| File name: | setup.msi |
| Full analysis: | https://app.any.run/tasks/3f862d71-d14f-4231-9e16-ff7c700eef48 |
| Verdict: | Malicious activity |
| Analysis date: | January 30, 2025, 16:16:03 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
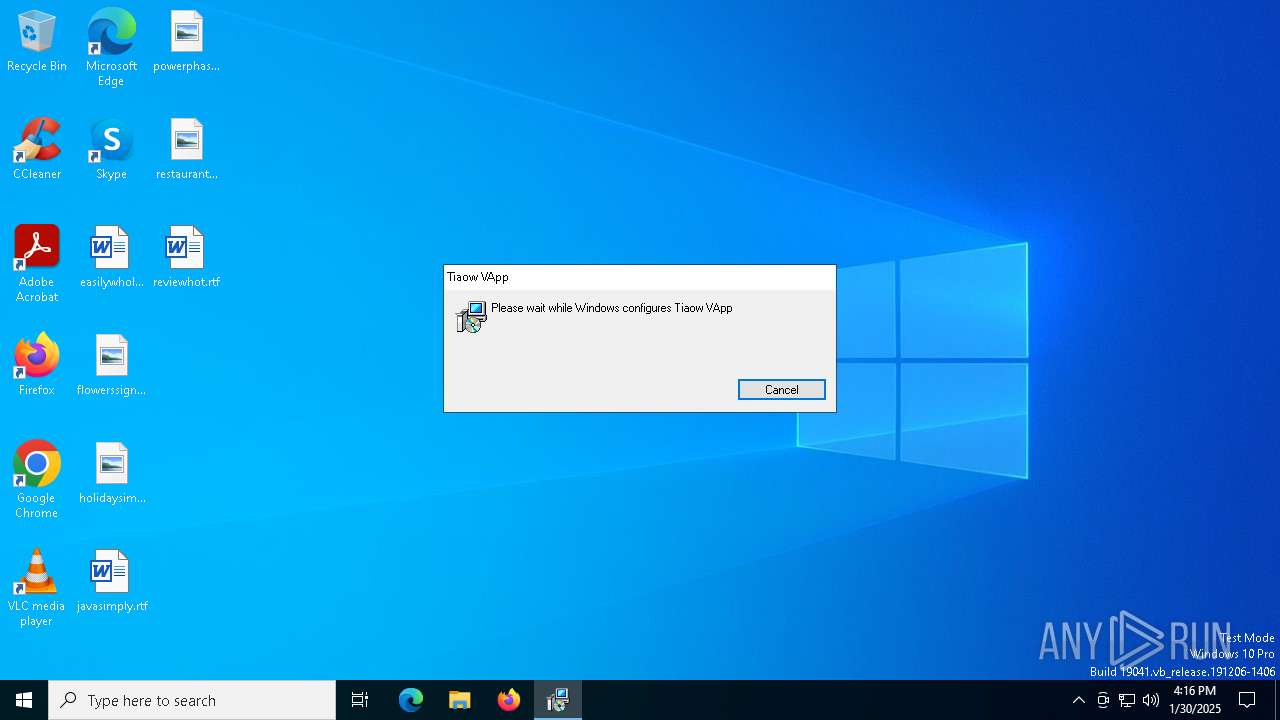
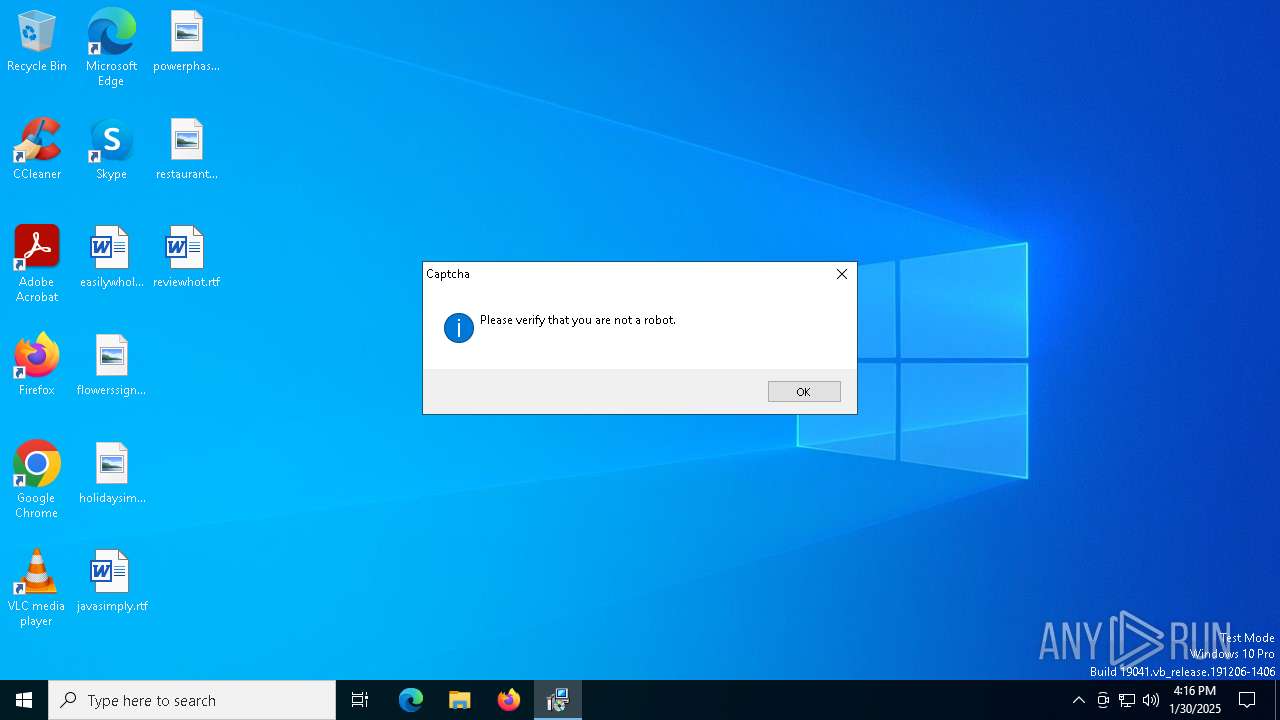
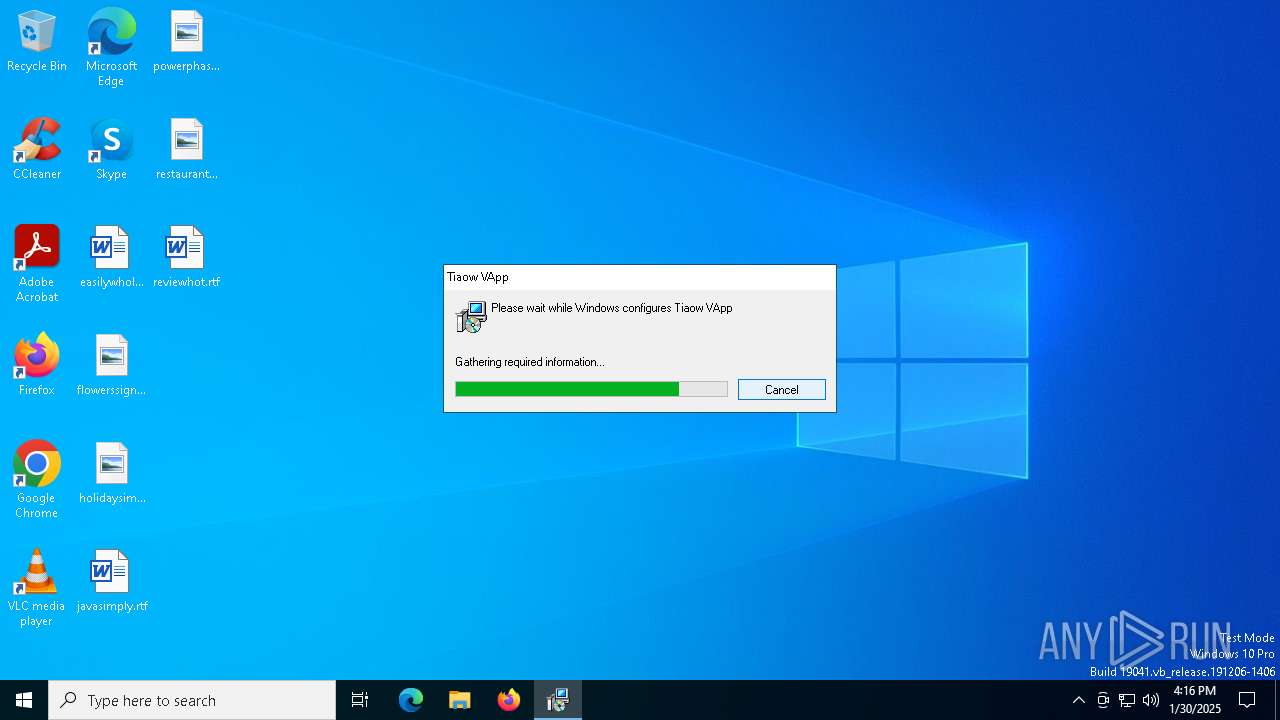
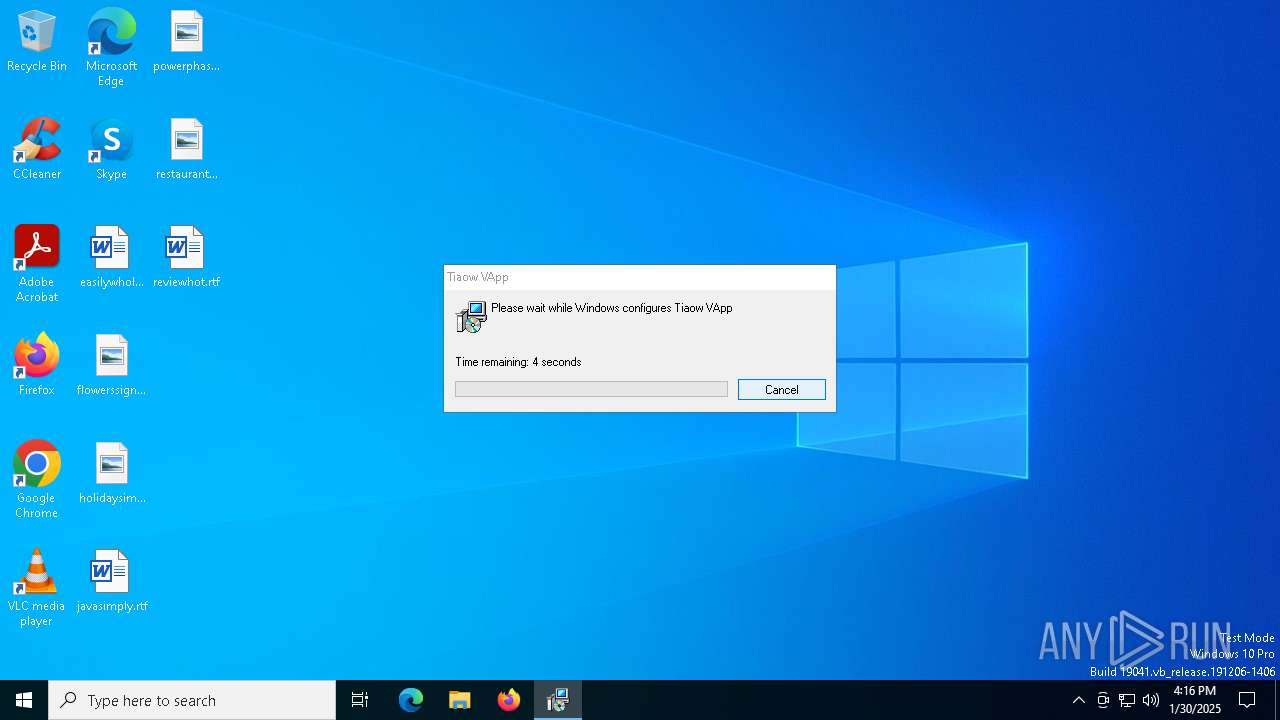
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Security: 0, Code page: 1252, Revision Number: {348FA94D-0CA3-40E9-9CD9-7050EAE770B1}, Number of Words: 10, Subject: Tiaow VApp, Author: Tusiq Juso Corp, Name of Creating Application: Tiaow VApp, Template: x64;2057, Comments: This installer database contains the logic and data required to install Tiaow VApp., Title: Installation Database, Keywords: Installer, MSI, Database, Create Time/Date: Thu Jan 30 11:59:55 2025, Last Saved Time/Date: Thu Jan 30 11:59:55 2025, Last Printed: Thu Jan 30 11:59:55 2025, Number of Pages: 450 |
| MD5: | C28E4D5C4719CCA2FFE76F033E79E028 |
| SHA1: | B2B4E1E2B337E7DE7DCEF05DAFAA249F6CED2EAA |
| SHA256: | BDFECF574BA864AD209AE5E7F1EF57FCC6C461F46E9FD8F21D94CB9312EC9A45 |
| SSDEEP: | 196608:bZIFJBAlJDEk7e/AVED13vz5rojr+hRolv0rUWDLj:desQk7ZER/4r+hSlv0HDL |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Windows owner or organization settings
- msiexec.exe (PID: 5320)
The process drops C-runtime libraries
- msiexec.exe (PID: 5320)
Process drops legitimate windows executable
- msiexec.exe (PID: 5320)
Executable content was dropped or overwritten
- UnRar.exe (PID: 3912)
Executes application which crashes
- obs-ffmpeg-mux.exe (PID: 5112)
INFO
Checks supported languages
- msiexec.exe (PID: 4076)
- msiexec.exe (PID: 5320)
- UnRar.exe (PID: 3912)
- createdump.exe (PID: 4388)
- obs-ffmpeg-mux.exe (PID: 5112)
The sample compiled with english language support
- msiexec.exe (PID: 5320)
Reads the computer name
- msiexec.exe (PID: 4076)
- msiexec.exe (PID: 5320)
An automatically generated document
- msiexec.exe (PID: 3060)
Creates a software uninstall entry
- msiexec.exe (PID: 5320)
Creates files or folders in the user directory
- UnRar.exe (PID: 3912)
- msiexec.exe (PID: 5320)
Checks proxy server information
- explorer.exe (PID: 1356)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5320)
Reads security settings of Internet Explorer
- explorer.exe (PID: 1356)
Reads Environment values
- msiexec.exe (PID: 4076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (88.6) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (10) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Security: | None |
|---|---|
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {348FA94D-0CA3-40E9-9CD9-7050EAE770B1} |
| Words: | 10 |
| Subject: | Tiaow VApp |
| Author: | Tusiq Juso Corp |
| LastModifiedBy: | - |
| Software: | Tiaow VApp |
| Template: | x64;2057 |
| Comments: | This installer database contains the logic and data required to install Tiaow VApp. |
| Title: | Installation Database |
| Keywords: | Installer, MSI, Database |
| CreateDate: | 2025:01:30 11:59:55 |
| ModifyDate: | 2025:01:30 11:59:55 |
| LastPrinted: | 2025:01:30 11:59:55 |
| Pages: | 450 |
Total processes
133
Monitored processes
11
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 640 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | UnRar.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 848 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | createdump.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1020 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | obs-ffmpeg-mux.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1356 | C:\WINDOWS\SysWOW64\explorer.exe explorer.exe | C:\Windows\SysWOW64\explorer.exe | obs-ffmpeg-mux.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3060 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\setup.msi | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3912 | "C:\Users\admin\AppData\Roaming\Tusiq Juso Corp\Tiaow VApp\UnRar.exe" x -p156427613t -o+ "C:\Users\admin\AppData\Roaming\Tusiq Juso Corp\Tiaow VApp\iwhgjds.rar" "C:\Users\admin\AppData\Roaming\Tusiq Juso Corp\Tiaow VApp\" | C:\Users\admin\AppData\Roaming\Tusiq Juso Corp\Tiaow VApp\UnRar.exe | msiexec.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: Command line RAR Exit code: 0 Version: 7.1.0 Modules
| |||||||||||||||
| 4076 | C:\Windows\syswow64\MsiExec.exe -Embedding FA4EDB2A1F0AEA22AEA38D41F3B88F5D | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4388 | "C:\Users\admin\AppData\Roaming\Tusiq Juso Corp\Tiaow VApp\createdump.exe" | C:\Users\admin\AppData\Roaming\Tusiq Juso Corp\Tiaow VApp\createdump.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Runtime Crash Dump Generator Exit code: 4294967295 Version: 6,0,2223,42425 @Commit: 4bb6dc195c0a3bc4c7e24ff54a8925b98db Modules
| |||||||||||||||
| 5112 | "C:\Users\admin\AppData\Roaming\Tusiq Juso Corp\Tiaow VApp\obs-ffmpeg-mux.exe" | C:\Users\admin\AppData\Roaming\Tusiq Juso Corp\Tiaow VApp\obs-ffmpeg-mux.exe | msiexec.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 5320 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 668
Read events
2 523
Write events
136
Delete events
9
Modification events
| (PID) Process: | (5320) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: C814000027DAB0513273DB01 | |||
| (PID) Process: | (5320) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 41D9FB8A645E02D6E13AD7975CE3023425476048C59FCA7D61CA16F0EFE12BDA | |||
| (PID) Process: | (5320) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (5320) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Folders |
| Operation: | write | Name: | C:\Config.Msi\ |
Value: | |||
| (PID) Process: | (5320) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\1397b1.rbs |
Value: 31159090 | |||
| (PID) Process: | (5320) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\1397b1.rbsLow |
Value: | |||
| (PID) Process: | (5320) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-21-1693682860-607145093-2874071422-1001\Components\1DA51AE393E3A2E44AD642274DF874C9 |
| Operation: | write | Name: | CE0905C3756E23249A0C5E1843CDE12D |
Value: C:\Users\admin\AppData\Roaming\Tusiq Juso Corp\Tiaow VApp\api-ms-win-core-processthreads-l1-1-1.dll | |||
| (PID) Process: | (5320) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-21-1693682860-607145093-2874071422-1001\Components\EE9277BB1523DD045952C0B8CCCF2CF8 |
| Operation: | write | Name: | CE0905C3756E23249A0C5E1843CDE12D |
Value: C:\Users\admin\AppData\Roaming\Tusiq Juso Corp\Tiaow VApp\api-ms-win-core-profile-l1-1-0.dll | |||
| (PID) Process: | (5320) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-21-1693682860-607145093-2874071422-1001\Components\27B23E0DE8354FA4984FE3E6EA64A0DA |
| Operation: | write | Name: | CE0905C3756E23249A0C5E1843CDE12D |
Value: C:\Users\admin\AppData\Roaming\Tusiq Juso Corp\Tiaow VApp\api-ms-win-core-rtlsupport-l1-1-0.dll | |||
| (PID) Process: | (5320) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-21-1693682860-607145093-2874071422-1001\Components\E053C72B9492790418B6BC8963A132B1 |
| Operation: | write | Name: | CE0905C3756E23249A0C5E1843CDE12D |
Value: C:\Users\admin\AppData\Roaming\Tusiq Juso Corp\Tiaow VApp\api-ms-win-core-string-l1-1-0.dll | |||
Executable files
52
Suspicious files
21
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5320 | msiexec.exe | C:\Windows\Installer\1397af.msi | — | |
MD5:— | SHA256:— | |||
| 5320 | msiexec.exe | C:\Windows\Installer\MSI98A9.tmp | executable | |
MD5:EE09D6A1BB908B42C05FD0BEEB67DFD2 | SHA256:7BBF611F5E2A16439DC8CD11936F6364F6D5CC0044545C92775DA5646AFC7752 | |||
| 5320 | msiexec.exe | C:\Windows\Installer\MSI9FE3.tmp | executable | |
MD5:EE09D6A1BB908B42C05FD0BEEB67DFD2 | SHA256:7BBF611F5E2A16439DC8CD11936F6364F6D5CC0044545C92775DA5646AFC7752 | |||
| 5320 | msiexec.exe | C:\Windows\Installer\inprogressinstallinfo.ipi | binary | |
MD5:0D6D0790D7F485AD219774269FB7F70D | SHA256:9934DB905DBF4D67C110EF50CFE587C01B584E6F20AB2DB398D91449A0555D36 | |||
| 5320 | msiexec.exe | C:\Windows\Installer\MSI9E6B.tmp | executable | |
MD5:EE09D6A1BB908B42C05FD0BEEB67DFD2 | SHA256:7BBF611F5E2A16439DC8CD11936F6364F6D5CC0044545C92775DA5646AFC7752 | |||
| 5320 | msiexec.exe | C:\Users\admin\AppData\Roaming\Tusiq Juso Corp\Tiaow VApp\vcruntime140_1.dll | executable | |
MD5:135359D350F72AD4BF716B764D39E749 | SHA256:34048ABAA070ECC13B318CEA31425F4CA3EDD133D350318AC65259E6058C8B32 | |||
| 5320 | msiexec.exe | C:\Users\admin\AppData\Roaming\Tusiq Juso Corp\Tiaow VApp\msvcp140.dll | executable | |
MD5:6DA7F4530EDB350CF9D967D969CCECF8 | SHA256:9FEE6F36547D6F6EA7CA0338655555DBA6BB0F798BC60334D29B94D1547DA4DA | |||
| 5320 | msiexec.exe | C:\Users\admin\AppData\Roaming\Tusiq Juso Corp\Tiaow VApp\vcruntime140.dll | executable | |
MD5:F34EB034AA4A9735218686590CBA2E8B | SHA256:9D2B40F0395CC5D1B4D5EA17B84970C29971D448C37104676DB577586D4AD1B1 | |||
| 5320 | msiexec.exe | C:\Windows\Installer\MSIB6C7.tmp | binary | |
MD5:45FFAB84B79102B01DE78359CC92CA7C | SHA256:6EA7A3511E7244E58BB1EB03E0343D288ADB920C74FE641C8F4C69E63C83D83D | |||
| 5320 | msiexec.exe | C:\Users\admin\AppData\Roaming\Tusiq Juso Corp\Tiaow VApp\utest.dll | executable | |
MD5:01DACEA3CBE5F2557D0816FC64FAE363 | SHA256:B4C96B1E5EEE34871D9AB43BCEE8096089742032C0669DF3C9234941AAC3D502 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
32
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | svchost.exe | GET | 200 | 23.32.238.34:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | svchost.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4640 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4640 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1356 | explorer.exe | GET | 200 | 169.150.247.39:80 | http://emarketstats.com/front.php?a=BJw3f5rM6balnGz&id=0 | unknown | — | — | unknown |
1144 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5496 | svchost.exe | 23.32.238.34:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | svchost.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.130:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1076 | svchost.exe | 23.213.166.81:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 20.190.160.5:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
emarketstats.com |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
obs-ffmpeg-mux.exe | Operation completed successfully. |