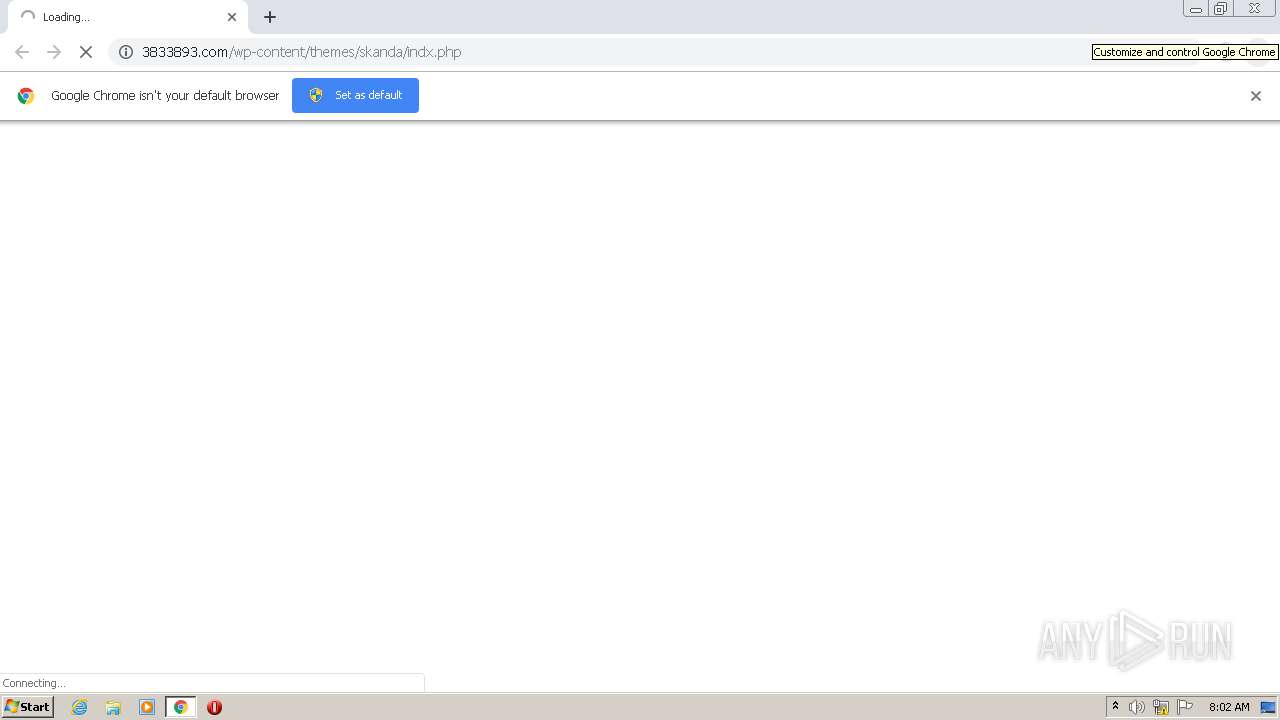
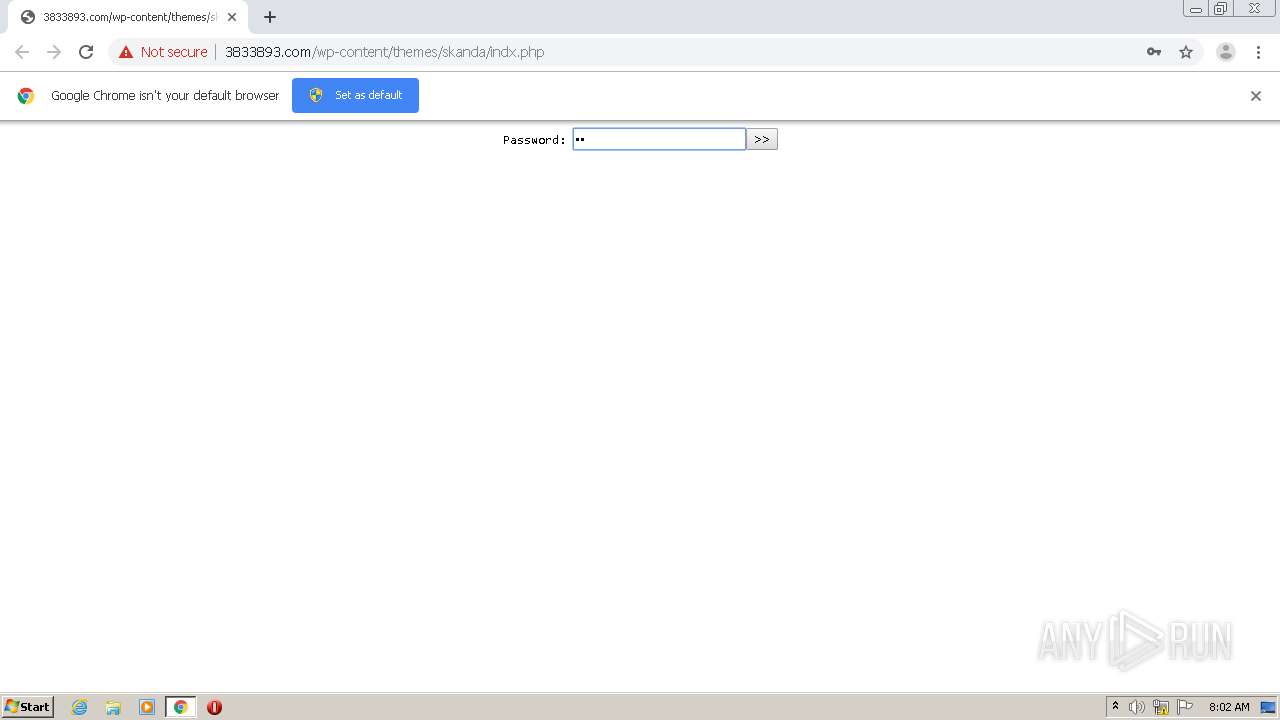
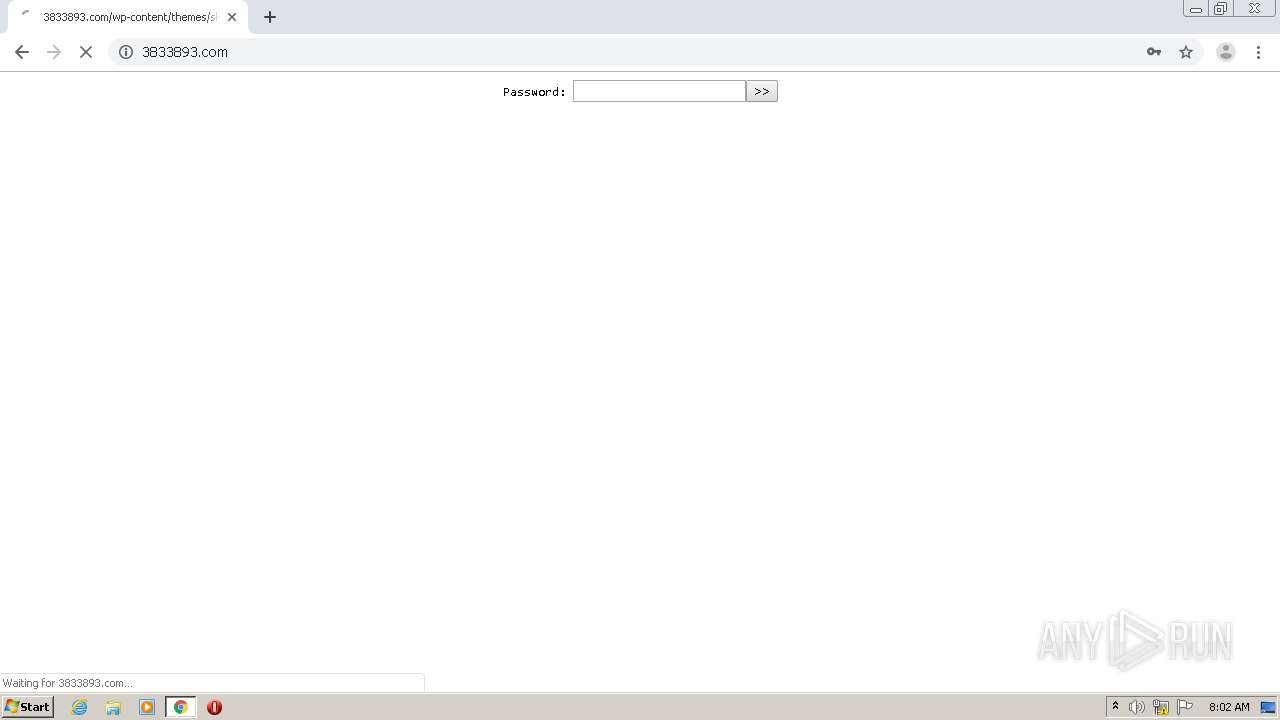
| URL: | http://3833893.com/wp-content/themes/skanda/indx.php |
| Full analysis: | https://app.any.run/tasks/b2128d0e-dae6-44d7-8a1f-ff0d3355c567 |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 07:01:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C1E611010BAE05F782E953735418311D |
| SHA1: | 044B7664120F00A674E16733F77E2FF25516C01E |
| SHA256: | BE3264AF7F337470BA05548D92171E1EAB0E839C8A4EEA9FFE9E3153F0F6A524 |
| SSDEEP: | 3:N1KPWacHK2OlAQrFciEX1bH:CgHK2OlAkF0X1bH |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2724)
Reads the hosts file
- chrome.exe (PID: 2724)
- chrome.exe (PID: 3972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
15
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,17089365209320955749,10863728008648371911,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17285570685471880330 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2688 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,17089365209320955749,10863728008648371911,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15362320055842179518 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2504 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,17089365209320955749,10863728008648371911,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7985219319707156117 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1844 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,17089365209320955749,10863728008648371911,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14388450475682457981 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2216 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,17089365209320955749,10863728008648371911,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14488894244192317903 --mojo-platform-channel-handle=3556 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6c57a9d0,0x6c57a9e0,0x6c57a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://3833893.com/wp-content/themes/skanda/indx.php" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,17089365209320955749,10863728008648371911,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=8035384091287851392 --mojo-platform-channel-handle=3552 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,17089365209320955749,10863728008648371911,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5382076398770528833 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3556 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
596
Read events
521
Write events
71
Delete events
4
Modification events
| (PID) Process: | (2724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2104) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2724-13247650934466375 |
Value: 259 | |||
| (PID) Process: | (2724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2724) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
24
Text files
74
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8E8B77-AA4.pma | — | |
MD5:— | SHA256:— | |||
| 2724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF2d4192.TMP | text | |
MD5:— | SHA256:— | |||
| 2724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF2d4192.TMP | text | |
MD5:— | SHA256:— | |||
| 2724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF2d41ff.TMP | text | |
MD5:— | SHA256:— | |||
| 2724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF2d41a1.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
63
TCP/UDP connections
32
DNS requests
25
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
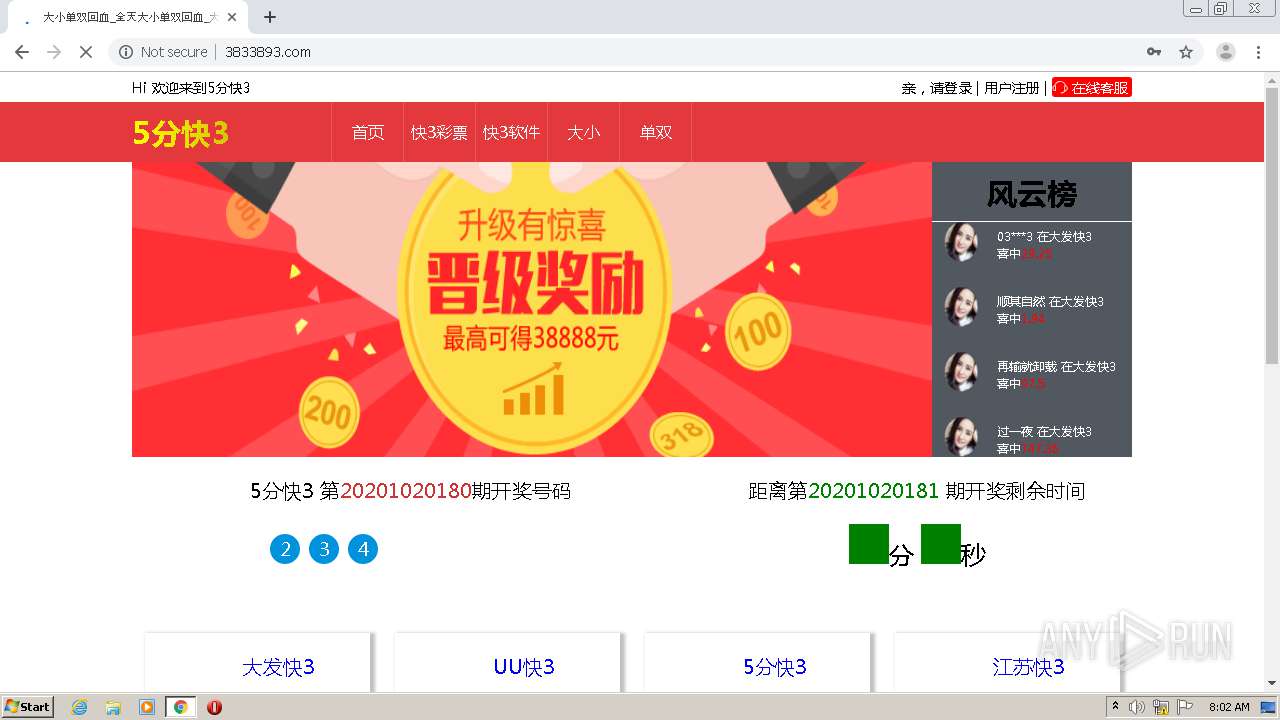
3972 | chrome.exe | GET | 200 | 154.216.29.104:80 | http://3833893.com/images/b1.png | US | image | 45.5 Kb | suspicious |
3972 | chrome.exe | GET | 200 | 154.216.29.104:80 | http://3833893.com/images/more.png | US | image | 164 b | suspicious |
3972 | chrome.exe | GET | 200 | 154.216.29.104:80 | http://3833893.com/js/rem.js | US | text | 663 b | suspicious |
3972 | chrome.exe | GET | 200 | 154.216.29.104:80 | http://3833893.com/images/b_01.jpg | US | image | 135 Kb | suspicious |
3972 | chrome.exe | GET | 200 | 154.216.29.104:80 | http://3833893.com/a/js.js | US | html | 369 b | suspicious |
3972 | chrome.exe | GET | 200 | 154.216.29.104:80 | http://3833893.com/images/n_06.jpg | US | image | 3.60 Kb | suspicious |
3972 | chrome.exe | GET | 200 | 154.216.29.104:80 | http://3833893.com/images/k_03.jpg | US | image | 8.68 Kb | suspicious |
3972 | chrome.exe | GET | 200 | 154.216.29.104:80 | http://3833893.com/css/k3style.css | US | text | 14.0 Kb | suspicious |
3972 | chrome.exe | GET | 200 | 154.216.29.104:80 | http://3833893.com/js/slides.min.jquery.js | US | text | 6.73 Kb | suspicious |
3972 | chrome.exe | GET | 200 | 154.216.29.104:80 | http://3833893.com/images/ke.png | US | image | 355 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
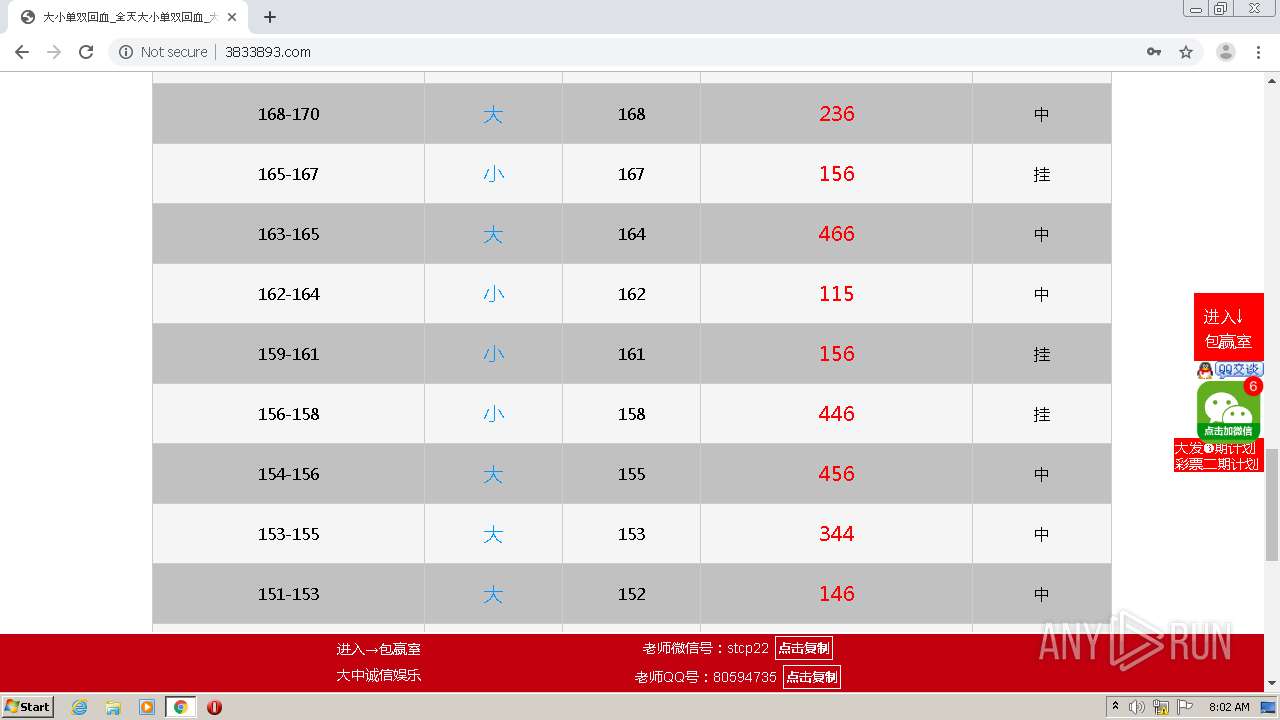
3972 | chrome.exe | 154.216.29.104:80 | 3833893.com | MULTACOM CORPORATION | US | suspicious |
3972 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
3972 | chrome.exe | 216.58.212.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
— | — | 172.217.23.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
3972 | chrome.exe | 122.228.91.87:443 | js.users.51.la | CHINANET Sichuan province Chengdu MAN network | CN | malicious |
3972 | chrome.exe | 183.131.207.66:80 | ia.51.la | DaLi | CN | malicious |
— | — | 61.147.67.184:80 | count17.51yes.com | No.31,Jin-rong Street | CN | unknown |
3972 | chrome.exe | 157.185.189.159:80 | pixel-insight.ucweb.com | — | US | unknown |
— | — | 111.206.37.189:80 | push.zhanzhang.baidu.com | China Unicom Beijing Province Network | CN | malicious |
3972 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
3833893.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
count17.51yes.com |
| unknown |
www.ifengjx.com |
| unknown |
www.ha03333.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3972 | chrome.exe | Web Application Attack | ET WEB_CLIENT Generic WSO Webshell Password Prompt Accessed on External Compromised Server |
3972 | chrome.exe | Web Application Attack | ET WEB_CLIENT Generic Webshell Password Prompt Accessed on External Compromised Server |
3972 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY HTTP POST contains pass= in cleartext |
3972 | chrome.exe | Web Application Attack | ET WEB_CLIENT Generic WSO Webshell Password Prompt Accessed on External Compromised Server |
3972 | chrome.exe | Web Application Attack | ET WEB_CLIENT Generic Webshell Password Prompt Accessed on External Compromised Server |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |