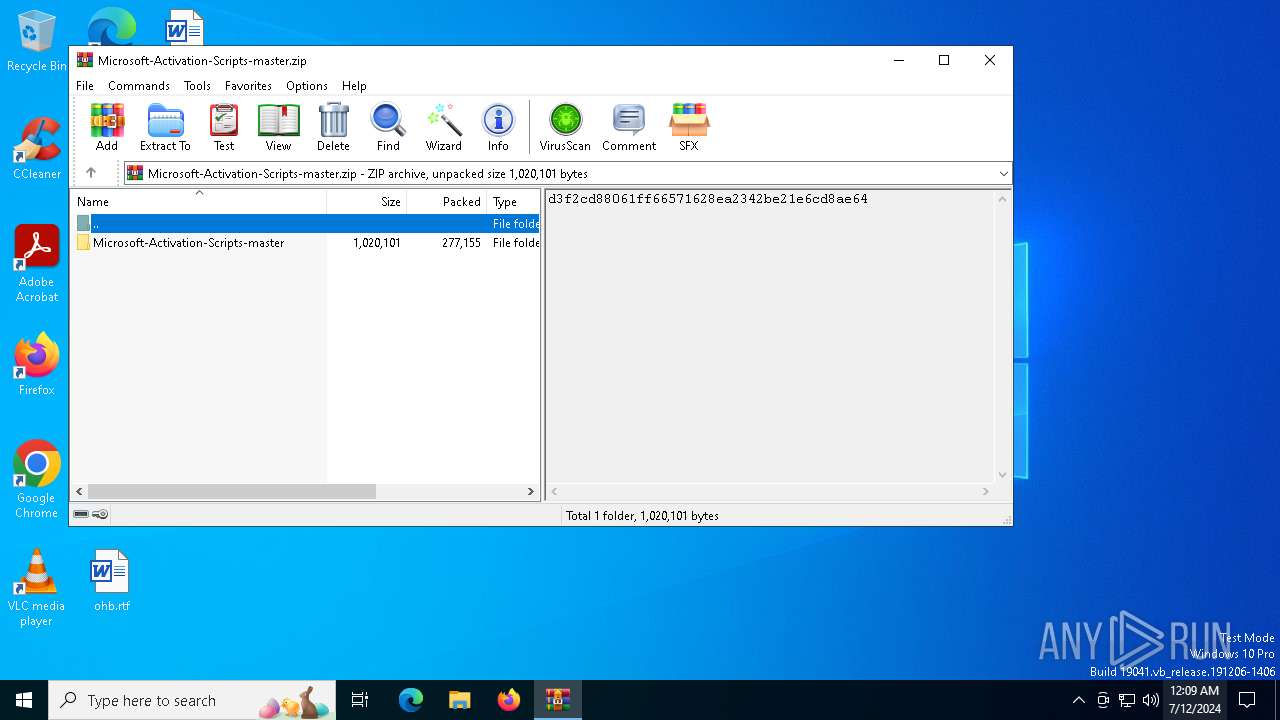
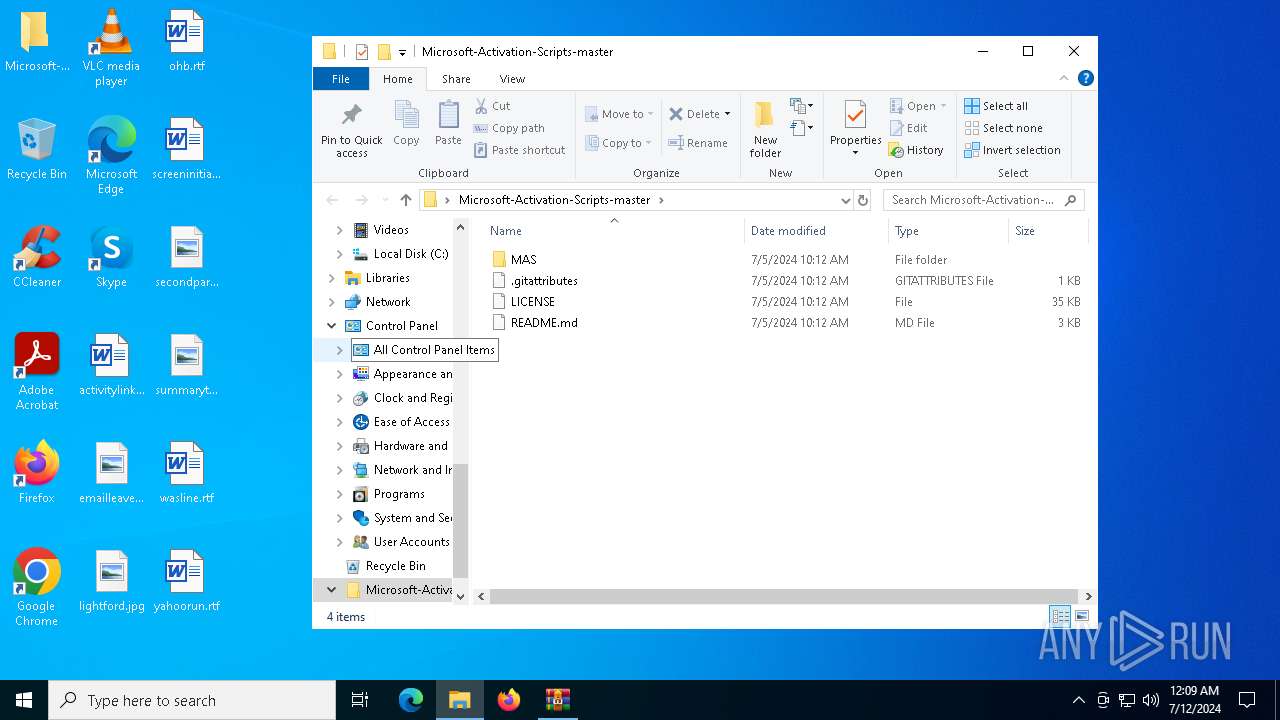
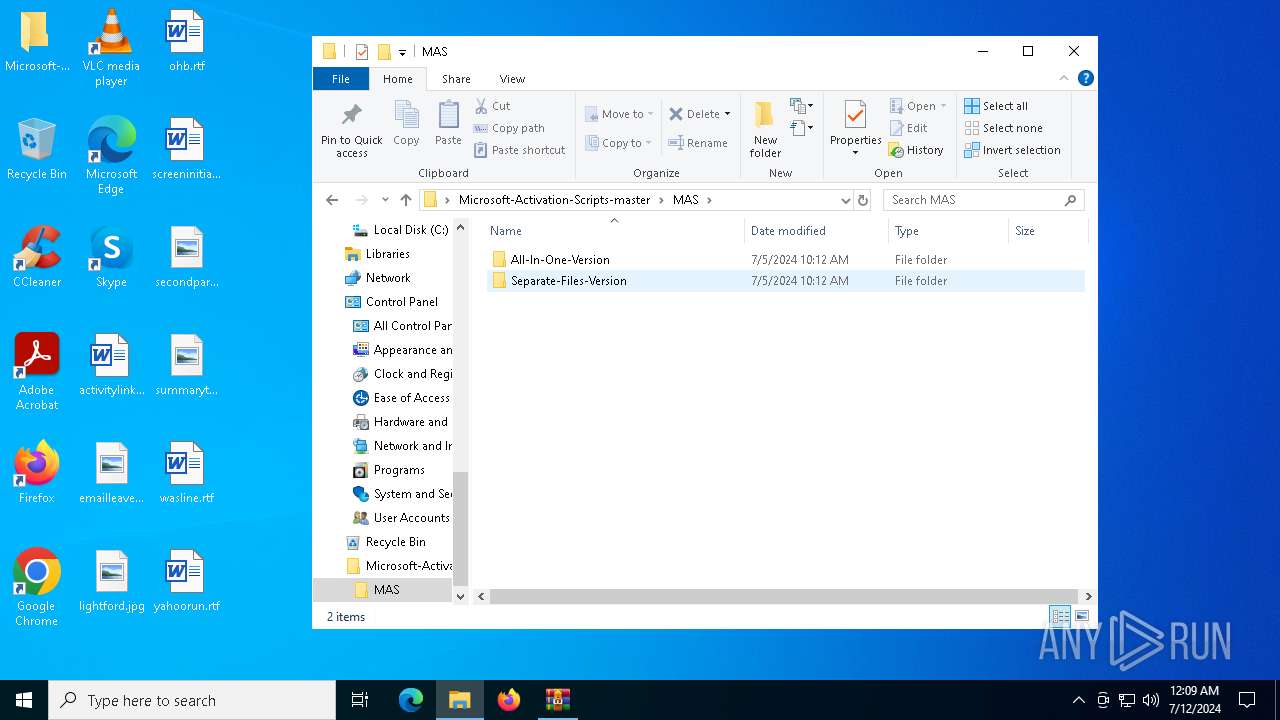
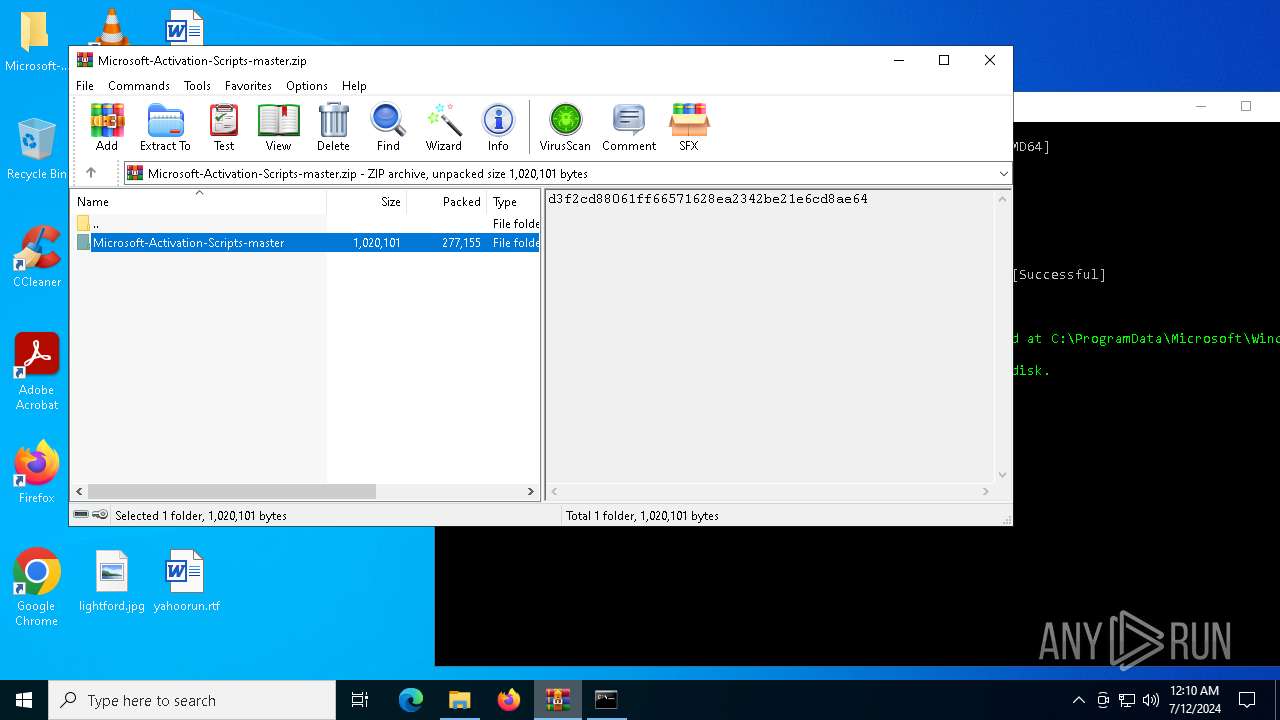
| File name: | Microsoft-Activation-Scripts-master.zip |
| Full analysis: | https://app.any.run/tasks/4c43f14b-d067-4fd4-a1f1-b7701756567f |
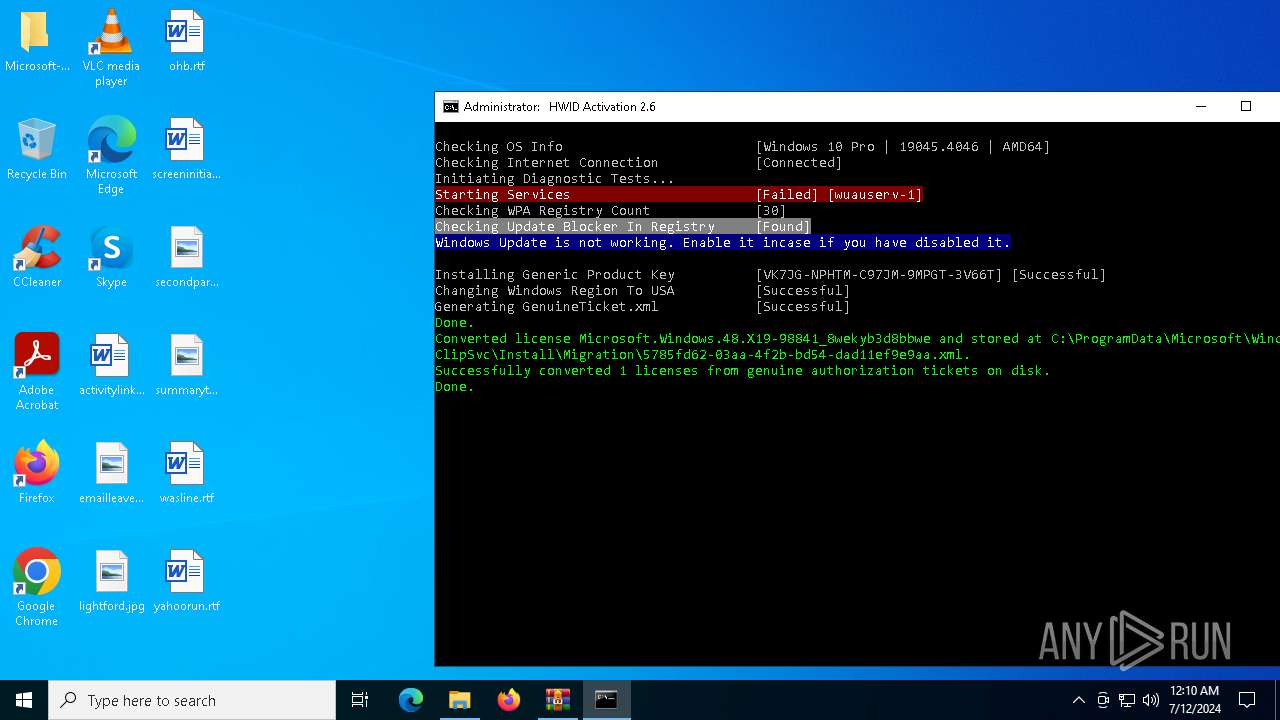
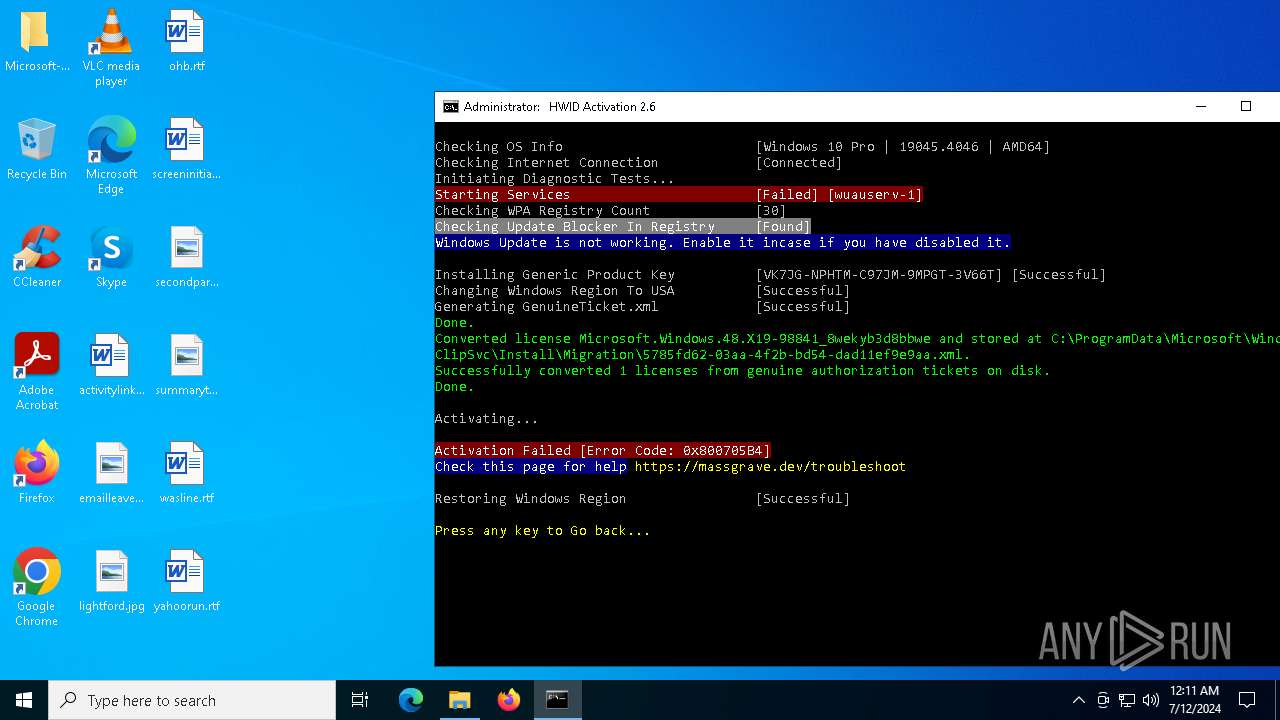
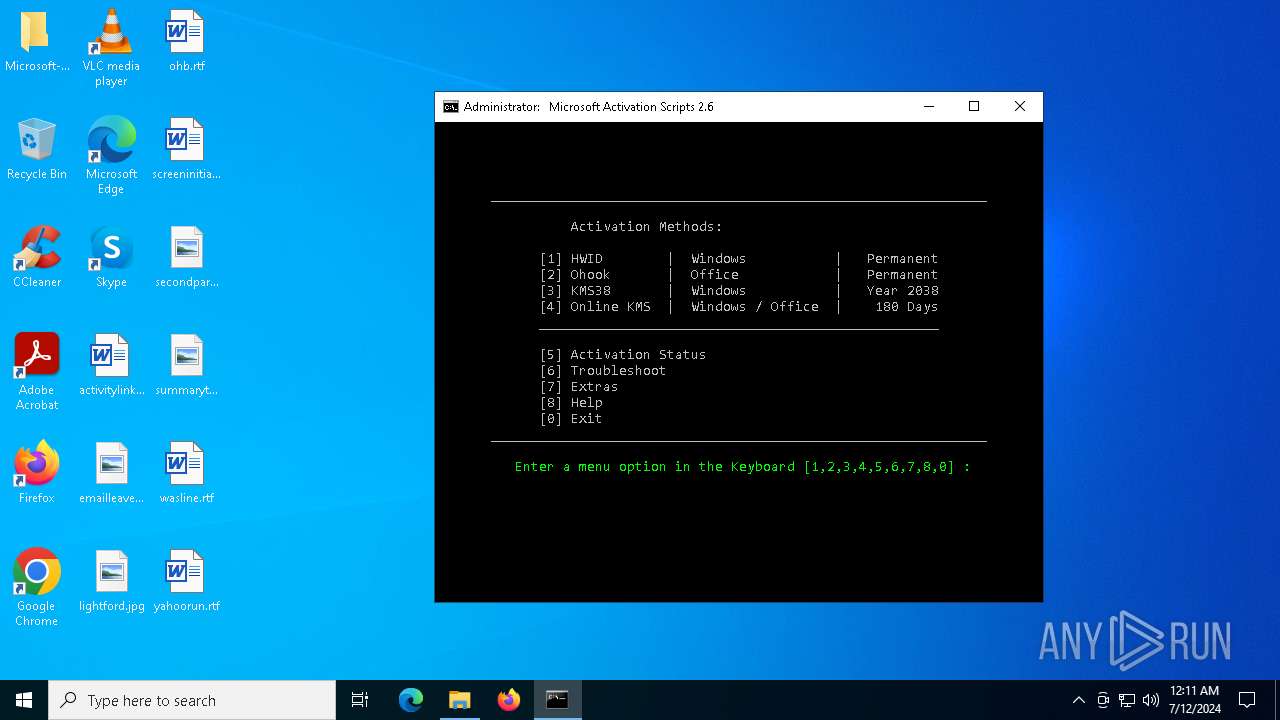
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2024, 00:09:00 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | EEDCF0DD0452BBBFB728435CBEC08F31 |
| SHA1: | F0547D59FDFE97345BCF212CF108D21F258173CB |
| SHA256: | BE2B14D6C100A6A873594A7ECA14189F992A5D5FC03DFBAC80124E7397E772CD |
| SSDEEP: | 12288:FauHgj9QU74jV6YbDOcSgChEexkMvziaZOnA74rBa:F9H/u8V6ODOcSg2Ee2MriaZOnA74U |
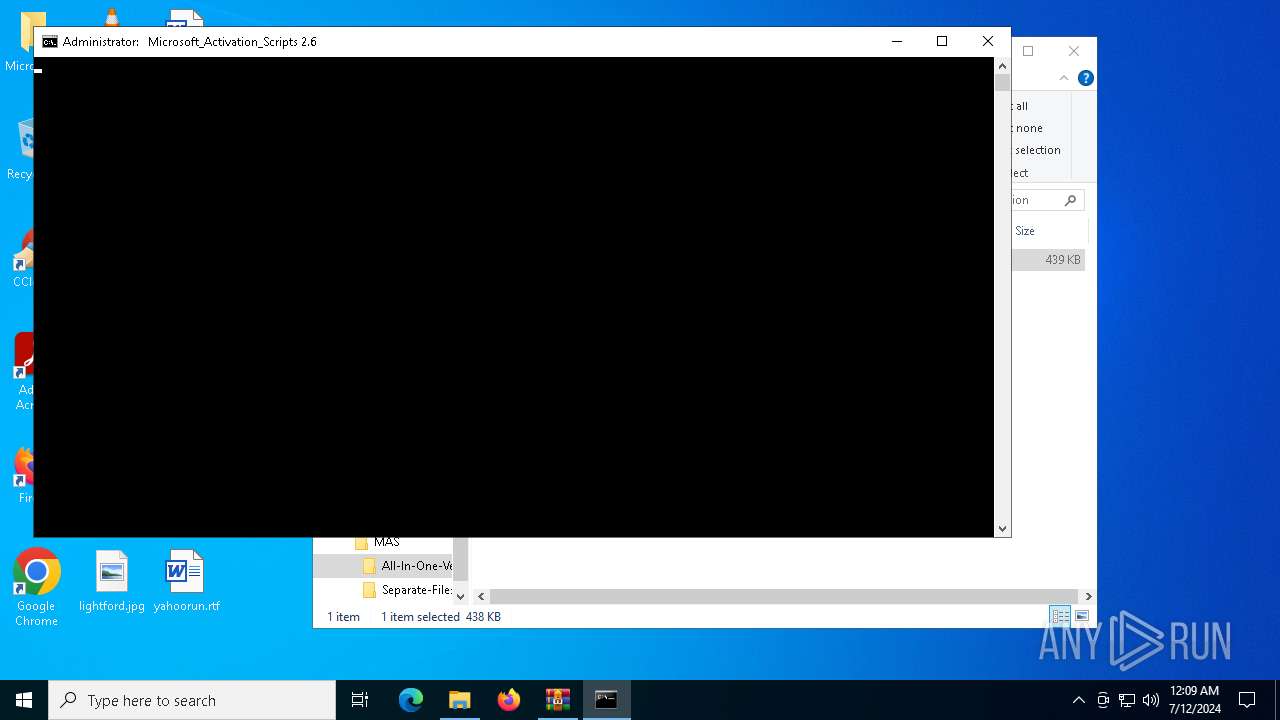
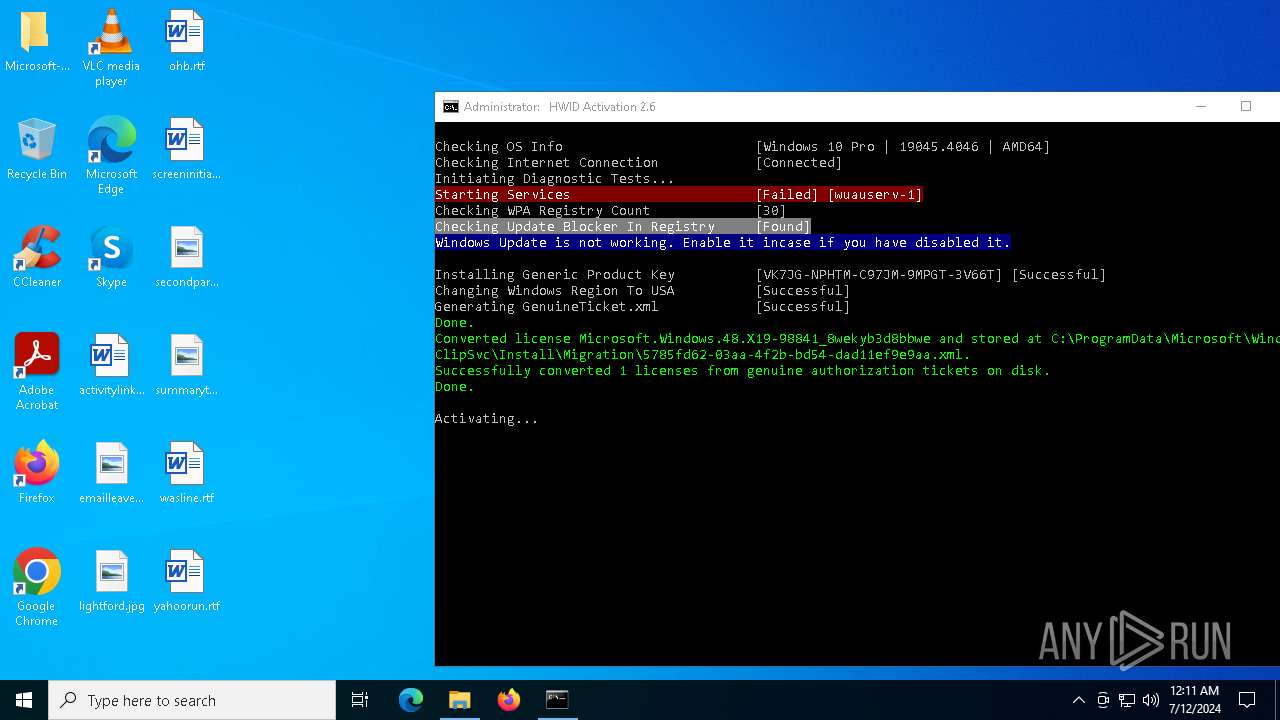
MALICIOUS
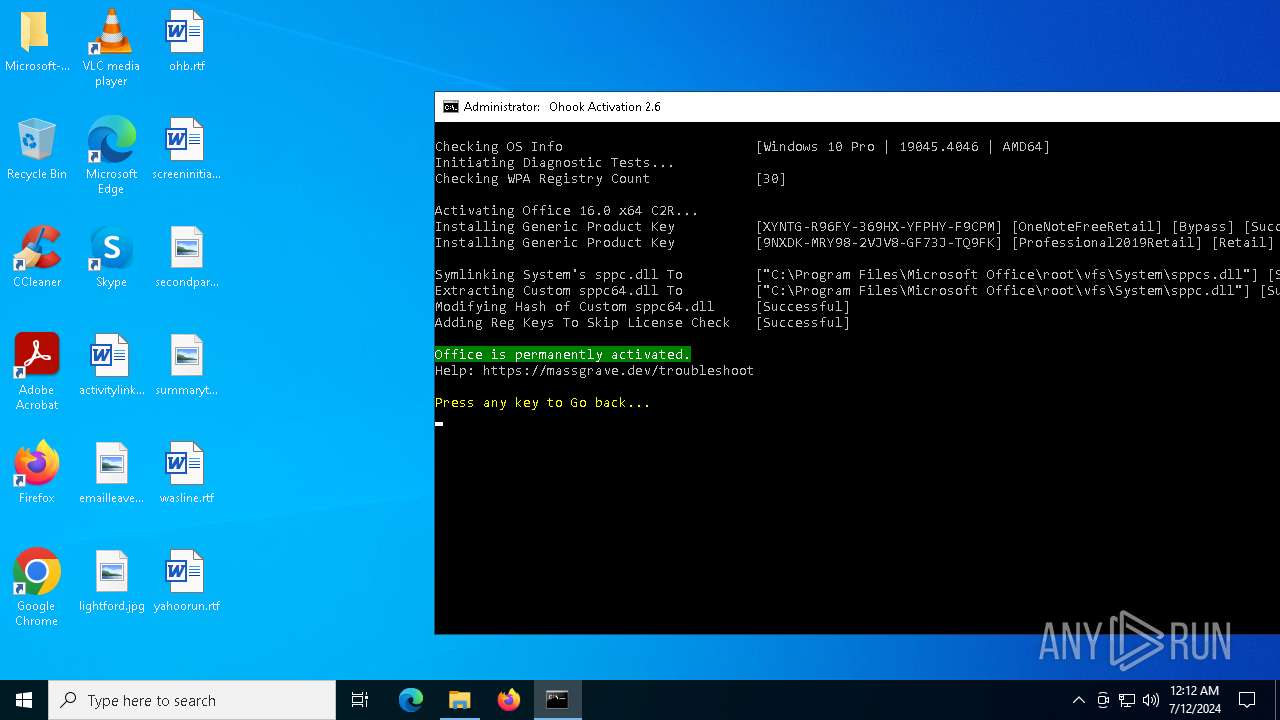
Drops the executable file immediately after the start
- powershell.exe (PID: 3868)
SUSPICIOUS
Starts SC.EXE for service management
- cmd.exe (PID: 7068)
- cmd.exe (PID: 6432)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7068)
- cmd.exe (PID: 6432)
- cmd.exe (PID: 6876)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7068)
- cmd.exe (PID: 6432)
- cmd.exe (PID: 6876)
Application launched itself
- cmd.exe (PID: 2140)
- cmd.exe (PID: 7068)
- cmd.exe (PID: 6444)
- cmd.exe (PID: 6320)
- cmd.exe (PID: 6432)
- ClipUp.exe (PID: 5248)
- cmd.exe (PID: 528)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7068)
- cmd.exe (PID: 2140)
- cmd.exe (PID: 6444)
- cmd.exe (PID: 6320)
- cmd.exe (PID: 6432)
- cmd.exe (PID: 528)
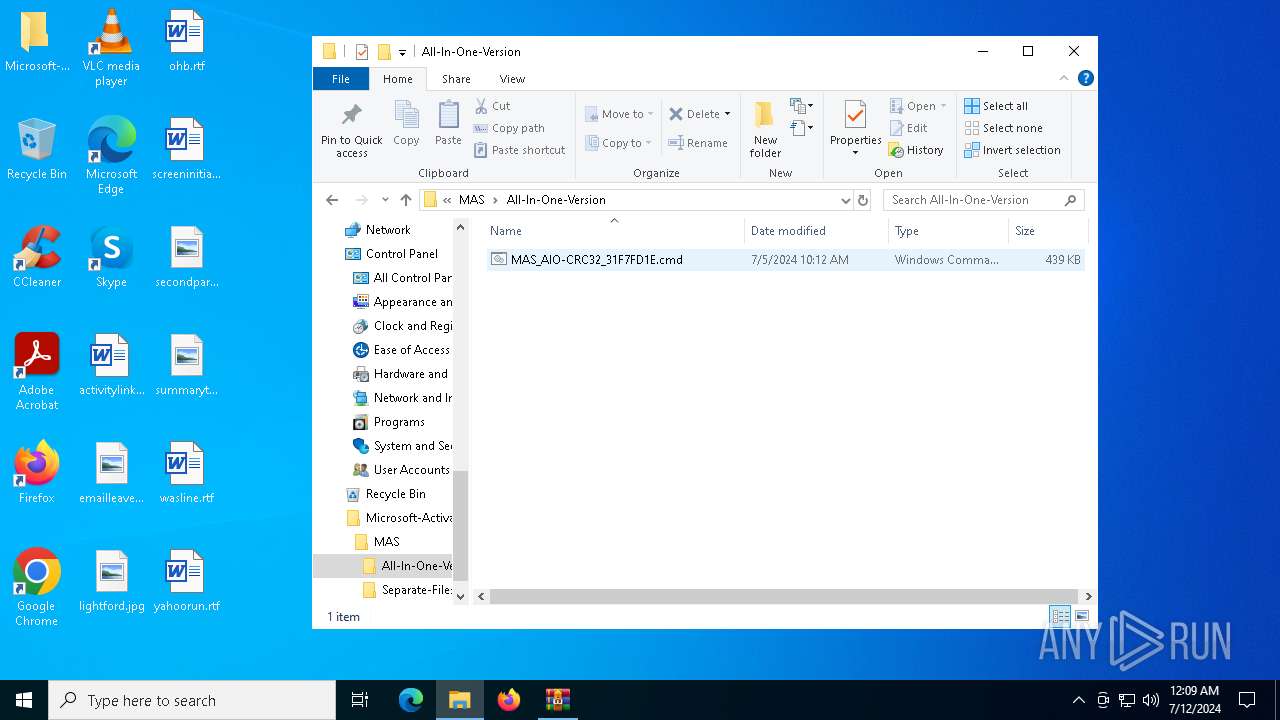
Executing commands from ".cmd" file
- cmd.exe (PID: 7068)
- cmd.exe (PID: 6432)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 6432)
- cmd.exe (PID: 6288)
- cmd.exe (PID: 6960)
- cmd.exe (PID: 6068)
- cmd.exe (PID: 1092)
Hides command output
- cmd.exe (PID: 4840)
- cmd.exe (PID: 1132)
- cmd.exe (PID: 7160)
- cmd.exe (PID: 2516)
- cmd.exe (PID: 6288)
- cmd.exe (PID: 1848)
- cmd.exe (PID: 3808)
- cmd.exe (PID: 3584)
- cmd.exe (PID: 2288)
- cmd.exe (PID: 6776)
- cmd.exe (PID: 3156)
- cmd.exe (PID: 1796)
- cmd.exe (PID: 3724)
- cmd.exe (PID: 6960)
- cmd.exe (PID: 1236)
- cmd.exe (PID: 2824)
- cmd.exe (PID: 7148)
- cmd.exe (PID: 3668)
- cmd.exe (PID: 6876)
- cmd.exe (PID: 6224)
- cmd.exe (PID: 4172)
- cmd.exe (PID: 6100)
- cmd.exe (PID: 5480)
- cmd.exe (PID: 5652)
- cmd.exe (PID: 5280)
- cmd.exe (PID: 6068)
- cmd.exe (PID: 7112)
- cmd.exe (PID: 6544)
- cmd.exe (PID: 1092)
- cmd.exe (PID: 876)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 1132)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 1192)
- powershell.exe (PID: 4752)
- powershell.exe (PID: 3868)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 7160)
- cmd.exe (PID: 6776)
- cmd.exe (PID: 6432)
- cmd.exe (PID: 876)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 7160)
- cmd.exe (PID: 6776)
- cmd.exe (PID: 6432)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7160)
- cmd.exe (PID: 6292)
- cmd.exe (PID: 6432)
- cmd.exe (PID: 5300)
- cmd.exe (PID: 6688)
- cmd.exe (PID: 5300)
- cmd.exe (PID: 4136)
- cmd.exe (PID: 6776)
- cmd.exe (PID: 876)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 6856)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 6432)
Process drops legitimate windows executable
- Dism.exe (PID: 3748)
- Dism.exe (PID: 7100)
The process creates files with name similar to system file names
- Dism.exe (PID: 3748)
- Dism.exe (PID: 7100)
The process executes VB scripts
- cmd.exe (PID: 6432)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- cscript.exe (PID: 6380)
- cscript.exe (PID: 6452)
- cscript.exe (PID: 4452)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 1192)
- powershell.exe (PID: 6172)
- powershell.exe (PID: 4752)
- powershell.exe (PID: 3868)
Executable content was dropped or overwritten
- Dism.exe (PID: 3748)
- Dism.exe (PID: 7100)
- powershell.exe (PID: 3868)
Starts a Microsoft application from unusual location
- DismHost.exe (PID: 6932)
- DismHost.exe (PID: 2112)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 6432)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 6432)
Gets full path of the running script (SCRIPT)
- cscript.exe (PID: 6380)
- cscript.exe (PID: 6452)
- cscript.exe (PID: 4452)
Reads data from a binary Stream object (SCRIPT)
- cscript.exe (PID: 6380)
- cscript.exe (PID: 6452)
- cscript.exe (PID: 4452)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 3868)
INFO
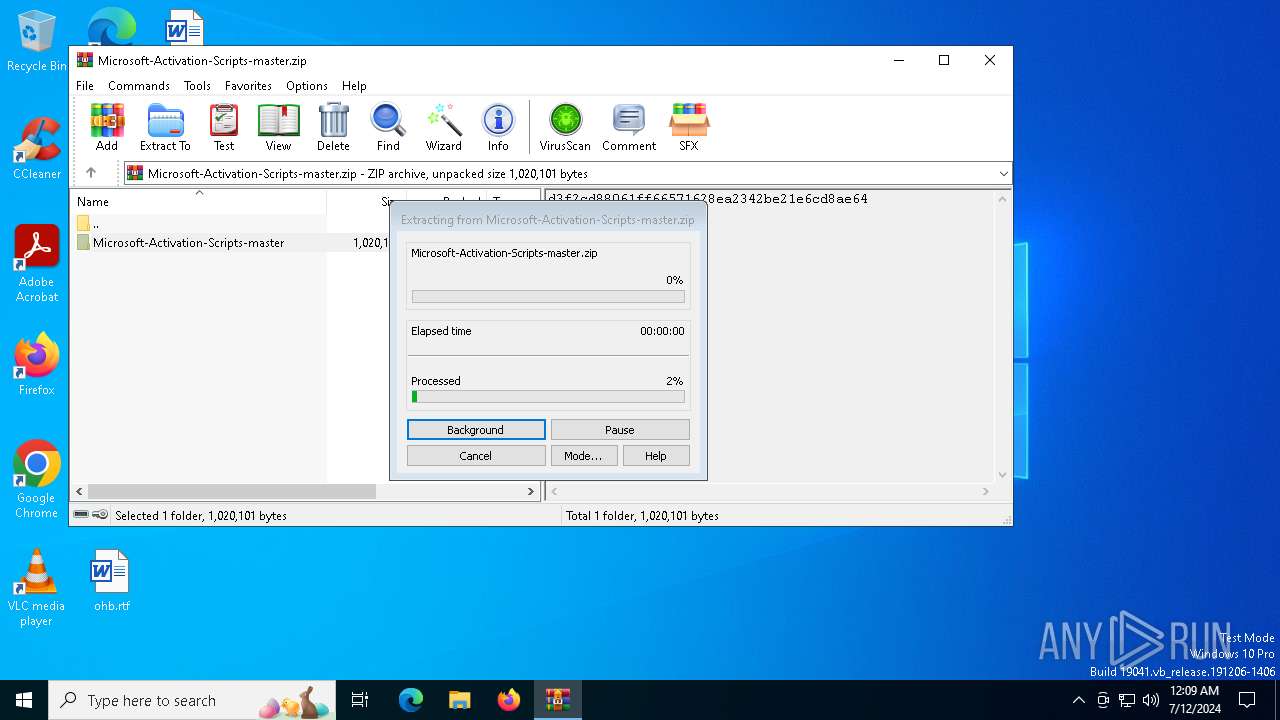
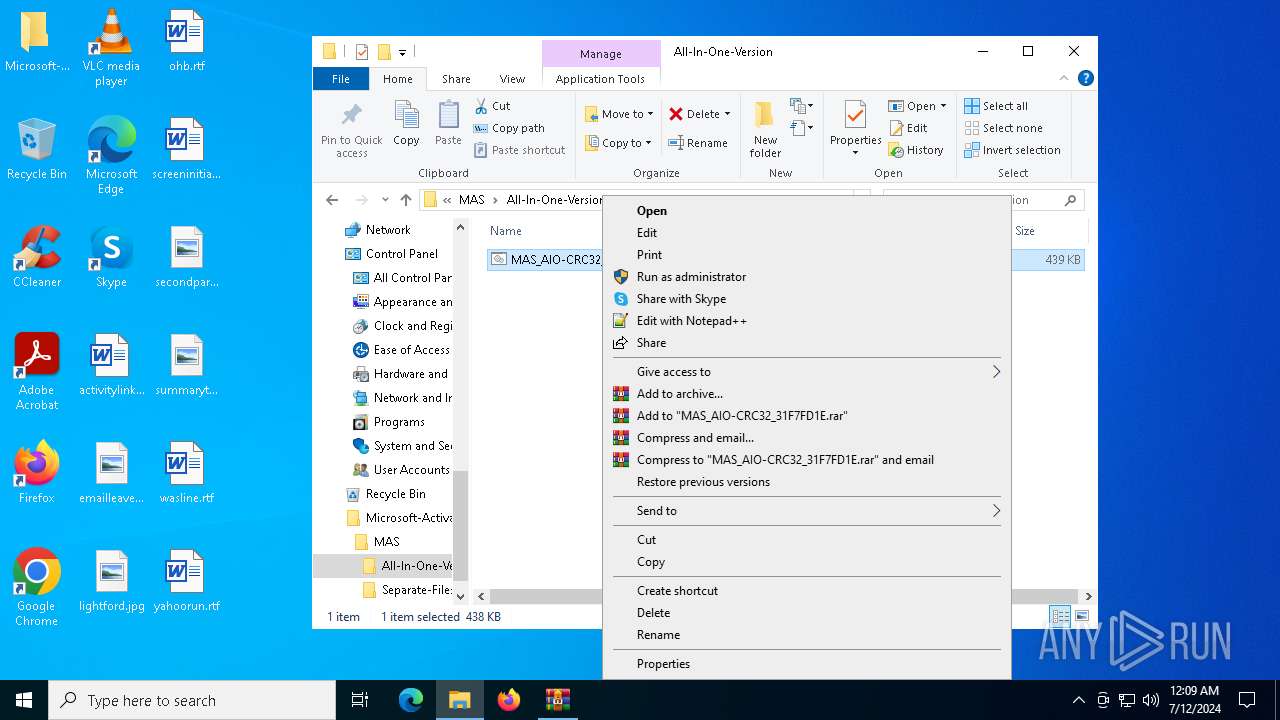
Manual execution by a user
- cmd.exe (PID: 7068)
Checks operating system version
- cmd.exe (PID: 7068)
- cmd.exe (PID: 6432)
Checks supported languages
- mode.com (PID: 6804)
- mode.com (PID: 480)
- DismHost.exe (PID: 6932)
- mode.com (PID: 3972)
- mode.com (PID: 2476)
- mode.com (PID: 6876)
- DismHost.exe (PID: 2112)
- mode.com (PID: 6856)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6636)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 420)
- WMIC.exe (PID: 7064)
- cscript.exe (PID: 6380)
- WMIC.exe (PID: 6024)
- WMIC.exe (PID: 1220)
- WMIC.exe (PID: 4028)
- WMIC.exe (PID: 1060)
- cscript.exe (PID: 6452)
- WMIC.exe (PID: 3584)
- WMIC.exe (PID: 2176)
- WMIC.exe (PID: 6340)
- WMIC.exe (PID: 6160)
- cscript.exe (PID: 4452)
- WMIC.exe (PID: 6256)
- WMIC.exe (PID: 7076)
- WMIC.exe (PID: 6768)
- WMIC.exe (PID: 2120)
- WMIC.exe (PID: 5980)
- WMIC.exe (PID: 7032)
- WMIC.exe (PID: 1304)
- WMIC.exe (PID: 5248)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 1192)
- powershell.exe (PID: 4752)
- powershell.exe (PID: 3868)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 1192)
- powershell.exe (PID: 4752)
- powershell.exe (PID: 3868)
Create files in a temporary directory
- Dism.exe (PID: 3748)
- ClipUp.exe (PID: 1160)
- Dism.exe (PID: 7100)
Reads the computer name
- DismHost.exe (PID: 6932)
- DismHost.exe (PID: 2112)
Drops the executable file immediately after the start
- Dism.exe (PID: 3748)
- Dism.exe (PID: 7100)
Reads Environment values
- DismHost.exe (PID: 6932)
- DismHost.exe (PID: 2112)
Creates files in the program directory
- cmd.exe (PID: 6432)
- ClipUp.exe (PID: 1160)
- powershell.exe (PID: 3868)
Reads Microsoft Office registry keys
- reg.exe (PID: 2364)
- reg.exe (PID: 2448)
- reg.exe (PID: 2828)
- reg.exe (PID: 3780)
- reg.exe (PID: 3884)
- reg.exe (PID: 4752)
- reg.exe (PID: 2120)
- reg.exe (PID: 1648)
- reg.exe (PID: 6220)
- reg.exe (PID: 7088)
- reg.exe (PID: 6152)
- reg.exe (PID: 2008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:07:05 03:12:00 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Microsoft-Activation-Scripts-master/ |
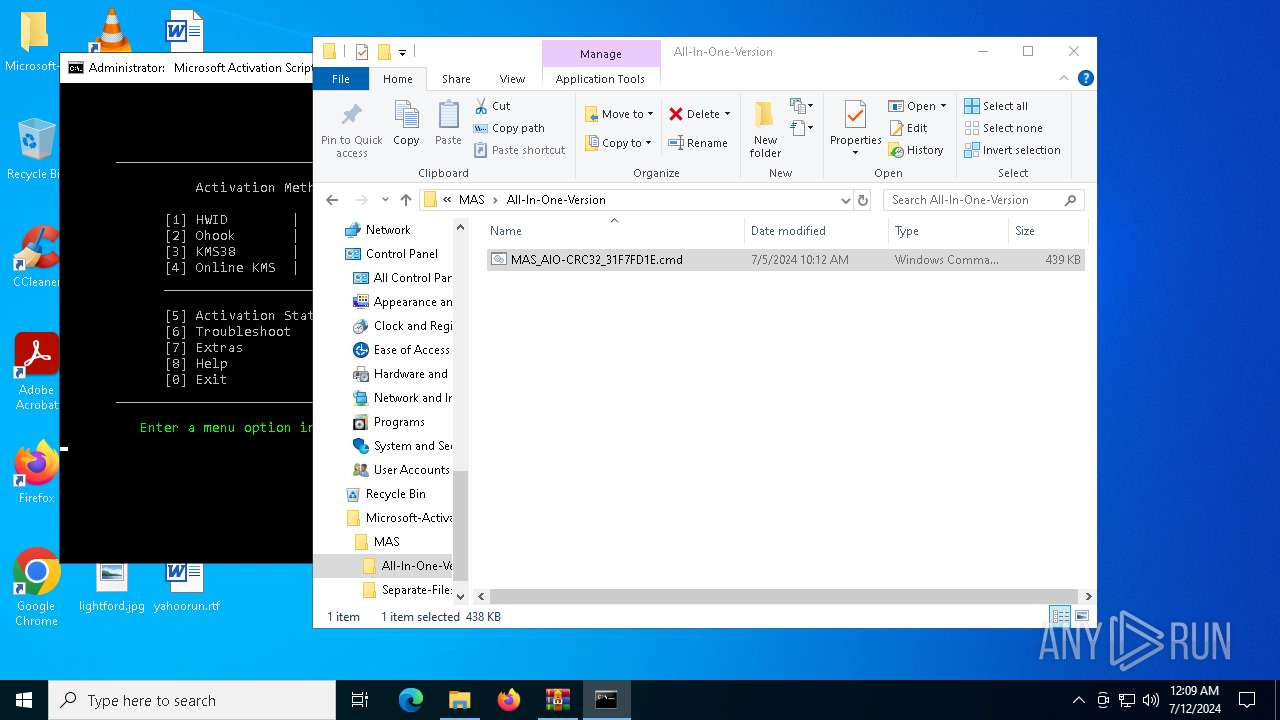
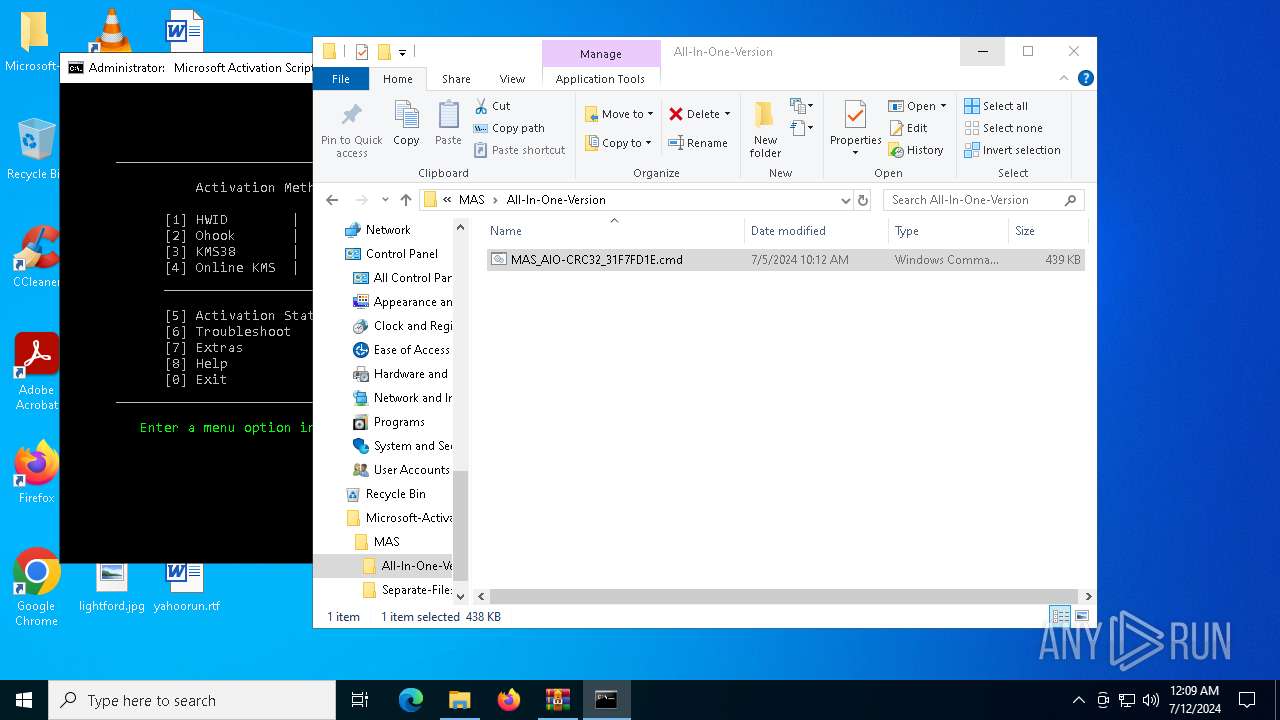
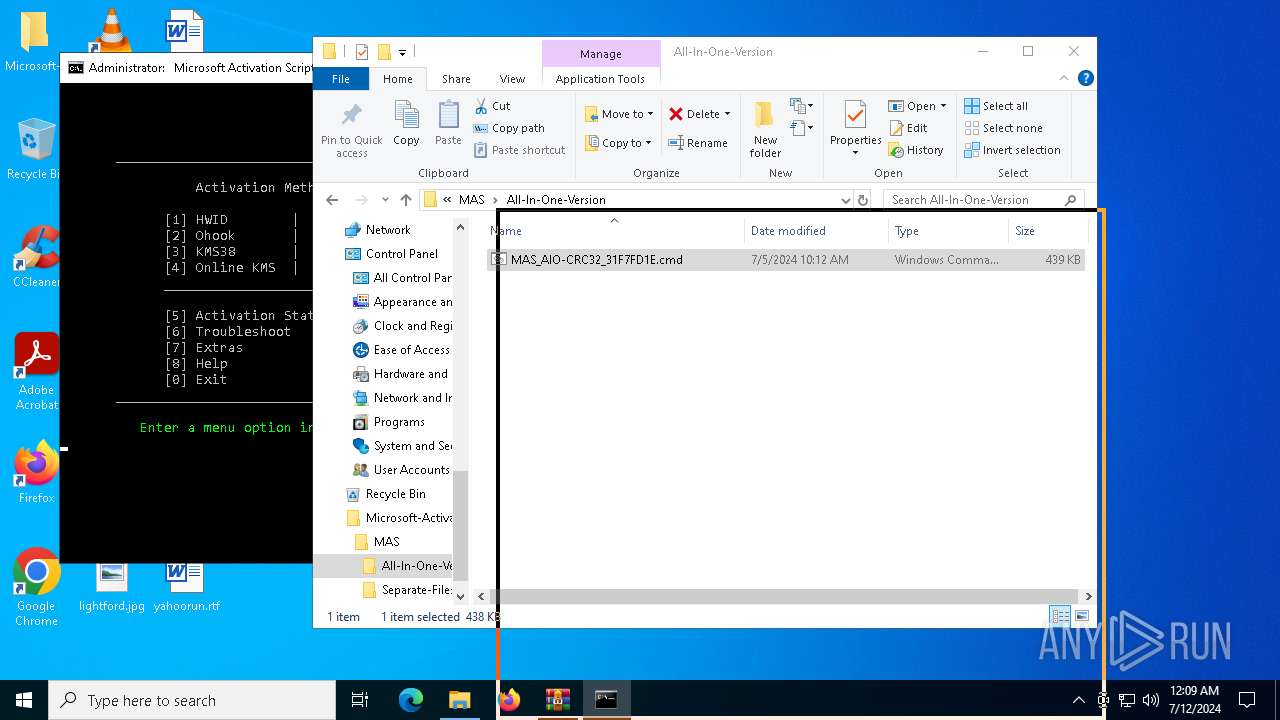
Total processes
693
Monitored processes
536
Malicious processes
8
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | reg query HKLM\SYSTEM\CurrentControlSet\Services\sppsvc /v DisplayName | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 308 | find /i "Error Found" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | wmic Path Win32_OperatingSystem Get OperatingSystemSKU /format:LIST | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | sc start WaaSMedicSvc | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1056 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 436 | reg query HKLM\SYSTEM\CurrentControlSet\Services\TrustedInstaller /v Description | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 448 | sc query sppsvc | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 452 | sc start KeyIso | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1056 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 480 | mode 76, 30 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 480 | reg query HKLM\SYSTEM\CurrentControlSet\Services\TrustedInstaller /v DependOnService | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 524 | reg query HKLM\SYSTEM\CurrentControlSet\Services\Winmgmt /v ImagePath | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
124 409
Read events
124 374
Write events
35
Delete events
0
Modification events
| (PID) Process: | (3152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (3152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Microsoft-Activation-Scripts-master.zip | |||
| (PID) Process: | (3152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (6576) reg.exe | Key: | HKEY_CURRENT_USER\Console |
| Operation: | write | Name: | QuickEdit |
Value: 0 | |||
Executable files
102
Suspicious files
1
Text files
67
Unknown types
0
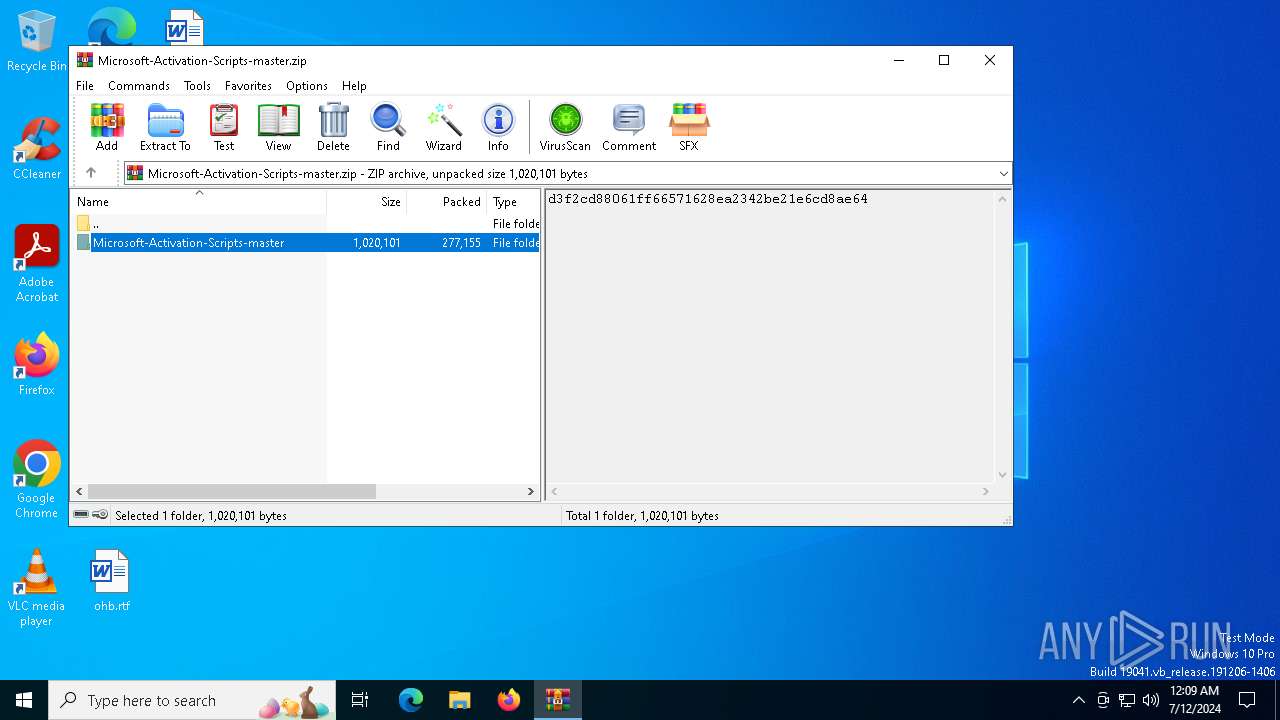
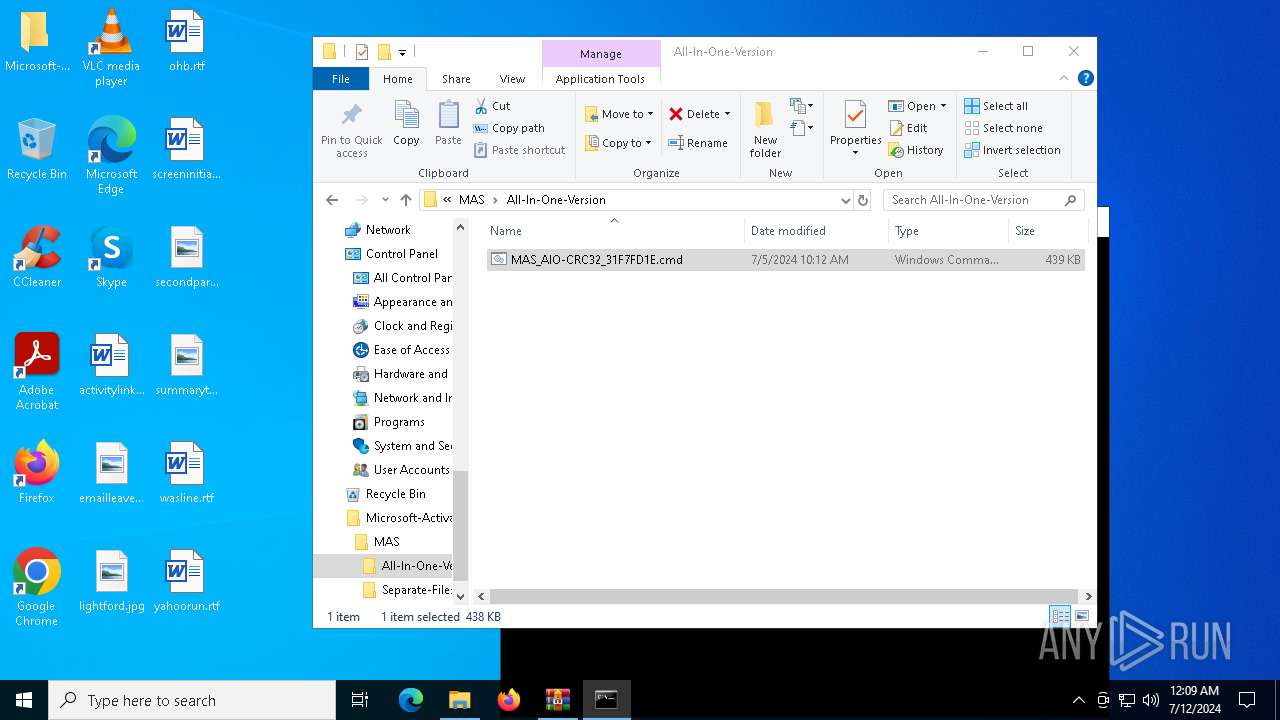
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3152 | WinRAR.exe | C:\Users\admin\Desktop\Microsoft-Activation-Scripts-master\MAS\Separate-Files-Version\Activators\Ohook_Activation_AIO.cmd | text | |
MD5:80E83AD7099009CCBCD5C910340FA9A8 | SHA256:2C968BEC692B144FEF41C6F3798000FCDFC5319774168AB56BF867FFF3F1A9A7 | |||
| 3152 | WinRAR.exe | C:\Users\admin\Desktop\Microsoft-Activation-Scripts-master\MAS\Separate-Files-Version\Activators\KMS38_Activation.cmd | text | |
MD5:421BE375C0E33294CF4E0F75D97AA928 | SHA256:D85D2DAF27AFCF21DBAA1AF528F034009E30BACA8050A1A4D26C8DA7927C95A6 | |||
| 3152 | WinRAR.exe | C:\Users\admin\Desktop\Microsoft-Activation-Scripts-master\MAS\Separate-Files-Version\Activators\HWID_Activation.cmd | text | |
MD5:28312C7DAAFDE6AAC9F829513715C69F | SHA256:00836E3642F9D4E027BBBE8BDB206284E817EE60553FD1340B50C7EEF77DA847 | |||
| 3152 | WinRAR.exe | C:\Users\admin\Desktop\Microsoft-Activation-Scripts-master\MAS\Separate-Files-Version\Change_Edition.cmd | text | |
MD5:D20EA1F7448A12E835E3F40DF0FF9AFA | SHA256:E55544BF48735CD7DF2E891E0B7B809FC96EF2703E0772DD6C232498DAD8B110 | |||
| 3152 | WinRAR.exe | C:\Users\admin\Desktop\Microsoft-Activation-Scripts-master\.gitattributes | text | |
MD5:F9F25F50652FBF7E61039A620BE51FA6 | SHA256:42708C4FE8A9F14722BF6C2BA13BC7218C4E2ECCEB8A87C0FFBBD62D2D7CBB74 | |||
| 3152 | WinRAR.exe | C:\Users\admin\Desktop\Microsoft-Activation-Scripts-master\README.md | html | |
MD5:C5851AFD84CD55556F3E7DF57F991006 | SHA256:77507C9D77F593EE752B1634A5EEF8E4F95F51AB977B1AC4A69374074A46340E | |||
| 3152 | WinRAR.exe | C:\Users\admin\Desktop\Microsoft-Activation-Scripts-master\MAS\Separate-Files-Version\Activators\ReadMe.txt | text | |
MD5:B7FA33165116723BC2F83676FD62CC69 | SHA256:B0218B2723A32157A094EE3B852159B339EC3E01CE25AA05E19B28F55A0E9528 | |||
| 3152 | WinRAR.exe | C:\Users\admin\Desktop\Microsoft-Activation-Scripts-master\MAS\Separate-Files-Version\Troubleshoot.cmd | text | |
MD5:CA4F211BED0FD63236E2CECE5BCA2E0D | SHA256:5DFA0352906231CE8769EEEF1056711C5F5E88770AB21FA44EF1B65D5178422F | |||
| 3152 | WinRAR.exe | C:\Users\admin\Desktop\Microsoft-Activation-Scripts-master\MAS\Separate-Files-Version\Extract_OEM_Folder.cmd | text | |
MD5:B1EC6D1E48D653D74D896910A2763402 | SHA256:CB1EA084614DE7B67177A127505F0864E2CA5BD807B2A578D28CD30957F3FF21 | |||
| 6856 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_oyelhs5r.41l.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
71
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4752 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4752 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6408 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6408 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5600 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
640 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
652 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
3040 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4752 | svchost.exe | 20.211.142.183:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | AU | unknown |
1452 | RUXIMICS.exe | 20.211.142.183:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | AU | unknown |
1776 | MoUsoCoreWorker.exe | 20.211.142.183:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | AU | unknown |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4752 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4752 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
4752 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
4656 | SearchApp.exe | 104.126.37.185:443 | www.bing.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Dism.exe | PID=3748 TID=1920 Instantiating the Provider Store. - CDISMImageSession::get_ProviderStore |
Dism.exe | PID=3748 TID=1920 Initializing a provider store for the LOCAL session type. - CDISMProviderStore::Final_OnConnect |
Dism.exe | PID=3748 TID=1920 Attempting to initialize the logger from the Image Session. - CDISMProviderStore::Final_OnConnect |
Dism.exe | PID=3748 TID=1920 Provider has not previously been encountered. Attempting to initialize the provider. - CDISMProviderStore::Internal_GetProvider |
Dism.exe | PID=3748 TID=1920 Loading Provider from location C:\Windows\System32\Dism\LogProvider.dll - CDISMProviderStore::Internal_GetProvider |
Dism.exe | PID=3748 TID=1920 Connecting to the provider located at C:\Windows\System32\Dism\LogProvider.dll. - CDISMProviderStore::Internal_LoadProvider |
DismHost.exe | PID=6932 TID=6520 Disconnecting the provider store - CDISMImageSession::Final_OnDisconnect |
DismHost.exe | PID=6932 TID=6520 Encountered a loaded provider DISMLogger. - CDISMProviderStore::Internal_DisconnectProvider |
DismHost.exe | PID=6932 TID=6520 Disconnecting Provider: DISMLogger - CDISMProviderStore::Internal_DisconnectProvider |
Dism.exe | PID=3748 TID=1920 Encountered a loaded provider DISMLogger. - CDISMProviderStore::Internal_DisconnectProvider |