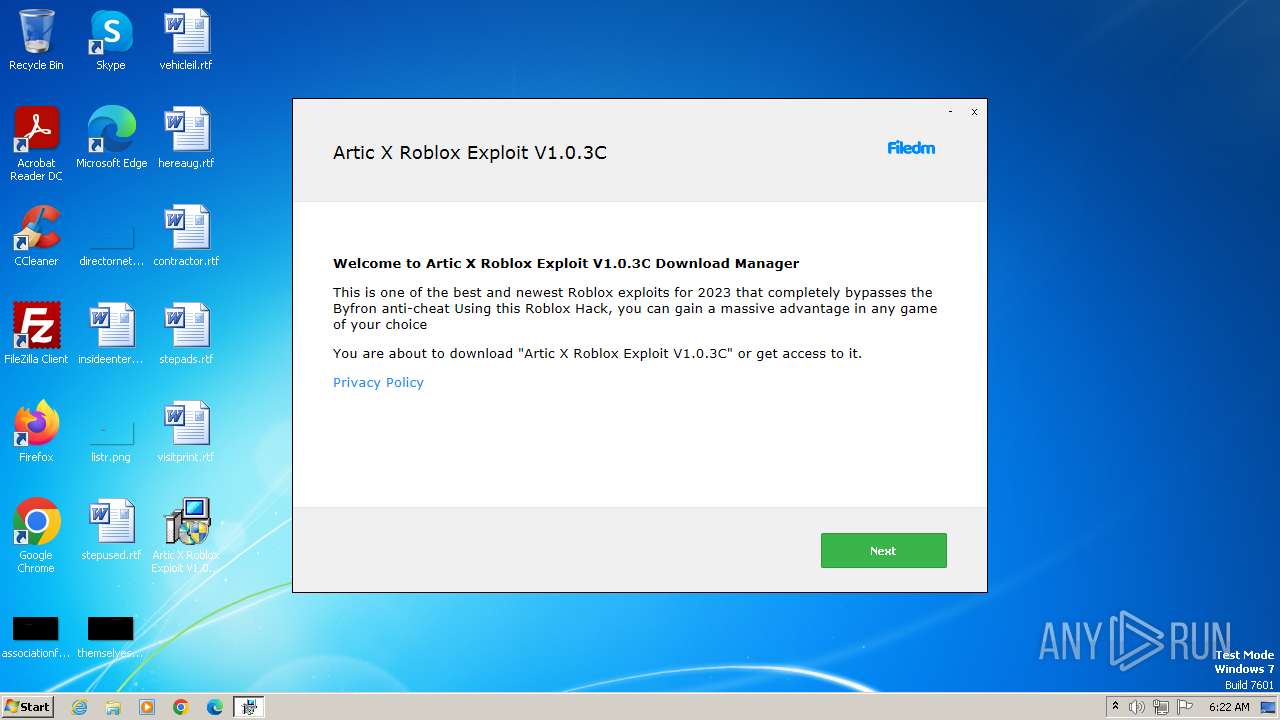
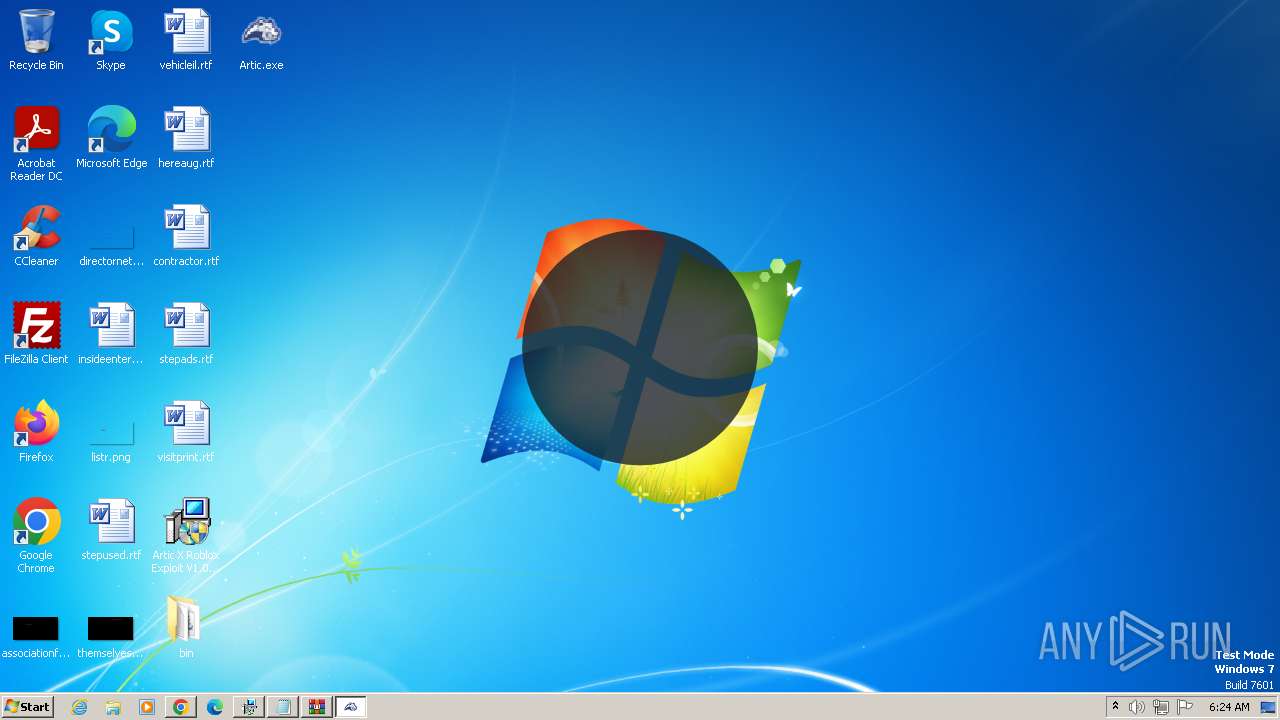
| File name: | Artic X Roblox Exploit V1.0.3C_62044477.exe |
| Full analysis: | https://app.any.run/tasks/b47fd7e9-e91d-48cb-9eda-66c6096832e1 |
| Verdict: | Malicious activity |
| Analysis date: | December 15, 2023, 06:22:26 |
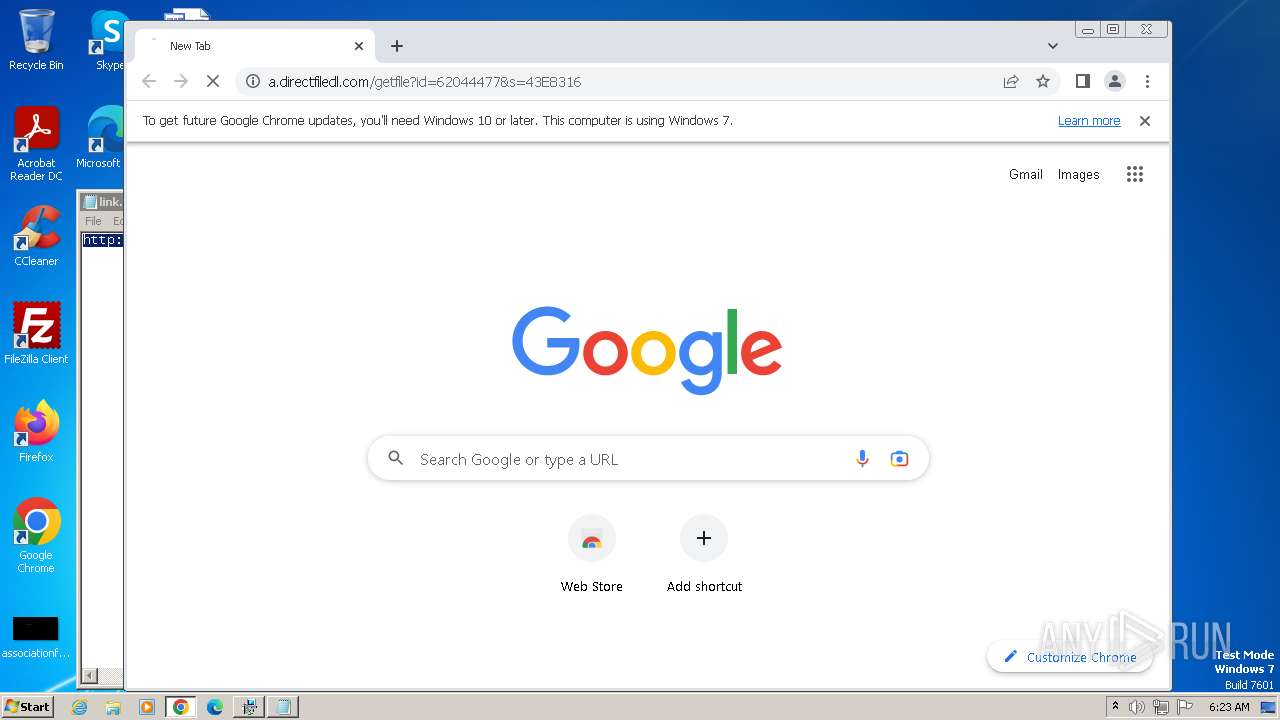
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 93D16508432C3FF3512EB9DE584F48E6 |
| SHA1: | 6ED9FD4D190AFC6C5154730D85CF883FD3AD4D2E |
| SHA256: | BE5357F63B036DA79D198978CBC5B652EA02B1CCFCB1538352442CDC7F4D5549 |
| SSDEEP: | 98304:F7GowcdPyJC8JRlobIlEQBYIXwUOZkj0o14vZGcwhnVx/mp9814L/fKBUe3VBOUu:R/JiB |
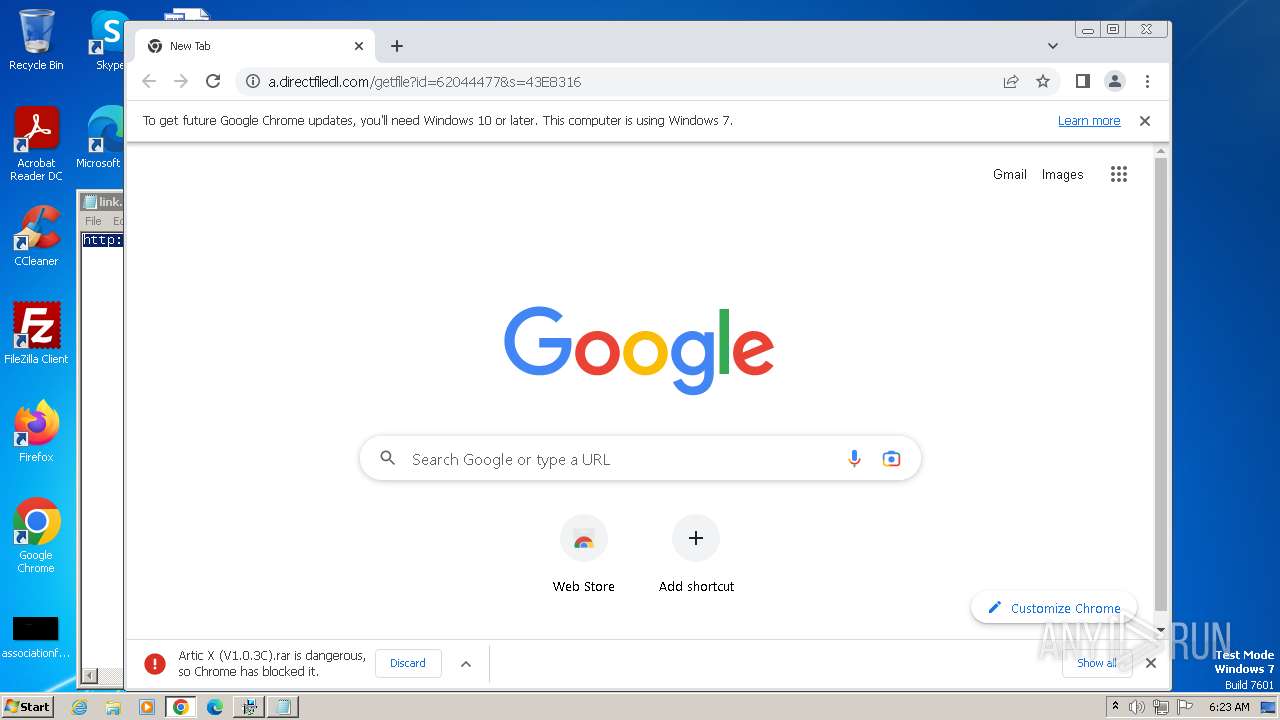
MALICIOUS
Drops the executable file immediately after the start
- setup62044477.exe (PID: 2764)
- Artic X Roblox Exploit V1.0.3C_62044477.exe (PID: 1840)
- setup62044477.exe (PID: 3864)
Actions looks like stealing of personal data
- setup62044477.exe (PID: 2764)
SUSPICIOUS
Reads the Internet Settings
- Artic X Roblox Exploit V1.0.3C_62044477.exe (PID: 1840)
- setup62044477.exe (PID: 2764)
- setup62044477.exe (PID: 3864)
- Artic.exe (PID: 1936)
Reads settings of System Certificates
- Artic X Roblox Exploit V1.0.3C_62044477.exe (PID: 1840)
- setup62044477.exe (PID: 2764)
Reads security settings of Internet Explorer
- Artic X Roblox Exploit V1.0.3C_62044477.exe (PID: 1840)
- setup62044477.exe (PID: 2764)
Reads the Windows owner or organization settings
- setup62044477.exe (PID: 2764)
Checks Windows Trust Settings
- Artic X Roblox Exploit V1.0.3C_62044477.exe (PID: 1840)
- setup62044477.exe (PID: 2764)
Process drops legitimate windows executable
- setup62044477.exe (PID: 2764)
- setup62044477.exe (PID: 3864)
- chrome.exe (PID: 4000)
The process drops C-runtime libraries
- setup62044477.exe (PID: 2764)
- setup62044477.exe (PID: 3864)
The process creates files with name similar to system file names
- setup62044477.exe (PID: 2764)
- setup62044477.exe (PID: 3864)
Executing commands from a ".bat" file
- setup62044477.exe (PID: 2764)
Starts CMD.EXE for commands execution
- setup62044477.exe (PID: 2764)
Searches for installed software
- setup62044477.exe (PID: 2764)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 3108)
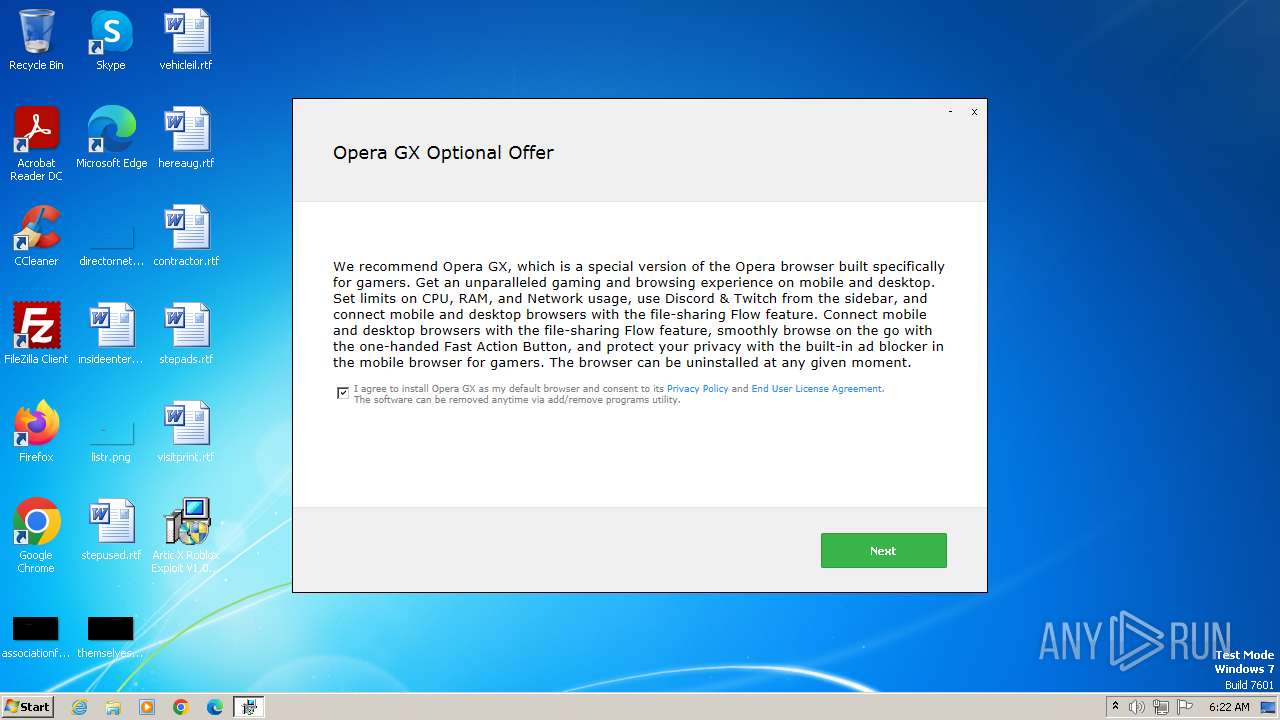
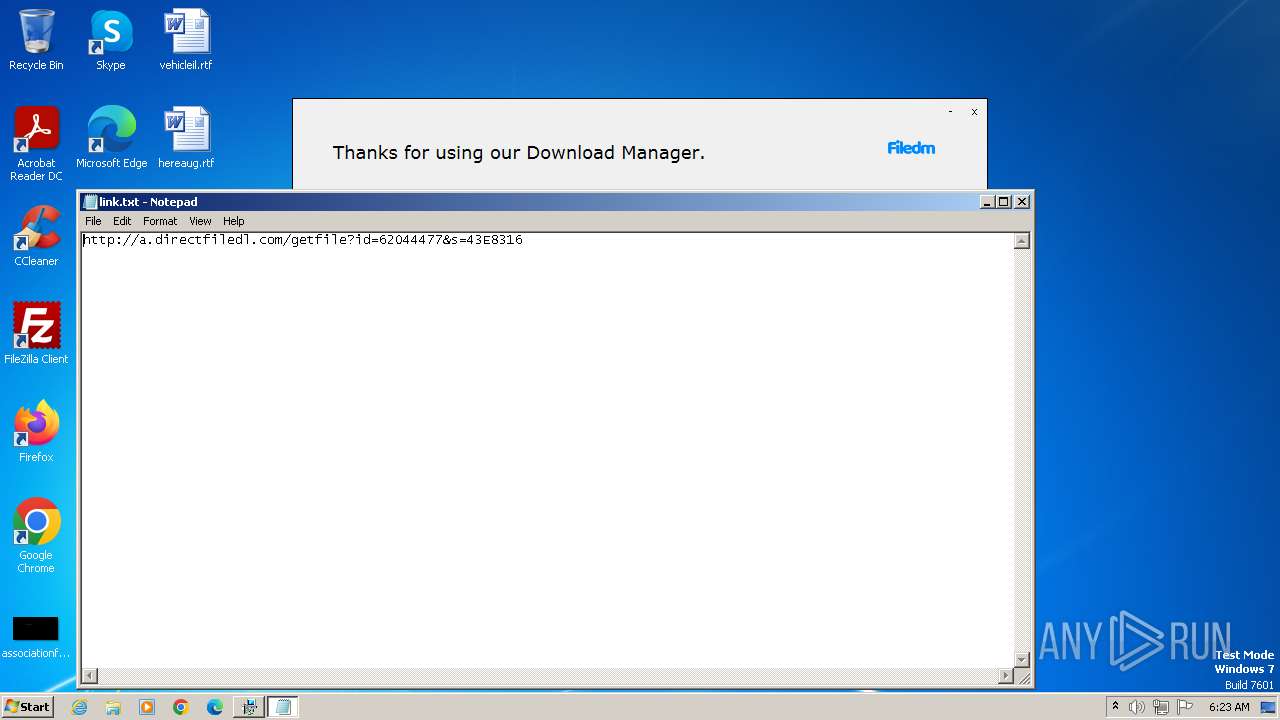
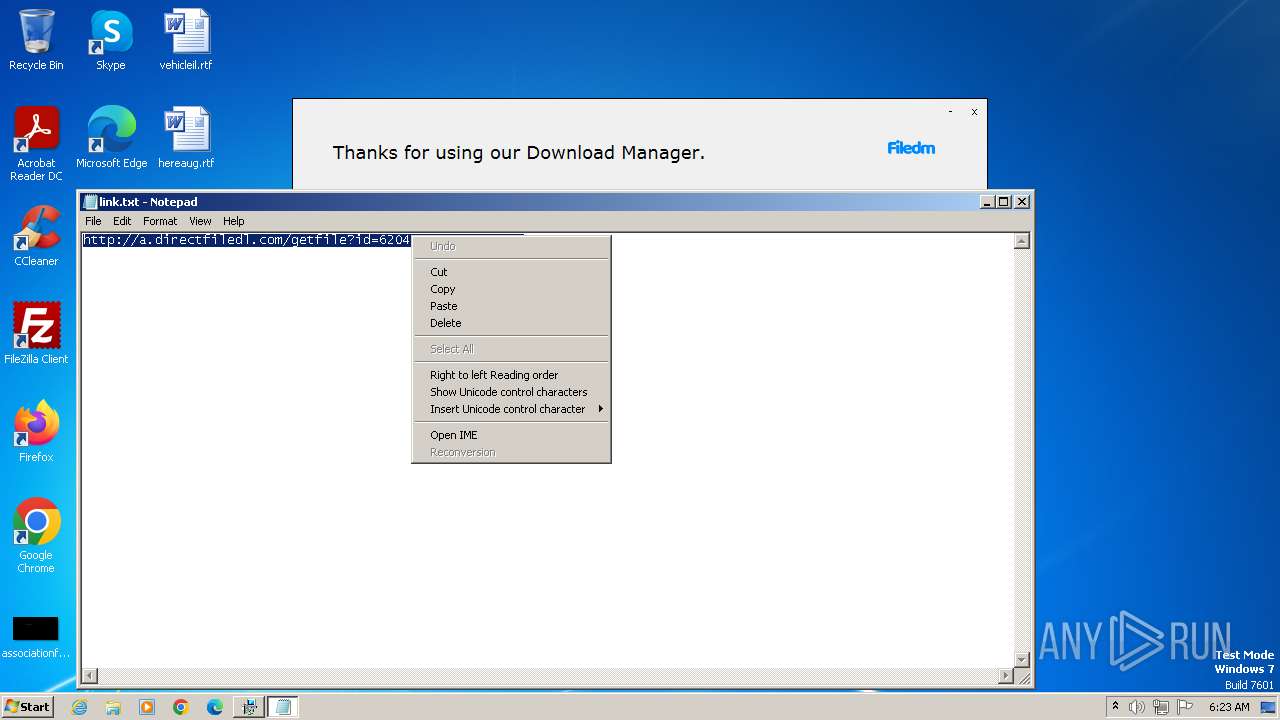
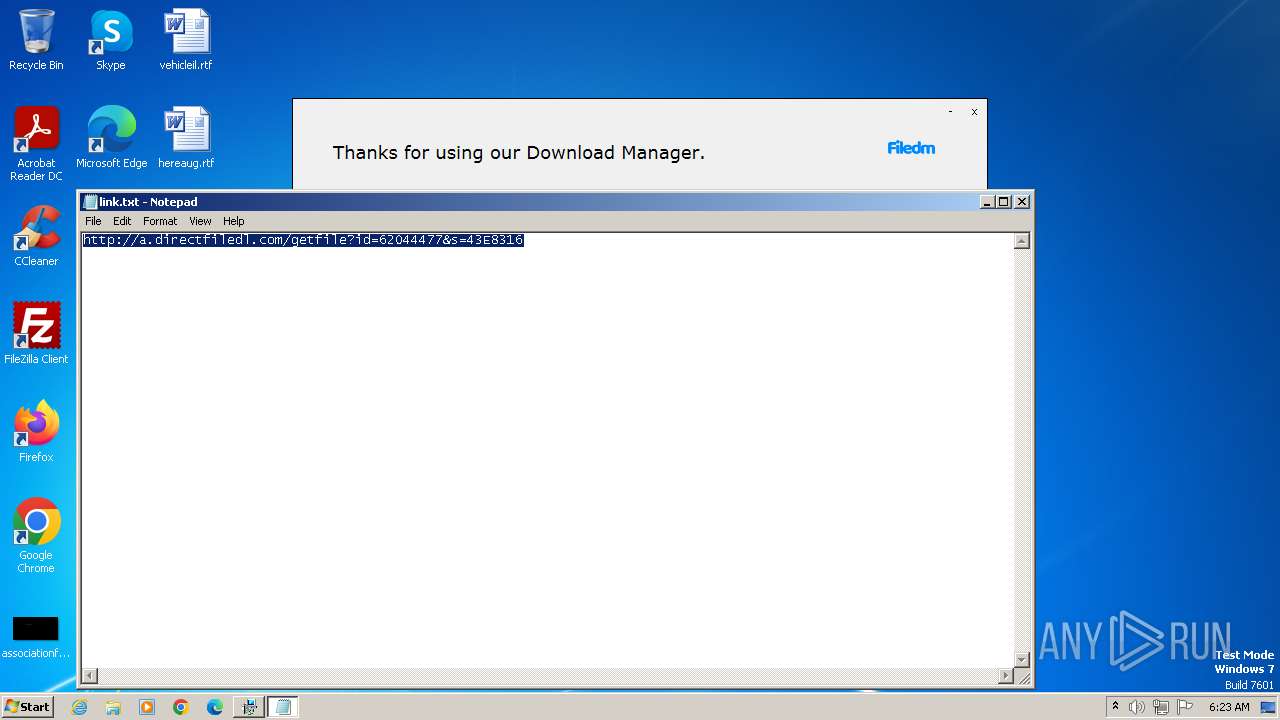
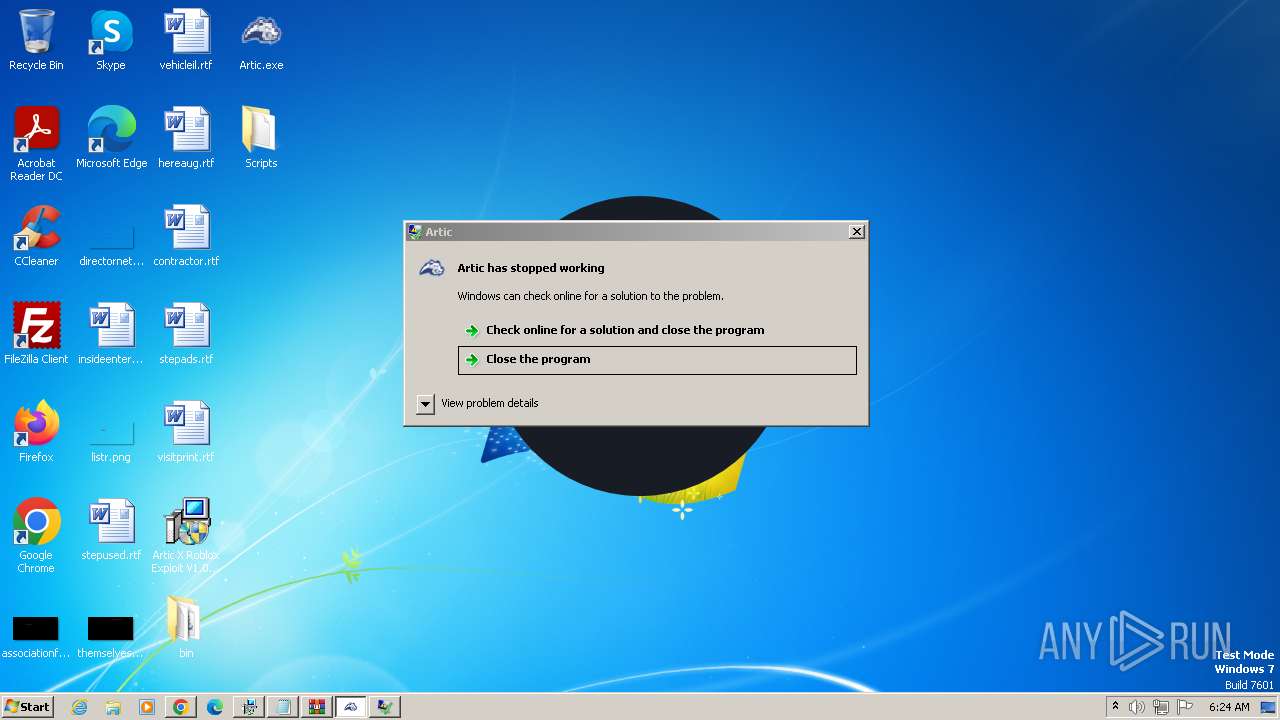
Start notepad (likely ransomware note)
- Artic X Roblox Exploit V1.0.3C_62044477.exe (PID: 1840)
Get information on the list of running processes
- cmd.exe (PID: 3108)
Adds/modifies Windows certificates
- Artic X Roblox Exploit V1.0.3C_62044477.exe (PID: 1840)
- setup62044477.exe (PID: 2764)
INFO
Checks supported languages
- Artic X Roblox Exploit V1.0.3C_62044477.exe (PID: 1840)
- wmpnscfg.exe (PID: 3680)
- setup62044477.exe (PID: 2764)
- setup62044477.exe (PID: 3864)
- Artic.exe (PID: 1936)
Reads the computer name
- Artic X Roblox Exploit V1.0.3C_62044477.exe (PID: 1840)
- setup62044477.exe (PID: 2764)
- wmpnscfg.exe (PID: 3680)
- setup62044477.exe (PID: 3864)
- Artic.exe (PID: 1936)
Checks proxy server information
- Artic X Roblox Exploit V1.0.3C_62044477.exe (PID: 1840)
Reads the machine GUID from the registry
- Artic X Roblox Exploit V1.0.3C_62044477.exe (PID: 1840)
- setup62044477.exe (PID: 2764)
- setup62044477.exe (PID: 3864)
- Artic.exe (PID: 1936)
Creates files or folders in the user directory
- Artic X Roblox Exploit V1.0.3C_62044477.exe (PID: 1840)
- setup62044477.exe (PID: 2764)
Create files in a temporary directory
- setup62044477.exe (PID: 2764)
- setup62044477.exe (PID: 3864)
- Artic X Roblox Exploit V1.0.3C_62044477.exe (PID: 1840)
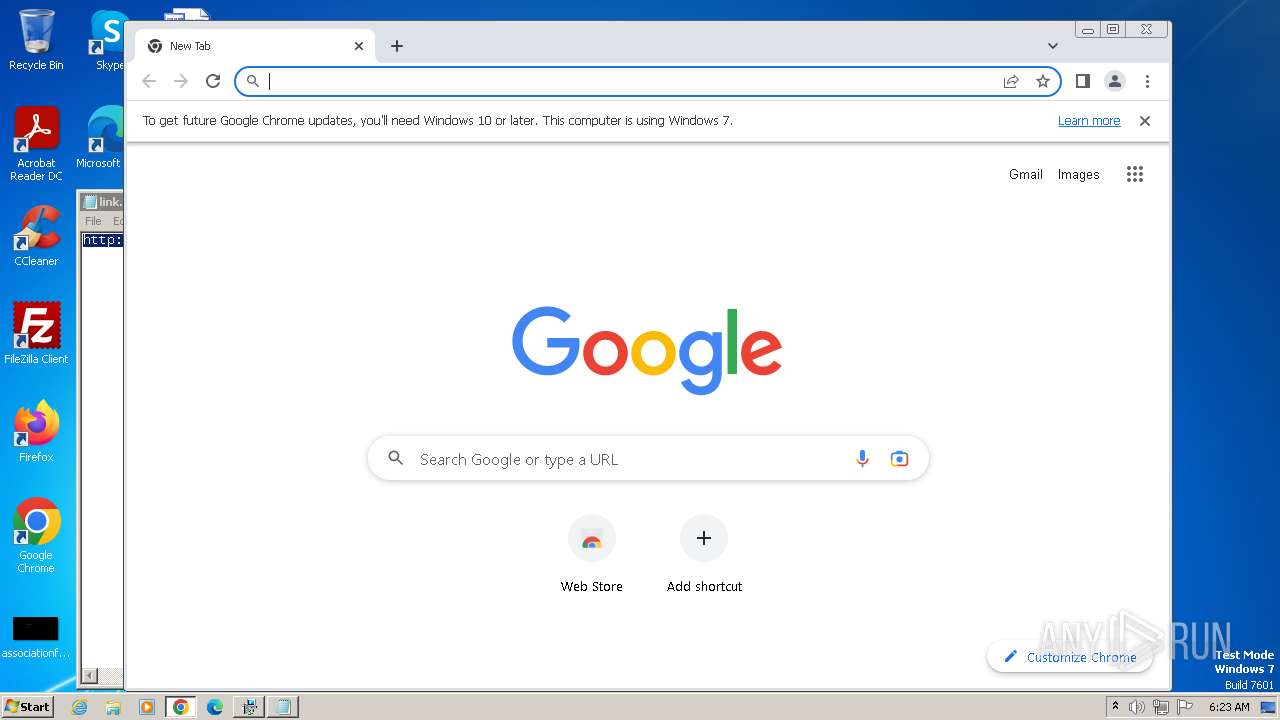
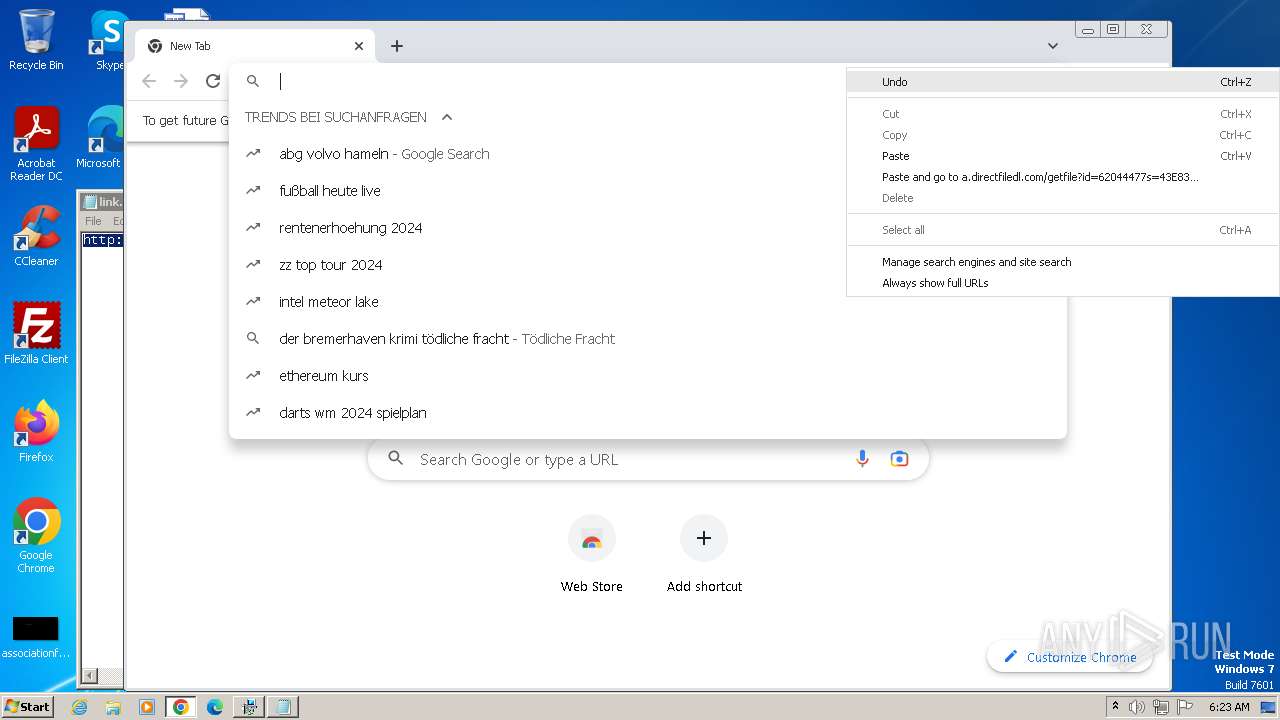
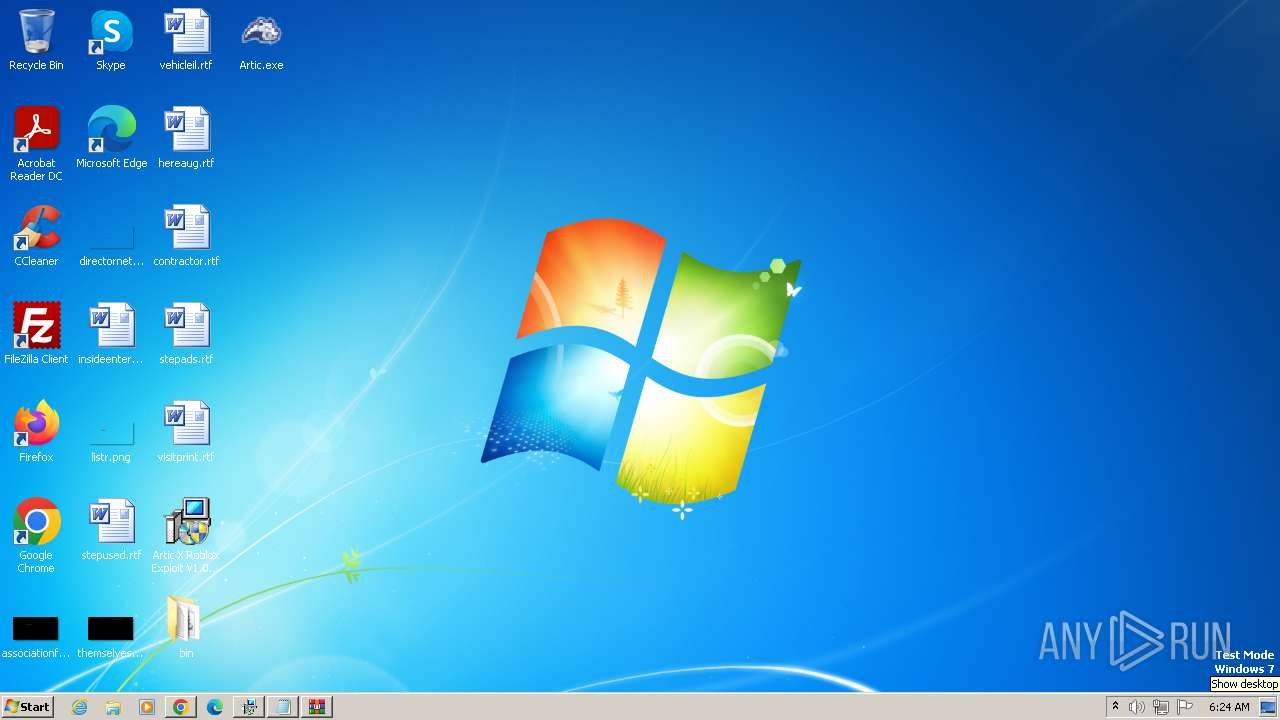
Manual execution by a user
- wmpnscfg.exe (PID: 3680)
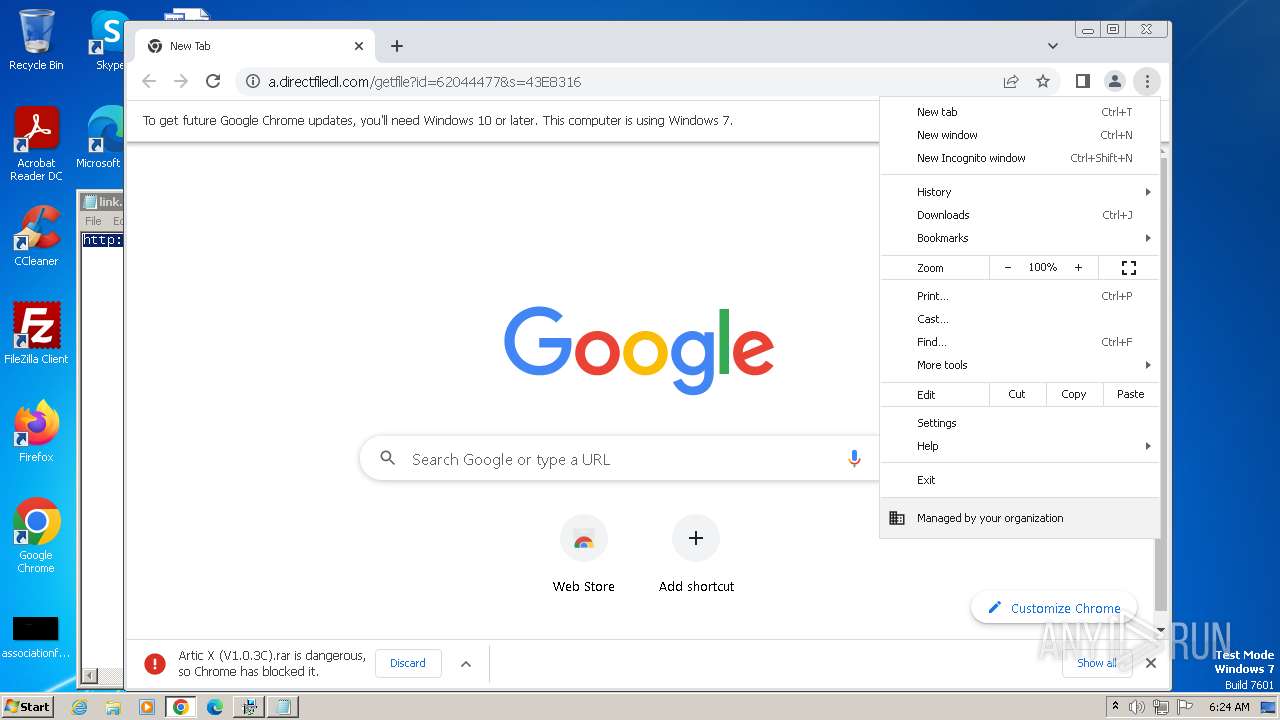
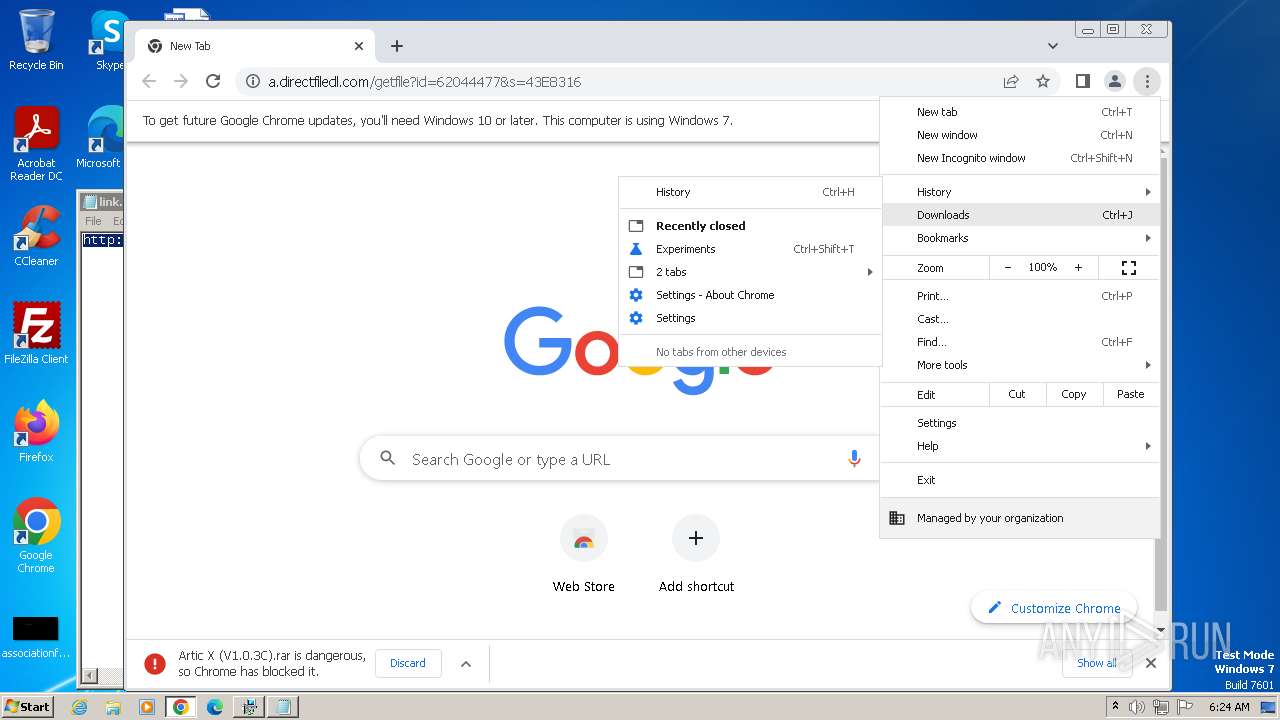
- chrome.exe (PID: 4000)
- Artic.exe (PID: 1936)
Reads Environment values
- setup62044477.exe (PID: 2764)
- Artic.exe (PID: 1936)
Reads product name
- setup62044477.exe (PID: 2764)
Application launched itself
- chrome.exe (PID: 4000)
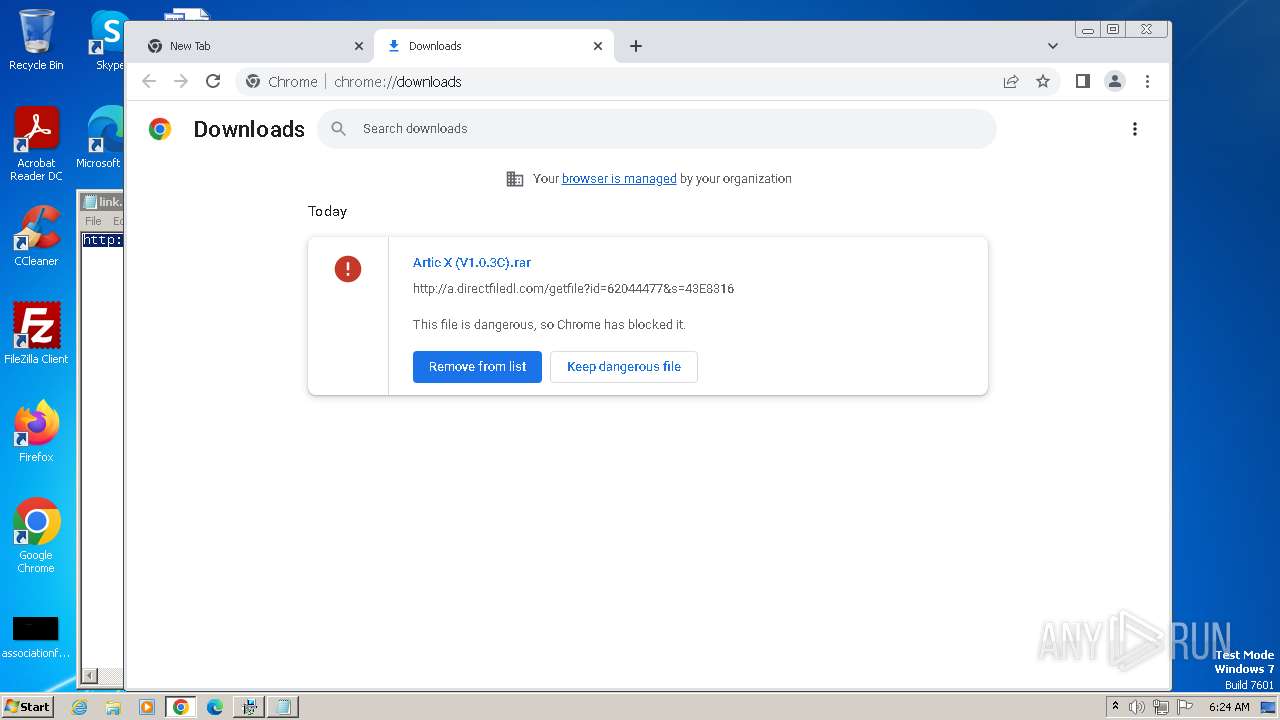
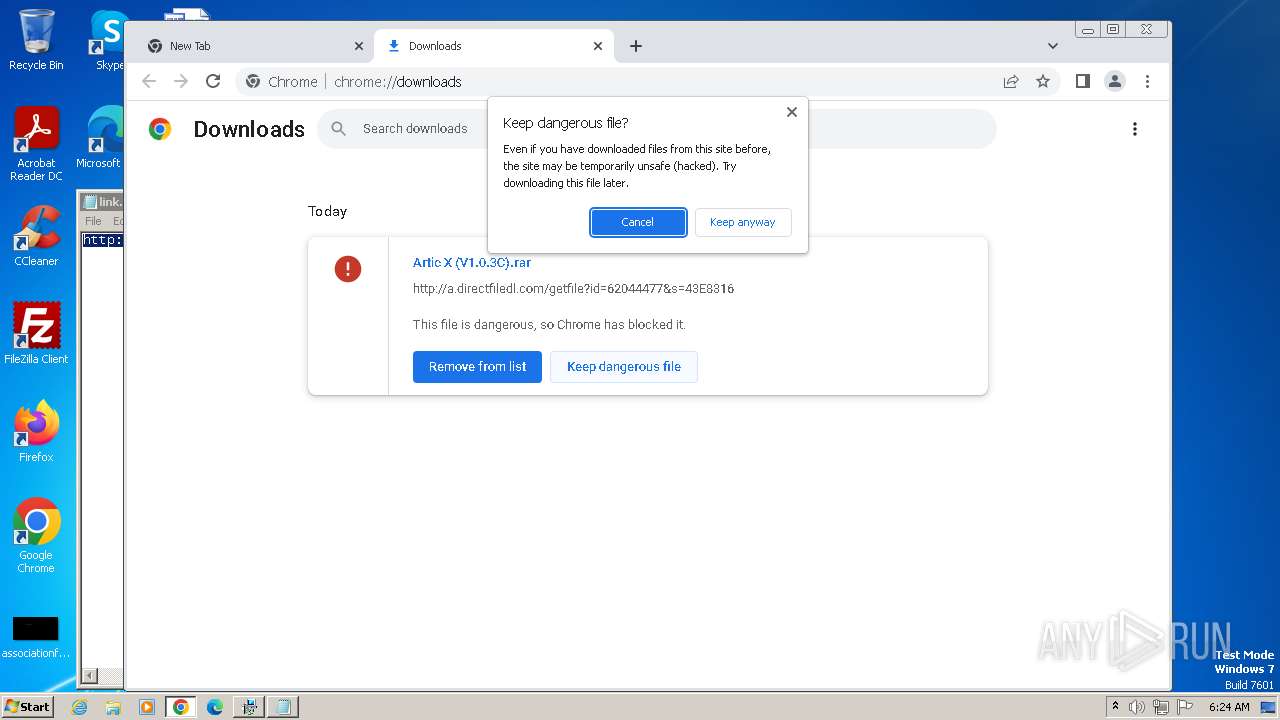
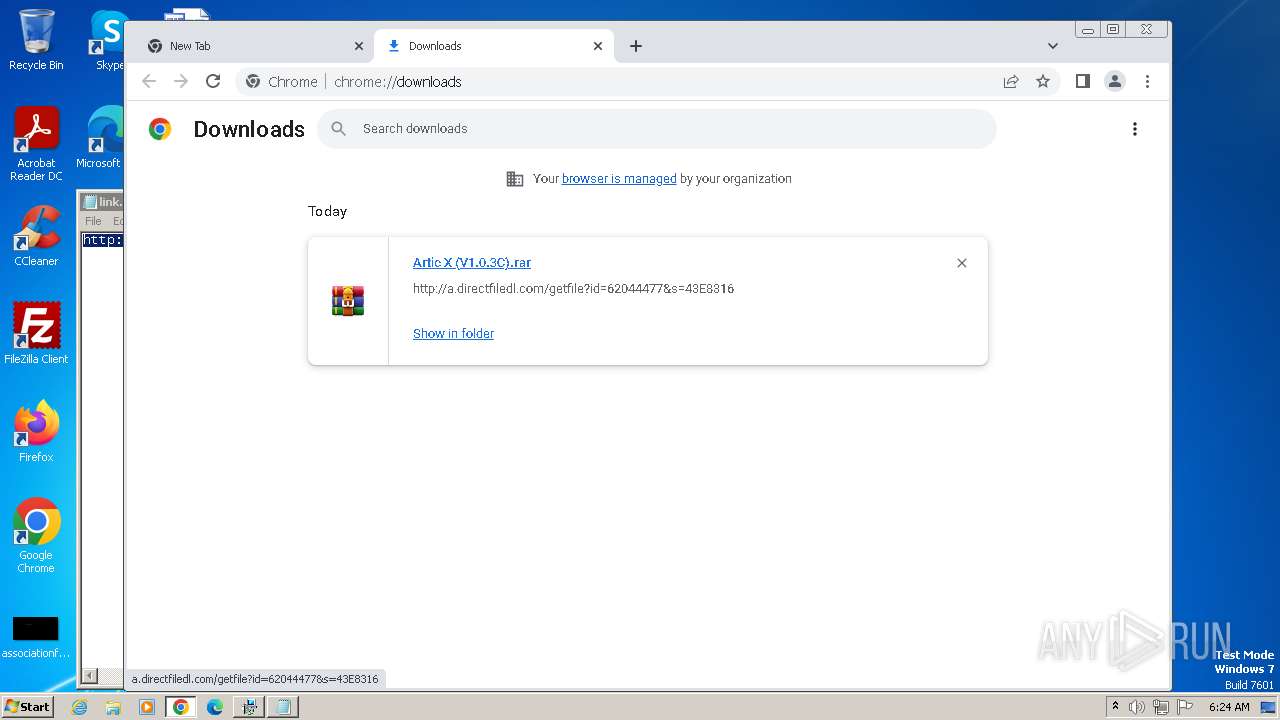
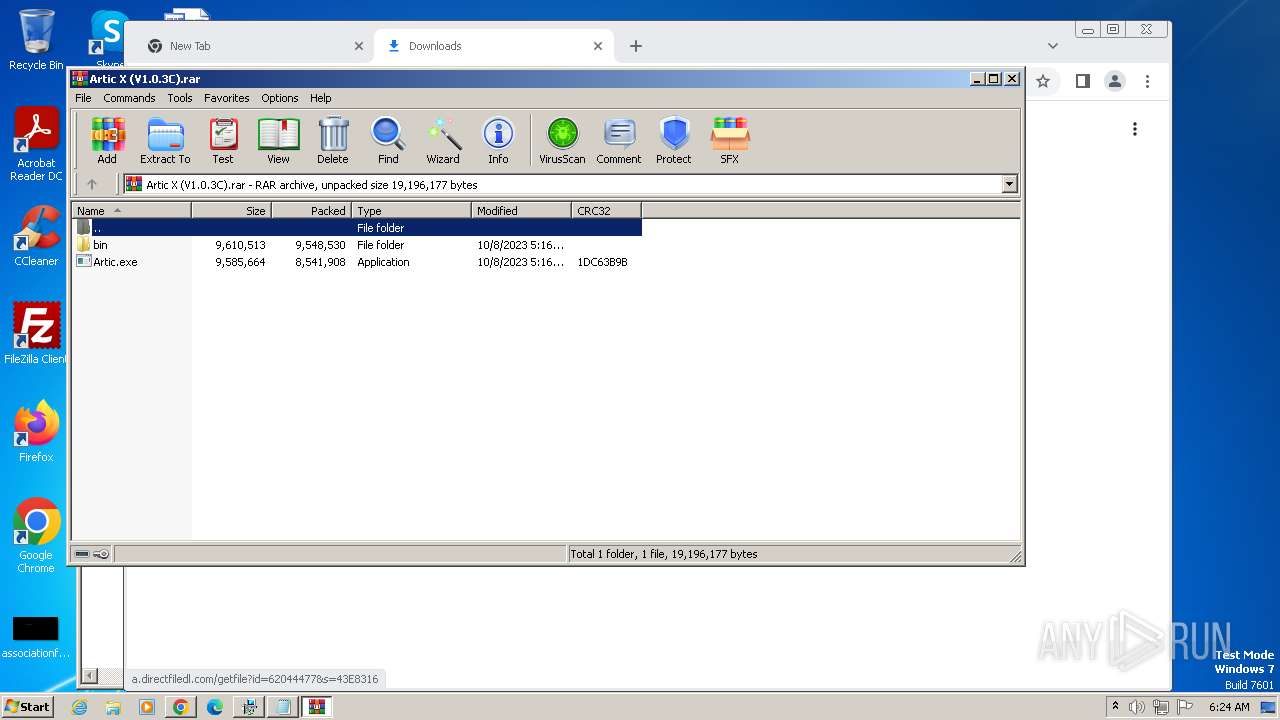
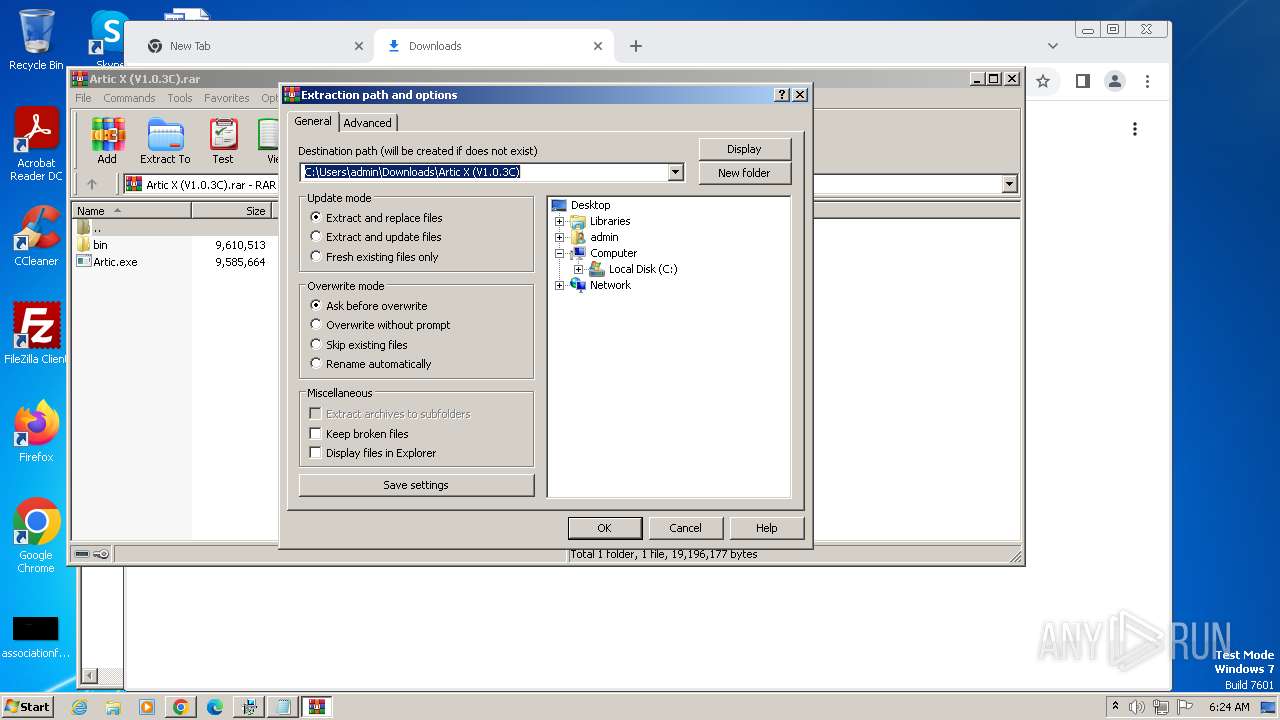
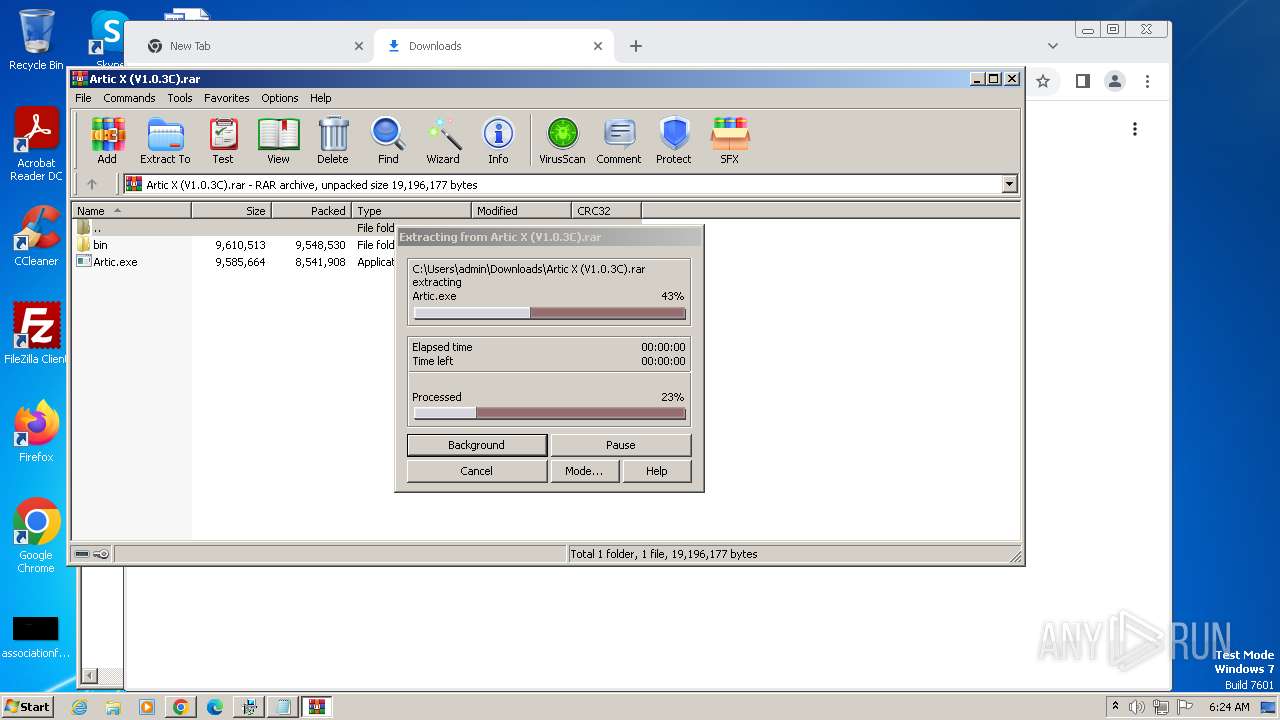
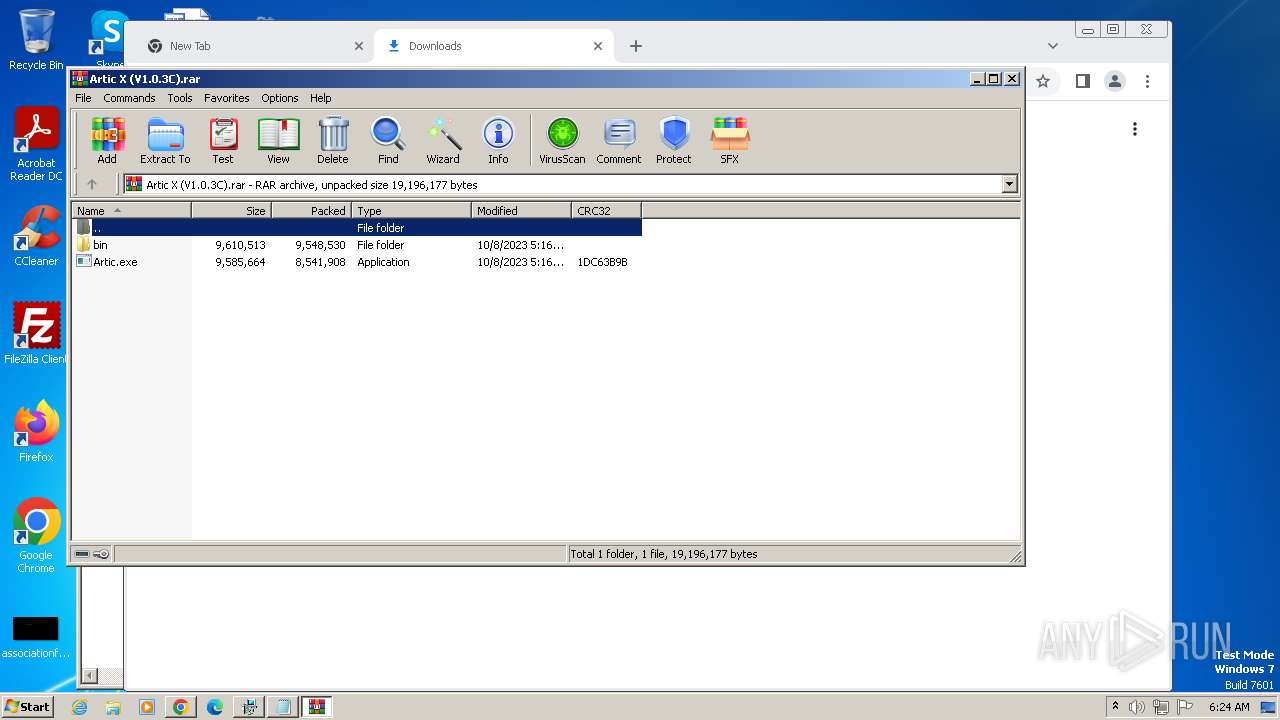
Drops the executable file immediately after the start
- chrome.exe (PID: 4000)
- WinRAR.exe (PID: 3112)
The process uses the downloaded file
- chrome.exe (PID: 2688)
- WinRAR.exe (PID: 3112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:11:21 20:16:16+01:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.22 |
| CodeSize: | 4345344 |
| InitializedDataSize: | 5646336 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x39649e |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
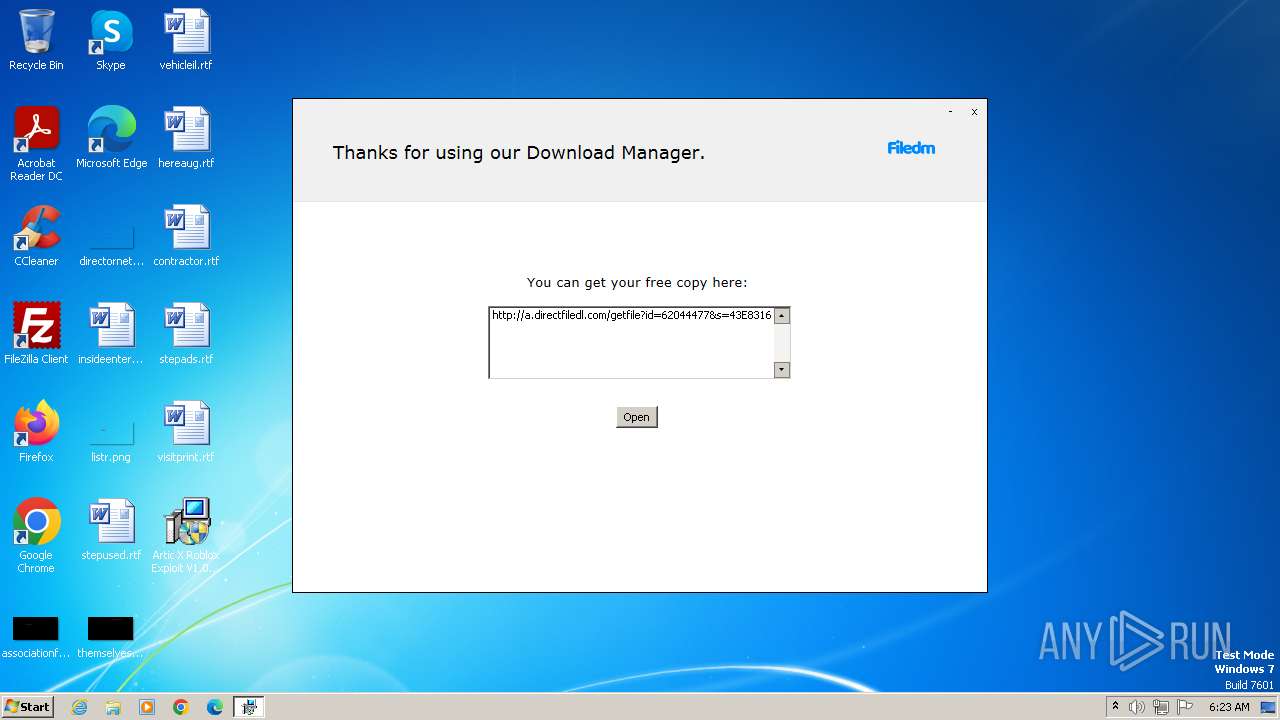
| FileDescription: | Download Manager |
| FileVersion: | 1 |
| InternalName: | Download Manager |
| LegalCopyright: | Download Manager |
| OriginalFileName: | Download Manager |
| ProductName: | Download Manager |
| ProductVersion: | 1 |
Total processes
80
Monitored processes
32
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1392 --field-trial-handle=1176,i,5089773194949534556,5815360616810248334,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3580 --field-trial-handle=1176,i,5089773194949534556,5815360616810248334,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3328 --field-trial-handle=1176,i,5089773194949534556,5815360616810248334,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1840 | "C:\Users\admin\Desktop\Artic X Roblox Exploit V1.0.3C_62044477.exe" | C:\Users\admin\Desktop\Artic X Roblox Exploit V1.0.3C_62044477.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Download Manager Exit code: 0 Version: 1 Modules
| |||||||||||||||
| 1904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1440 --field-trial-handle=1176,i,5089773194949534556,5815360616810248334,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1936 | "C:\Users\admin\Desktop\Artic.exe" | C:\Users\admin\Desktop\Artic.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Artic Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --mojo-platform-channel-handle=3460 --field-trial-handle=1176,i,5089773194949534556,5815360616810248334,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3692 --field-trial-handle=1176,i,5089773194949534556,5815360616810248334,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2548 | tasklist /FI "PID eq 2764" /fo csv | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3492 --field-trial-handle=1176,i,5089773194949534556,5815360616810248334,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
19 007
Read events
18 790
Write events
216
Delete events
1
Modification events
| (PID) Process: | (1840) Artic X Roblox Exploit V1.0.3C_62044477.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1840) Artic X Roblox Exploit V1.0.3C_62044477.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005A010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1840) Artic X Roblox Exploit V1.0.3C_62044477.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1840) Artic X Roblox Exploit V1.0.3C_62044477.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1840) Artic X Roblox Exploit V1.0.3C_62044477.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1840) Artic X Roblox Exploit V1.0.3C_62044477.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1840) Artic X Roblox Exploit V1.0.3C_62044477.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1840) Artic X Roblox Exploit V1.0.3C_62044477.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1840) Artic X Roblox Exploit V1.0.3C_62044477.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2764) setup62044477.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager |
| Operation: | write | Name: | PendingFileRenameOperations |
Value: \??\C:\Users\admin\AppData\Local\Temp\ec05d89197b949eb6957b79472e8723d\ServiceHide.dll | |||
Executable files
40
Suspicious files
73
Text files
44
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2764 | setup62044477.exe | C:\Users\admin\AppData\Local\Temp\ec05d89197b949eb6957b79472e8723d\Ninject.dll | executable | |
MD5:8DB691813A26E7D0F1DB5E2F4D0D05E3 | SHA256:3043A65F11AC204E65BCA142FF4166D85F1B22078B126B806F1FECB2A315C701 | |||
| 2764 | setup62044477.exe | C:\Users\admin\AppData\Local\Temp\ec05d89197b949eb6957b79472e8723d\H2OServices.dll | executable | |
MD5:6DF226BDA27D26CE4523B80DBF57A9EA | SHA256:17D737175D50EEE97AC1C77DB415FE25CC3C7A3871B65B93CC3FAD63808A9ABC | |||
| 2764 | setup62044477.exe | C:\Users\admin\AppData\Local\Temp\ec05d89197b949eb6957b79472e8723d\vcruntime140.dll | executable | |
MD5:1A84957B6E681FCA057160CD04E26B27 | SHA256:9FAEAA45E8CC986AF56F28350B38238B03C01C355E9564B849604B8D690919C5 | |||
| 1840 | Artic X Roblox Exploit V1.0.3C_62044477.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\869CC3B84BEE922ABCE8CDCAA964F3D9_6F32A0985879EB33E63263938C358721 | binary | |
MD5:5EF9F715AFDD594C06331D839760A9F0 | SHA256:46D860FD0E8373112A105351B4D25A94A1F798B5C6CD94E146EDE66E4930379F | |||
| 2764 | setup62044477.exe | C:\Users\admin\AppData\Local\Temp\ec05d89197b949eb6957b79472e8723d\OfferSDK.dll | executable | |
MD5:B199DCD6824A02522A4D29A69AB65058 | SHA256:9310A58F26BE8BD453CDE5CA6AA05042942832711FBDEB5430A2840232BFA5E4 | |||
| 1840 | Artic X Roblox Exploit V1.0.3C_62044477.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:B323D99E9FF67FD4B6371C30651159DA | SHA256:4E30C794CB6BCD36EE602F69955A9763019D495F15D1FEA1A2EDF802F338796D | |||
| 2764 | setup62044477.exe | C:\Users\admin\AppData\Local\Temp\ec05d89197b949eb6957b79472e8723d\GenericSetup.LastScreen.dll | executable | |
MD5:6E001F8D0EE4F09A6673A9E8168836B6 | SHA256:6A30F9C604C4012D1D2E1BA075213C378AFB1BFCB94276DE7995ED7BBF492859 | |||
| 1840 | Artic X Roblox Exploit V1.0.3C_62044477.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:6738DBF4AF0B9733227741785321CF91 | SHA256:87BD80DD95110EE0679E24209B064A134A161B20FDE8EBDC00E452509F40EFC3 | |||
| 1840 | Artic X Roblox Exploit V1.0.3C_62044477.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 2764 | setup62044477.exe | C:\Users\admin\AppData\Local\Temp\ec05d89197b949eb6957b79472e8723d\msvcp140.dll | executable | |
MD5:8FF1898897F3F4391803C7253366A87B | SHA256:51398691FEEF7AE0A876B523AEC47C4A06D9A1EE62F1A0AEE27DE6D6191C68AD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
30
DNS requests
37
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1840 | Artic X Roblox Exploit V1.0.3C_62044477.exe | GET | 200 | 142.250.184.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
1840 | Artic X Roblox Exploit V1.0.3C_62044477.exe | GET | 200 | 23.212.210.158:80 | http://x2.c.lencr.org/ | unknown | binary | 300 b | unknown |
1840 | Artic X Roblox Exploit V1.0.3C_62044477.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e529d4aeadbe986d | unknown | compressed | 4.66 Kb | unknown |
1840 | Artic X Roblox Exploit V1.0.3C_62044477.exe | GET | 200 | 142.250.184.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIAjrICMzZli2TN25s%3D | unknown | binary | 724 b | unknown |
1840 | Artic X Roblox Exploit V1.0.3C_62044477.exe | GET | 200 | 142.250.184.131:80 | http://ocsp.pki.goog/s/gts1d4/BLyg_-h63RA/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSMBFDqU0NJQdZdEGU3bkhj0FoRrQQUJeIYDrJXkZQq5dRdhpCD3lOzuJICEACRI2vGqzWlEof0zfA2Du0%3D | unknown | binary | 471 b | unknown |
— | — | GET | 200 | 142.250.184.131:80 | http://ocsp.pki.goog/s/gts1d4/tPVfSrt3g1k/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSMBFDqU0NJQdZdEGU3bkhj0FoRrQQUJeIYDrJXkZQq5dRdhpCD3lOzuJICEQDASJ2qLaCI5xAFjJiGxx93 | unknown | binary | 472 b | unknown |
1840 | Artic X Roblox Exploit V1.0.3C_62044477.exe | GET | 200 | 23.212.210.158:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 10.7 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 9.94 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1840 | Artic X Roblox Exploit V1.0.3C_62044477.exe | 35.190.60.70:443 | www.dlsft.com | GOOGLE | US | whitelisted |
1840 | Artic X Roblox Exploit V1.0.3C_62044477.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
1840 | Artic X Roblox Exploit V1.0.3C_62044477.exe | 142.250.184.131:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
2764 | setup62044477.exe | 104.17.8.52:443 | flow.lavasoft.com | CLOUDFLARENET | — | shared |
1840 | Artic X Roblox Exploit V1.0.3C_62044477.exe | 188.114.96.3:443 | filedm.com | CLOUDFLARENET | NL | unknown |
1840 | Artic X Roblox Exploit V1.0.3C_62044477.exe | 23.212.210.158:80 | x1.c.lencr.org | AKAMAI-AS | AU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.dlsft.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.google.com |
| whitelisted |
flow.lavasoft.com |
| whitelisted |
dlsft.com |
| unknown |
filedm.com |
| malicious |
x1.c.lencr.org |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report