
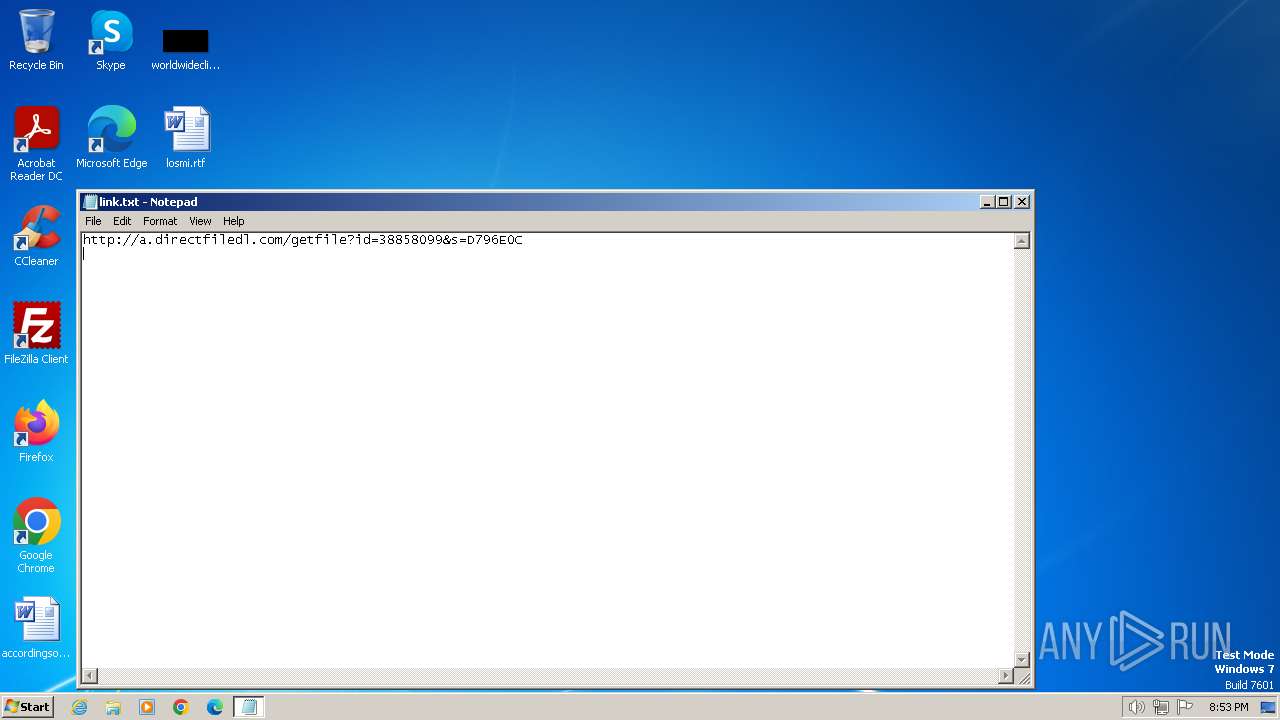
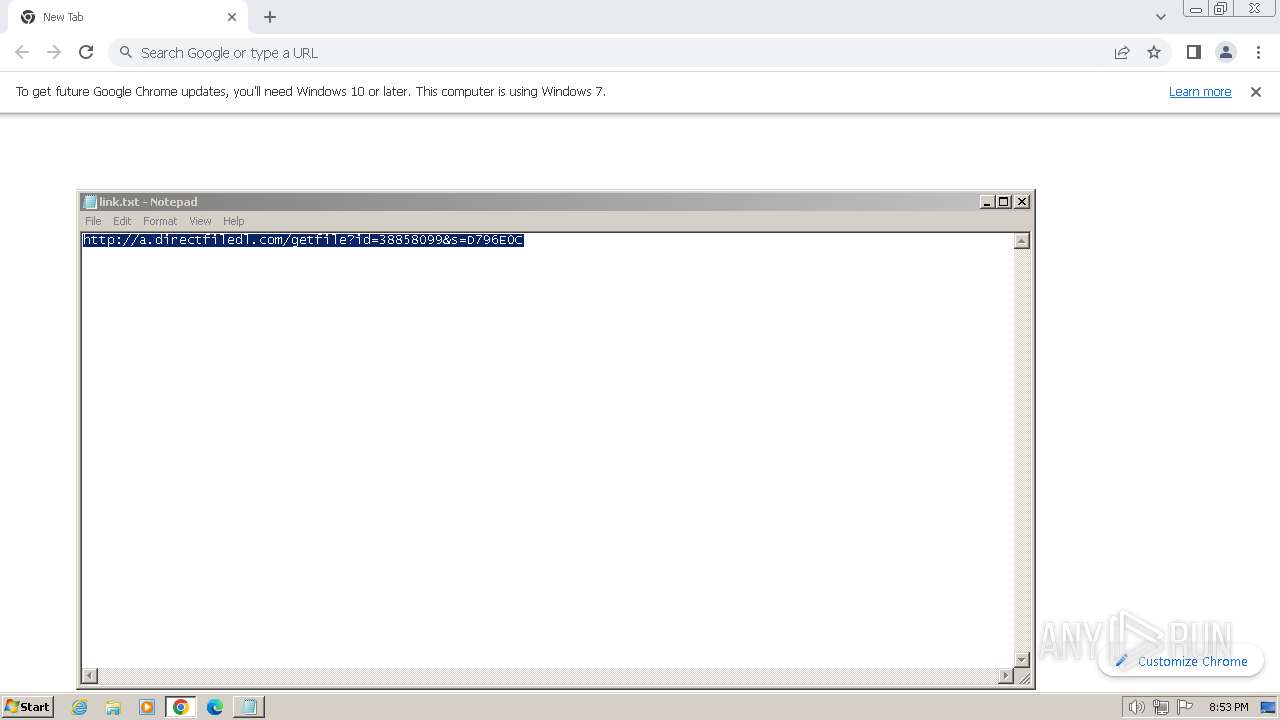
Start notepad (likely ransomware note)
- Vega X Windows_38858099.exe (PID: 2260)
INFO
Checks supported languages
- Vega X Windows_38858099.exe (PID: 2260)
- setup38858099.exe (PID: 2420)
- setup38858099.exe (PID: 968)
- OfferInstaller.exe (PID: 2528)
Reads the computer name
- Vega X Windows_38858099.exe (PID: 2260)
- setup38858099.exe (PID: 2420)
- setup38858099.exe (PID: 968)
- OfferInstaller.exe (PID: 2528)
Reads the machine GUID from the registry
- Vega X Windows_38858099.exe (PID: 2260)
- setup38858099.exe (PID: 2420)
- setup38858099.exe (PID: 968)
- OfferInstaller.exe (PID: 2528)
Creates files or folders in the user directory
- Vega X Windows_38858099.exe (PID: 2260)
- setup38858099.exe (PID: 2420)
- OfferInstaller.exe (PID: 2528)
Checks proxy server information
- Vega X Windows_38858099.exe (PID: 2260)
Create files in a temporary directory
- setup38858099.exe (PID: 2420)
- Vega X Windows_38858099.exe (PID: 2260)
- setup38858099.exe (PID: 968)
- OfferInstaller.exe (PID: 2528)
Reads product name
- setup38858099.exe (PID: 2420)
- OfferInstaller.exe (PID: 2528)
Reads Environment values
- setup38858099.exe (PID: 2420)
- OfferInstaller.exe (PID: 2528)
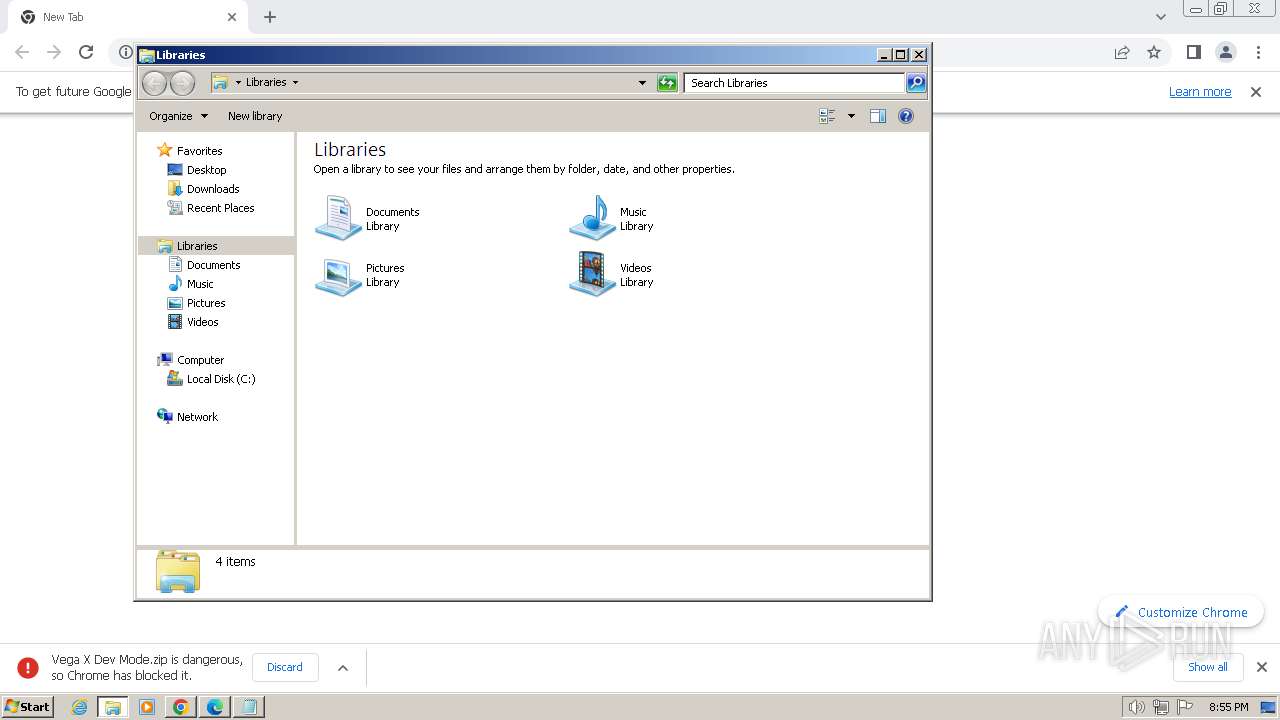
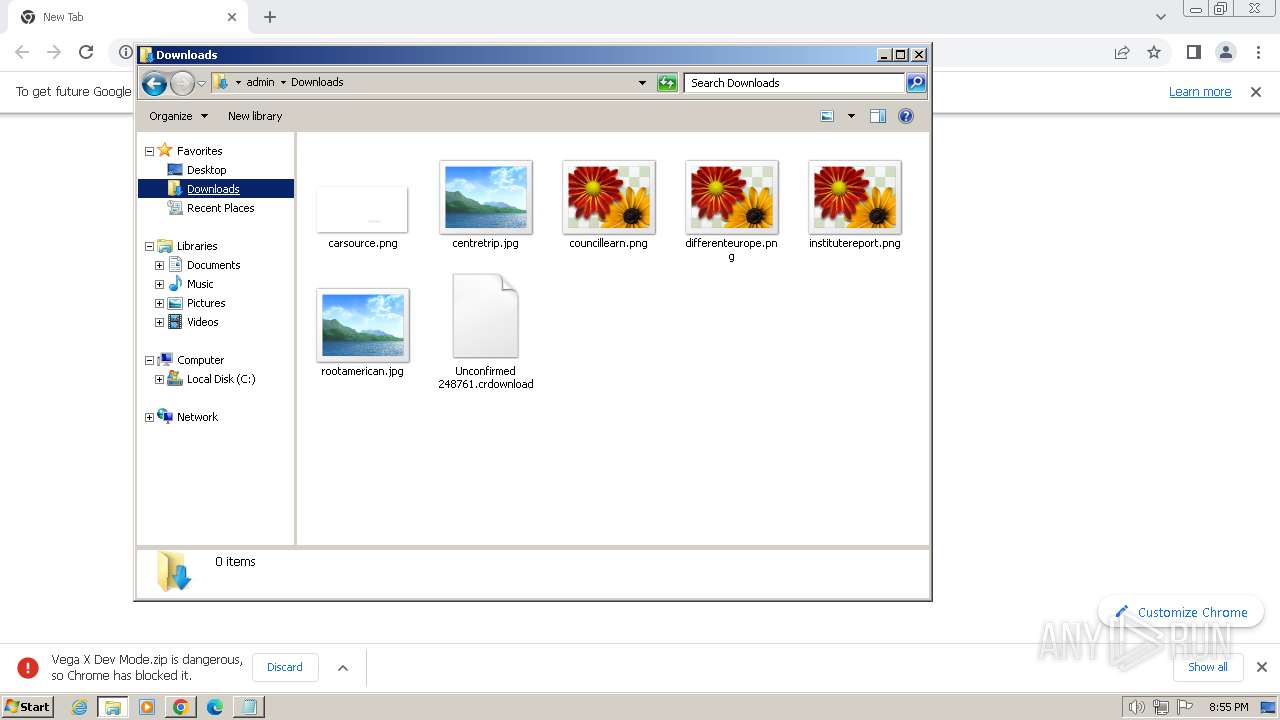
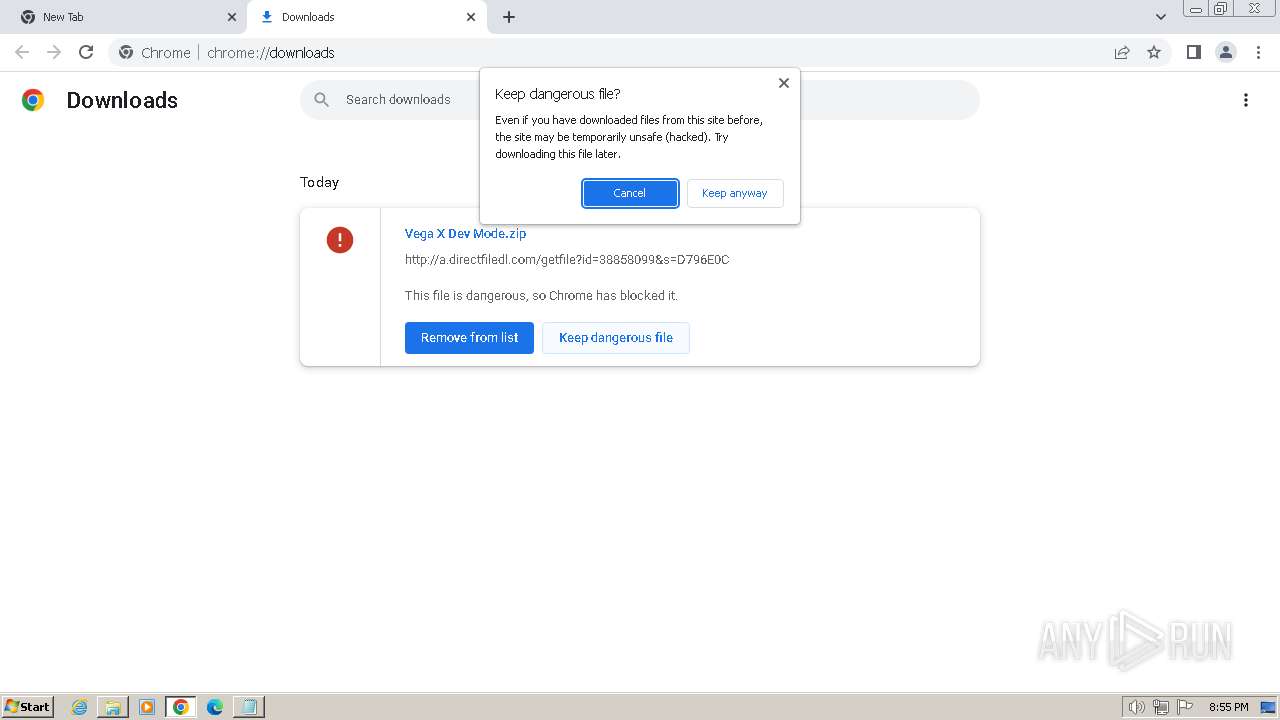
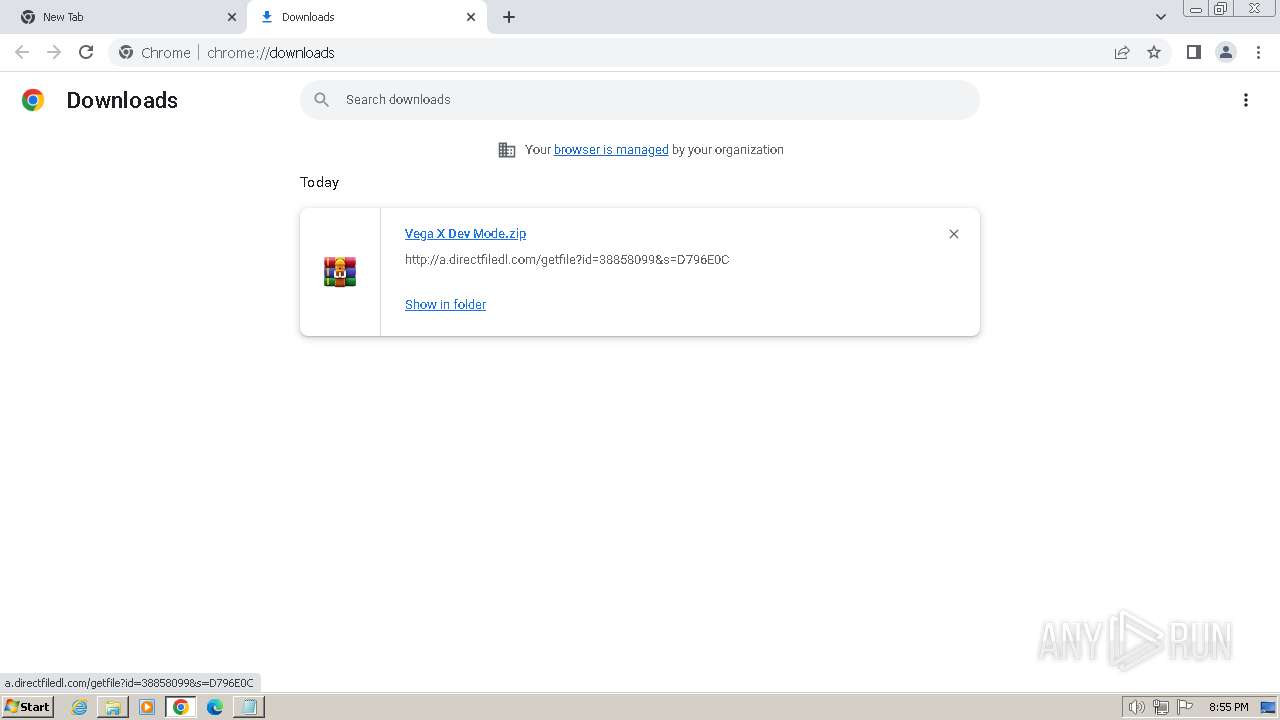
Manual execution by a user
- explorer.exe (PID: 3372)
- chrome.exe (PID: 2340)
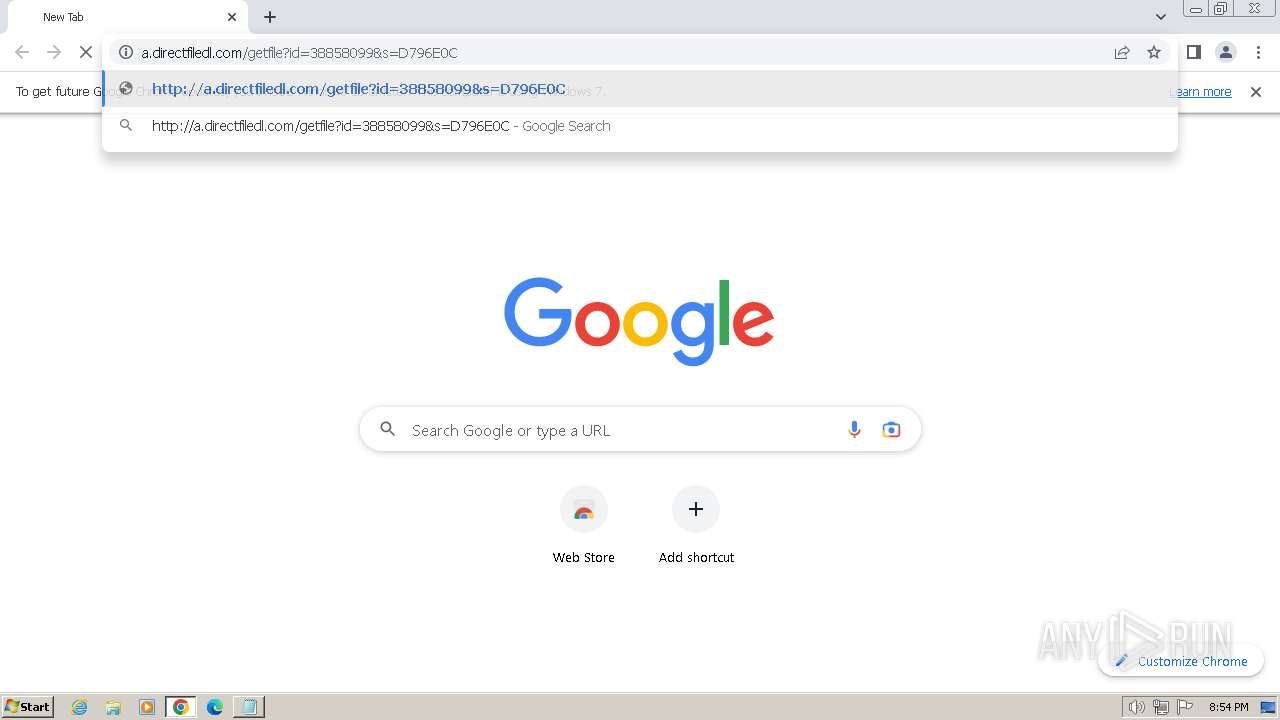
Application launched itself
- chrome.exe (PID: 2340)
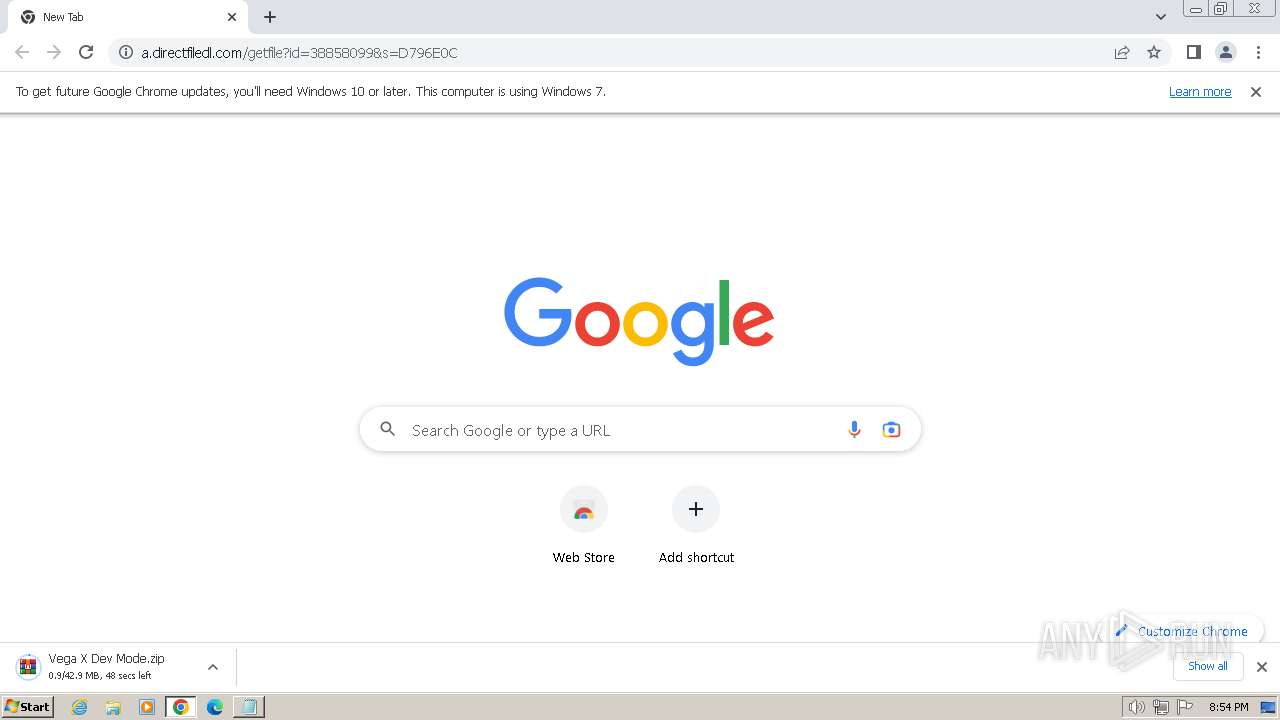
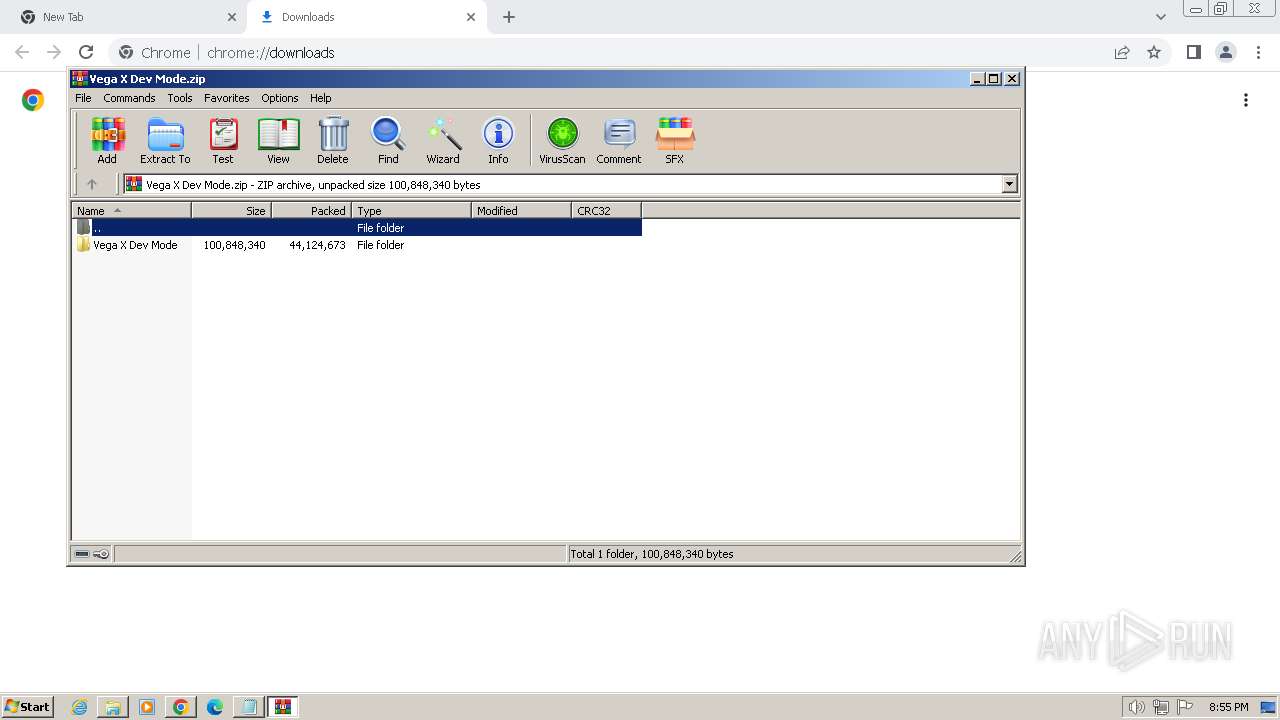
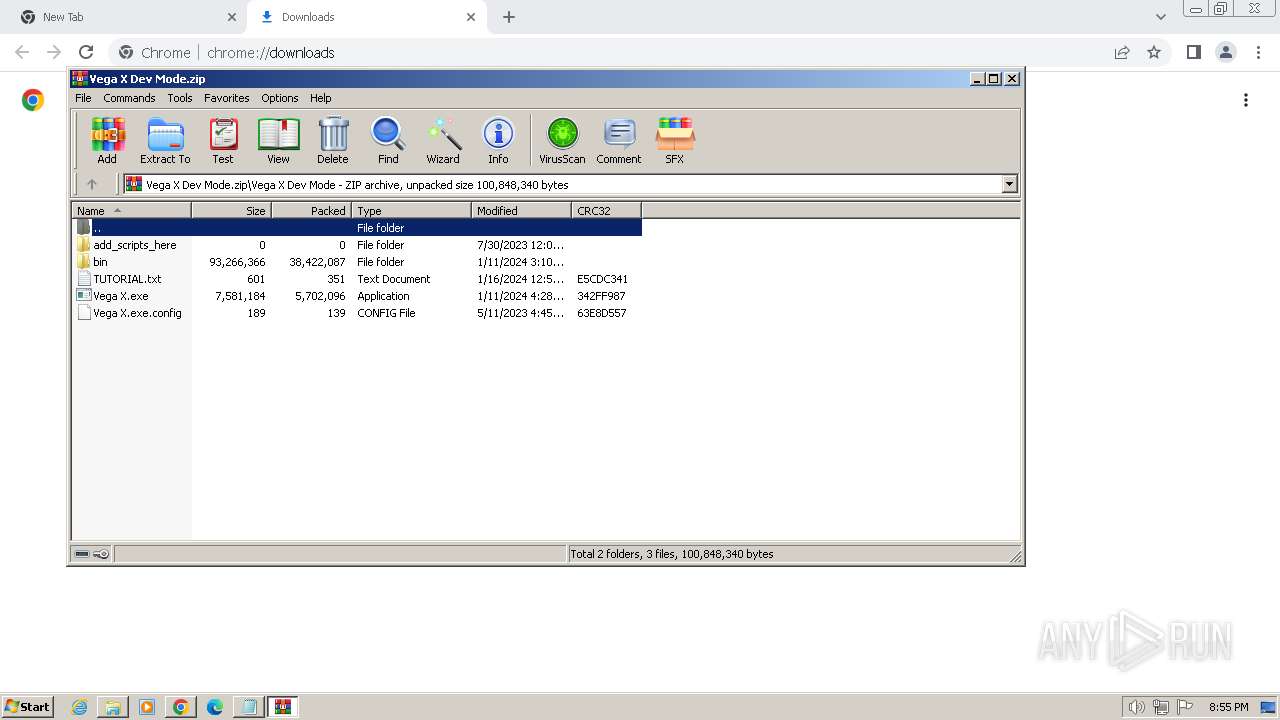
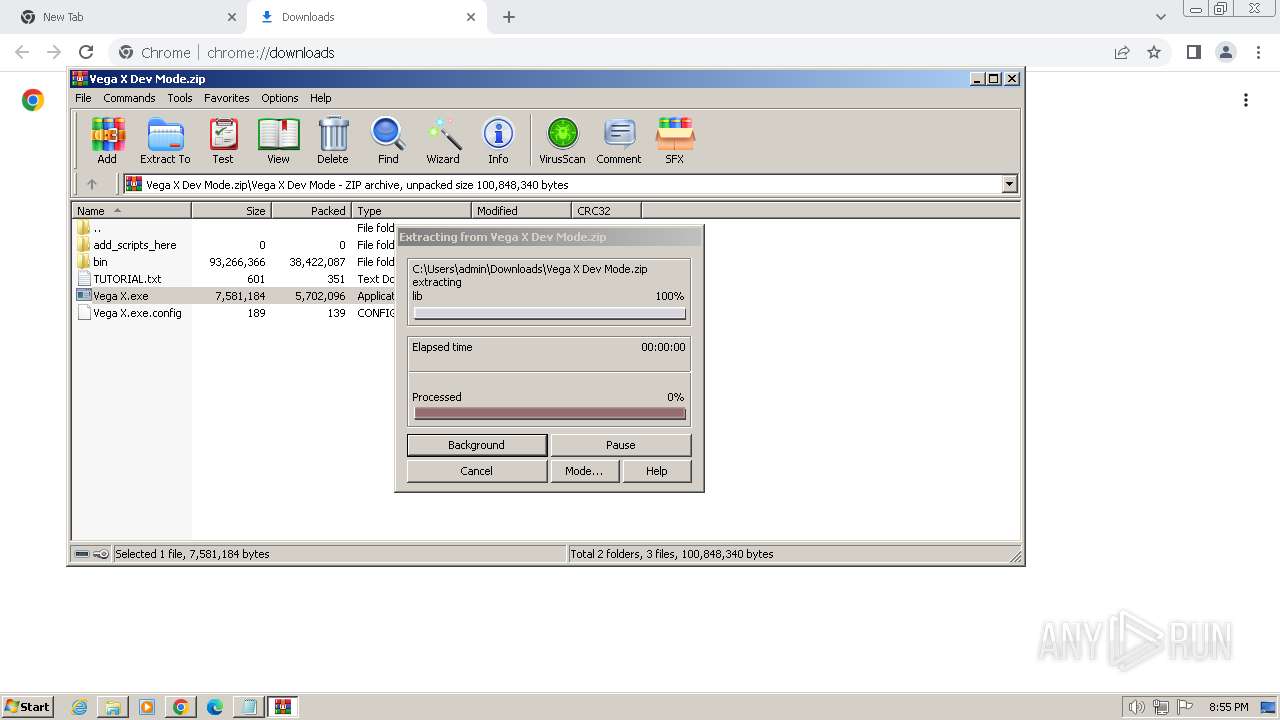
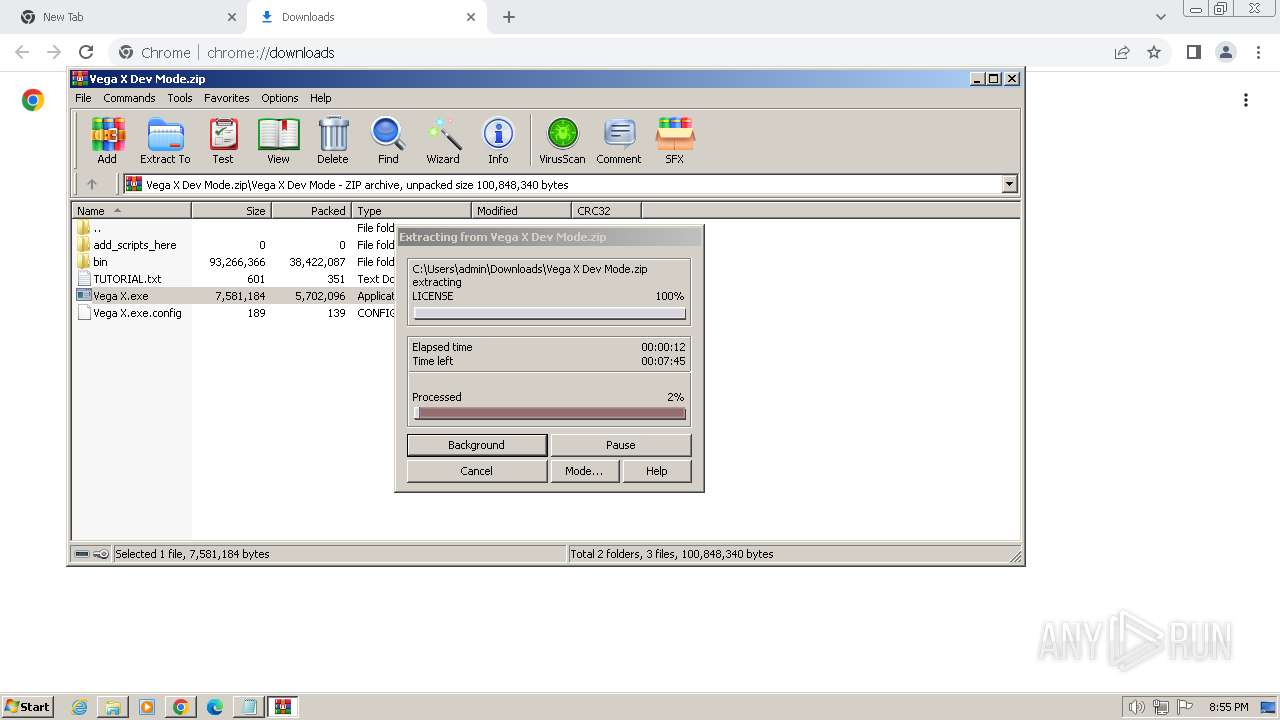
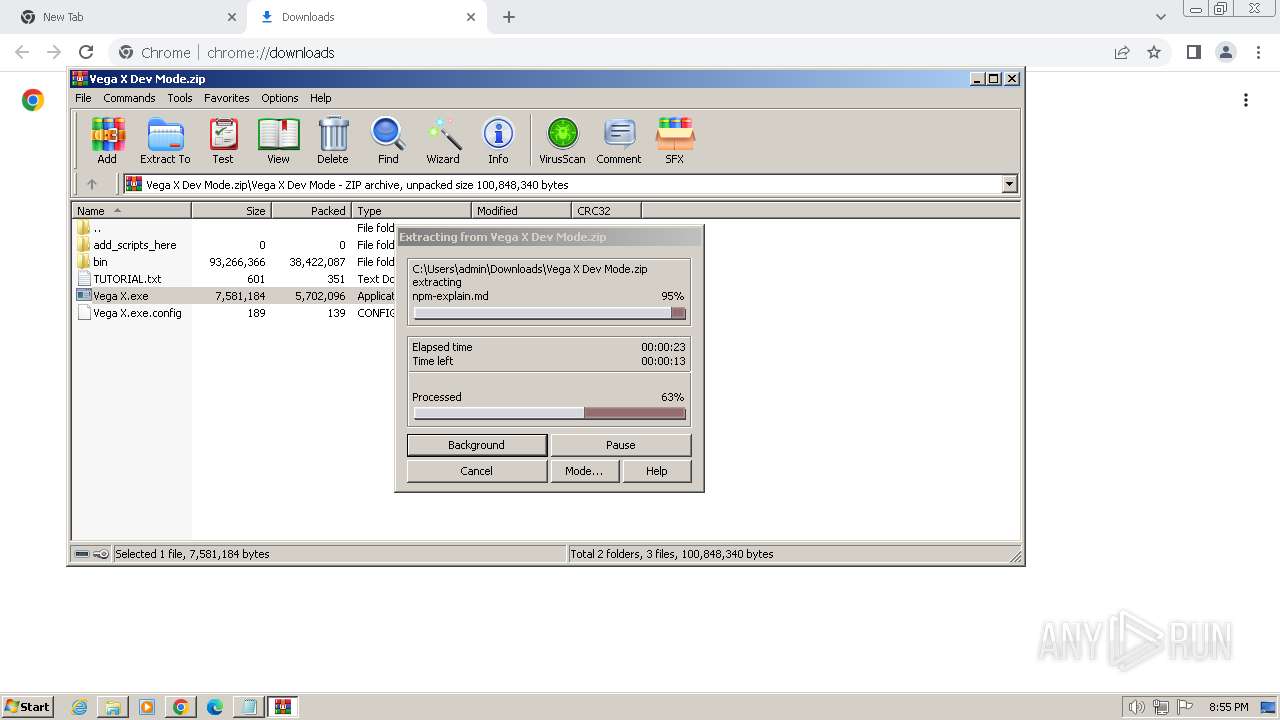
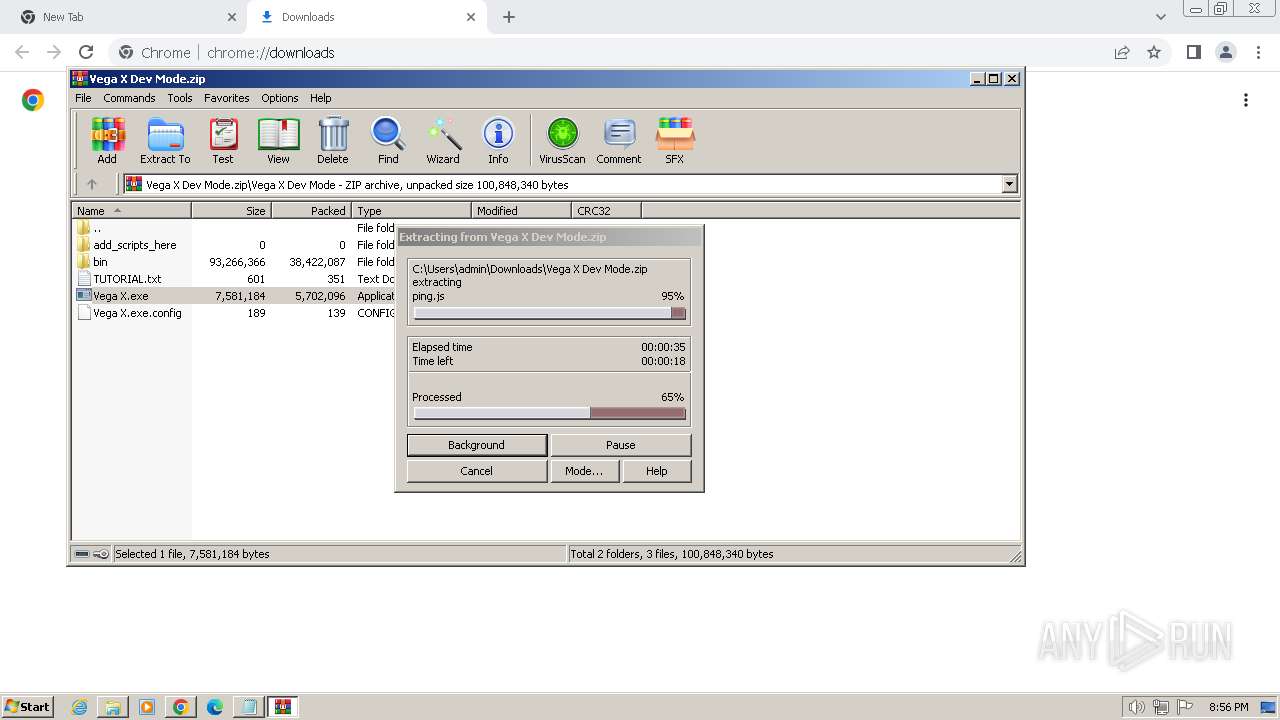
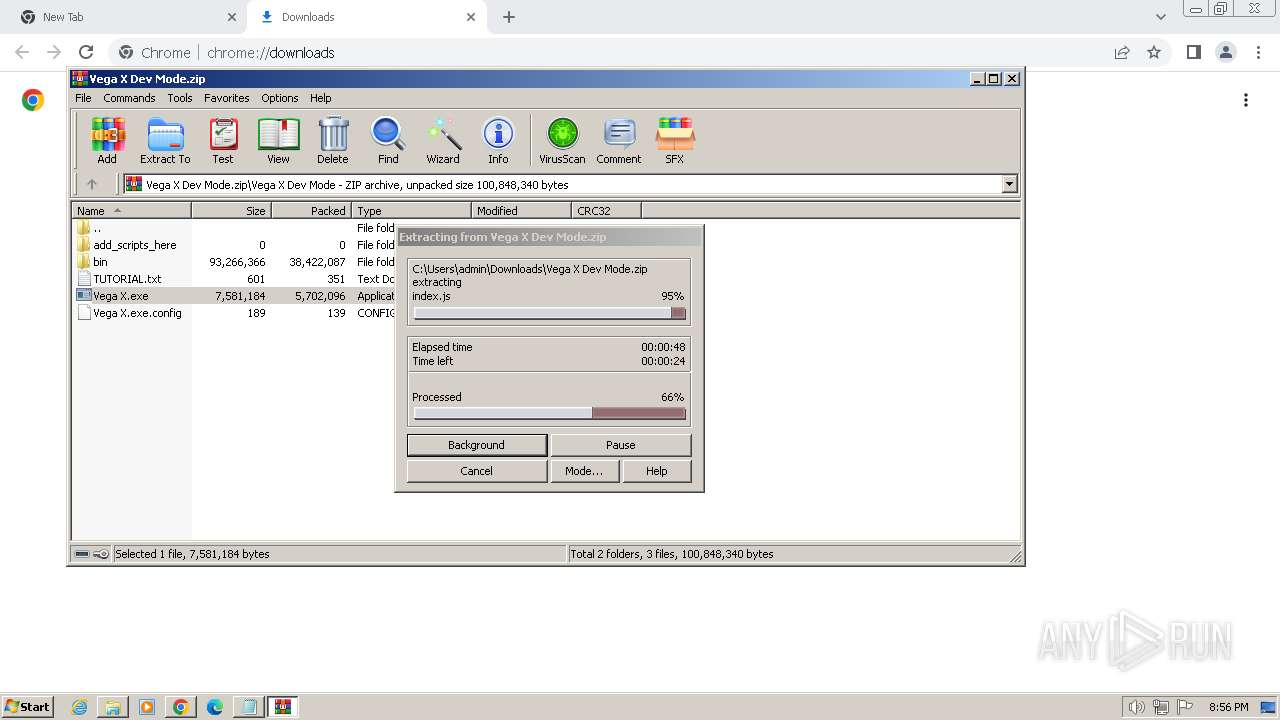
The process uses the downloaded file
- chrome.exe (PID: 1836)
- WinRAR.exe (PID: 1168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:11:21 20:16:16+01:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.22 |
| CodeSize: | 4345344 |
| InitializedDataSize: | 5646336 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x39649e |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileDescription: | Download Manager |
| FileVersion: | 1 |
| InternalName: | Download Manager |
| LegalCopyright: | Download Manager |
| OriginalFileName: | Download Manager |
| ProductName: | Download Manager |
| ProductVersion: | 1 |
Total processes
96
Monitored processes
41
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | find /I "2528" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1608 --field-trial-handle=1168,i,13942822727958254445,13995445146951474380,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1440 --field-trial-handle=1168,i,13942822727958254445,13995445146951474380,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 968 | C:\Users\admin\AppData\Local\setup38858099.exe hready | C:\Users\admin\AppData\Local\setup38858099.exe | — | Vega X Windows_38858099.exe | |||||||||||
User: admin Company: DT001 Integrity Level: HIGH Description: Software Installation Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1036 | "C:\Users\admin\Desktop\Vega X Windows_38858099.exe" | C:\Users\admin\Desktop\Vega X Windows_38858099.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Download Manager Exit code: 3221226540 Version: 1 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1084 --field-trial-handle=1168,i,13942822727958254445,13995445146951474380,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1044 | timeout 1 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1168 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Vega X Dev Mode.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1680 --field-trial-handle=1168,i,13942822727958254445,13995445146951474380,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1288 | tasklist /FI "PID eq 2528" /fo csv | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
30 544
Read events
30 295
Write events
248
Delete events
1
Modification events
| (PID) Process: | (2260) Vega X Windows_38858099.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2260) Vega X Windows_38858099.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2260) Vega X Windows_38858099.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2260) Vega X Windows_38858099.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2260) Vega X Windows_38858099.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2260) Vega X Windows_38858099.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2260) Vega X Windows_38858099.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2260) Vega X Windows_38858099.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2260) Vega X Windows_38858099.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2260) Vega X Windows_38858099.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EnterpriseCertificates\Root\Certificates\9F6134C5FA75E4FDDE631B232BE961D6D4B97DB6 |
| Operation: | write | Name: | Blob |
Value: 0300000001000000140000009F6134C5FA75E4FDDE631B232BE961D6D4B97DB6200000000100000047030000308203433082022BA00302010202147327B7C17D5AE708EF73F1F45A79D78B4E99A29F300D06092A864886F70D01010B05003031310B3009060355040613025553310F300D06035504080C06426F73746F6E3111300F060355040A0C084469676943657274301E170D3233303932393130353030335A170D3339303530383130353030335A3031310B3009060355040613025553310F300D06035504080C06426F73746F6E3111300F060355040A0C08446967694365727430820122300D06092A864886F70D01010105000382010F003082010A0282010100D91B7A55548F44F3E97C493153B75B055695736B184640D7335A2E6218083B5A1BEE2695209350E57A3EB76FBC604CB3B250DF3D9D0C560D1FBDFE30108D233A3C555100BE1A3F8E543C0B253E06E91B6D5F9CB3A093009BC8B4D3A0EB19DB59E56DA7E3D637847970D6C2AEB4A1FCF3896A7C080FE68759BAA62E6AAA8B7C7CBDA176DDC72F8D259A16D3469E31F19D2959904611D730D7D26FCFED789A0C49698FDFABF3F6727D08C61A073BB11E85C96486D49B0E0D38364C008A5EB964F8813C5DF004F9E76D2F8DB90702D800032674959BF0DF823785419101CEA928A10ACBAE7E48FE19202F3CB7BCF416476D17CB64C5570FCED443BD75D9F2C632FF0203010001A3533051301D0603551D0E041604145D6CA352CEFC713CBBC5E21F663C3639FD19D4D7301F0603551D230418301680145D6CA352CEFC713CBBC5E21F663C3639FD19D4D7300F0603551D130101FF040530030101FF300D06092A864886F70D01010B05000382010100AF2218E4CA18144728FCC76EA14958061522FD4A018BED1A4BFCC5CCE70BC6AE9DF7D3795C9A010D53628E2B6E7C10D6B07E53546235A5EE480E5A434E312154BF1E39AAC27D2C18D4F41CBBECFE4538CEF93EF62C17D187A7F720F4A9478410D09620C9F8B293B5786A5440BC0743B7B7753CF66FBA498B7E083BC267597238DC031B9BB131F997D9B8164AAED0D6E328420E53E1969DA6CD035078179677A7177BB2BF9C87CF592910CD380E8501B92040A39469C782BA383BEAE498C060FCC7C429BC10B7B6B7A0659C9BE03DC13DB46C638CF5E3B22A303726906DC8DD91C64501EBFC282A3A497EC430CACC066EE4BF9C5C8F2F2A05D0C1921A9E3E85E3 | |||
Executable files
35
Suspicious files
278
Text files
1 557
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2260 | Vega X Windows_38858099.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\3465EF07B9A6512425B2408FA7DBF4E5_F38ABF5BFFF4E687C6F66BAEAE5ADE1C | binary | |
MD5:02A593519B104E2F5512E04C85E4FFDD | SHA256:DBE76D7B2A081076D8BAC9B51F92078E71AA273EB44CB15046CA506EB49C2391 | |||
| 2260 | Vega X Windows_38858099.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_45E3C223BCF135987E4038FB6B0DBA13 | binary | |
MD5:0D5E4D21D1D8B5EBD79A6BCA0066BF32 | SHA256:92BBA577E55F63338B8D5606E33BF5B4C7733930D59E73B1DDDB074C0666A39B | |||
| 2260 | Vega X Windows_38858099.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_45E3C223BCF135987E4038FB6B0DBA13 | binary | |
MD5:037AE8164352CA91E80AD33054D1906D | SHA256:07C018EB07002663D5248DAA8A65EAF587955E3DB45735E7E3AC9CB13D7D664E | |||
| 2420 | setup38858099.exe | C:\Users\admin\AppData\Local\Temp\ec05d89197b949eb6957b79472e8723d\ServiceHide.dll | executable | |
MD5:72990C7E32EE6C811EA3D2EA64523234 | SHA256:E77E0B4F2762F76A3EAAADF5A3138A35EC06ECE80EDC4B3396DE7A601F8DA1B3 | |||
| 2260 | Vega X Windows_38858099.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\3465EF07B9A6512425B2408FA7DBF4E5_F38ABF5BFFF4E687C6F66BAEAE5ADE1C | binary | |
MD5:445A75ACAF601797124A28D9EF7F6586 | SHA256:CFB8857F8F916AFD056045ADFF46F157AD8C0990056A7940B694B5EFAD1744FF | |||
| 2260 | Vega X Windows_38858099.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:428FE3FE7E538D6A248E7A41EDE8DA84 | SHA256:513A1E99E25E99E65FA76F96CFEDB39327B07582944C81E371B8FF0E5D2E260C | |||
| 2260 | Vega X Windows_38858099.exe | C:\Users\admin\AppData\Local\setup38858099.exe | executable | |
MD5:29D3A70CEC060614E1691E64162A6C1E | SHA256:CC70B093A19610E9752794D757AEC9EF07CA862EA9267EC6F9CC92B2AA882C72 | |||
| 2260 | Vega X Windows_38858099.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\service[1].htm | text | |
MD5:5C765B87DCEBA7A15DD71C6EBF3E68A7 | SHA256:FF64098C17FF9EF9EB7945726B153FE60EF118823DD65456C431DA1EDEEA870C | |||
| 2260 | Vega X Windows_38858099.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:7C82CEAEEC0FEC80AD940B58A74C0617 | SHA256:7FF6D014F20CF1636DA1EA969B9B2B7373302A6EFB84560ED03081C0A61D4D89 | |||
| 2260 | Vega X Windows_38858099.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:5F4DB3481FB4F8DD774BF286990FF064 | SHA256:B5C18F4F5A1C48E56448E27911A9764258FBDACCE0B98F765CF7A70D297AC44F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
55
DNS requests
44
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2260 | Vega X Windows_38858099.exe | GET | 304 | 184.24.77.187:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d6a55f8027a20df0 | unknown | — | — | unknown |
2260 | Vega X Windows_38858099.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/s/gts1d4/tPVfSrt3g1k/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSMBFDqU0NJQdZdEGU3bkhj0FoRrQQUJeIYDrJXkZQq5dRdhpCD3lOzuJICEQDASJ2qLaCI5xAFjJiGxx93 | unknown | binary | 472 b | unknown |
2260 | Vega X Windows_38858099.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/s/gts1d4/tE2rewqz3dw/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSMBFDqU0NJQdZdEGU3bkhj0FoRrQQUJeIYDrJXkZQq5dRdhpCD3lOzuJICECdevec1BTW3CTOOyMl566o%3D | unknown | binary | 471 b | unknown |
2260 | Vega X Windows_38858099.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
2260 | Vega X Windows_38858099.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
2260 | Vega X Windows_38858099.exe | GET | 200 | 184.24.77.187:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?c1b3e067d8f7e683 | unknown | compressed | 65.2 Kb | unknown |
2260 | Vega X Windows_38858099.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIAjrICMzZli2TN25s%3D | unknown | binary | 724 b | unknown |
2260 | Vega X Windows_38858099.exe | GET | 200 | 69.192.161.44:80 | http://x2.c.lencr.org/ | unknown | binary | 300 b | unknown |
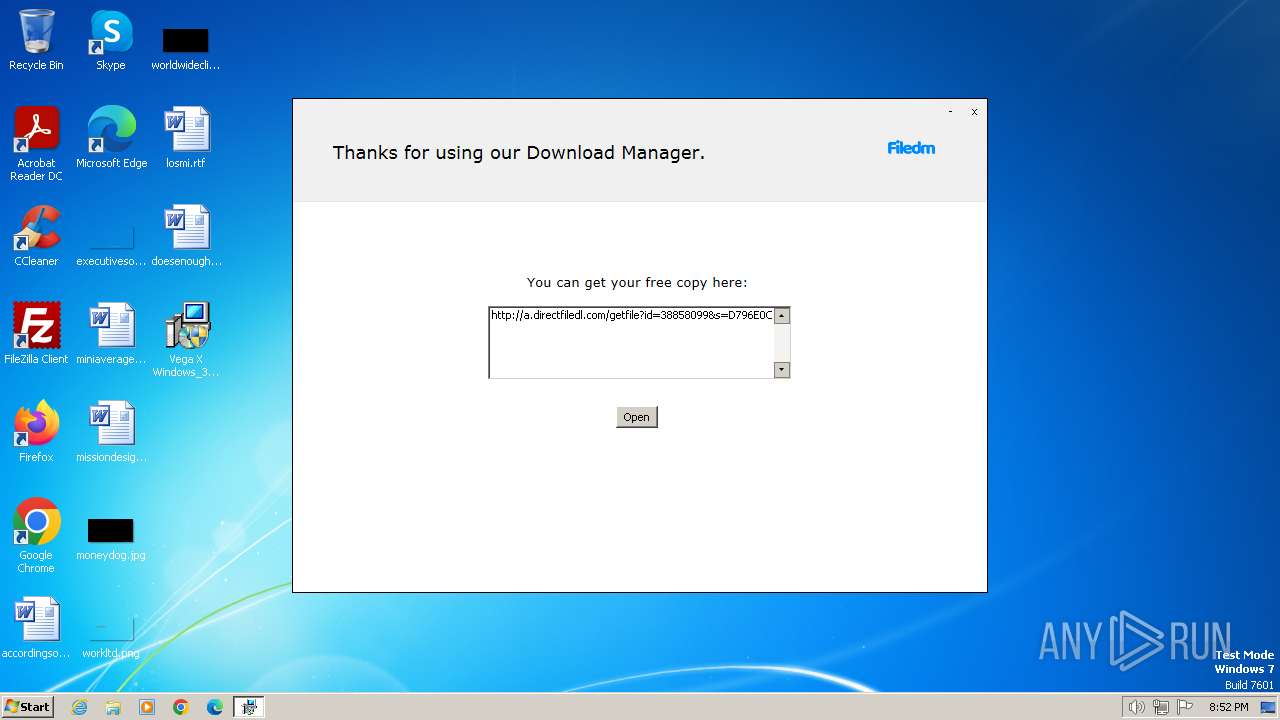
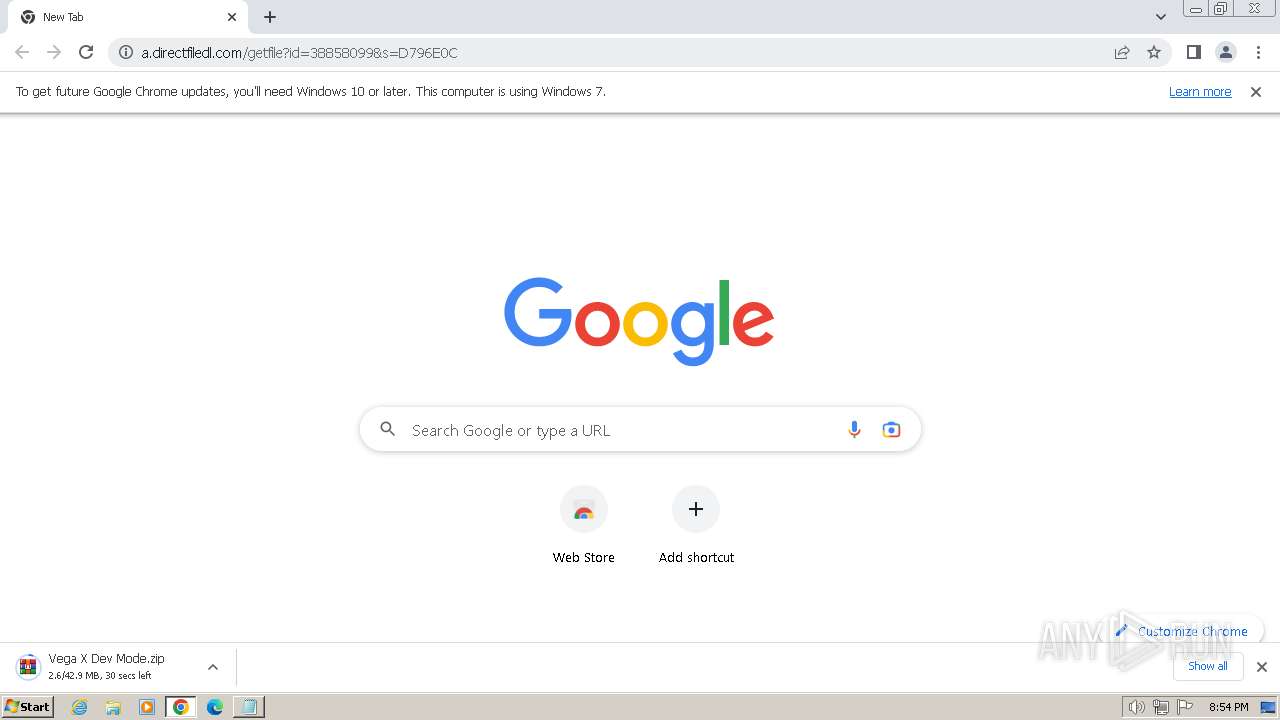
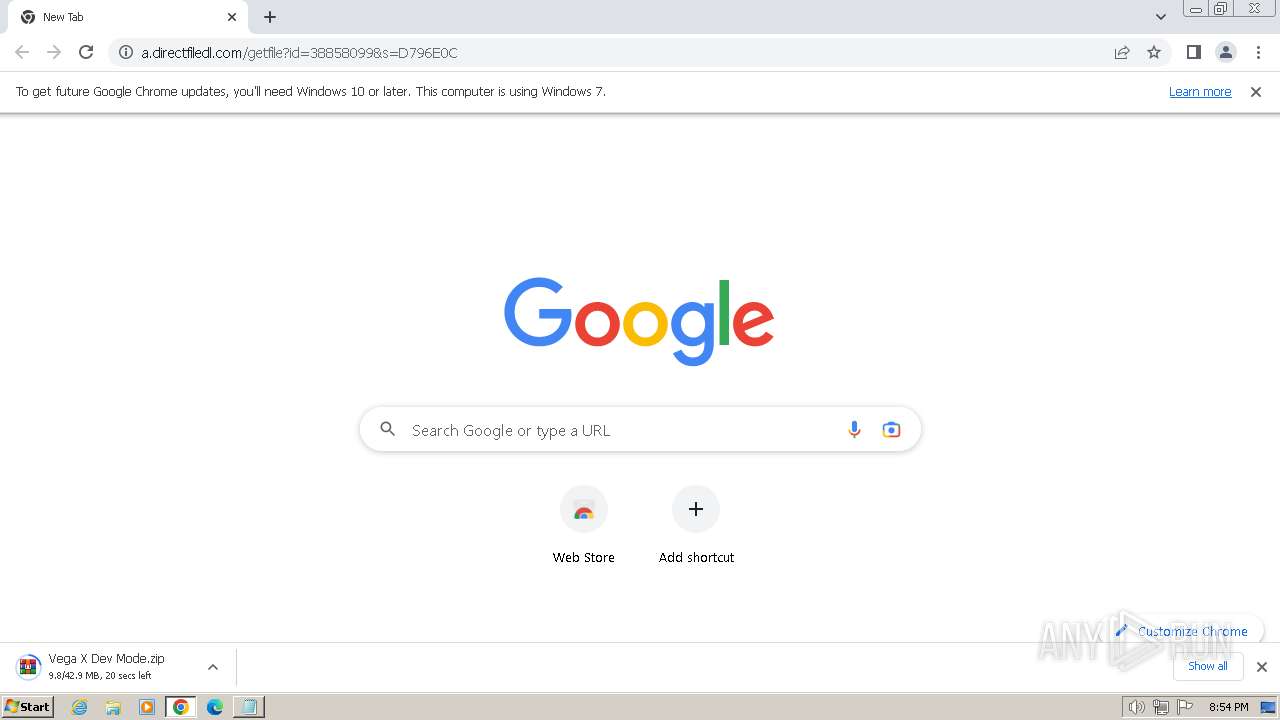
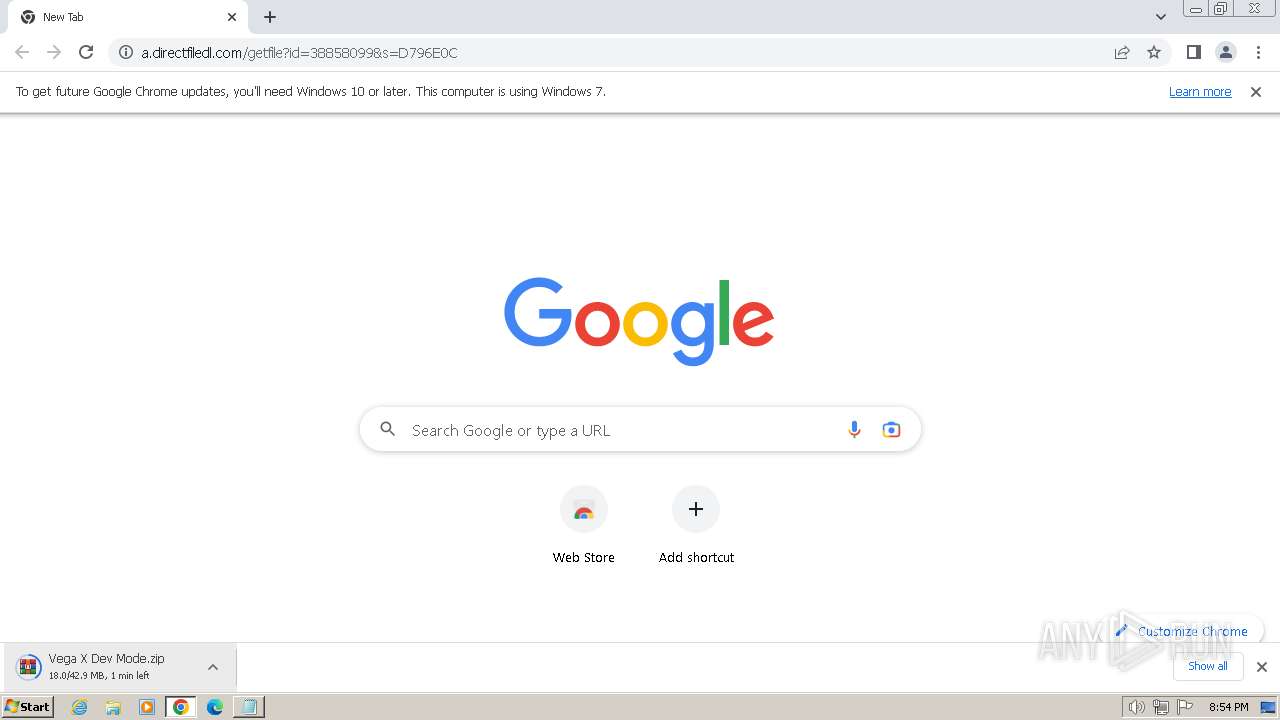
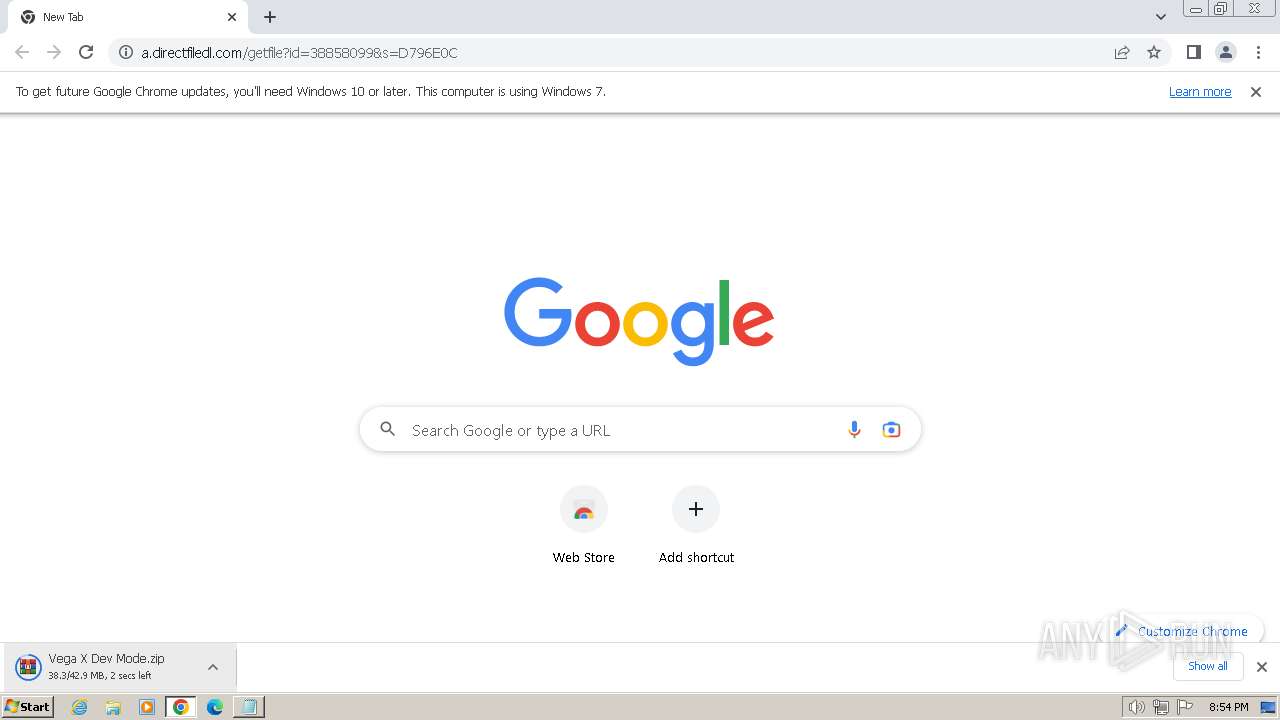
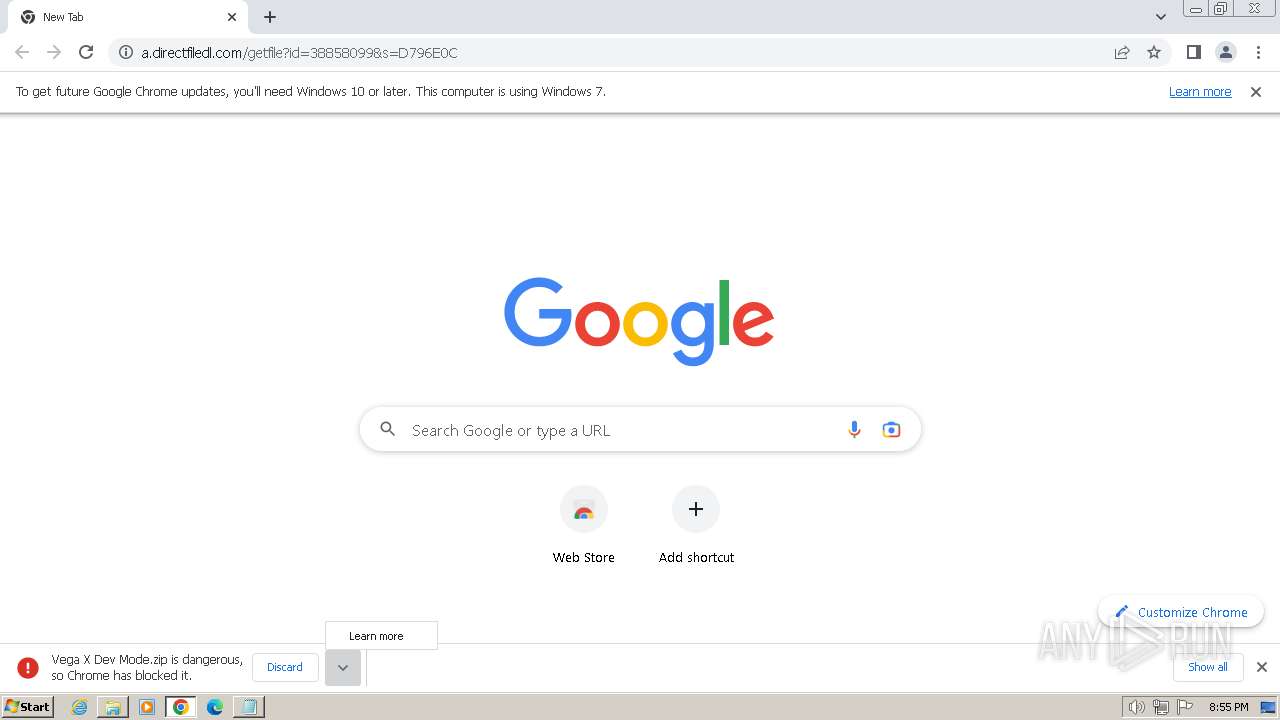
664 | chrome.exe | GET | 200 | 167.235.218.62:80 | http://a.directfiledl.com/getfile?id=38858099&s=D796E0C | unknown | compressed | 42.9 Mb | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2260 | Vega X Windows_38858099.exe | 35.190.60.70:443 | www.dlsft.com | GOOGLE | US | whitelisted |
2260 | Vega X Windows_38858099.exe | 184.24.77.187:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2260 | Vega X Windows_38858099.exe | 142.250.185.67:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
2420 | setup38858099.exe | 104.17.8.52:443 | flow.lavasoft.com | CLOUDFLARENET | — | shared |
2420 | setup38858099.exe | 104.18.68.73:443 | sos.adaware.com | CLOUDFLARENET | — | unknown |
2260 | Vega X Windows_38858099.exe | 188.114.96.3:443 | filedm.com | CLOUDFLARENET | NL | unknown |
2260 | Vega X Windows_38858099.exe | 69.192.161.44:80 | x1.c.lencr.org | AKAMAI-AS | DE | unknown |
2420 | setup38858099.exe | 18.245.86.104:443 | download.enigmasoftware.com | — | US | unknown |
2420 | setup38858099.exe | 169.150.247.39:443 | spyhunter-download-v2.b-cdn.net | — | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.dlsft.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.google.com |
| whitelisted |
flow.lavasoft.com |
| whitelisted |
sos.adaware.com |
| whitelisted |
dlsft.com |
| unknown |
filedm.com |
| malicious |
x1.c.lencr.org |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
Threats
6 ETPRO signatures available at the full report
Process | Message |
|---|---|
setup38858099.exe | file:resources/tis/TranslateOfferTemplate.tis(82) : warning :'async' does not contain any 'await'
|
setup38858099.exe | at sciter:init-script.tis
|
setup38858099.exe | |
setup38858099.exe | |
setup38858099.exe | Error: File not found - sciterwrapper:console.tis
|
setup38858099.exe | Error: File not found - sciterwrapper:console.tis
|
setup38858099.exe | at sciter:init-script.tis
|
setup38858099.exe | |
setup38858099.exe | |
setup38858099.exe | file:resources/tis/TranslateOfferTemplate.tis(82) : warning :'async' does not contain any 'await'
|