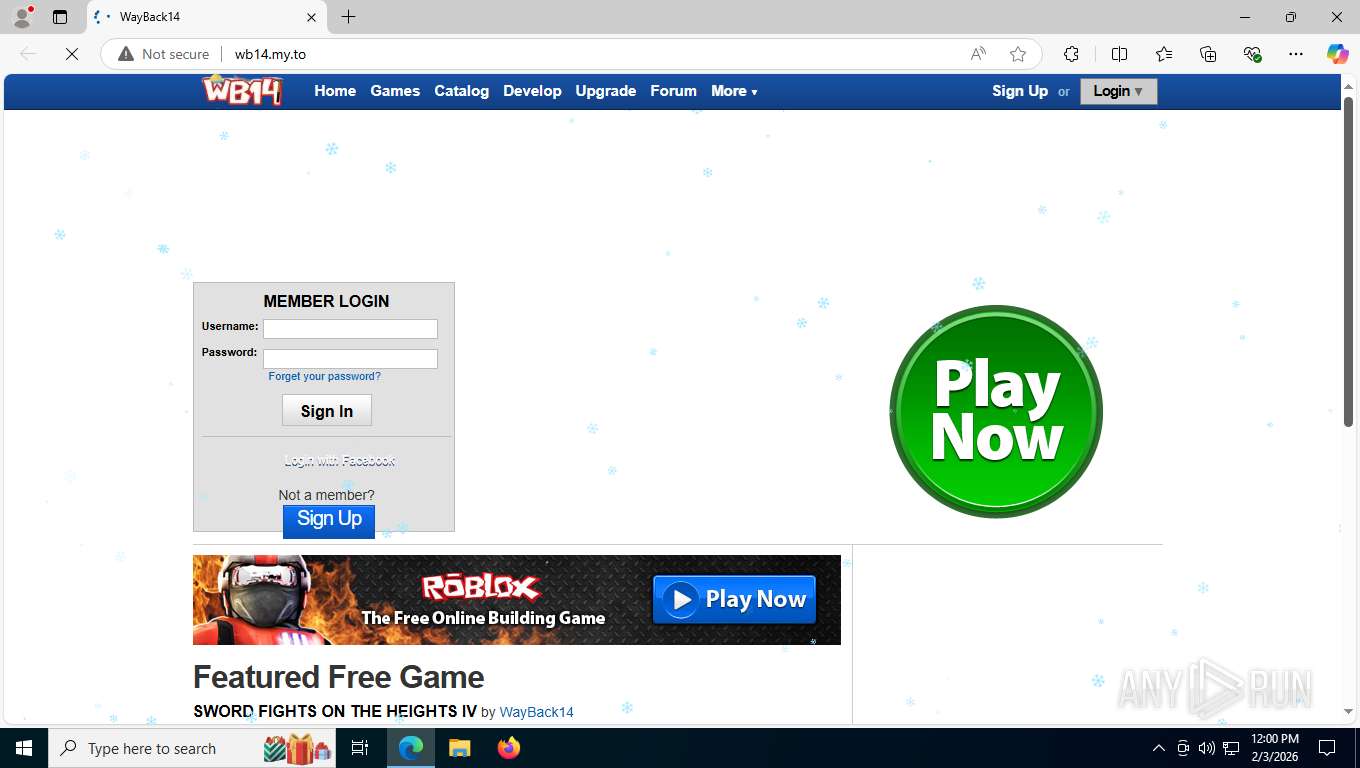
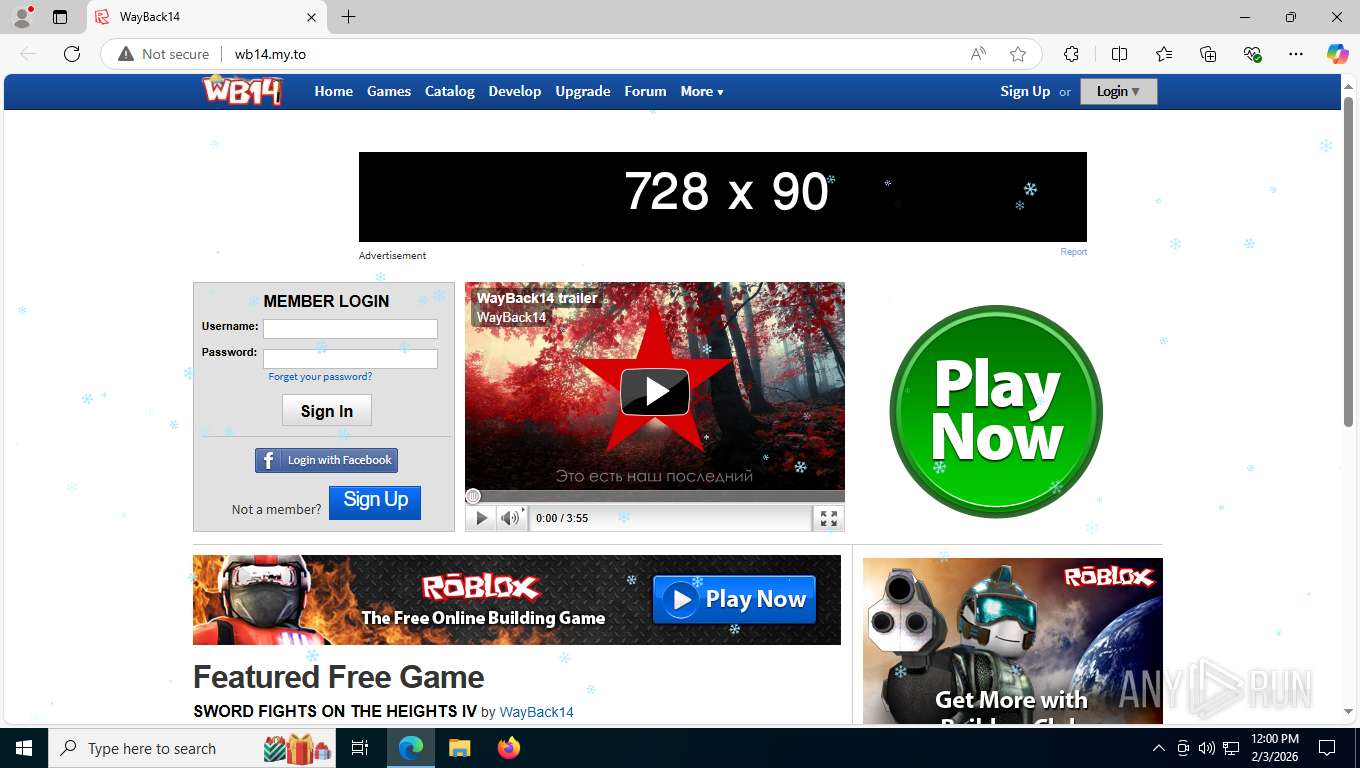
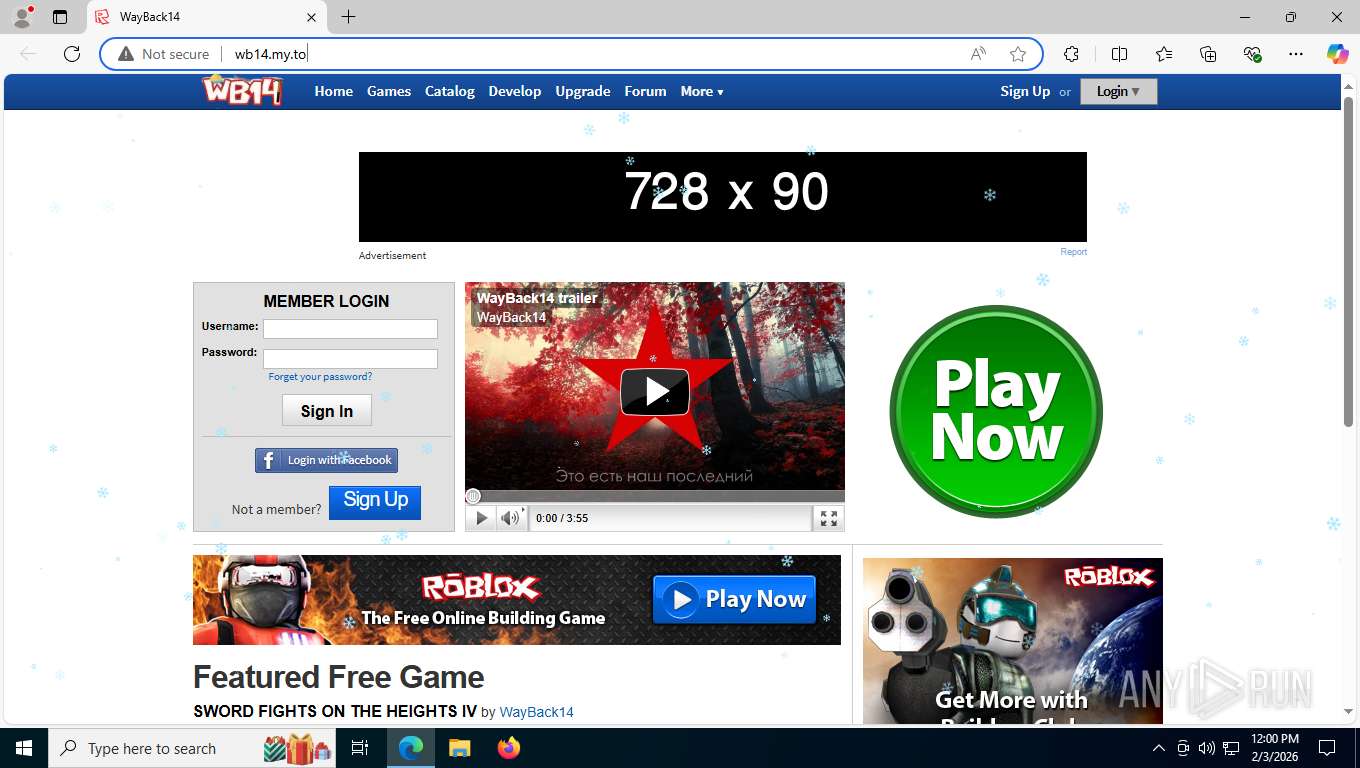
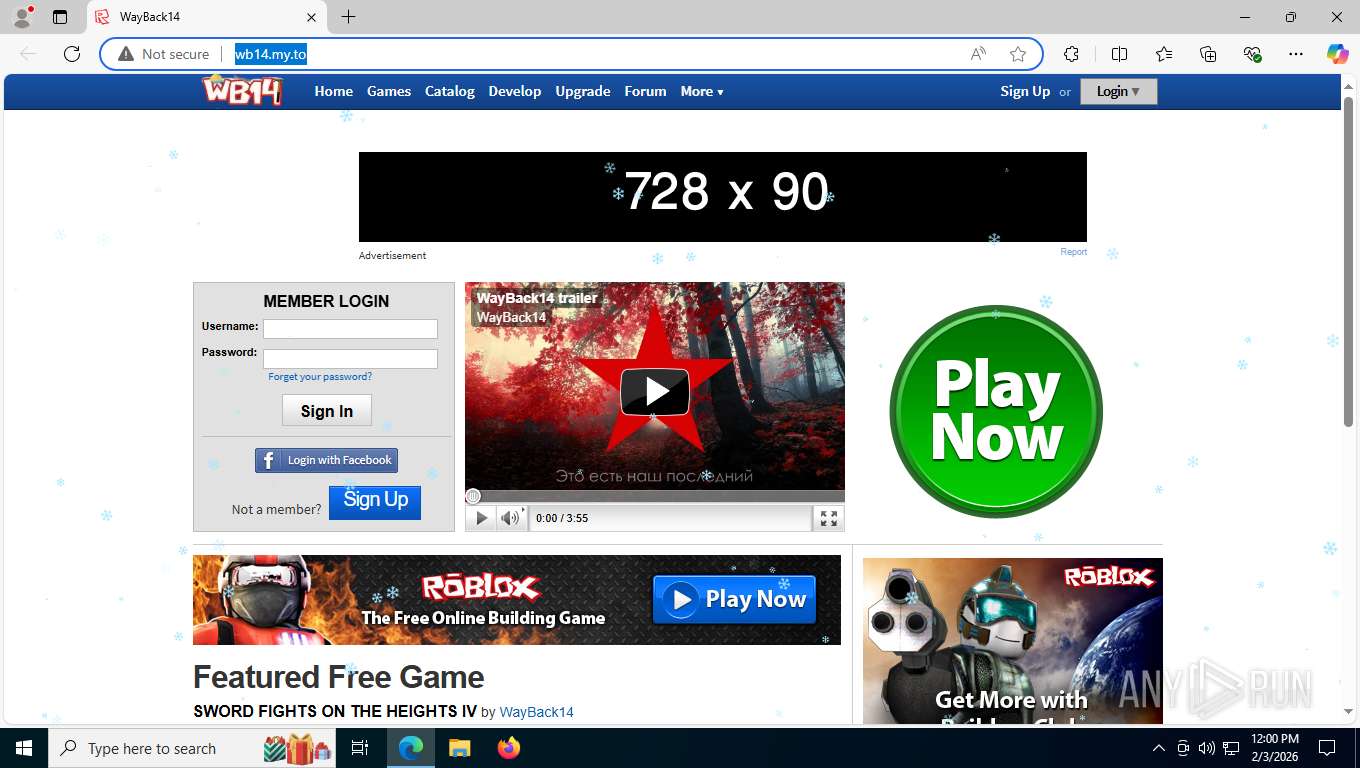
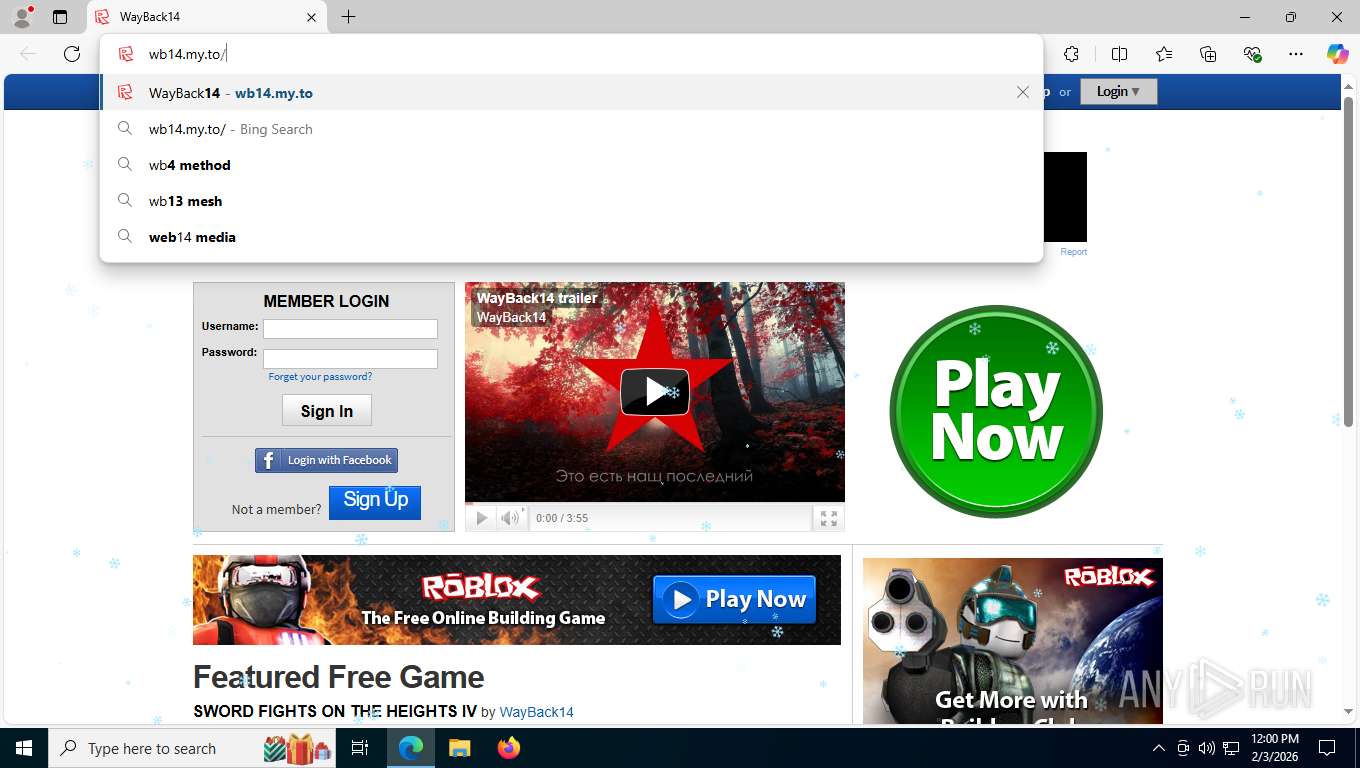
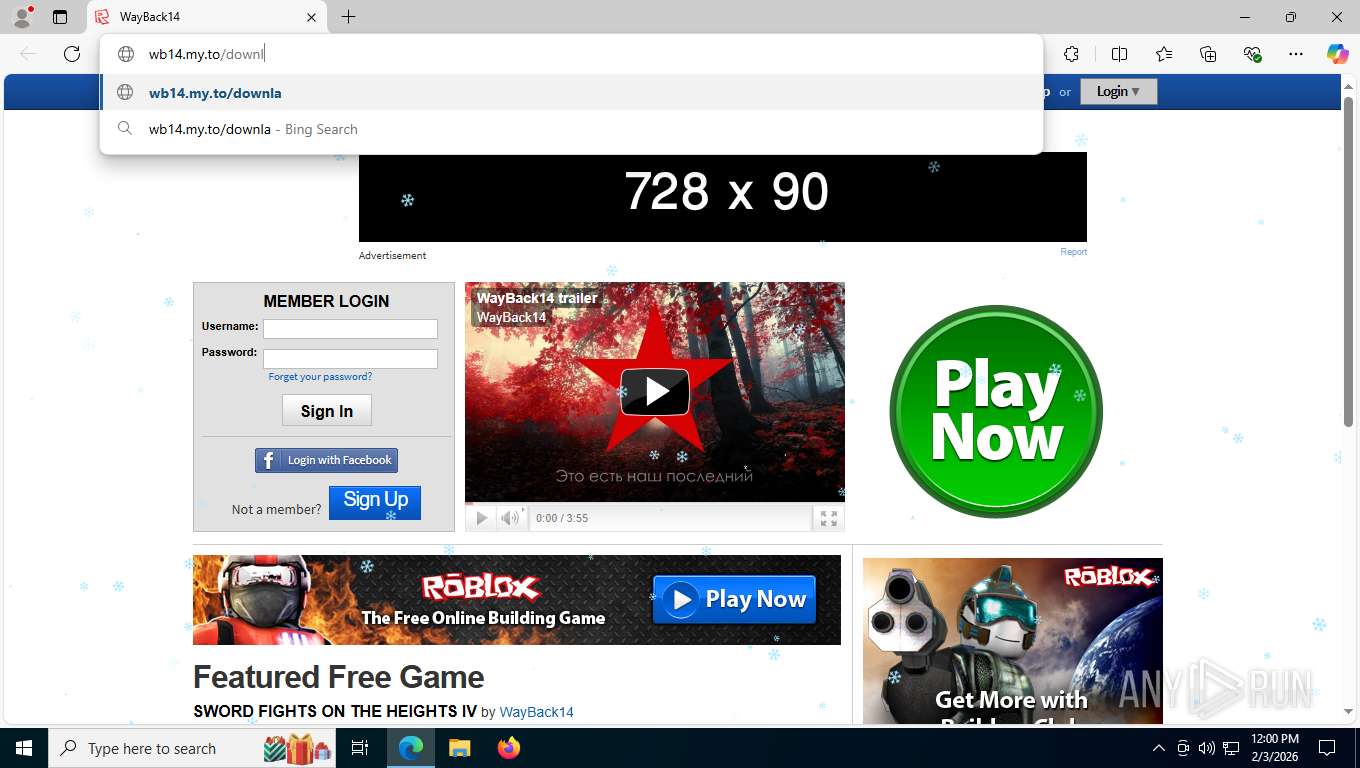
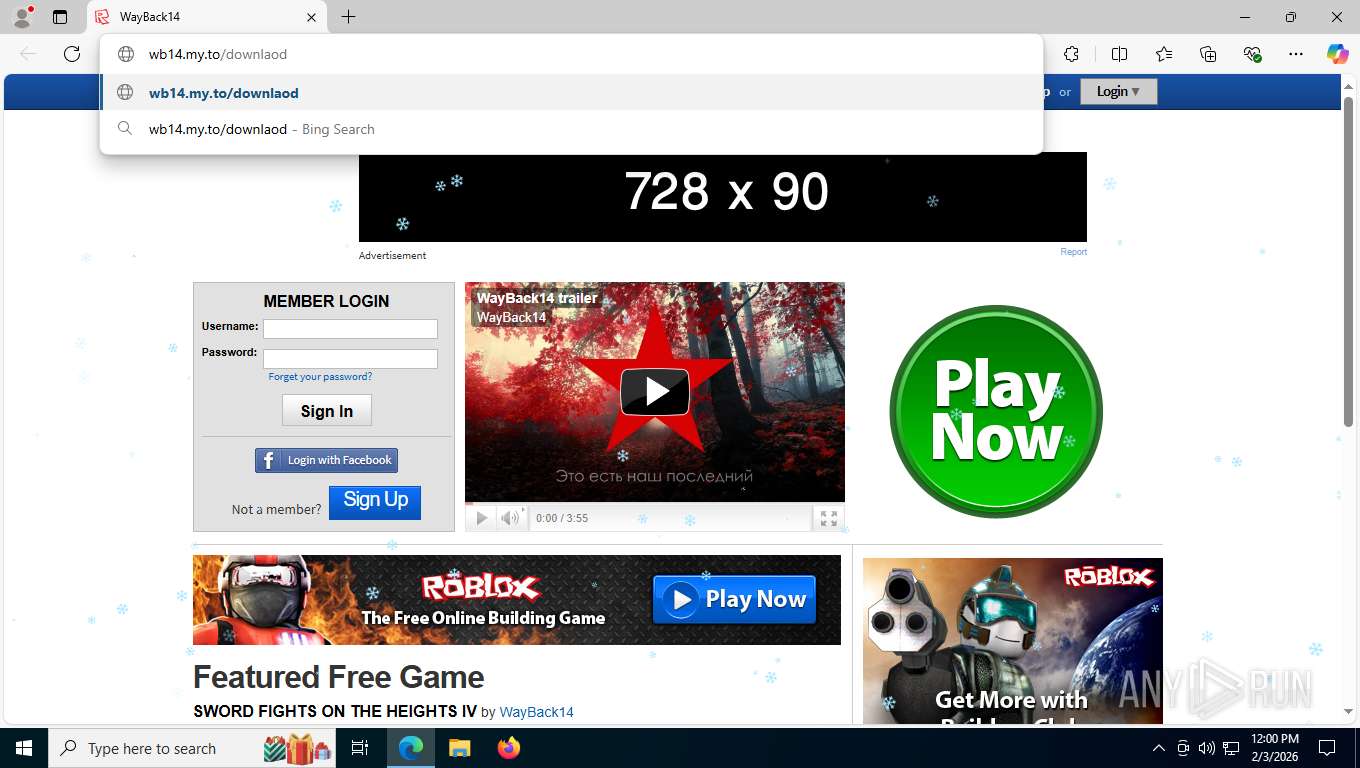
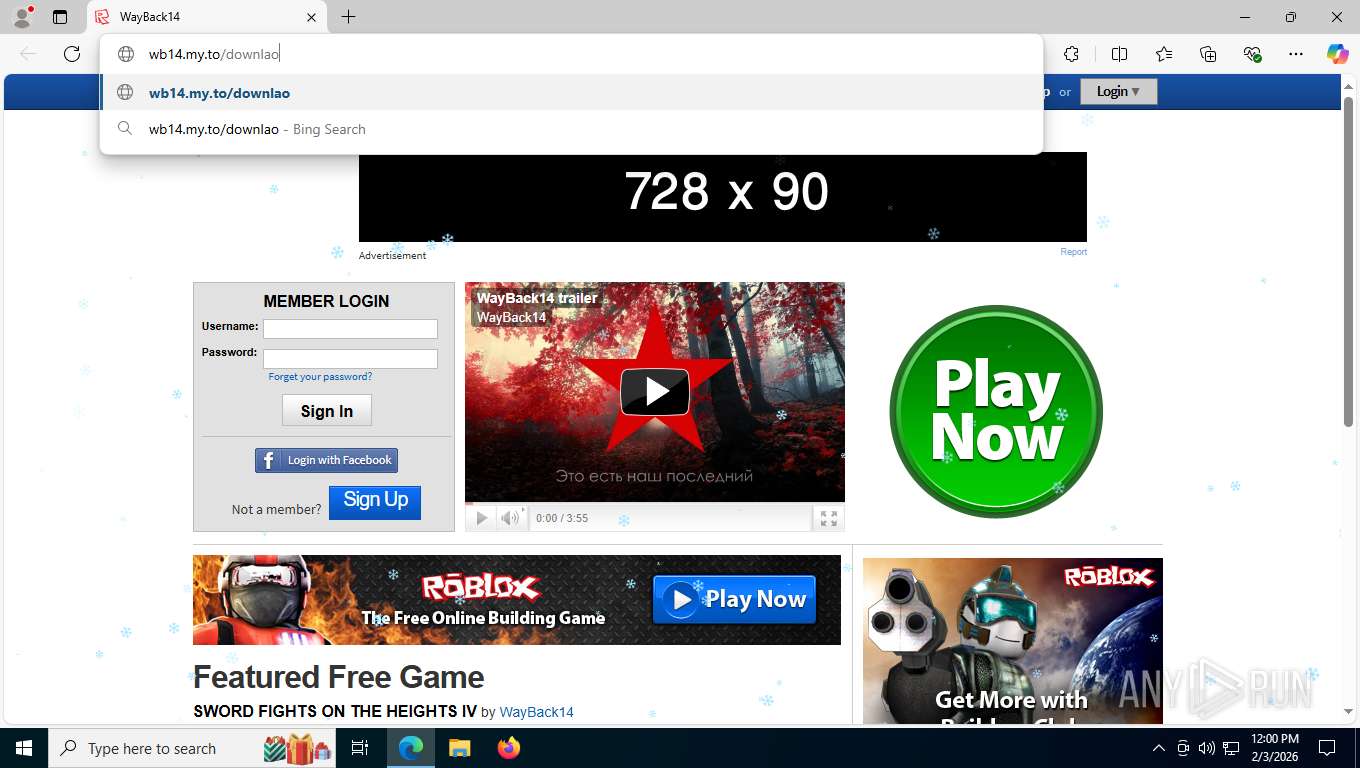
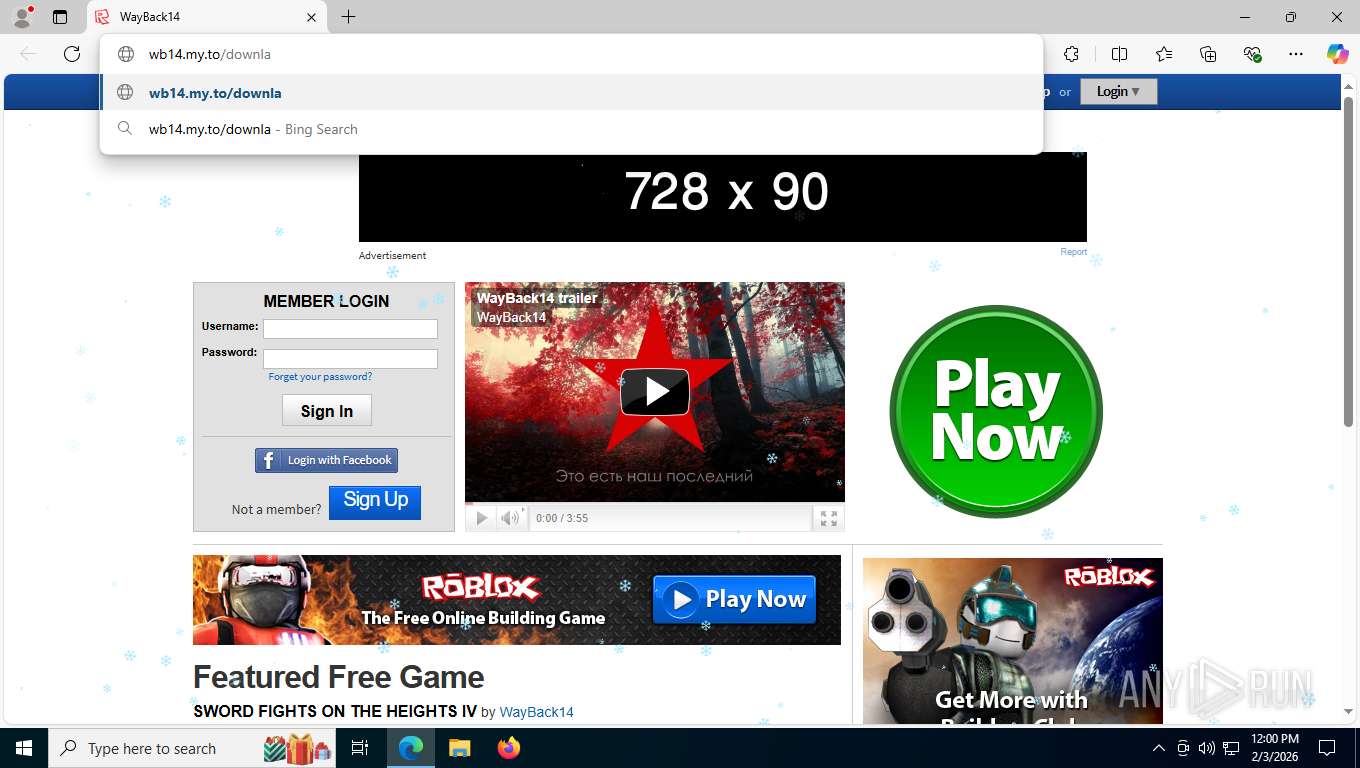
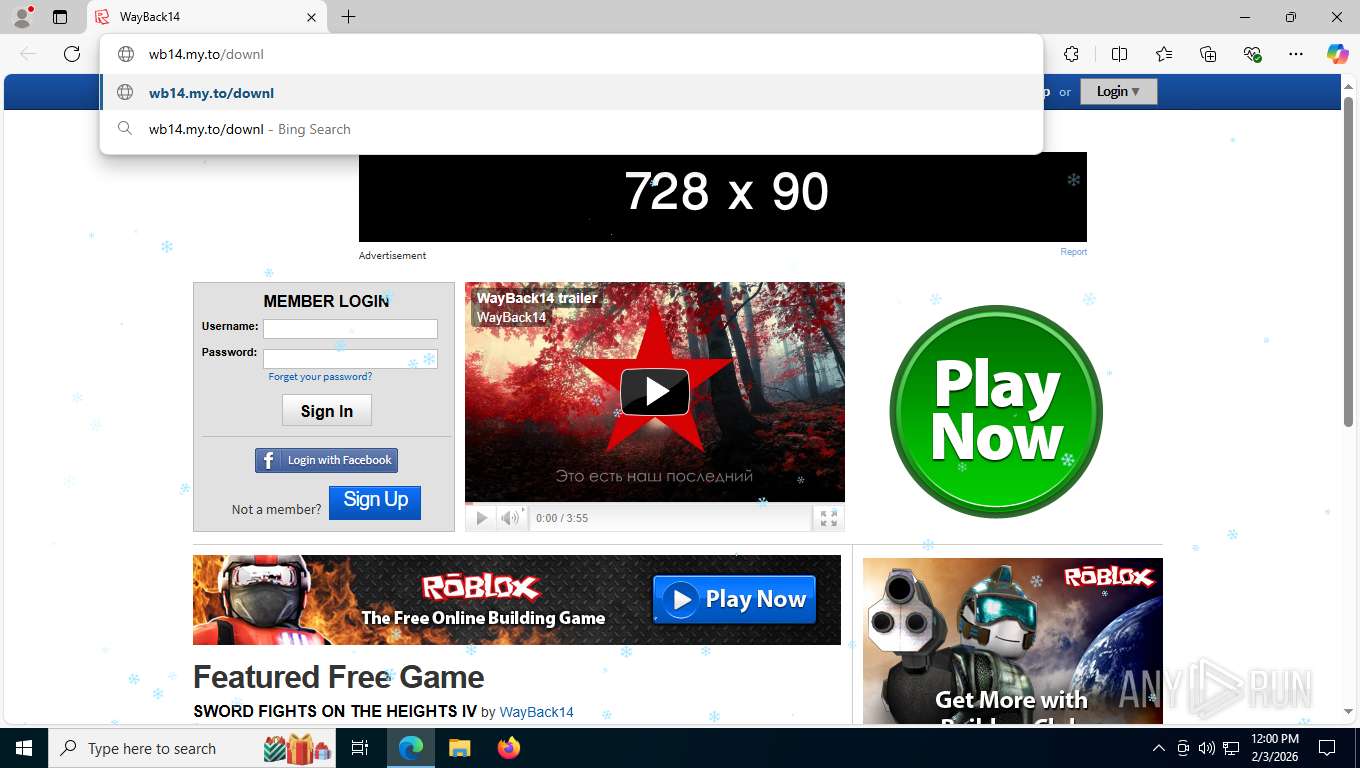
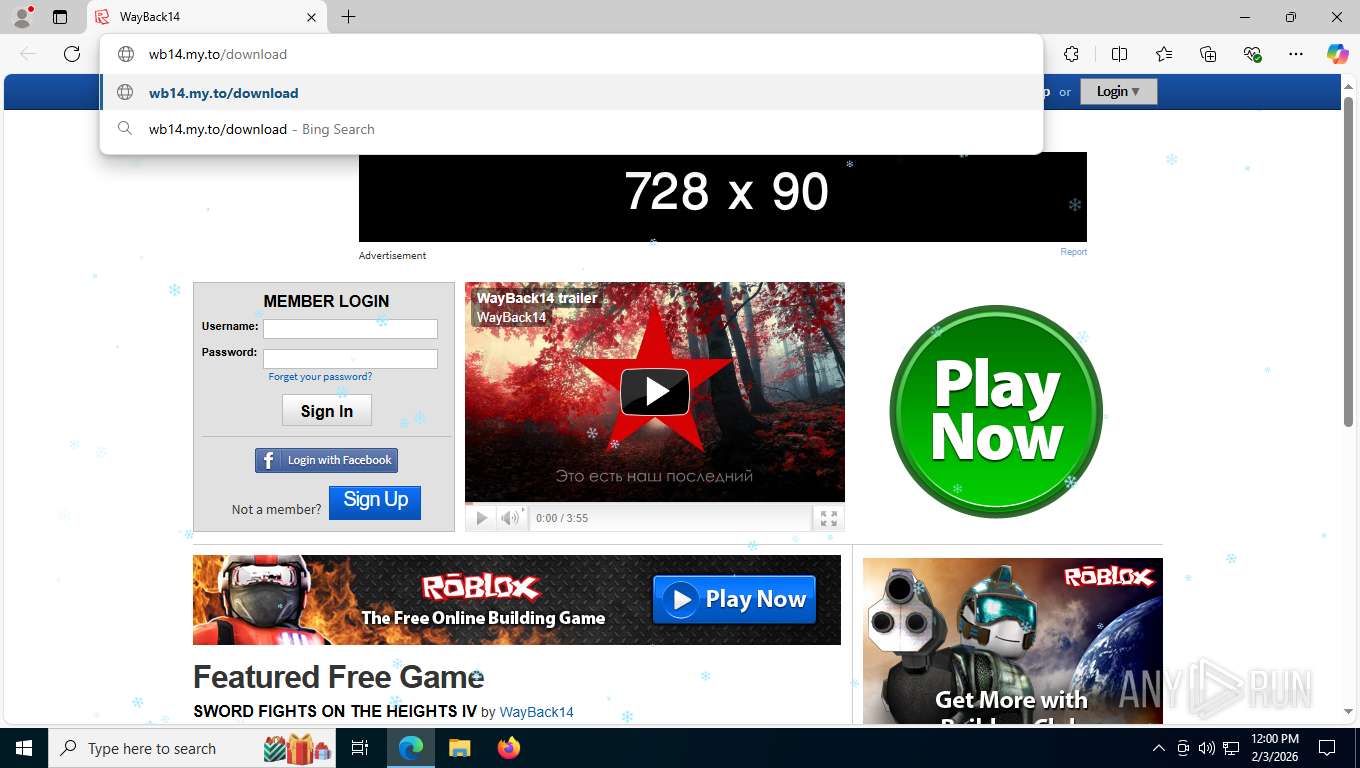
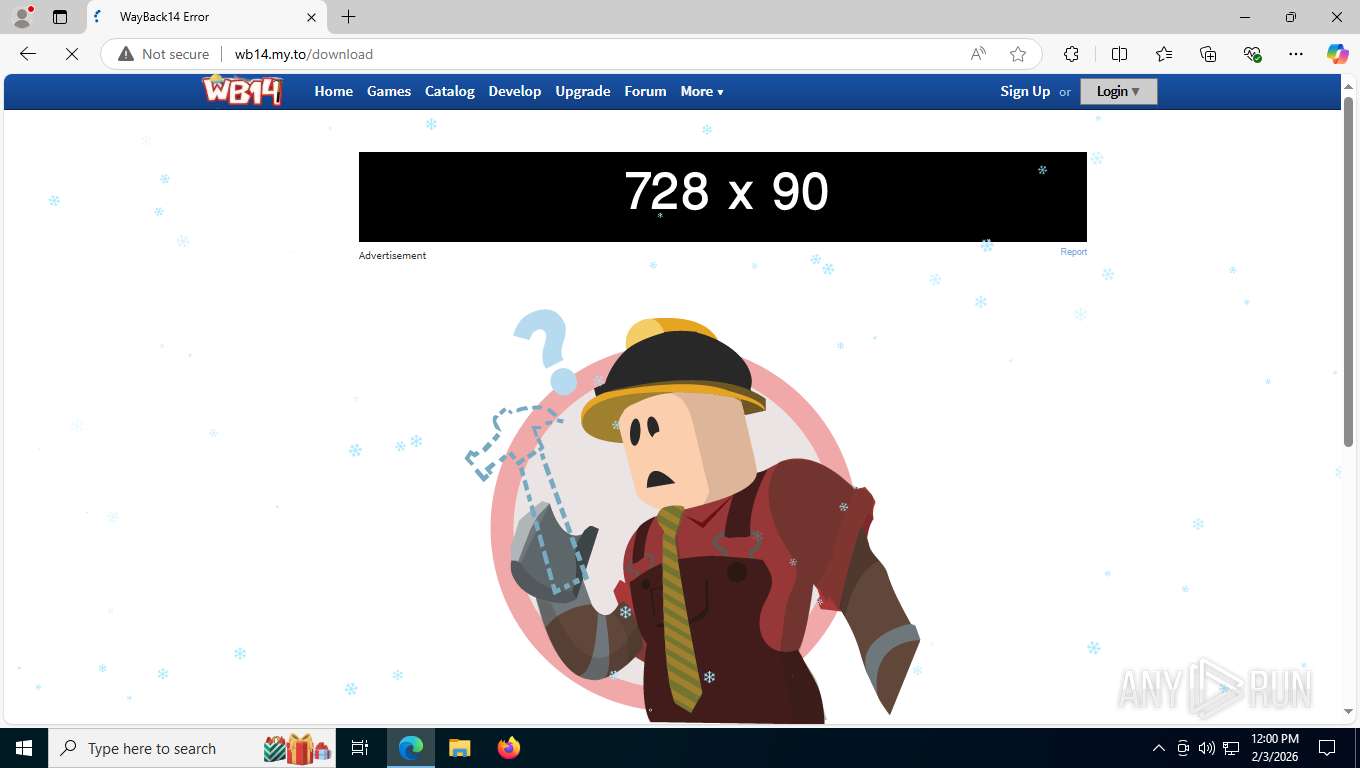
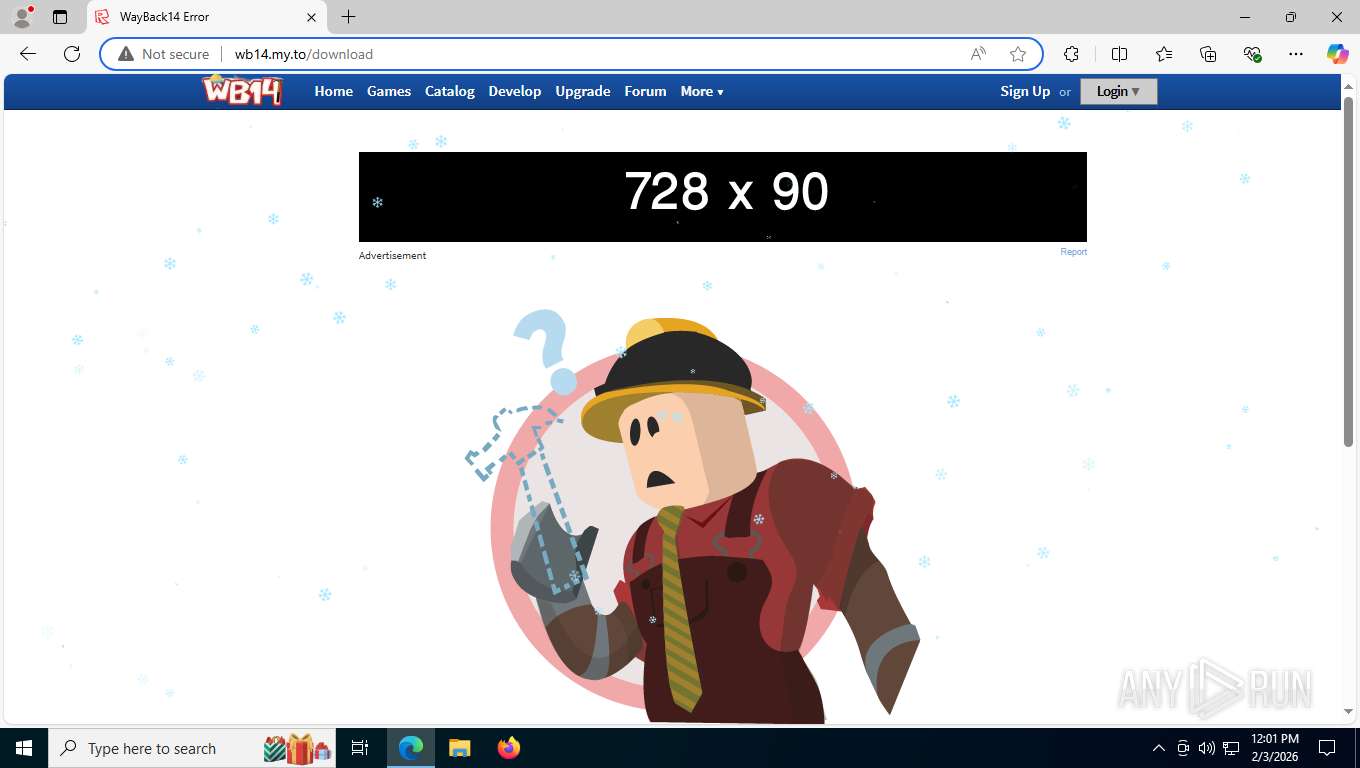
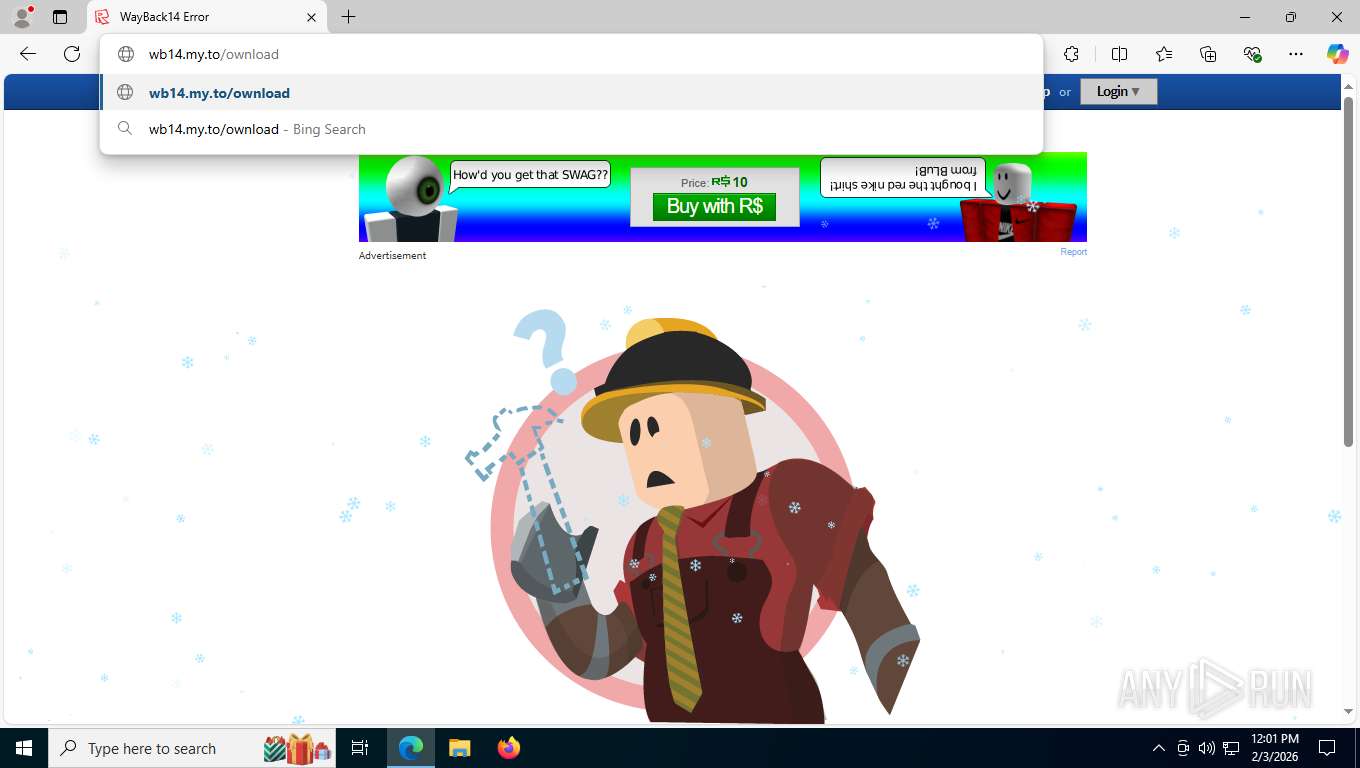
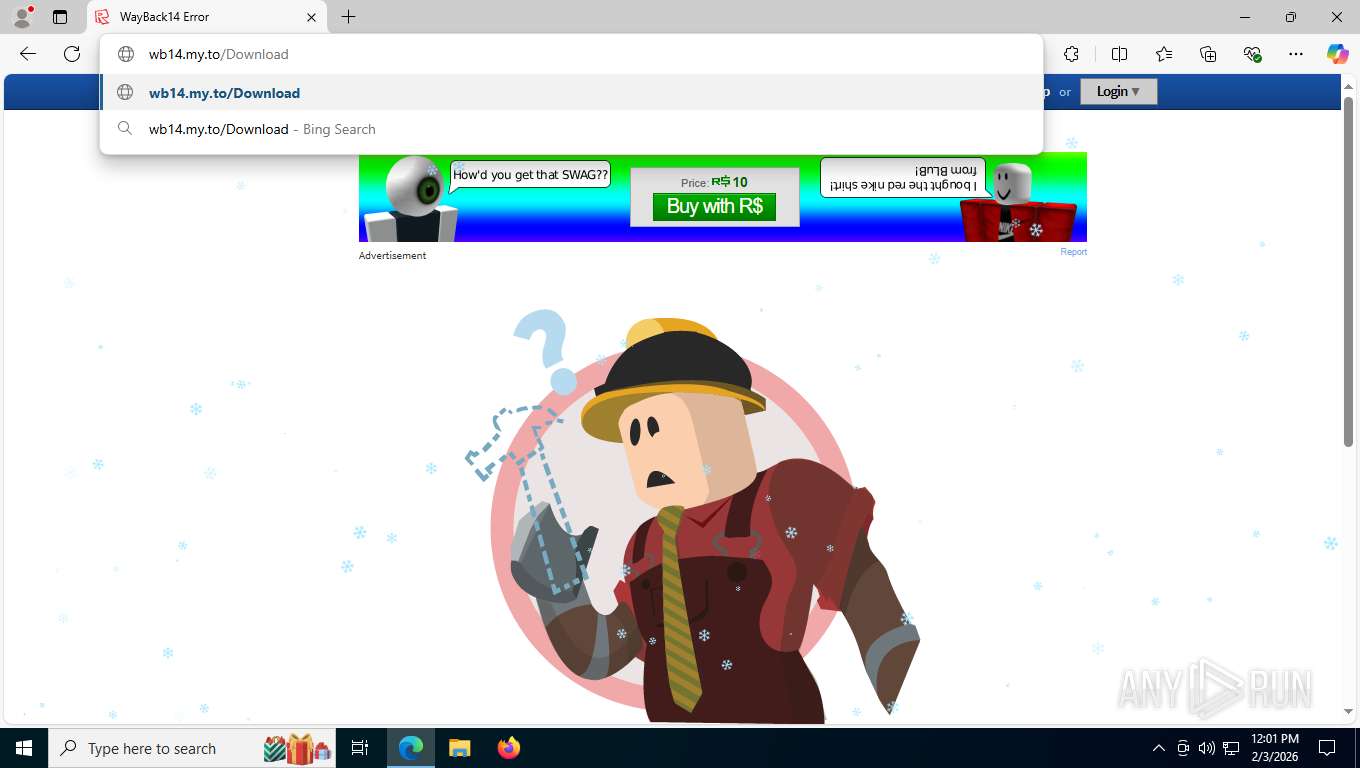
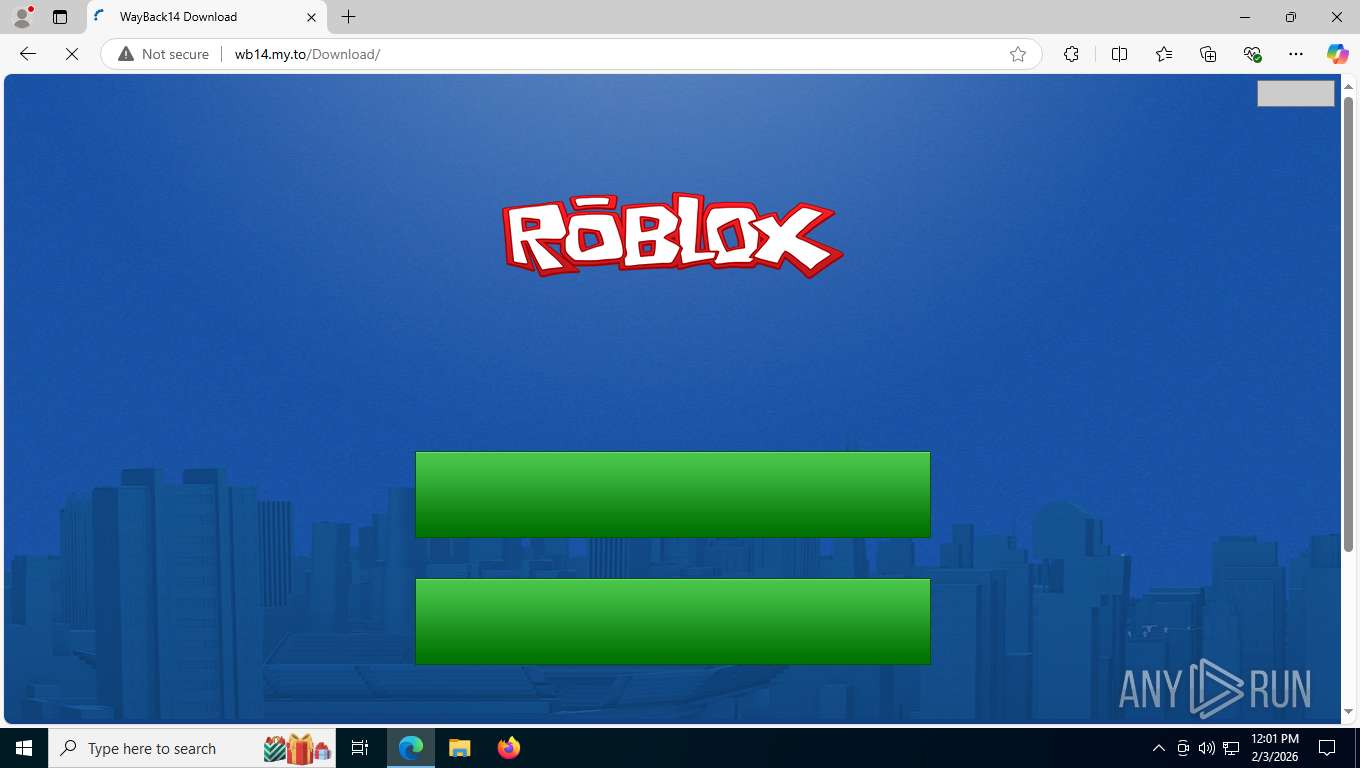
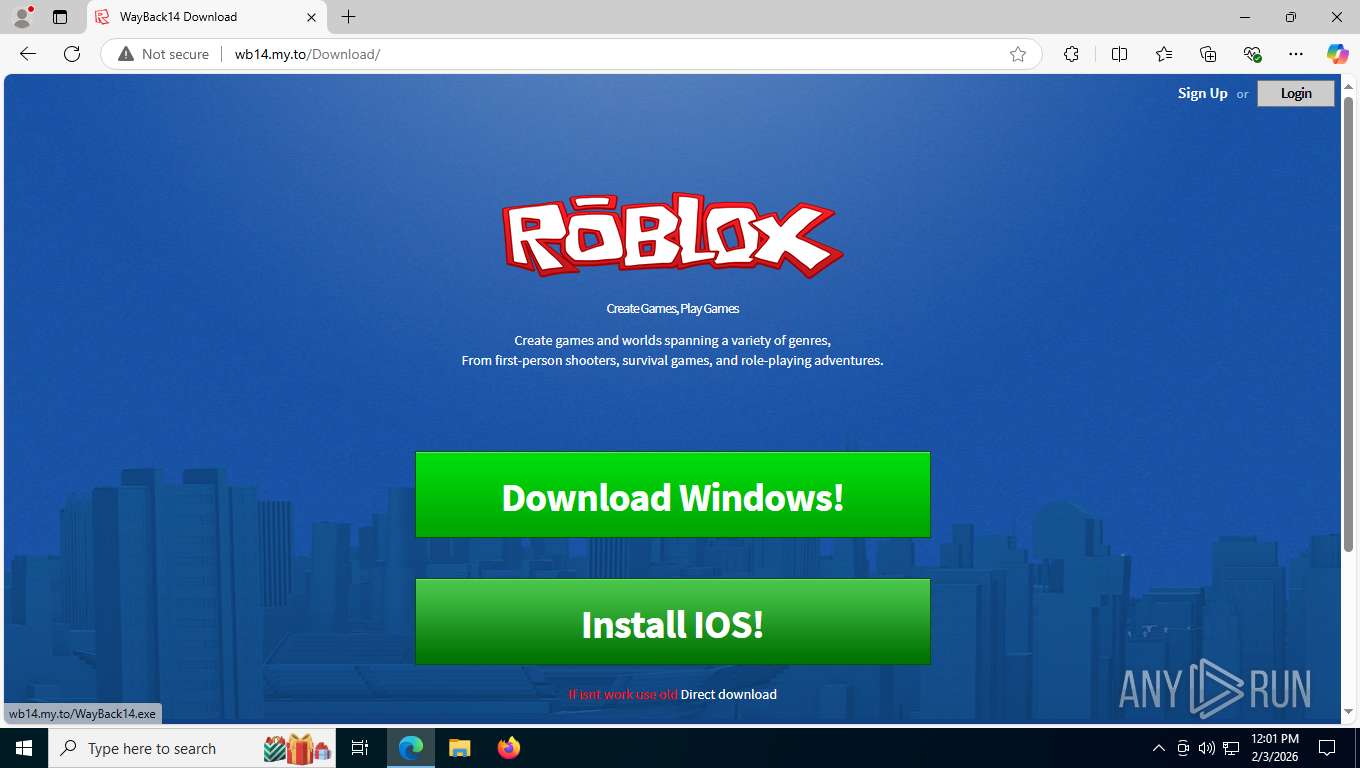
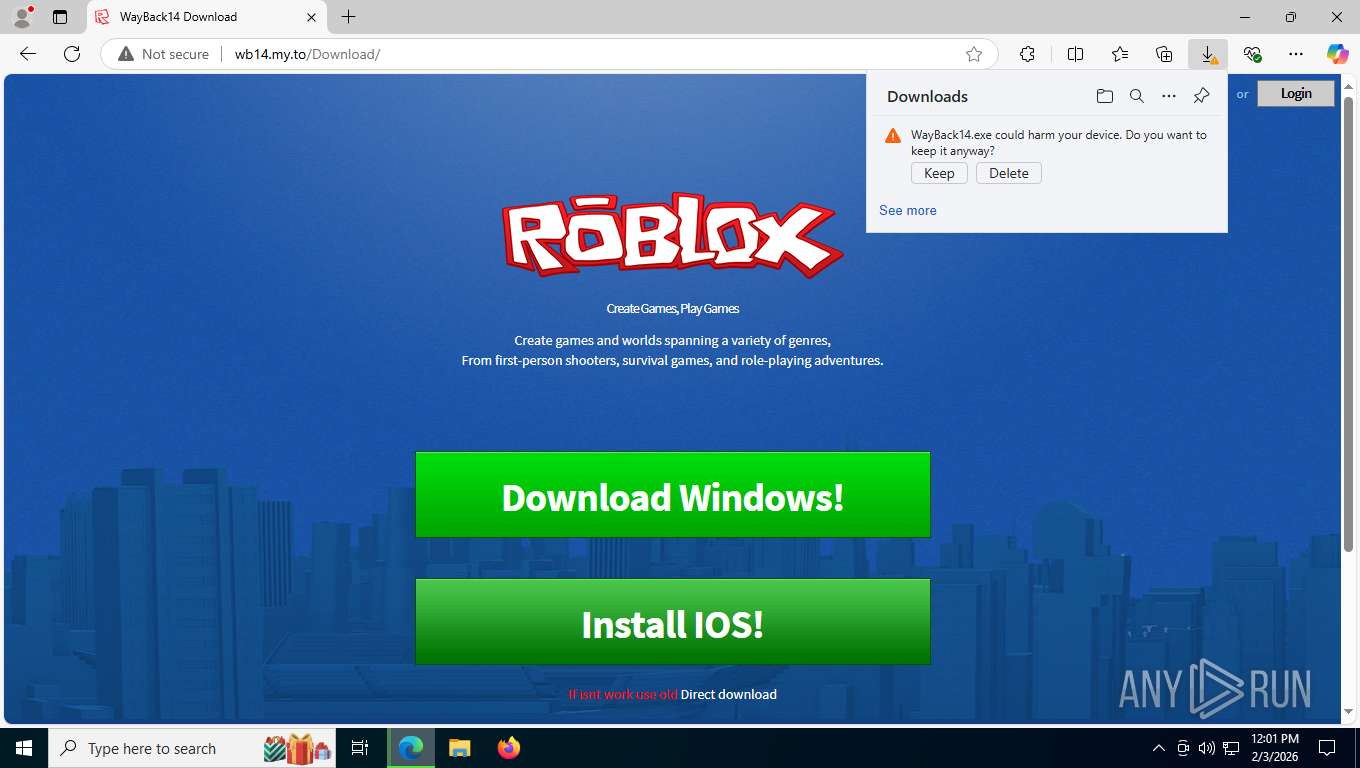
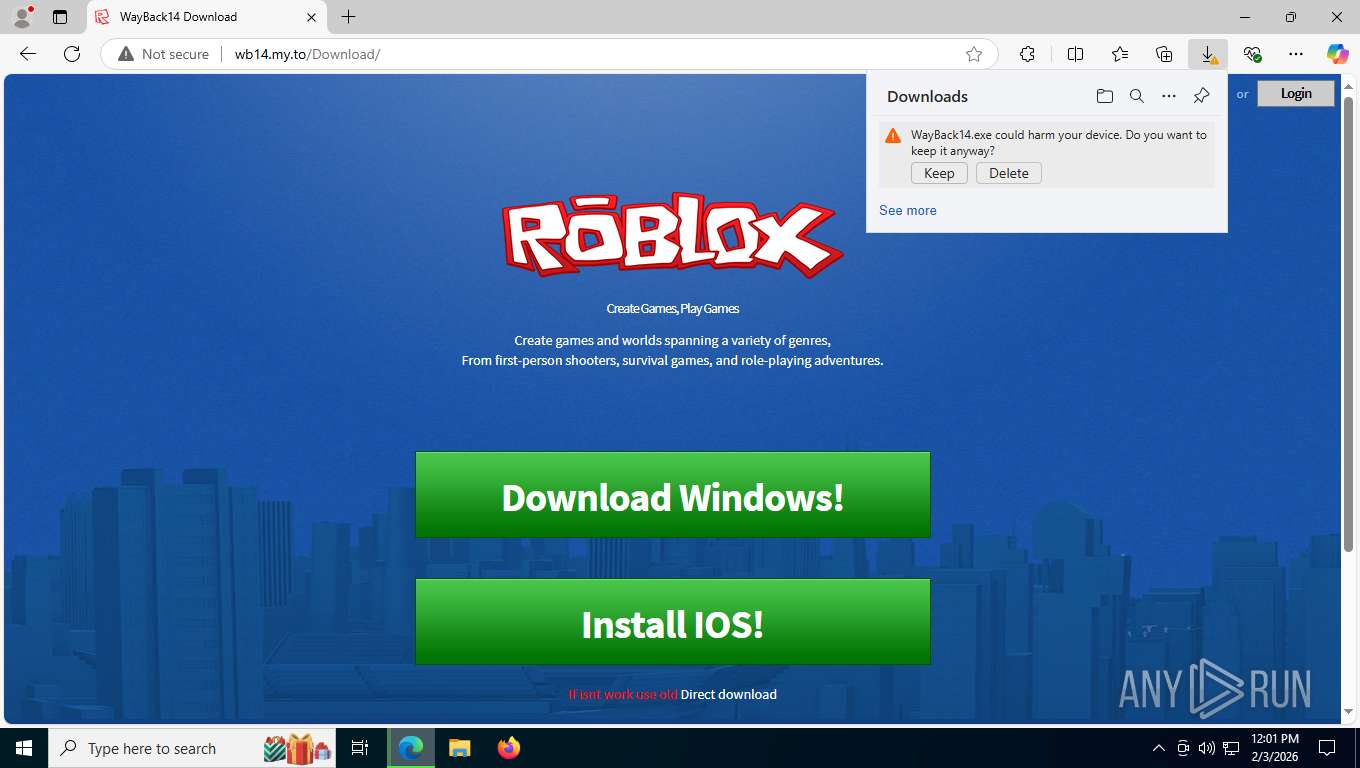
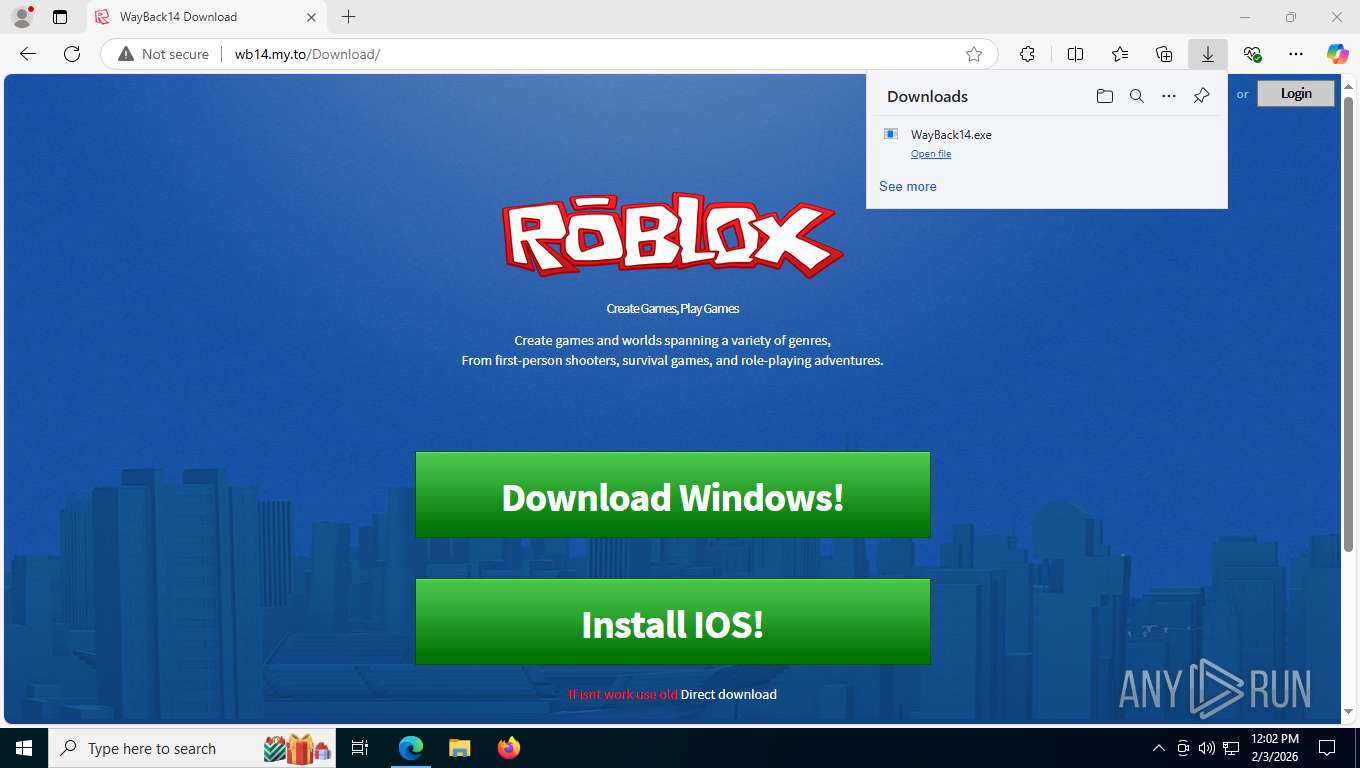
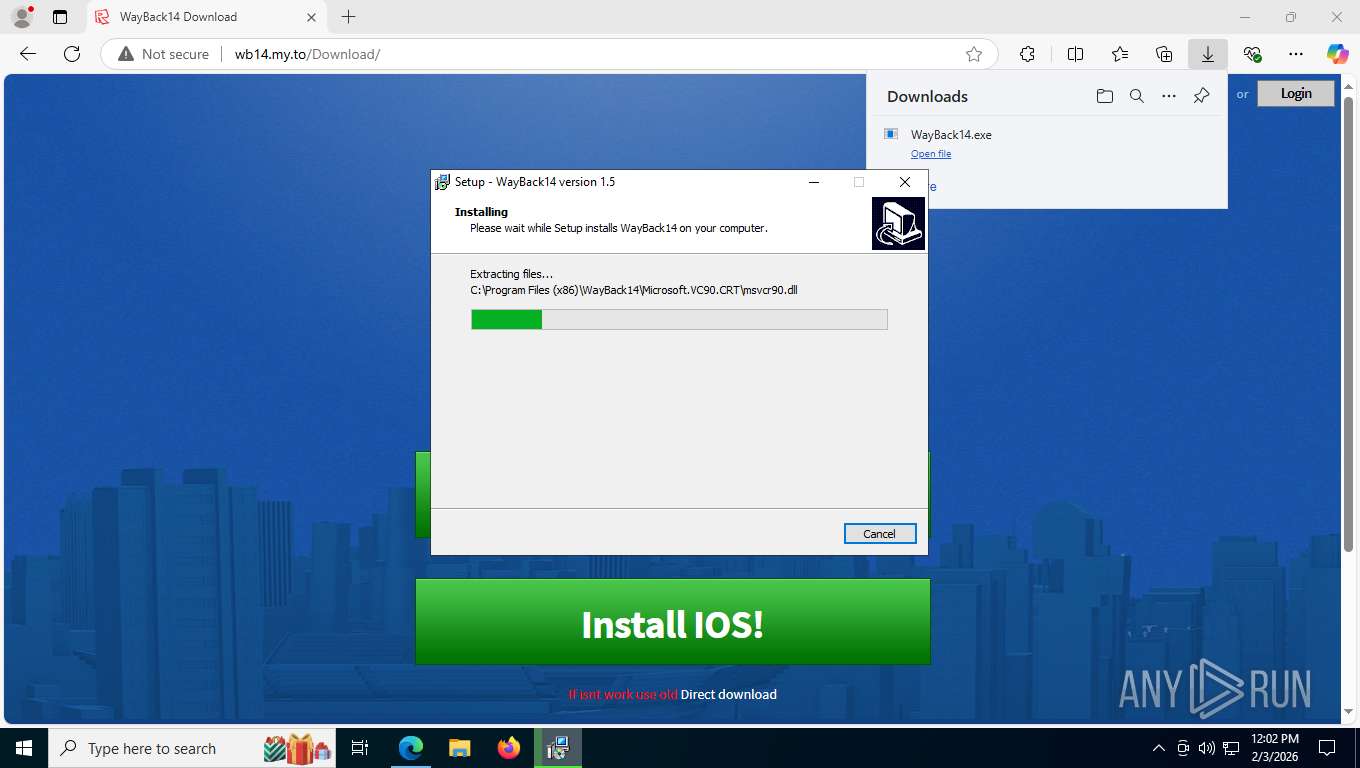
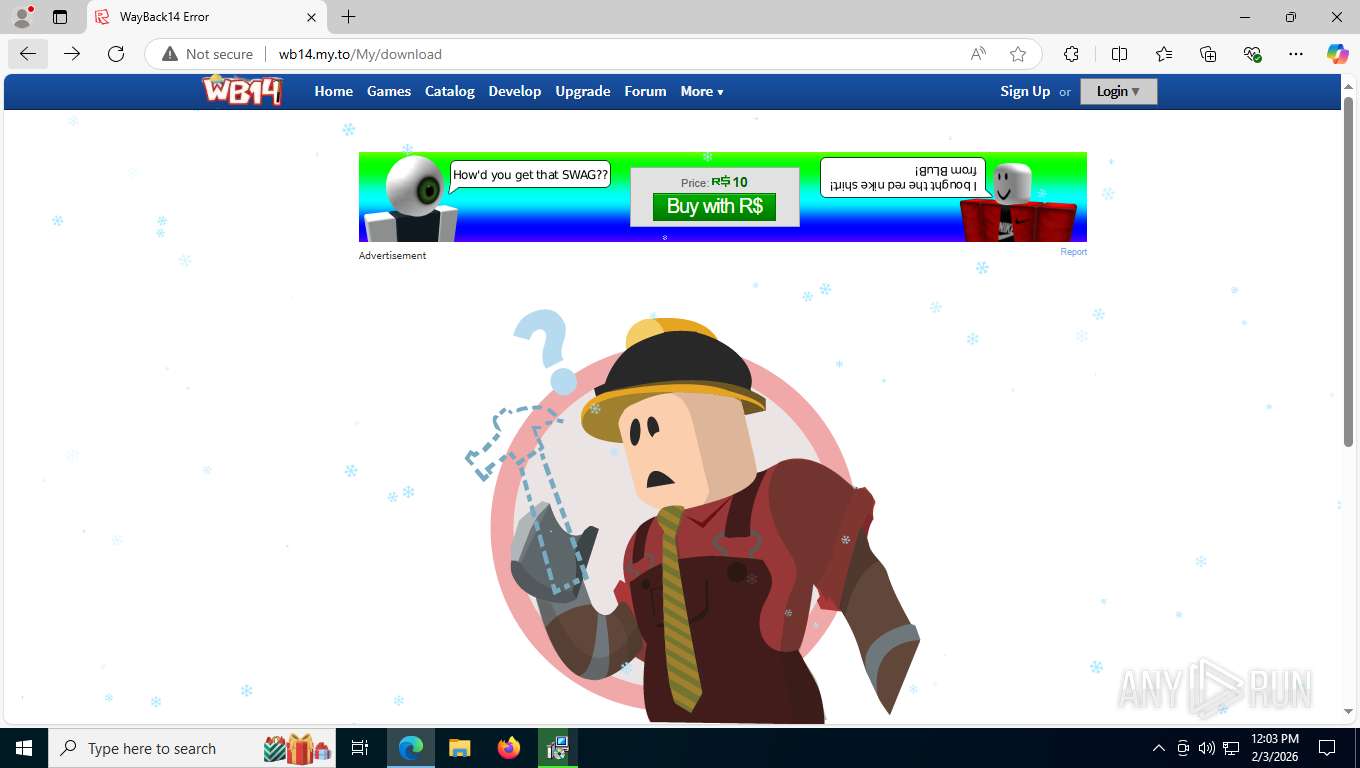
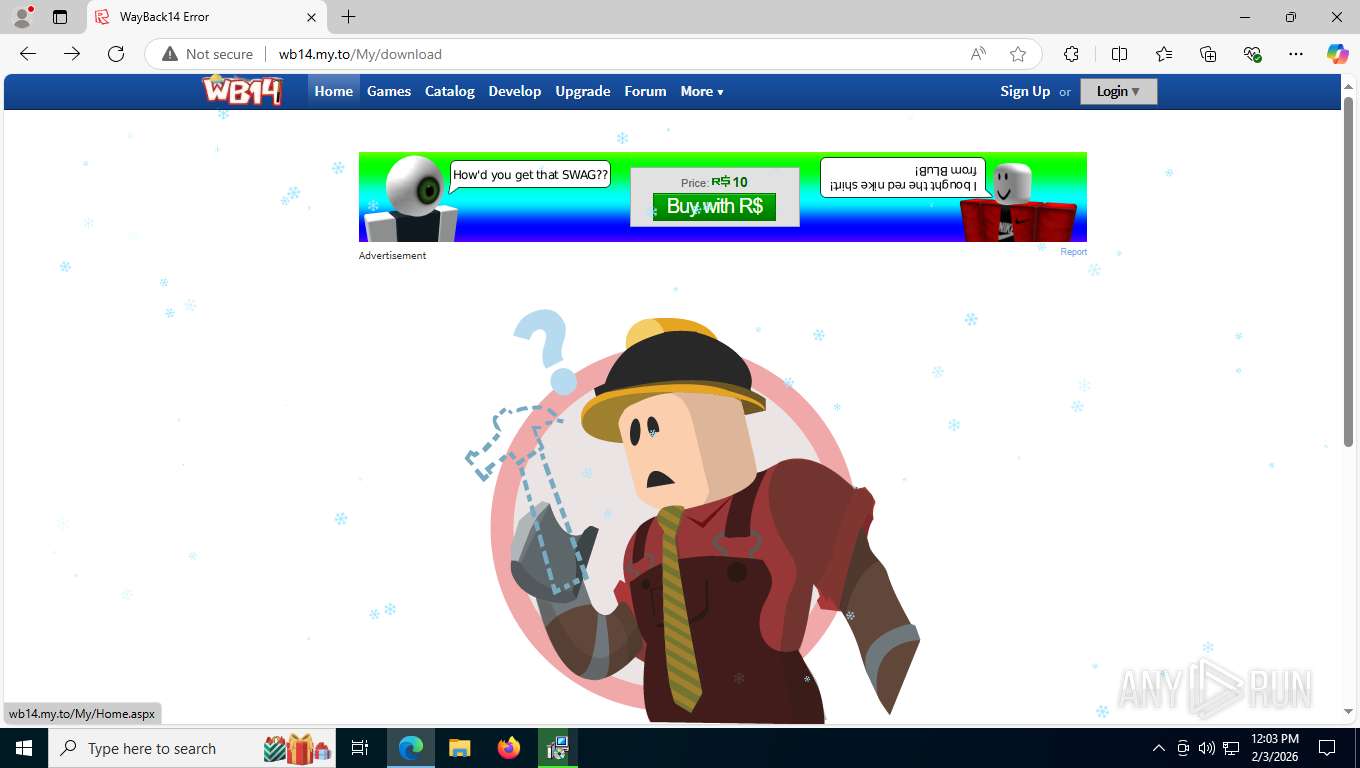
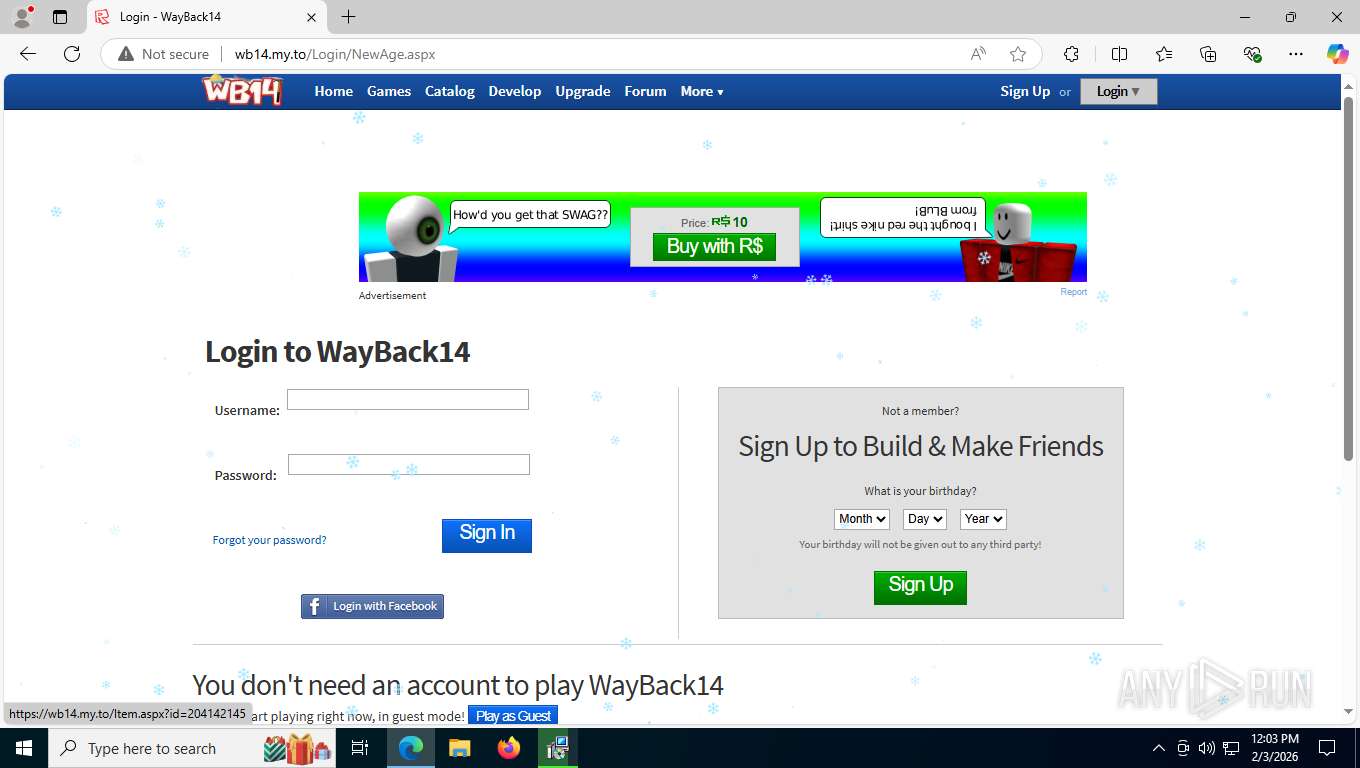
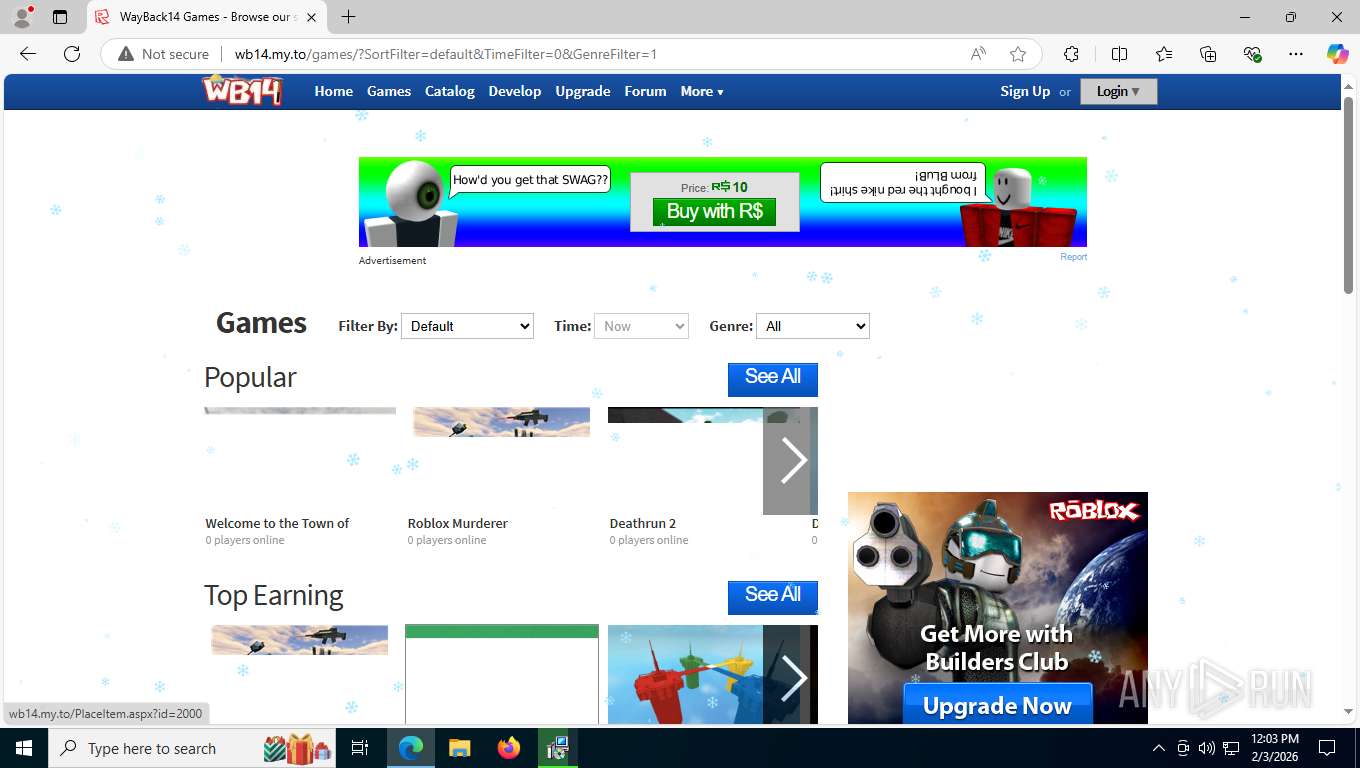
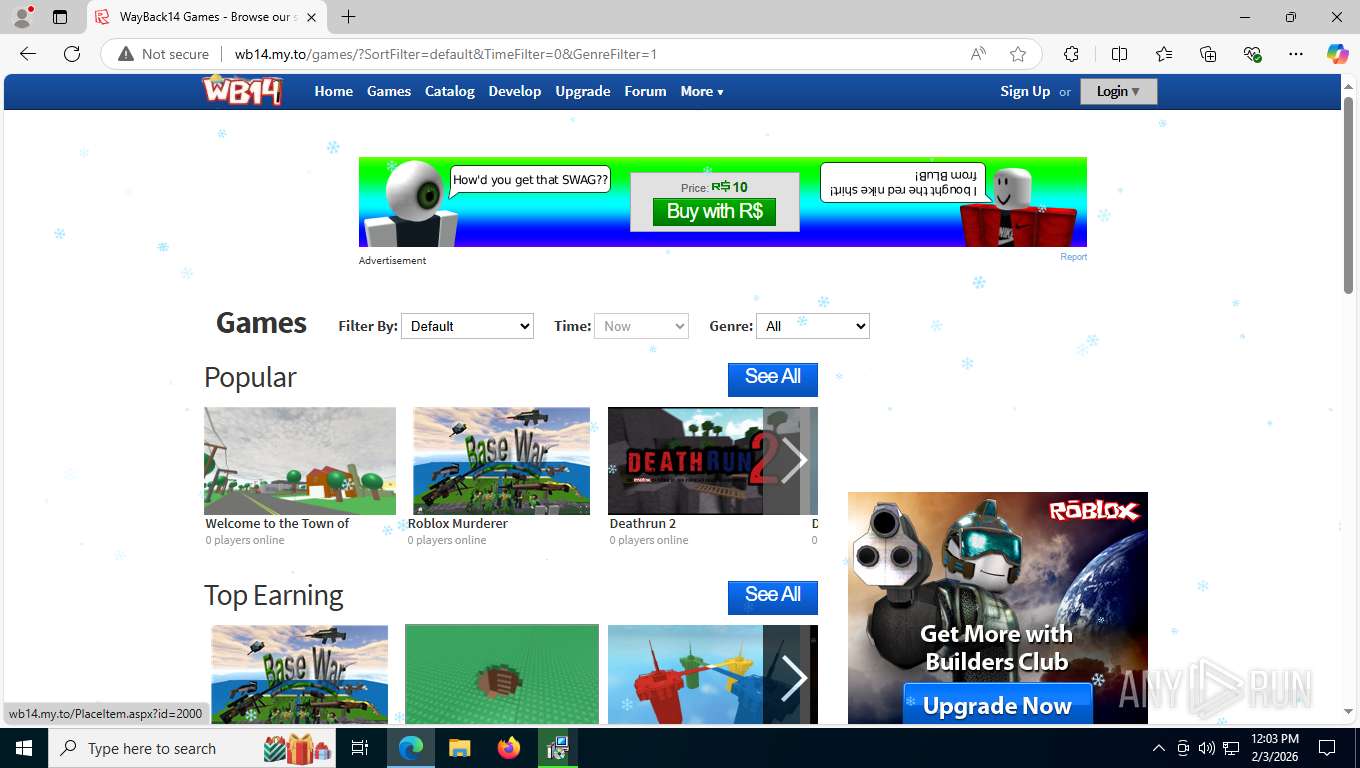
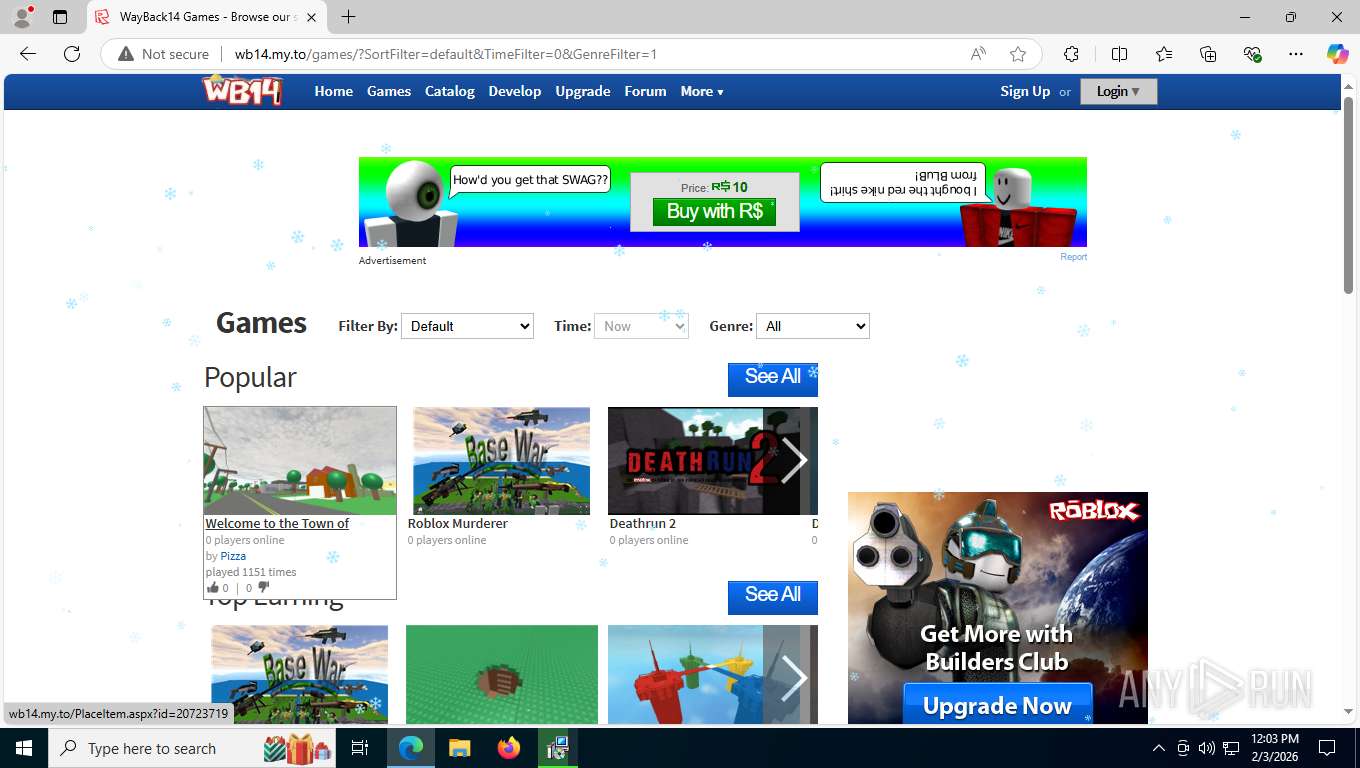
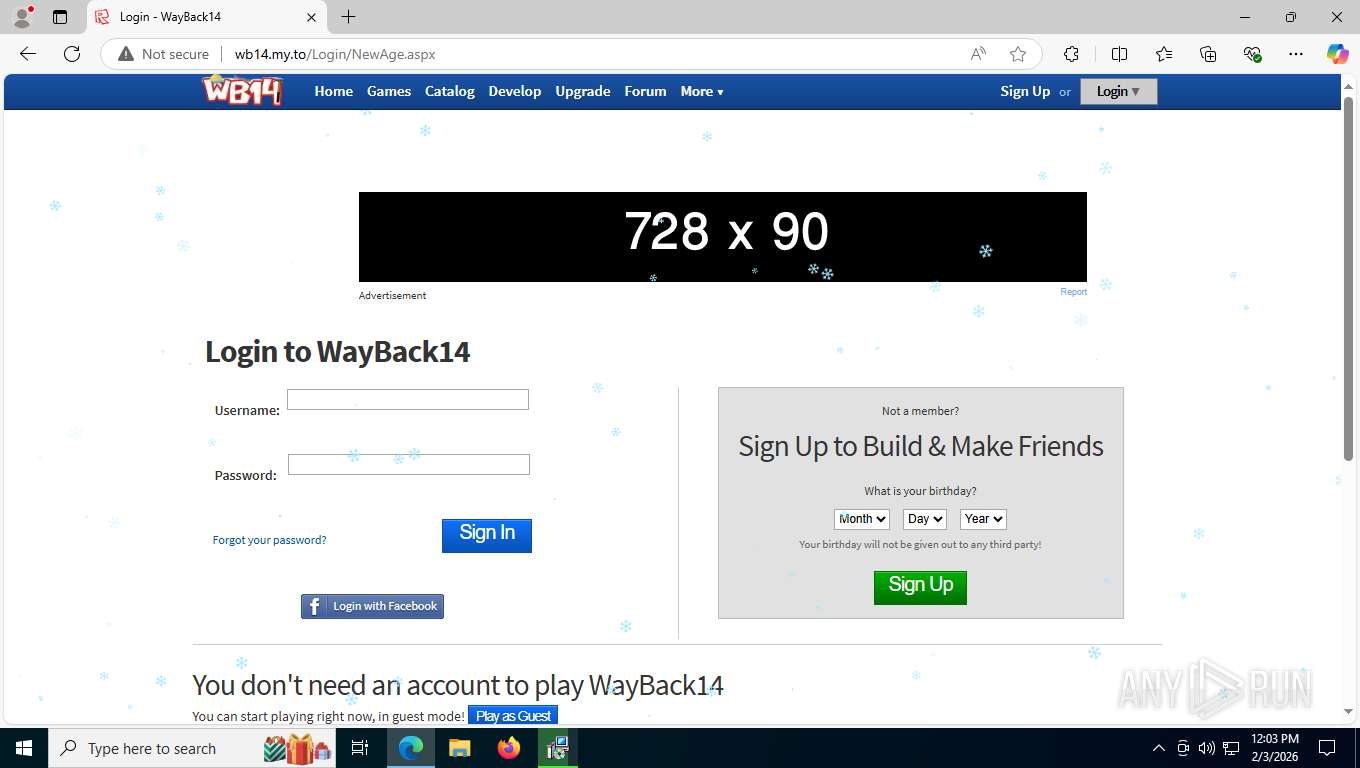
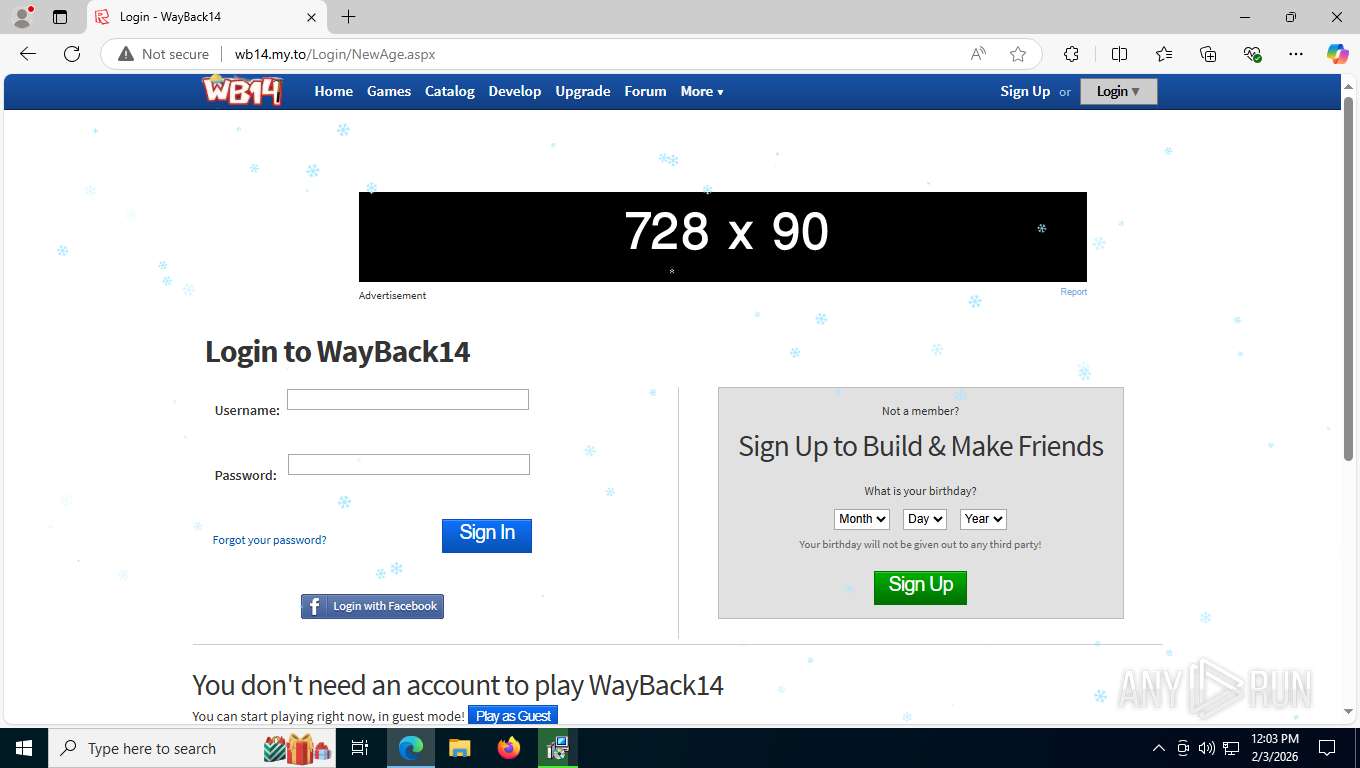
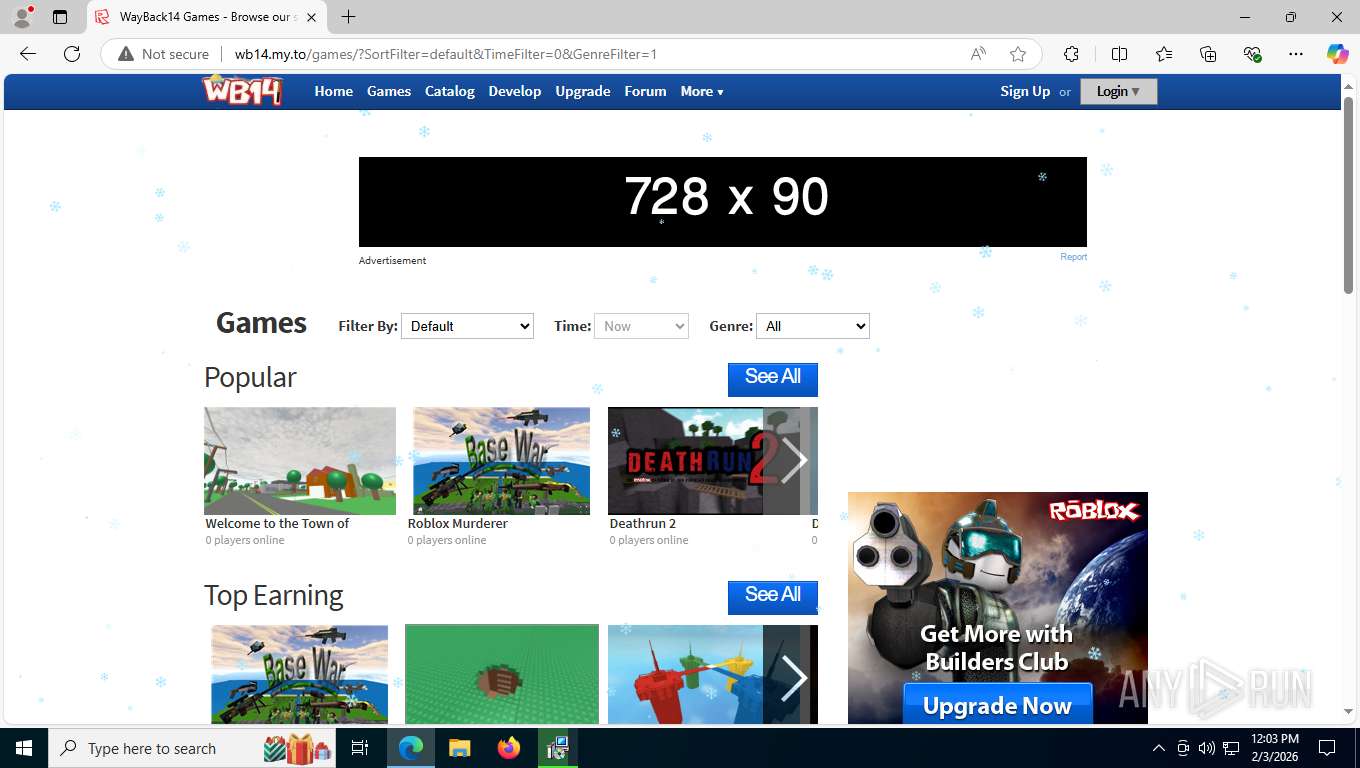
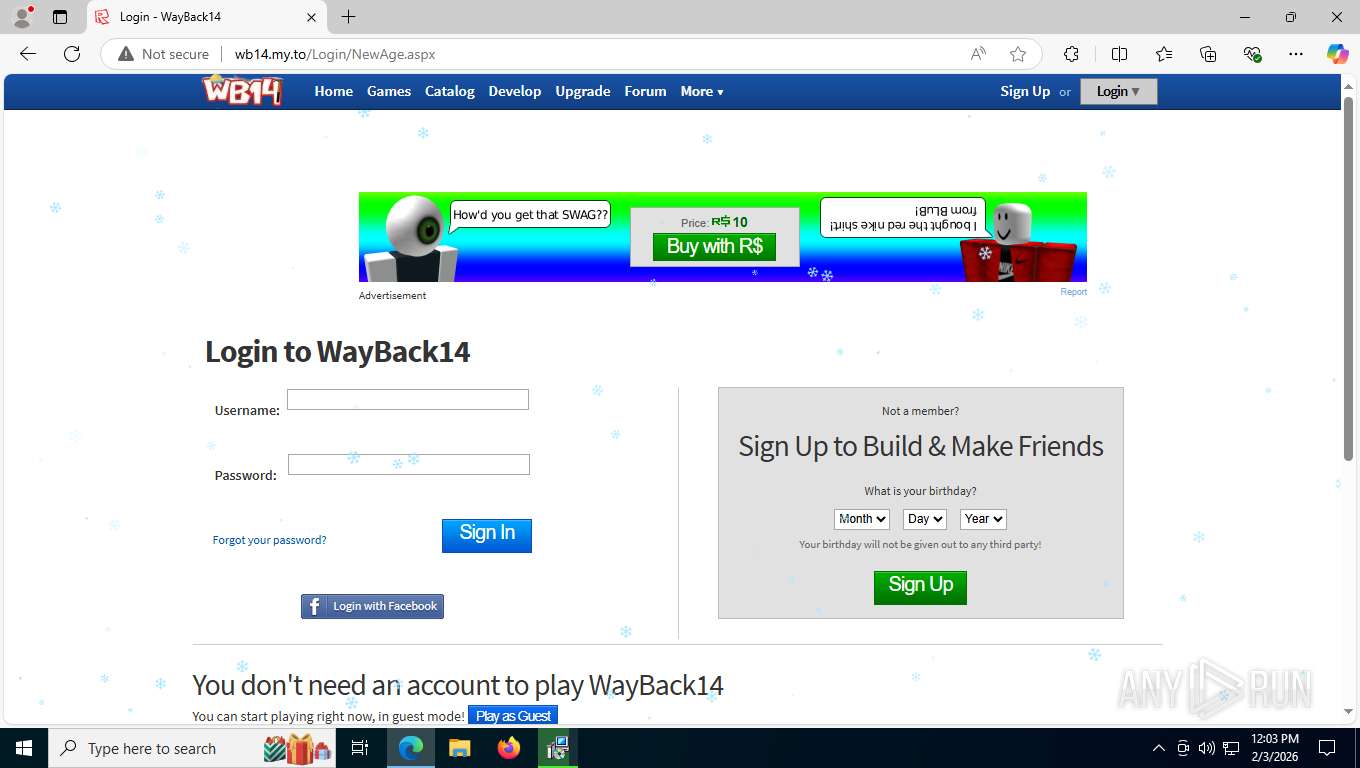
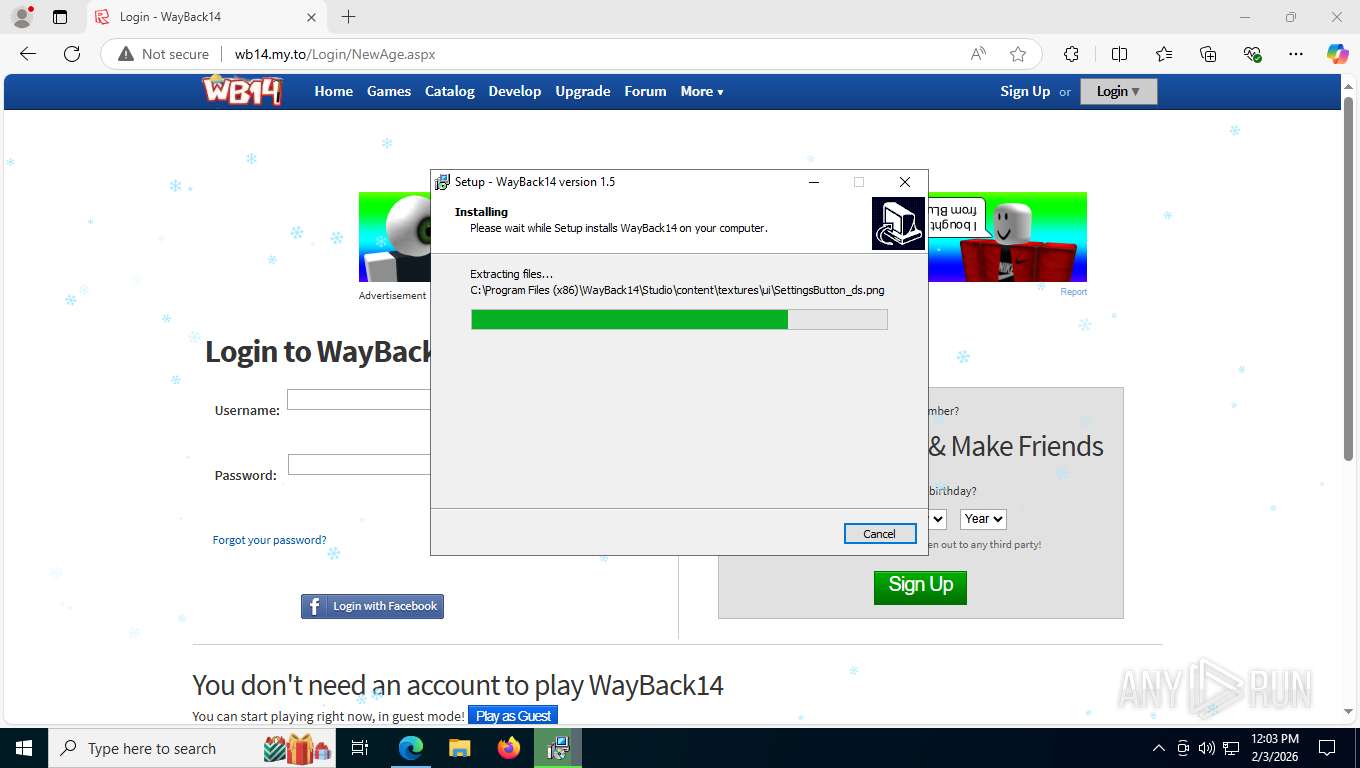
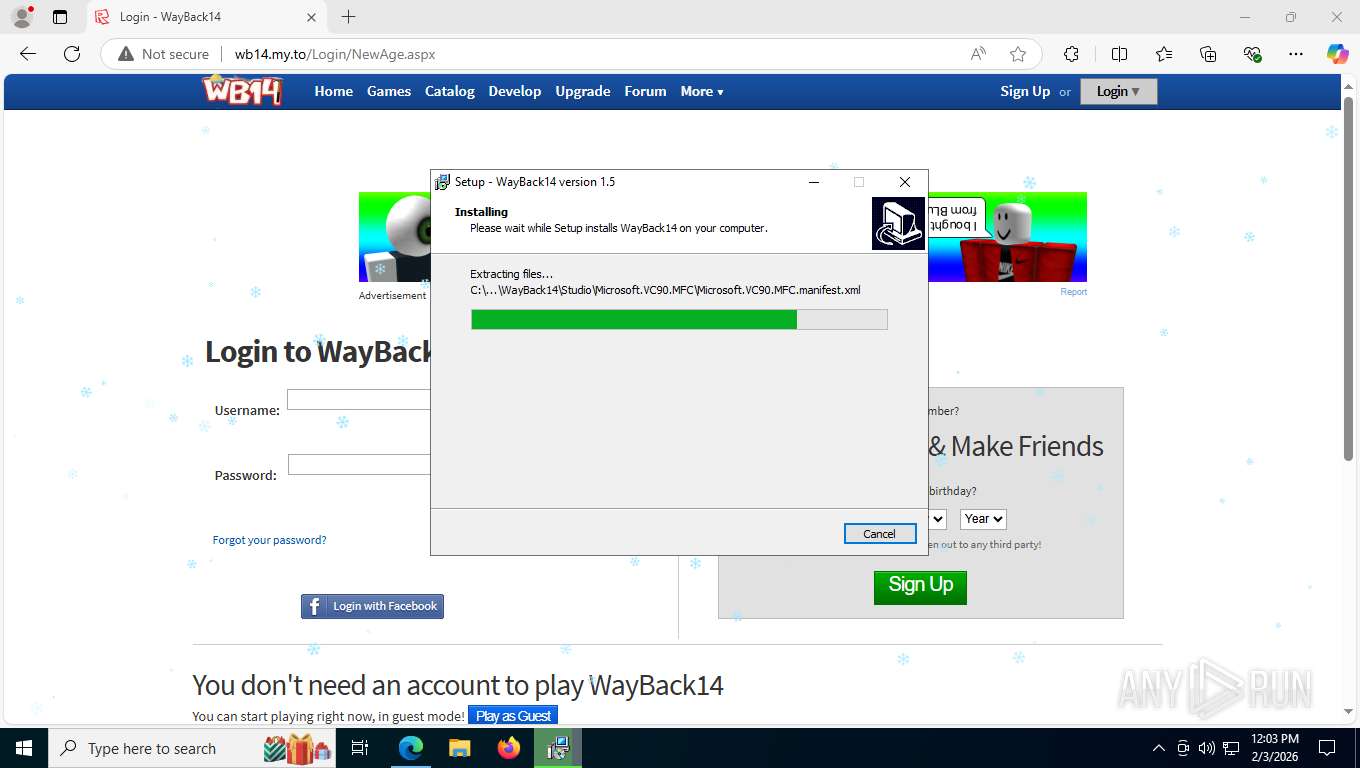
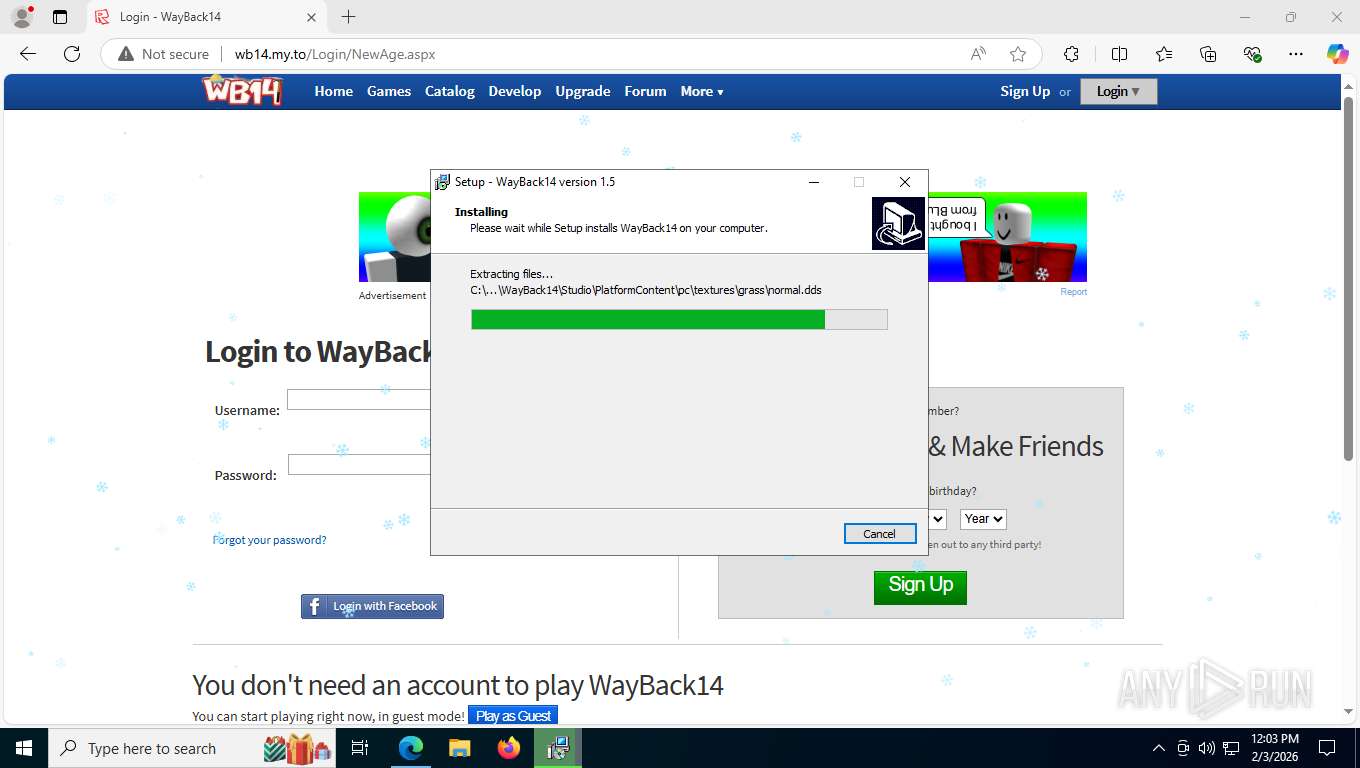
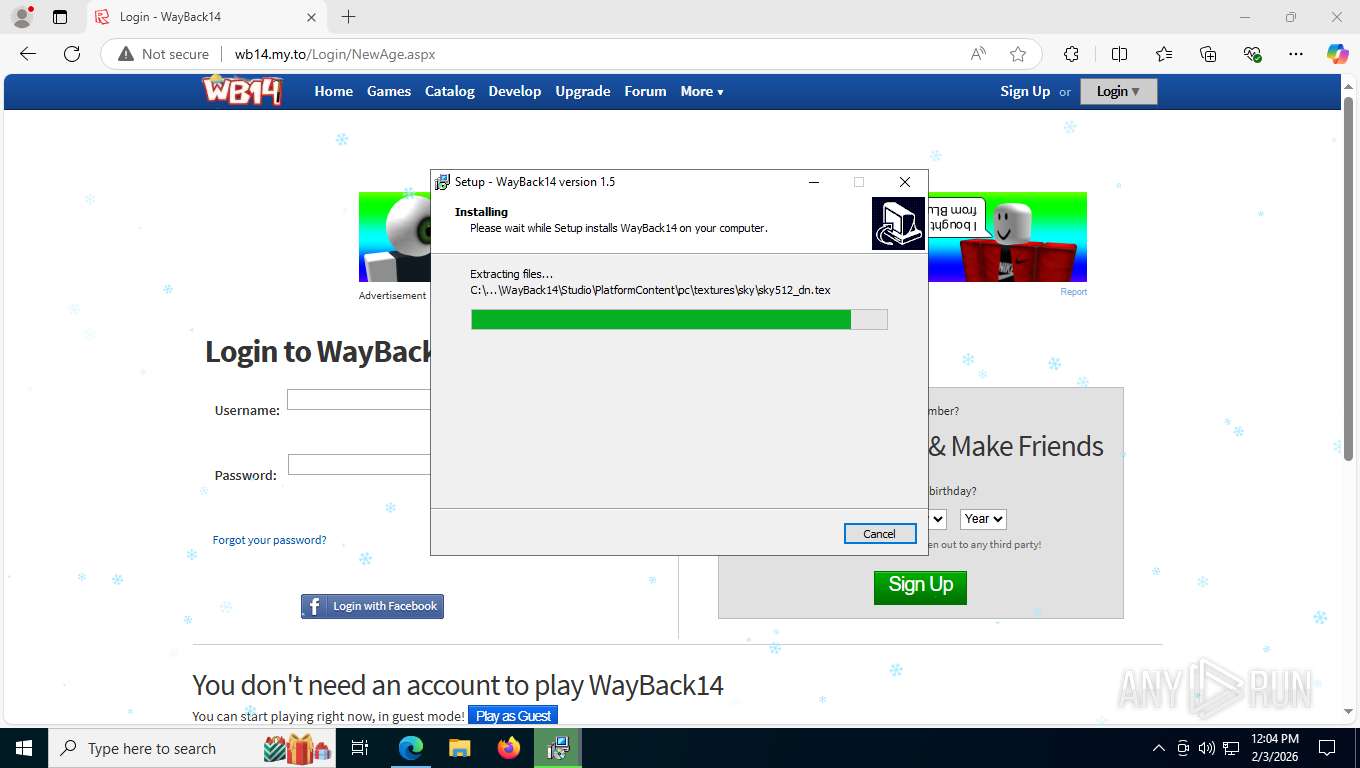
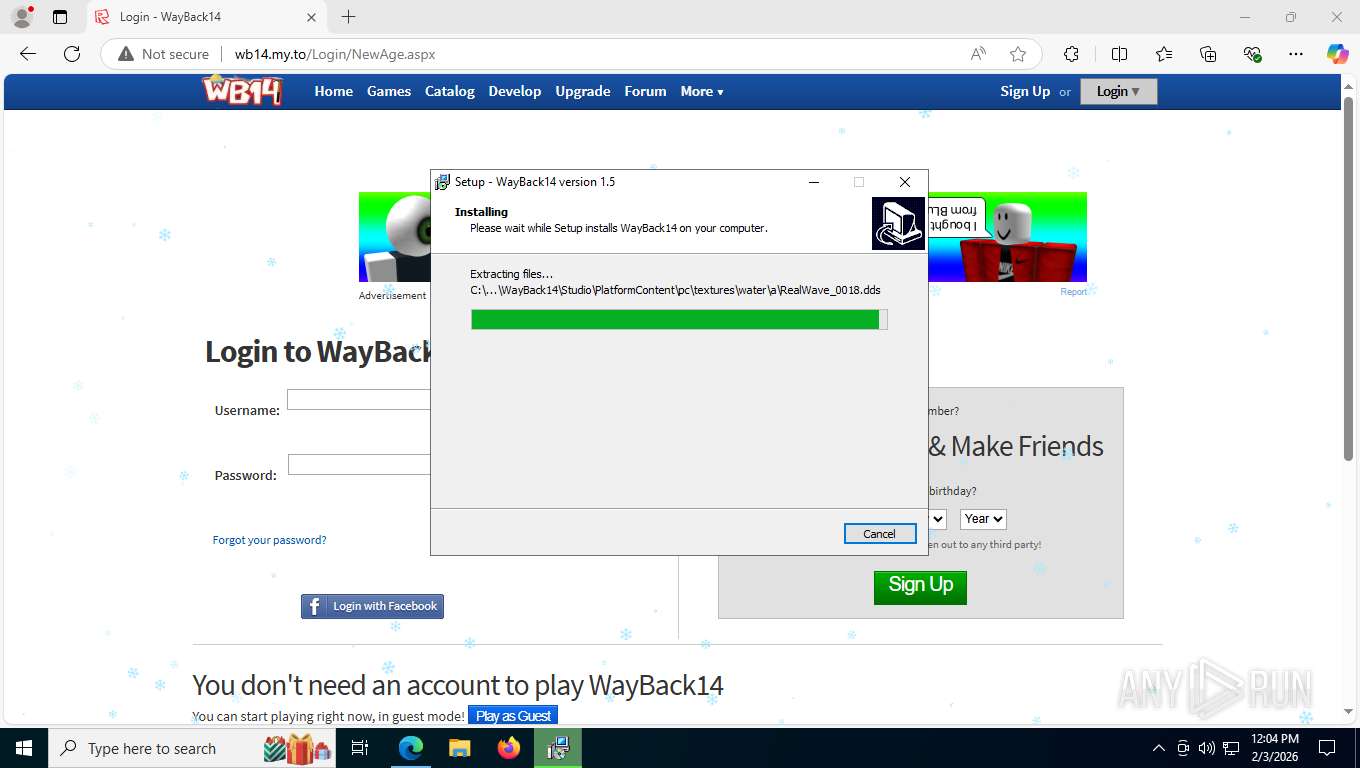
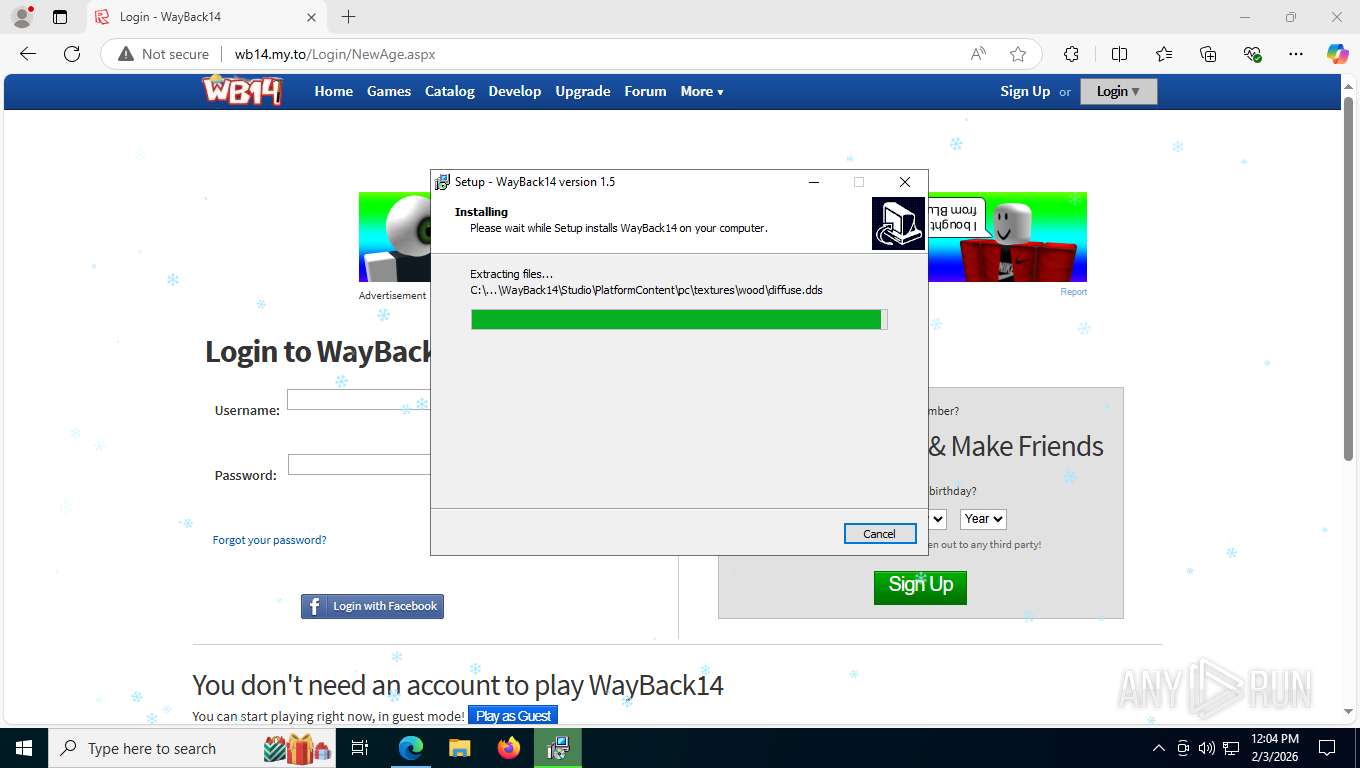
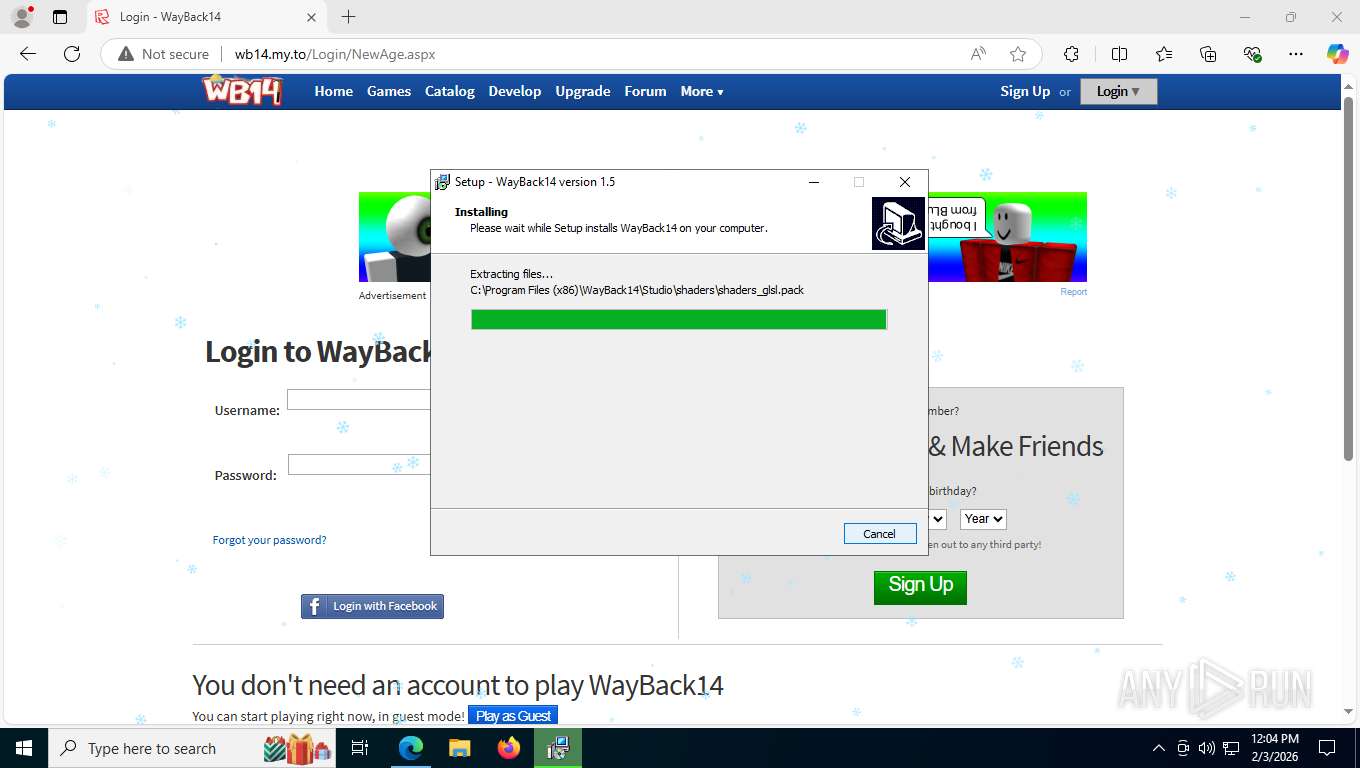
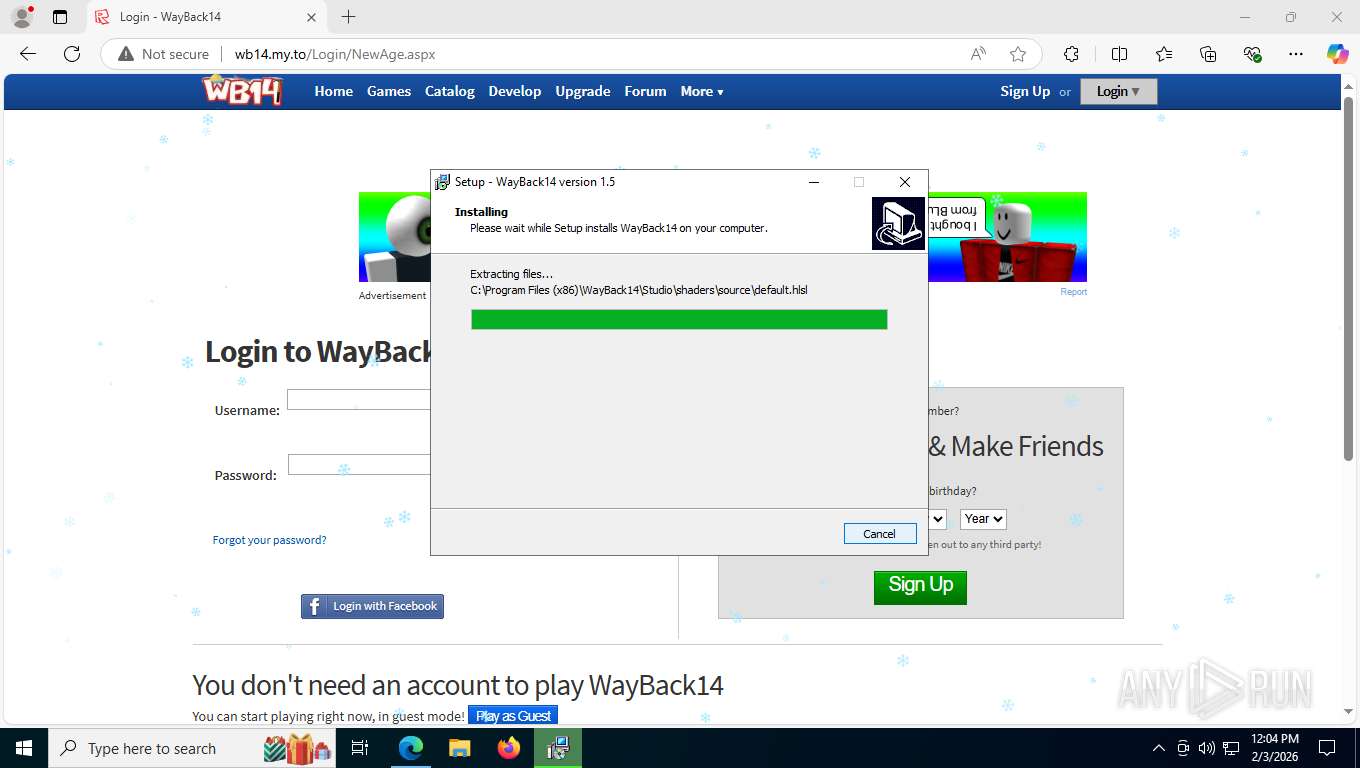
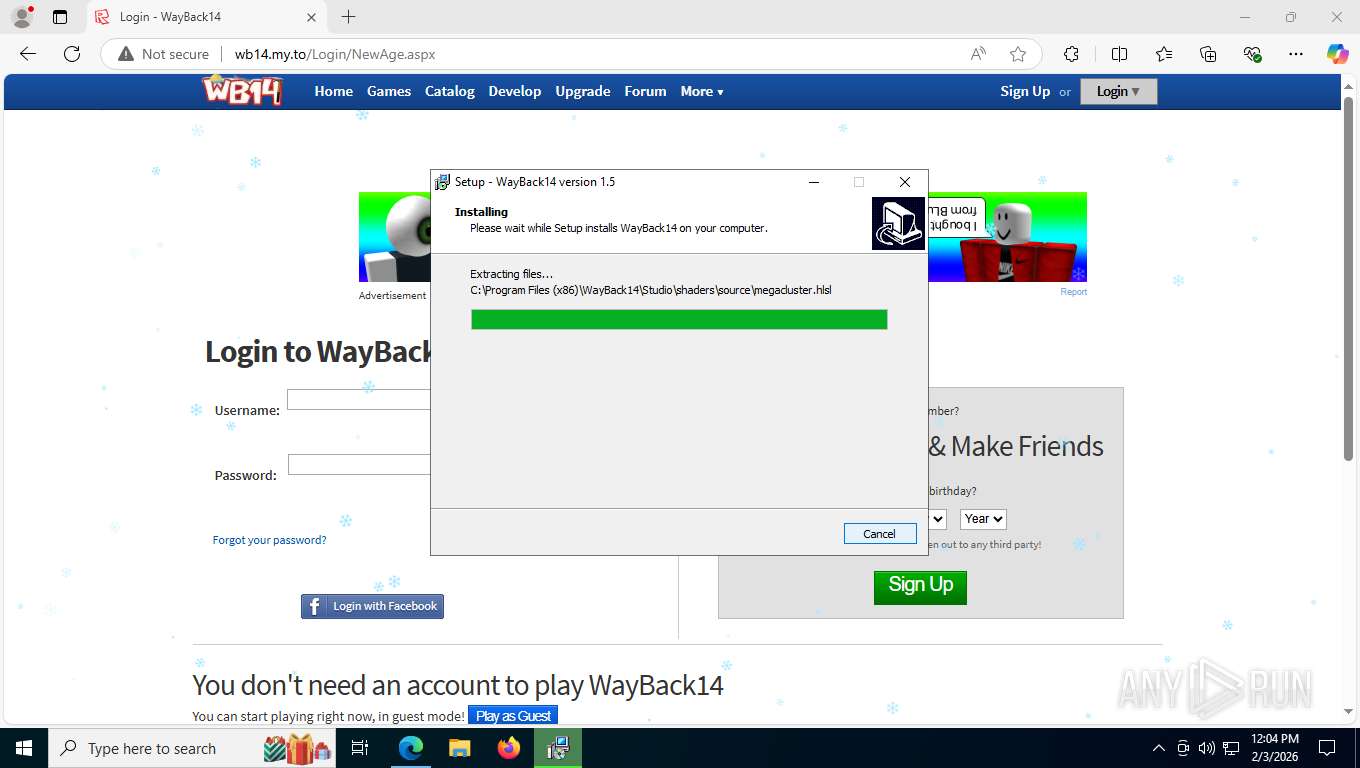
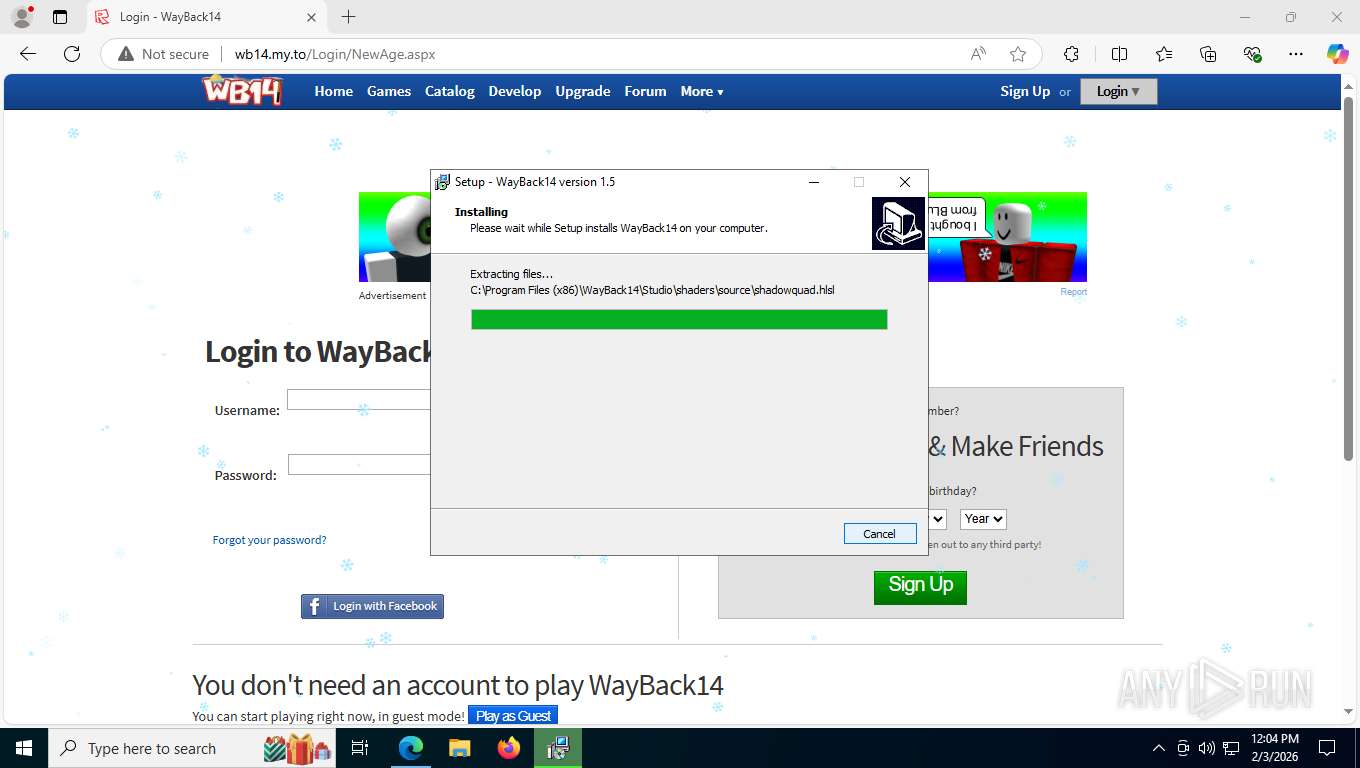
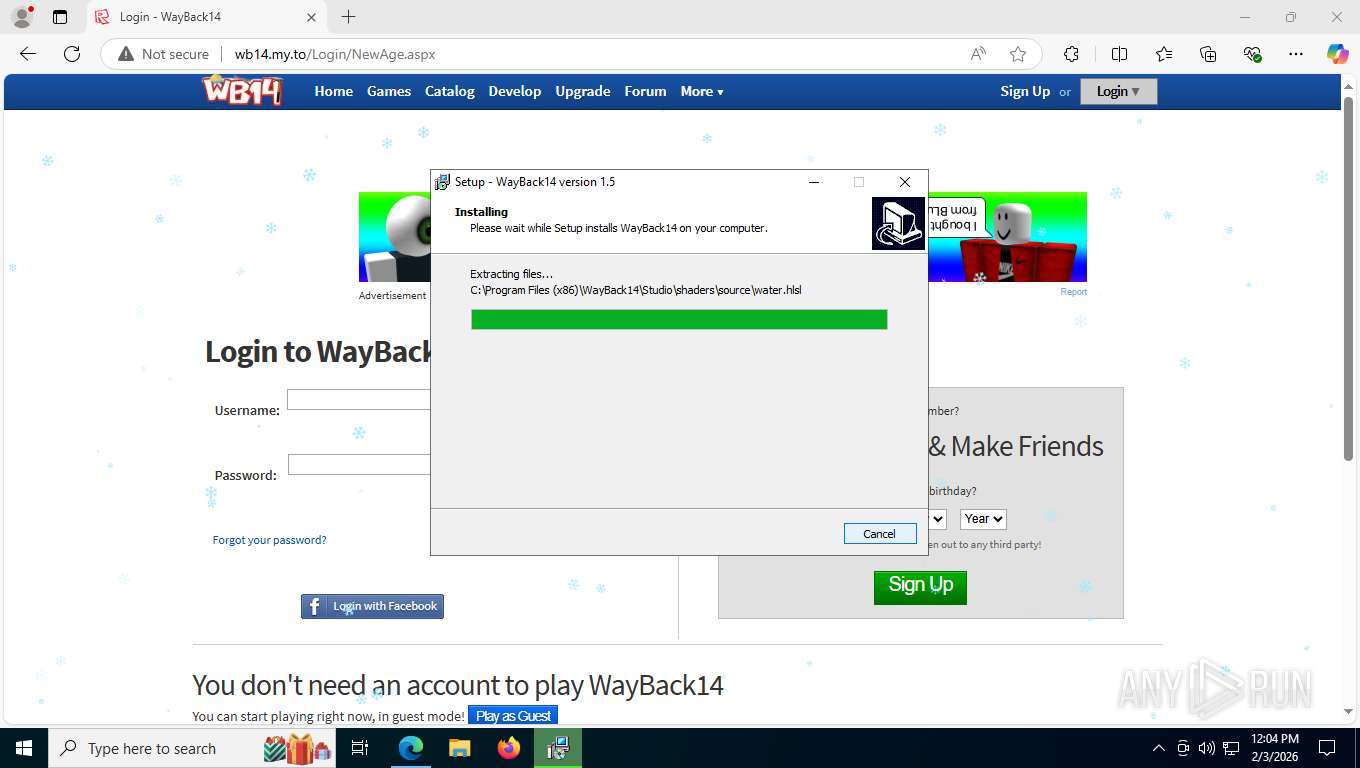
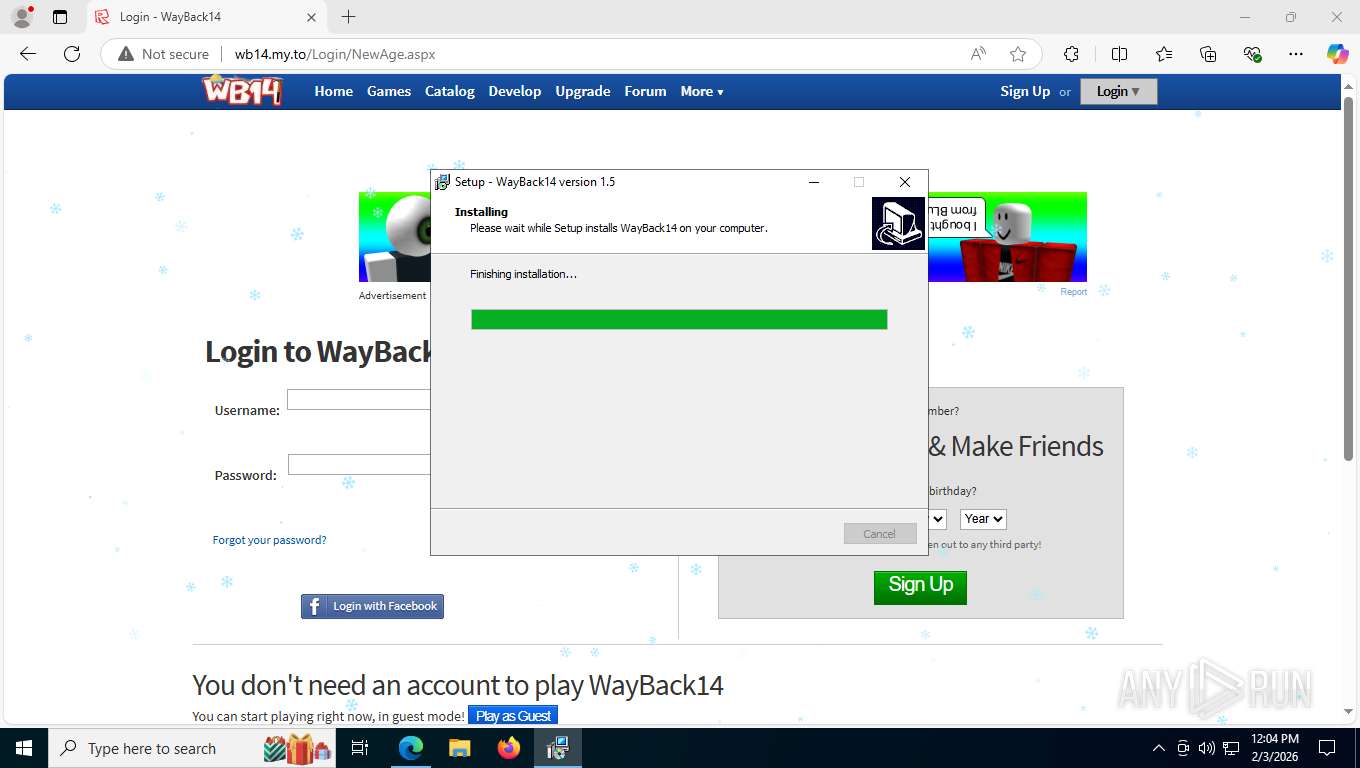
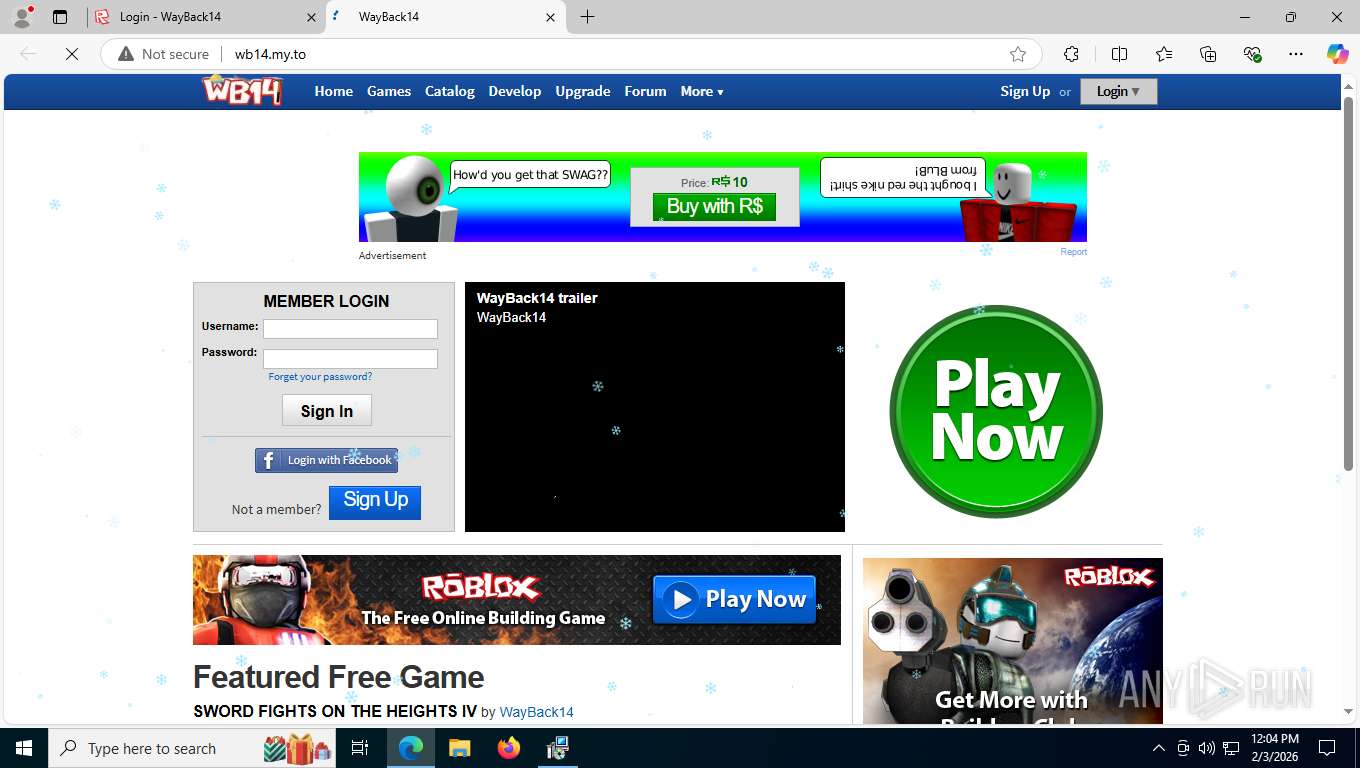
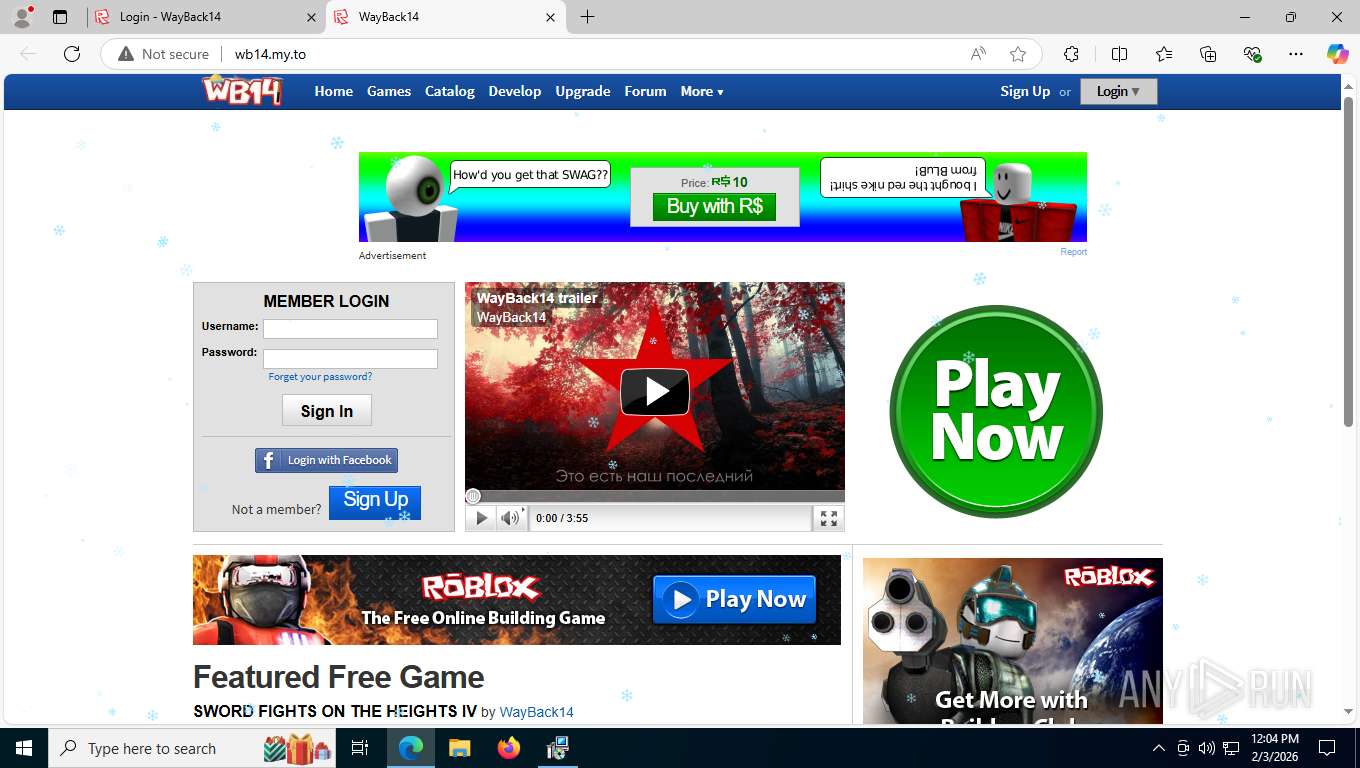
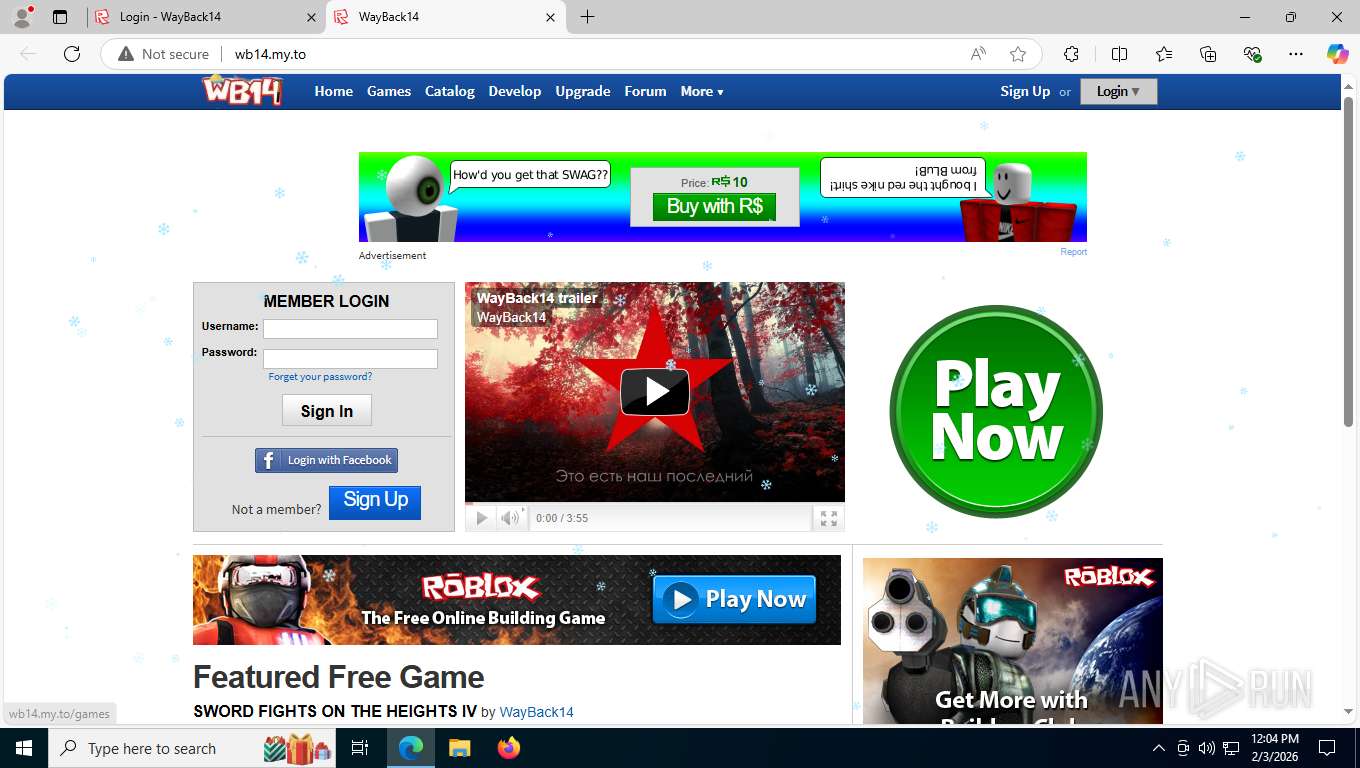
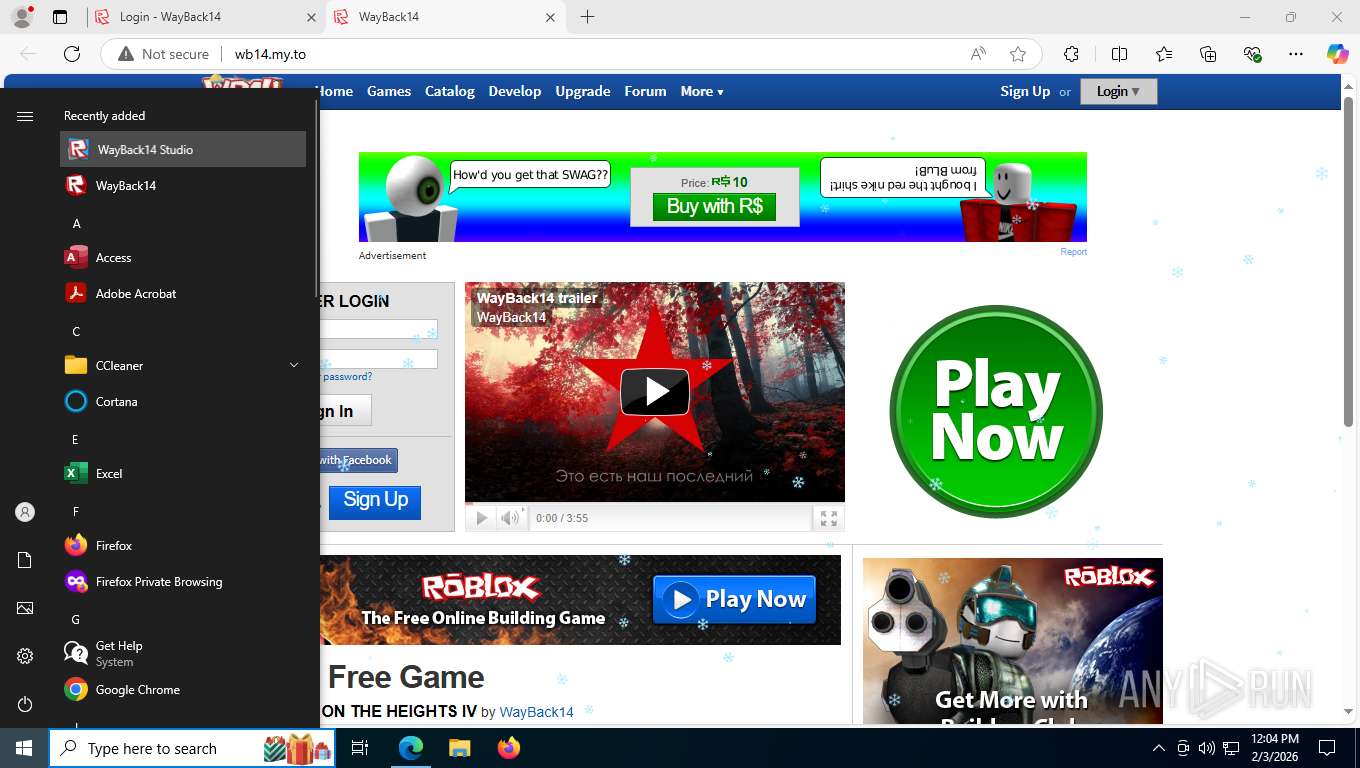
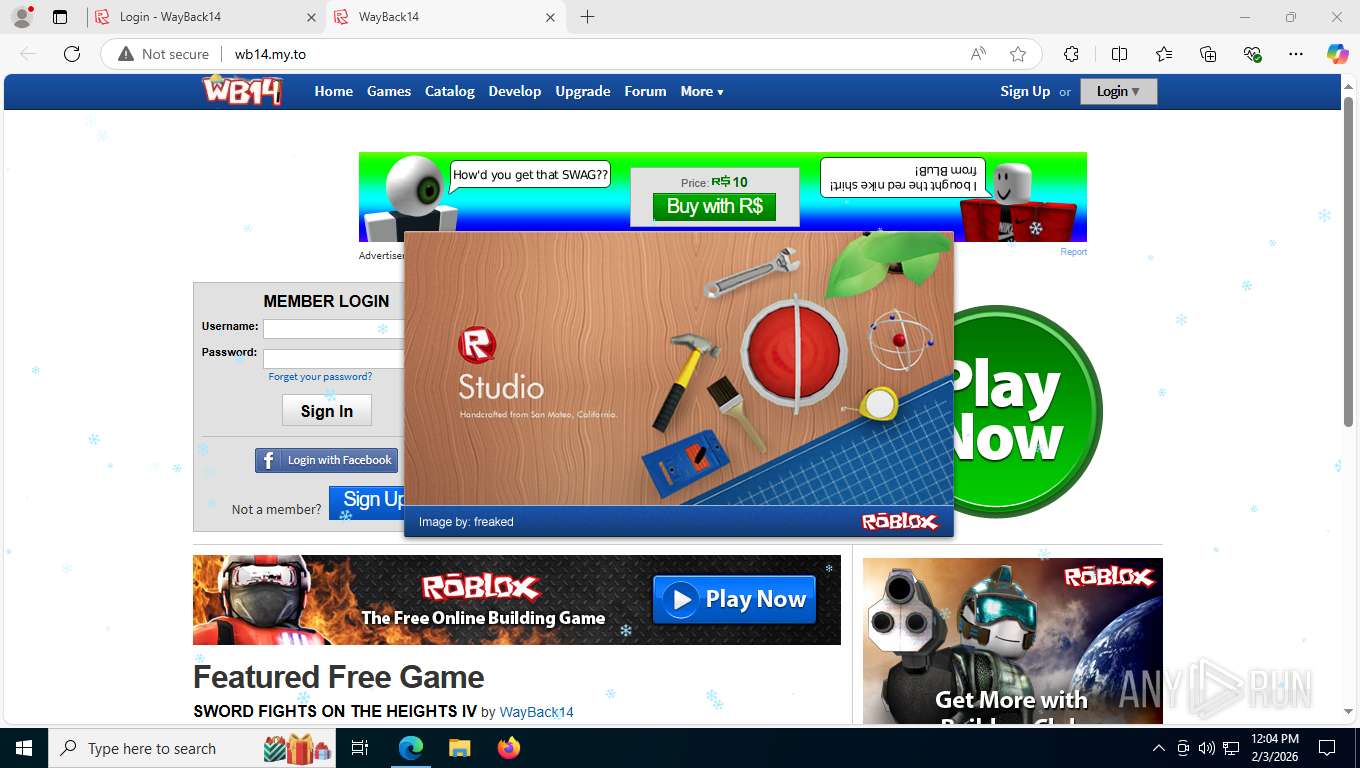
| URL: | wb14.my.to |
| Full analysis: | https://app.any.run/tasks/a3c06ce6-18a2-4b1f-a285-52f1611e557e |
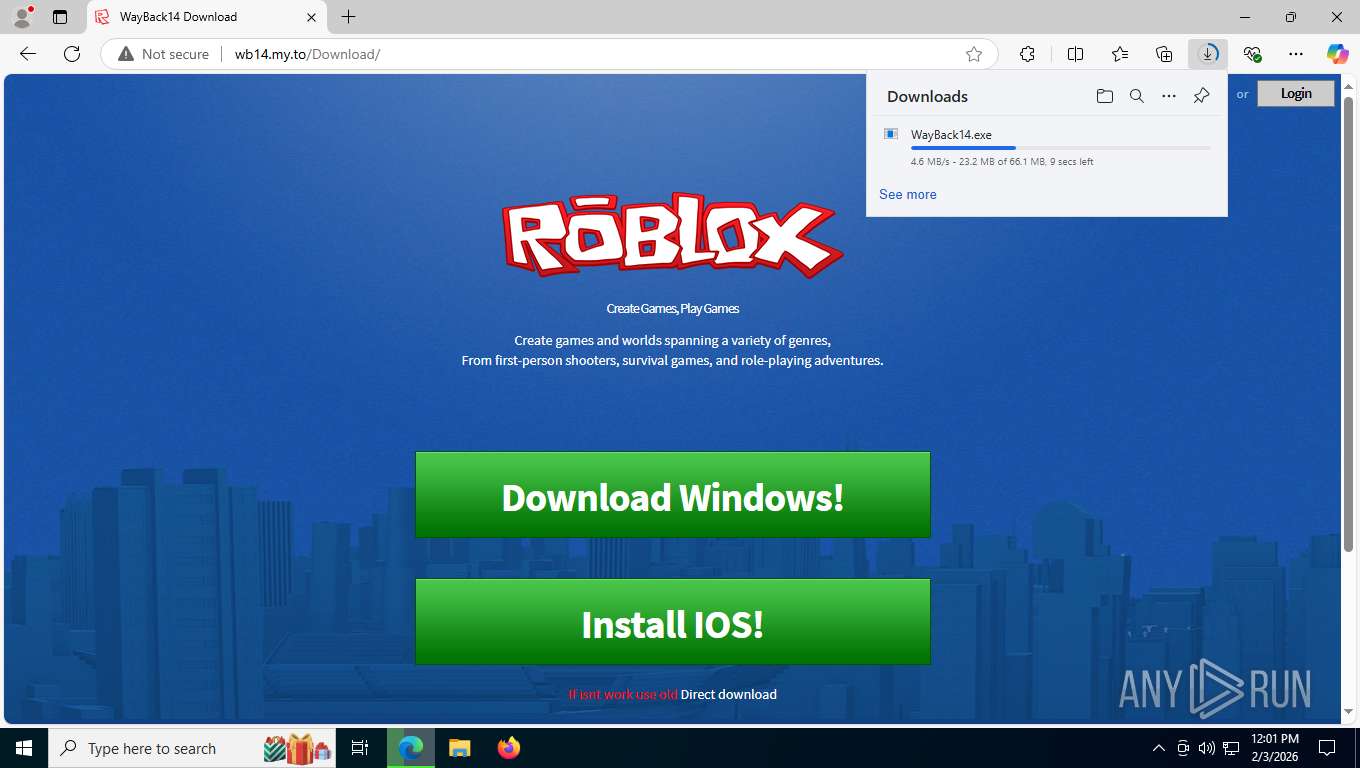
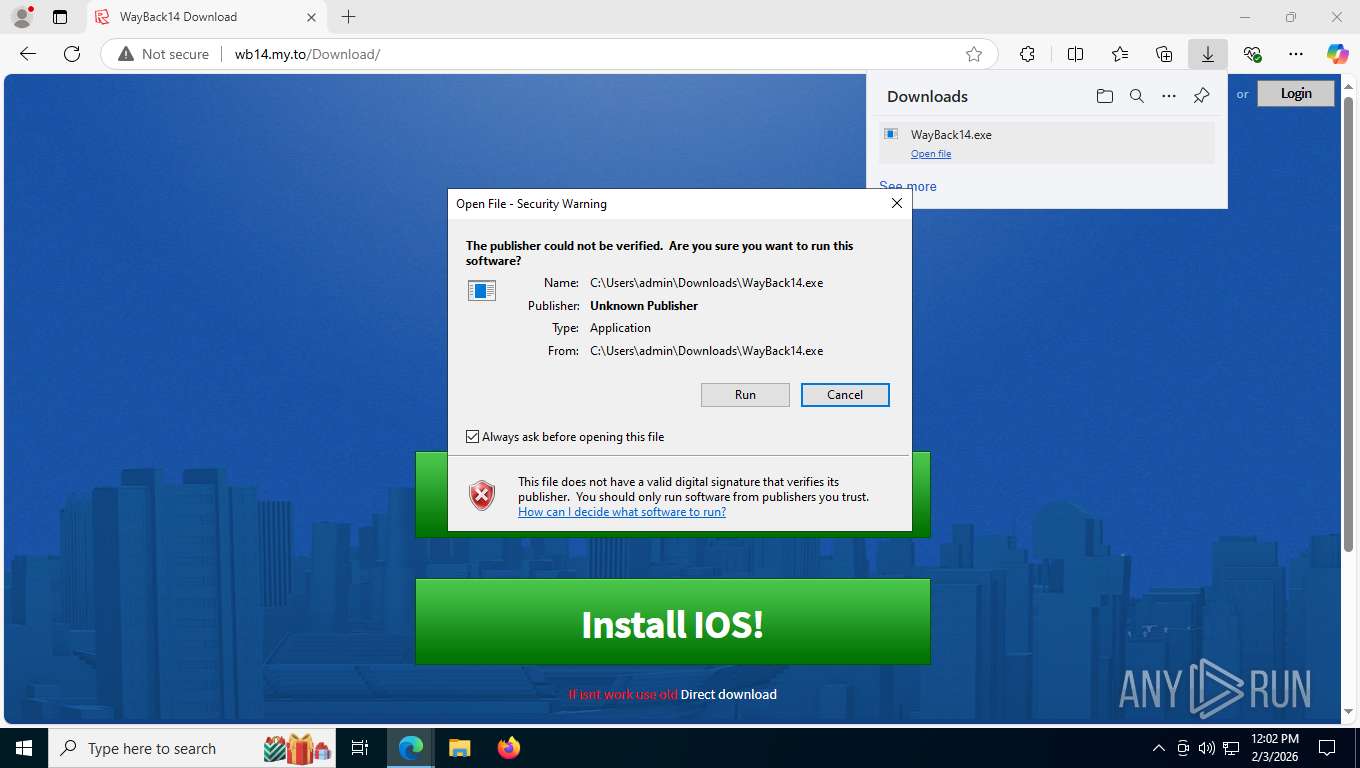
| Verdict: | Malicious activity |
| Analysis date: | February 03, 2026, 17:00:29 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 5CA24520A8156C24A7A021F661D45D6B |
| SHA1: | 912E429182864D35F4CD1D939CD0020D437D9A49 |
| SHA256: | BDD4A621B485224536A759F8D15A496052BAF59BD9E5F2FAFAD18763C6922E69 |
| SSDEEP: | 3:tthQn:tg |
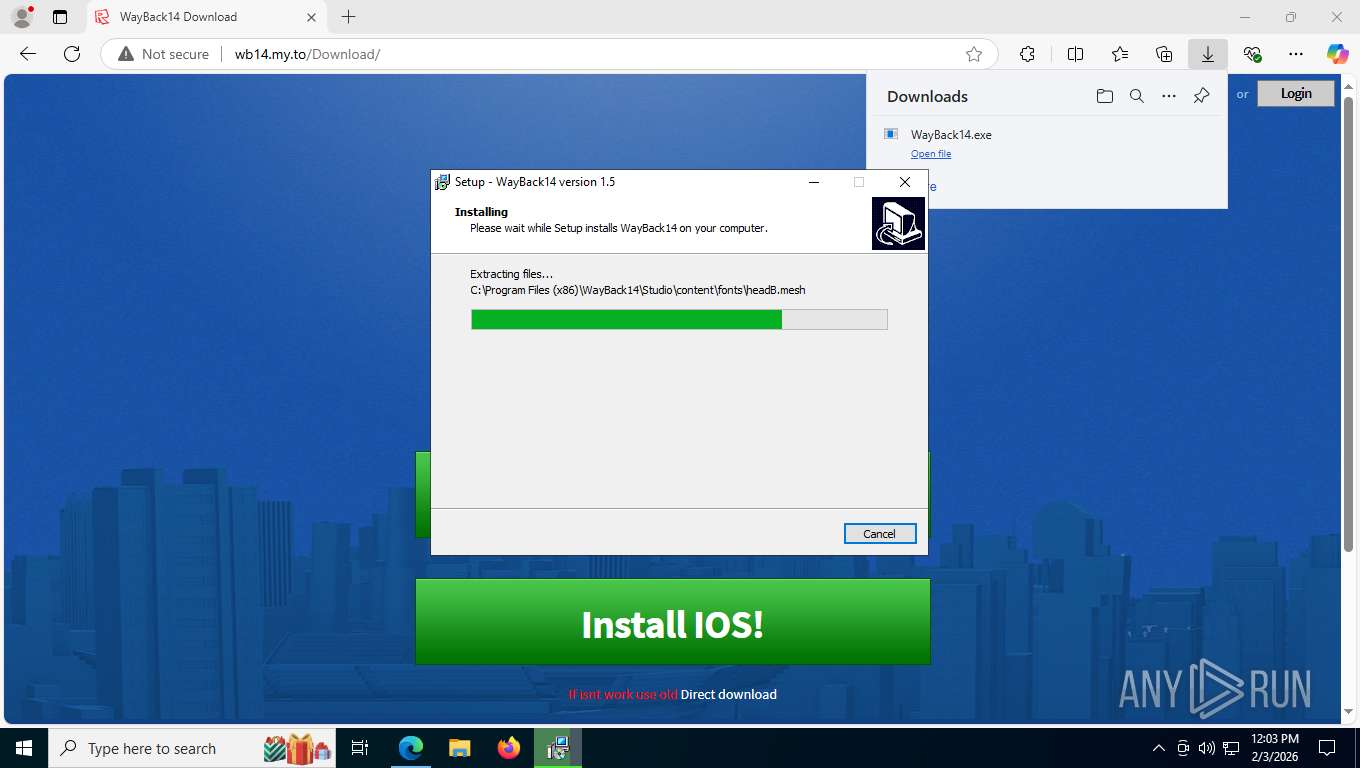
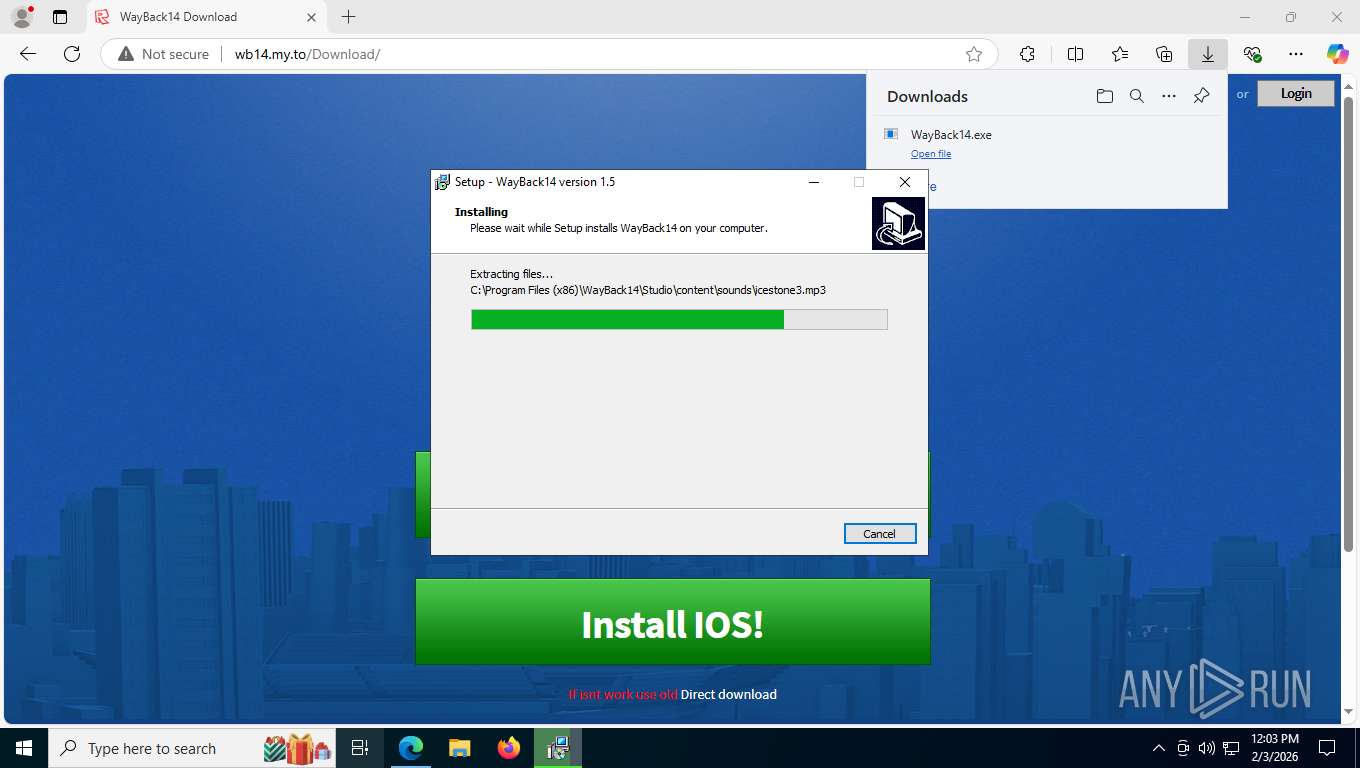
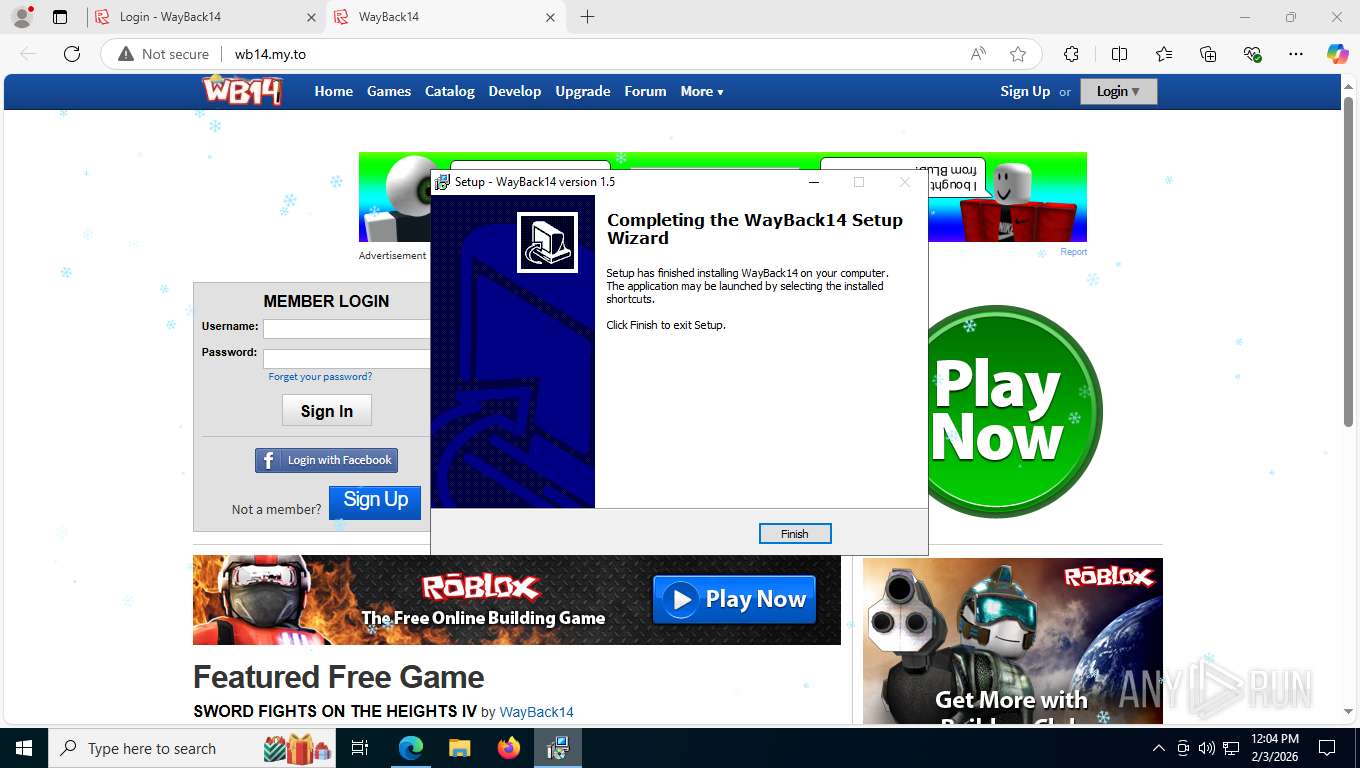
MALICIOUS
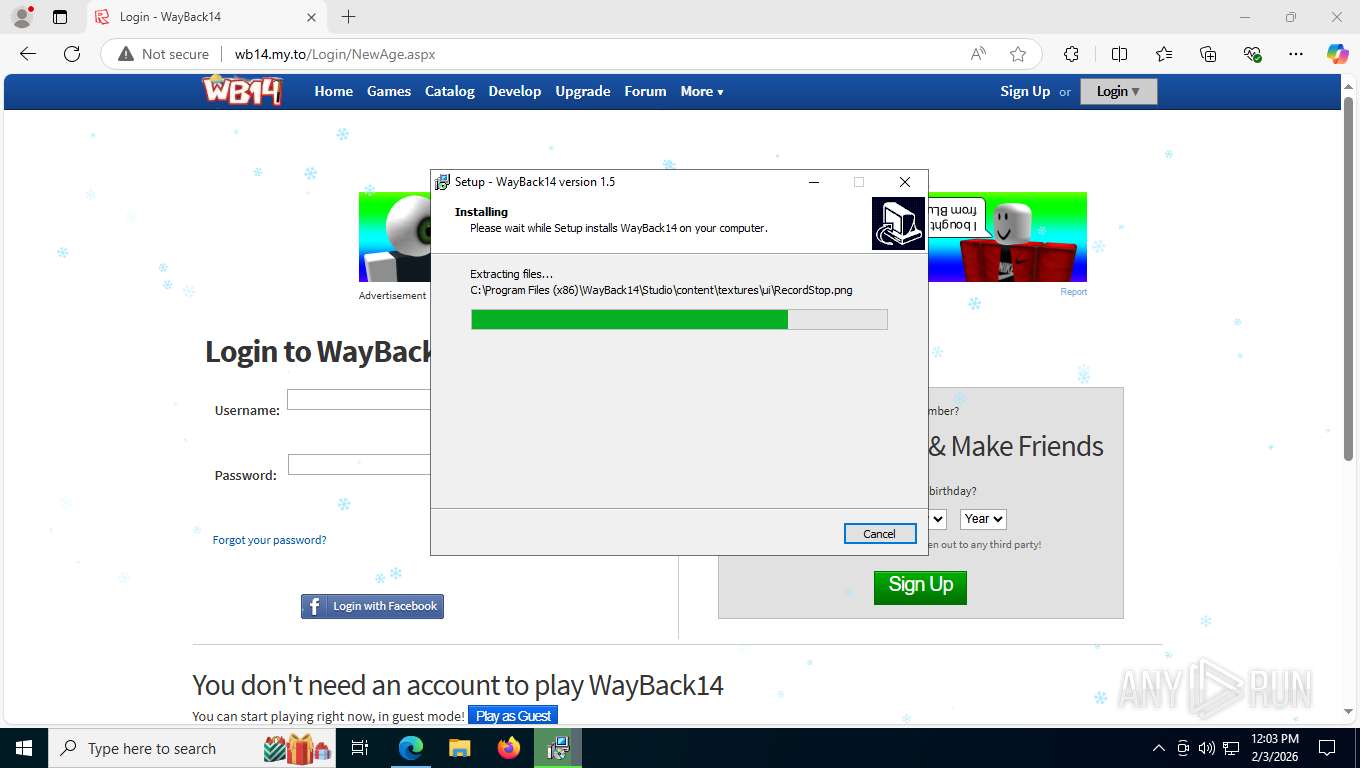
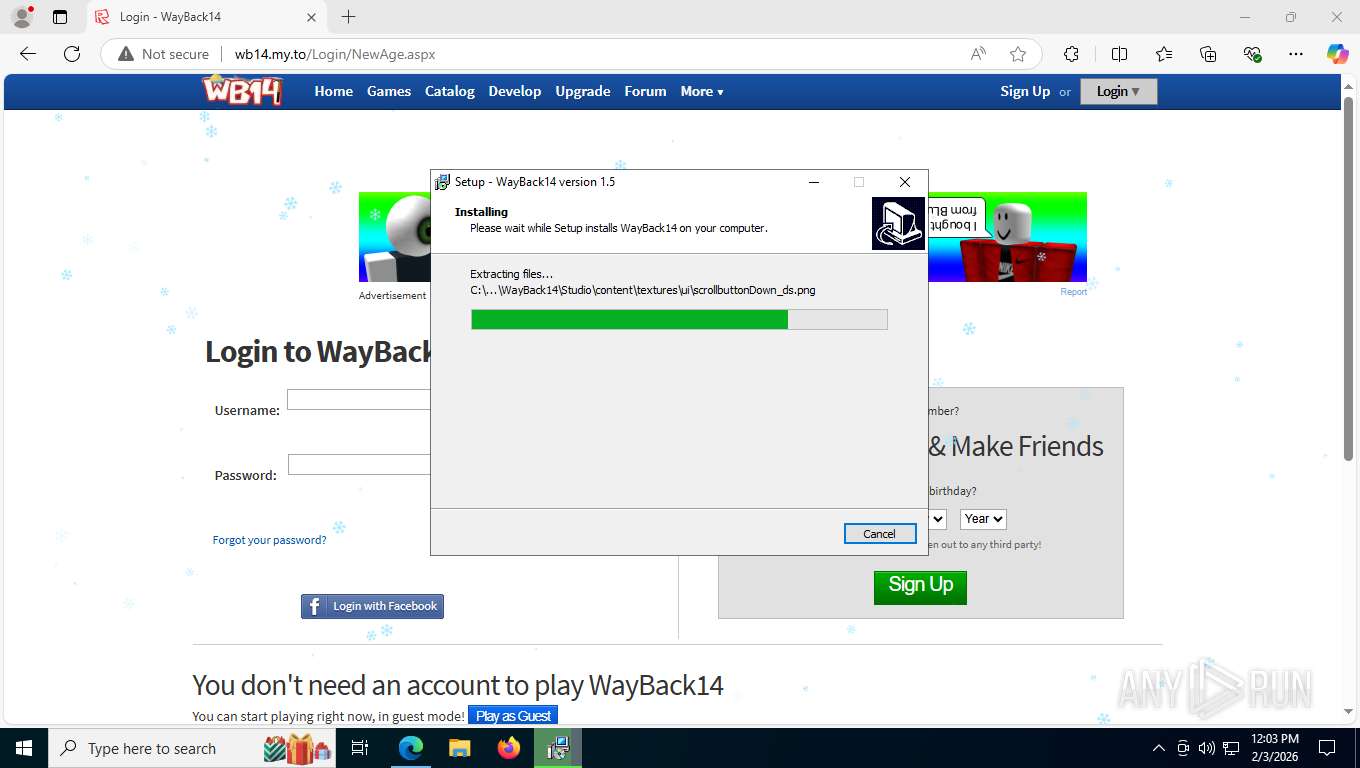
Executing a file with an untrusted certificate
- Bootstraper.exe (PID: 4544)
- RobloxStudioBeta.exe (PID: 8696)
SUSPICIOUS
Reads the Windows owner or organization settings
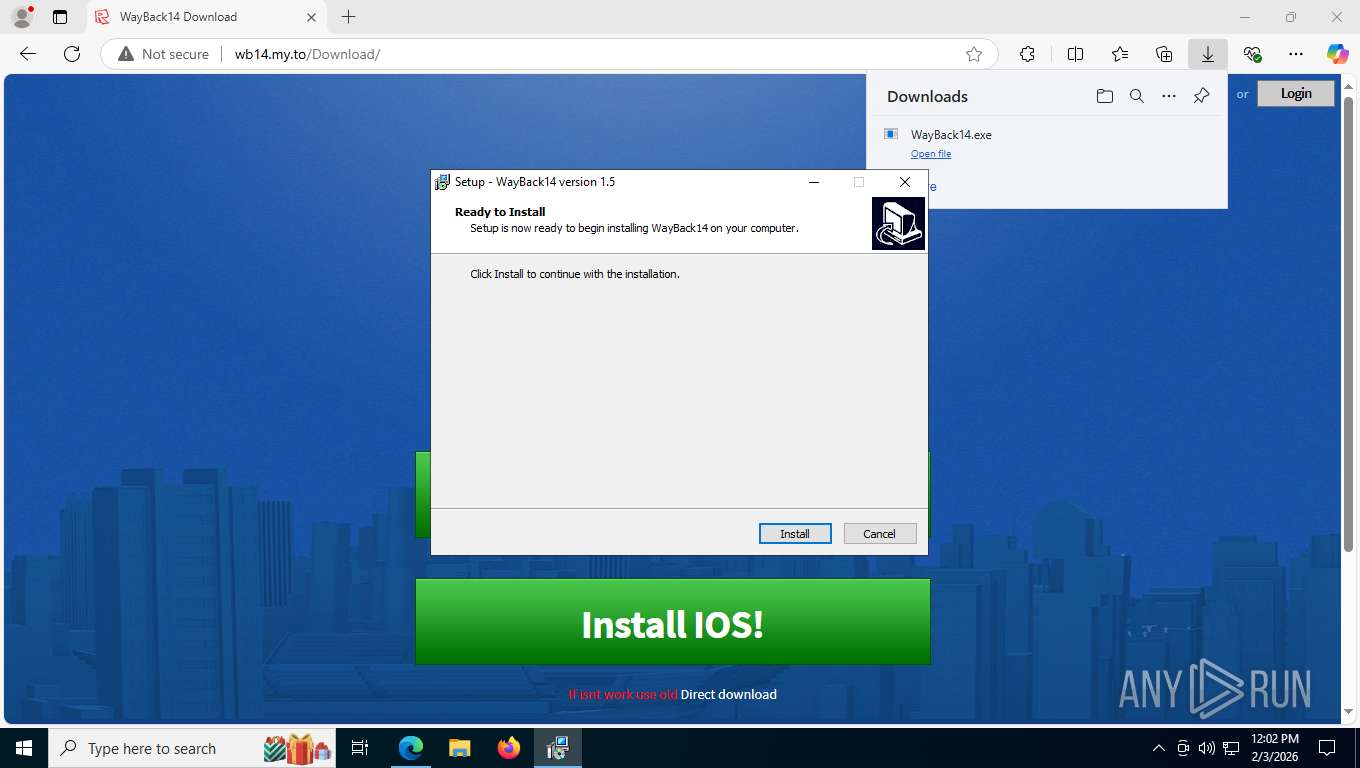
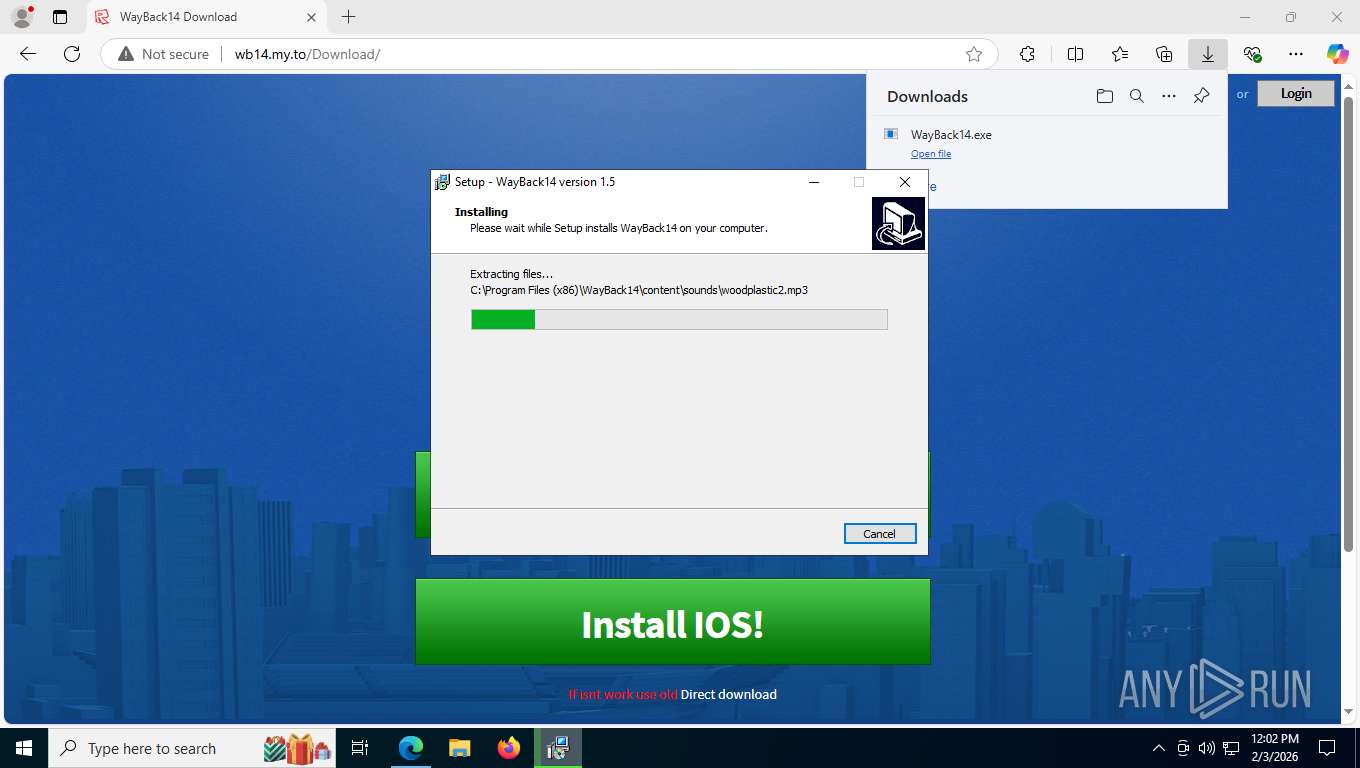
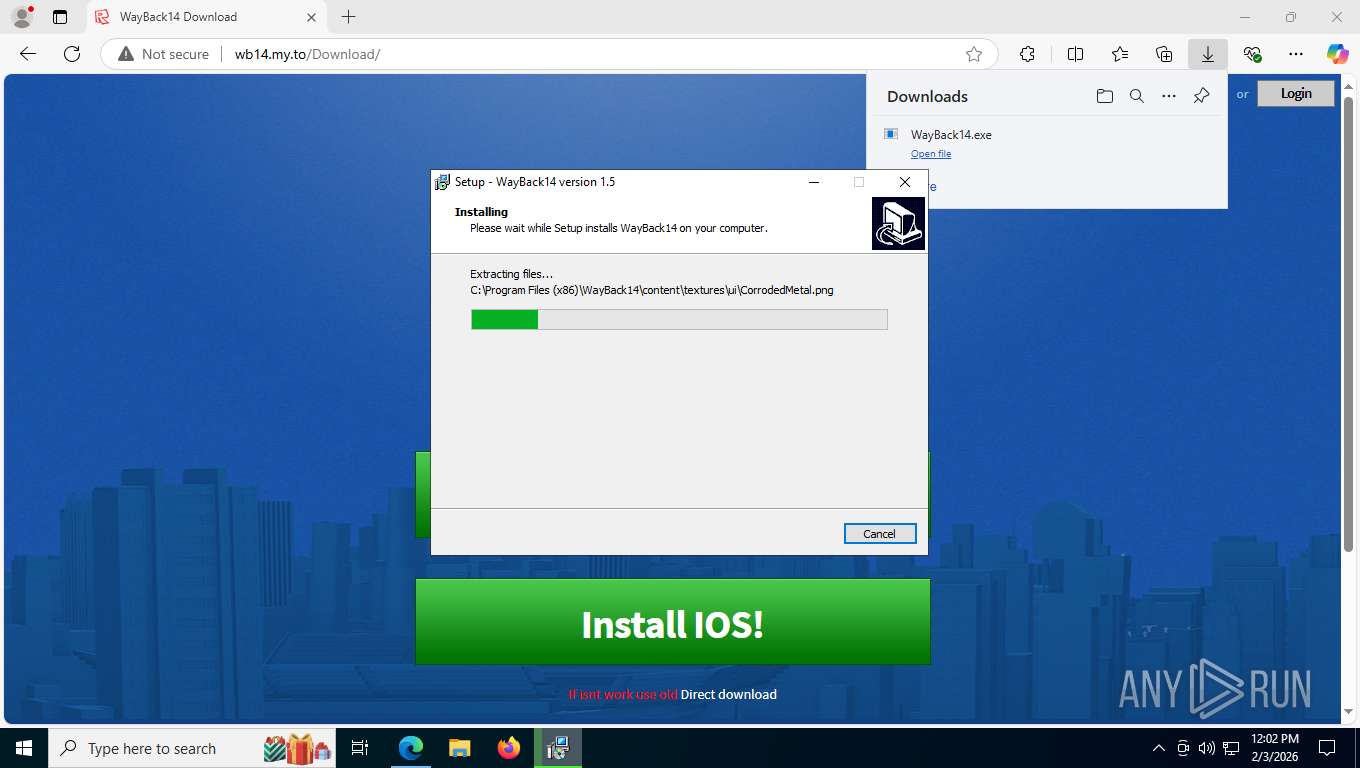
- WayBack14.tmp (PID: 7036)
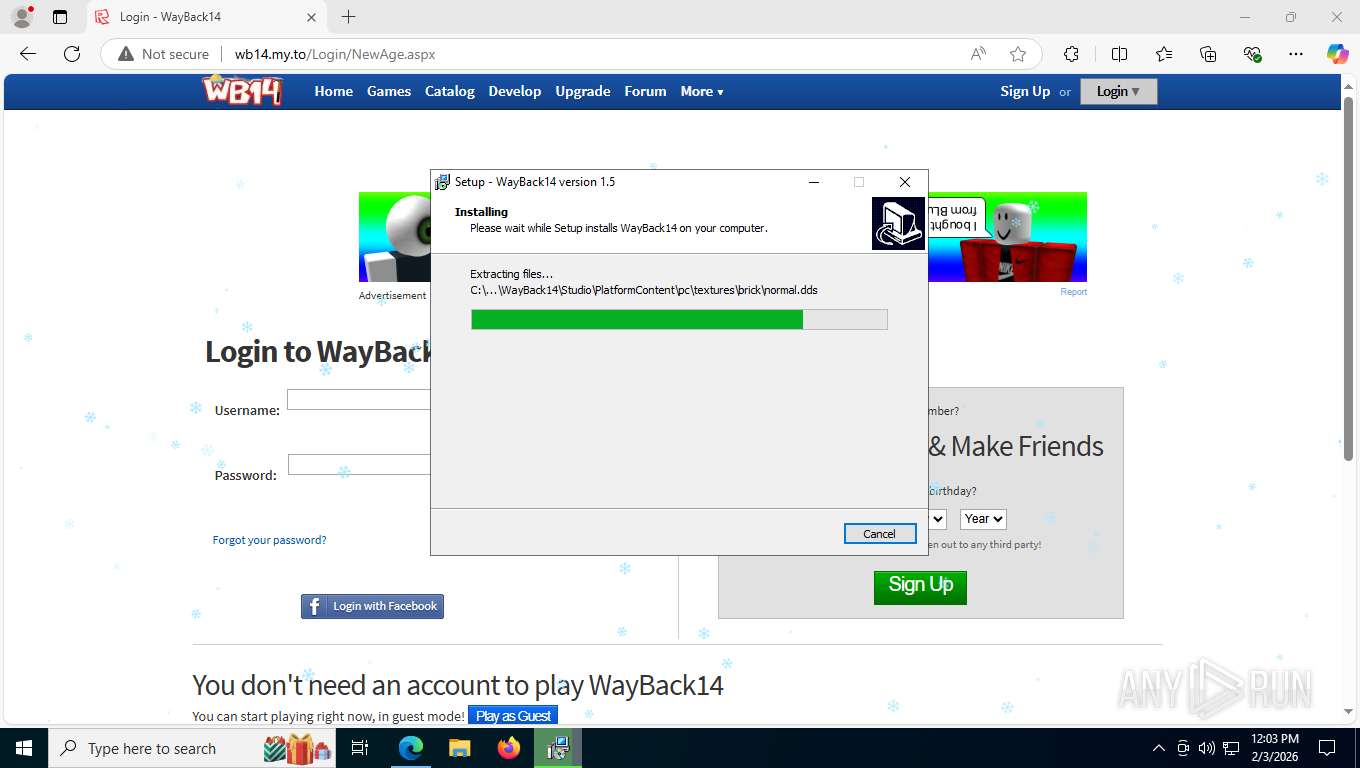
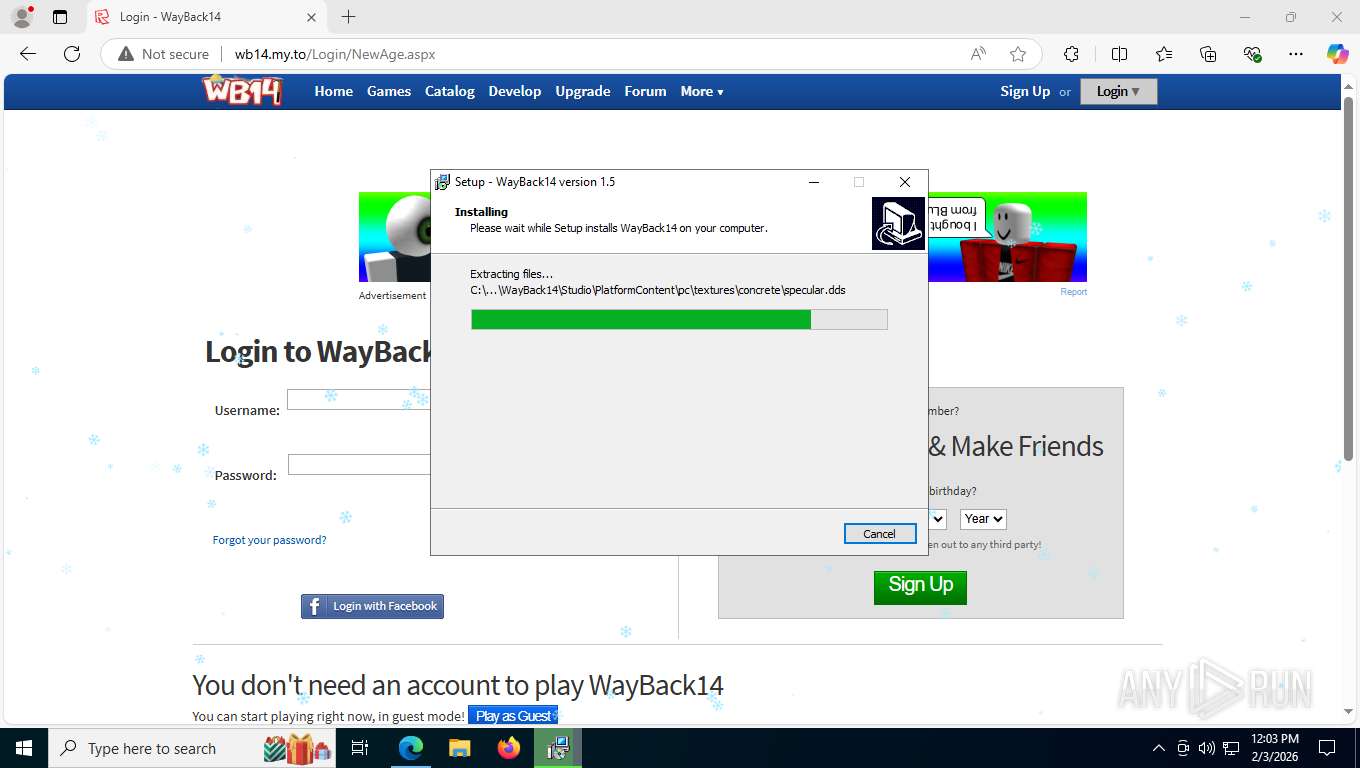
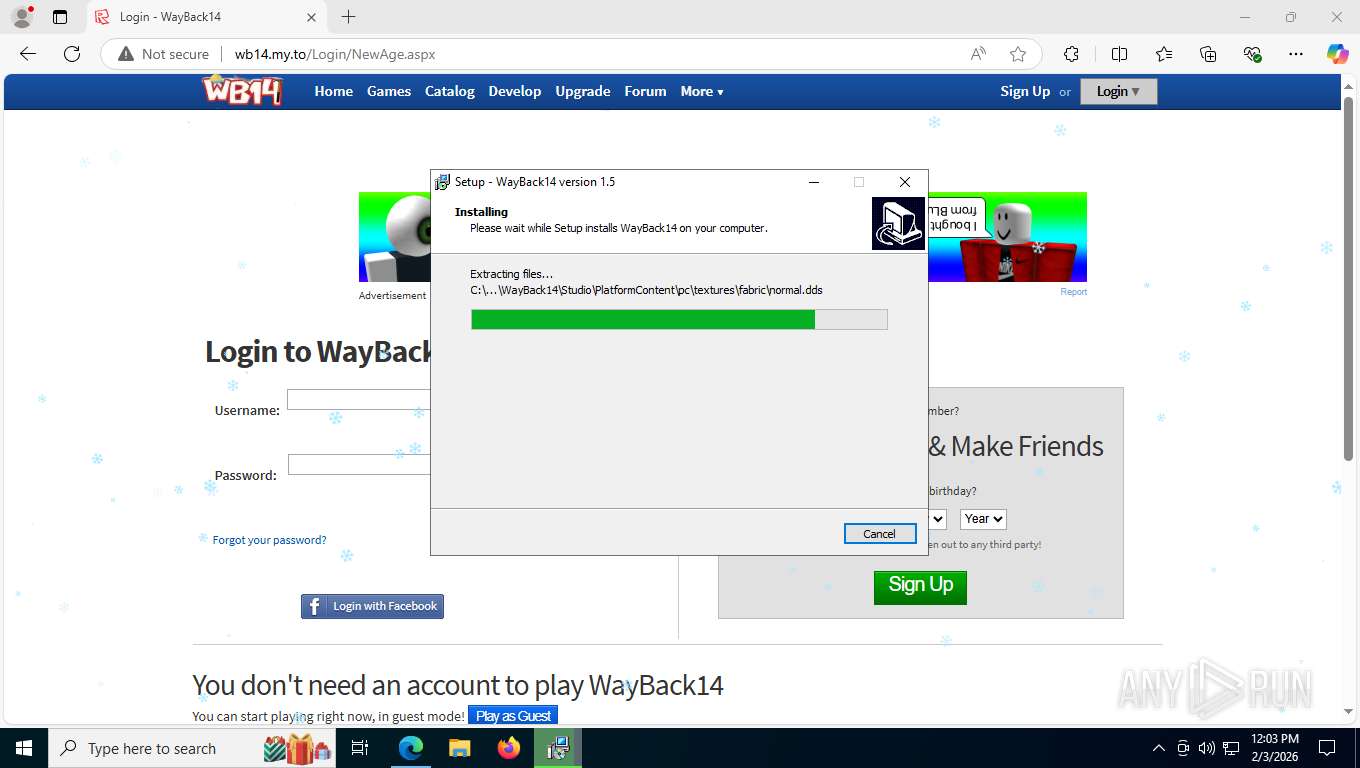
Process drops legitimate windows executable
- WayBack14.tmp (PID: 7036)
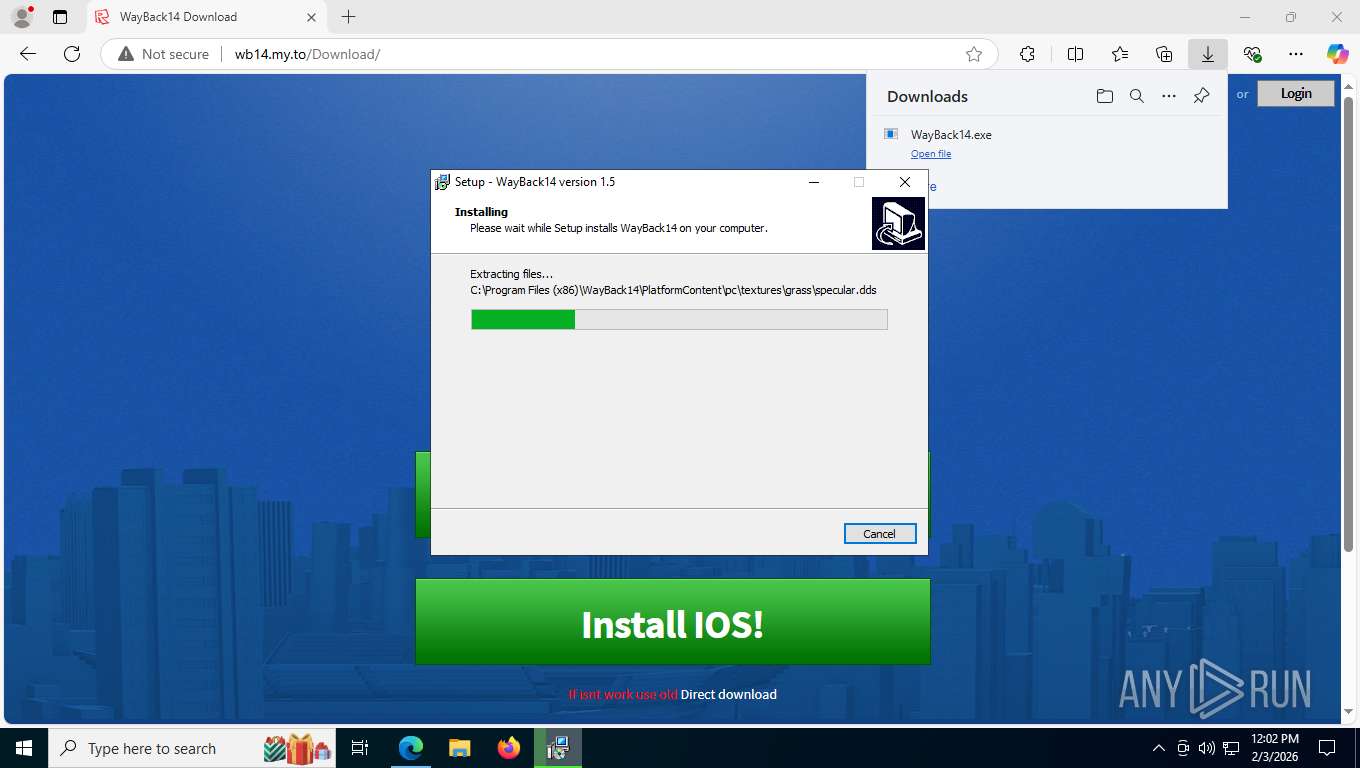
The process drops C-runtime libraries
- WayBack14.tmp (PID: 7036)
The process checks if it is being run in the virtual environment
- RobloxStudioBeta.exe (PID: 8696)
INFO
Drops script file
- msedge.exe (PID: 6156)
- msedge.exe (PID: 7904)
- WayBack14.tmp (PID: 7036)
Checks supported languages
- identity_helper.exe (PID: 5992)
- WayBack14.exe (PID: 6080)
- WayBack14.tmp (PID: 2764)
- WayBack14.exe (PID: 5088)
- WayBack14.tmp (PID: 7036)
- Bootstraper.exe (PID: 4544)
- GameBar.exe (PID: 7408)
- RobloxStudioBeta.exe (PID: 8696)
Application launched itself
- msedge.exe (PID: 6156)
- msedge.exe (PID: 8004)
Reads Environment values
- identity_helper.exe (PID: 5992)
Reads the computer name
- identity_helper.exe (PID: 5992)
- WayBack14.tmp (PID: 2764)
- WayBack14.tmp (PID: 7036)
- RobloxStudioBeta.exe (PID: 8696)
- Bootstraper.exe (PID: 4544)
- GameBar.exe (PID: 7408)
Create files in a temporary directory
- WayBack14.exe (PID: 6080)
- WayBack14.exe (PID: 5088)
- WayBack14.tmp (PID: 7036)
Process checks computer location settings
- WayBack14.tmp (PID: 2764)
Reads security settings of Internet Explorer
- WayBack14.tmp (PID: 2764)
- Bootstraper.exe (PID: 4544)
- GameBar.exe (PID: 7408)
- RobloxStudioBeta.exe (PID: 8696)
Developer hotkeys prevention is present
- msedge.exe (PID: 6156)
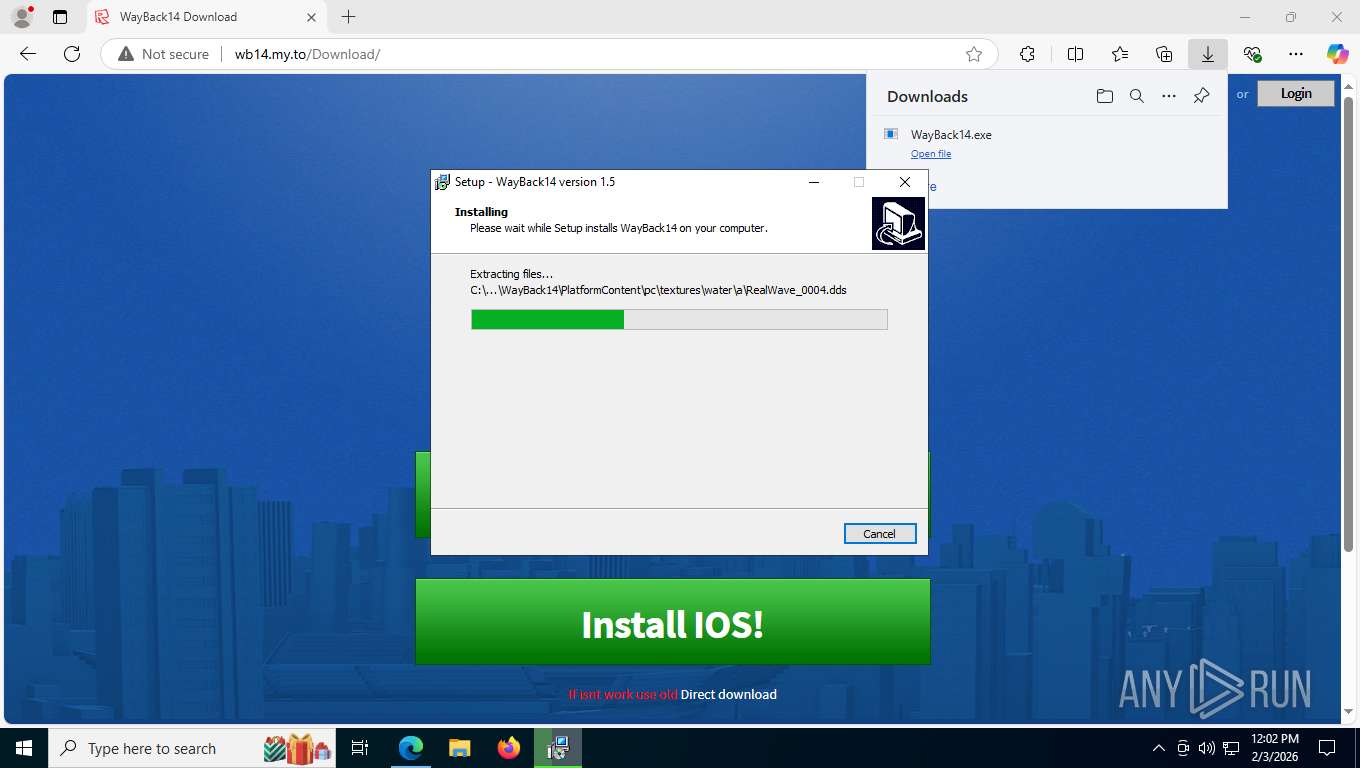
Creates files in the program directory
- WayBack14.tmp (PID: 7036)
The sample compiled with english language support
- WayBack14.tmp (PID: 7036)
Compiled with Borland Delphi (YARA)
- WayBack14.tmp (PID: 2764)
- WayBack14.tmp (PID: 7036)
Detects InnoSetup installer (YARA)
- WayBack14.tmp (PID: 2764)
- WayBack14.tmp (PID: 7036)
- WayBack14.exe (PID: 5088)
- WayBack14.exe (PID: 6080)
Checks proxy server information
- slui.exe (PID: 2372)
- RobloxStudioBeta.exe (PID: 8696)
Reads the machine GUID from the registry
- Bootstraper.exe (PID: 4544)
- RobloxStudioBeta.exe (PID: 8696)
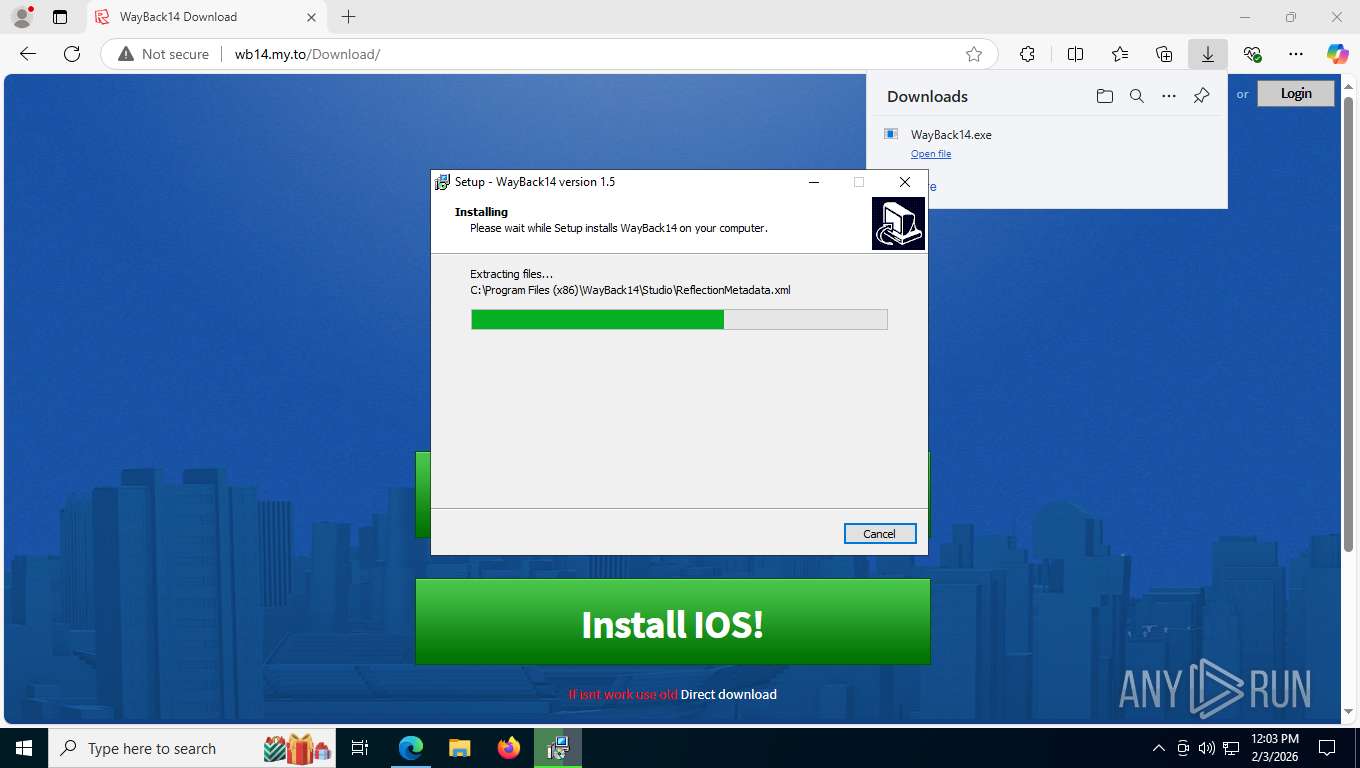
Creates a software uninstall entry
- WayBack14.tmp (PID: 7036)
Reads CPU info
- RobloxStudioBeta.exe (PID: 8696)
Manual execution by a user
- RobloxStudioBeta.exe (PID: 8696)
Creates files or folders in the user directory
- RobloxStudioBeta.exe (PID: 8696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
207
Monitored processes
55
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 148 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=1284,i,15295945936880672652,14499887067567080487,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=4960 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 752 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=8 --always-read-main-dll --field-trial-handle=4280,i,15295945936880672652,14499887067567080487,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5272 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1568 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=36 --always-read-main-dll --field-trial-handle=5740,i,15295945936880672652,14499887067567080487,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=7416 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1784 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6748,i,15295945936880672652,14499887067567080487,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=1520 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1944 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --pdf-upsell-enabled --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=31 --always-read-main-dll --field-trial-handle=5852,i,15295945936880672652,14499887067567080487,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=4312 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2264 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=5944,i,15295945936880672652,14499887067567080487,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=3828 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2292 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2372 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2760 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2768,i,15295945936880672652,14499887067567080487,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=2756 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2764 | "C:\Users\admin\AppData\Local\Temp\is-M4VN1.tmp\WayBack14.tmp" /SL5="$140050,69066834,58368,C:\Users\admin\Downloads\WayBack14.exe" | C:\Users\admin\AppData\Local\Temp\is-M4VN1.tmp\WayBack14.tmp | — | WayBack14.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
Total events
11 756
Read events
11 694
Write events
60
Delete events
2
Modification events
| (PID) Process: | (7036) WayBack14.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{1293FFAF-6559-4467-B876-21DE91B4EA46}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.6.1 (a) | |||
| (PID) Process: | (7036) WayBack14.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{1293FFAF-6559-4467-B876-21DE91B4EA46}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files (x86)\WayBack14 | |||
| (PID) Process: | (7036) WayBack14.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{1293FFAF-6559-4467-B876-21DE91B4EA46}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files (x86)\WayBack14\ | |||
| (PID) Process: | (7036) WayBack14.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{1293FFAF-6559-4467-B876-21DE91B4EA46}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: WayBack14 | |||
| (PID) Process: | (7036) WayBack14.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{1293FFAF-6559-4467-B876-21DE91B4EA46}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (7036) WayBack14.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{1293FFAF-6559-4467-B876-21DE91B4EA46}_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: default | |||
| (PID) Process: | (7036) WayBack14.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{1293FFAF-6559-4467-B876-21DE91B4EA46}_is1 |
| Operation: | write | Name: | DisplayName |
Value: WayBack14 version 1.5 | |||
| (PID) Process: | (7036) WayBack14.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{1293FFAF-6559-4467-B876-21DE91B4EA46}_is1 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files (x86)\WayBack14\unins000.exe" | |||
| (PID) Process: | (7036) WayBack14.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{1293FFAF-6559-4467-B876-21DE91B4EA46}_is1 |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Program Files (x86)\WayBack14\unins000.exe" /SILENT | |||
| (PID) Process: | (7036) WayBack14.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{1293FFAF-6559-4467-B876-21DE91B4EA46}_is1 |
| Operation: | write | Name: | DisplayVersion |
Value: 1.5 | |||
Executable files
87
Suspicious files
1 052
Text files
1 486
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1e4fc4.TMP | — | |
MD5:— | SHA256:— | |||
| 6156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1e4fd3.TMP | — | |
MD5:— | SHA256:— | |||
| 6156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1e4fd3.TMP | — | |
MD5:— | SHA256:— | |||
| 6156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1e4fd3.TMP | — | |
MD5:— | SHA256:— | |||
| 6156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1e4fd3.TMP | — | |
MD5:— | SHA256:— | |||
| 6156 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
409
TCP/UDP connections
173
DNS requests
133
Threats
233
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6596 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:E2o-Vwi981gx5Z_8Lk6CapK6oVoRNcw3i0qj4x0P6oc&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 101 b | whitelisted |
5568 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 312 b | whitelisted |
6596 | msedge.exe | GET | 200 | 88.214.231.100:80 | http://wb14.my.to/CSS/Base/CSS/Ads.css | RU | text | 662 b | unknown |
6596 | msedge.exe | GET | 200 | 88.214.231.100:80 | http://wb14.my.to/ | RU | text | 11.6 Kb | unknown |
6596 | msedge.exe | GET | 200 | 88.214.231.100:80 | http://wb14.my.to/CSS/PartialViews/Navigation.css | RU | text | 2.08 Kb | unknown |
6596 | msedge.exe | GET | — | 88.214.231.100:80 | http://wb14.my.to/CSS/Base/CSS/Roblox.css | RU | — | — | unknown |
6596 | msedge.exe | GET | 200 | 88.214.231.100:80 | http://wb14.my.to/CSS/RBXCommon.css | RU | text | 1.61 Kb | unknown |
6596 | msedge.exe | GET | 200 | 88.214.231.100:80 | http://wb14.my.to/CSS/Base/CSS/carouselpager.css | RU | text | 267 b | unknown |
6596 | msedge.exe | GET | 200 | 88.214.231.100:80 | http://wb14.my.to/CSS/Base/CSS/ContentBuilder.css | RU | text | 535 b | unknown |
6596 | msedge.exe | GET | 200 | 88.214.231.100:80 | http://wb14.my.to/CSS/Base/CSS/Footer.css | RU | text | 728 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7004 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7544 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 2.16.241.206:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
5568 | SearchApp.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3412 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6596 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6596 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
wb14.my.to |
| unknown |
api.edgeoffer.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6596 | msedge.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.my .to Domain |
6596 | msedge.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.my .to Domain |
6596 | msedge.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS HTTP Request to a *.my .to Domain |
6596 | msedge.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS HTTP Request to a *.my .to Domain |
6596 | msedge.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS HTTP Request to a *.my .to Domain |
6596 | msedge.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS HTTP Request to a *.my .to Domain |
6596 | msedge.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS HTTP Request to a *.my .to Domain |
6596 | msedge.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS HTTP Request to a *.my .to Domain |
6596 | msedge.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS HTTP Request to a *.my .to Domain |
6596 | msedge.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS HTTP Request to a *.my .to Domain |
Process | Message |
|---|---|
RobloxStudioBeta.exe | Object::connect: No such slot RobloxFindWidget::endItem() in D:\BuildAgent\work\Trunk2012\Client\RobloxStudio\RobloxFindWidget.cpp:126
|