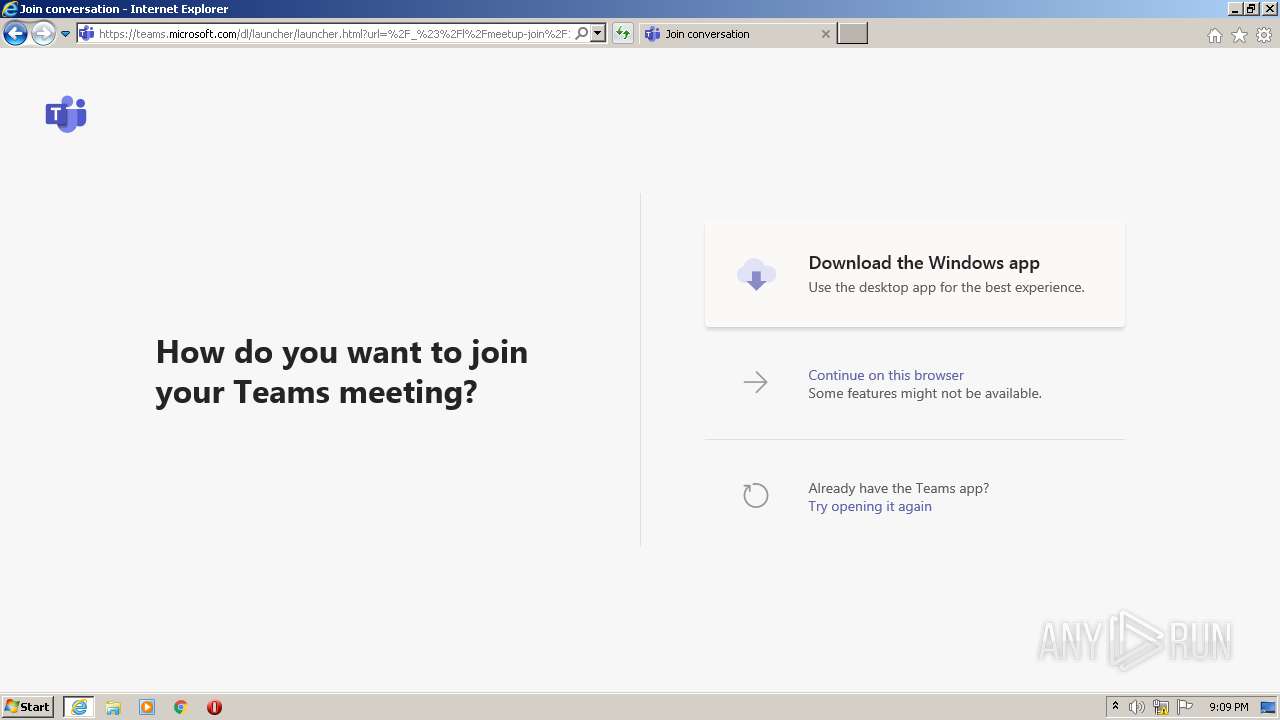
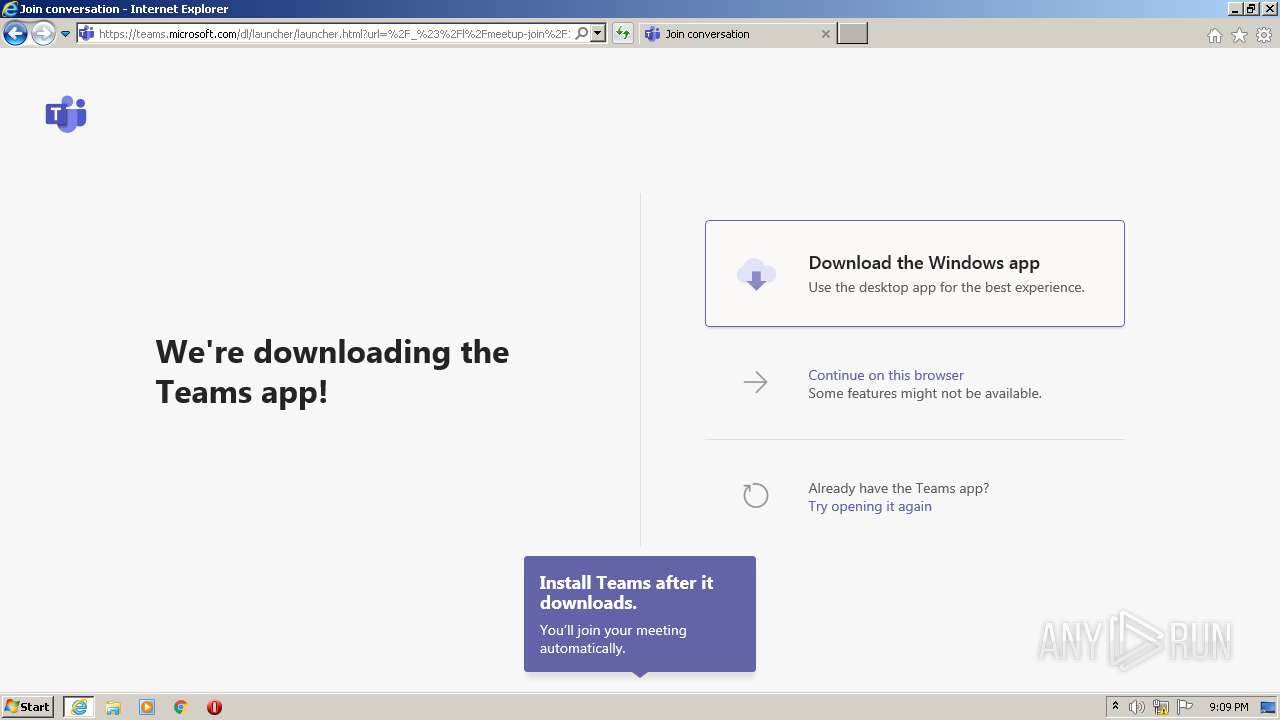
| URL: | https://teams.microsoft.com/l/meetup-join/19%3ameeting_ZjQ5ZTAzM2EtNmVhOS00NzRmLTgwYjctMGZmZjc3NmQ1MzQ5%40thread.v2/0?context=%7b%22Tid%22%3a%221d96fa6e-38c4-4eff-a0b0-72c01218a89c%22%2c%22Oid%22%3a%22c9a94c60-2057-4f96-8ed4-6c82e53a7193%22%7d |
| Full analysis: | https://app.any.run/tasks/66c131de-9ee3-4440-86e3-f2d3d581149a |
| Verdict: | Malicious activity |
| Analysis date: | December 16, 2020, 21:09:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4852E825319777E3F25F5E0B5ED0CDB4 |
| SHA1: | ECA2DA99B20F837FCEED5CEEBDB4C2E29334BB3B |
| SHA256: | BDCD705ECA99DF47FB1732FC9B1A11274B573C780CEB5E0643CFD37393A265D7 |
| SSDEEP: | 6:2In+DEDryczKH/1rgpTIHvUFAoXyj8AKwGh7VP0dEovADAcso//r:2In+DEyVOKHeXXCKwGrNovdE3r |
MALICIOUS
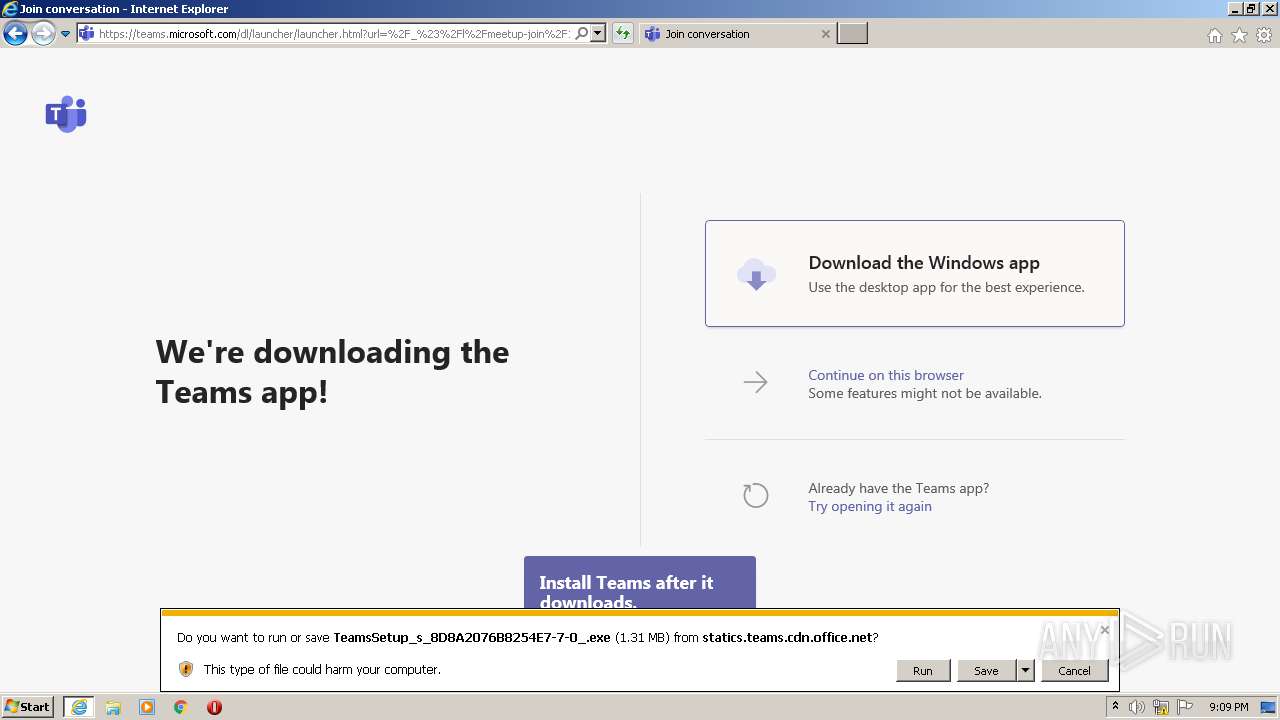
Application was dropped or rewritten from another process
- TeamsSetup_s_8D8A2076B8254E7-7-0_.exe (PID: 1852)
- Update.exe (PID: 2904)
- Squirrel.exe (PID: 3856)
- Update.exe (PID: 1440)
Drops executable file immediately after starts
- TeamsSetup_s_8D8A2076B8254E7-7-0_.exe (PID: 1852)
Loads dropped or rewritten executable
- Teams.exe (PID: 3992)
- regsvr32.exe (PID: 2584)
- Teams.exe (PID: 3568)
- Teams.exe (PID: 636)
- Teams.exe (PID: 1520)
- Teams.exe (PID: 2072)
- Teams.exe (PID: 1296)
- Teams.exe (PID: 1144)
- Teams.exe (PID: 2128)
- Teams.exe (PID: 3852)
- Teams.exe (PID: 1560)
- Teams.exe (PID: 3148)
- Teams.exe (PID: 2568)
Registers / Runs the DLL via REGSVR32.EXE
- Update.exe (PID: 2904)
SUSPICIOUS
Executable content was dropped or overwritten
- iexplore.exe (PID: 1960)
- TeamsSetup_s_8D8A2076B8254E7-7-0_.exe (PID: 1852)
- iexplore.exe (PID: 1892)
- Update.exe (PID: 2904)
- Squirrel.exe (PID: 3856)
Drops a file with a compile date too recent
- iexplore.exe (PID: 1892)
- iexplore.exe (PID: 1960)
- TeamsSetup_s_8D8A2076B8254E7-7-0_.exe (PID: 1852)
- Update.exe (PID: 2904)
- Squirrel.exe (PID: 3856)
Reads Environment values
- Update.exe (PID: 2904)
- Squirrel.exe (PID: 3856)
- Update.exe (PID: 1440)
- Teams.exe (PID: 3568)
Creates files in the user directory
- Update.exe (PID: 2904)
- Teams.exe (PID: 3148)
- Update.exe (PID: 1440)
- Teams.exe (PID: 3568)
- Teams.exe (PID: 1520)
- Teams.exe (PID: 1560)
- Teams.exe (PID: 3468)
Reads CPU info
- Teams.exe (PID: 3148)
- Teams.exe (PID: 3568)
Application launched itself
- Teams.exe (PID: 3148)
- Teams.exe (PID: 3568)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 2584)
Changes default file association
- Teams.exe (PID: 3568)
Drops a file with too old compile date
- Update.exe (PID: 2904)
Creates a software uninstall entry
- Update.exe (PID: 2904)
Drops a file that was compiled in debug mode
- Update.exe (PID: 2904)
INFO
Application launched itself
- iexplore.exe (PID: 1892)
Reads settings of System Certificates
- iexplore.exe (PID: 1960)
- iexplore.exe (PID: 1892)
- Teams.exe (PID: 1520)
- Squirrel.exe (PID: 3856)
- Teams.exe (PID: 1560)
Reads internet explorer settings
- iexplore.exe (PID: 1960)
Changes internet zones settings
- iexplore.exe (PID: 1892)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 1960)
Changes settings of System certificates
- iexplore.exe (PID: 1892)
Creates files in the user directory
- iexplore.exe (PID: 1960)
- iexplore.exe (PID: 1892)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1892)
Modifies the phishing filter of IE
- iexplore.exe (PID: 1892)
Reads Microsoft Office registry keys
- Update.exe (PID: 2904)
- Update.exe (PID: 1440)
- Teams.exe (PID: 3568)
- Squirrel.exe (PID: 3856)
Reads the hosts file
- Teams.exe (PID: 3148)
- Teams.exe (PID: 3568)
- Teams.exe (PID: 1520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
58
Monitored processes
20
Malicious processes
11
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 636 | "C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe" --type=gpu-process --field-trial-handle=1112,7276041775504283787,1488835834570080914,131072 --enable-features=WebComponentsV0Enabled --disable-features=PictureInPicture,SpareRendererForSitePerProcess --no-sandbox --electron-shared-settings=eyJjci5jb21wYW55IjoiRWxlY3Ryb24iLCJjci5kdW1wcyI6IiIsImNyLmVuYWJsZWQiOmZhbHNlLCJjci5wcm9kdWN0IjoiRWxlY3Ryb24iLCJjci5zZXNzaW9uIjoiIiwiY3IudXJsIjoiIiwiY3IudmVyc2lvbiI6IiJ9 --gpu-preferences=KAAAAAAAAADgAAAwAAAAAAAAYAAAAAAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --mojo-platform-channel-handle=1144 /prefetch:2 | C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe | — | Teams.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 0 Version: 1.3.00.28779 Modules
| |||||||||||||||
| 1144 | "C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe" --type=gpu-process --field-trial-handle=1112,7276041775504283787,1488835834570080914,131072 --enable-features=WebComponentsV0Enabled --disable-features=PictureInPicture,SpareRendererForSitePerProcess --no-sandbox --electron-shared-settings=eyJjci5jb21wYW55IjoiRWxlY3Ryb24iLCJjci5kdW1wcyI6IiIsImNyLmVuYWJsZWQiOmZhbHNlLCJjci5wcm9kdWN0IjoiRWxlY3Ryb24iLCJjci5zZXNzaW9uIjoiIiwiY3IudXJsIjoiIiwiY3IudmVyc2lvbiI6IiJ9 --gpu-preferences=KAAAAAAAAADgAAAwAAAAAAAAYAAAAAAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1144 /prefetch:2 | C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe | — | Teams.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 0 Version: 1.3.00.28779 Modules
| |||||||||||||||
| 1296 | "C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe" --type=renderer --no-sandbox --autoplay-policy=no-user-gesture-required --disable-background-timer-throttling --field-trial-handle=1112,7276041775504283787,1488835834570080914,131072 --enable-features=WebComponentsV0Enabled --disable-features=PictureInPicture,SpareRendererForSitePerProcess --lang=en-US --enable-wer --ms-legacy-ipc-serialization --app-user-model-id=com.squirrel.Teams.Teams --app-path="C:\Users\admin\AppData\Local\Microsoft\Teams\current\resources\app.asar" --no-sandbox --no-zygote --preload="C:\Users\admin\AppData\Local\Microsoft\Teams\current\resources\app.asar\lib\renderer\notifications\preload_notifications.js" --background-color=#fff --enable-websql --electron-shared-settings=eyJjci5jb21wYW55IjoiRWxlY3Ryb24iLCJjci5kdW1wcyI6IiIsImNyLmVuYWJsZWQiOmZhbHNlLCJjci5wcm9kdWN0IjoiRWxlY3Ryb24iLCJjci5zZXNzaW9uIjoiIiwiY3IudXJsIjoiIiwiY3IudmVyc2lvbiI6IiJ9 --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1960 /prefetch:1 --msteams-process-type=notificationsManager | C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe | — | Teams.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 0 Version: 1.3.00.28779 Modules
| |||||||||||||||
| 1440 | C:\Users\admin\AppData\Local\Microsoft\Teams\Update.exe --createShortcut=Teams.exe -l=StartMenu,Desktop | C:\Users\admin\AppData\Local\Microsoft\Teams\Update.exe | Teams.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 0 Version: 1.10.54.0 Modules
| |||||||||||||||
| 1520 | "C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe" --type=utility --field-trial-handle=1112,7276041775504283787,1488835834570080914,131072 --enable-features=WebComponentsV0Enabled --disable-features=PictureInPicture,SpareRendererForSitePerProcess --lang=en-US --service-sandbox-type=network --no-sandbox --enable-wer --ms-legacy-ipc-serialization --electron-shared-settings=eyJjci5jb21wYW55IjoiRWxlY3Ryb24iLCJjci5kdW1wcyI6IiIsImNyLmVuYWJsZWQiOmZhbHNlLCJjci5wcm9kdWN0IjoiRWxlY3Ryb24iLCJjci5zZXNzaW9uIjoiIiwiY3IudXJsIjoiIiwiY3IudmVyc2lvbiI6IiJ9 --mojo-platform-channel-handle=1436 /prefetch:8 | C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe | Teams.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 0 Version: 1.3.00.28779 Modules
| |||||||||||||||
| 1560 | "C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe" --type=renderer --no-sandbox --autoplay-policy=no-user-gesture-required --disable-background-timer-throttling --field-trial-handle=1112,7276041775504283787,1488835834570080914,131072 --enable-features=WebComponentsV0Enabled --disable-features=PictureInPicture,SpareRendererForSitePerProcess --disable-gpu-compositing --lang=en-US --enable-wer --ms-legacy-ipc-serialization --app-user-model-id=com.squirrel.Teams.Teams --app-path="C:\Users\admin\AppData\Local\Microsoft\Teams\current\resources\app.asar" --no-sandbox --no-zygote --preload="C:\Users\admin\AppData\Local\Microsoft\Teams\current\resources\app.asar\lib\pluginhost\preload.js" --background-color=#fff --enable-websql --electron-shared-settings=eyJjci5jb21wYW55IjoiRWxlY3Ryb24iLCJjci5kdW1wcyI6IiIsImNyLmVuYWJsZWQiOmZhbHNlLCJjci5wcm9kdWN0IjoiRWxlY3Ryb24iLCJjci5zZXNzaW9uIjoiIiwiY3IudXJsIjoiIiwiY3IudmVyc2lvbiI6IiJ9 --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2444 /prefetch:1 --msteams-process-type=pluginHost | C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe | Teams.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 0 Version: 1.3.00.28779 Modules
| |||||||||||||||
| 1852 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\TeamsSetup_s_8D8A2076B8254E7-7-0_.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\TeamsSetup_s_8D8A2076B8254E7-7-0_.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 0 Version: 1.3.00.28779 Modules
| |||||||||||||||
| 1892 | "C:\Program Files\Internet Explorer\iexplore.exe" https://teams.microsoft.com/l/meetup-join/19%3ameeting_ZjQ5ZTAzM2EtNmVhOS00NzRmLTgwYjctMGZmZjc3NmQ1MzQ5%40thread.v2/0?context=%7b%22Tid%22%3a%221d96fa6e-38c4-4eff-a0b0-72c01218a89c%22%2c%22Oid%22%3a%22c9a94c60-2057-4f96-8ed4-6c82e53a7193%22%7d | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1960 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1892 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2072 | "C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe" --type=renderer --no-sandbox --autoplay-policy=no-user-gesture-required --disable-background-timer-throttling --field-trial-handle=1112,7276041775504283787,1488835834570080914,131072 --enable-features=WebComponentsV0Enabled --disable-features=PictureInPicture,SpareRendererForSitePerProcess --lang=en-US --enable-wer --ms-legacy-ipc-serialization --app-user-model-id=com.squirrel.Teams.Teams --app-path="C:\Users\admin\AppData\Local\Microsoft\Teams\current\resources\app.asar" --no-sandbox --no-zygote --preload="C:\Users\admin\AppData\Local\Microsoft\Teams\current\resources\app.asar\lib\renderer\preload_default.js" --background-color=#FFFFFFFF --enable-websql --electron-shared-settings=eyJjci5jb21wYW55IjoiRWxlY3Ryb24iLCJjci5kdW1wcyI6IiIsImNyLmVuYWJsZWQiOmZhbHNlLCJjci5wcm9kdWN0IjoiRWxlY3Ryb24iLCJjci5zZXNzaW9uIjoiIiwiY3IudXJsIjoiIiwiY3IudmVyc2lvbiI6IiJ9 --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1608 /prefetch:1 --msteams-process-type=loadingWindow | C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe | — | Teams.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 0 Version: 1.3.00.28779 Modules
| |||||||||||||||
Total events
5 553
Read events
5 017
Write events
531
Delete events
5
Modification events
| (PID) Process: | (1892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3616964700 | |||
| (PID) Process: | (1892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30856175 | |||
| (PID) Process: | (1892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1892) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
491
Suspicious files
78
Text files
383
Unknown types
93
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1960 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab463F.tmp | — | |
MD5:— | SHA256:— | |||
| 1960 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar4640.tmp | — | |
MD5:— | SHA256:— | |||
| 1960 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\3D0GG386.txt | — | |
MD5:— | SHA256:— | |||
| 1960 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\M5AHY3YN.txt | — | |
MD5:— | SHA256:— | |||
| 1960 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 1960 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\launcher[1].htm | html | |
MD5:— | SHA256:— | |||
| 1960 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\launcher.ebb9dfff696e8aafc37b[1].css | text | |
MD5:— | SHA256:— | |||
| 1960 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\4JLZI02E.txt | text | |
MD5:— | SHA256:— | |||
| 1960 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\launcher.5c24f1e70f34f56835c7[1].js | text | |
MD5:— | SHA256:— | |||
| 1960 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\DOMStore\CTF95U70\teams.microsoft[1].xml | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
88
DNS requests
69
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1960 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQQX6Z6gAidtSefNc6DC0OInqPHDQQUD4BhHIIxYdUvKOeNRji0LOHG2eICEAx1RnvjEFg%2BN7i1aftiJ0A%3D | US | der | 471 b | whitelisted |
1960 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | US | der | 471 b | whitelisted |
1960 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 471 b | whitelisted |
1960 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQQX6Z6gAidtSefNc6DC0OInqPHDQQUD4BhHIIxYdUvKOeNRji0LOHG2eICEAx1RnvjEFg%2BN7i1aftiJ0A%3D | US | der | 471 b | whitelisted |
1960 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 471 b | whitelisted |
1960 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 471 b | whitelisted |
1960 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
1892 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
1960 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1960 | iexplore.exe | 52.114.74.23:443 | scheduler.teams.microsoft.com | Microsoft Corporation | NL | unknown |
1960 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1960 | iexplore.exe | 52.113.194.132:443 | teams.microsoft.com | Microsoft Corporation | US | suspicious |
1892 | iexplore.exe | 52.113.194.132:443 | teams.microsoft.com | Microsoft Corporation | US | suspicious |
1960 | iexplore.exe | 52.114.158.91:443 | browser.pipe.aria.microsoft.com | Microsoft Corporation | US | unknown |
1892 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1960 | iexplore.exe | 92.122.188.29:443 | statics.teams.cdn.office.net | NTT America, Inc. | — | suspicious |
1960 | iexplore.exe | 152.199.19.160:443 | az725175.vo.msecnd.net | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1960 | iexplore.exe | 40.77.226.250:443 | web.vortex.data.microsoft.com | Microsoft Corporation | IE | whitelisted |
2904 | Update.exe | 52.113.194.132:443 | teams.microsoft.com | Microsoft Corporation | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
teams.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
statics.teams.microsoft.com |
| whitelisted |
statics.teams.cdn.office.net |
| whitelisted |
scheduler.teams.microsoft.com |
| whitelisted |
az725175.vo.msecnd.net |
| whitelisted |
web.vortex.data.microsoft.com |
| whitelisted |
browser.pipe.aria.microsoft.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Update.exe | Update.exe Information: 0 : |
Update.exe | Starting TelemetryManager constructor
|
Update.exe | Update.exe Information: 0 : |
Update.exe | TelemetryManagerImpl creation started
|
Update.exe | Update.exe Information: 0 : |
Update.exe | Performance counters are disabled. Skipping creation of counters category.
|
Update.exe | Update.exe Information: 0 : |
Update.exe | RecordBatcherTask with ID 4 started.
|
Update.exe | Update.exe Information: 0 : |
Update.exe | DataPackageSender with UserAgent name: AST-exe-C#, version: 1.10.54.0, [Ast_Default_Source]
|