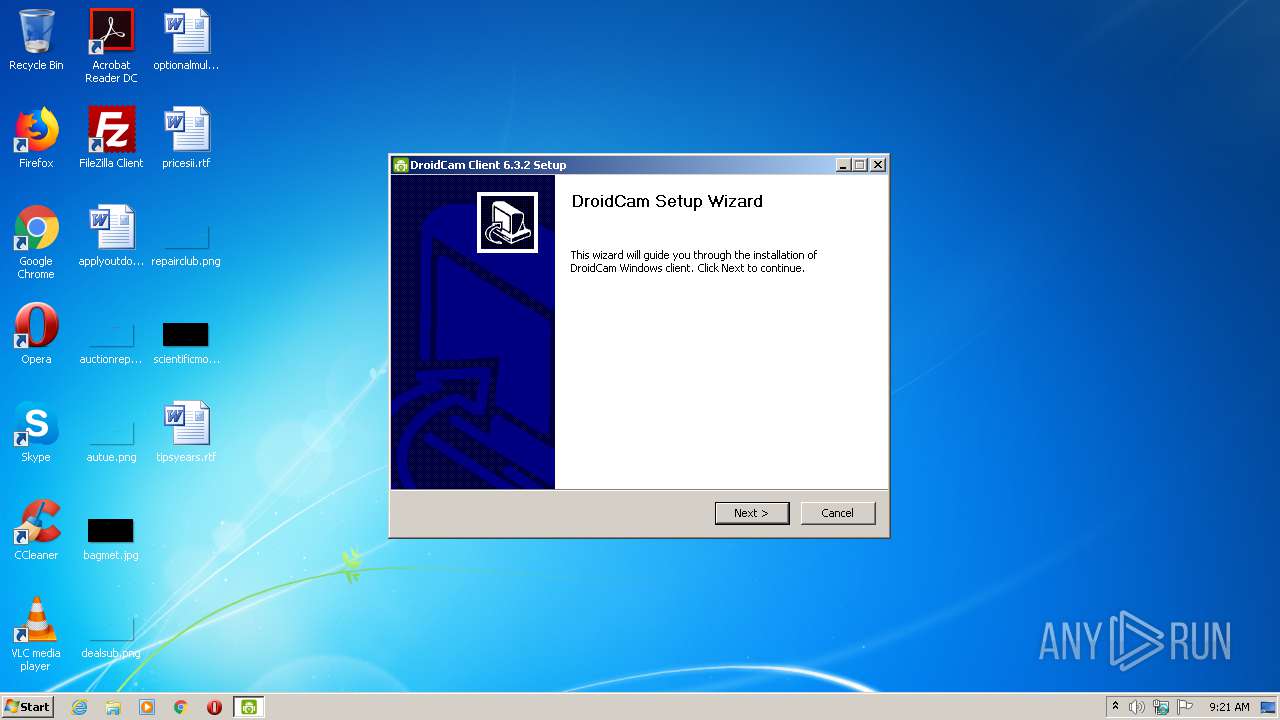
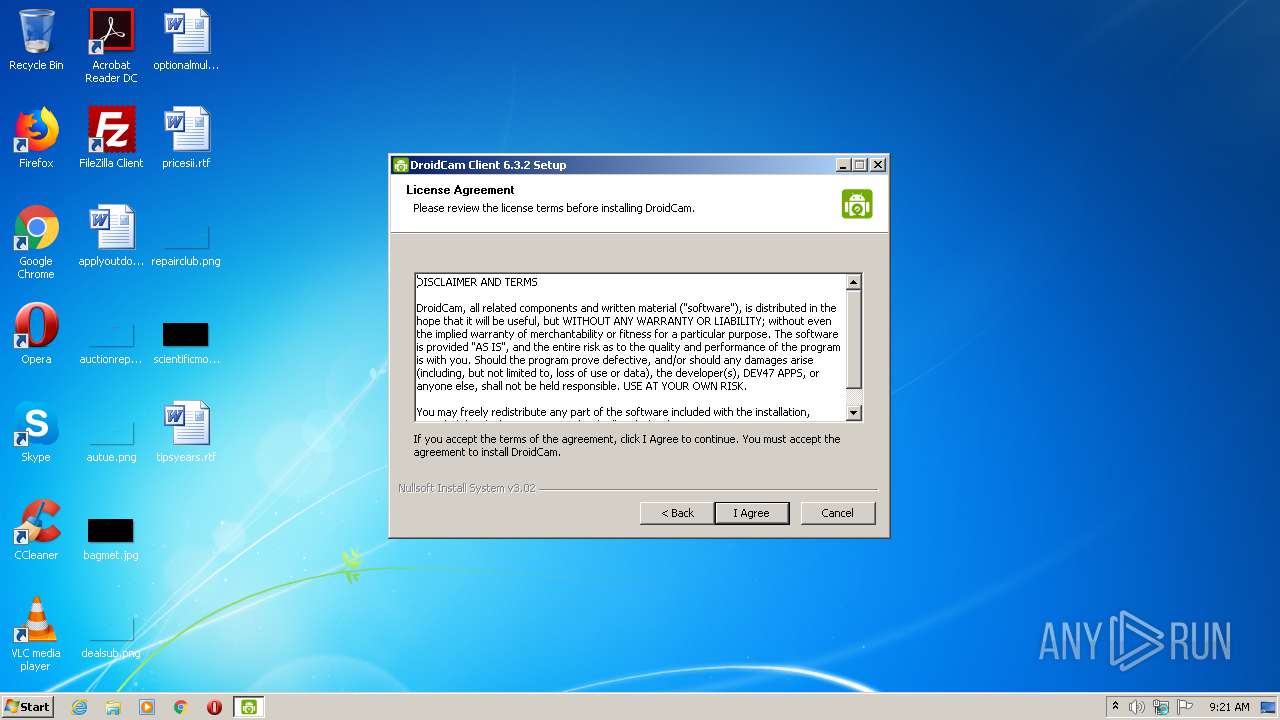
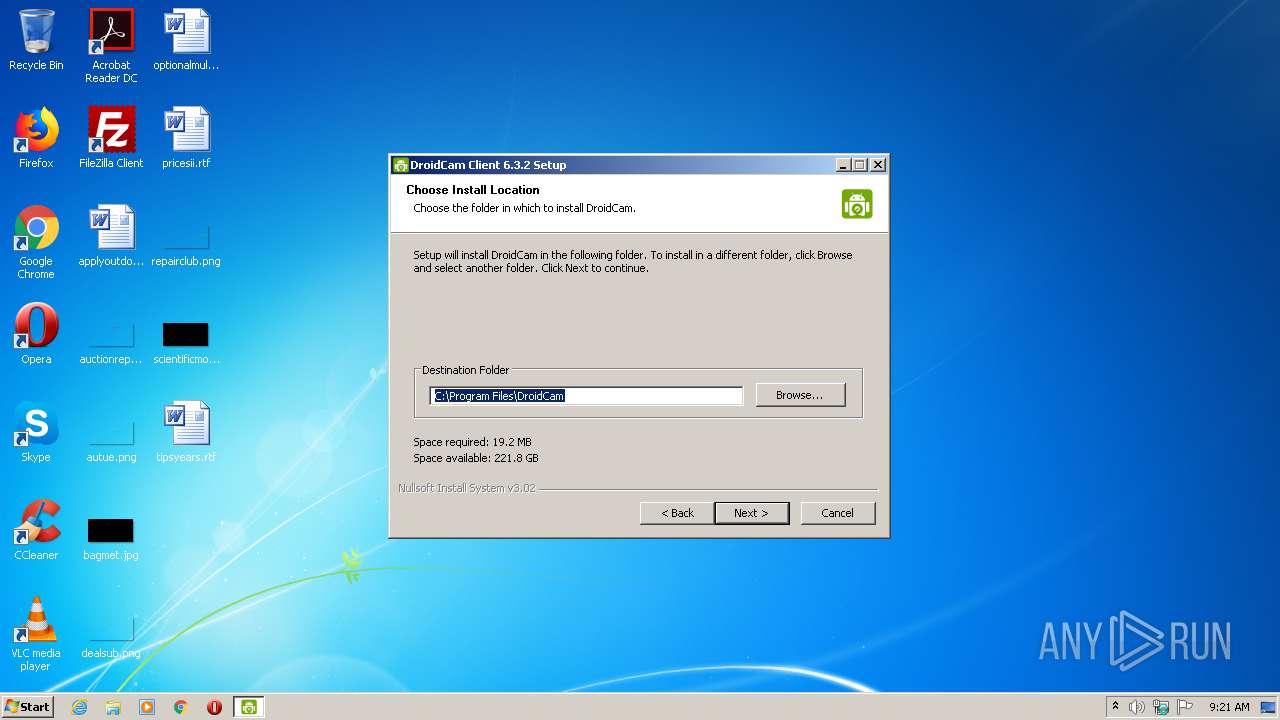
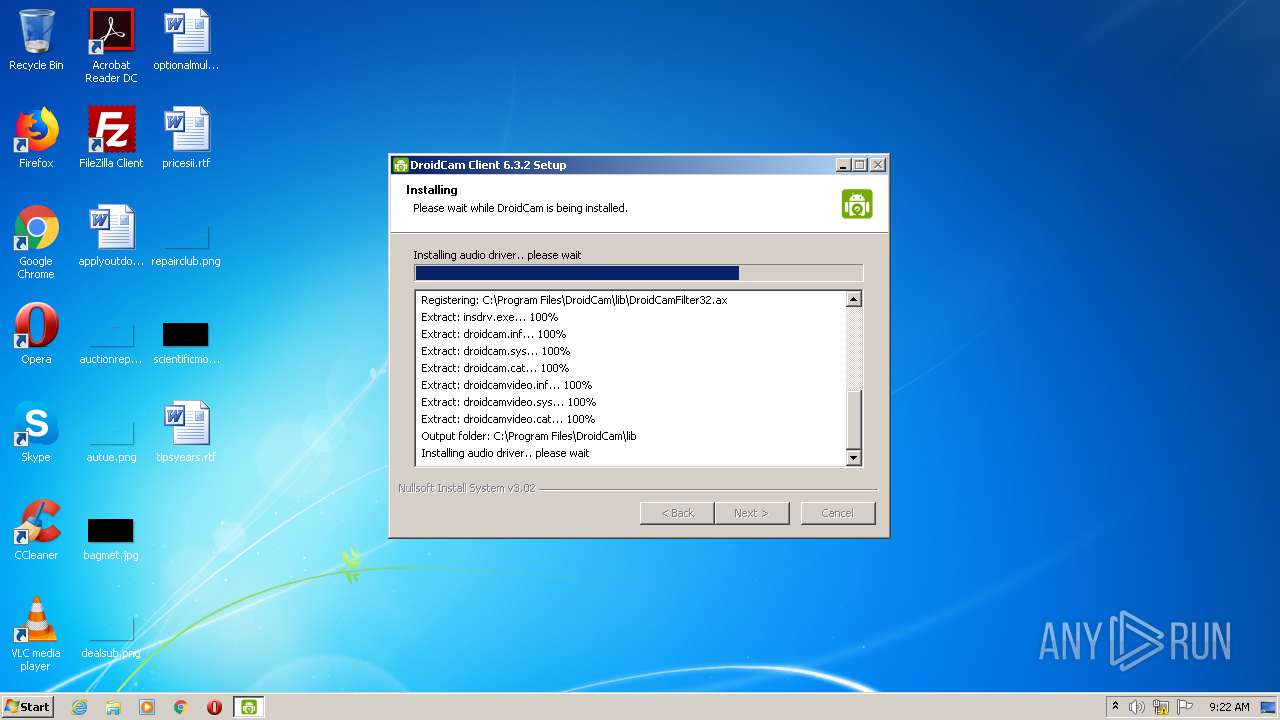
| File name: | DroidCam.Setup.6.3.2.exe |
| Full analysis: | https://app.any.run/tasks/04112f36-5f32-40f1-b92b-f143c0b5c0ca |
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2020, 08:21:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 32E9A8A7C91445B7CF4282BA076F45B4 |
| SHA1: | A671959D3D9CF2B89A732B767E5AF497615CFF46 |
| SHA256: | BE42A4D6259A7B332F30B50D88065488153CF41E9AD9D9F4724F355D2E9D5961 |
| SSDEEP: | 393216:ZZsfzTD12zS7SEOegn4j7BgNE9O+wcDGFdClu8ZLzz+:7sf/D1kS7249O3cDGvClnS |
MALICIOUS
Loads dropped or rewritten executable
- DroidCam.Setup.6.3.2.exe (PID: 2456)
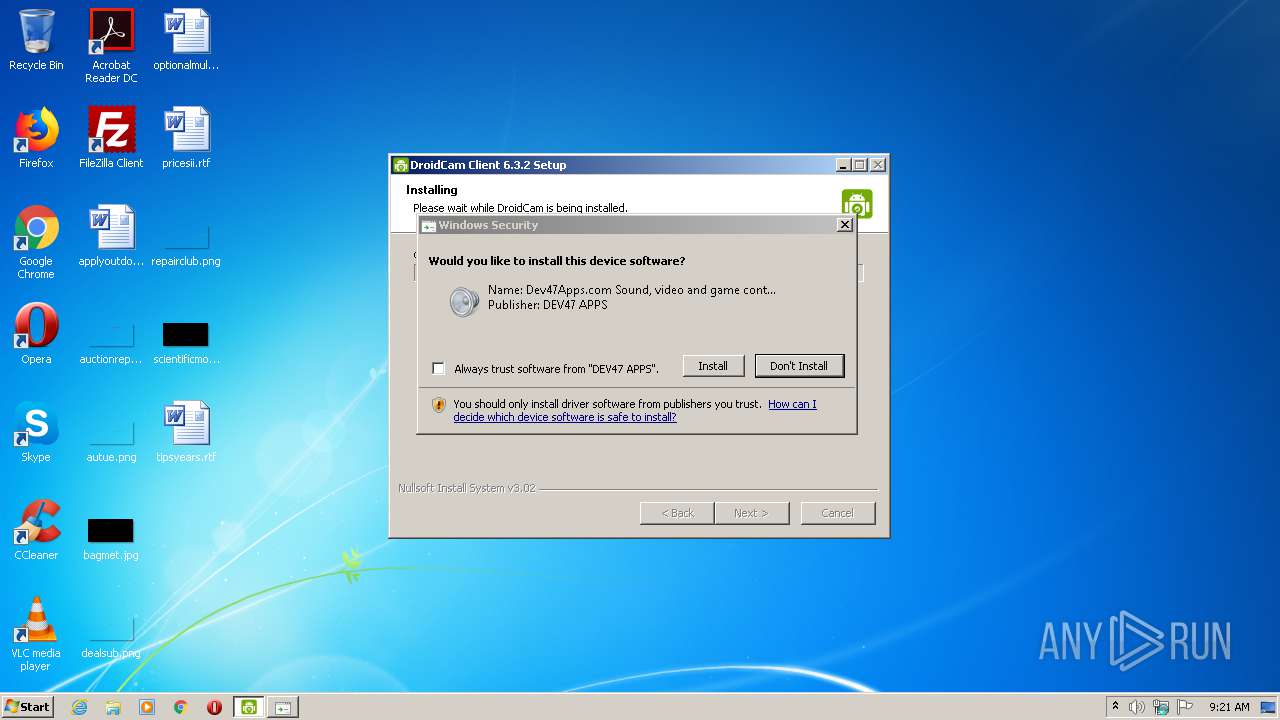
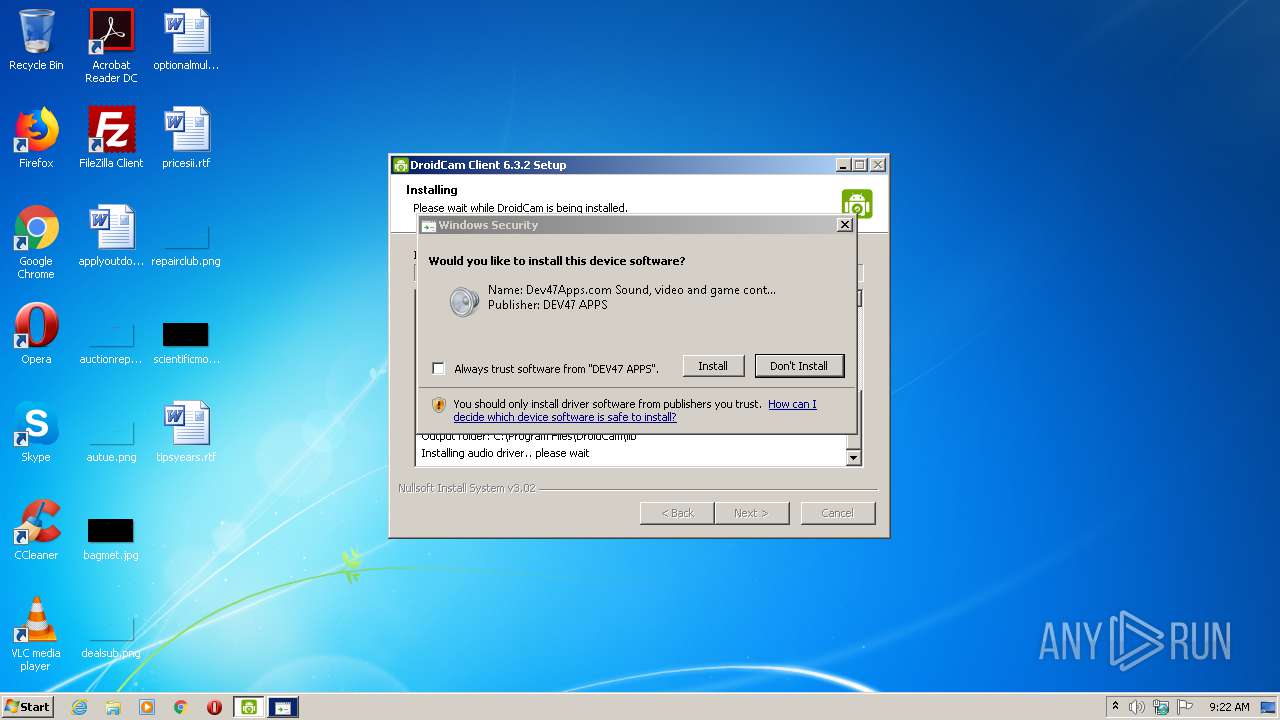
Changes settings of System certificates
- insdrv.exe (PID: 3112)
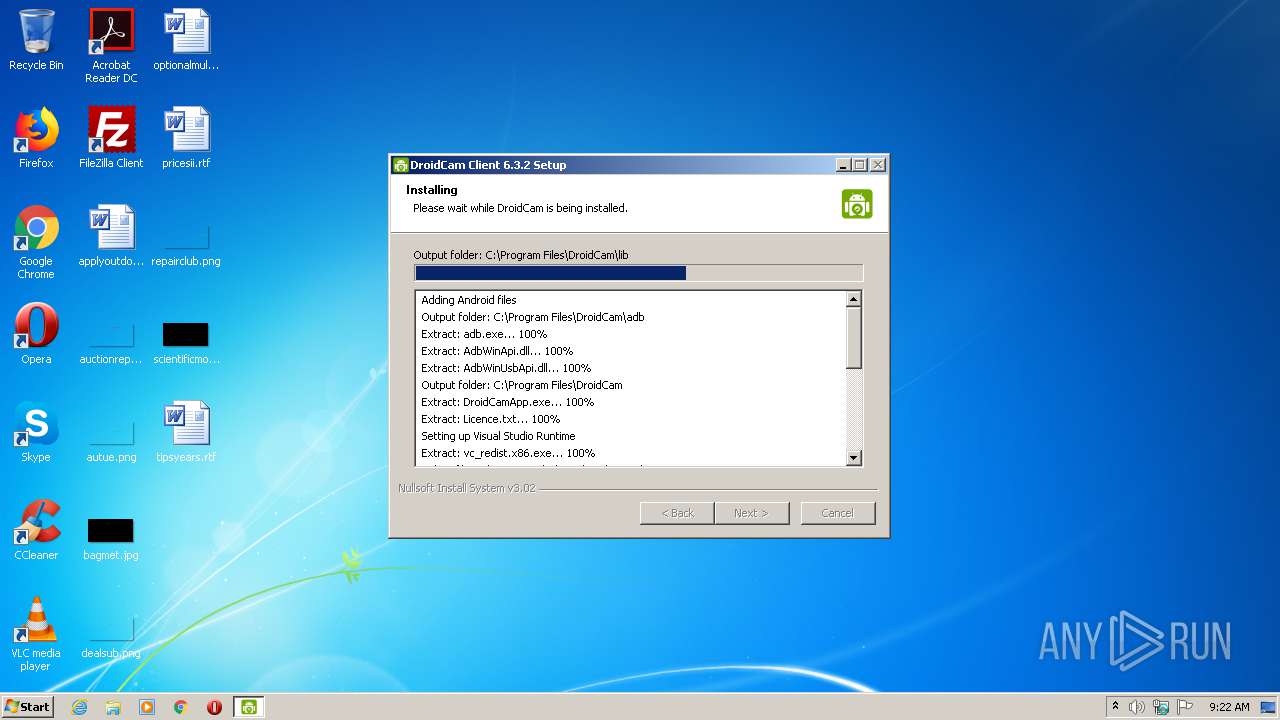
Application was dropped or rewritten from another process
- vc_redist.x86.exe (PID: 3984)
- vc_redist.x86.exe (PID: 2096)
- insdrv.exe (PID: 3112)
- nsD7AF.tmp (PID: 3140)
- ns3F74.tmp (PID: 3792)
- insdrv.exe (PID: 2584)
- nsDB0B.tmp (PID: 2688)
SUSPICIOUS
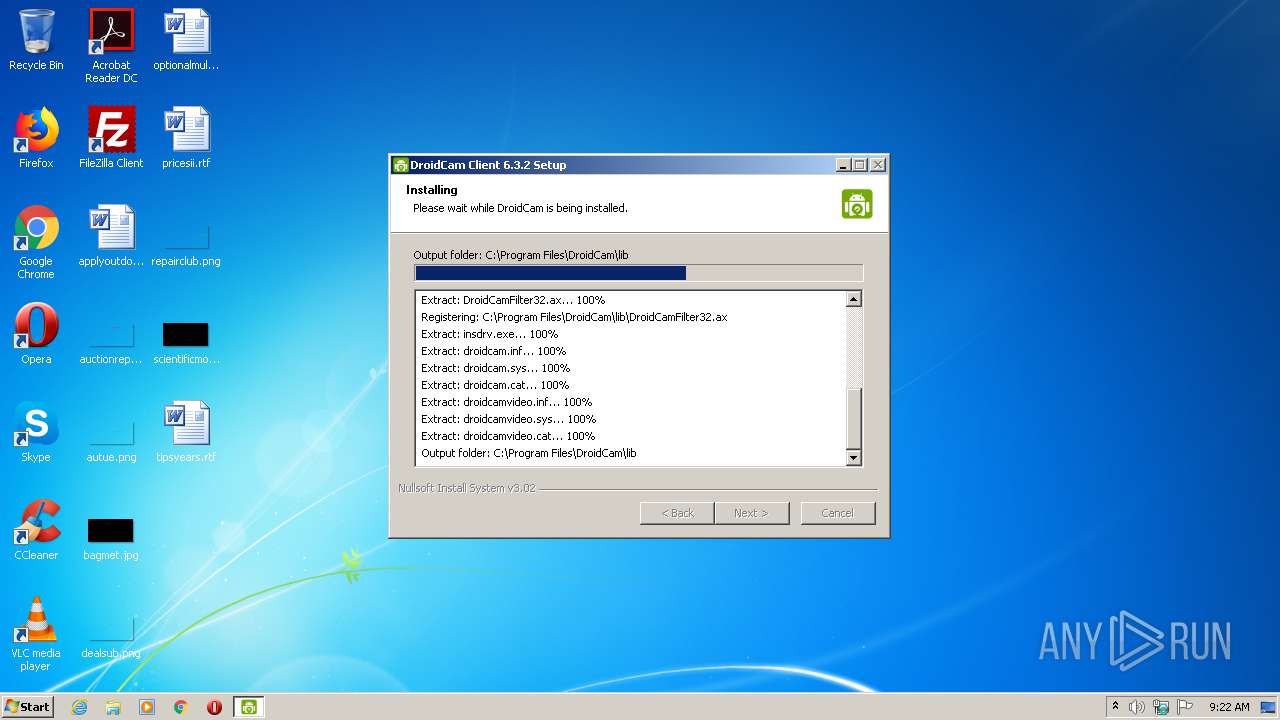
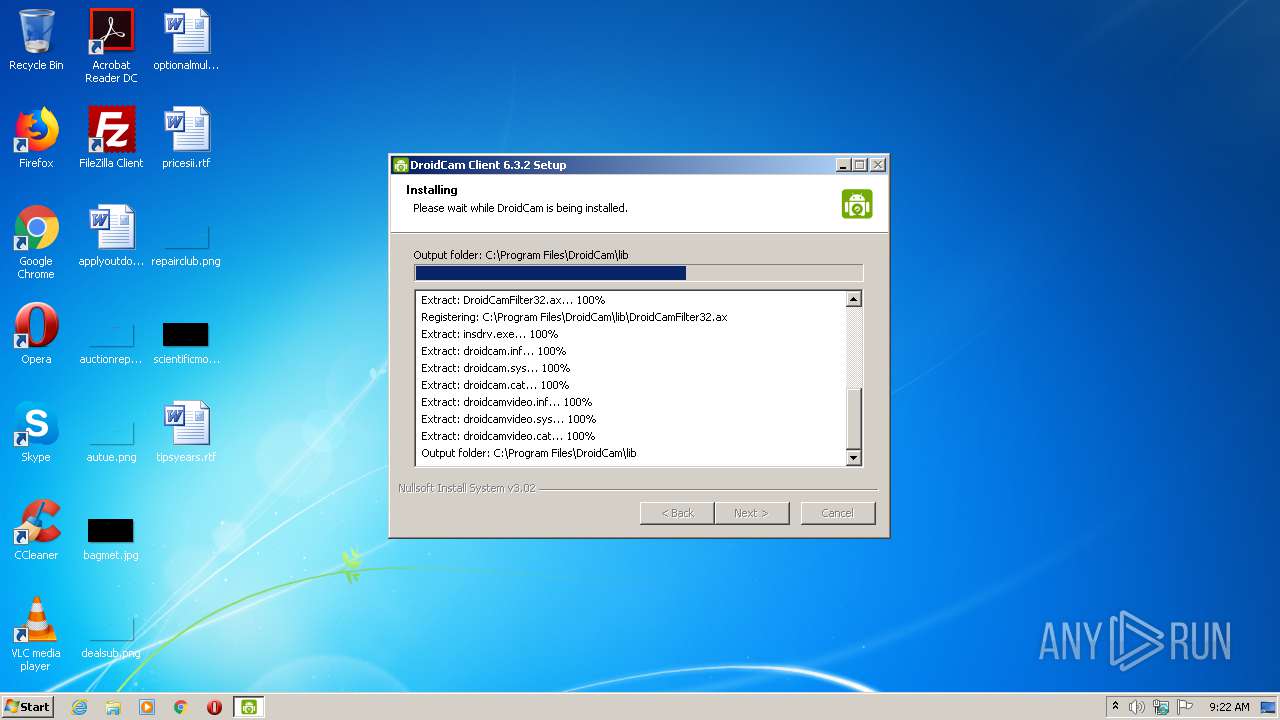
Executable content was dropped or overwritten
- DroidCam.Setup.6.3.2.exe (PID: 2456)
- insdrv.exe (PID: 3112)
- DrvInst.exe (PID: 2252)
- DrvInst.exe (PID: 2380)
- insdrv.exe (PID: 2584)
- DrvInst.exe (PID: 604)
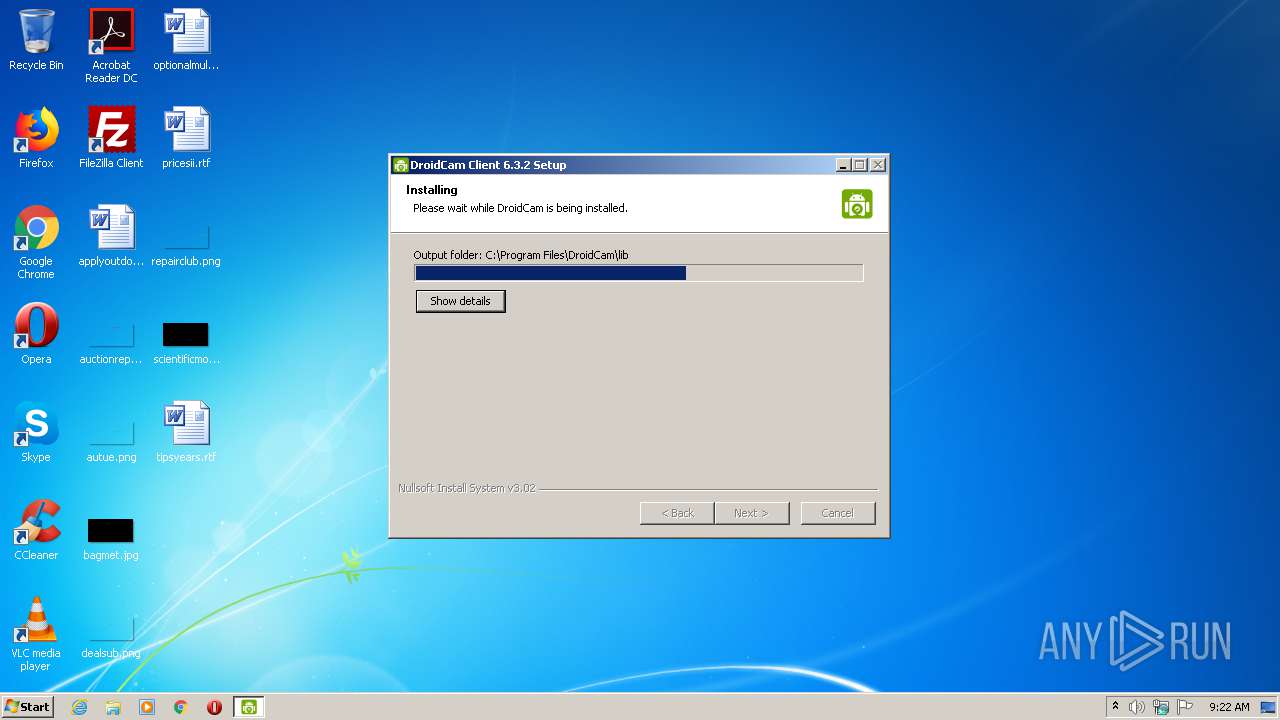
Creates files in the program directory
- DroidCam.Setup.6.3.2.exe (PID: 2456)
Starts application with an unusual extension
- DroidCam.Setup.6.3.2.exe (PID: 2456)
Application launched itself
- vc_redist.x86.exe (PID: 3984)
Adds / modifies Windows certificates
- insdrv.exe (PID: 3112)
Executed via COM
- DrvInst.exe (PID: 2252)
- DrvInst.exe (PID: 2380)
- DrvInst.exe (PID: 604)
Searches for installed software
- vc_redist.x86.exe (PID: 2096)
Creates files in the driver directory
- DrvInst.exe (PID: 2252)
- DrvInst.exe (PID: 2380)
- DrvInst.exe (PID: 604)
Removes files from Windows directory
- DrvInst.exe (PID: 2252)
- DrvInst.exe (PID: 2380)
- DrvInst.exe (PID: 604)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 2252)
- DrvInst.exe (PID: 604)
Creates files in the Windows directory
- DrvInst.exe (PID: 2252)
- DrvInst.exe (PID: 2380)
- DrvInst.exe (PID: 604)
Executed as Windows Service
- vssvc.exe (PID: 2624)
INFO
Dropped object may contain Bitcoin addresses
- DroidCam.Setup.6.3.2.exe (PID: 2456)
Searches for installed software
- DrvInst.exe (PID: 2252)
- DrvInst.exe (PID: 604)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2624)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:07:24 08:35:15+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24576 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x31bb |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Jul-2017 06:35:15 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 24-Jul-2017 06:35:15 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005ED2 | 0x00006000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44218 |
.rdata | 0x00007000 | 0x00001248 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.00765 |
.data | 0x00009000 | 0x0001A818 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.13586 |
.ndata | 0x00024000 | 0x00018000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003C000 | 0x00009C90 | 0x00009E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.66515 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28847 | 1070 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.96986 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 4.73845 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 5.11387 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 0 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.68418 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.65946 | 280 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
55
Monitored processes
15
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 604 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{277c5949-2590-0b23-38a8-da6c43211647}\droidcam.inf" "0" "6e67c8bbf" "000005C0" "WinSta0\Default" "000005CC" "208" "c:\program files\droidcam\lib" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2096 | "C:\Program Files\DroidCam\vc_redist.x86.exe" /install /quiet -burn.unelevated BurnPipe.{5E35FDEB-8423-42F7-B3E9-C1557E653D66} {51D9B705-A9DD-48F5-882A-FDB7154DCA4D} 3984 | C:\Program Files\DroidCam\vc_redist.x86.exe | — | vc_redist.x86.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015 Redistributable (x86) - 14.0.23026 Exit code: 1638 Version: 14.0.23026.0 Modules
| |||||||||||||||
| 2252 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{5d535b41-3d6e-65a4-a9b4-85046e3da465}\droidcamvideo.inf" "0" "61e7d49db" "000005B4" "WinSta0\Default" "00000544" "208" "c:\program files\droidcam\lib" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2380 | DrvInst.exe "2" "211" "ROOT\MEDIA\0000" "C:\Windows\INF\oem4.inf" "droidcamvideo.inf:Microsoft:DroidCamVideo.Device:12.0.0.1:droidcamvideo" "61e7d49db" "000005B4" "000003B0" "000005D8" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2396 | rundll32.exe C:\Windows\system32\pnpui.dll,InstallSecurityPromptRunDllW 20 Global\{671b0fb7-380c-3d5b-3b5e-3a61e9a94155} Global\{3d2b62c8-5ce9-722a-77f5-0a77a0372d76} C:\Windows\System32\DriverStore\Temp\{767da9d4-50e8-7b9d-6e92-d32140abd958}\droidcam.inf C:\Windows\System32\DriverStore\Temp\{767da9d4-50e8-7b9d-6e92-d32140abd958}\droidcam.cat | C:\Windows\system32\rundll32.exe | — | DrvInst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2428 | rundll32.exe C:\Windows\system32\pnpui.dll,InstallSecurityPromptRunDllW 20 Global\{42205803-dea7-11a8-6d01-7f30fe269e31} Global\{6dfaf50b-6030-3eb4-8168-0034aaa6f857} C:\Windows\System32\DriverStore\Temp\{427c4e9a-4e4e-2c5a-9acf-66428c7f5325}\droidcamvideo.inf C:\Windows\System32\DriverStore\Temp\{427c4e9a-4e4e-2c5a-9acf-66428c7f5325}\droidcamvideo.cat | C:\Windows\system32\rundll32.exe | — | DrvInst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2456 | "C:\Users\admin\AppData\Local\Temp\DroidCam.Setup.6.3.2.exe" | C:\Users\admin\AppData\Local\Temp\DroidCam.Setup.6.3.2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2584 | "C:\Program Files\DroidCam\lib\insdrv.exe" +a | C:\Program Files\DroidCam\lib\insdrv.exe | ns3F74.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2624 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2688 | "C:\Users\admin\AppData\Local\Temp\nsg9297.tmp\nsDB0B.tmp" "C:\Program Files\DroidCam\lib\insdrv.exe" +v | C:\Users\admin\AppData\Local\Temp\nsg9297.tmp\nsDB0B.tmp | — | DroidCam.Setup.6.3.2.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
1 332
Read events
672
Write events
641
Delete events
19
Modification events
| (PID) Process: | (2456) DroidCam.Setup.6.3.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\DroidCam |
| Operation: | write | Name: | (default) |
Value: C:\Program Files\DroidCam | |||
| (PID) Process: | (2456) DroidCam.Setup.6.3.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\DroidCam |
| Operation: | write | Name: | Version |
Value: 6.3.2 | |||
| (PID) Process: | (2456) DroidCam.Setup.6.3.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{9E2FBAC0-C951-4AA8-BFA9-4B196644964C} |
| Operation: | write | Name: | (default) |
Value: DroidCam Source 2 | |||
| (PID) Process: | (2456) DroidCam.Setup.6.3.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{9E2FBAC0-C951-4AA8-BFA9-4B196644964C}\InprocServer32 |
| Operation: | write | Name: | (default) |
Value: C:\Program Files\DroidCam\lib\DroidCamFilter32.ax | |||
| (PID) Process: | (2456) DroidCam.Setup.6.3.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{9E2FBAC0-C951-4AA8-BFA9-4B196644964C}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (2456) DroidCam.Setup.6.3.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{860BB310-5D01-11d0-BD3B-00A0C911CE86}\Instance\{9E2FBAC0-C951-4AA8-BFA9-4B196644964C} |
| Operation: | write | Name: | FriendlyName |
Value: DroidCam Source 2 | |||
| (PID) Process: | (2456) DroidCam.Setup.6.3.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{860BB310-5D01-11d0-BD3B-00A0C911CE86}\Instance\{9E2FBAC0-C951-4AA8-BFA9-4B196644964C} |
| Operation: | write | Name: | CLSID |
Value: {9E2FBAC0-C951-4AA8-BFA9-4B196644964C} | |||
| (PID) Process: | (2456) DroidCam.Setup.6.3.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{860BB310-5D01-11d0-BD3B-00A0C911CE86}\Instance\{9E2FBAC0-C951-4AA8-BFA9-4B196644964C} |
| Operation: | write | Name: | FilterData |
Value: 02000000000060000100000000000000307069330800000000000000010000000000000000000000307479330000000038000000480000007669647300001000800000AA00389B7100000000000000000000000000000000 | |||
| (PID) Process: | (2456) DroidCam.Setup.6.3.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{860BB310-5D01-11d0-BD3B-00A0C911CE86}\Instance\{9E2FBAC0-C951-4AA8-BFA9-4B196644964C} |
| Operation: | write | Name: | DevicePath |
Value: droidcam:2 | |||
| (PID) Process: | (3112) insdrv.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.app.log |
Value: 4096 | |||
Executable files
20
Suspicious files
15
Text files
199
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2096 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\wixstdba.dll | — | |
MD5:— | SHA256:— | |||
| 2096 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1028\license.rtf | — | |
MD5:— | SHA256:— | |||
| 2096 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1029\license.rtf | — | |
MD5:— | SHA256:— | |||
| 2096 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1031\license.rtf | — | |
MD5:— | SHA256:— | |||
| 2096 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1036\license.rtf | — | |
MD5:— | SHA256:— | |||
| 2096 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1040\license.rtf | — | |
MD5:— | SHA256:— | |||
| 2096 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1041\license.rtf | — | |
MD5:— | SHA256:— | |||
| 2096 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1042\license.rtf | — | |
MD5:— | SHA256:— | |||
| 2096 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1045\license.rtf | — | |
MD5:— | SHA256:— | |||
| 2096 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1046\license.rtf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report