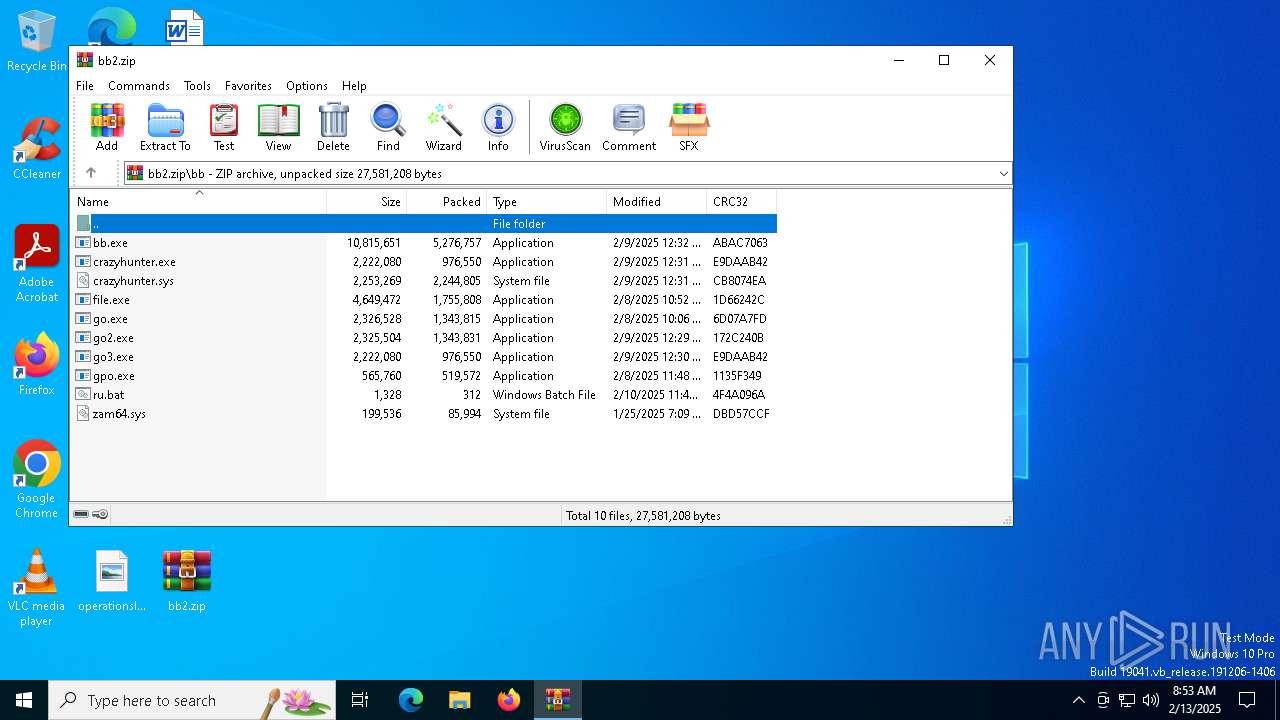
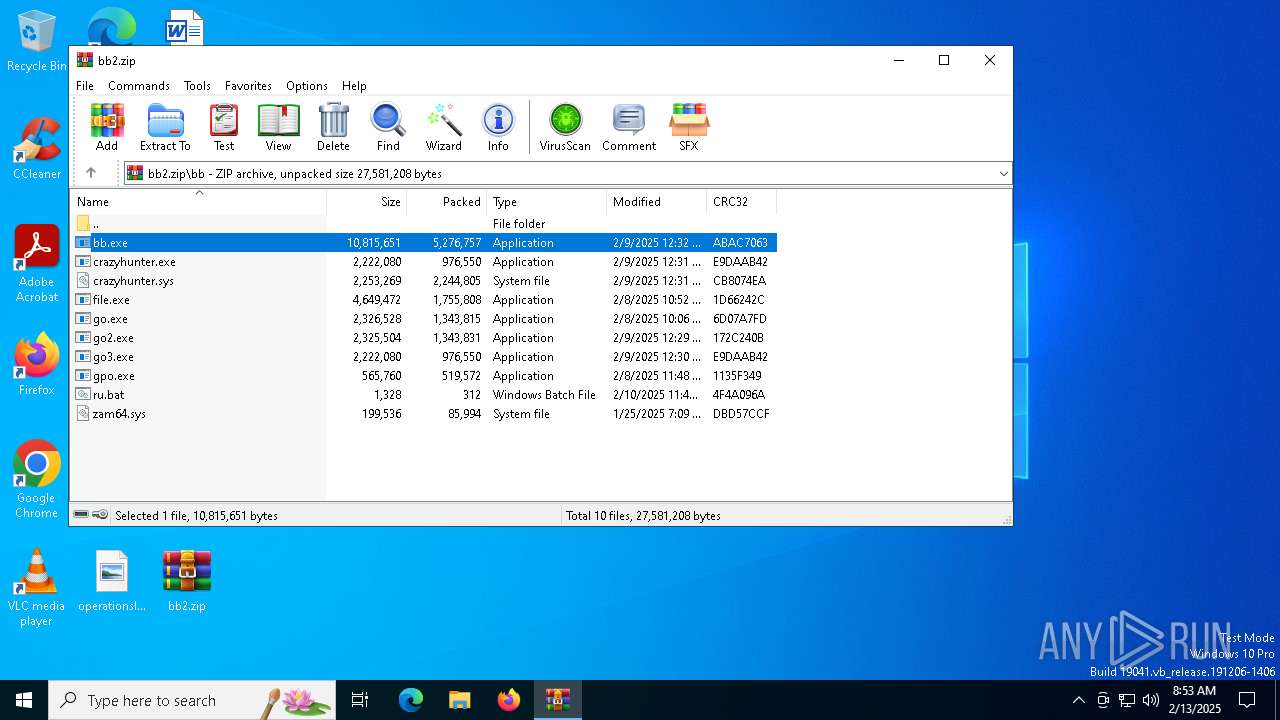
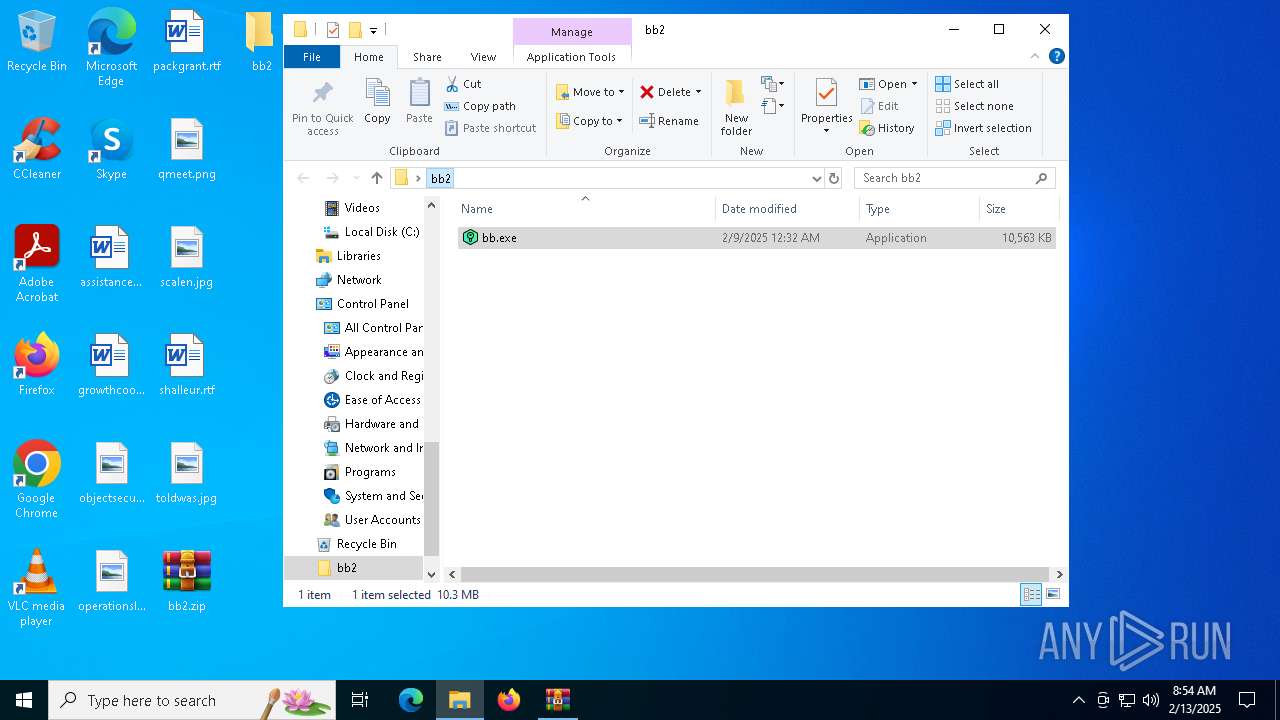
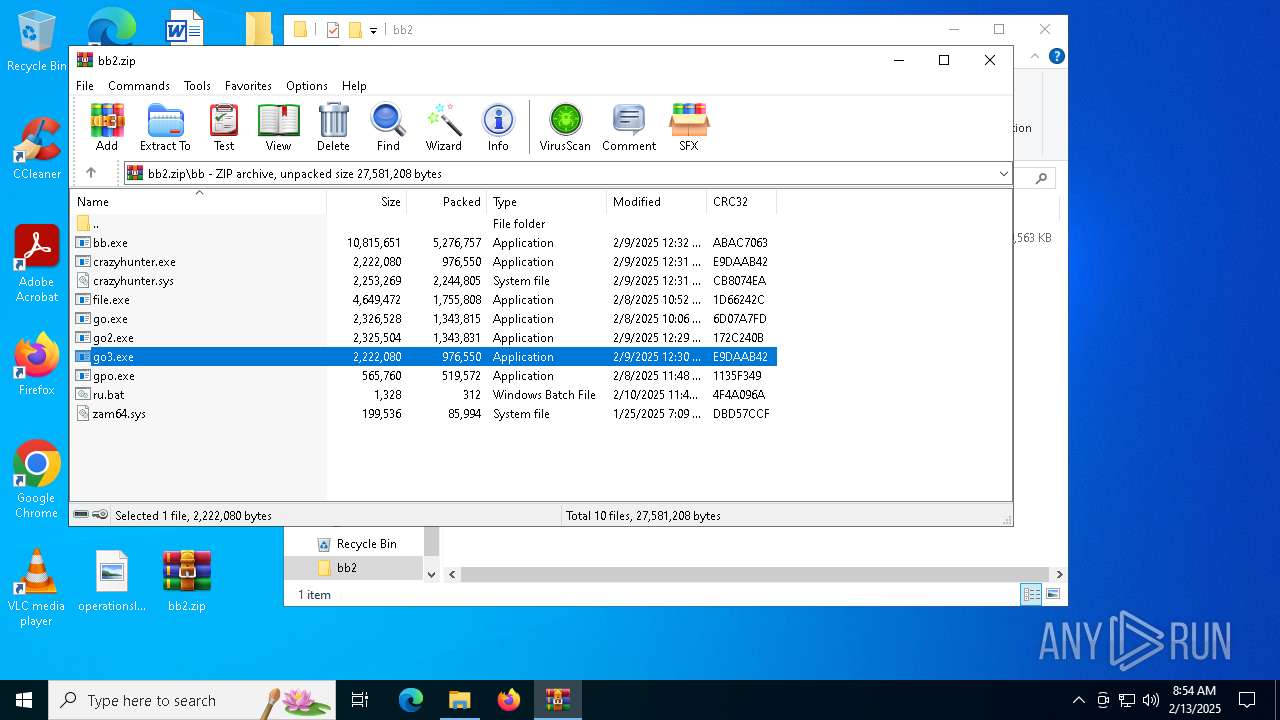
| File name: | bb2.zip |
| Full analysis: | https://app.any.run/tasks/cc2b62f6-2fe6-497e-8f16-fe63b8401320 |
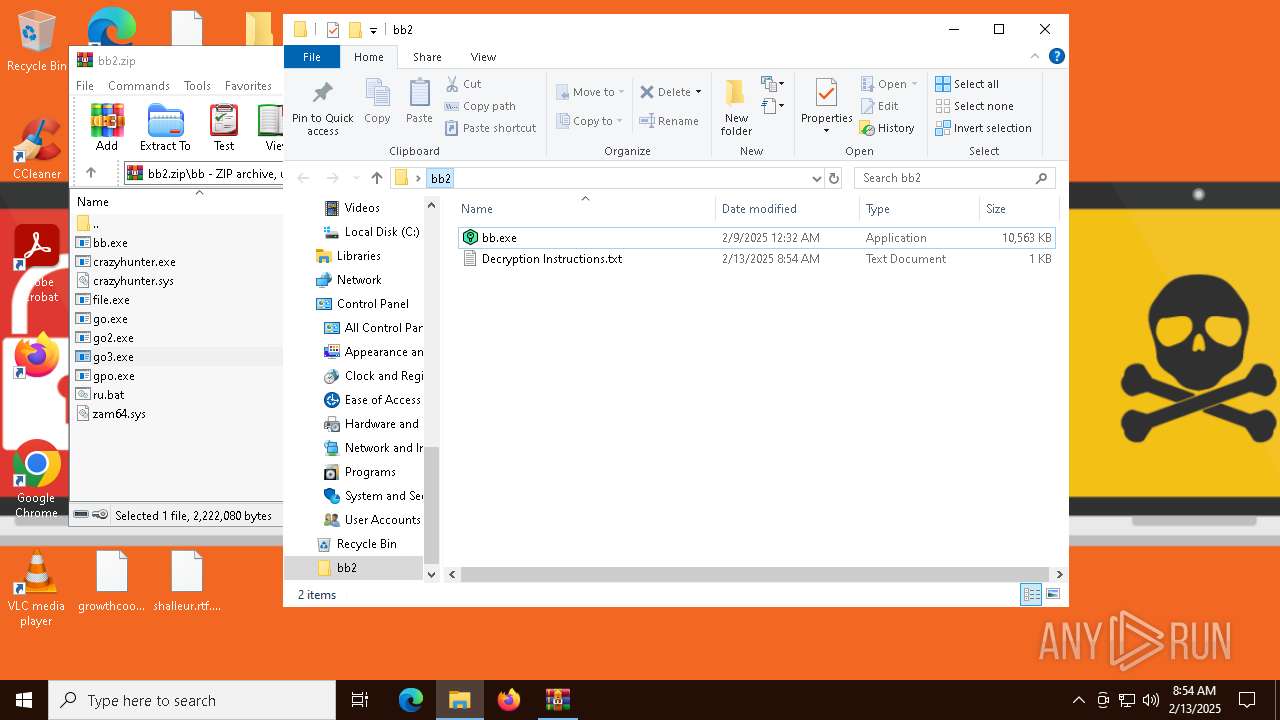
| Verdict: | Malicious activity |
| Analysis date: | February 13, 2025, 08:53:31 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
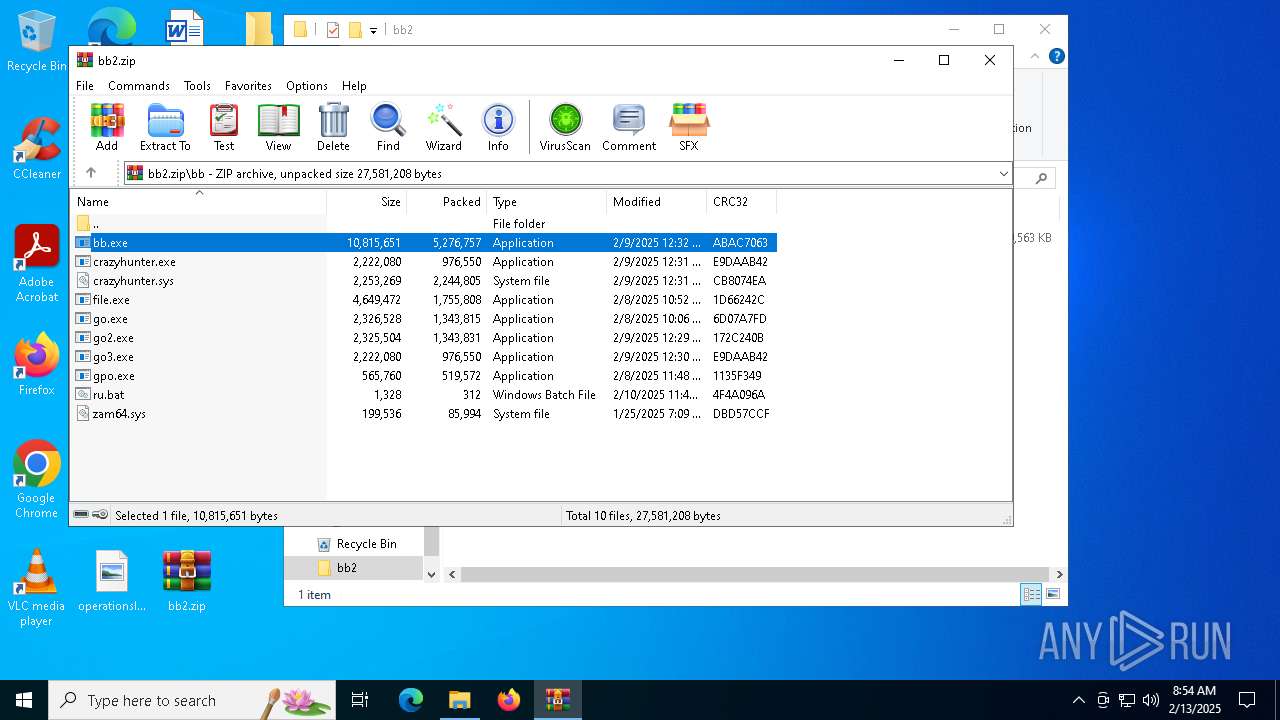
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 558D7088D39A8C569C6289C5D185C730 |
| SHA1: | 142F3F2474E3145F16F3EA553B6430B3C9DB070F |
| SHA256: | BDFC66266A2A19FC3D5DCCEF3EEFE4C0EE928BA5B7ABAD60BC320218B2082FEA |
| SSDEEP: | 98304:sL6Ag6GE0nkZIMLVqYIcZY1hILfZlWqZa3vszThm4v/dfQThF7b1/gfUQsV95jtm:Wj/tYvUt3SKx37qIfFH/QurYDc |
MALICIOUS
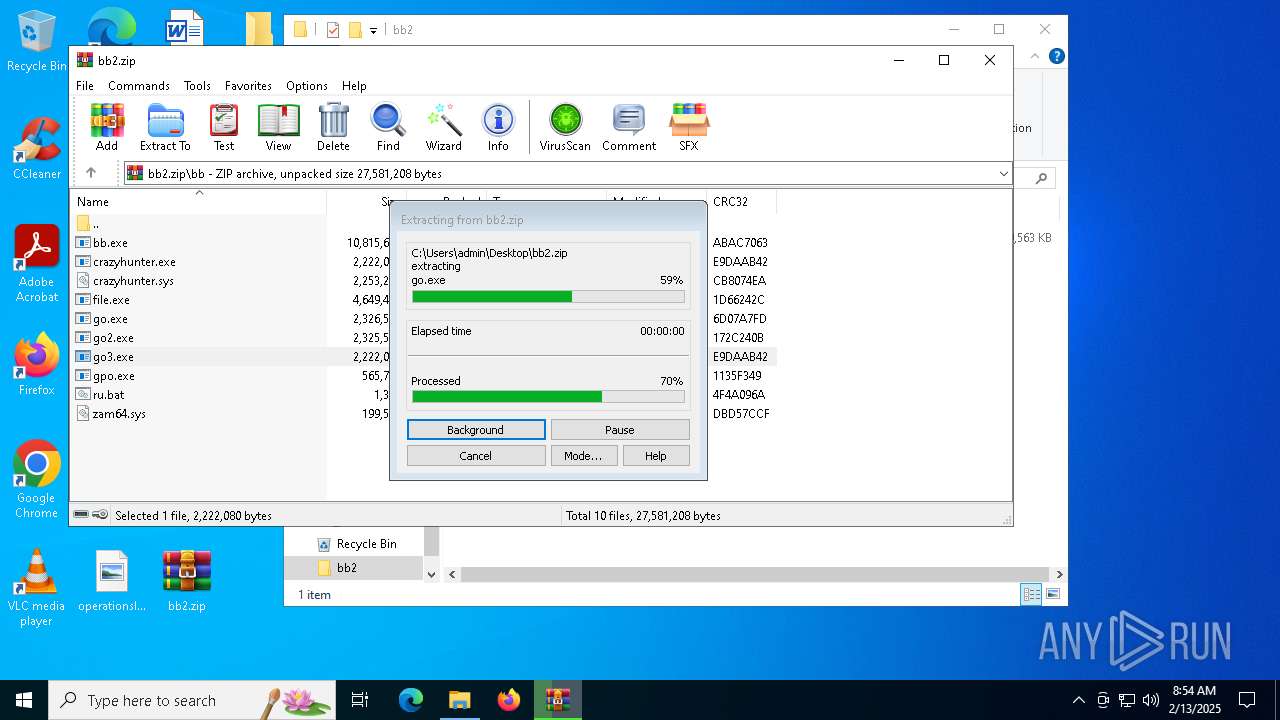
Generic archive extractor
- WinRAR.exe (PID: 6096)
RANSOMWARE has been detected
- go3.exe (PID: 6940)
Renames files like ransomware
- go3.exe (PID: 6940)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 7104)
SUSPICIOUS
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 6096)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6096)
Creates file in the systems drive root
- go3.exe (PID: 6940)
Imports DLL using pinvoke
- powershell.exe (PID: 3436)
CSC.EXE is used to compile C# code
- csc.exe (PID: 5028)
Executable content was dropped or overwritten
- csc.exe (PID: 5028)
Probably download files using WebClient
- go3.exe (PID: 6940)
Starts POWERSHELL.EXE for commands execution
- go3.exe (PID: 6940)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6096)
Creates files in the program directory
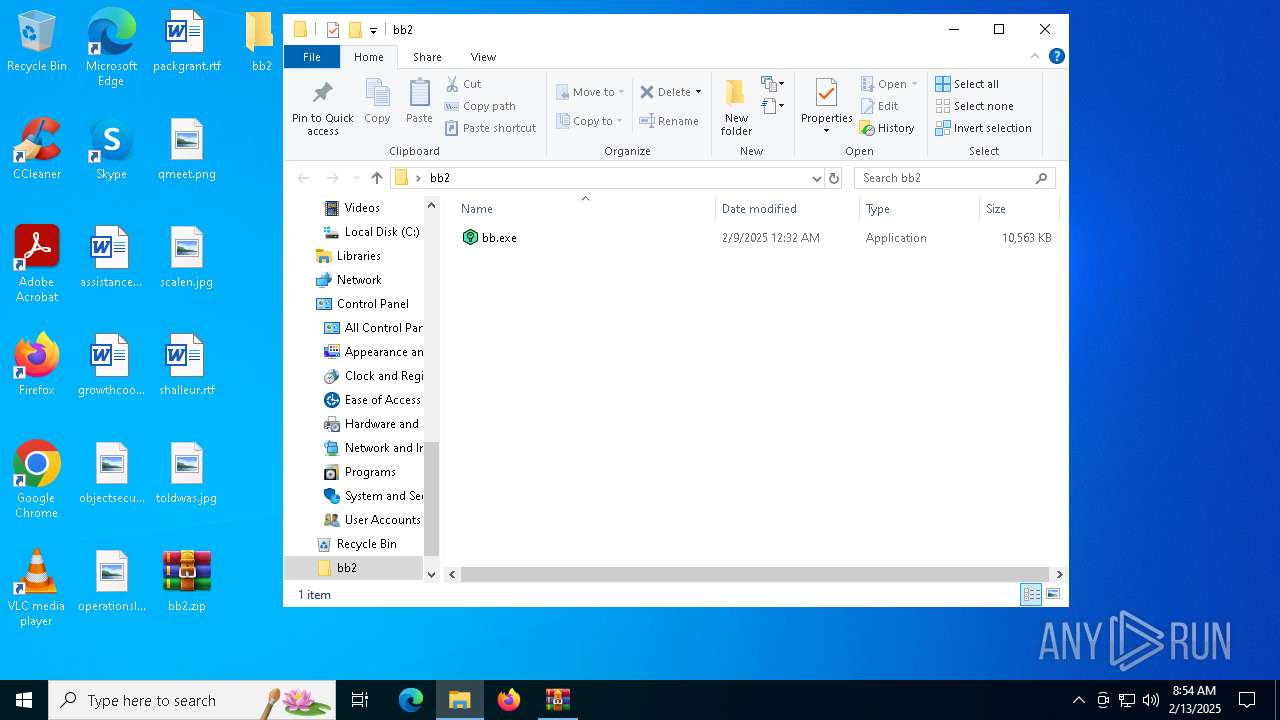
- bb.exe (PID: 6696)
- go3.exe (PID: 6940)
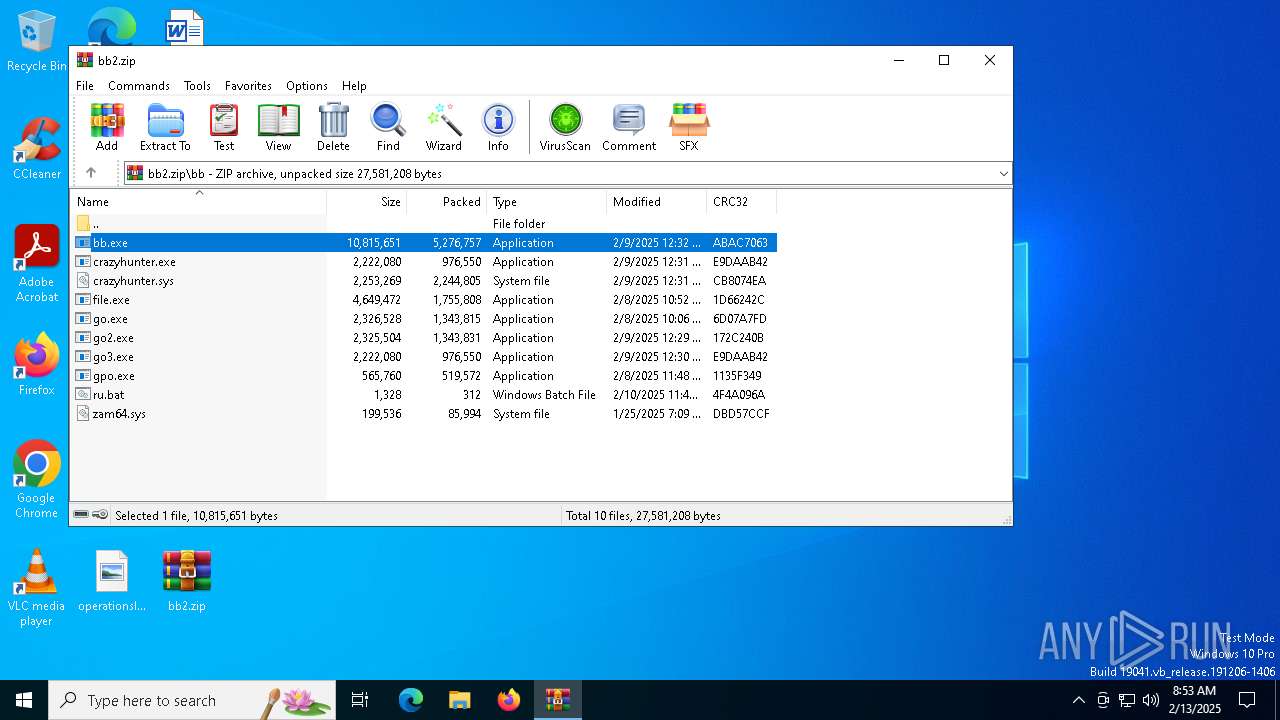
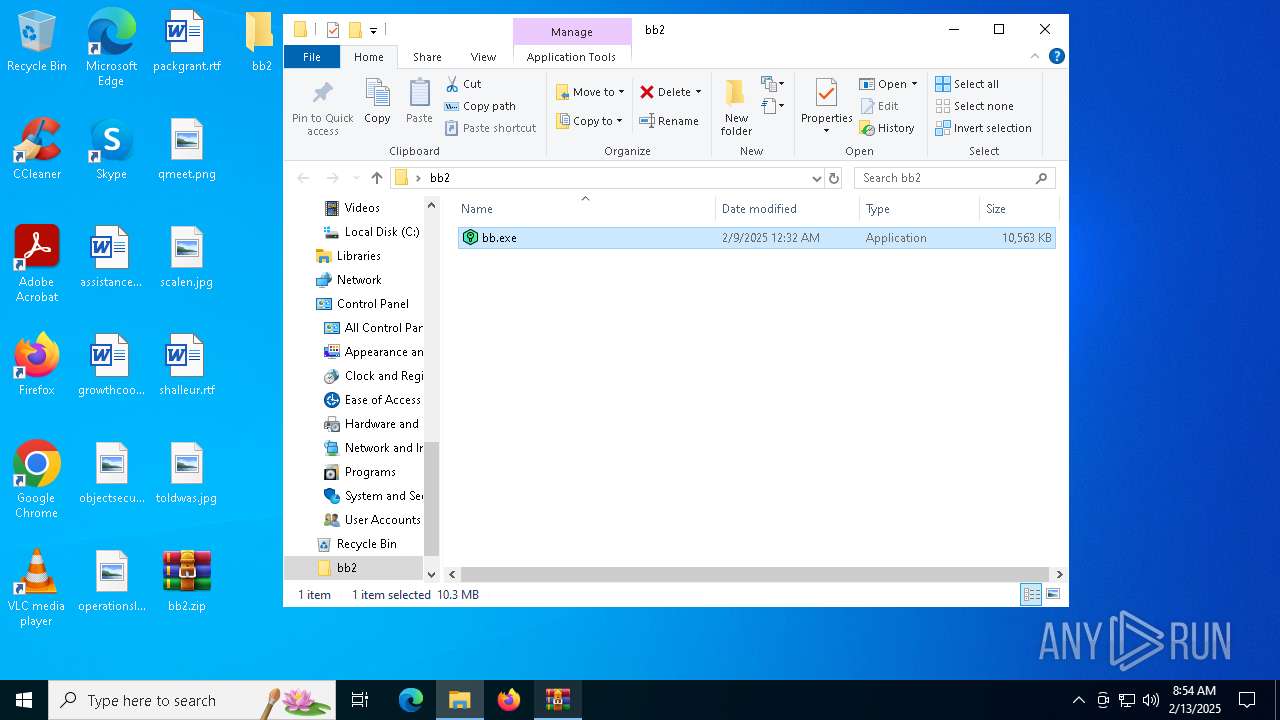
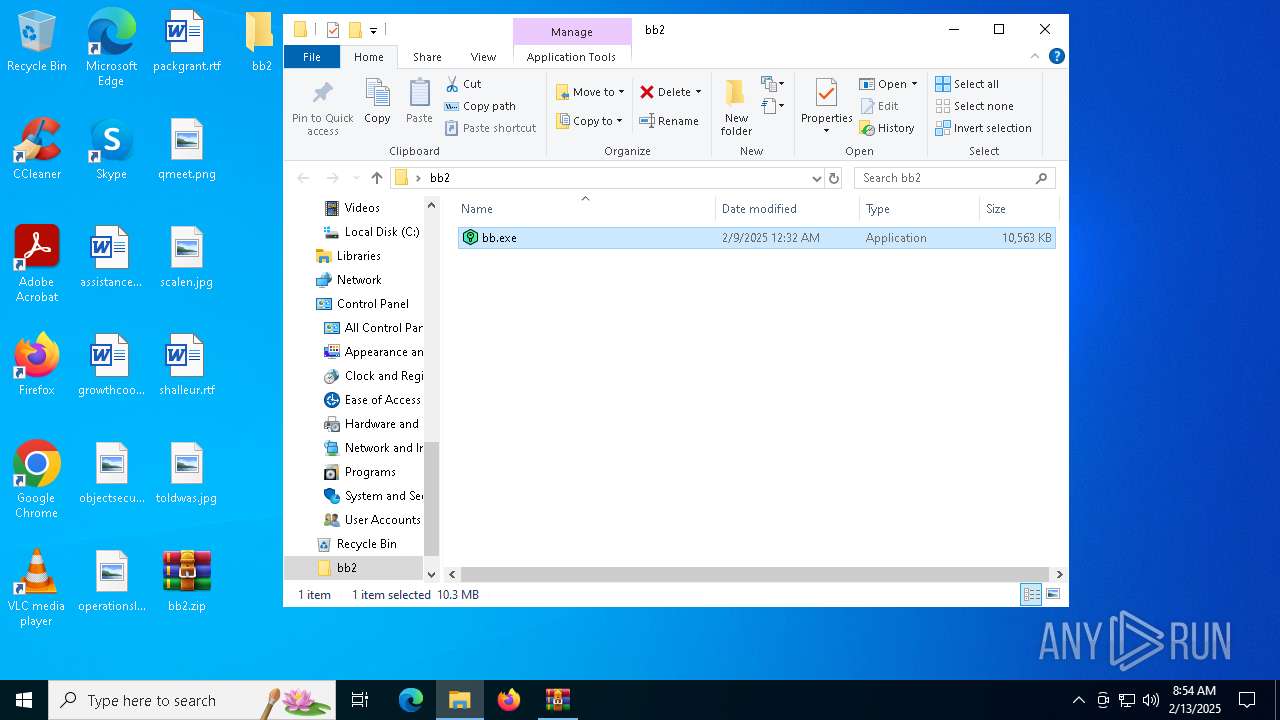
Manual execution by a user
- bb.exe (PID: 6696)
- bb.exe (PID: 6876)
Checks supported languages
- bb.exe (PID: 6696)
- bb.exe (PID: 6876)
- csc.exe (PID: 5028)
- cvtres.exe (PID: 5536)
The sample compiled with english language support
- WinRAR.exe (PID: 6096)
Creates files or folders in the user directory
- go3.exe (PID: 6940)
Drops encrypted JS script (Microsoft Script Encoder)
- go3.exe (PID: 6940)
Reads the machine GUID from the registry
- csc.exe (PID: 5028)
Create files in a temporary directory
- csc.exe (PID: 5028)
Checks proxy server information
- powershell.exe (PID: 7104)
Disables trace logs
- powershell.exe (PID: 7104)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:02:10 17:51:14 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | bb/ |
Total processes
129
Monitored processes
11
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3436 | powershell -Command "Add-Type -TypeDefinition 'using System; using System.Runtime.InteropServices; public class Wallpaper { [DllImport(\"user32.dll\", CharSet = CharSet.Auto)] public static extern int SystemParametersInfo(int uAction, int uParam, string lpvParam, int fuWinIni); public static void Set(string path) { SystemParametersInfo(20, 0, path, 3); } }'; [Wallpaper]::Set('C:\Users\admin\AppData\Local\Temp\Wallpaper.png')" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | go3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5028 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\20jyme1t.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 5096 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5536 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES3537.tmp" "c:\Users\admin\AppData\Local\Temp\CSCEA612F48A591443FA1AE813C6DD88AB8.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
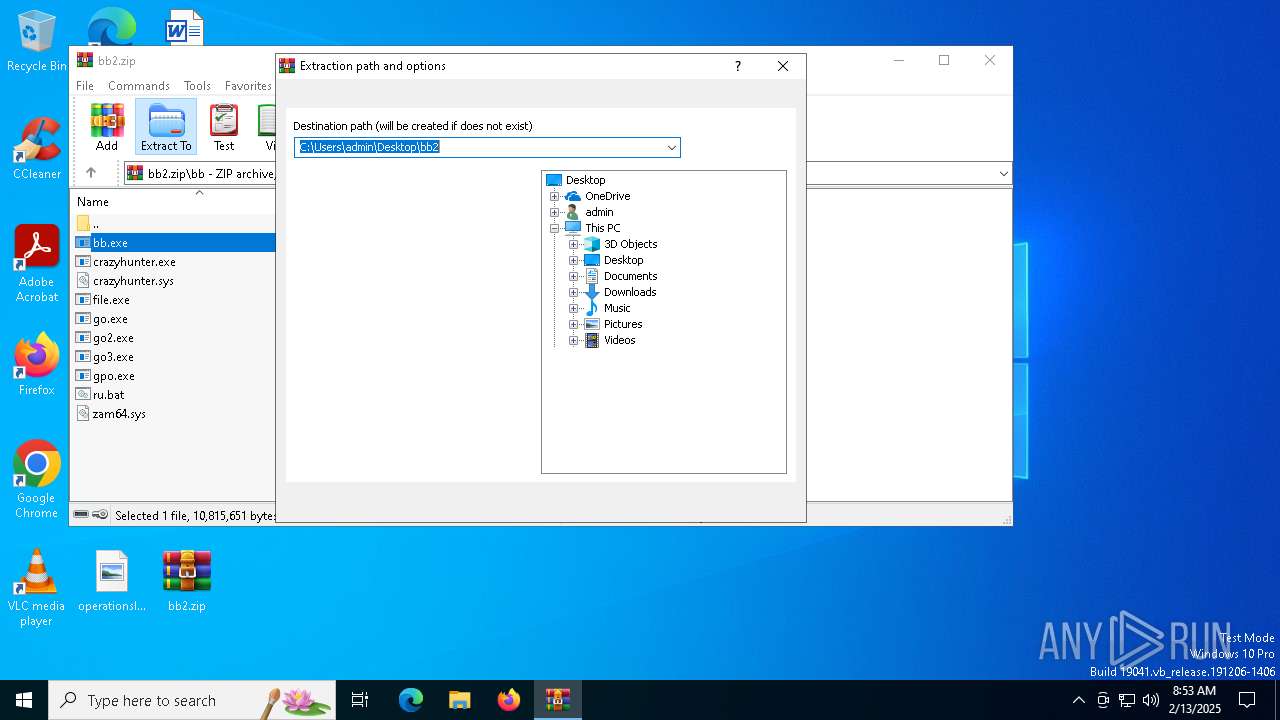
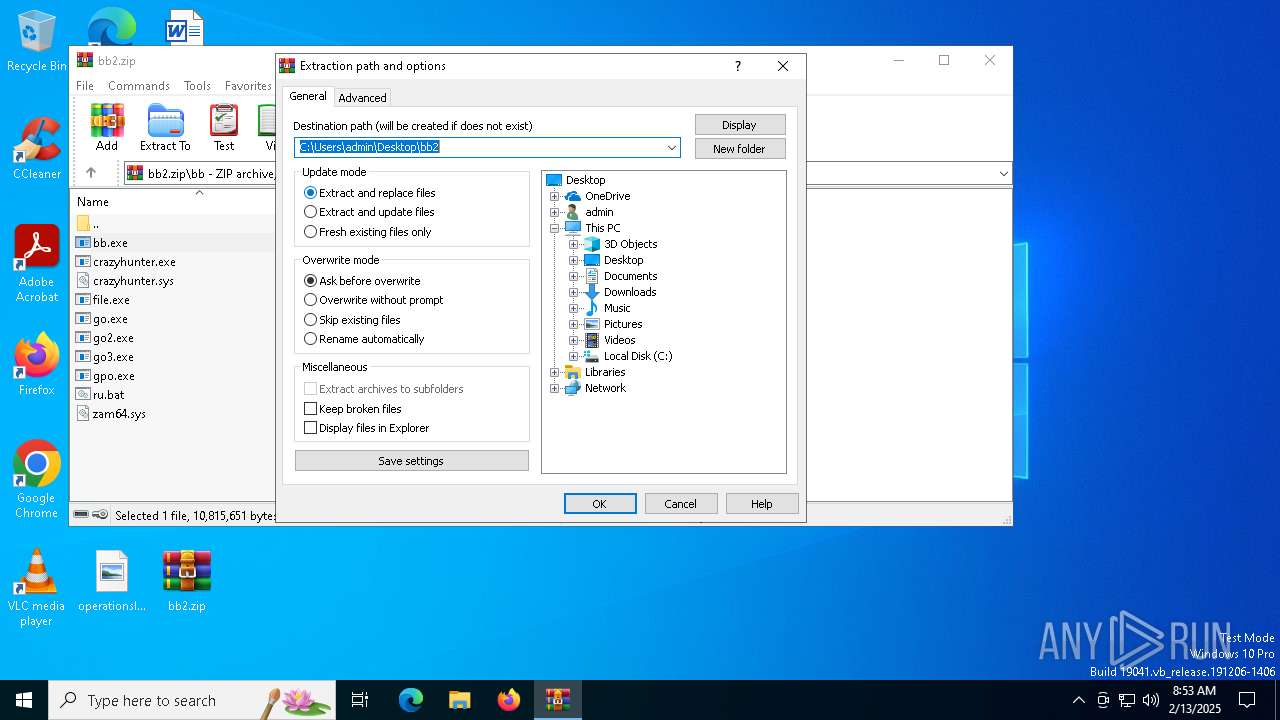
| 6096 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\bb2.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6652 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6696 | "C:\Users\admin\Desktop\bb2\bb.exe" | C:\Users\admin\Desktop\bb2\bb.exe | — | explorer.exe | |||||||||||
User: admin Company: Windows Integrity Level: MEDIUM Description: Windows Office Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
| 6876 | "C:\Users\admin\Desktop\bb2\bb.exe" | C:\Users\admin\Desktop\bb2\bb.exe | — | explorer.exe | |||||||||||
User: admin Company: Windows Integrity Level: MEDIUM Description: Windows Office Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
| 6940 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6096.17849\bb\go3.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa6096.17849\bb\go3.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7104 | powershell -Command "(New-Object System.Net.WebClient).DownloadFile('https://ncmep.org/files/2023/05/ransomeware-01-1280x640.png', 'C:\Users\admin\AppData\Local\Temp\Wallpaper.png')" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | go3.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 356
Read events
13 332
Write events
11
Delete events
13
Modification events
| (PID) Process: | (6096) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6096) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6096) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6096) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\bb2.zip | |||
| (PID) Process: | (6096) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6096) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6096) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6096) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6096) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (6096) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
10
Suspicious files
73
Text files
62
Unknown types
0
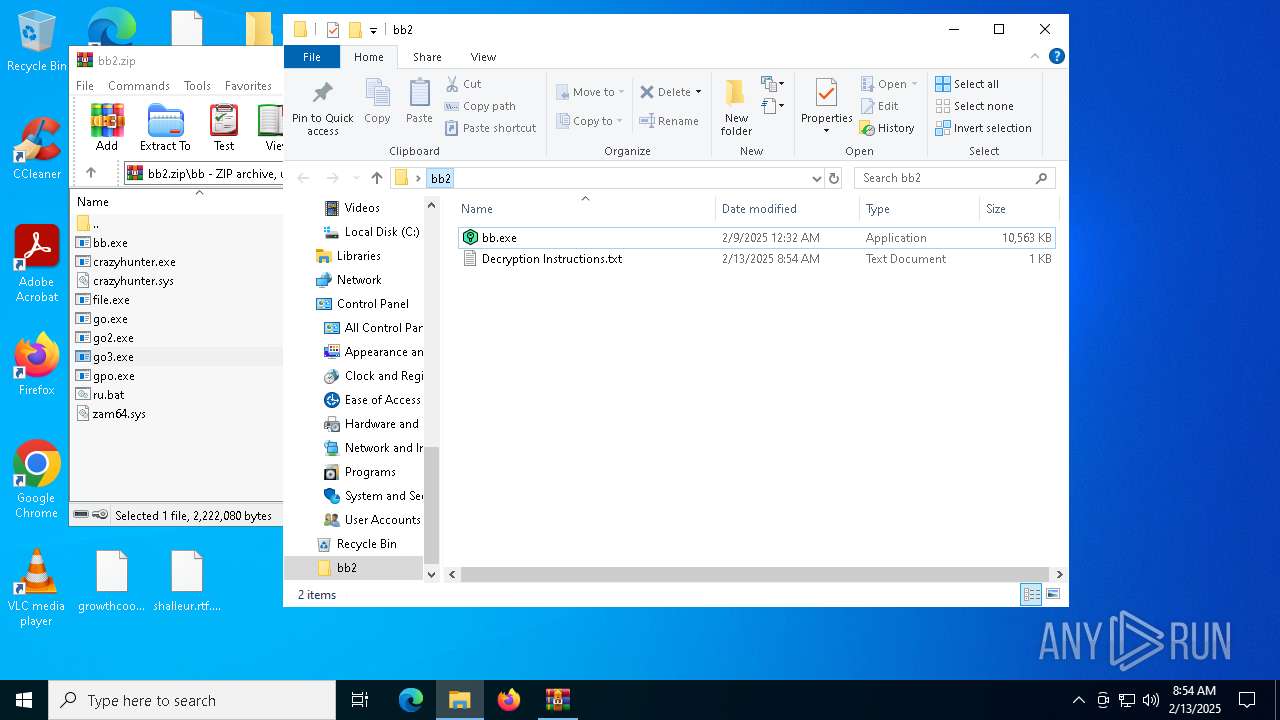
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6096 | WinRAR.exe | C:\Users\admin\Desktop\bb2\bb.exe | executable | |
MD5:9FE3322DD4FC35D1ED510BF715DAE814 | SHA256:2CC975FDB21F6DD20775AA52C7B3DB6866C50761E22338B08FFC7F7748B2ACAA | |||
| 6096 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6096.17849\bb\go3.exe | executable | |
MD5:6A70C22A5778EAA433B6CE44513068DA | SHA256:F72C03D37DB77E8C6959B293CE81D009BF1C85F7D3BDAA4F873D3241833C146B | |||
| 6096 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6096.17849\bb\crazyhunter.sys | binary | |
MD5:906E89F6EB39919C6D12A660B68AE81F | SHA256:5316060745271723C9934047155DAE95A3920CB6343CA08C93531E1C235861BA | |||
| 6096 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6096.17849\bb\crazyhunter.exe | executable | |
MD5:6A70C22A5778EAA433B6CE44513068DA | SHA256:F72C03D37DB77E8C6959B293CE81D009BF1C85F7D3BDAA4F873D3241833C146B | |||
| 6096 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6096.17849\bb\bb.exe | executable | |
MD5:9FE3322DD4FC35D1ED510BF715DAE814 | SHA256:2CC975FDB21F6DD20775AA52C7B3DB6866C50761E22338B08FFC7F7748B2ACAA | |||
| 6940 | go3.exe | C:\Users\Default\Favorites\Decryption Instructions.txt | text | |
MD5:EE8C636DC0B6C96D41DD61F38BF2066F | SHA256:0C5E7F344812D3AF51EBB572A8D57EB85A8A75635236ED21EE54E94EA532AB41 | |||
| 6940 | go3.exe | C:\Users\Default\Documents\Decryption Instructions.txt | text | |
MD5:EE8C636DC0B6C96D41DD61F38BF2066F | SHA256:0C5E7F344812D3AF51EBB572A8D57EB85A8A75635236ED21EE54E94EA532AB41 | |||
| 6096 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6096.17849\bb\gpo.exe | executable | |
MD5:9E45AB7D2D942A575B2F902CCCFB3839 | SHA256:512F785D3C2A787B30FA760A153723D02090C0812D01BB519B670ECFC9780D93 | |||
| 6096 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6096.17849\bb\go.exe | executable | |
MD5:CA257AAA1DED22CA22086B9E95CB456D | SHA256:754D5C0C494099B72C050E745DDE45EE4F6195C1F559A0F3A0FDDBA353004DB6 | |||
| 6096 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6096.17849\bb\go2.exe | executable | |
MD5:DA1A93627CEC6665AE28BAAF23FF27C5 | SHA256:983F5346756D61FEC35DF3E6E773FF43973EB96AABAA8094DCBFB5CA17821C81 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
25
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1176 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6740 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6740 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5496 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3220 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1076 | svchost.exe | 2.19.217.152:443 | go.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | backgroundTaskHost.exe | 20.31.169.57:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | backgroundTaskHost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
5496 | backgroundTaskHost.exe | 20.103.156.88:443 | fd.api.iris.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6740 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |