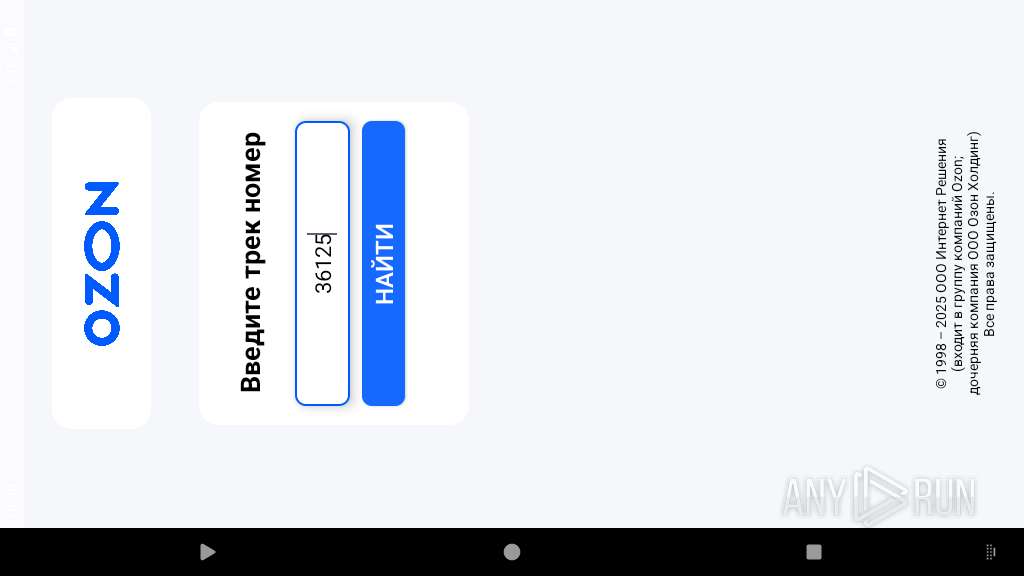
| File name: | OzonTracker.apk |
| Full analysis: | https://app.any.run/tasks/cee759e7-635e-4df5-997e-5764dd25a266 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 10:30:02 |
| OS: | Android 14 |
| MIME: | application/vnd.android.package-archive |
| File info: | Android package (APK), with gradle app-metadata.properties |
| MD5: | AA0F9E63574A2FD27A9BA43DF7F6D54C |
| SHA1: | 0F0FA15E9B37D9980890DC723CED26D75EB1A5E4 |
| SHA256: | BDC94D6BAF0CF939B33F4928CC4CC15ACC24A87FFFD53AFAD3CC6D8FC5D6A047 |
| SSDEEP: | 98304:Sf4q6JEebOtc5Aul6iBIwedFXoRkZChgFRfcYRLBLW+ELgy9DXYywnpn+a4nuMxw:Mz6CnMdGu5TDS5HpgQIC |
MALICIOUS
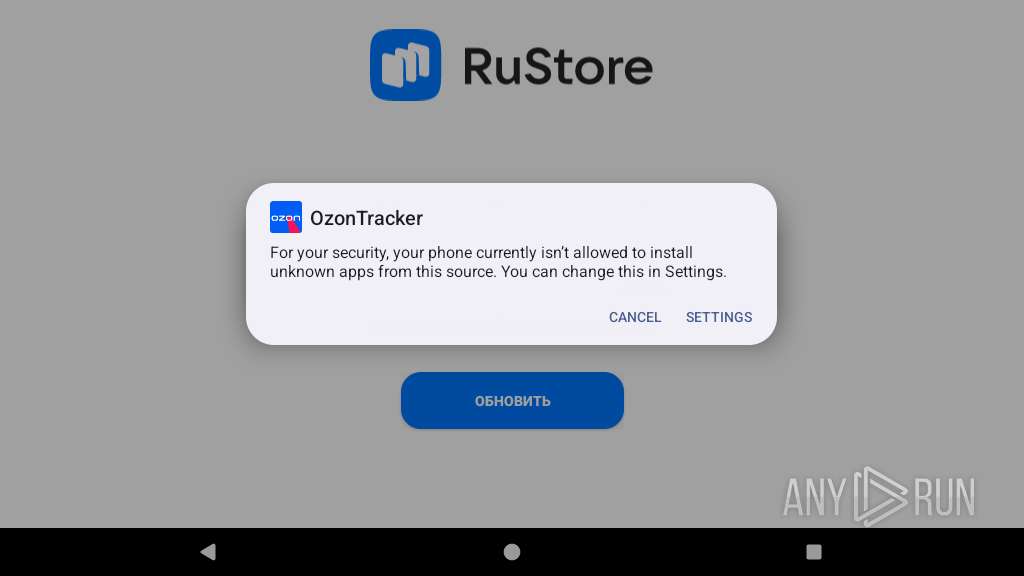
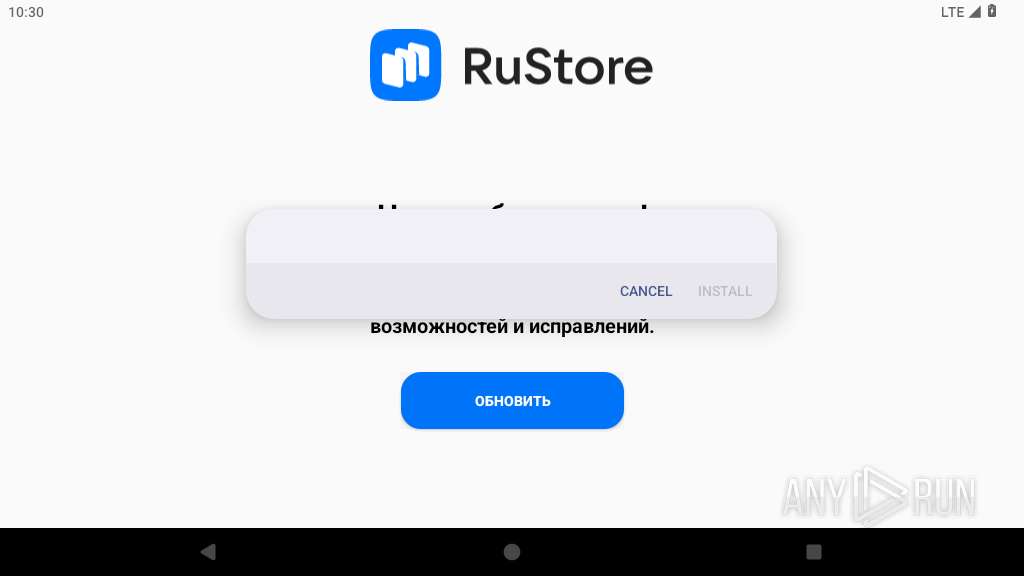
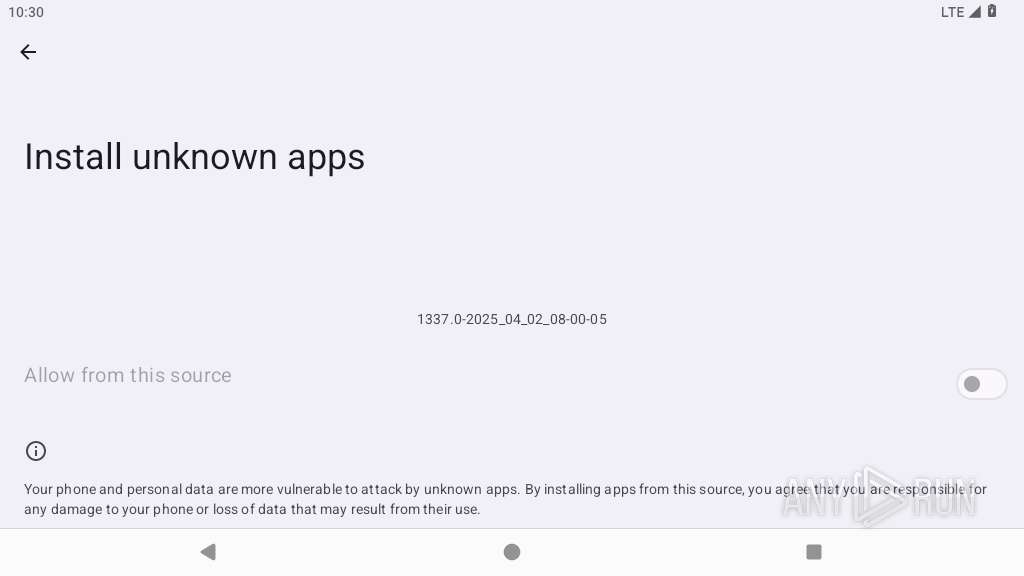
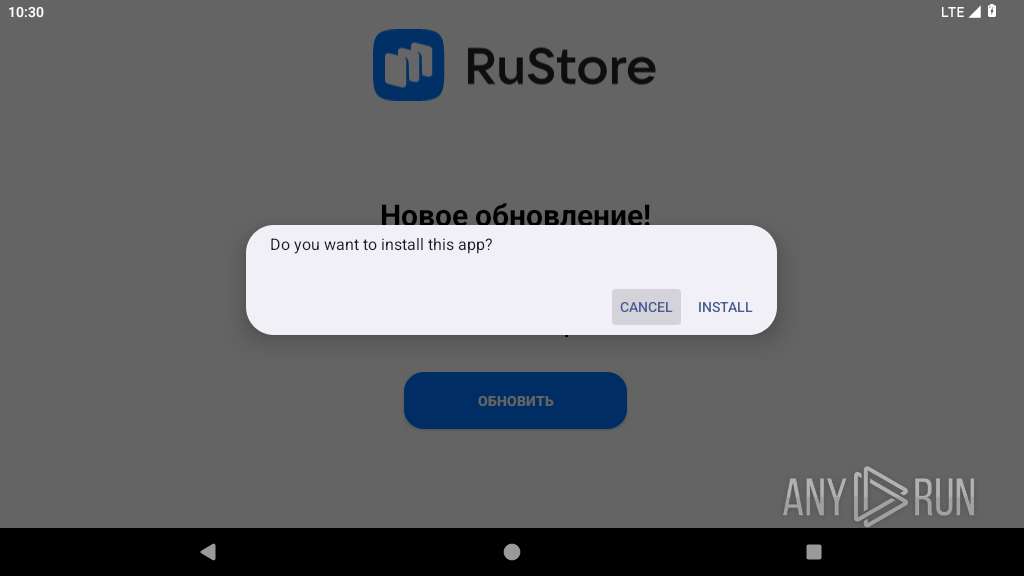
Initiates background APK installation
- app_process64 (PID: 2253)
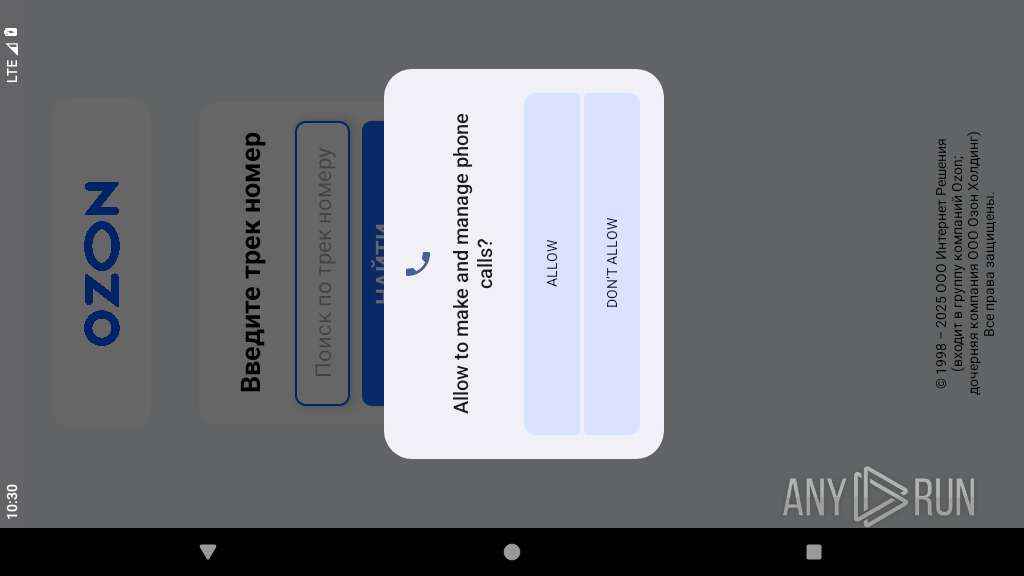
Returns the phone's primary line number (MSISDN)
- app_process64 (PID: 2396)
SUSPICIOUS
Launches a new activity
- app_process64 (PID: 2253)
- app_process64 (PID: 2396)
Starts a service
- app_process64 (PID: 2396)
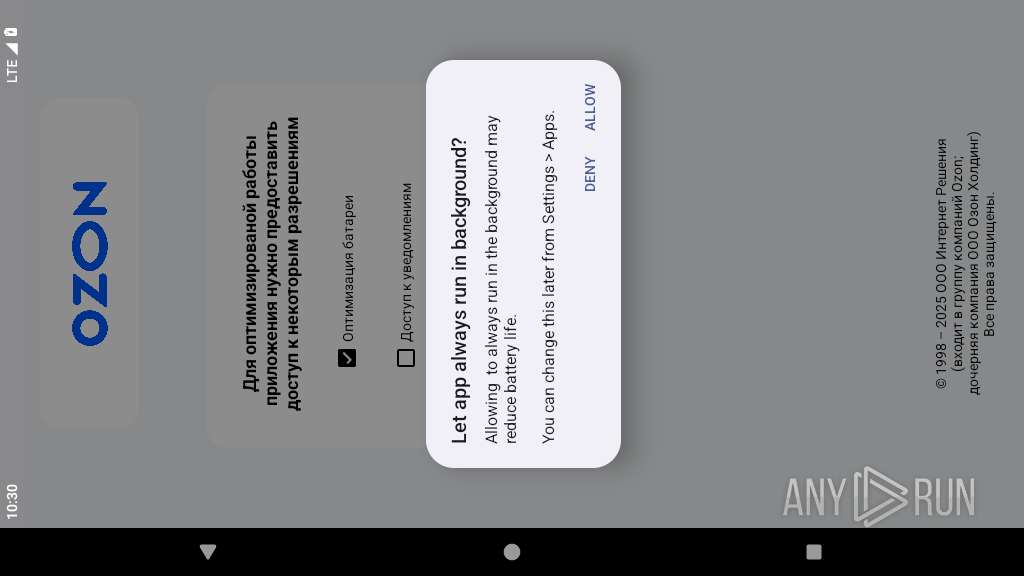
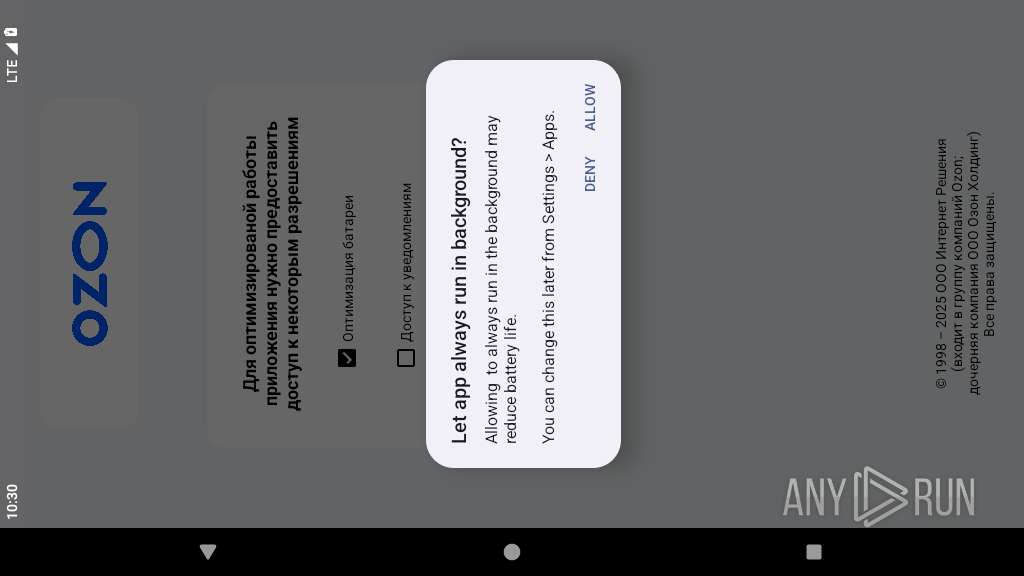
Abuses foreground service for persistence
- app_process64 (PID: 2396)
Retrieves current clipboard content
- app_process64 (PID: 2396)
Establishing a connection
- app_process64 (PID: 2396)
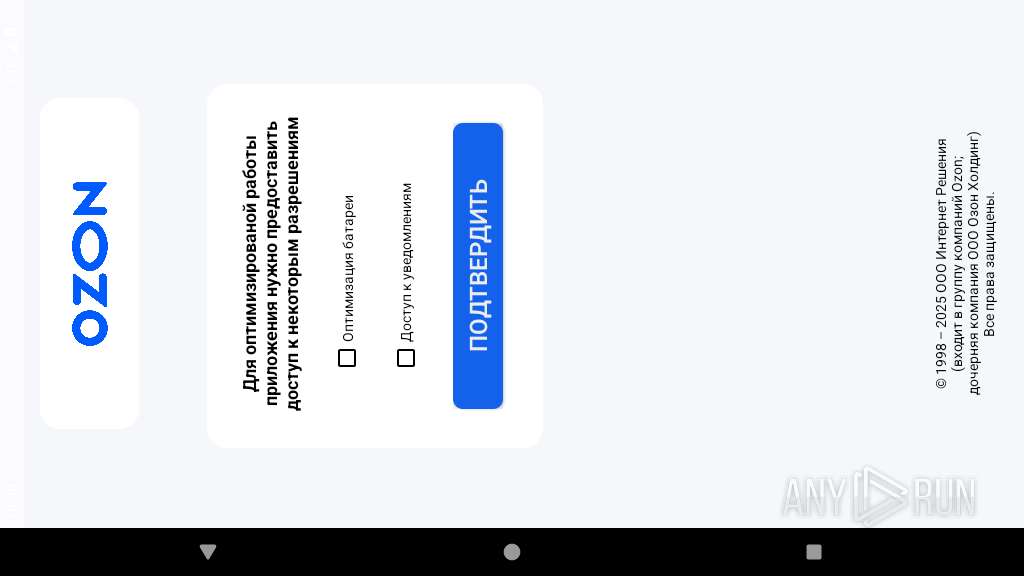
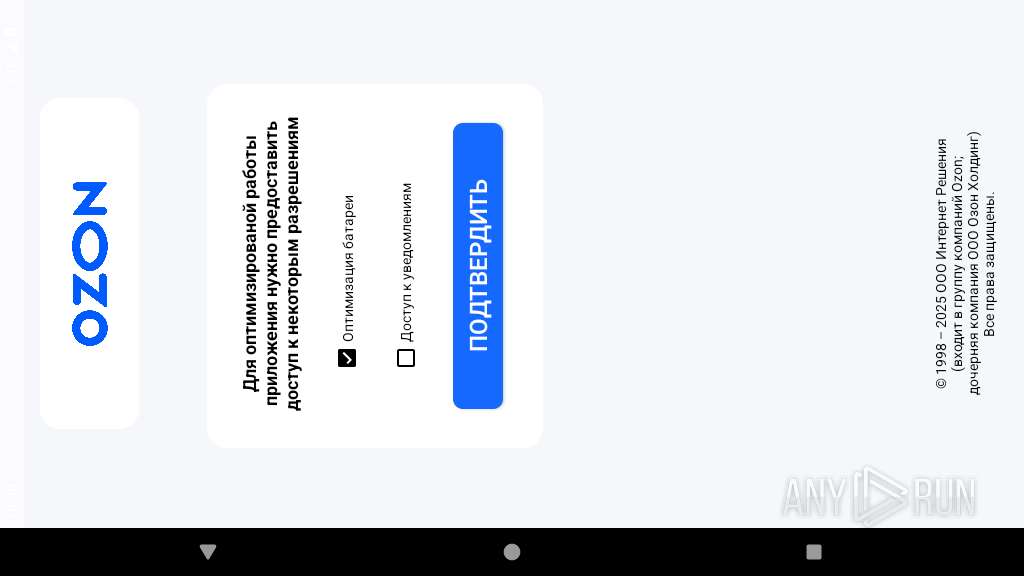
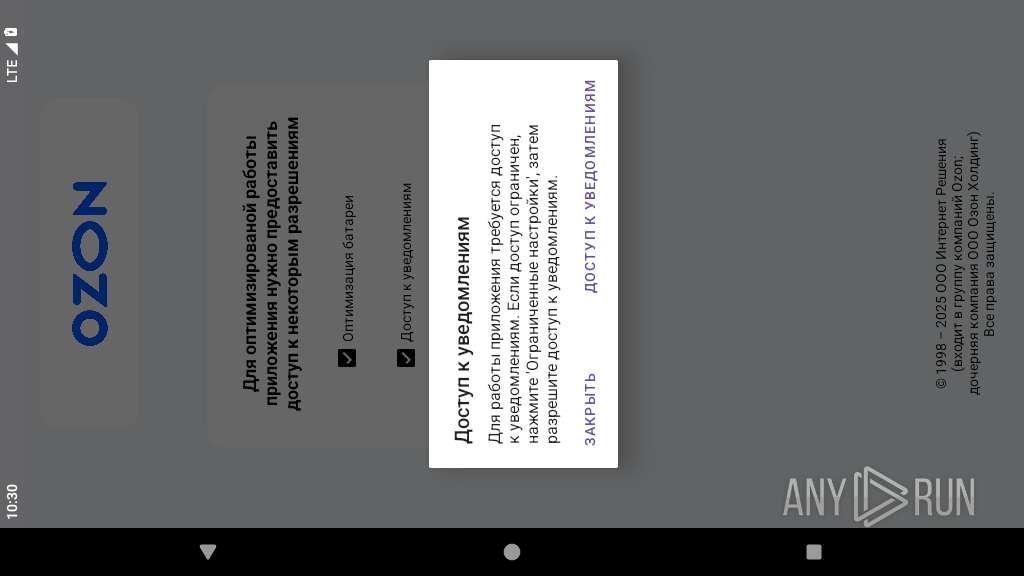
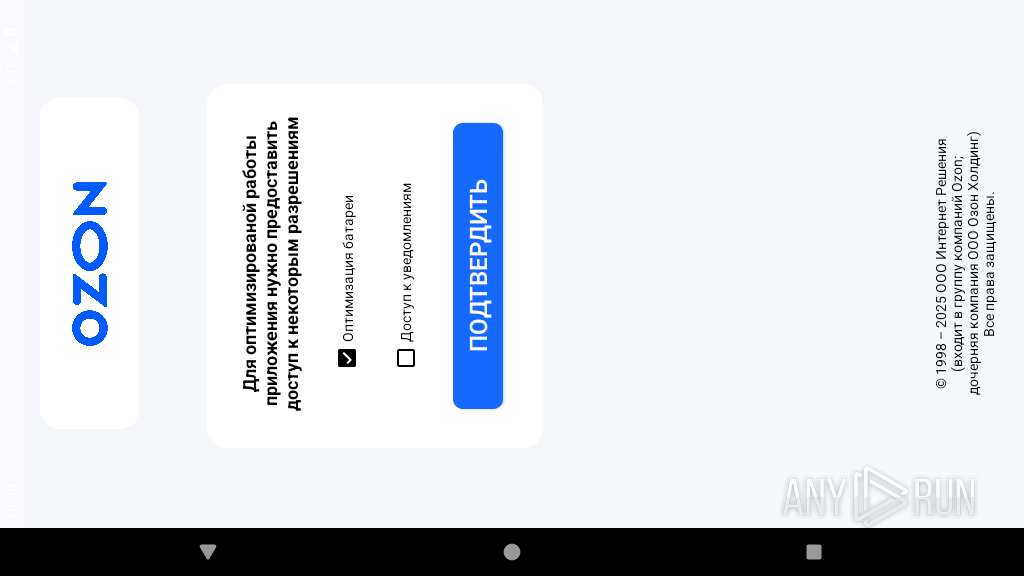
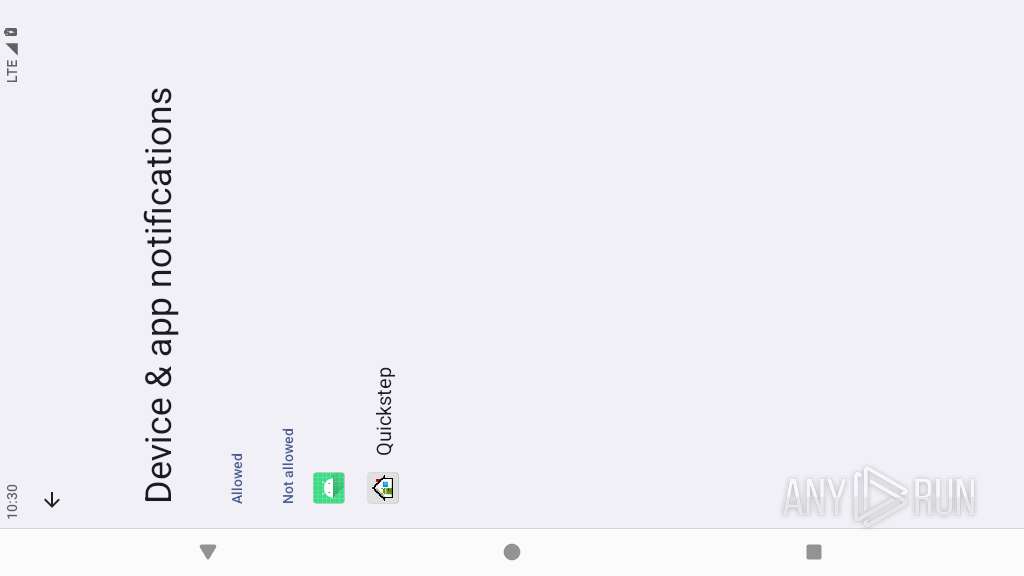
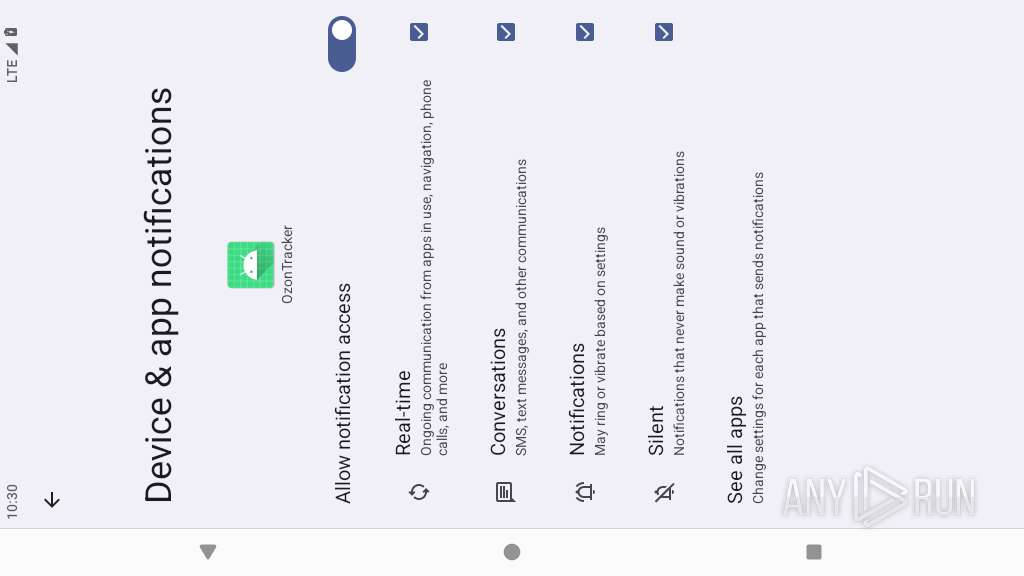
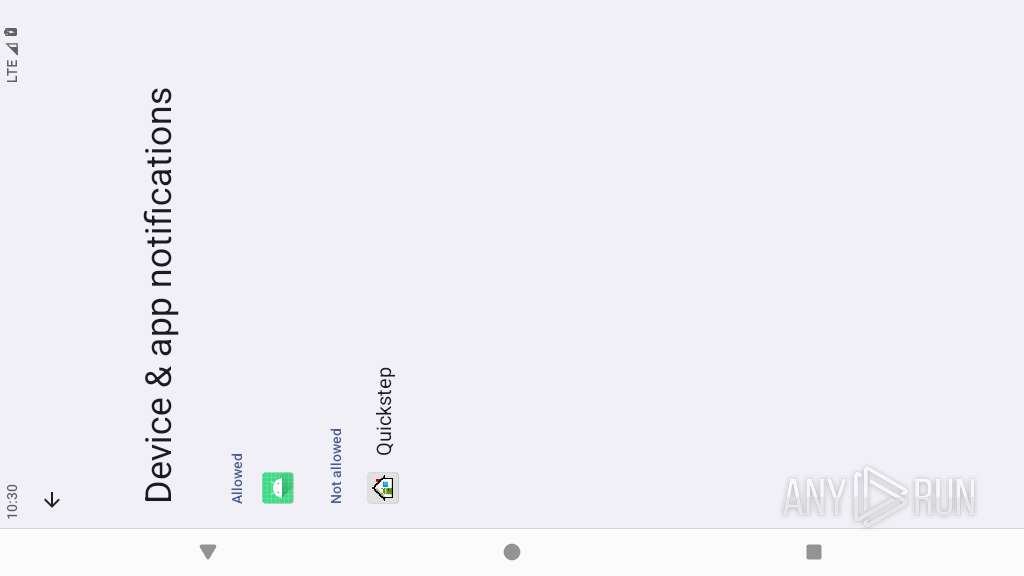
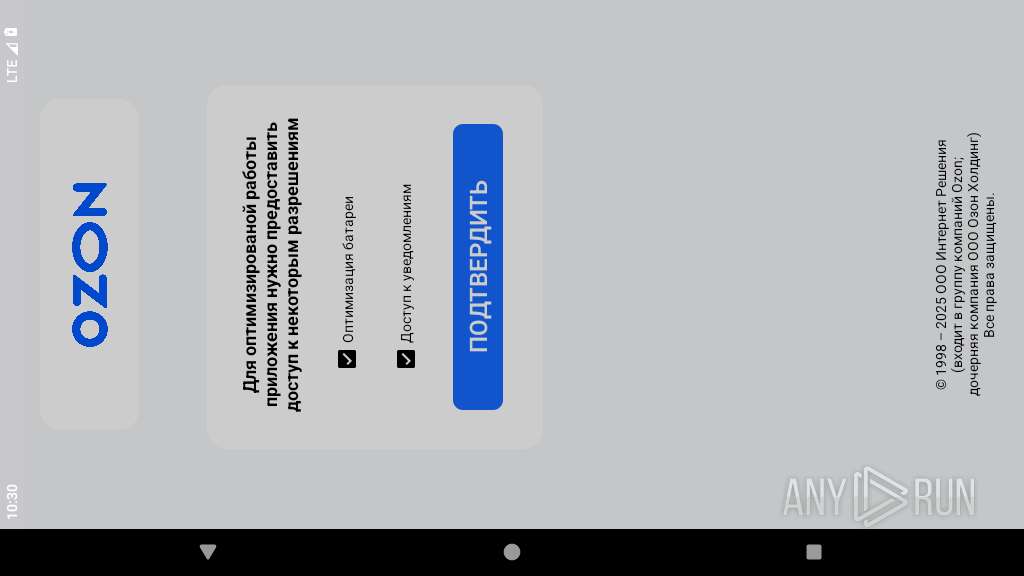
Requests access to notification listener
- app_process64 (PID: 2396)
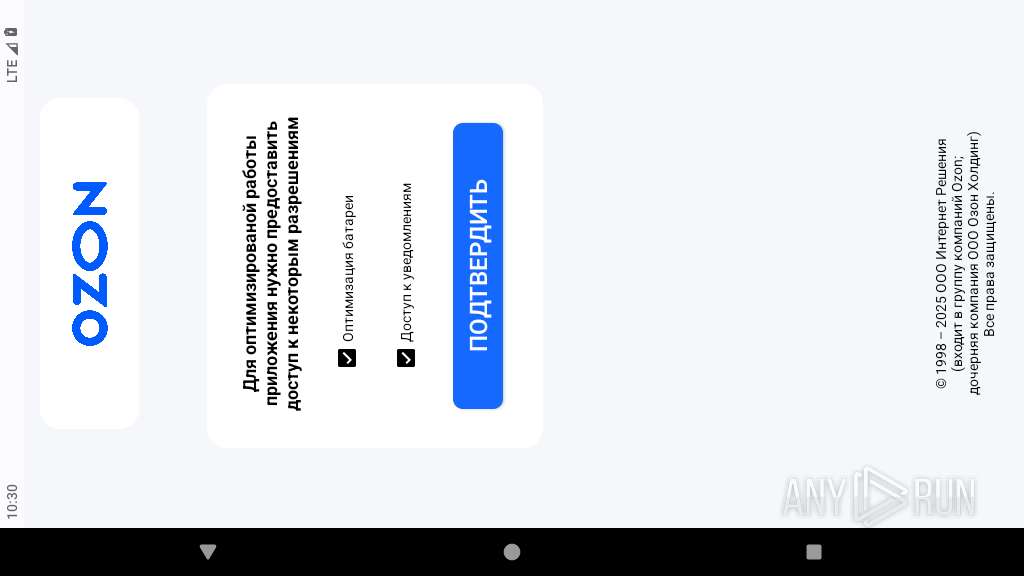
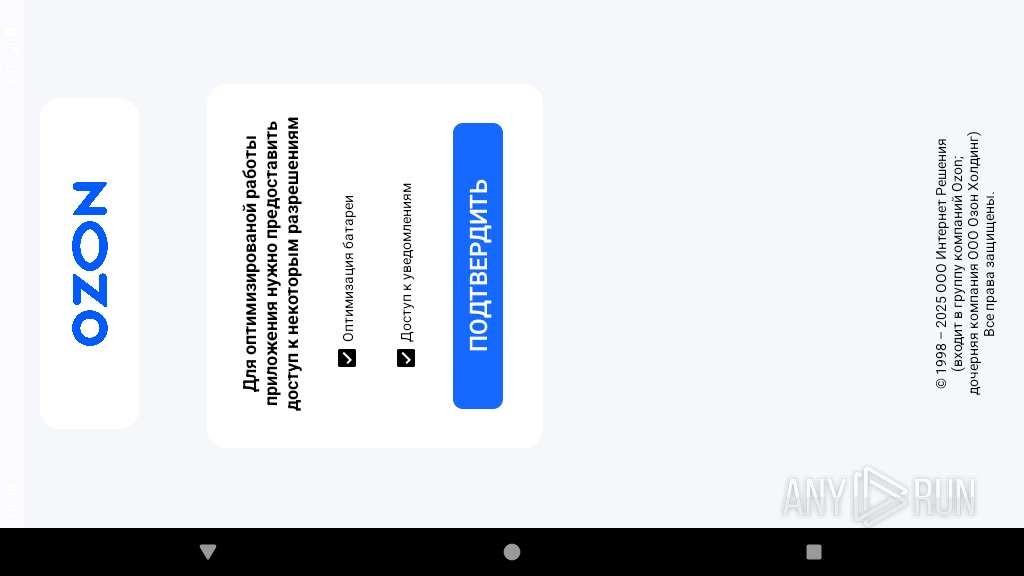
Checks exemption from battery optimization
- app_process64 (PID: 2396)
Creates a WakeLock to manage power state
- app_process64 (PID: 2396)
Acquires a wake lock to keep the device awake
- app_process64 (PID: 2396)
Retrieves installed applications on device
- app_process64 (PID: 2396)
Retrieves a list of running services
- app_process64 (PID: 2396)
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 2396)
Reads messages from SMS inbox
- app_process64 (PID: 2396)
Returns the name of the current network operator
- app_process64 (PID: 2396)
INFO
Verifies whether the device is connected to the internet
- app_process64 (PID: 2396)
Retrieves the value of a secure system setting
- app_process64 (PID: 2396)
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 2396)
Verifies presence of SIM card
- app_process64 (PID: 2396)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .apk | | | Android Package (62.8) |
|---|---|---|
| .jar | | | Java Archive (17.3) |
| .vym | | | VYM Mind Map (14.9) |
| .zip | | | ZIP compressed archive (4.7) |
EXIF
ZIP
| ZipRequiredVersion: | - |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1981:01:01 01:01:02 |
| ZipCRC: | 0x2b084705 |
| ZipCompressedSize: | 52 |
| ZipUncompressedSize: | 56 |
| ZipFileName: | META-INF/com/android/build/gradle/app-metadata.properties |
Total processes
125
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2253 | com.harry.loader | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2339 | com.android.settings | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 9 | ||||
| 2396 | <pre-initialized> | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
1
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2396 | app_process64 | /data/data/com.delviskesyty.OzonTrack/files/profileInstalled | binary | |
MD5:— | SHA256:— | |||
| 2396 | app_process64 | /data/data/com.delviskesyty.OzonTrack/shared_prefs/MyPrefs.xml | xml | |
MD5:— | SHA256:— | |||
| 2396 | app_process64 | /data/data/com.delviskesyty.OzonTrack/cache/image_manager_disk_cache/journal.tmp | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
28
DNS requests
6
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 216.58.206.67:80 | http://connectivitycheck.gstatic.com/generate_204 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
449 | mdnsd | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 216.239.35.4:123 | time.android.com | — | — | whitelisted |
— | — | 216.58.206.67:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
— | — | 142.250.186.164:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.251.31.81:443 | staging-remoteprovisioning.sandbox.googleapis.com | GOOGLE | US | whitelisted |
2396 | app_process64 | 188.114.96.3:443 | shvuor.com | CLOUDFLARENET | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivitycheck.gstatic.com |
| whitelisted |
www.google.com |
| whitelisted |
google.com |
| whitelisted |
time.android.com |
| whitelisted |
staging-remoteprovisioning.sandbox.googleapis.com |
| whitelisted |
shvuor.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Android Device Connectivity Check |