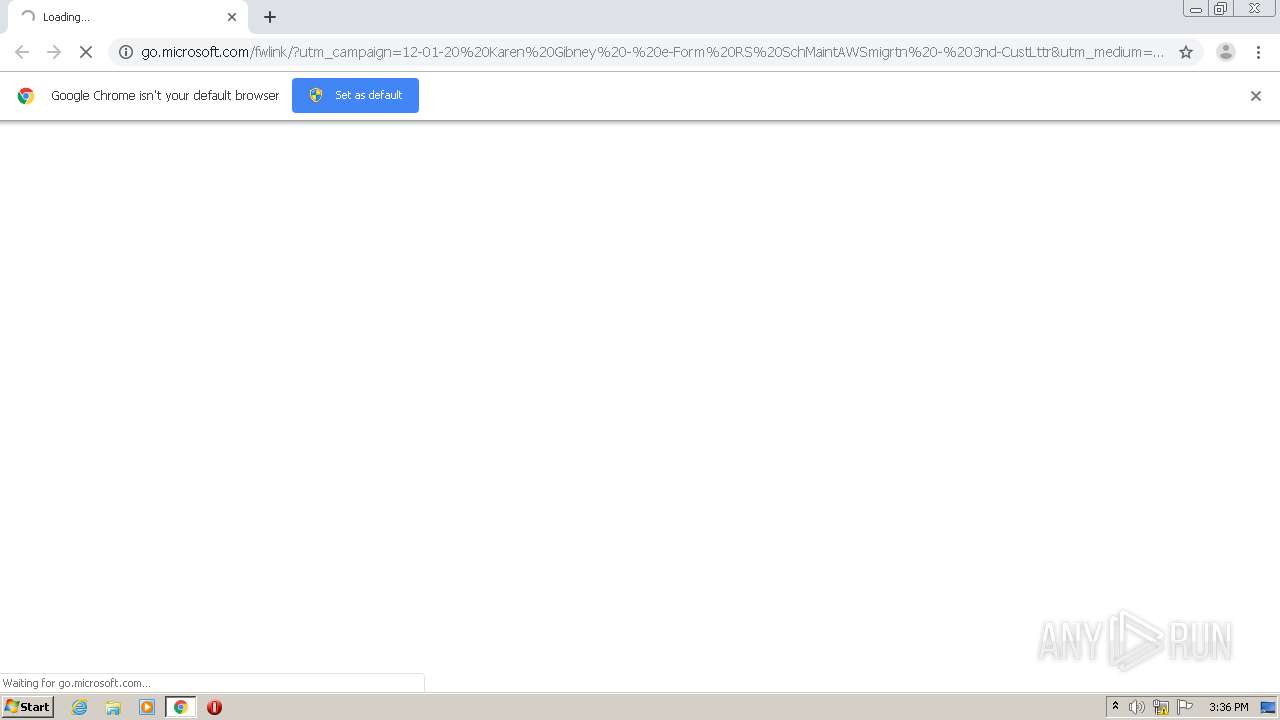
| URL: | http://go.microsoft.com/fwlink/?utm_campaign=12-01-20%20Karen%20Gibney%20-%20e-Form%20RS%20SchMaintAWSmigrtn%20-%203nd-CustLttr&utm_medium=email&utm_source=Eloqua&site_id=82769734&cid=N%2FA&chl=em&sfdccampaignid=&elq_mid=24476&elq_cid=5015172&elq_ename=12-01-20%20Karen%20Gibney%20-%20e-Form%20RS%20SchMaintAWSmigrtn%20-%203nd-CustLttr&LinkId=863262&elqTrackId=45a46887a08c4894be8277ce00e900bb&elq=8d26be52d6434cce835f7a96a349813d&elqaid=24476&elqat=1&elqCampaignId=17323 |
| Full analysis: | https://app.any.run/tasks/e47150d5-eb02-4925-8722-be5935ea8827 |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2020, 15:36:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E5DFC2BCCE3601663C3CA4CB41DA9C16 |
| SHA1: | 928082EEA1682F5CA9679AB93B831979E06F18C1 |
| SHA256: | BDC763CD1FD5339A87CD9D21F3F304EC13A2CB1630596775604BE34A4ED5E0AA |
| SSDEEP: | 12:LDPO/Nml/G9KHvMlyiQmJPBwcEGXbfAuGz/G9KHvMlyxLdhDMS6wHclSrYLWXB:LTJXs51vr+zLdh408leYO |
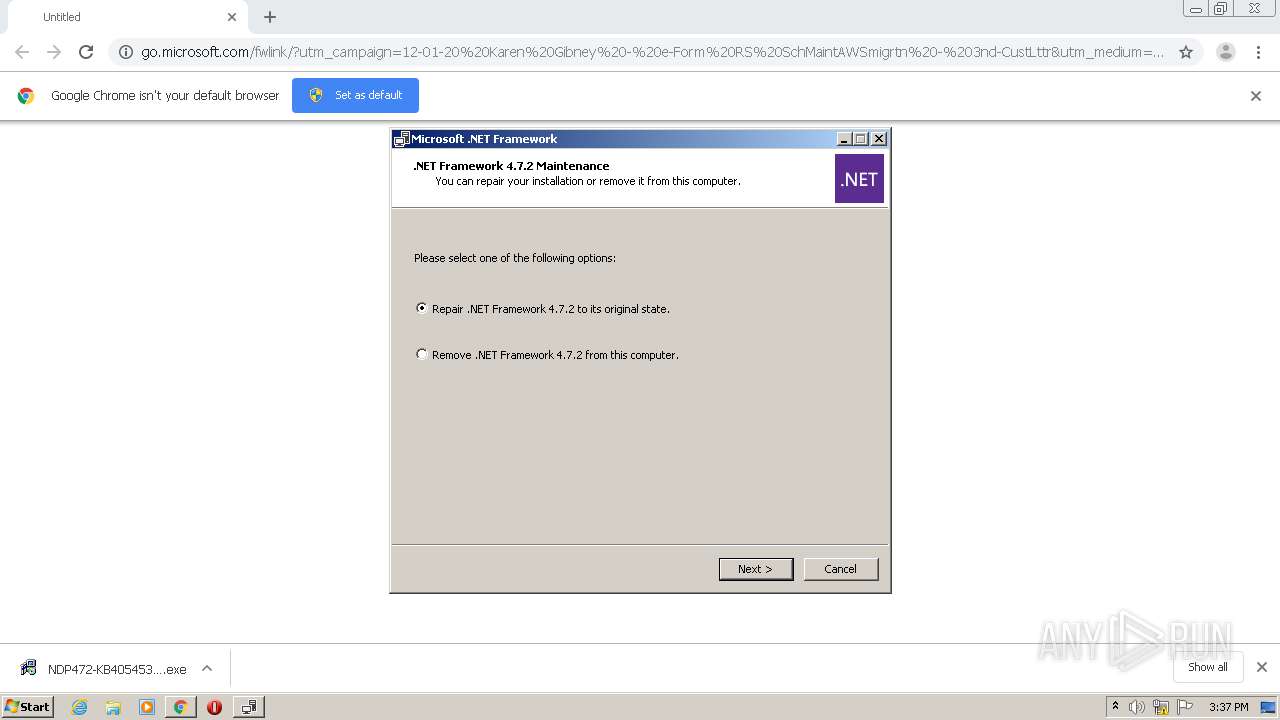
MALICIOUS
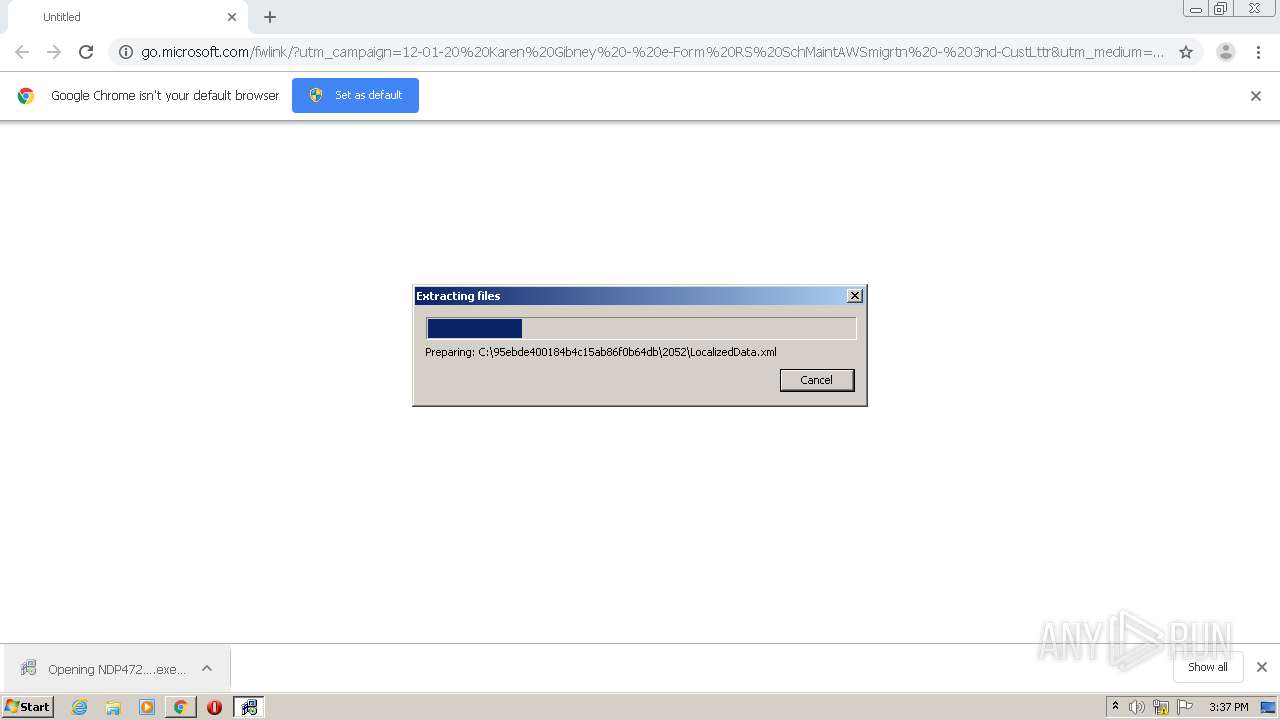
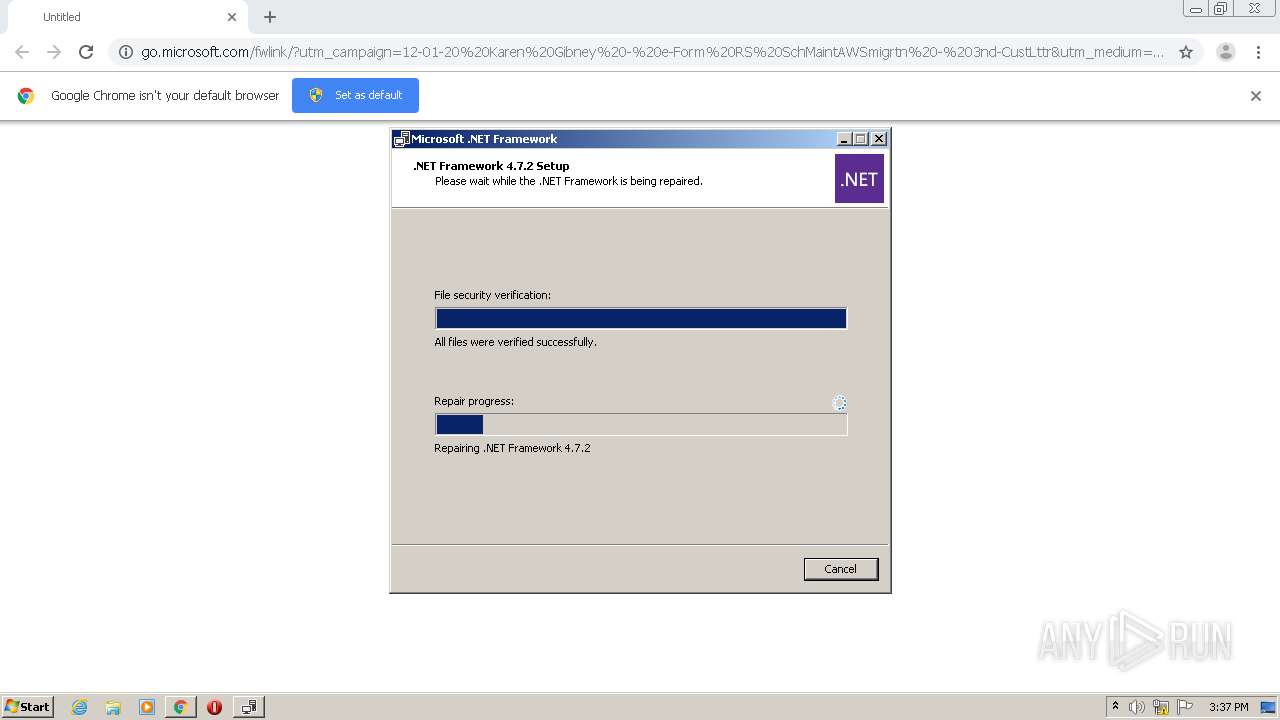
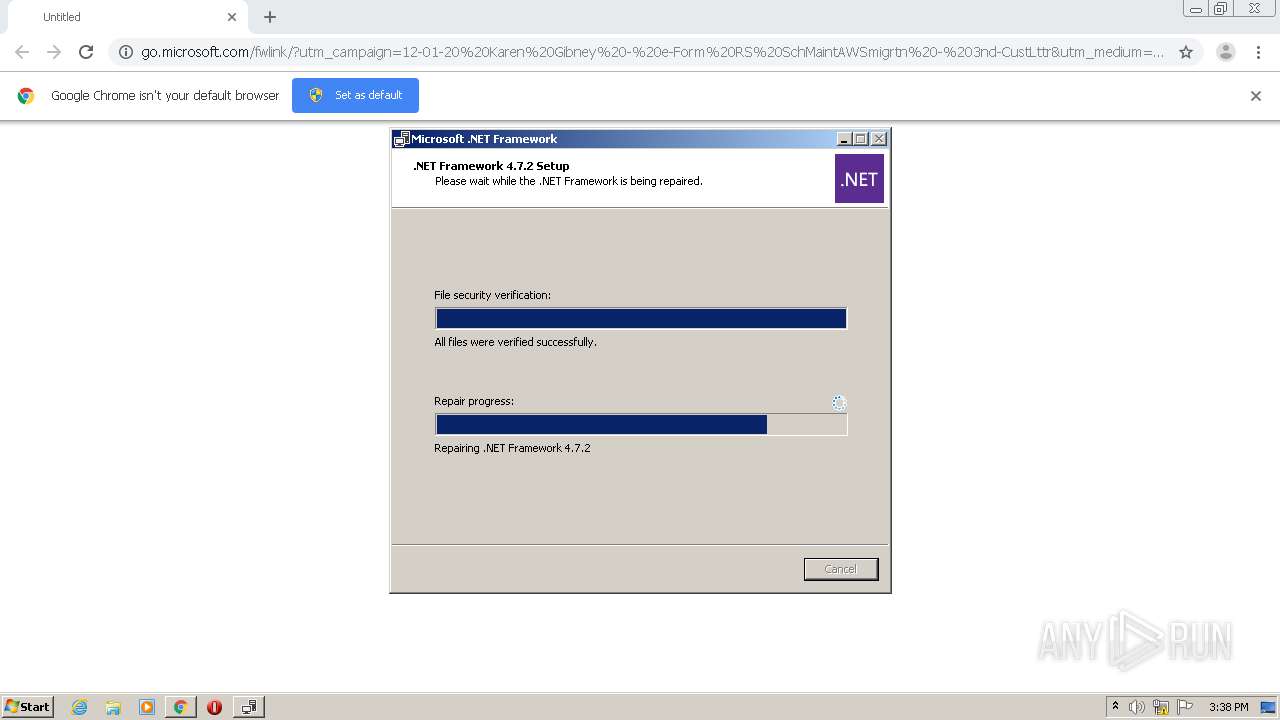
Application was dropped or rewritten from another process
- NDP472-KB4054531-Web.exe (PID: 920)
- NDP472-KB4054531-Web.exe (PID: 2132)
- Setup.exe (PID: 1632)
- SetupUtility.exe (PID: 2120)
- aspnet_regiis.exe (PID: 1256)
- ngen.exe (PID: 2284)
- regtlibv12.exe (PID: 2524)
- regtlibv12.exe (PID: 2236)
- regtlibv12.exe (PID: 3764)
- regtlibv12.exe (PID: 3716)
- regtlibv12.exe (PID: 2648)
- regtlibv12.exe (PID: 1964)
- regtlibv12.exe (PID: 2588)
- ngen.exe (PID: 1732)
- ServiceModelReg.exe (PID: 3052)
- mscorsvw.exe (PID: 1324)
- mscorsvw.exe (PID: 1152)
- mscorsvw.exe (PID: 3788)
- mscorsvw.exe (PID: 2952)
- mscorsvw.exe (PID: 3152)
- mscorsvw.exe (PID: 2040)
- mscorsvw.exe (PID: 2032)
- mscorsvw.exe (PID: 3224)
- mscorsvw.exe (PID: 2752)
- mscorsvw.exe (PID: 3684)
- mscorsvw.exe (PID: 3352)
- mscorsvw.exe (PID: 2980)
- mscorsvw.exe (PID: 3092)
- mscorsvw.exe (PID: 2700)
- mscorsvw.exe (PID: 3352)
- mscorsvw.exe (PID: 3936)
- mscorsvw.exe (PID: 2464)
- mscorsvw.exe (PID: 2588)
- mscorsvw.exe (PID: 340)
- mscorsvw.exe (PID: 3564)
- mscorsvw.exe (PID: 3208)
- mscorsvw.exe (PID: 2084)
- mscorsvw.exe (PID: 1196)
- mscorsvw.exe (PID: 3732)
Loads dropped or rewritten executable
- Setup.exe (PID: 1632)
- svchost.exe (PID: 760)
- wmiprvse.exe (PID: 3076)
- ngen.exe (PID: 2284)
- aspnet_regiis.exe (PID: 1256)
- mscorsvw.exe (PID: 1324)
- ngen.exe (PID: 1732)
- mscorsvw.exe (PID: 1152)
- mscorsvw.exe (PID: 3788)
- mscorsvw.exe (PID: 3152)
- mscorsvw.exe (PID: 2040)
- mscorsvw.exe (PID: 3224)
- mscorsvw.exe (PID: 2952)
- mscorsvw.exe (PID: 2032)
- mscorsvw.exe (PID: 2752)
- mscorsvw.exe (PID: 3352)
- mscorsvw.exe (PID: 2980)
- mscorsvw.exe (PID: 3684)
- mscorsvw.exe (PID: 3092)
- mscorsvw.exe (PID: 3352)
- mscorsvw.exe (PID: 2464)
- mscorsvw.exe (PID: 2588)
- mscorsvw.exe (PID: 340)
- mscorsvw.exe (PID: 3564)
- mscorsvw.exe (PID: 3208)
- mscorsvw.exe (PID: 2084)
- mscorsvw.exe (PID: 2700)
- mscorsvw.exe (PID: 3936)
- mscorsvw.exe (PID: 1196)
- mscorsvw.exe (PID: 3732)
Actions looks like stealing of personal data
- NDP472-KB4054531-Web.exe (PID: 2132)
Changes settings of System certificates
- Setup.exe (PID: 1632)
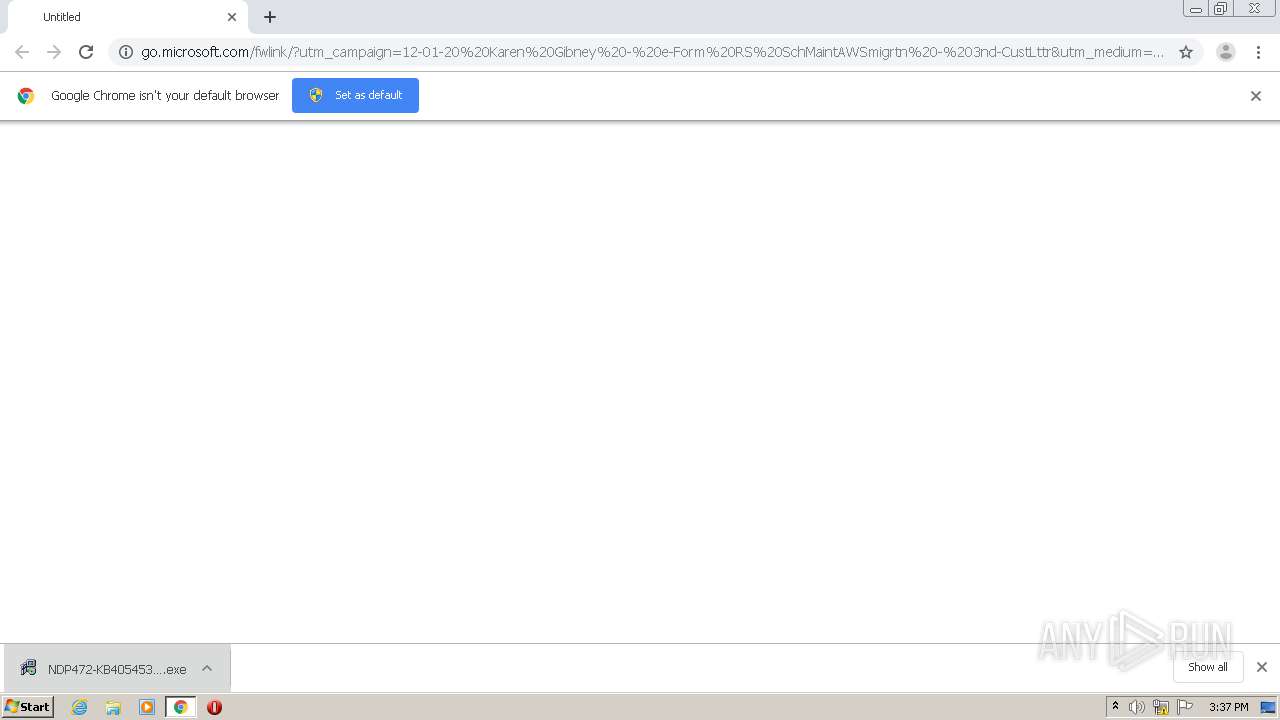
Drops executable file immediately after starts
- msiexec.exe (PID: 2428)
Loads the Task Scheduler COM API
- ngen.exe (PID: 2284)
- ngen.exe (PID: 1732)
Application was injected by another process
- smss.exe (PID: 264)
- spoolsv.exe (PID: 1188)
- svchost.exe (PID: 828)
- svchost.exe (PID: 1216)
- lsm.exe (PID: 496)
- wininit.exe (PID: 380)
- csrss.exe (PID: 388)
- lsass.exe (PID: 488)
- winlogon.exe (PID: 428)
- ctfmon.exe (PID: 1656)
- explorer.exe (PID: 1724)
- dwm.exe (PID: 1608)
- svchost.exe (PID: 800)
- IMEDICTUPDATE.EXE (PID: 1368)
- svchost.exe (PID: 856)
- services.exe (PID: 472)
- svchost.exe (PID: 592)
- csrss.exe (PID: 344)
- svchost.exe (PID: 672)
- svchost.exe (PID: 1044)
- svchost.exe (PID: 2252)
- conhost.exe (PID: 3216)
- svchost.exe (PID: 280)
- SearchIndexer.exe (PID: 1688)
- srvpost.exe (PID: 1452)
- taskeng.exe (PID: 1532)
- host.exe (PID: 1496)
Runs injected code in another process
- wmiprvse.exe (PID: 3076)
SUSPICIOUS
Drops a file that was compiled in debug mode
- chrome.exe (PID: 1228)
- NDP472-KB4054531-Web.exe (PID: 2132)
- msiexec.exe (PID: 2428)
Executable content was dropped or overwritten
- chrome.exe (PID: 1228)
- NDP472-KB4054531-Web.exe (PID: 2132)
- msiexec.exe (PID: 2428)
Creates COM task schedule object
- msiexec.exe (PID: 2428)
- aspnet_regiis.exe (PID: 1256)
Drops a file with too old compile date
- msiexec.exe (PID: 2428)
Changes the autorun value in the registry
- msiexec.exe (PID: 2428)
Removes files from Windows directory
- lodctr.exe (PID: 2844)
- aspnet_regiis.exe (PID: 1256)
- msiexec.exe (PID: 2428)
- lodctr.exe (PID: 3296)
- lodctr.exe (PID: 3776)
- lodctr.exe (PID: 688)
- lodctr.exe (PID: 2852)
Creates files in the Windows directory
- lodctr.exe (PID: 2844)
- aspnet_regiis.exe (PID: 1256)
- lodctr.exe (PID: 3776)
- lodctr.exe (PID: 3296)
- lodctr.exe (PID: 688)
- lodctr.exe (PID: 2852)
- ngen.exe (PID: 2284)
- msiexec.exe (PID: 2428)
- ngen.exe (PID: 1732)
- mscorsvw.exe (PID: 1324)
Searches for installed software
- svchost.exe (PID: 800)
Creates or modifies windows services
- services.exe (PID: 472)
INFO
Reads the hosts file
- chrome.exe (PID: 2348)
- chrome.exe (PID: 1228)
Application launched itself
- chrome.exe (PID: 1228)
- msiexec.exe (PID: 2428)
Reads settings of System Certificates
- Setup.exe (PID: 1632)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2744)
- msiexec.exe (PID: 2428)
- MsiExec.exe (PID: 1132)
Creates files in the program directory
- msiexec.exe (PID: 2428)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 2428)
- mscorsvw.exe (PID: 1324)
Creates a software uninstall entry
- msiexec.exe (PID: 2428)
Creates or modifies windows services
- msiexec.exe (PID: 2428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
126
Monitored processes
94
Malicious processes
41
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 264 | \SystemRoot\System32\smss.exe | C:\Windows\System32\smss.exe | System | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Session Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 280 | C:\Windows\system32\svchost.exe -k NetworkServiceNetworkRestricted | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 316 | "C:\Windows\system32\wbem\mofcomp.exe" "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MOF\ServiceModel.mof" | C:\Windows\system32\wbem\mofcomp.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: The Managed Object Format (MOF) Compiler Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 340 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 1e0 -InterruptEvent 0 -NGENProcess 1cc -Pipe 1d4 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | — | ngen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 344 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,12288,512 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=winsrv:ConServerDllInitialization,2 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\System32\csrss.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 380 | wininit.exe | C:\Windows\System32\wininit.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Start-Up Application Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 388 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,12288,512 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=winsrv:ConServerDllInitialization,2 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\System32\csrss.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 428 | winlogon.exe | C:\Windows\System32\winlogon.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Logon Application Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) | |||||||||||||||
| 472 | C:\Windows\system32\services.exe | C:\Windows\System32\services.exe | wininit.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Services and Controller app Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 488 | C:\Windows\system32\lsass.exe | C:\Windows\System32\lsass.exe | wininit.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Local Security Authority Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
Total events
29 220
Read events
15 416
Write events
13 372
Delete events
432
Modification events
| (PID) Process: | (1228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2612) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1228-13251397013543250 |
Value: 259 | |||
| (PID) Process: | (1228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1228) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
Executable files
1 348
Suspicious files
48
Text files
919
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FC7B496-4CC.pma | — | |
MD5:— | SHA256:— | |||
| 1228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d5ca7b5c-eb84-445b-b12e-115665023cf2.tmp | — | |
MD5:— | SHA256:— | |||
| 1228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 828 | svchost.exe | C:\Windows\ServiceProfiles\LocalService\AppData\Local\~FontCache-S-1-5-21-1302019708-1500728564-335382590-1000.dat | — | |
MD5:— | SHA256:— | |||
| 856 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 1228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT~RF18d2ac.TMP | text | |
MD5:— | SHA256:— | |||
| 1228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF18d2cc.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
11
DNS requests
7
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2348 | chrome.exe | GET | 302 | 92.123.16.55:80 | http://go.microsoft.com/fwlink/?utm_campaign=12-01-20%20Karen%20Gibney%20-%20e-Form%20RS%20SchMaintAWSmigrtn%20-%203nd-CustLttr&utm_medium=email&utm_source=Eloqua&site_id=82769734&cid=N%2FA&chl=em&sfdccampaignid=&elq_mid=24476&elq_cid=5015172&elq_ename=12-01-20%20Karen%20Gibney%20-%20e-Form%20RS%20SchMaintAWSmigrtn%20-%203nd-CustLttr&LinkId=863262&elqTrackId=45a46887a08c4894be8277ce00e900bb&elq=8d26be52d6434cce835f7a96a349813d&elqaid=24476&elqat=1&elqCampaignId=17323 | FR | — | — | whitelisted |
1632 | Setup.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | der | 781 b | whitelisted |
1632 | Setup.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | der | 550 b | whitelisted |
1632 | Setup.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | unknown | der | 564 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2348 | chrome.exe | 92.123.16.55:80 | go.microsoft.com | Telia Company AB | FR | malicious |
— | — | 92.123.16.55:80 | go.microsoft.com | Telia Company AB | FR | malicious |
2348 | chrome.exe | 23.46.252.120:443 | download.microsoft.com | Akamai Technologies, Inc. | US | suspicious |
2348 | chrome.exe | 216.58.206.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1632 | Setup.exe | 2.16.186.74:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
2348 | chrome.exe | 172.217.21.206:443 | clients4.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.23.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
2348 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
accounts.google.com |
| shared |
download.microsoft.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
clients1.google.com |
| whitelisted |
clients4.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2348 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
Process | Message |
|---|---|
msiexec.exe | Failed to release Service
|
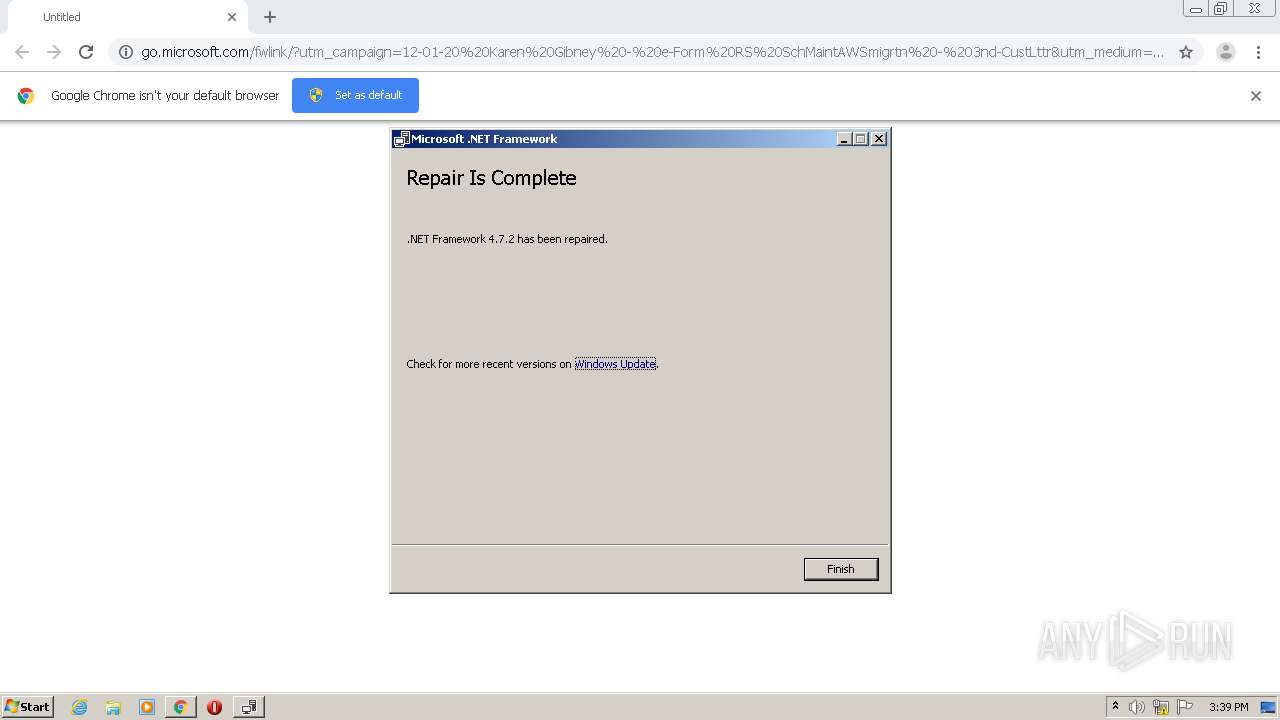
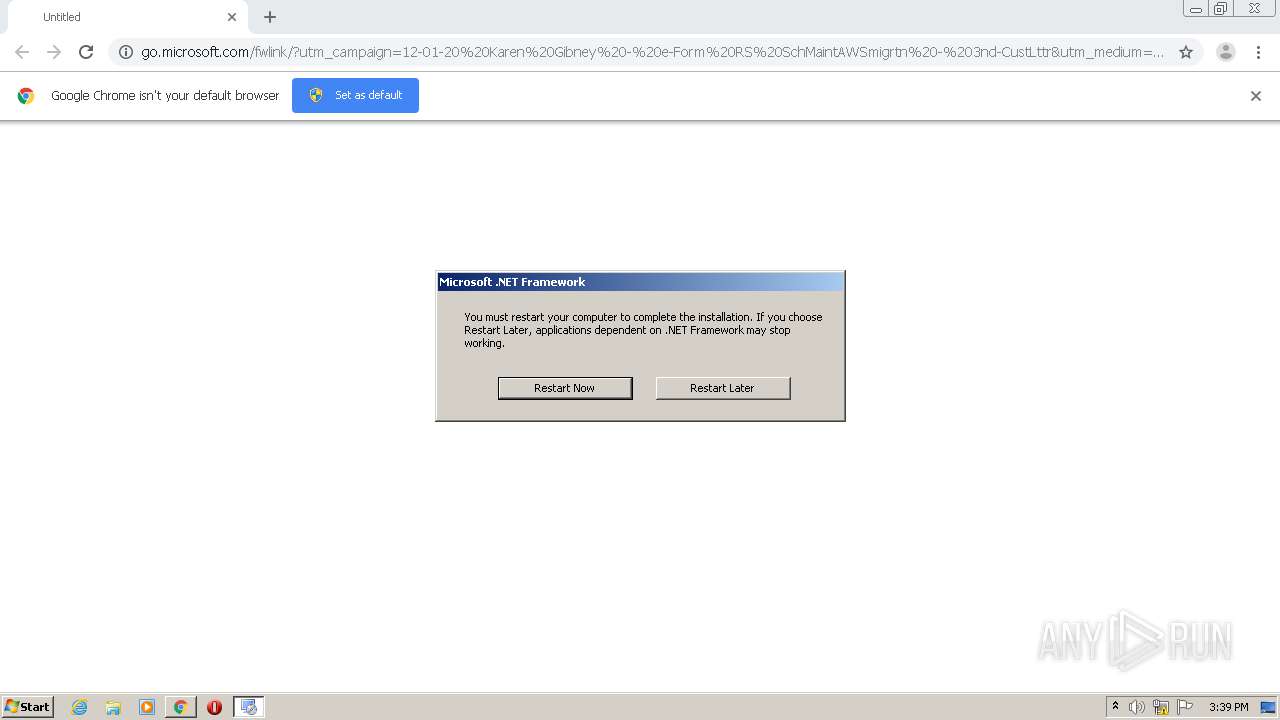
Setup.exe | The requested operation is successful. Changes will not be effective until the system is rebooted.
|
Setup.exe | The requested operation is successful. Changes will not be effective until the system is rebooted.
|