| File name: | UserProfileSvcEoP.exe |
| Full analysis: | https://app.any.run/tasks/874c630c-2e08-4a3a-a400-a7bd36463dcf |
| Verdict: | Malicious activity |
| Analysis date: | October 27, 2021, 13:49:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 170810AACA95544A43D2BE0E5F5BD59B |
| SHA1: | C8960E48ACD070F29FD53197590EF2283F4EE906 |
| SHA256: | BDCB86E57332CC0B98C9F86456C4D014F6CF9FF96C21287AF25046DC9DFF8FA5 |
| SSDEEP: | 12288:glAWxjfTuz0fZhOBmlM7/cx80ZXspi6wc8DYi39z:4ZdMQx8mspi1REYV |
MALICIOUS
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 3576)
SUSPICIOUS
Checks supported languages
- cmd.exe (PID: 1472)
- UserProfileSvcEoP.exe (PID: 3280)
- UserProfileSvcEoP.exe (PID: 3668)
- cmd.exe (PID: 3576)
- UserProfileSvcEoP.exe (PID: 1940)
Reads the computer name
- UserProfileSvcEoP.exe (PID: 3280)
- UserProfileSvcEoP.exe (PID: 3668)
- UserProfileSvcEoP.exe (PID: 1940)
INFO
Checks supported languages
- net.exe (PID: 3828)
- net1.exe (PID: 2504)
- osk.exe (PID: 4020)
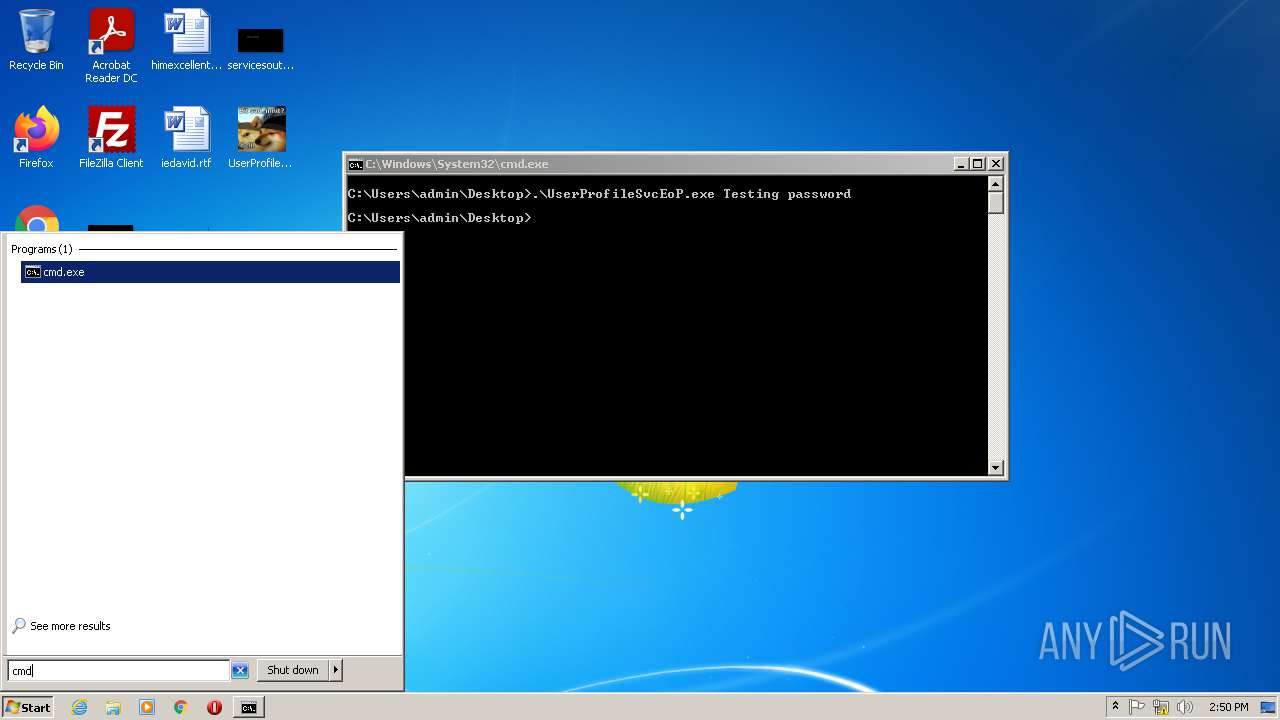
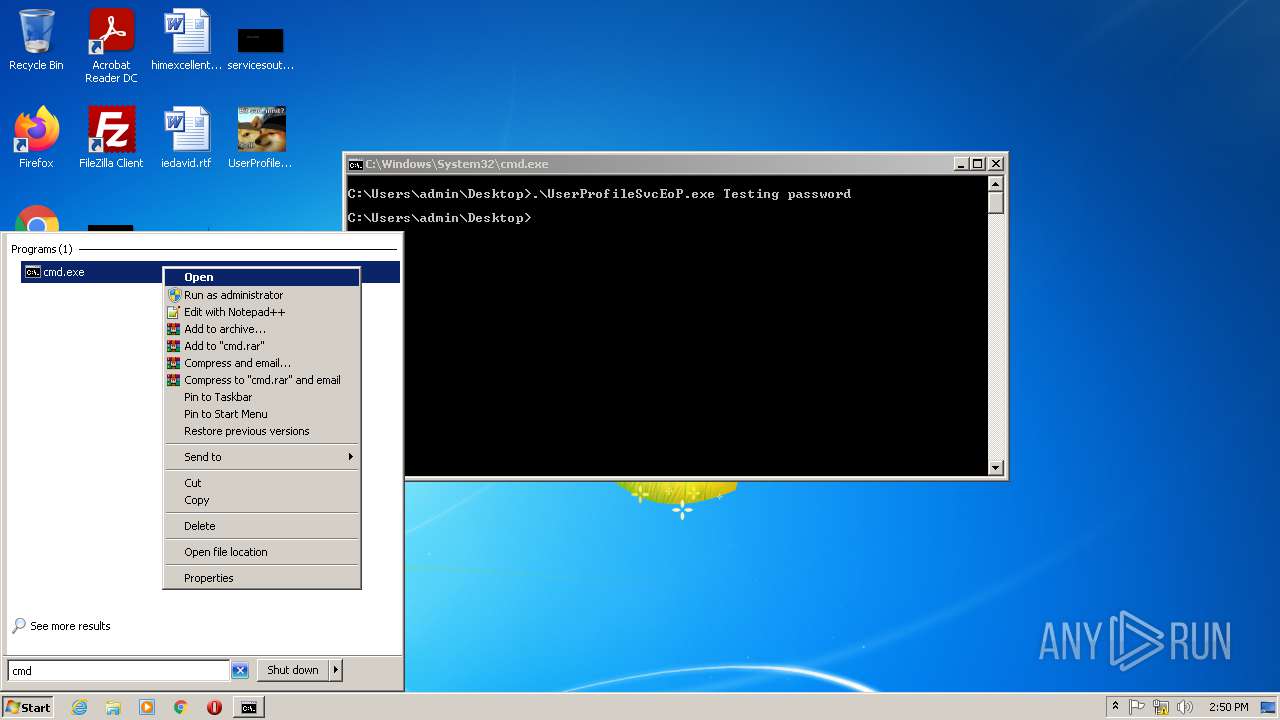
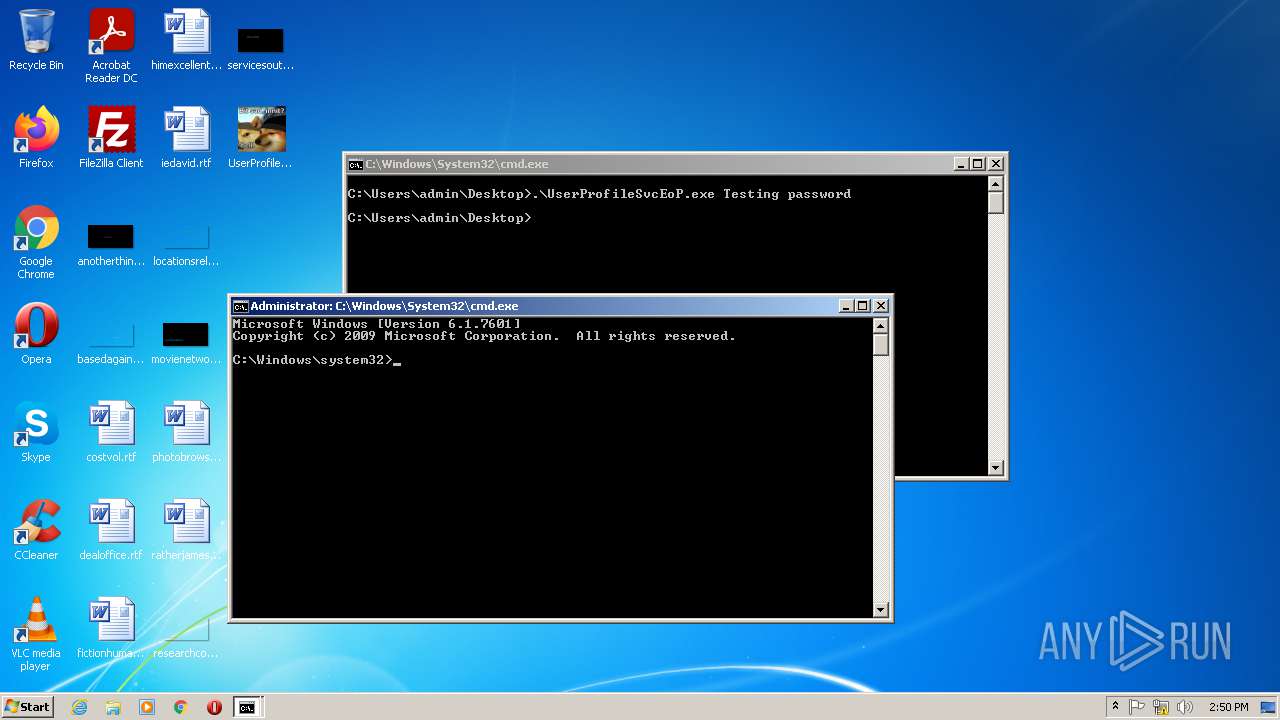
Manual execution by user
- cmd.exe (PID: 3576)
Reads the computer name
- net1.exe (PID: 2504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:10:22 16:09:32+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.29 |
| CodeSize: | 96256 |
| InitializedDataSize: | 425984 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6298 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 22-Oct-2021 14:09:32 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 22-Oct-2021 14:09:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001773D | 0x00017800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60467 |
.rdata | 0x00019000 | 0x00007FA6 | 0x00008000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.1341 |
.data | 0x00021000 | 0x00001624 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.41715 |
.rsrc | 0x00023000 | 0x0005D340 | 0x0005D400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.48472 |
.reloc | 0x00081000 | 0x00001400 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.53614 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 6.51079 | 67624 | UNKNOWN | English - United Kingdom | RT_ICON |
3 | 6.59815 | 16936 | UNKNOWN | English - United Kingdom | RT_ICON |
4 | 6.54201 | 9640 | UNKNOWN | English - United Kingdom | RT_ICON |
5 | 6.6483 | 4264 | UNKNOWN | English - United Kingdom | RT_ICON |
6 | 6.46979 | 1128 | UNKNOWN | English - United Kingdom | RT_ICON |
101 | 4.84924 | 10752 | UNKNOWN | English - United Kingdom | DLL |
107 | 2.76511 | 90 | UNKNOWN | English - United Kingdom | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHELL32.dll |
USERENV.dll |
ole32.dll |
Total processes
55
Monitored processes
11
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1472 | "C:\Windows\System32\cmd.exe" /k C:\Users\admin\Desktop\UserProfileSvcEoP.exe TestUser Password | C:\Windows\System32\cmd.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
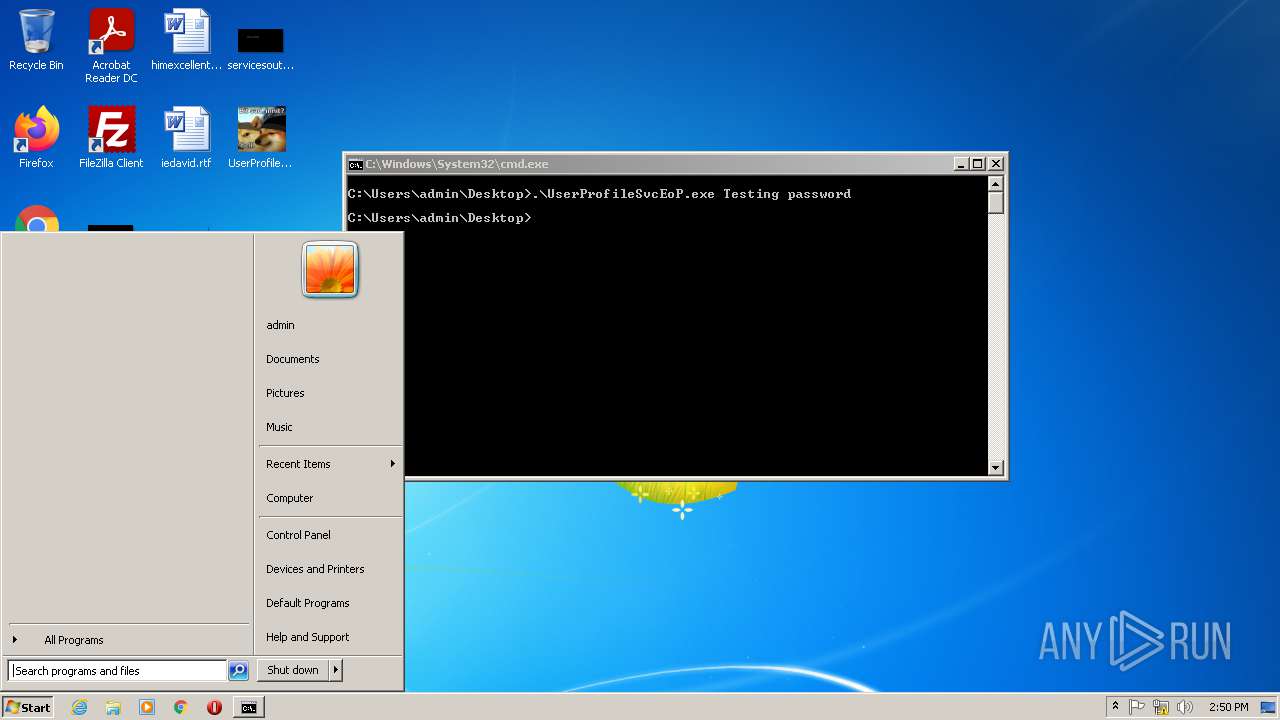
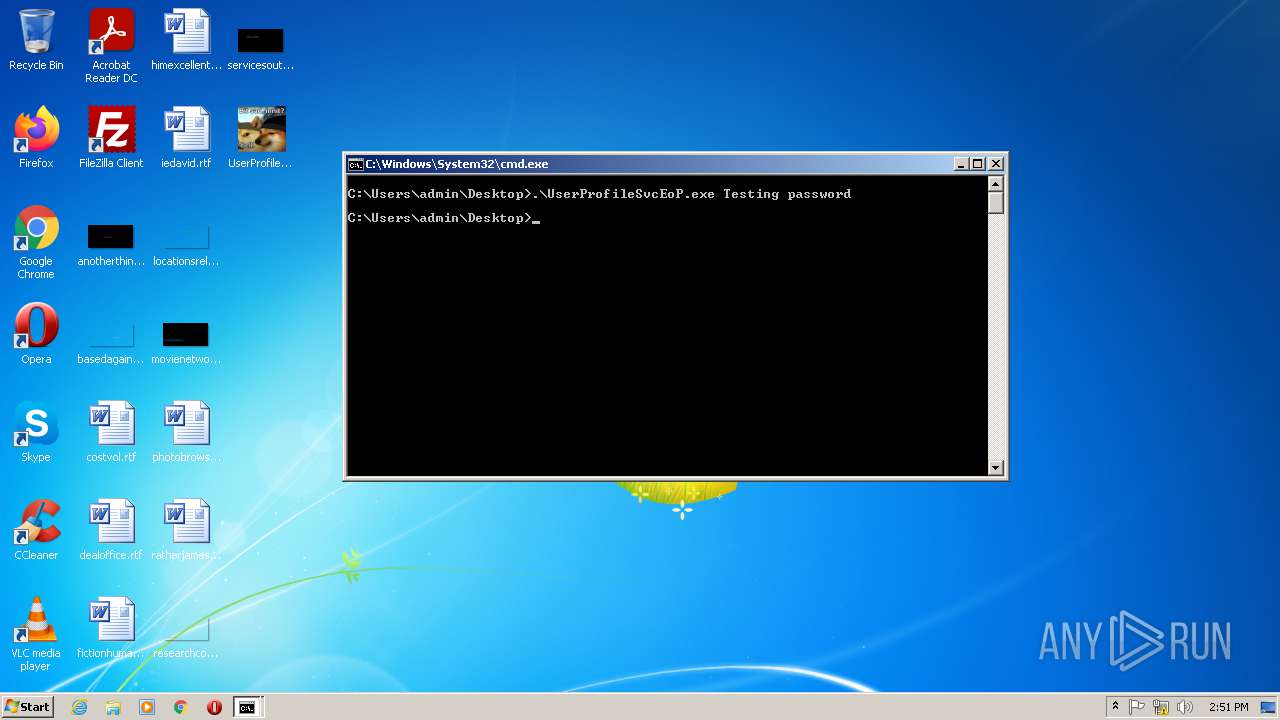
| 1940 | .\UserProfileSvcEoP.exe Testing password | C:\Users\admin\Desktop\UserProfileSvcEoP.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2132 | "C:\Windows\notepad.exe" | C:\Windows\notepad.exe | — | UserProfileSvcEoP.exe | |||||||||||
User: Testing Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2504 | C:\Windows\system32\net1 user /add Testing password | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3280 | C:\Users\admin\Desktop\UserProfileSvcEoP.exe TestUser Password | C:\Users\admin\Desktop\UserProfileSvcEoP.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 3352 | "C:\Windows\notepad.exe" | C:\Windows\notepad.exe | — | UserProfileSvcEoP.exe | |||||||||||
User: Testing Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
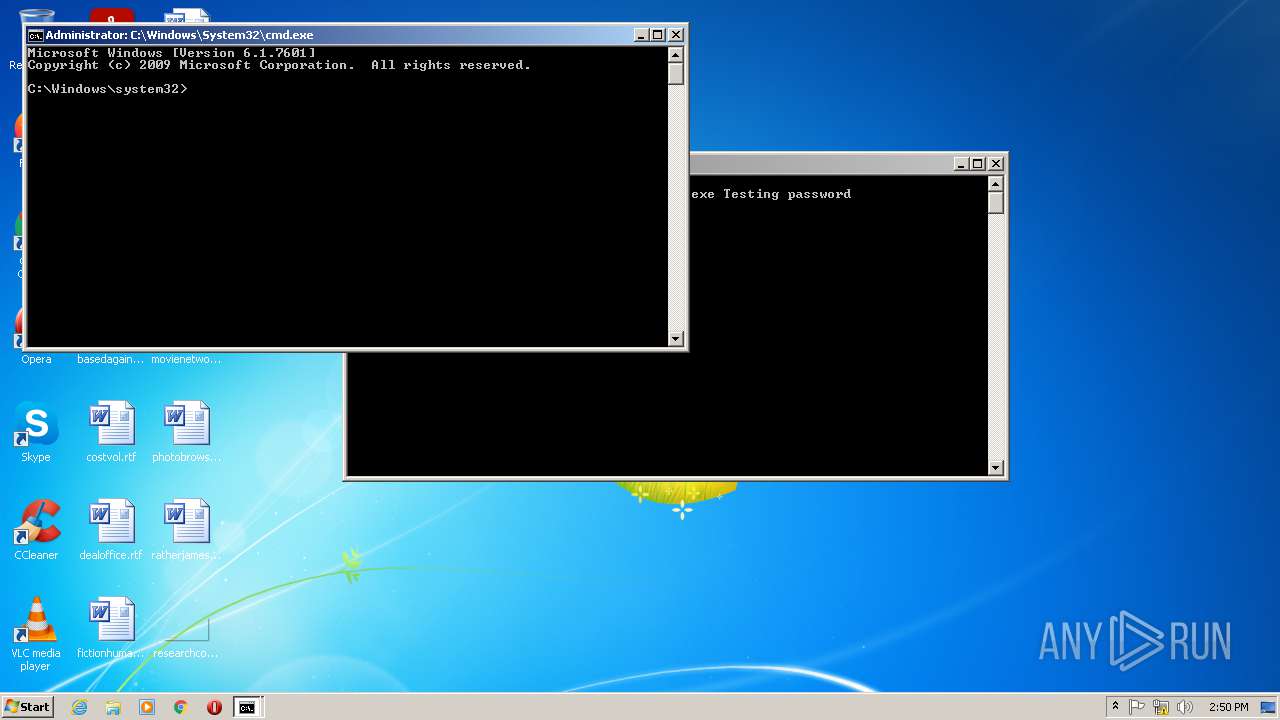
| 3576 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3668 | .\UserProfileSvcEoP.exe Testing password | C:\Users\admin\Desktop\UserProfileSvcEoP.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 3828 | net user /add Testing password | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3840 | "C:\Windows\System32\osk.exe" | C:\Windows\System32\osk.exe | — | UserProfileSvcEoP.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Accessibility On-Screen Keyboard Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
229
Read events
220
Write events
9
Delete events
0
Modification events
| (PID) Process: | (1940) UserProfileSvcEoP.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1940) UserProfileSvcEoP.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1940) UserProfileSvcEoP.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1940) UserProfileSvcEoP.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4020) osk.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\AccessibilityTemp |
| Operation: | write | Name: | osk |
Value: 3 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report