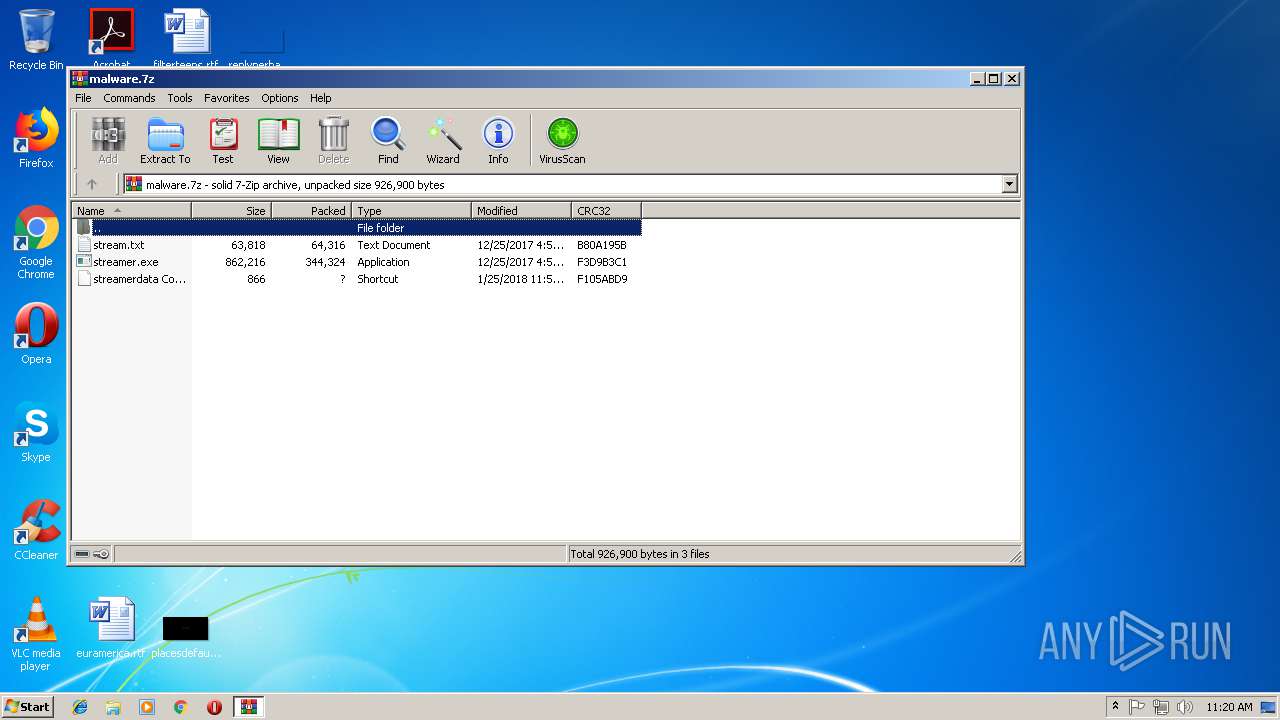
| File name: | malware.7z |
| Full analysis: | https://app.any.run/tasks/3635ffb6-76bb-494f-974b-a59a4550395d |
| Verdict: | Malicious activity |
| Analysis date: | October 15, 2018, 10:20:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | B5DAB8FA021EF3D9400768E7A587CC4C |
| SHA1: | 9637592A930198982581773FC9DA9341AD4EFDC4 |
| SHA256: | BDD9F4F8ED39B6DEE2C1A185F0C855AB444D72D1B6A7AFF7D2DB512A3EC47A99 |
| SSDEEP: | 6144:wsdfqixfNNKuHv5qyWciQbAJLyEP1ox5LuanYlHPbYOuCY+vO/Sjr5Cu:OiVN9oZciSuP9ox5zYlHjYn+2aP |
MALICIOUS
Application was dropped or rewritten from another process
- streamer.exe (PID: 2436)
- streamer.exe (PID: 2912)
- streamer.exe (PID: 3028)
Changes the autorun value in the registry
- streamer.exe (PID: 2436)
SUSPICIOUS
Executable content was dropped or overwritten
- streamer.exe (PID: 2436)
Starts itself from another location
- streamer.exe (PID: 2436)
Starts CMD.EXE for commands execution
- streamer.exe (PID: 2436)
Reads Internet Cache Settings
- rundll32.exe (PID: 3180)
- rundll32.exe (PID: 1708)
- rundll32.exe (PID: 3188)
- rundll32.exe (PID: 1264)
- rundll32.exe (PID: 1688)
- rundll32.exe (PID: 2704)
Connects to unusual port
- streamer.exe (PID: 2912)
INFO
Application launched itself
- firefox.exe (PID: 3332)
Reads CPU info
- firefox.exe (PID: 3332)
- firefox.exe (PID: 3312)
- firefox.exe (PID: 3612)
- firefox.exe (PID: 1308)
Creates files in the user directory
- firefox.exe (PID: 3332)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
56
Monitored processes
18
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 676 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1264 | "C:\Windows\system32\rundll32.exe" "C:\Windows\system32\WININET.dll",DispatchAPICall 1 | C:\Windows\system32\rundll32.exe | — | firefox.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1308 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3332.12.1580503031\958150693" -childID 3 -isForBrowser -prefsHandle 2888 -prefsLen 11807 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3332 "\\.\pipe\gecko-crash-server-pipe.3332" 2920 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 1688 | "C:\Windows\system32\rundll32.exe" "C:\Windows\system32\WININET.dll",DispatchAPICall 1 | C:\Windows\system32\rundll32.exe | — | streamer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1708 | "C:\Windows\system32\rundll32.exe" "C:\Windows\system32\WININET.dll",DispatchAPICall 1 | C:\Windows\system32\rundll32.exe | — | streamer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
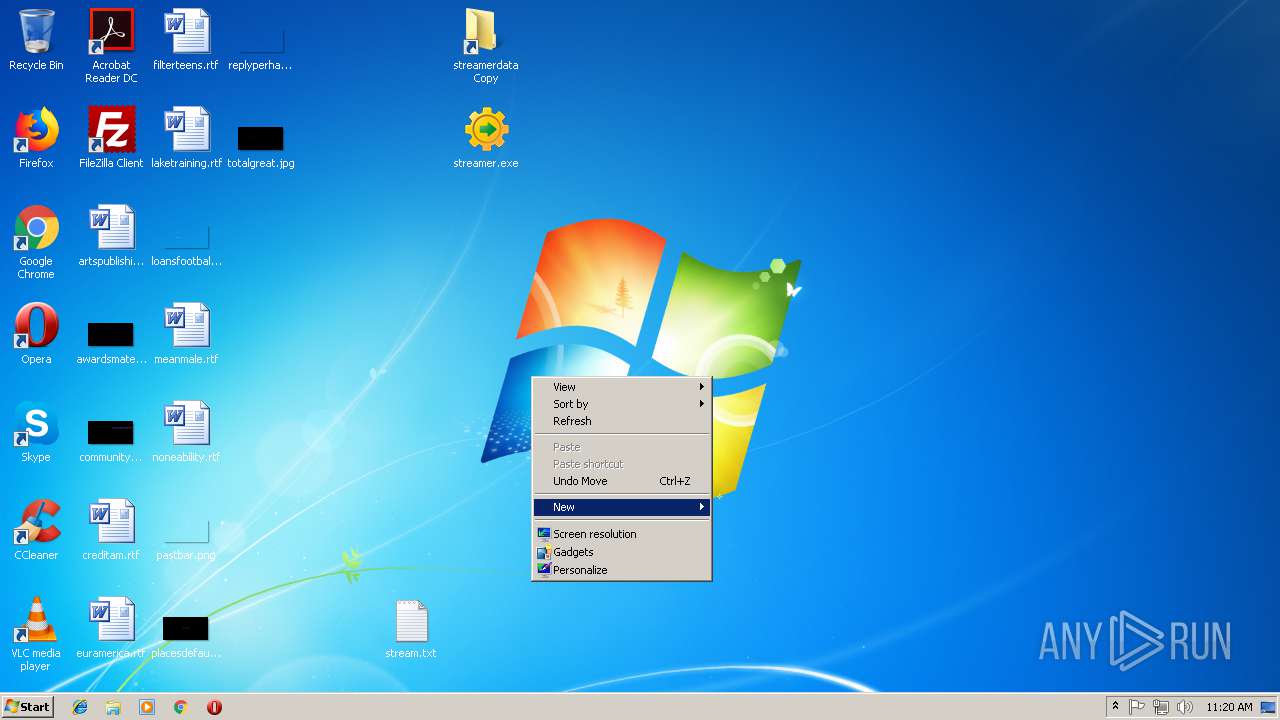
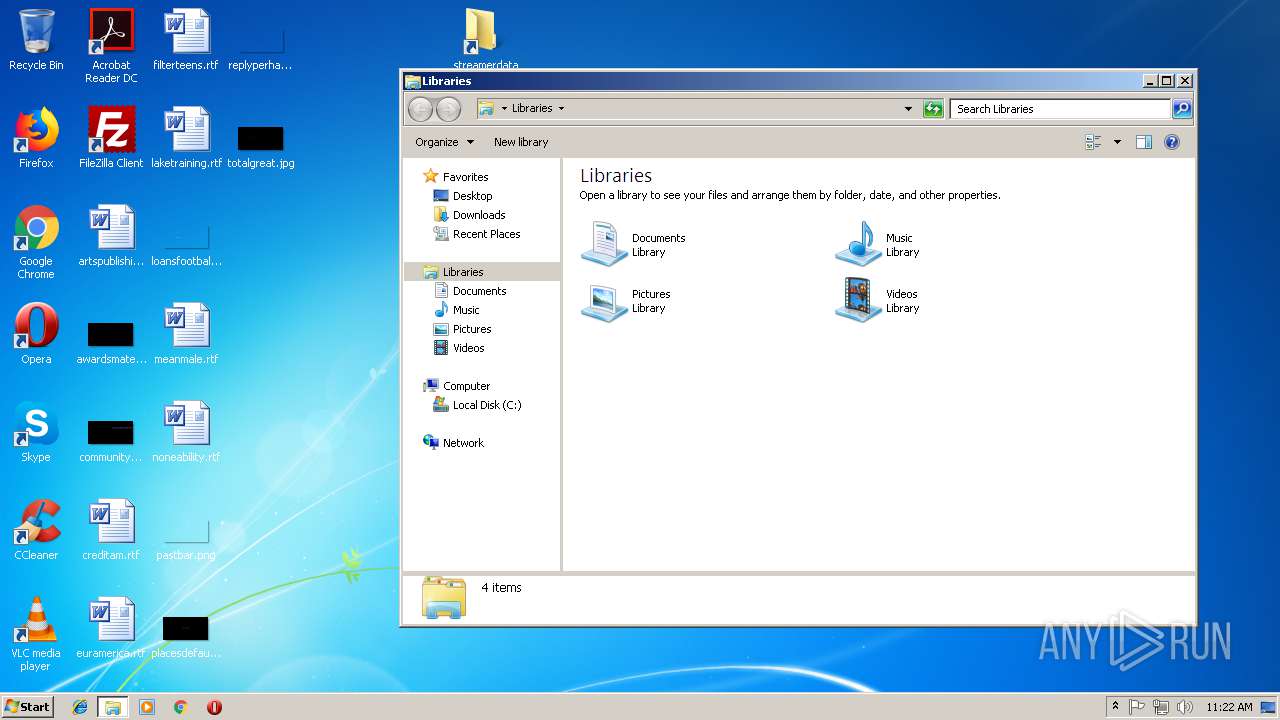
| 2436 | streamerdata\streamer.exe /AutoIt3ExecuteScript "streamerdata\stream.txt" XG3ZZ0Qe0K2vH67 | C:\Users\admin\Desktop\streamerdata\streamer.exe | cmd.exe | ||||||||||||
User: admin Company: Carifred Integrity Level: MEDIUM Description: Ultra Virus Killer AutoIt script parser Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2532 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\malware.7z" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2704 | "C:\Windows\system32\rundll32.exe" "C:\Windows\system32\WININET.dll",DispatchAPICall 1 | C:\Windows\system32\rundll32.exe | — | streamer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2912 | "C:\streamer\streamer.exe" /AutoIt3ExecuteScript C:\streamer\stream.txt | C:\streamer\streamer.exe | streamer.exe | ||||||||||||
User: admin Company: Carifred Integrity Level: MEDIUM Description: Ultra Virus Killer AutoIt script parser Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3028 | C:\streamer\streamer.exe /AutoIt3ExecuteScript C:\streamer\stream.txt | C:\streamer\streamer.exe | — | cmd.exe | |||||||||||
User: admin Company: Carifred Integrity Level: MEDIUM Description: Ultra Virus Killer AutoIt script parser Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
1 006
Read events
943
Write events
63
Delete events
0
Modification events
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\malware.7z | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
2
Suspicious files
43
Text files
24
Unknown types
34
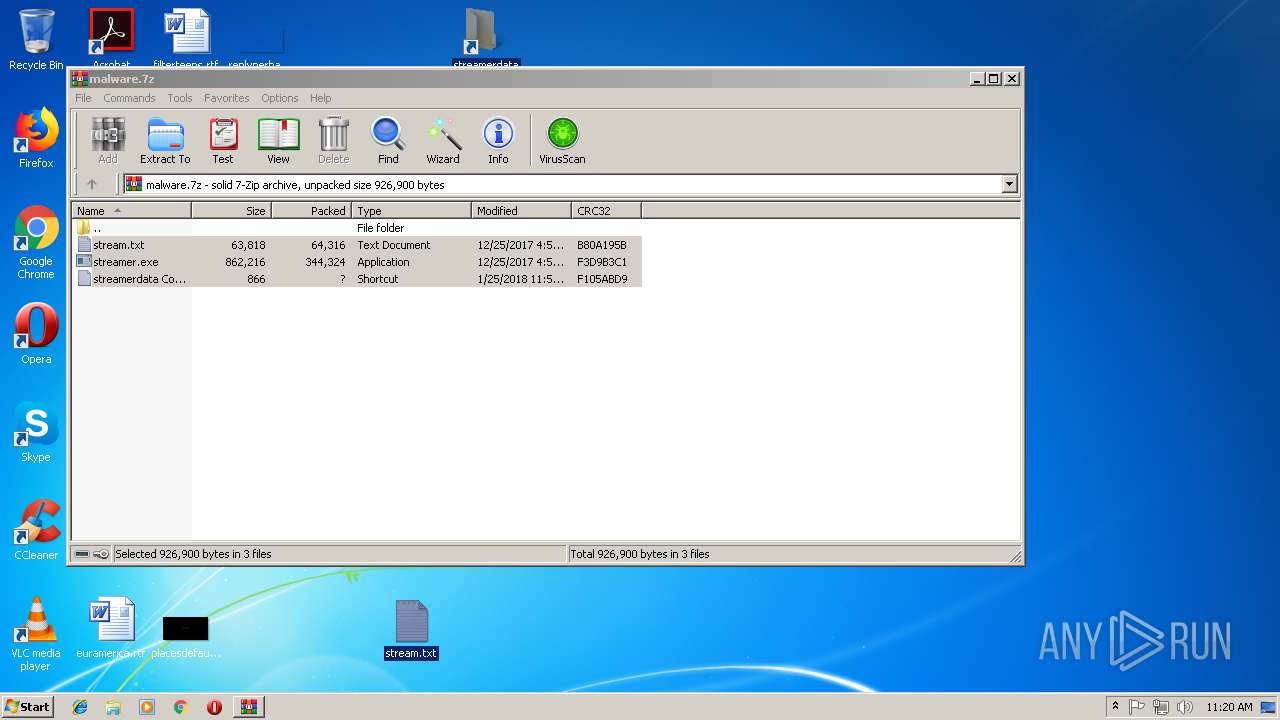
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2532 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2532.1354\stream.txt | — | |
MD5:— | SHA256:— | |||
| 2532 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2532.1354\streamerdata Copy.lnk | — | |
MD5:— | SHA256:— | |||
| 2532 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2532.1354\streamer.exe | — | |
MD5:— | SHA256:— | |||
| 3332 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3332 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 3332 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3332 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3332 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3332 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2912 | streamer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\0[1].txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
16
DNS requests
50
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2912 | streamer.exe | GET | — | 176.9.47.165:8393 | http://newage.newminersage.com:8393/303430392D2D5838362D33333030353337393237/1/0/0 | DE | — | — | suspicious |
2912 | streamer.exe | GET | 200 | 176.9.47.165:8393 | http://newage.newminersage.com:8393/303430392D2D5838362D33333030353337393237/1/0/0 | DE | text | 50 b | suspicious |
2912 | streamer.exe | GET | 200 | 176.9.47.165:8393 | http://newage.newminersage.com:8393/303430392D2D5838362D33333030353337393237/1/0/0 | DE | text | 50 b | suspicious |
2912 | streamer.exe | GET | 200 | 176.9.47.165:8393 | http://newage.newminersage.com:8393/303430392D2D5838362D33333030353337393237/1/0/0 | DE | text | 50 b | suspicious |
2912 | streamer.exe | GET | 200 | 176.9.47.165:8393 | http://newage.newminersage.com:8393/303430392D2D5838362D33333030353337393237/1/0/0 | DE | text | 50 b | suspicious |
2912 | streamer.exe | GET | 200 | 176.9.47.165:8393 | http://newage.newminersage.com:8393/303430392D2D5838362D33333030353337393237/1/0/0 | DE | text | 50 b | suspicious |
3332 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3332 | firefox.exe | POST | 200 | 216.58.211.110:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 463 b | whitelisted |
3332 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3332 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2912 | streamer.exe | 176.9.47.165:8393 | newage.newminersage.com | Hetzner Online GmbH | DE | suspicious |
3332 | firefox.exe | 2.16.186.112:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
3332 | firefox.exe | 54.201.140.246:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3332 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3332 | firefox.exe | 52.39.131.77:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3332 | firefox.exe | 52.85.184.163:443 | snippets.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
3332 | firefox.exe | 34.252.164.43:443 | location.services.mozilla.com | Amazon.com, Inc. | IE | unknown |
3332 | firefox.exe | 216.58.211.110:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3636 | pingsender.exe | 52.11.162.210:443 | incoming.telemetry.mozilla.org | Amazon.com, Inc. | US | unknown |
3332 | firefox.exe | 54.201.6.28:443 | shavar.services.mozilla.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
newage.newminersage.com |
| malicious |
detectportal.firefox.com |
| whitelisted |
a1089.d.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
tiles.r53-2.services.mozilla.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2912 | streamer.exe | Potential Corporate Privacy Violation | ET POLICY Autoit Windows Automation tool User-Agent in HTTP Request - Possibly Hostile |
2912 | streamer.exe | Potential Corporate Privacy Violation | ET POLICY Autoit Windows Automation tool User-Agent in HTTP Request - Possibly Hostile |
2912 | streamer.exe | Potential Corporate Privacy Violation | ET POLICY Autoit Windows Automation tool User-Agent in HTTP Request - Possibly Hostile |
2912 | streamer.exe | Potential Corporate Privacy Violation | ET POLICY Autoit Windows Automation tool User-Agent in HTTP Request - Possibly Hostile |
2912 | streamer.exe | Potential Corporate Privacy Violation | ET POLICY Autoit Windows Automation tool User-Agent in HTTP Request - Possibly Hostile |