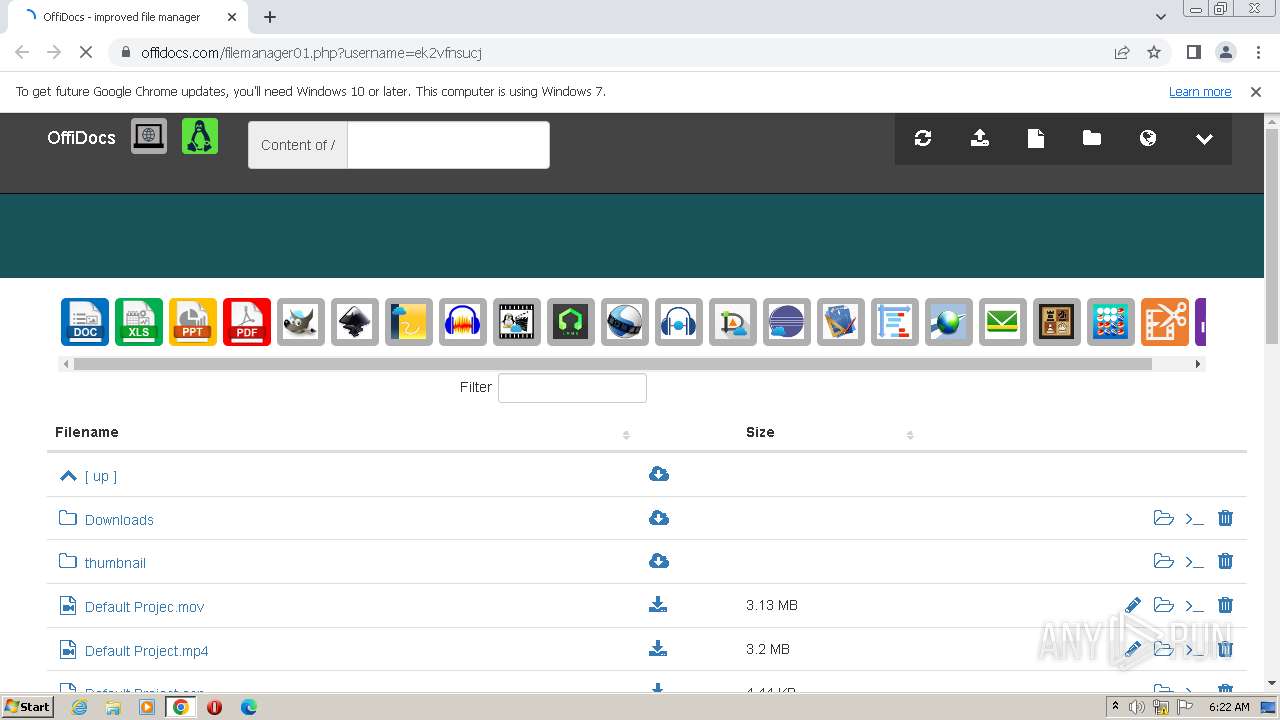
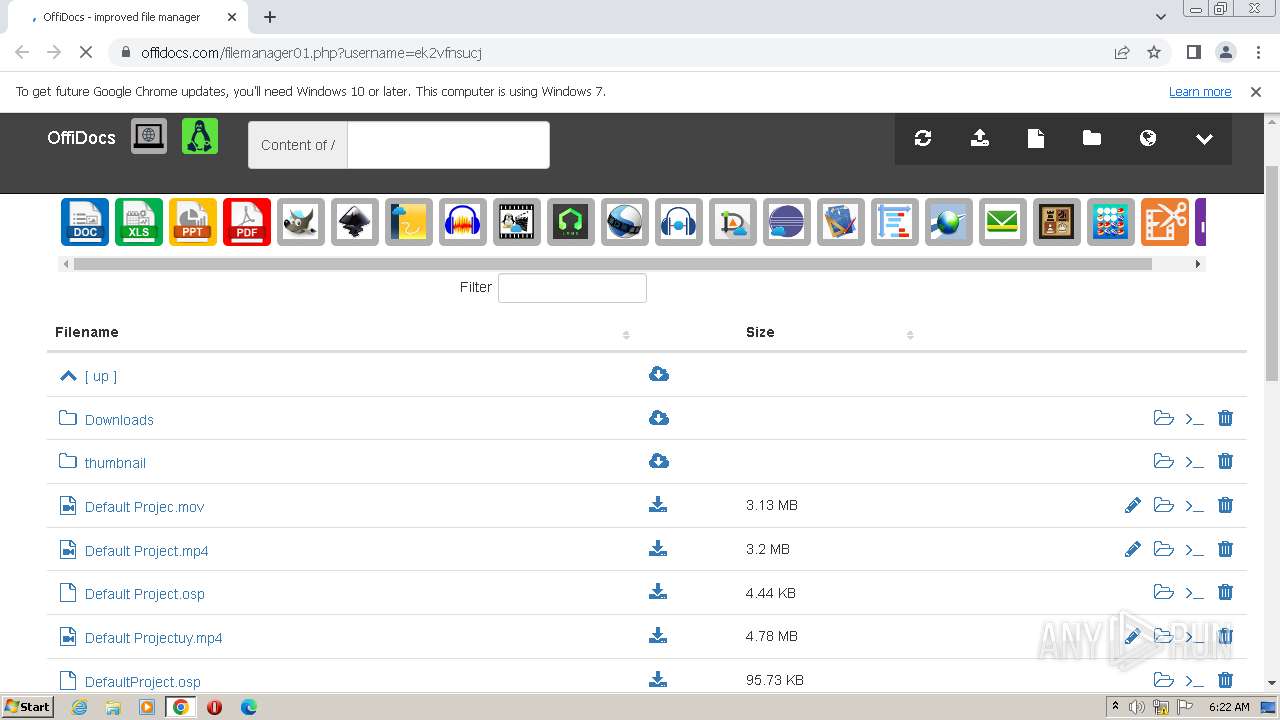
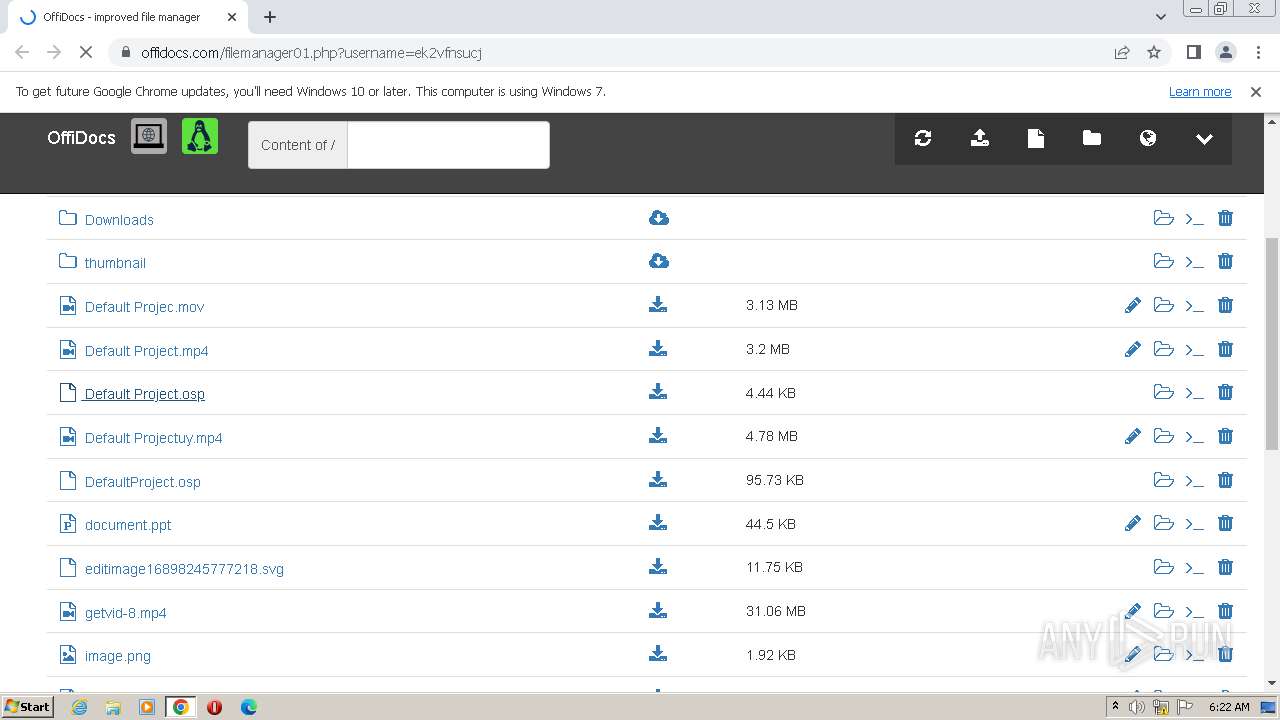
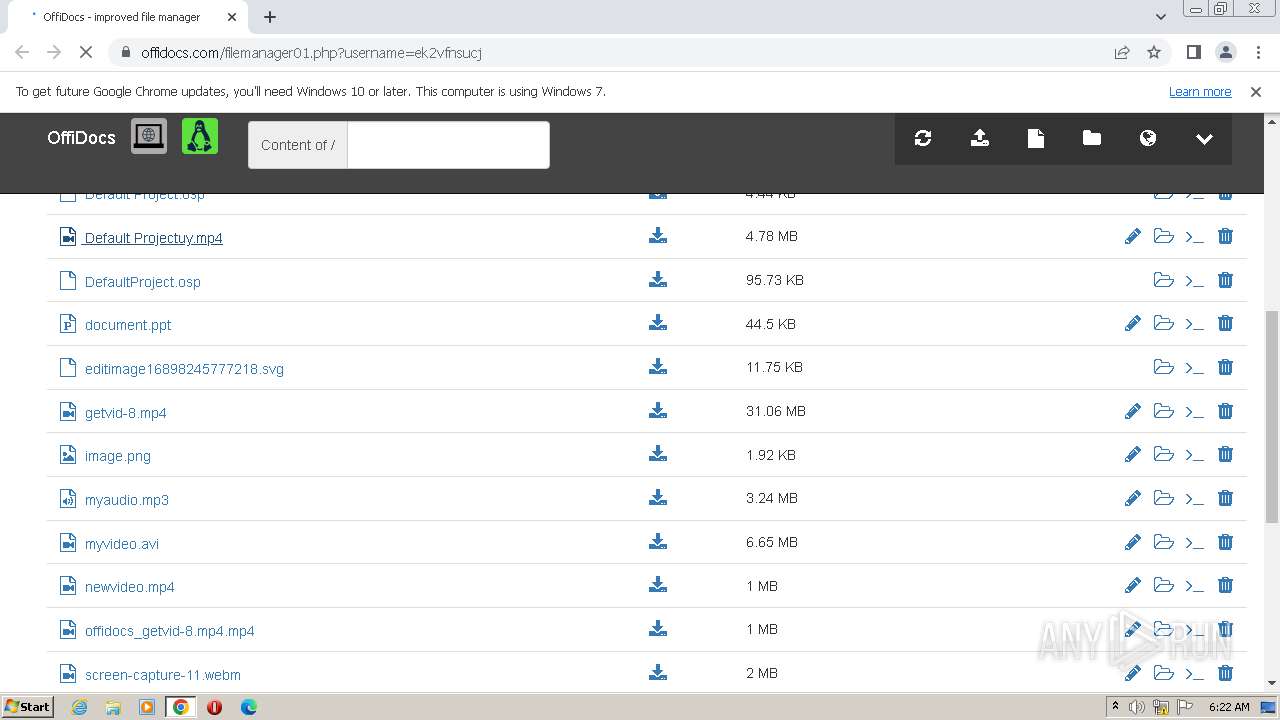
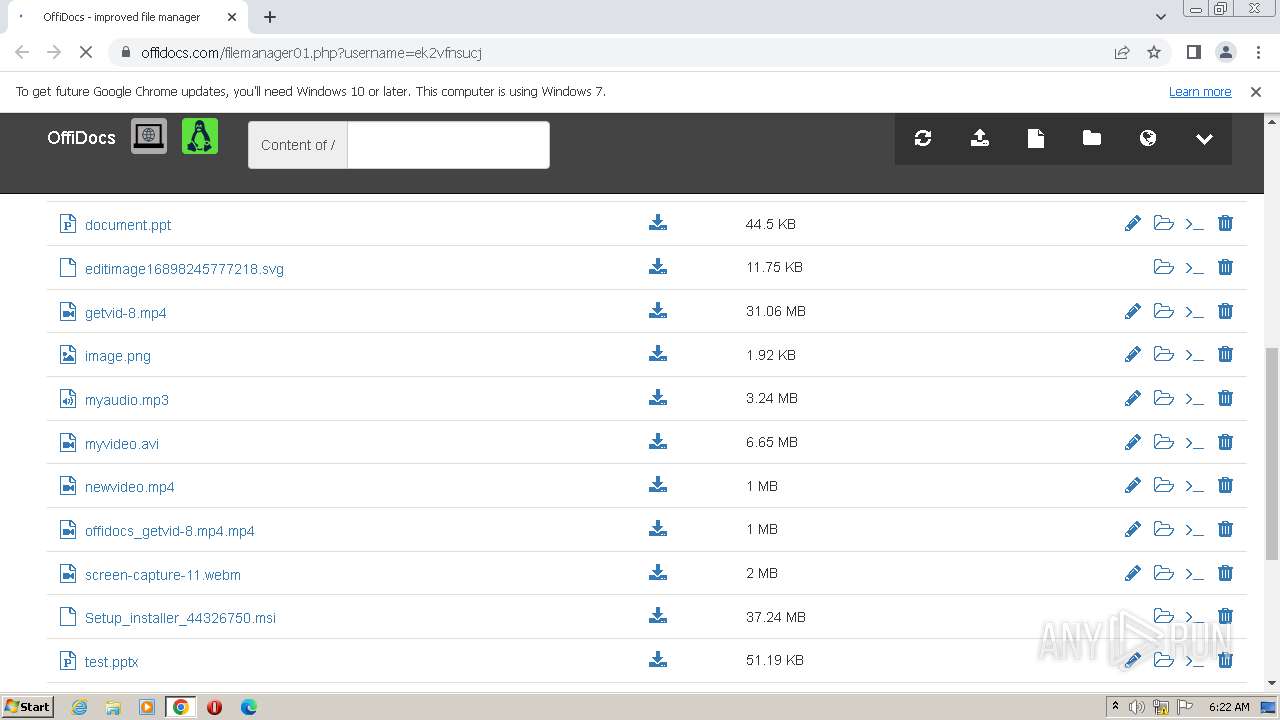
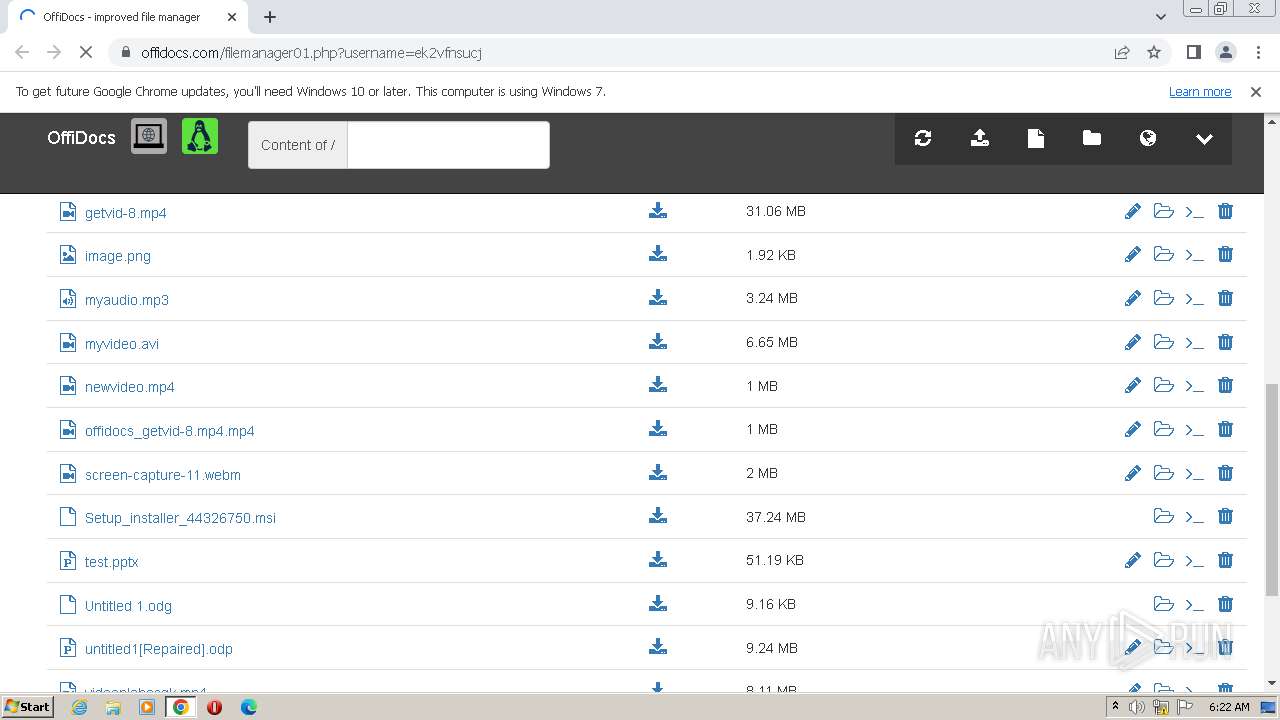
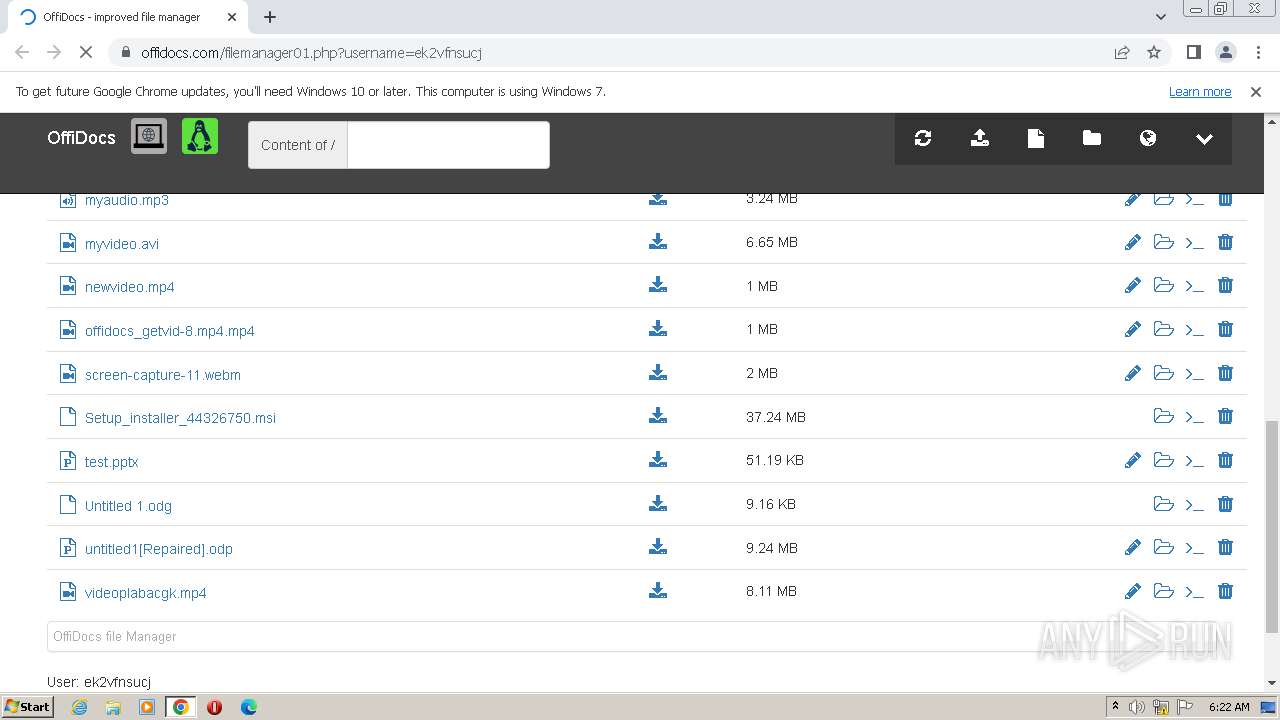
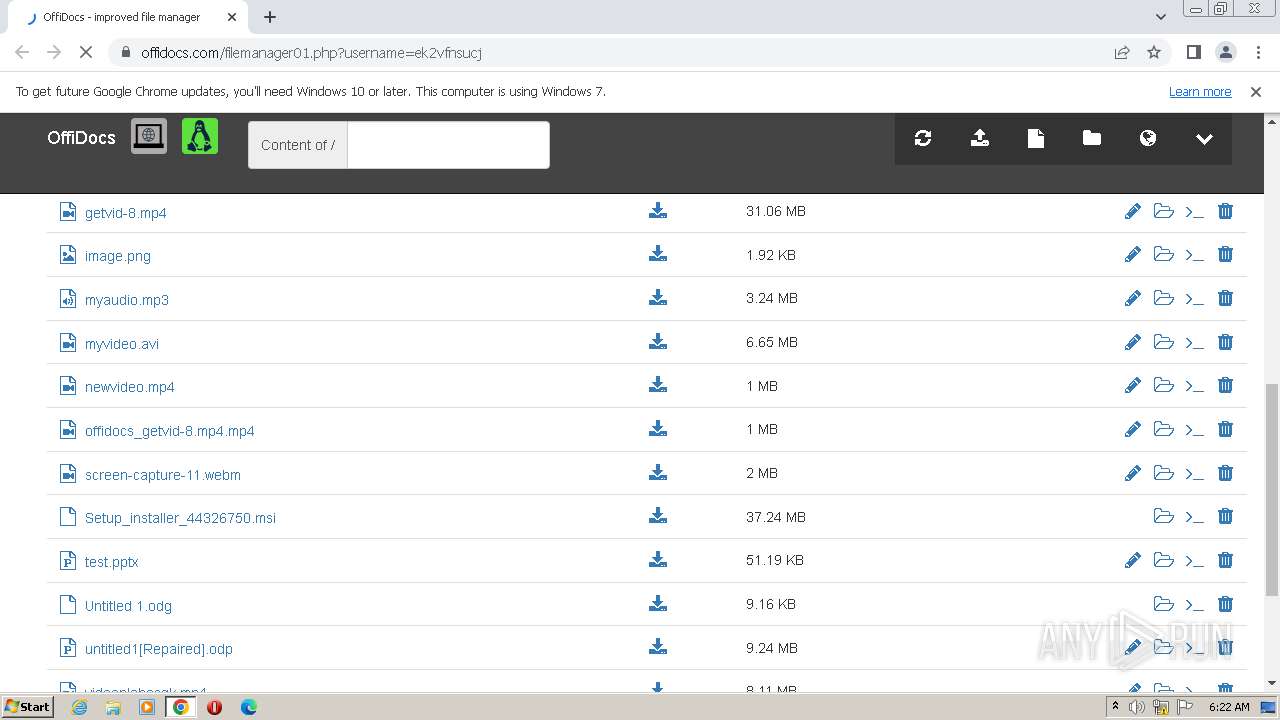
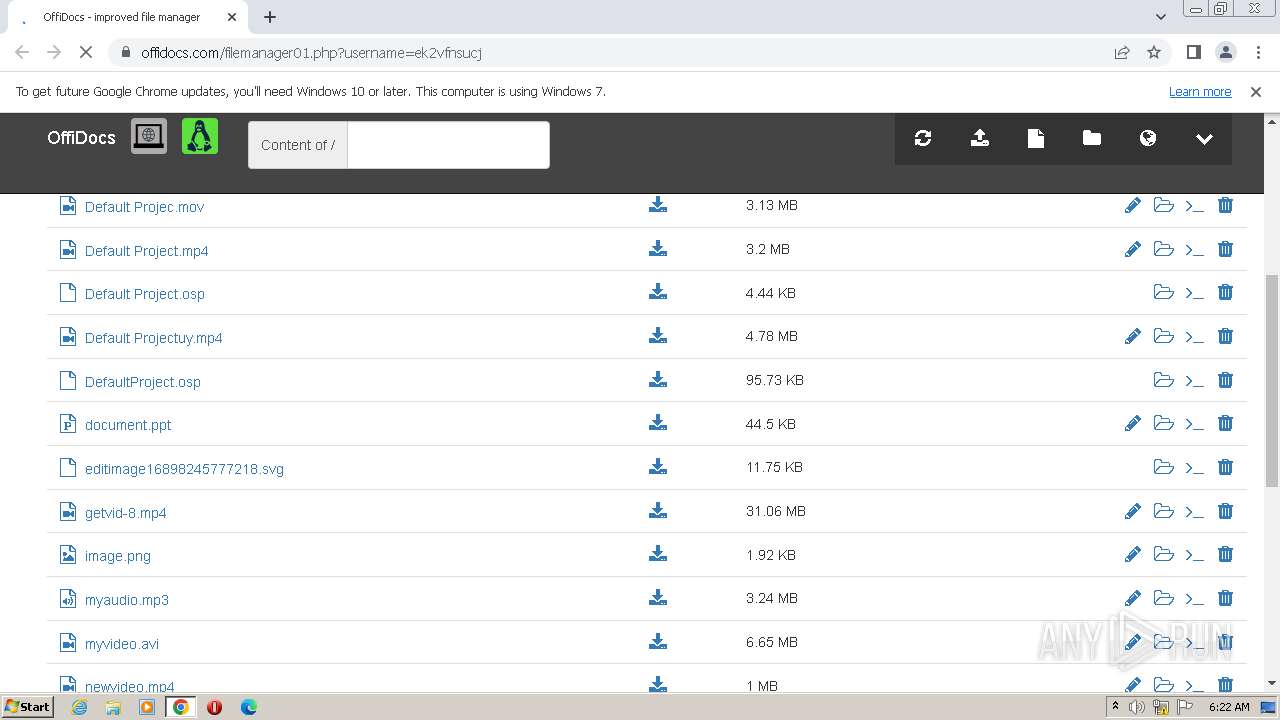
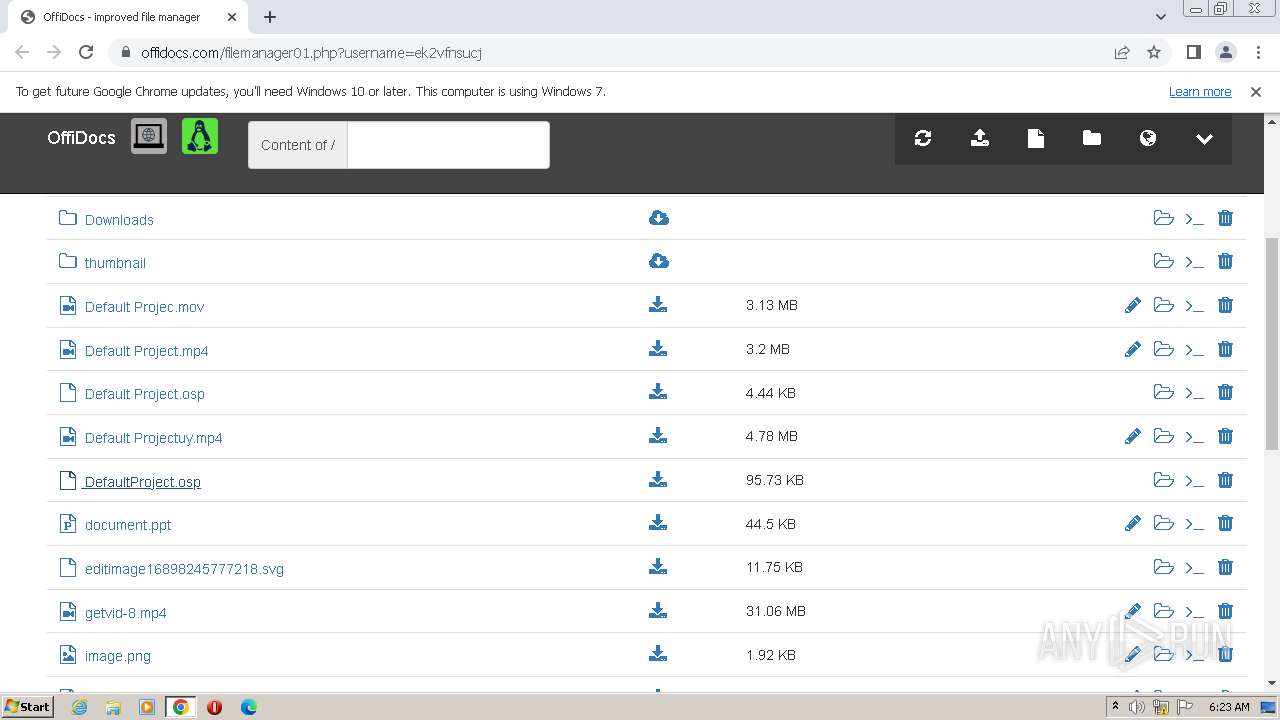
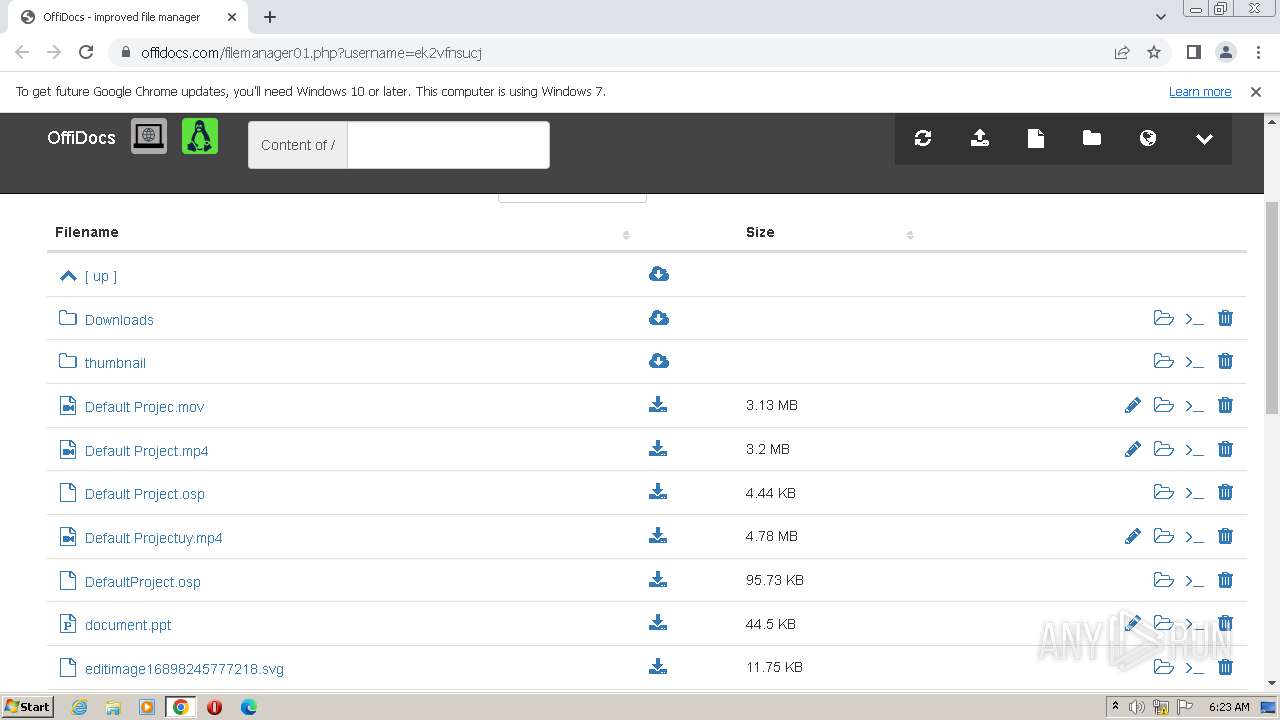
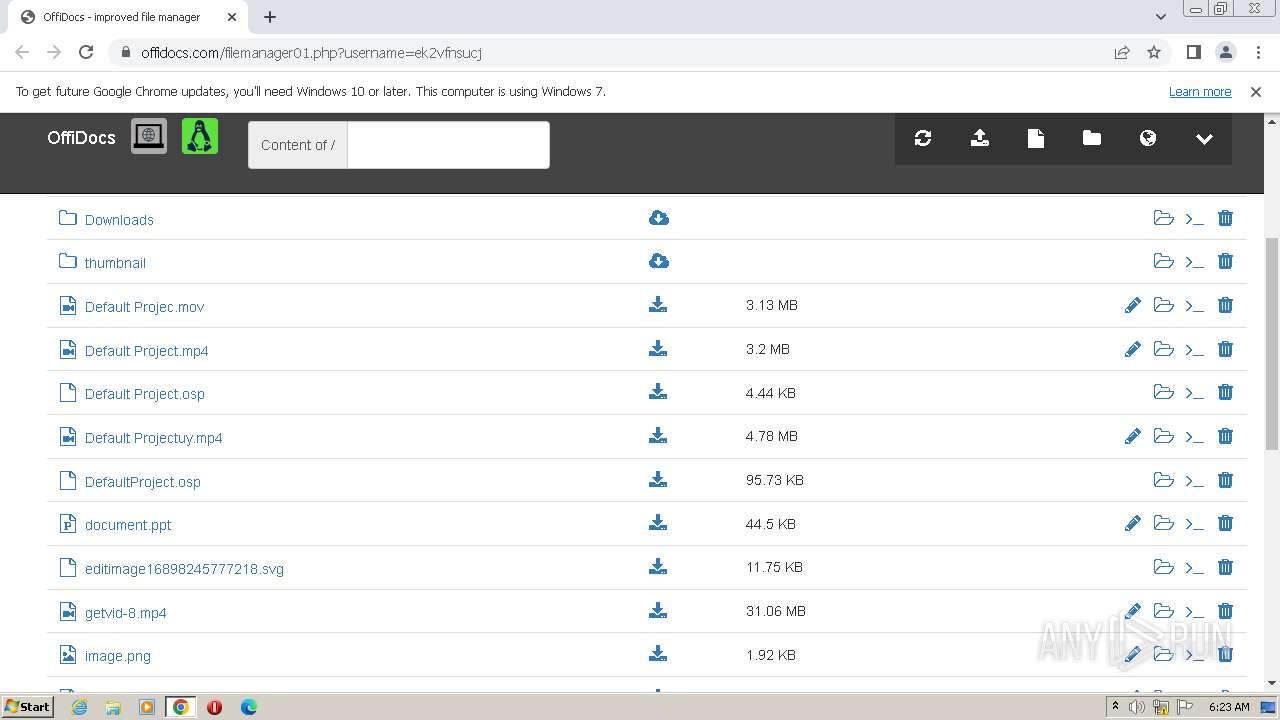
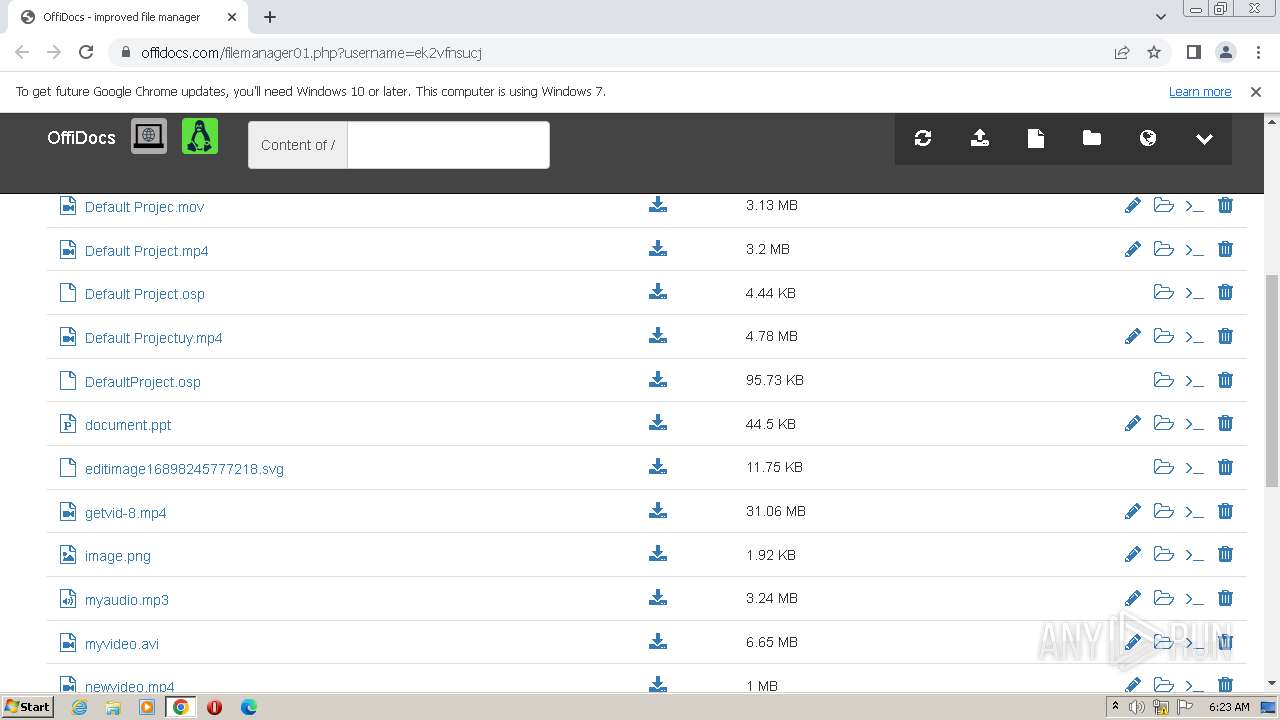
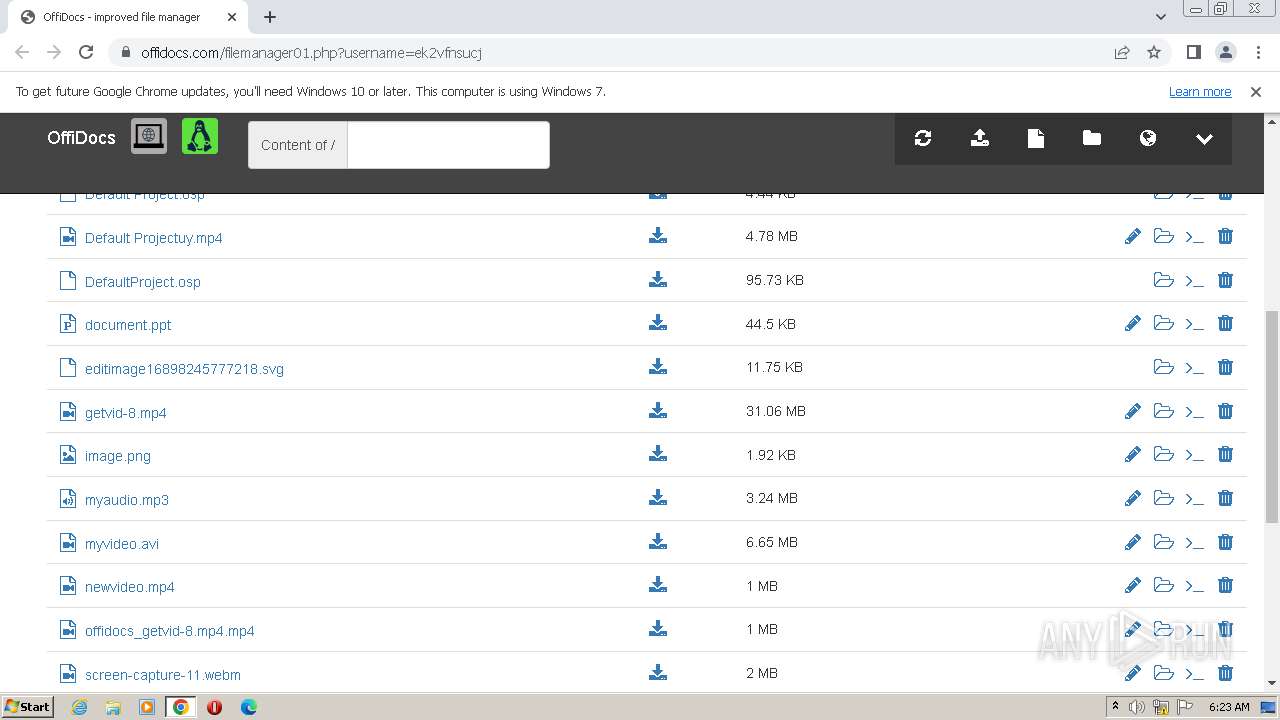
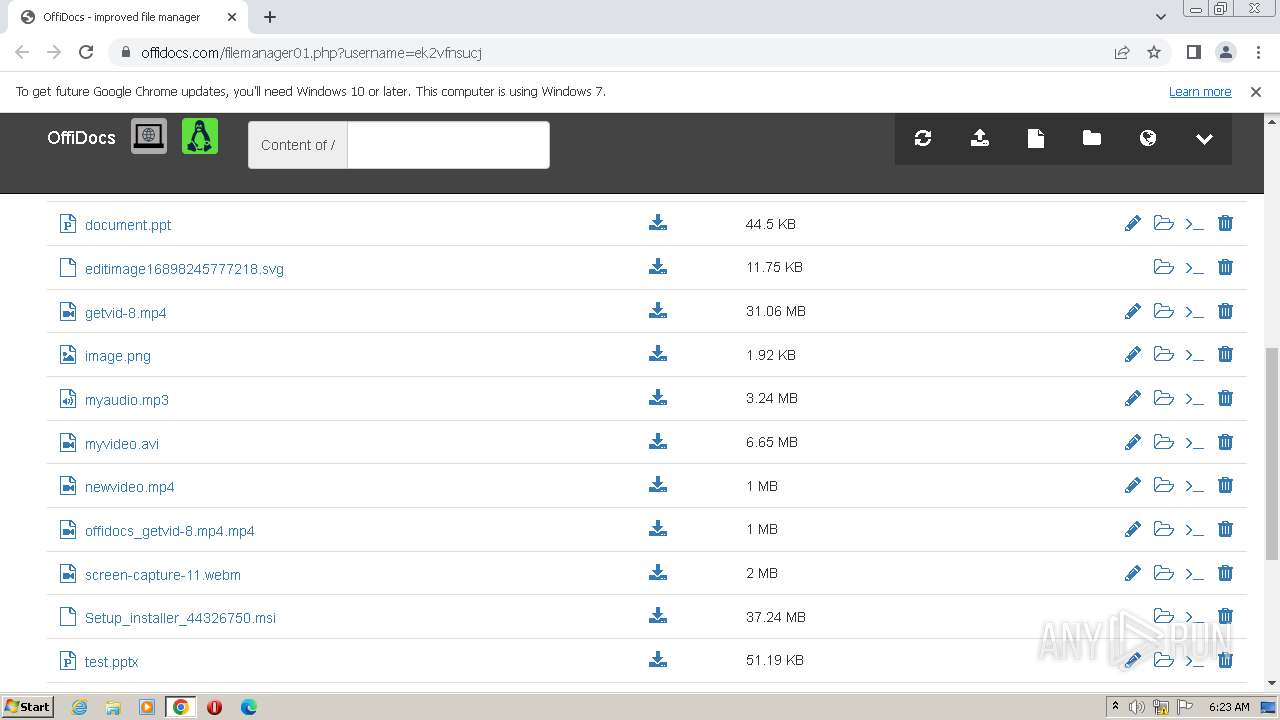
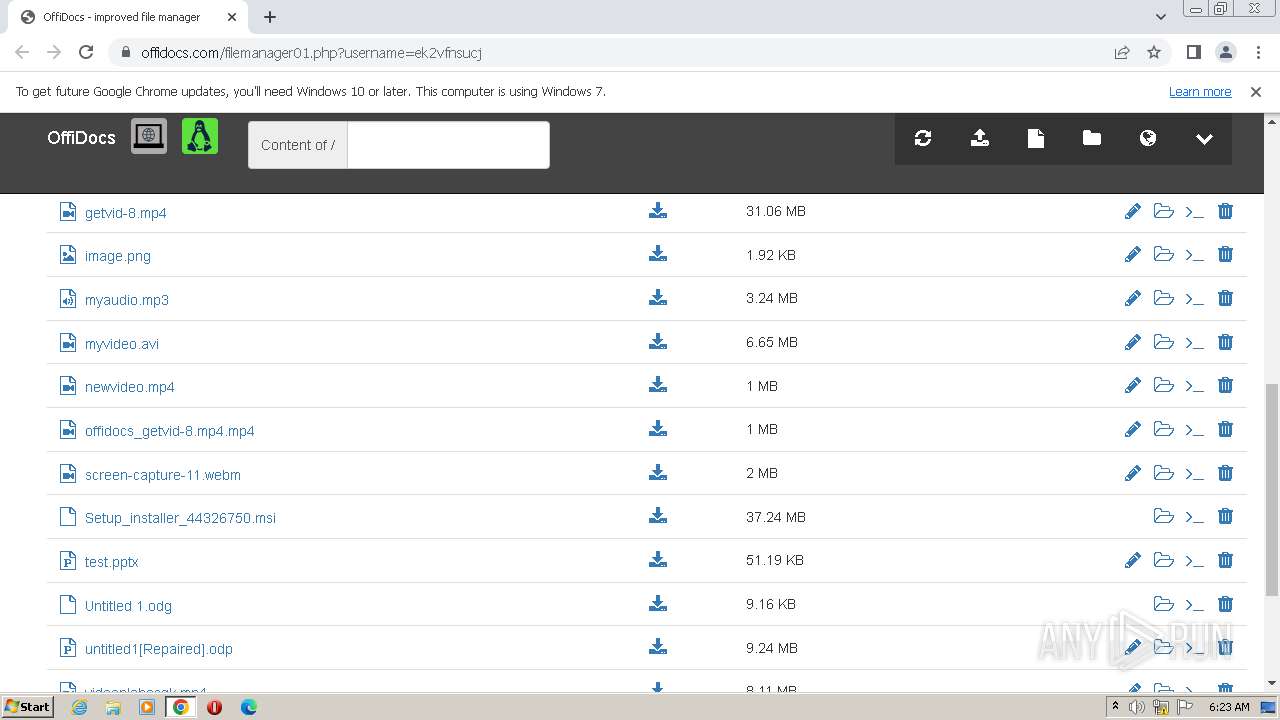
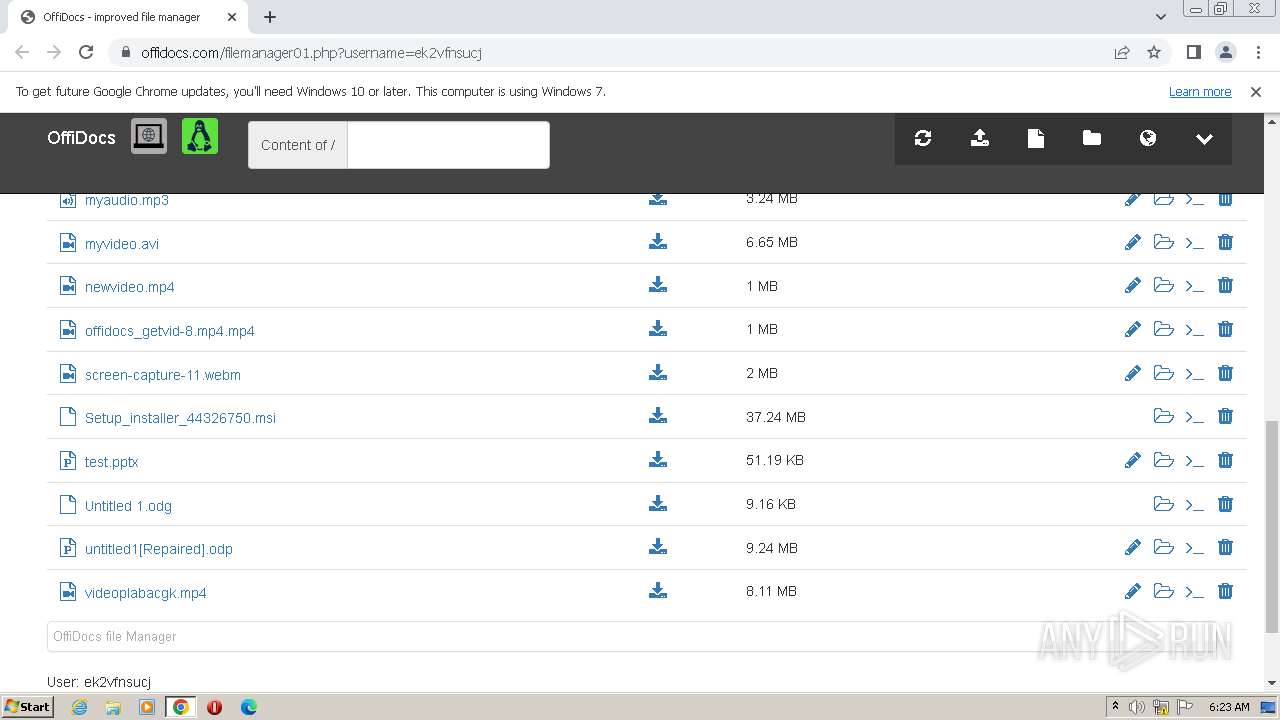
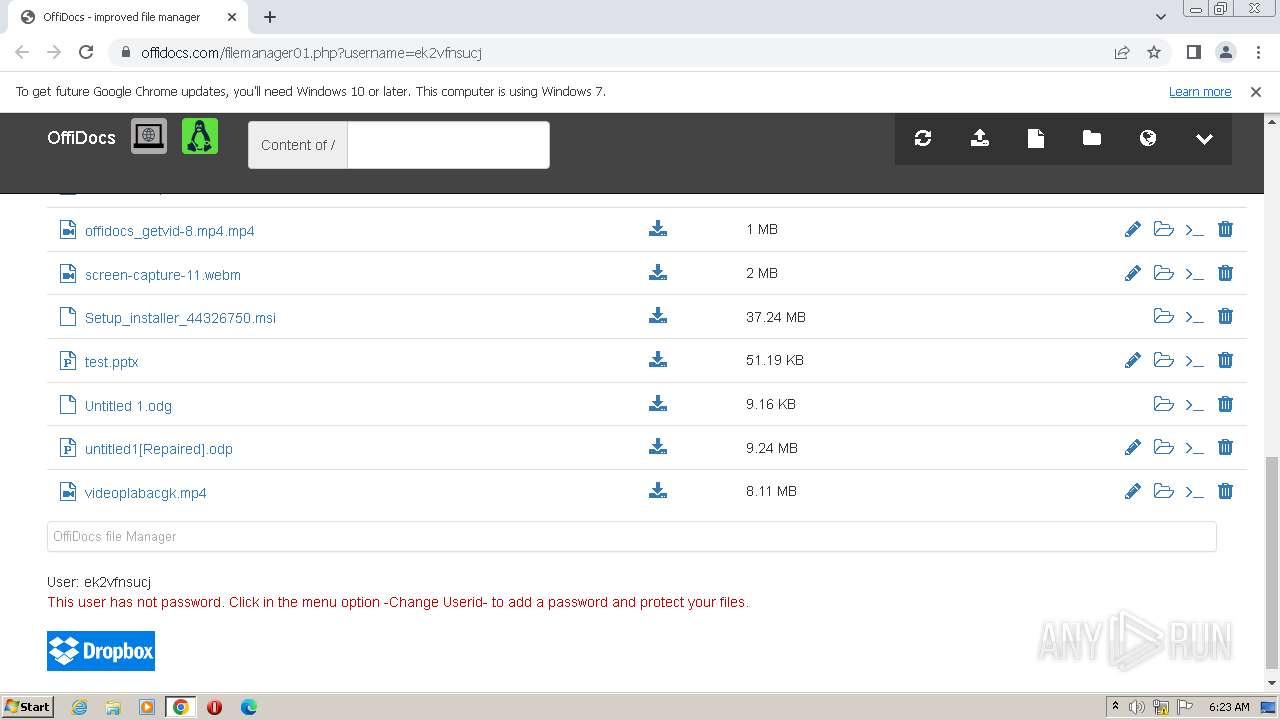
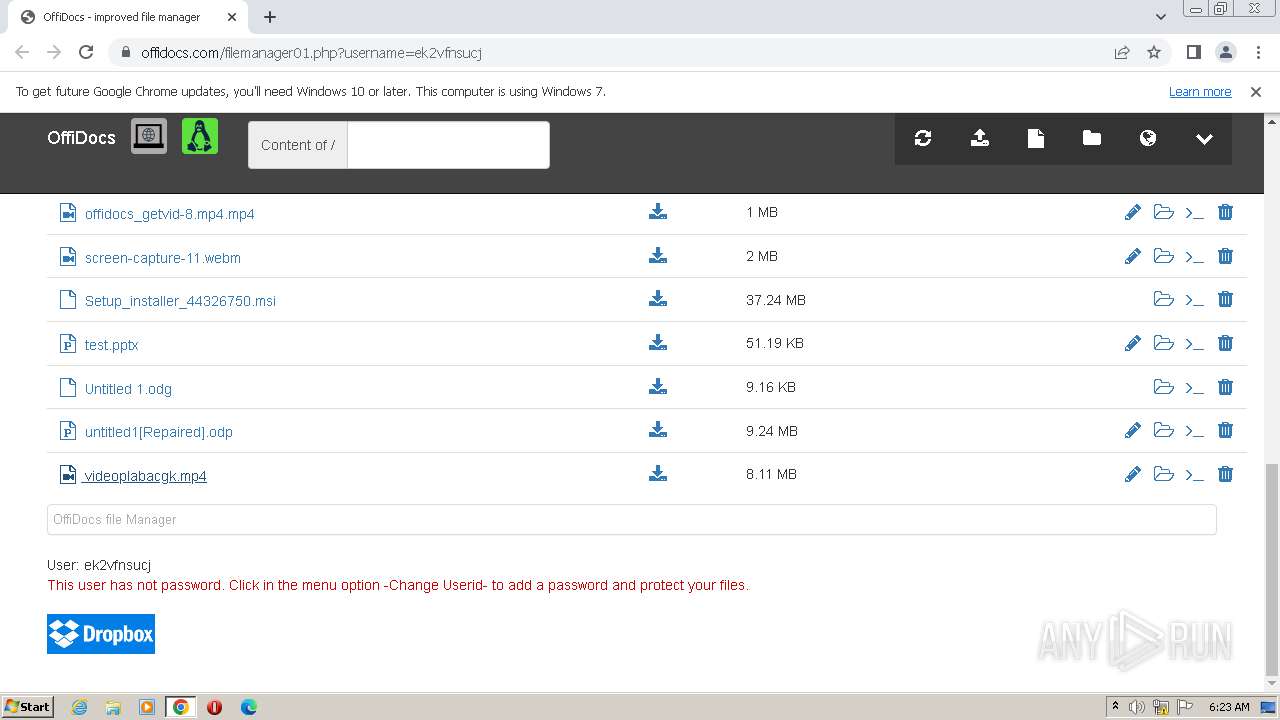
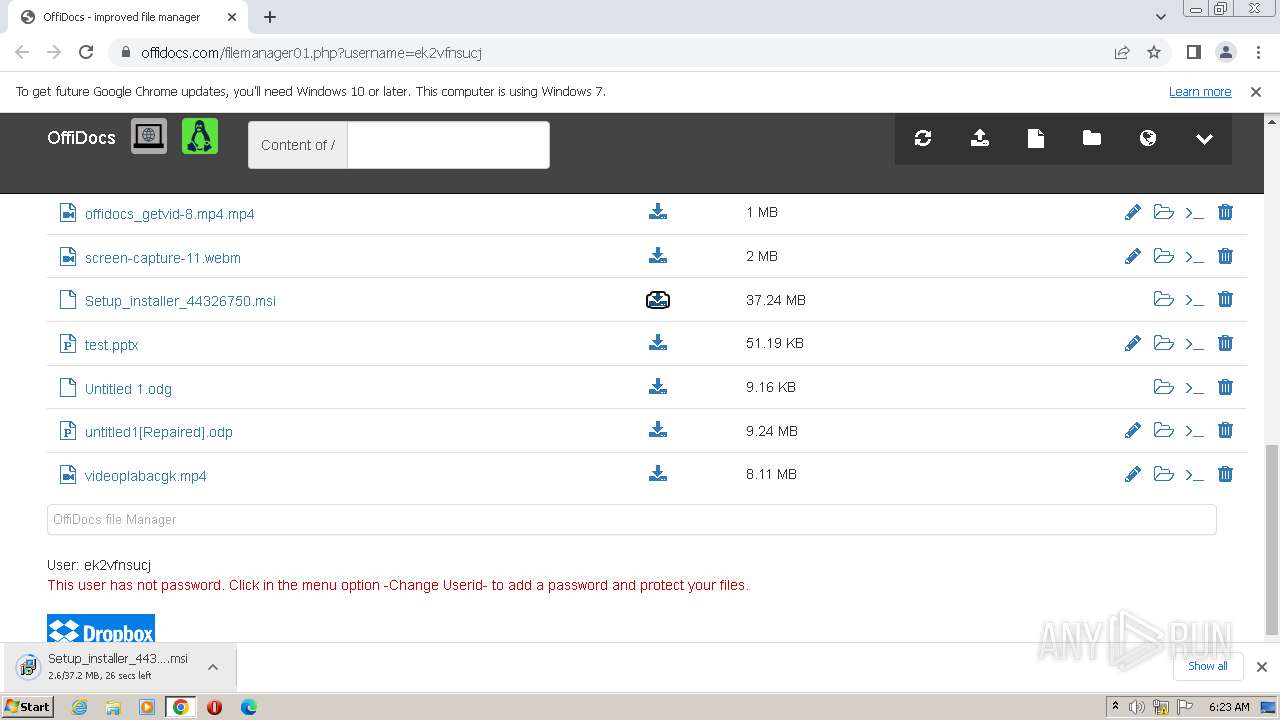
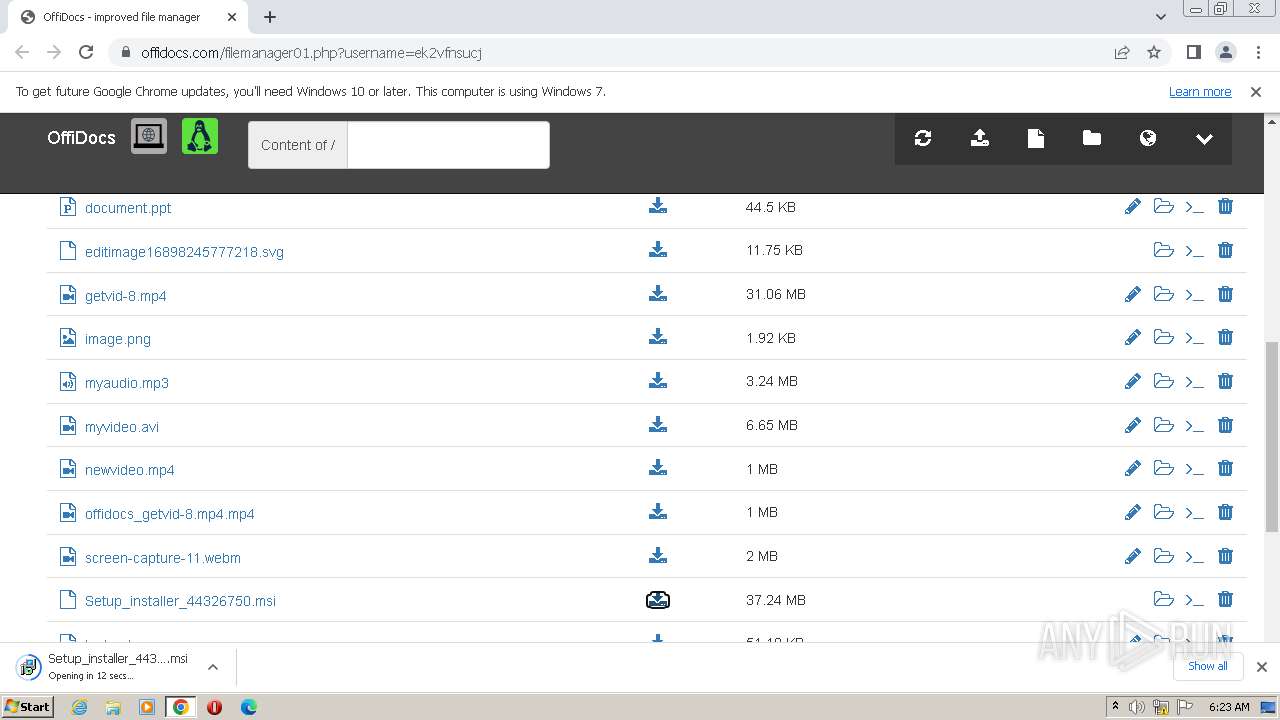
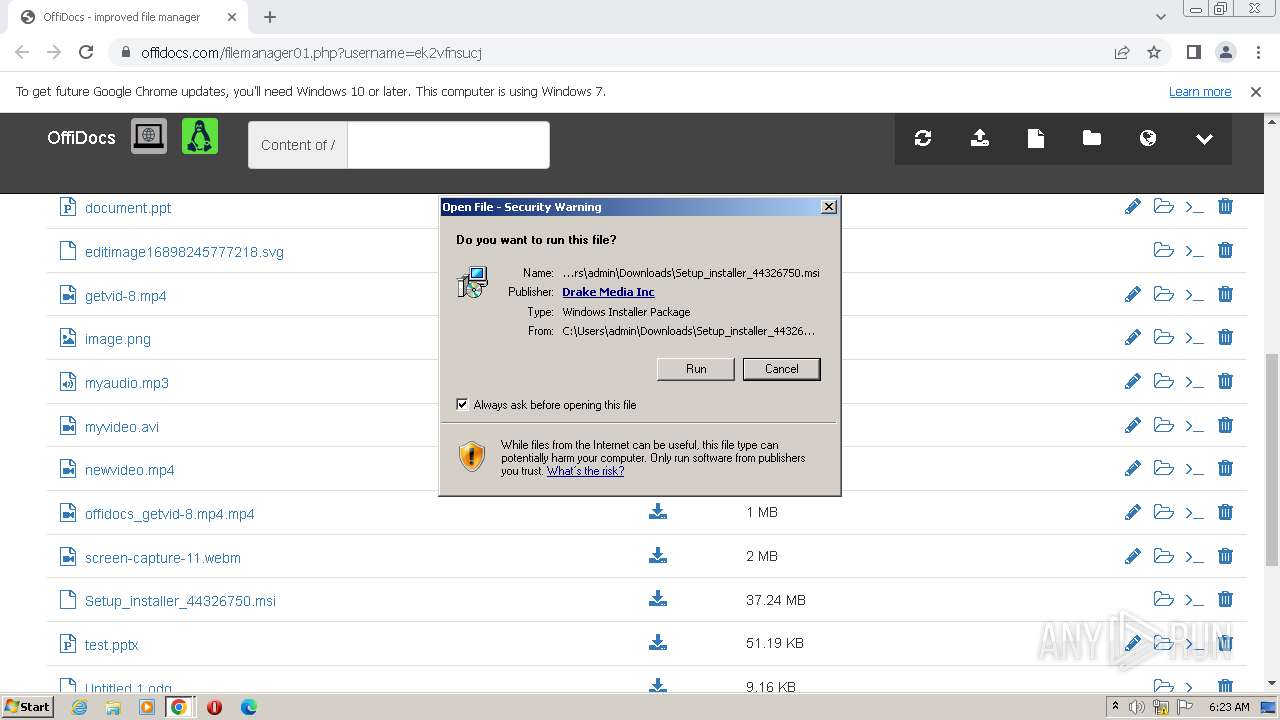
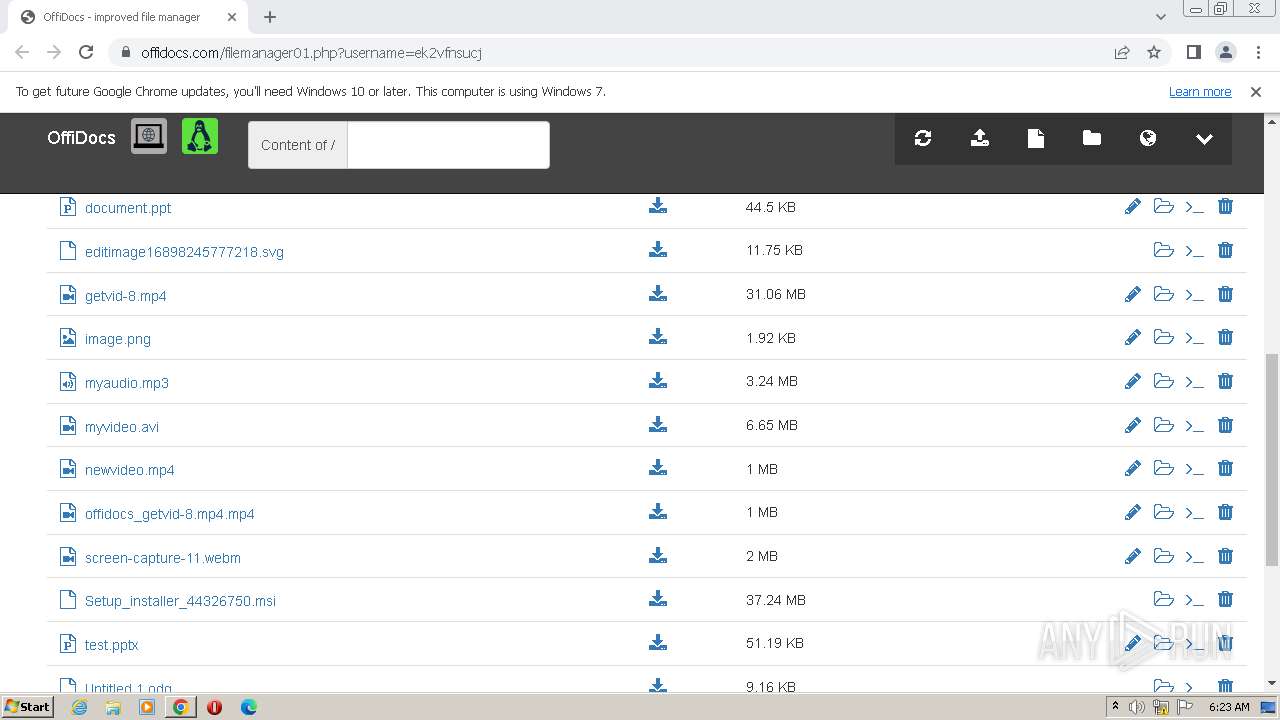
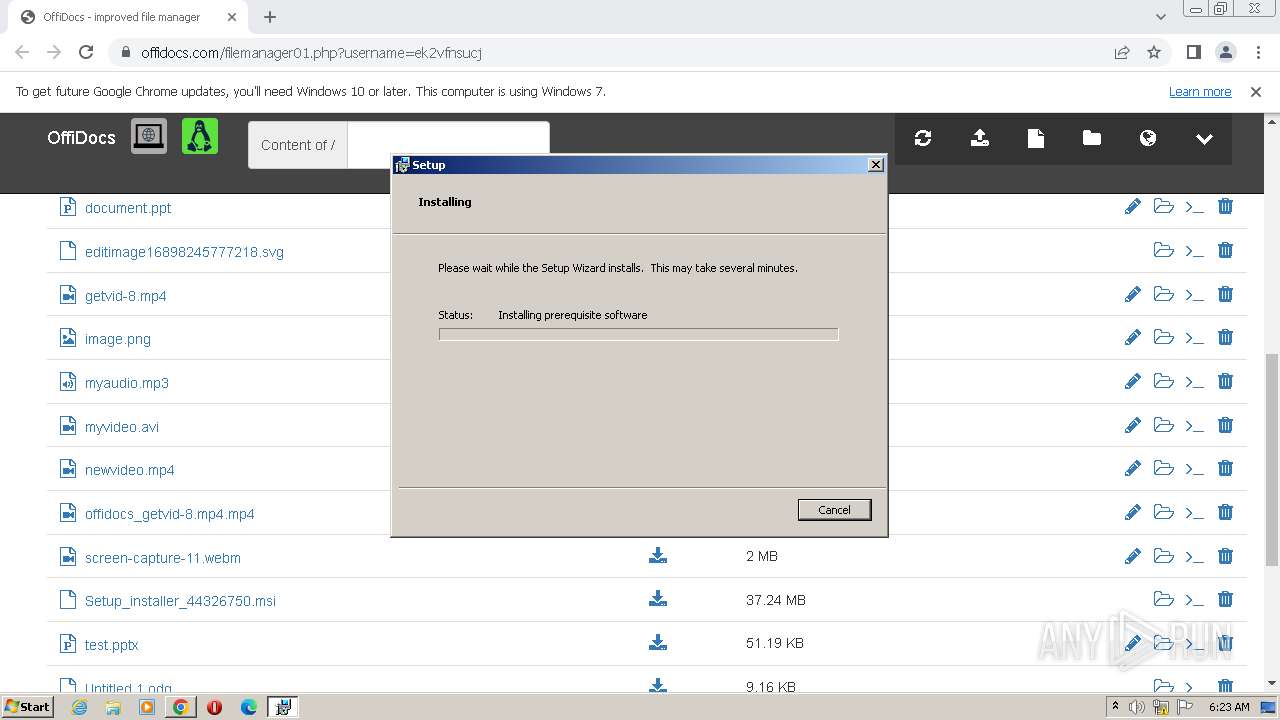
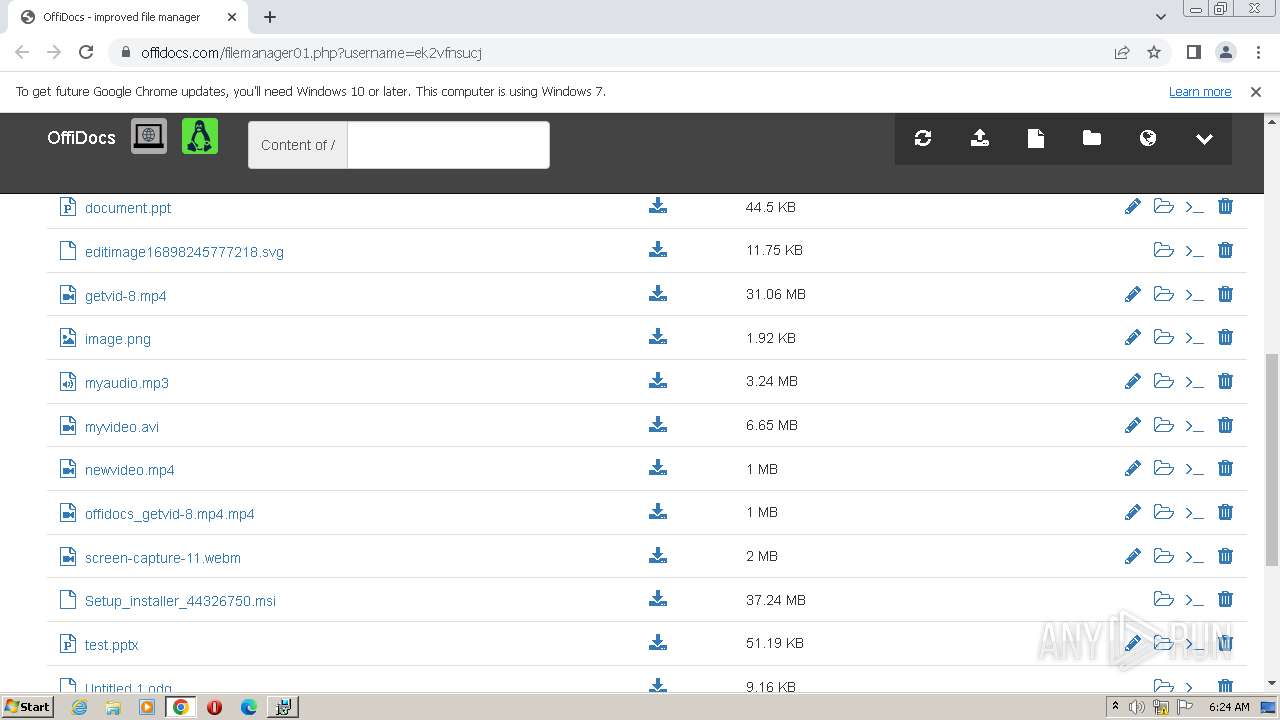
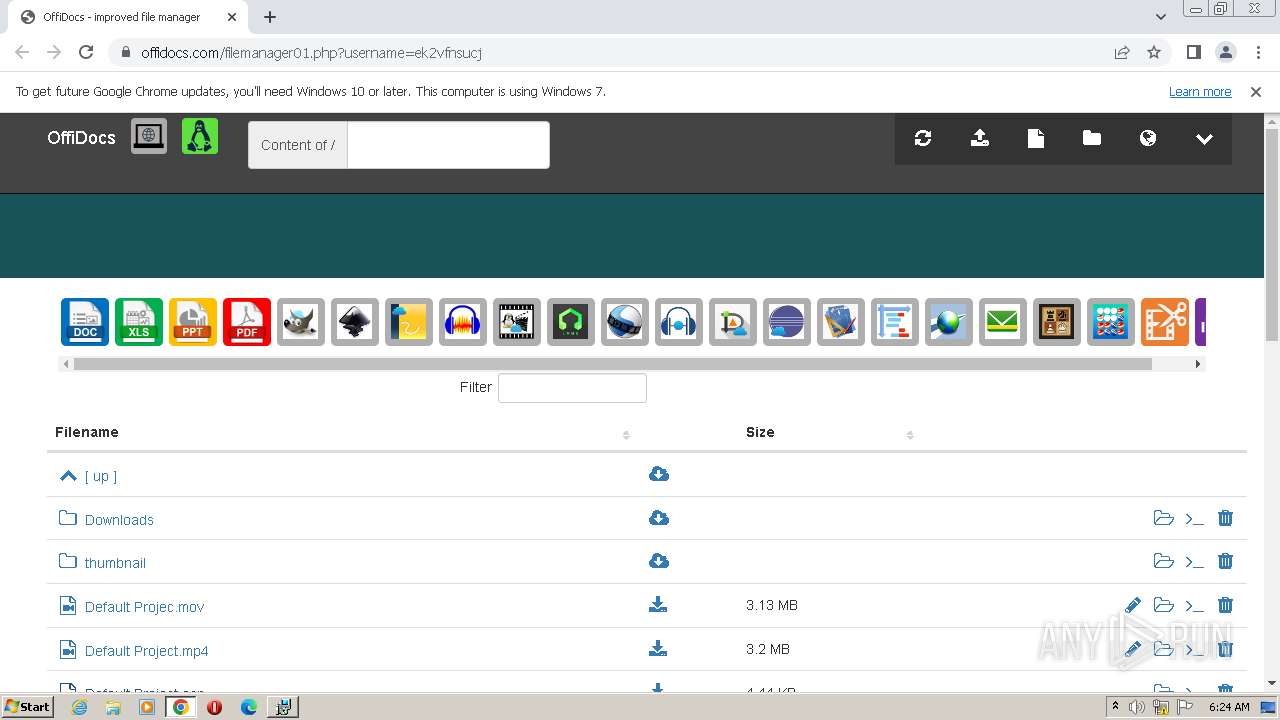
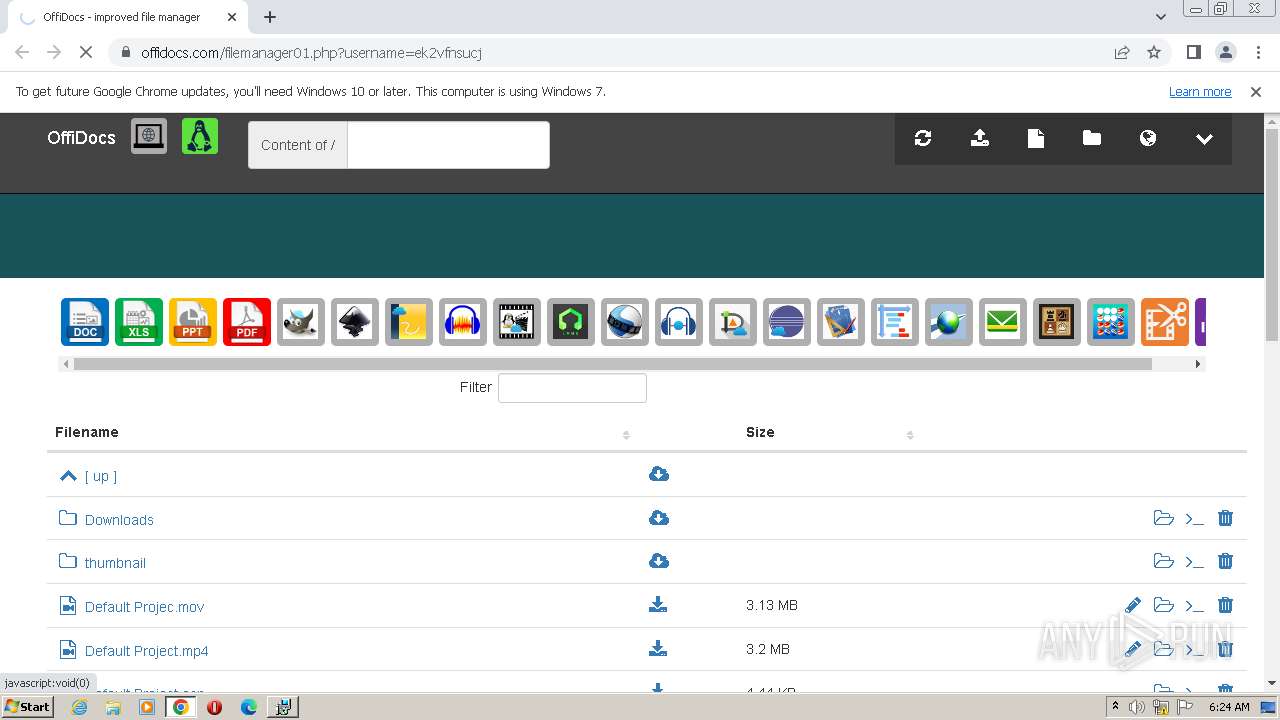
| URL: | https://www.offidocs.com/filemanager01.php?username=ek2vfnsucj |
| Full analysis: | https://app.any.run/tasks/7dd50937-016c-4b4c-a96e-6b5d152efd14 |
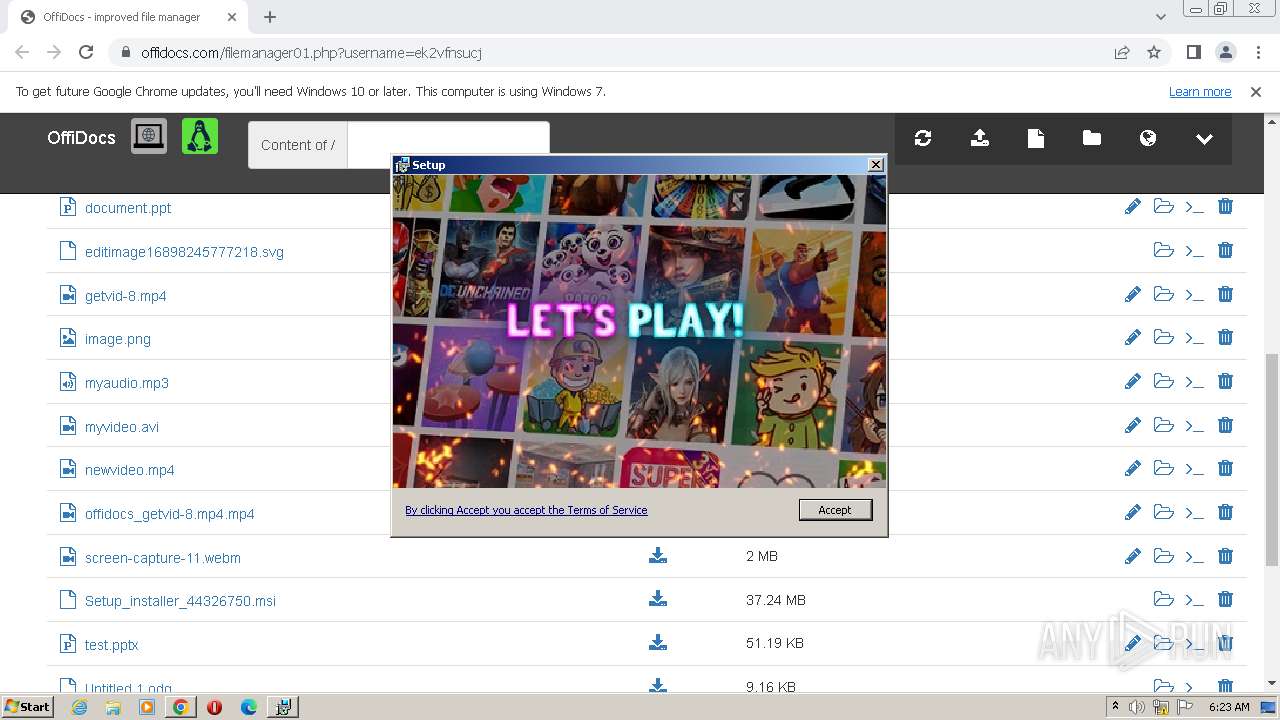
| Verdict: | Malicious activity |
| Analysis date: | July 31, 2023, 05:22:30 |
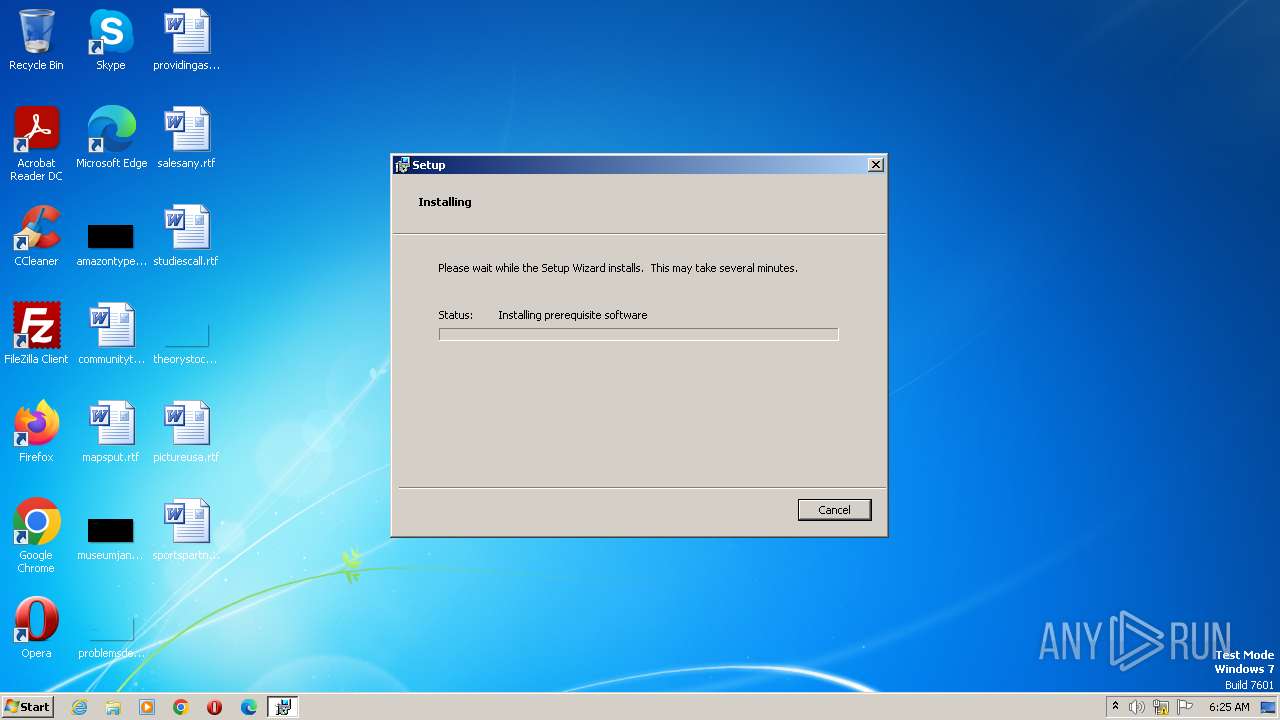
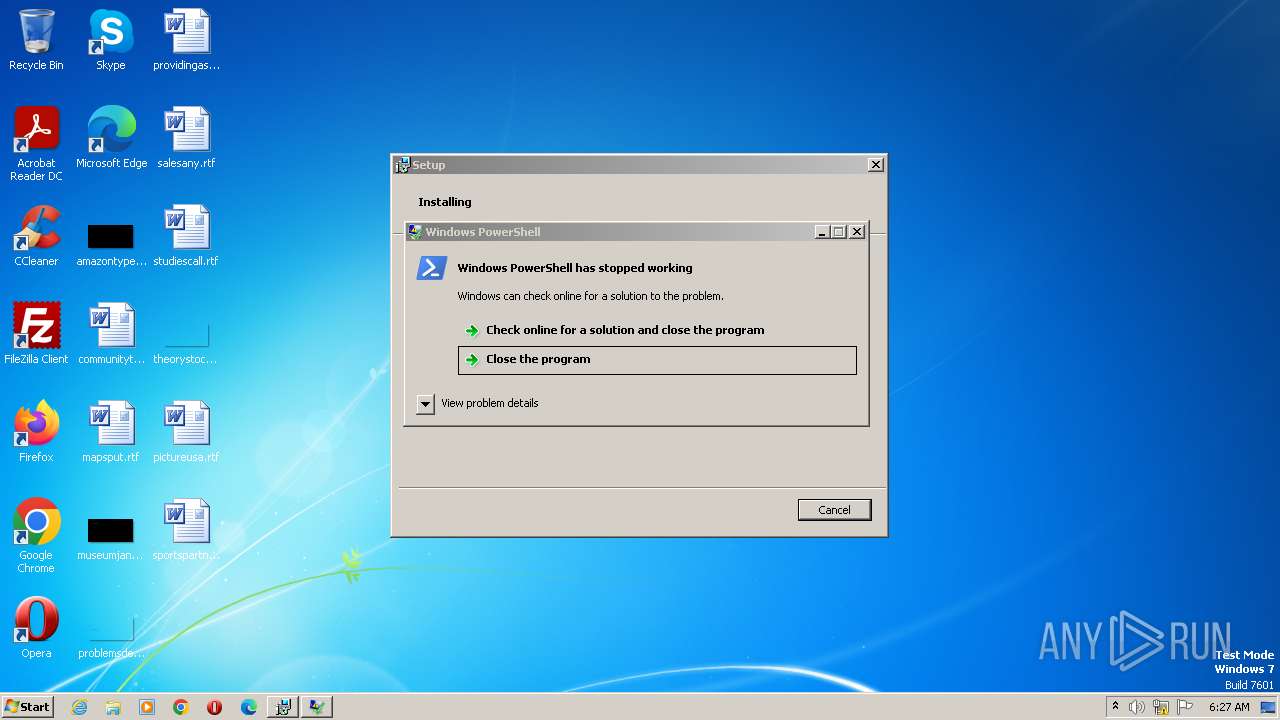
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 67173C3AD776CBDE76E09F146F9718DB |
| SHA1: | 8A20B69EB95E42BFE2E9245612B9BA319B438F6A |
| SHA256: | BDC0B612E3F1E76E1C7FCE6B9F71AC9BFA2DE980B77C1C8EC9515CBDE559C1E2 |
| SSDEEP: | 3:N8DSLD6IYqELOsHamLE9YAOqD:2OLDjEOs89YAl |
MALICIOUS
Changes powershell execution policy (Bypass)
- msiexec.exe (PID: 1868)
- msiexec.exe (PID: 3796)
- MSIBFBC.tmp (PID: 2440)
- msiexec.exe (PID: 2336)
- MSI56F1.tmp (PID: 3036)
- msiexec.exe (PID: 2396)
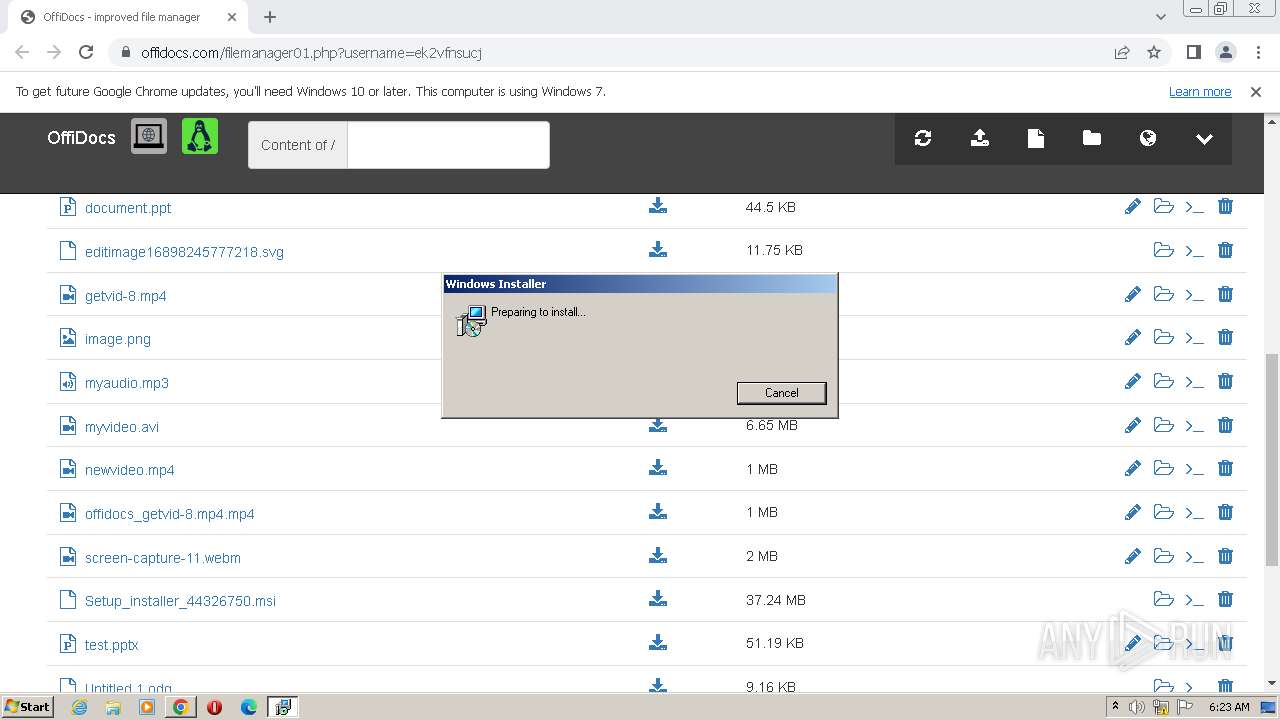
Bypass execution policy to execute commands
- powershell.exe (PID: 2404)
- powershell.exe (PID: 3800)
- powershell.exe (PID: 2676)
- powershell.exe (PID: 4072)
- powershell.exe (PID: 1896)
- powershell.exe (PID: 2076)
- powershell.exe (PID: 2592)
- powershell.exe (PID: 3112)
- powershell.exe (PID: 2532)
- powershell.exe (PID: 3396)
- powershell.exe (PID: 2512)
- powershell.exe (PID: 240)
- powershell.exe (PID: 2076)
- powershell.exe (PID: 3776)
- powershell.exe (PID: 1816)
- powershell.exe (PID: 3348)
- powershell.exe (PID: 2552)
- powershell.exe (PID: 3128)
- powershell.exe (PID: 2952)
- powershell.exe (PID: 1244)
- powershell.exe (PID: 1808)
- powershell.exe (PID: 3252)
Loads dropped or rewritten executable
- msiexec.exe (PID: 1868)
- msiexec.exe (PID: 3796)
- msiexec.exe (PID: 2336)
- node.exe (PID: 1132)
- msiexec.exe (PID: 2396)
Application was dropped or rewritten from another process
- 7za.exe (PID: 3340)
- 7za.exe (PID: 3300)
- node.exe (PID: 1132)
- 7za.exe (PID: 2984)
- 7za.exe (PID: 880)
Actions looks like stealing of personal data
- node.exe (PID: 1132)
SUSPICIOUS
The process executes Powershell scripts
- msiexec.exe (PID: 1868)
- msiexec.exe (PID: 3796)
- msiexec.exe (PID: 2336)
- msiexec.exe (PID: 2396)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 1868)
- msiexec.exe (PID: 3796)
- msiexec.exe (PID: 2336)
- msiexec.exe (PID: 2396)
The process hide an interactive prompt from the user
- msiexec.exe (PID: 1868)
- msiexec.exe (PID: 3796)
- MSIBFBC.tmp (PID: 2440)
- msiexec.exe (PID: 2336)
- MSI56F1.tmp (PID: 3036)
- msiexec.exe (PID: 2396)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 1868)
- msiexec.exe (PID: 3796)
- MSIBFBC.tmp (PID: 2440)
- msiexec.exe (PID: 2336)
- MSI56F1.tmp (PID: 3036)
- msiexec.exe (PID: 2396)
Reads the Internet Settings
- powershell.exe (PID: 2676)
- msiexec.exe (PID: 1868)
- powershell.exe (PID: 4072)
- powershell.exe (PID: 3112)
- powershell.exe (PID: 2076)
- powershell.exe (PID: 2592)
- MSIBFBC.tmp (PID: 2440)
- powershell.exe (PID: 240)
- powershell.exe (PID: 3396)
- powershell.exe (PID: 3776)
- MSI56F1.tmp (PID: 3036)
- powershell.exe (PID: 1816)
- powershell.exe (PID: 3348)
- node.exe (PID: 1132)
- powershell.exe (PID: 3128)
- powershell.exe (PID: 3252)
Searches for installed software
- powershell.exe (PID: 2676)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 3908)
Unusual connection from system programs
- powershell.exe (PID: 2676)
- powershell.exe (PID: 4072)
- powershell.exe (PID: 2592)
- powershell.exe (PID: 2076)
- powershell.exe (PID: 3112)
- powershell.exe (PID: 240)
- powershell.exe (PID: 3396)
- powershell.exe (PID: 3776)
- powershell.exe (PID: 1816)
- powershell.exe (PID: 3348)
- powershell.exe (PID: 3128)
- powershell.exe (PID: 3252)
Executable content was dropped or overwritten
- 7za.exe (PID: 3340)
- 7za.exe (PID: 3300)
Probably obfuscated PowerShell command line is found
- MSIBFBC.tmp (PID: 2440)
Uses TASKKILL.EXE to kill process
- powershell.exe (PID: 2076)
The Powershell connects to the Internet
- powershell.exe (PID: 3396)
Reads settings of System Certificates
- node.exe (PID: 1132)
INFO
Application launched itself
- chrome.exe (PID: 1004)
- msiexec.exe (PID: 3908)
- msiexec.exe (PID: 1868)
Checks supported languages
- msiexec.exe (PID: 3908)
- msiexec.exe (PID: 1868)
- msiexec.exe (PID: 3796)
- 7za.exe (PID: 3340)
- MSIBFBC.tmp (PID: 2440)
- msiexec.exe (PID: 2336)
- 7za.exe (PID: 3300)
- MSI56F1.tmp (PID: 3036)
- node.exe (PID: 1132)
- 7za.exe (PID: 2984)
- msiexec.exe (PID: 2396)
- 7za.exe (PID: 880)
The process checks LSA protection
- msiexec.exe (PID: 1496)
- msiexec.exe (PID: 3908)
- msiexec.exe (PID: 1868)
- powershell.exe (PID: 2404)
- powershell.exe (PID: 3800)
- powershell.exe (PID: 2676)
- msiexec.exe (PID: 272)
- msiexec.exe (PID: 3796)
- powershell.exe (PID: 4072)
- powershell.exe (PID: 1896)
- powershell.exe (PID: 3112)
- powershell.exe (PID: 2076)
- powershell.exe (PID: 2592)
- MSIBFBC.tmp (PID: 2440)
- powershell.exe (PID: 2532)
- powershell.exe (PID: 2512)
- msiexec.exe (PID: 3500)
- msiexec.exe (PID: 2336)
- powershell.exe (PID: 240)
- powershell.exe (PID: 3776)
- powershell.exe (PID: 2076)
- powershell.exe (PID: 1816)
- MSI56F1.tmp (PID: 3036)
- powershell.exe (PID: 3348)
- node.exe (PID: 1132)
- msiexec.exe (PID: 3996)
- msiexec.exe (PID: 2396)
- powershell.exe (PID: 3128)
- powershell.exe (PID: 2952)
- powershell.exe (PID: 1244)
- powershell.exe (PID: 1808)
- powershell.exe (PID: 3252)
Reads the computer name
- msiexec.exe (PID: 3908)
- msiexec.exe (PID: 1868)
- msiexec.exe (PID: 3796)
- 7za.exe (PID: 3340)
- MSIBFBC.tmp (PID: 2440)
- msiexec.exe (PID: 2336)
- 7za.exe (PID: 3300)
- MSI56F1.tmp (PID: 3036)
- 7za.exe (PID: 2984)
- msiexec.exe (PID: 2396)
- node.exe (PID: 1132)
- 7za.exe (PID: 880)
The process uses the downloaded file
- chrome.exe (PID: 2424)
- chrome.exe (PID: 1004)
- chrome.exe (PID: 3376)
- chrome.exe (PID: 2184)
Executable content was dropped or overwritten
- msiexec.exe (PID: 1496)
- msiexec.exe (PID: 1868)
- msiexec.exe (PID: 3908)
- chrome.exe (PID: 3544)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 1496)
- powershell.exe (PID: 3800)
- powershell.exe (PID: 2404)
- powershell.exe (PID: 2676)
- powershell.exe (PID: 4072)
- powershell.exe (PID: 1896)
- powershell.exe (PID: 3112)
- powershell.exe (PID: 2076)
- powershell.exe (PID: 2592)
- powershell.exe (PID: 2532)
- powershell.exe (PID: 2512)
- powershell.exe (PID: 240)
- powershell.exe (PID: 2076)
- powershell.exe (PID: 3776)
- powershell.exe (PID: 1816)
- powershell.exe (PID: 3348)
- powershell.exe (PID: 3128)
- powershell.exe (PID: 2952)
- powershell.exe (PID: 1244)
- powershell.exe (PID: 3252)
Reads the machine GUID from the registry
- msiexec.exe (PID: 3908)
- msiexec.exe (PID: 1868)
- msiexec.exe (PID: 3796)
- msiexec.exe (PID: 2336)
- node.exe (PID: 1132)
- msiexec.exe (PID: 2396)
Reads Environment values
- msiexec.exe (PID: 1868)
- msiexec.exe (PID: 3796)
- MSIBFBC.tmp (PID: 2440)
- msiexec.exe (PID: 2336)
- MSI56F1.tmp (PID: 3036)
- node.exe (PID: 1132)
- msiexec.exe (PID: 2396)
Create files in a temporary directory
- msiexec.exe (PID: 1868)
- powershell.exe (PID: 2404)
- powershell.exe (PID: 3800)
- powershell.exe (PID: 2676)
- msiexec.exe (PID: 3796)
- powershell.exe (PID: 4072)
- powershell.exe (PID: 1896)
- msiexec.exe (PID: 3908)
- powershell.exe (PID: 3112)
- powershell.exe (PID: 2076)
- powershell.exe (PID: 2592)
- powershell.exe (PID: 2512)
- powershell.exe (PID: 2532)
- msiexec.exe (PID: 2336)
- powershell.exe (PID: 240)
- powershell.exe (PID: 3776)
- powershell.exe (PID: 1816)
- powershell.exe (PID: 2076)
- powershell.exe (PID: 3348)
- msiexec.exe (PID: 2396)
- powershell.exe (PID: 2952)
- powershell.exe (PID: 1244)
- powershell.exe (PID: 3128)
- powershell.exe (PID: 3252)
Creates files or folders in the user directory
- powershell.exe (PID: 2404)
- msiexec.exe (PID: 1868)
- msiexec.exe (PID: 3908)
- 7za.exe (PID: 3340)
- 7za.exe (PID: 3300)
- 7za.exe (PID: 880)
Starts application with an unusual extension
- msiexec.exe (PID: 3908)
Application was dropped or rewritten from another process
- MSIBFBC.tmp (PID: 2440)
- MSI56F1.tmp (PID: 3036)
The executable file from the user directory is run by the Powershell process
- node.exe (PID: 1132)
Reads product name
- node.exe (PID: 1132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
124
Monitored processes
62
Malicious processes
13
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pssC4F3.tmp.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 272 | "C:\Windows\system32\msiexec.exe" /i "C:\Users\admin\AppData\Roaming\Eclipse Media Inc\Installer Assistant\prerequisites\WCSetupv1.11.1052.27169.msi" /q | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3836 --field-trial-handle=1164,i,11801152054457891508,15308194658910179971,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3428 --field-trial-handle=1164,i,11801152054457891508,15308194658910179971,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 880 | "C:\Users\admin\AppData\Roaming/Browser Extension/7za.exe" x Data.7z -y -p1.10.162.23111 | C:\Users\admin\AppData\Roaming\Browser Extension\7za.exe | — | powershell.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Standalone Console Exit code: 0 Version: 19.00 Modules
| |||||||||||||||
| 1004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://www.offidocs.com/filemanager01.php?username=ek2vfnsucj" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1132 | "C:\Users\admin\AppData\Roaming\Browser Assistant\edge\x86\node.exe" ./edge/startup.js | C:\Users\admin\AppData\Roaming\Browser Assistant\edge\x86\node.exe | powershell.exe | ||||||||||||
User: admin Company: Node.js Integrity Level: MEDIUM Description: Node.js: Server-side JavaScript Exit code: 0 Version: 12.15.0 Modules
| |||||||||||||||
| 1244 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pss5F7C.tmp.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1496 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\Downloads\Setup_installer_44326750.msi" | C:\Windows\System32\msiexec.exe | chrome.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6e9d8b38,0x6e9d8b48,0x6e9d8b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
37 860
Read events
37 684
Write events
152
Delete events
24
Modification events
| (PID) Process: | (1004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (1004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1004) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (1004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
135
Suspicious files
225
Text files
2 761
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF174edb.TMP | — | |
MD5:— | SHA256:— | |||
| 1004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF1750c0.TMP | text | |
MD5:F13F92FE0277FBD908E4410DEB43609A | SHA256:5746DB776E91B0EF58626F444ADC79E4F8B76C7CEDEEC1BD8D59F7726280880B | |||
| 1004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF175da0.TMP | — | |
MD5:— | SHA256:— | |||
| 1004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4ab68df3-91a1-4fac-9ecd-2033d263a6e2.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 1004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 1004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 1004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF174eeb.TMP | text | |
MD5:CF083E99BB51786FA31BD0E0FE2686E4 | SHA256:BC8DE81EFA52674CA26D55DFAFCBCE7A4D38994BEF5D267548EADF9985DBF5AC | |||
| 1004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:0917C6BFC618ACD47C1F53C7E7FFFF9C | SHA256:A5CAF56982DA7AE34B201E8609610786B4730371EF0812B7D418A2F9B73547BC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
65
DNS requests
40
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
860 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acfrxel7rbjfr2oo2pzgxizks4eq_403/lmelglejhemejginpboagddgdfbepgmp_403_all_ZZ_acs5nbh2ktbkojmgdvvippsdbkka.crx3 | US | — | — | whitelisted |
4072 | powershell.exe | POST | 200 | 108.138.24.52:80 | http://dhb63vq2dmigo.cloudfront.net/ | US | binary | 19 b | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | binary | 29.4 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | binary | 138 Kb | whitelisted |
2592 | powershell.exe | POST | 200 | 108.138.24.52:80 | http://dhb63vq2dmigo.cloudfront.net/ | US | binary | 19 b | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | binary | 9.00 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | binary | 83.7 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | binary | 358 Kb | whitelisted |
1004 | chrome.exe | GET | 200 | 104.18.20.226:80 | http://secure.globalsign.com/cacert/codesigningrootr45.crt | US | binary | 1.37 Kb | whitelisted |
860 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/cxpsjblnoxgjoqggdsbvujtof4_58/khaoiebndkojlmppeemjhbpbandiljpe_58_win_advr4ucepztwtigvw3fduftsvbeq.crx3 | US | binary | 1.94 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2640 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1004 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3148 | chrome.exe | 51.77.72.178:443 | www.offidocs.com | OVH SAS | FR | unknown |
3148 | chrome.exe | 142.250.185.136:443 | www.googletagmanager.com | GOOGLE | US | suspicious |
3148 | chrome.exe | 216.58.206.46:443 | www.google-analytics.com | GOOGLE | US | whitelisted |
3148 | chrome.exe | 216.58.212.162:443 | pagead2.googlesyndication.com | GOOGLE | US | whitelisted |
3148 | chrome.exe | 216.58.206.36:443 | www.google.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
www.offidocs.com |
| unknown |
www.googletagmanager.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
region1.google-analytics.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
www.googleapis.com |
| whitelisted |
optimizationguide-pa.googleapis.com |
| whitelisted |