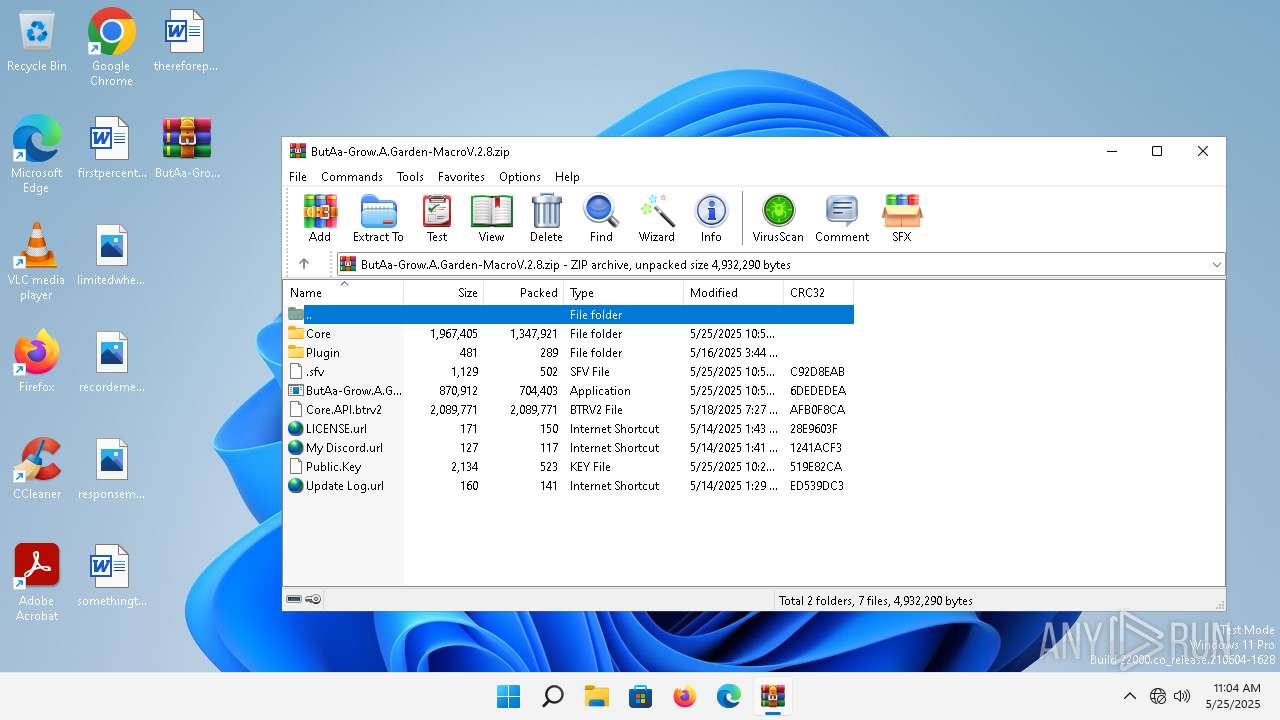
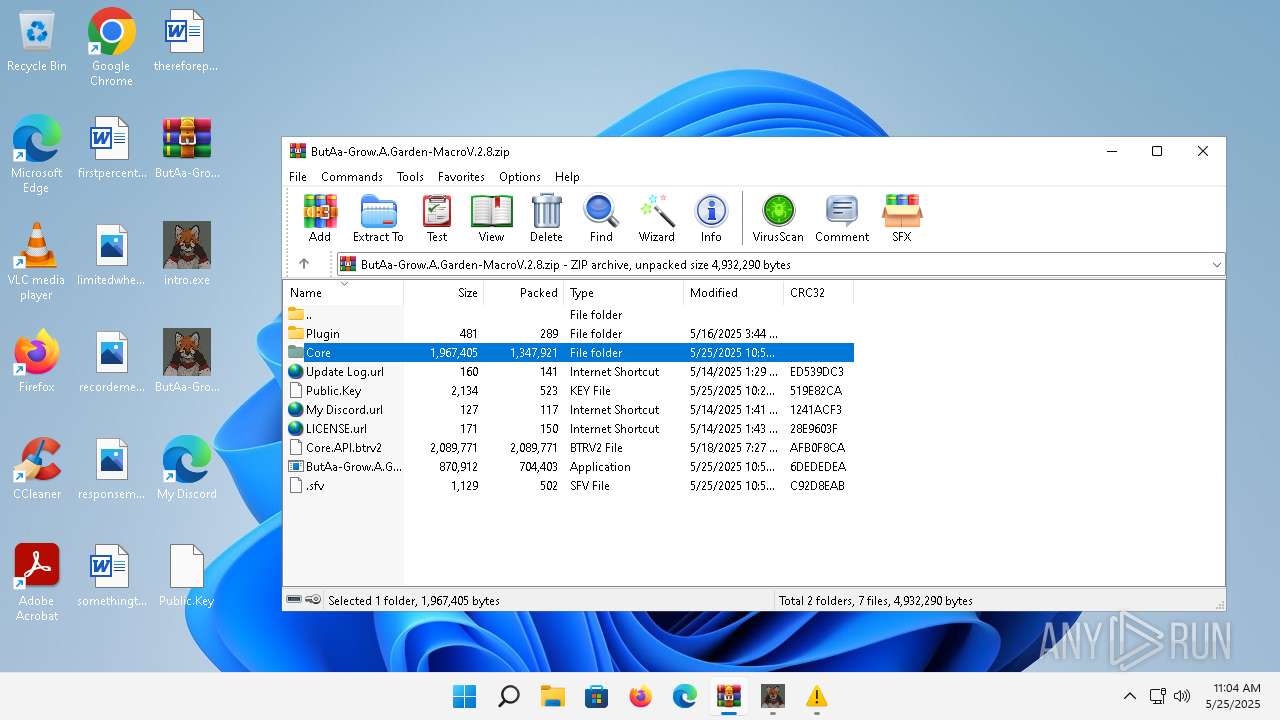
| File name: | ButAa-Grow.A.Garden-MacroV.2.8.zip |
| Full analysis: | https://app.any.run/tasks/b69d45d4-787b-4749-8ec3-c50900b6f9a5 |
| Verdict: | Malicious activity |
| Analysis date: | May 25, 2025, 11:04:03 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 2FED64E45EFB12616504B9D4BC2D0F00 |
| SHA1: | A47E3BF83B880D8D7CE7F40964B09D42D28DE4EA |
| SHA256: | BDC09B1D165E6A48D6E9591B565F1B2165F3416BB747749635D05A0183D619C5 |
| SSDEEP: | 98304:EFDWJGyZxixTxnx9WxXabNaUbImOfEDYdJsfj+wbGY24rReMBBKN3QeJDDhNBRSD:TrUKT6nJvJ |
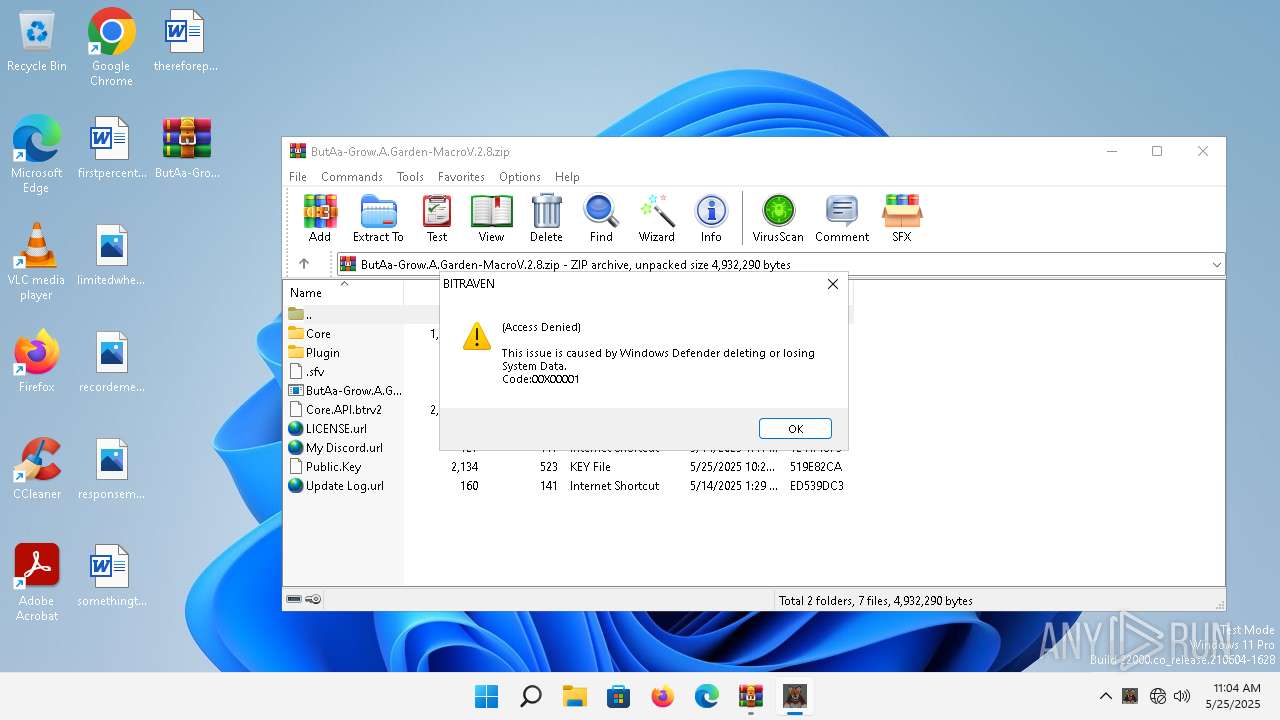
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 5740)
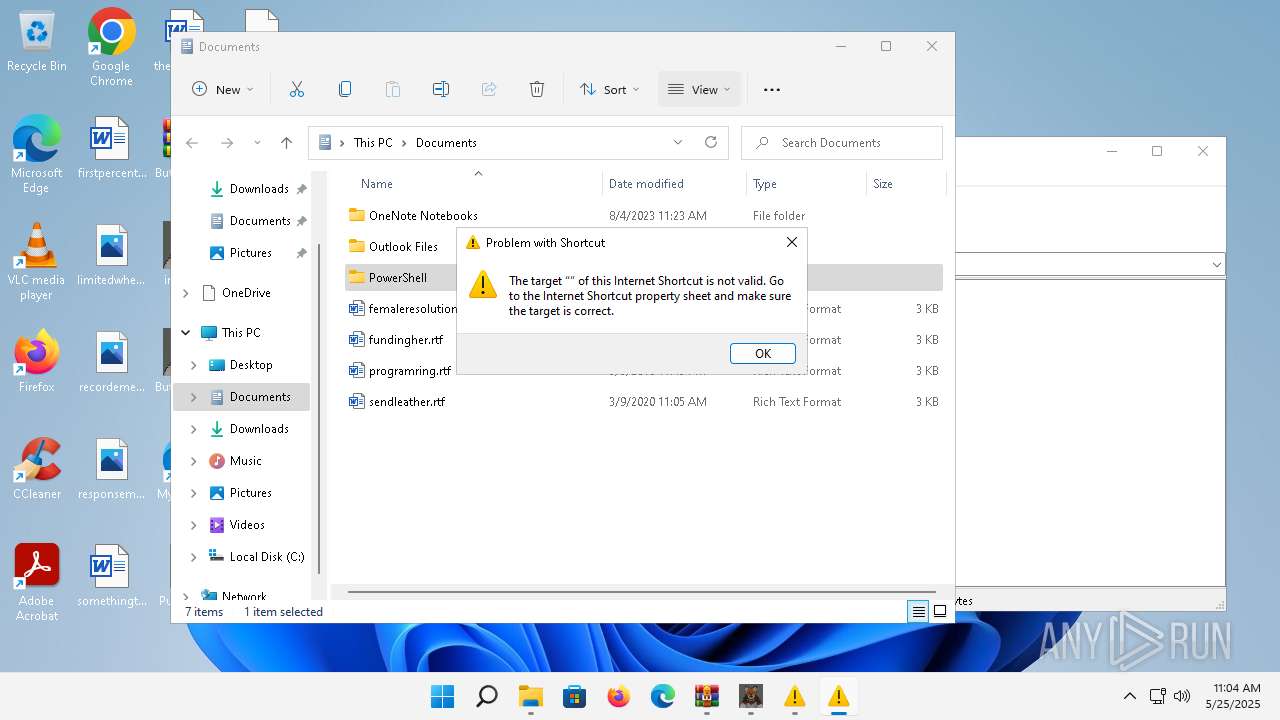
SUSPICIOUS
Creates file in the systems drive root
- WinRAR.exe (PID: 5740)
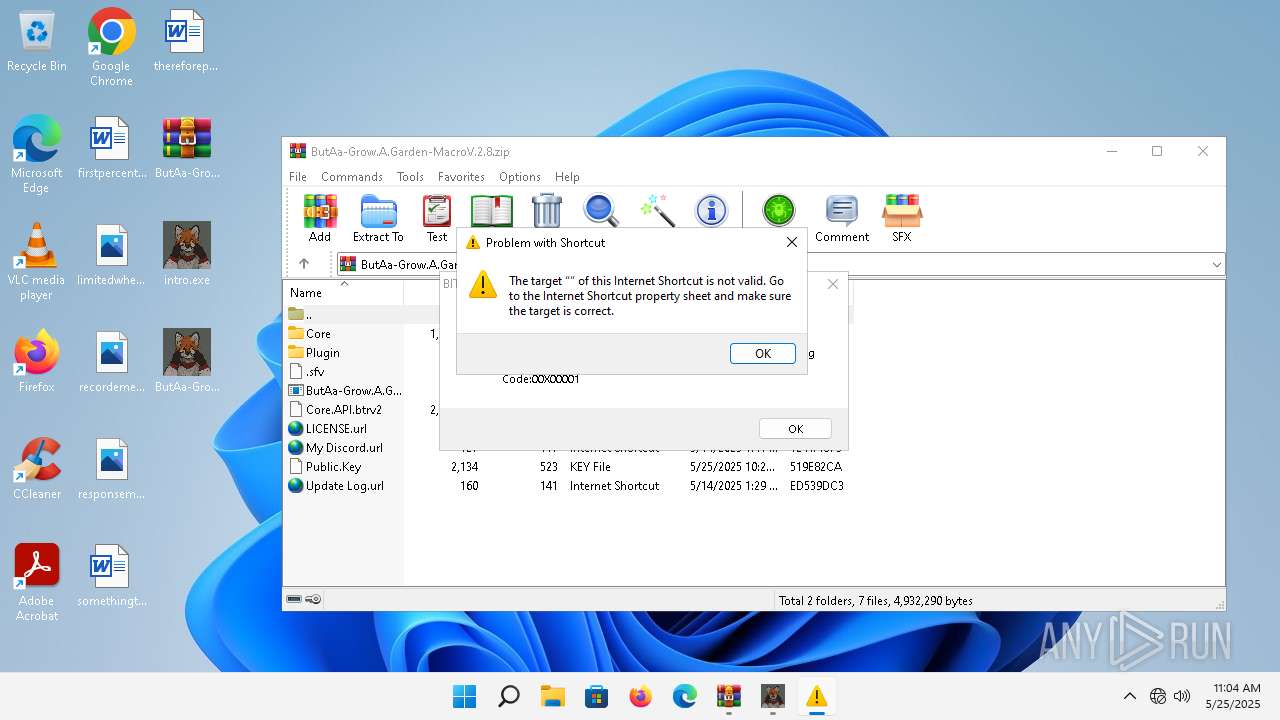
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5740)
Reads the Internet Settings
- rundll32.exe (PID: 3408)
- OpenWith.exe (PID: 3548)
There is functionality for taking screenshot (YARA)
- vlc.exe (PID: 2708)
INFO
Reads the computer name
- intro.exe (PID: 4632)
- ButAa-Grow.A.Garden-Macro(V.2.8).exe (PID: 2320)
- vlc.exe (PID: 2708)
Manual execution by a user
- ButAa-Grow.A.Garden-Macro(V.2.8).exe (PID: 2320)
- rundll32.exe (PID: 3044)
- intro.exe (PID: 4632)
- OpenWith.exe (PID: 3548)
- rundll32.exe (PID: 2112)
- rundll32.exe (PID: 3472)
- rundll32.exe (PID: 3408)
- vlc.exe (PID: 2708)
Checks supported languages
- intro.exe (PID: 4632)
- ButAa-Grow.A.Garden-Macro(V.2.8).exe (PID: 2320)
- vlc.exe (PID: 2708)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 3044)
- rundll32.exe (PID: 3472)
- rundll32.exe (PID: 3408)
- OpenWith.exe (PID: 3548)
- rundll32.exe (PID: 2112)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 3548)
- rundll32.exe (PID: 3408)
The process uses Lua
- vlc.exe (PID: 2708)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:05:25 17:59:34 |
| ZipCRC: | 0xc92d8eab |
| ZipCompressedSize: | 502 |
| ZipUncompressedSize: | 1129 |
| ZipFileName: | .sfv |
Total processes
110
Monitored processes
9
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2112 | "C:\Windows\System32\rundll32.exe" "C:\Windows\System32\ieframe.dll",OpenURL %l | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2320 | "C:\Users\admin\Desktop\ButAa-Grow.A.Garden-Macro(V.2.8).exe" | C:\Users\admin\Desktop\ButAa-Grow.A.Garden-Macro(V.2.8).exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Version: 1.1.37.02 Modules
| |||||||||||||||
| 2708 | "C:\Program Files\VideoLAN\VLC\vlc.exe" --started-from-file C:\Users\admin\Desktop\notify_pause.wav | C:\Program Files\VideoLAN\VLC\vlc.exe | explorer.exe | ||||||||||||
User: admin Company: VideoLAN Integrity Level: MEDIUM Description: VLC media player Version: 3.0.11 Modules
| |||||||||||||||
| 3044 | "C:\Windows\System32\rundll32.exe" "C:\Windows\System32\ieframe.dll",OpenURL %l | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3408 | "C:\Windows\System32\rundll32.exe" "C:\Program Files\Windows Photo Viewer\PhotoViewer.dll", ImageView_Fullscreen C:\Users\admin\Desktop\logo.jpg | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3472 | "C:\Windows\System32\rundll32.exe" "C:\Windows\System32\ieframe.dll",OpenURL %l | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3548 | "C:\Windows\System32\OpenWith.exe" C:\Users\admin\Desktop\12a10df0-f945-47e0-8316-617ba7fab53c | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4632 | "C:\Users\admin\Desktop\intro.exe" | C:\Users\admin\Desktop\intro.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.1.37.02 Modules
| |||||||||||||||
| 5740 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\ButAa-Grow.A.Garden-MacroV.2.8.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
34 549
Read events
34 488
Write events
61
Delete events
0
Modification events
| (PID) Process: | (5740) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5740) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5740) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\ButAa-Grow.A.Garden-MacroV.2.8.zip | |||
| (PID) Process: | (5740) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5740) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5740) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5740) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5740) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\4c\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\ieframe.dll,-10046 |
Value: Internet Shortcut | |||
| (PID) Process: | (5740) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (5740) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
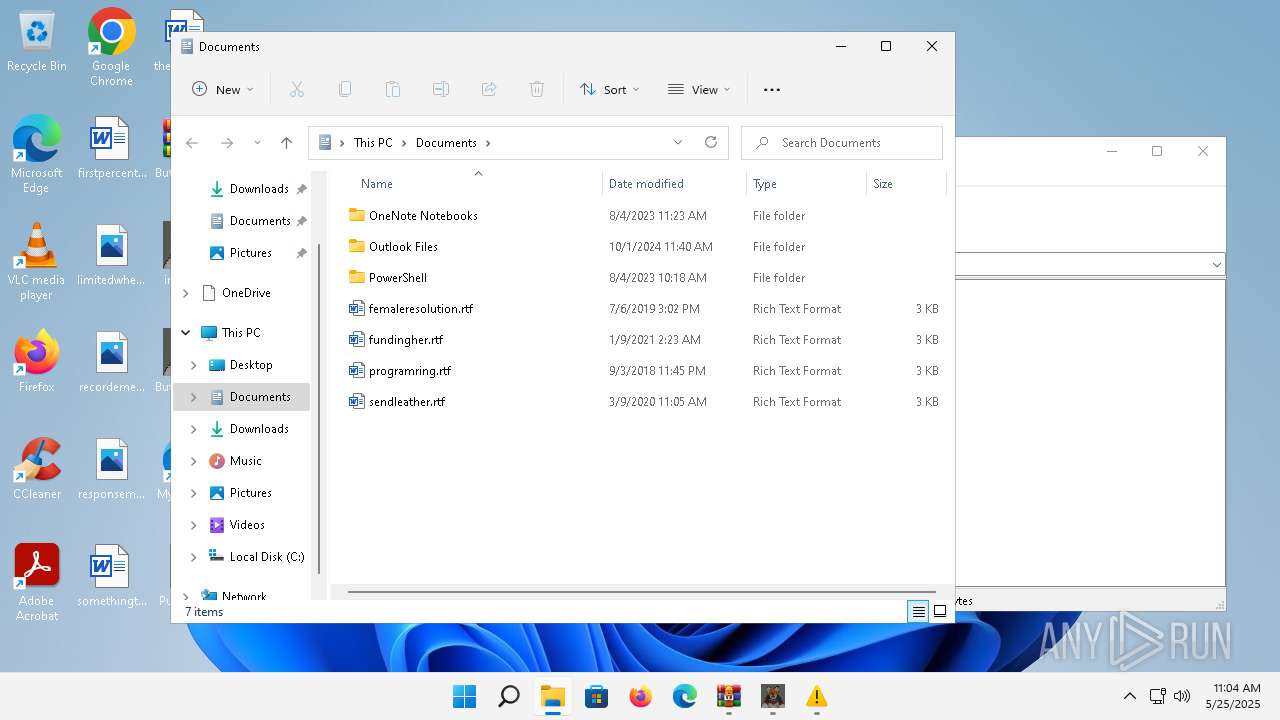
Executable files
2
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2708 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\vlc-qt-interface.ini | text | |
MD5:0E91FD68830AB679C4EDA904FABF828F | SHA256:A976AC6DE2E2425E9DC1E3C0CC8984C77D7252C6074151FD4BB4D4D7544FFE65 | |||
| 2708 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\vlc-qt-interface.ini.lock | text | |
MD5:F14C9ED311556DE31FE9184653DD8026 | SHA256:0B9157AC88DCDF76473F6C5A701D11F1DF1B16230F758A0EF8BBF2B42AE183DD | |||
| 2708 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\vlc-qt-interface.ini.Hp2708 | text | |
MD5:0E91FD68830AB679C4EDA904FABF828F | SHA256:A976AC6DE2E2425E9DC1E3C0CC8984C77D7252C6074151FD4BB4D4D7544FFE65 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
13
DNS requests
8
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1396 | smartscreen.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f37a682d6e2a699b | unknown | — | — | whitelisted |
— | — | POST | 200 | 48.209.164.47:443 | https://checkappexec.microsoft.com/windows/shell/actions | unknown | binary | 182 b | whitelisted |
— | — | HEAD | 200 | 23.197.142.186:443 | https://fs.microsoft.com/fs/windows/config.json | unknown | — | — | unknown |
1352 | svchost.exe | GET | 200 | 2.16.168.102:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.197.142.186:443 | https://fs.microsoft.com/fs/windows/config.json | unknown | binary | 55 b | whitelisted |
— | — | POST | 200 | 13.89.178.26:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | unknown | binary | 9 b | whitelisted |
2768 | svchost.exe | GET | 200 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?01658cdb802755c3 | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?e631054164025918 | unknown | — | — | whitelisted |
— | — | POST | 200 | 40.126.32.68:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
2768 | svchost.exe | GET | 200 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?d58461112108c32f | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1352 | svchost.exe | 2.16.168.102:80 | — | Akamai International B.V. | RU | unknown |
1396 | smartscreen.exe | 172.205.80.42:443 | checkappexec.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | VN | whitelisted |
1396 | smartscreen.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4976 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4296 | svchost.exe | 23.197.142.186:443 | fs.microsoft.com | Akamai International B.V. | US | whitelisted |
2768 | svchost.exe | 199.232.210.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
2988 | OfficeClickToRun.exe | 20.189.173.2:443 | self.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3640 | svchost.exe | 20.190.160.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
checkappexec.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
1352 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |
Process | Message |
|---|---|
vlc.exe | main libvlc debug: min period: 1 ms, max period: 1000000 ms
|
vlc.exe | main libvlc debug: configured with ../extras/package/win32/../../../configure '--enable-update-check' '--enable-lua' '--enable-faad' '--enable-flac' '--enable-theora' '--enable-avcodec' '--enable-merge-ffmpeg' '--enable-dca' '--enable-mpc' '--enable-libass' '--enable-schroedinger' '--enable-realrtsp' '--enable-live555' '--enable-dvdread' '--enable-shout' '--enable-goom' '--enable-caca' '--enable-qt' '--enable-skins2' '--enable-sse' '--enable-mmx' '--enable-libcddb' '--enable-zvbi' '--disable-telx' '--enable-nls' '--host=x86_64-w64-mingw32' '--with-breakpad=https://win.crashes.videolan.org' 'host_alias=x86_64-w64-mingw32' 'PKG_CONFIG_LIBDIR=/home/jenkins/workspace/vlc-release/windows/vlc-release-win32-x64/contrib/x86_64-w64-mingw32/lib/pkgconfig'
|
vlc.exe | main libvlc debug: using multimedia timers as clock source
|
vlc.exe | main libvlc debug: VLC media player - 3.0.11 Vetinari
|
vlc.exe | main libvlc debug: revision 3.0.11-0-gdc0c5ced72
|
vlc.exe | main libvlc debug: Copyright © 1996-2020 the VideoLAN team
|
vlc.exe | main libvlc debug: searching plug-in modules
|
vlc.exe | main libvlc debug: loading plugins cache file C:\Program Files\VideoLAN\VLC\plugins\plugins.dat
|
vlc.exe | main libvlc debug: recursively browsing `C:\Program Files\VideoLAN\VLC\plugins'
|
vlc.exe | main libvlc error: stale plugins cache: modified C:\Program Files\VideoLAN\VLC\plugins\access\libaccess_concat_plugin.dll
|