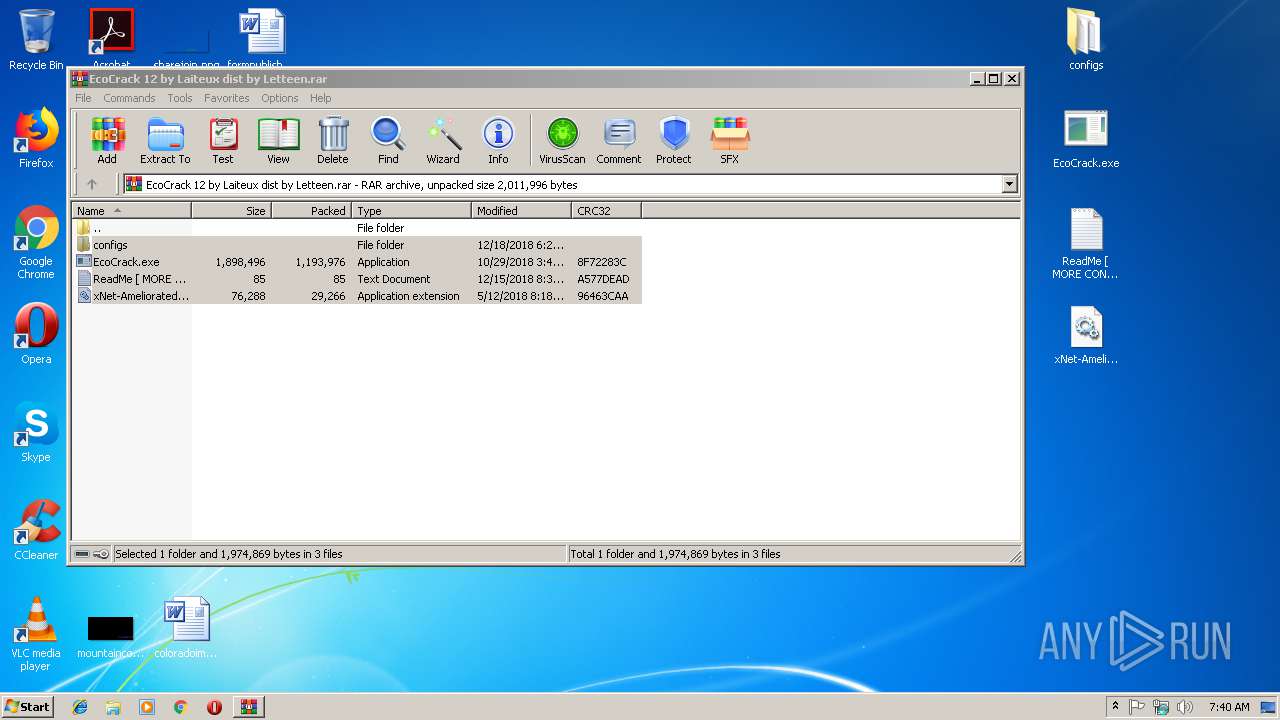
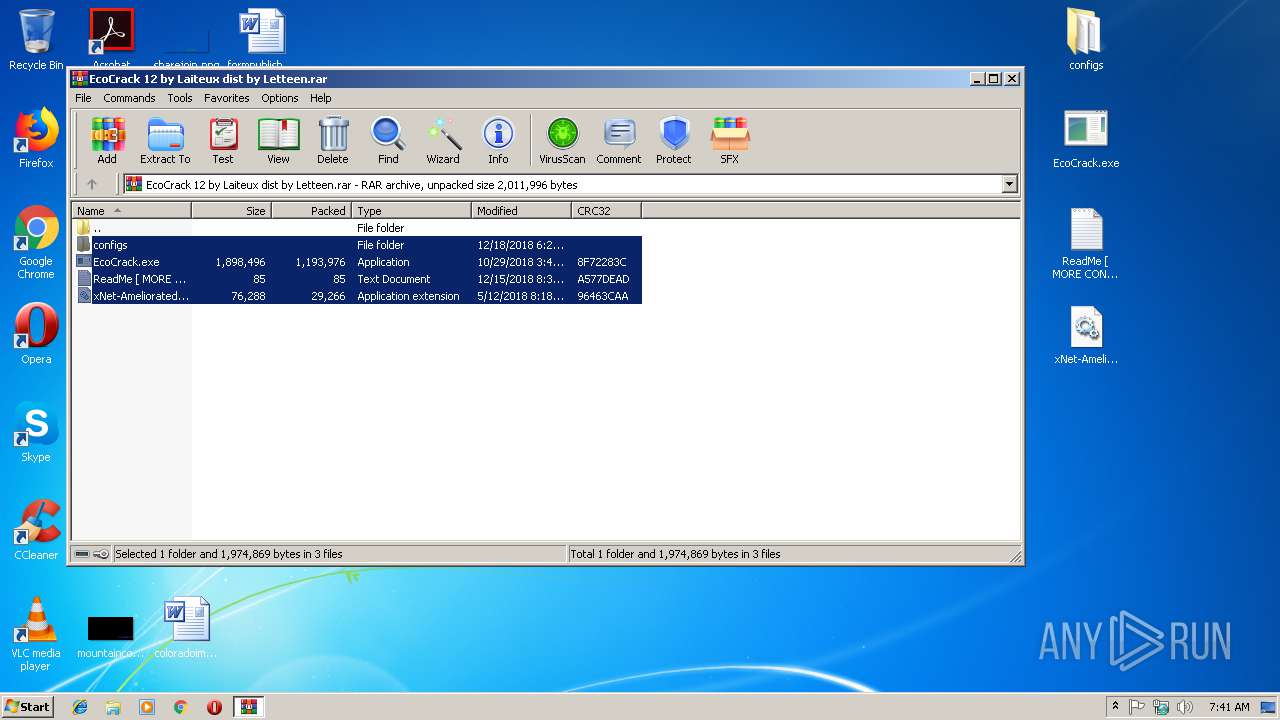
| File name: | EcoCrack 12 by Laiteux dist by Letteen.rar |
| Full analysis: | https://app.any.run/tasks/1e2075f1-accc-4b98-8904-8f6539836ba9 |
| Verdict: | Malicious activity |
| Analysis date: | December 18, 2018, 07:40:17 |
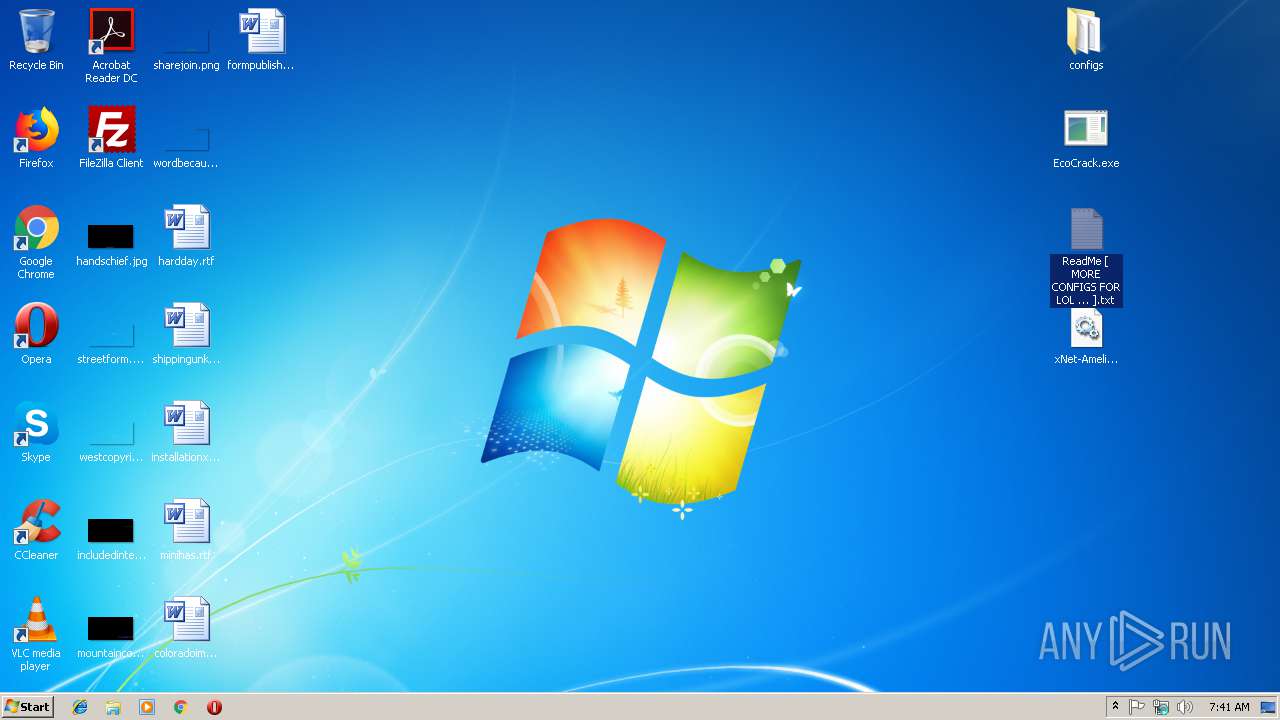
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | B51C69C63D5BE336FBD199F46ABDD14D |
| SHA1: | 046AB02524619EEEDCBEEDF5D9189C4084EE8F7A |
| SHA256: | BDBB7CFE7DC79C03097CBEF77F03CE17CFF91B0FC970A163E76C81DF9B3B0C3D |
| SSDEEP: | 24576:RJ2PnTz0lPD8T/YbrDj2TbIkJ69uFQAhxTT6OP53zeogjRBL:RsPTwh8TQbb2fIko9umATTT6OPNexzL |
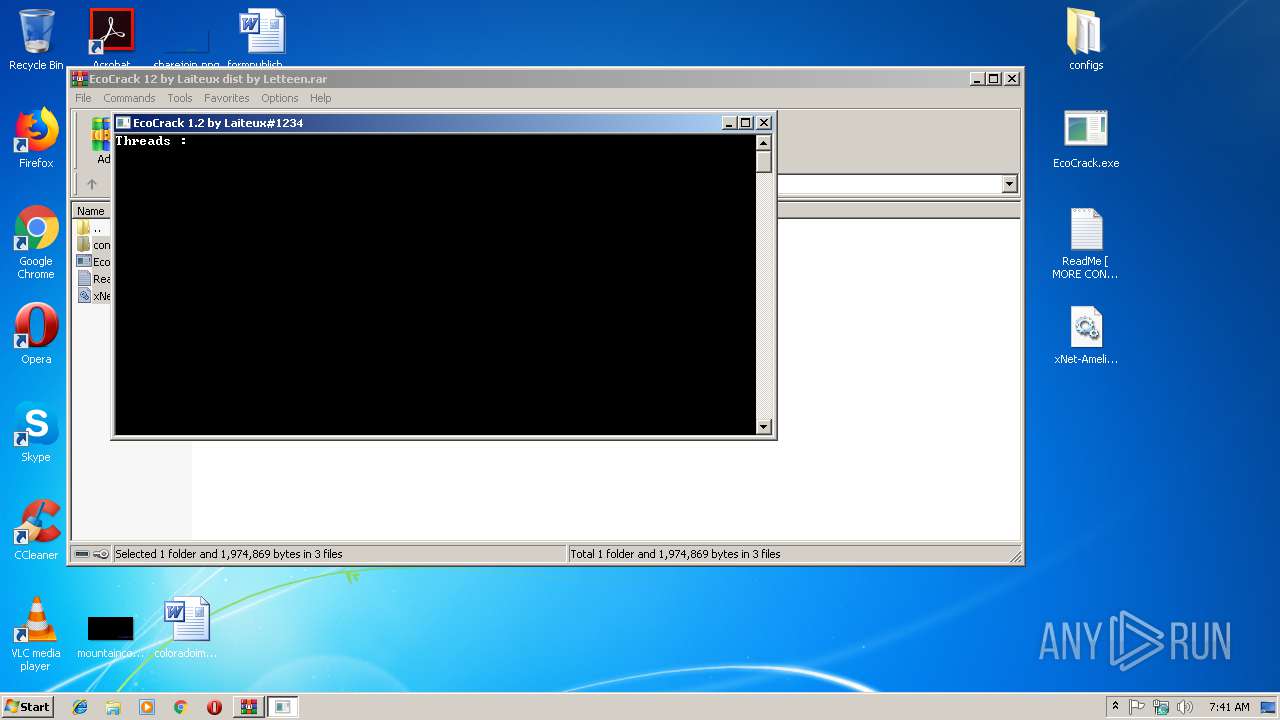
MALICIOUS
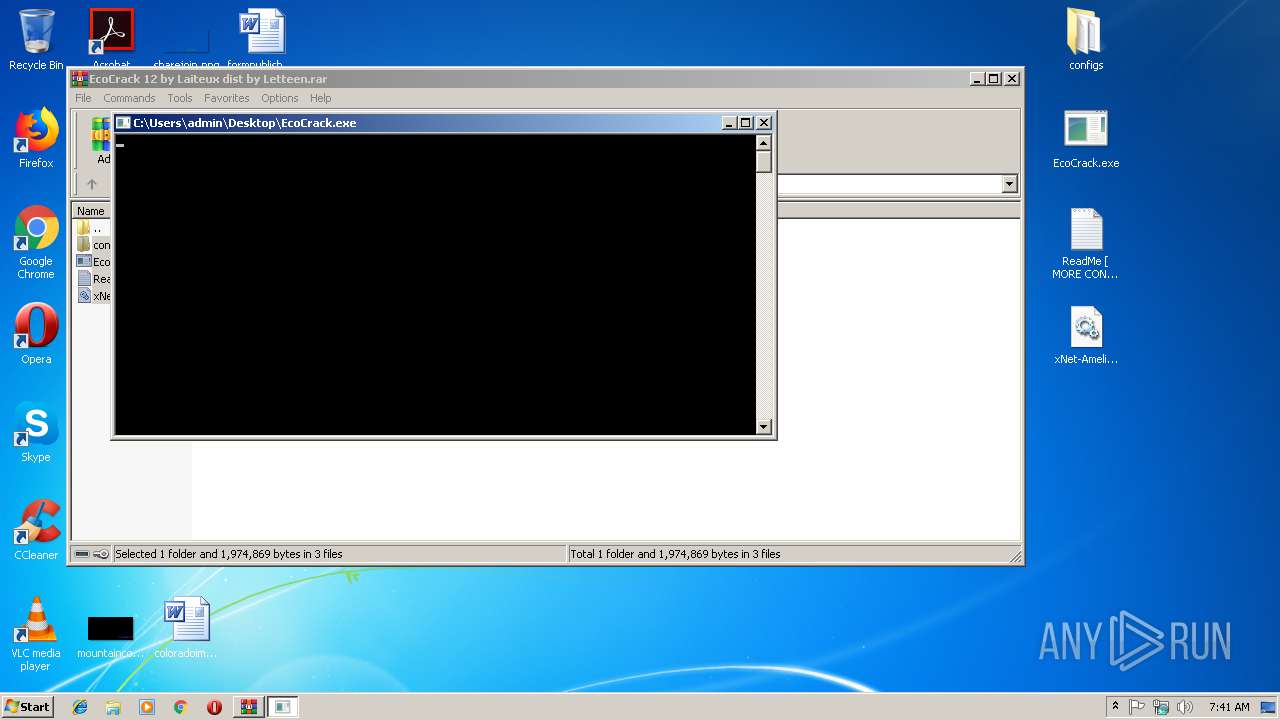
Application was dropped or rewritten from another process
- EcoCrack.exe (PID: 2800)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 1932)
- EcoCrack.exe (PID: 2800)
SUSPICIOUS
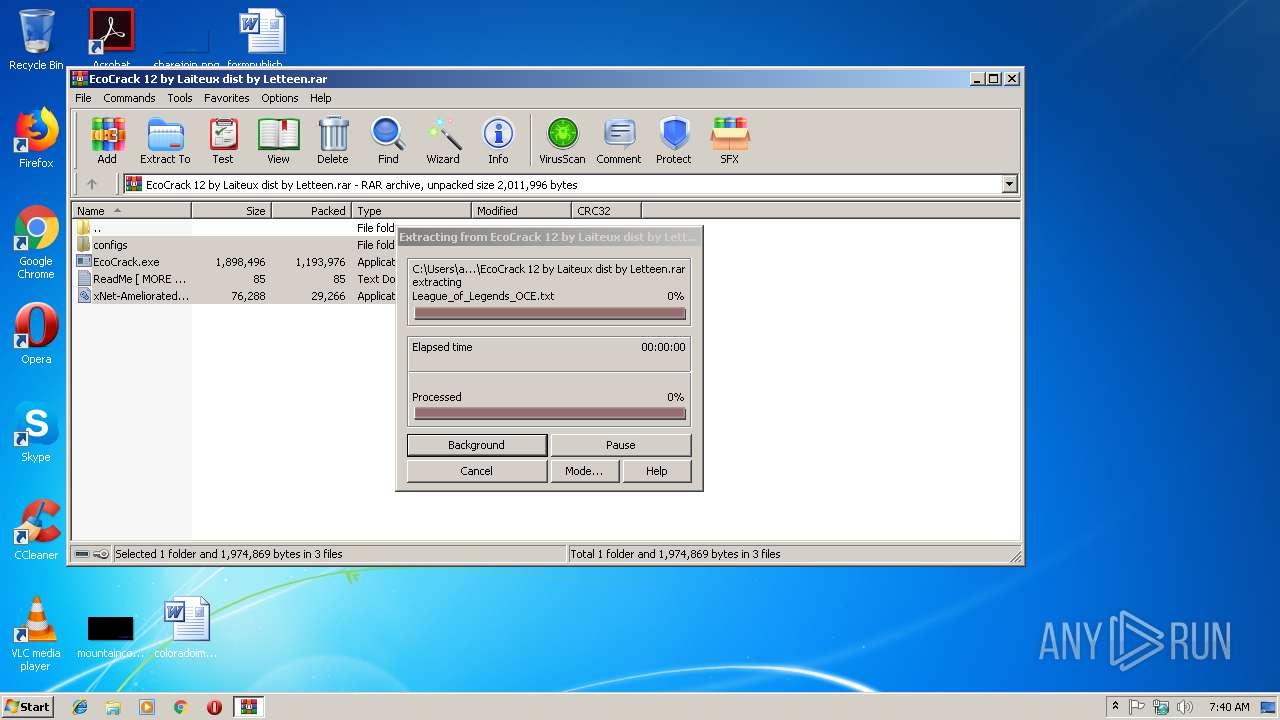
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2708)
Reads Internet Cache Settings
- EcoCrack.exe (PID: 2800)
INFO
Reads internet explorer settings
- iexplore.exe (PID: 2776)
Reads Internet Cache Settings
- iexplore.exe (PID: 2776)
Creates files in the user directory
- opera.exe (PID: 3576)
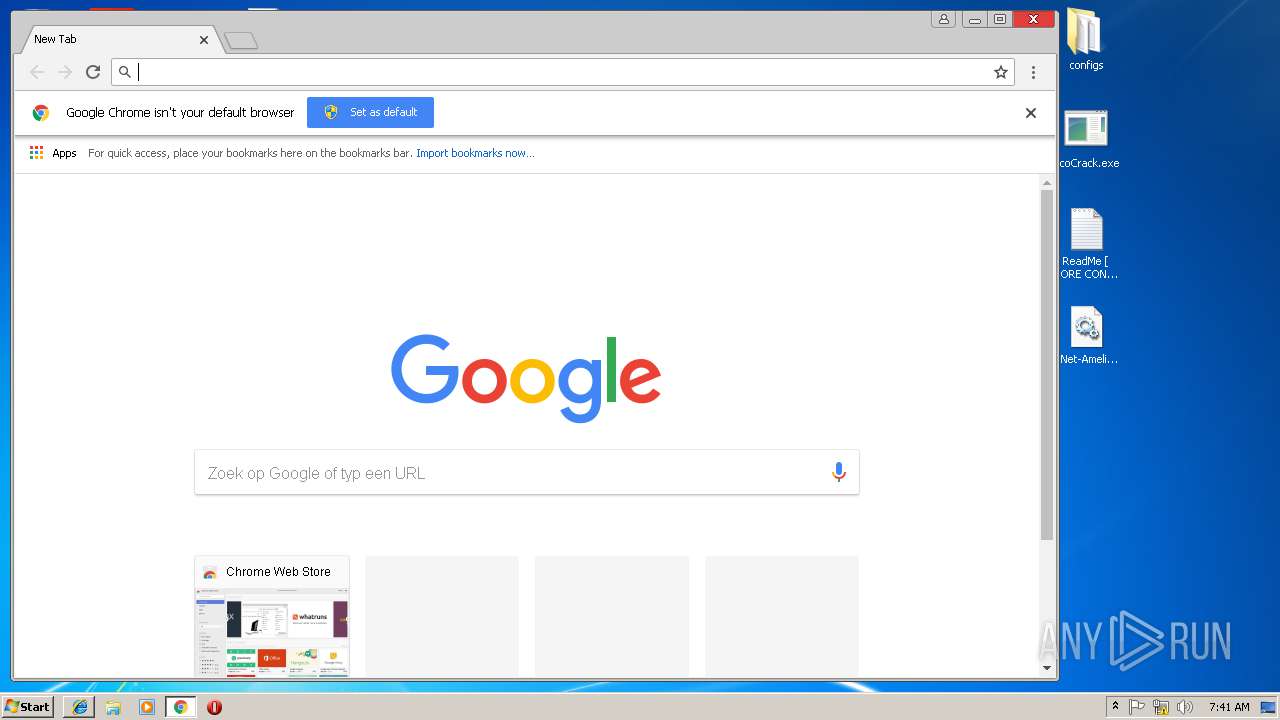
Application launched itself
- chrome.exe (PID: 2508)
- iexplore.exe (PID: 2640)
Reads settings of System Certificates
- chrome.exe (PID: 2508)
Changes internet zones settings
- iexplore.exe (PID: 2640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
50
Monitored processes
16
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1932 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe6_ Global\UsGthrCtrlFltPipeMssGthrPipe6 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2456 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
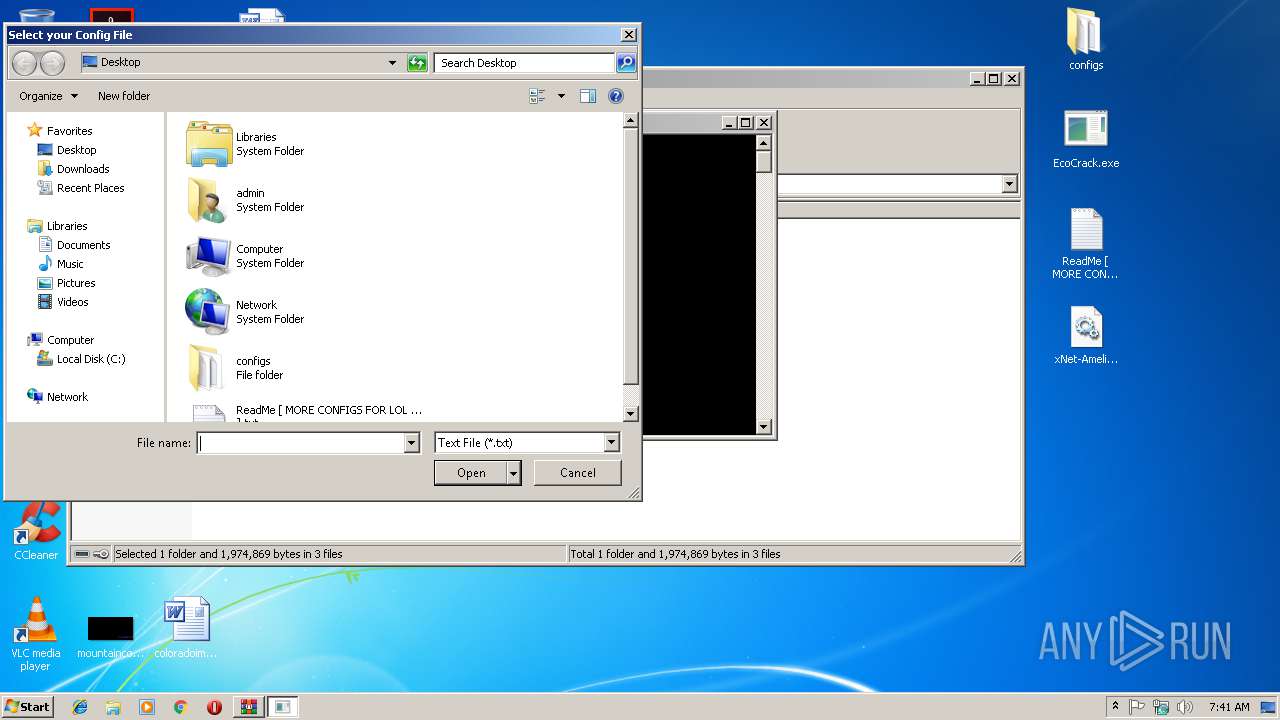
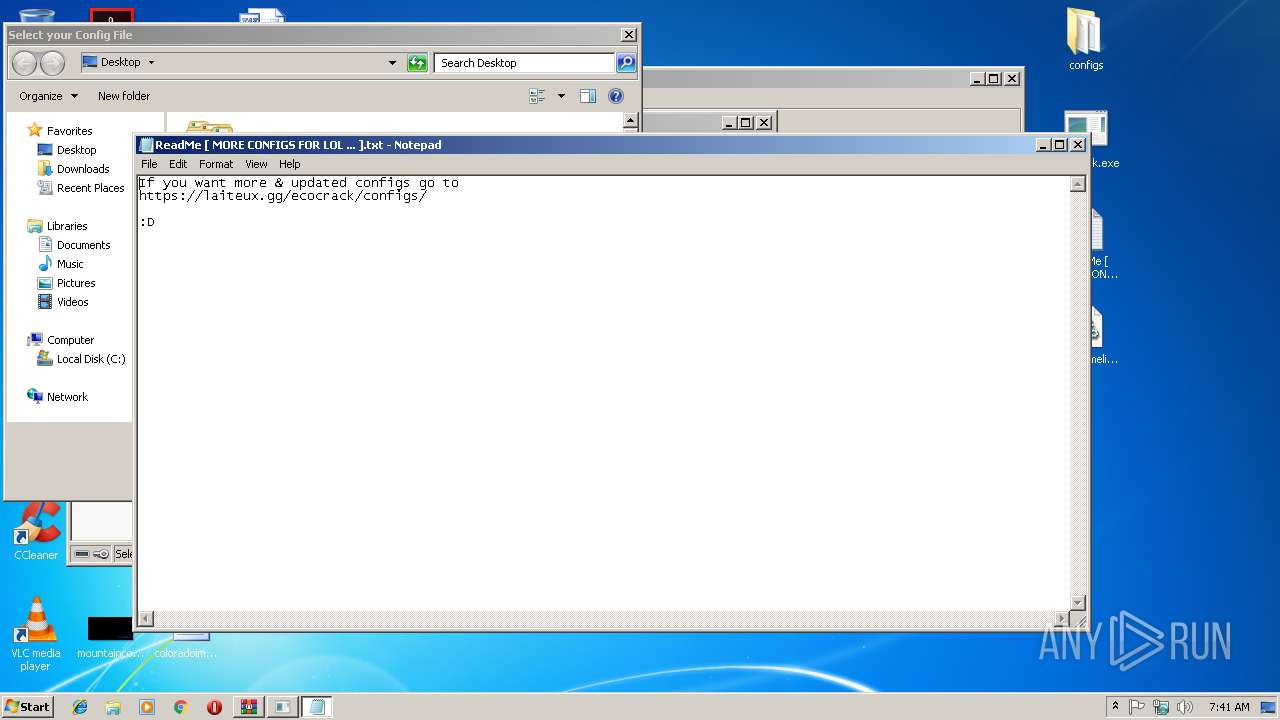
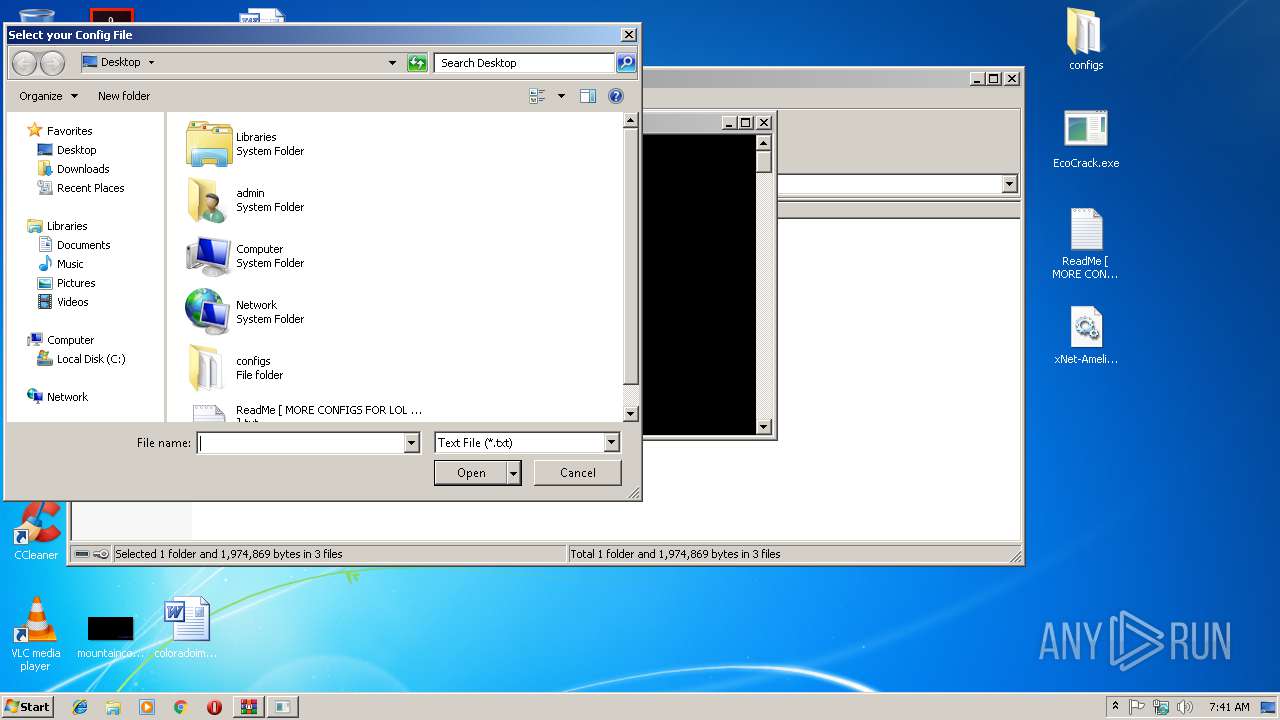
| 2476 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\ReadMe [ MORE CONFIGS FOR LOL ... ].txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f5200b0,0x6f5200c0,0x6f5200cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=880,6635755228321002718,12204616253173706903,131072 --enable-features=PasswordImport --service-pipe-token=9486D031FF2E8DFDB25F291EAC7BB823 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9486D031FF2E8DFDB25F291EAC7BB823 --renderer-client-id=5 --mojo-platform-channel-handle=1904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2640 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
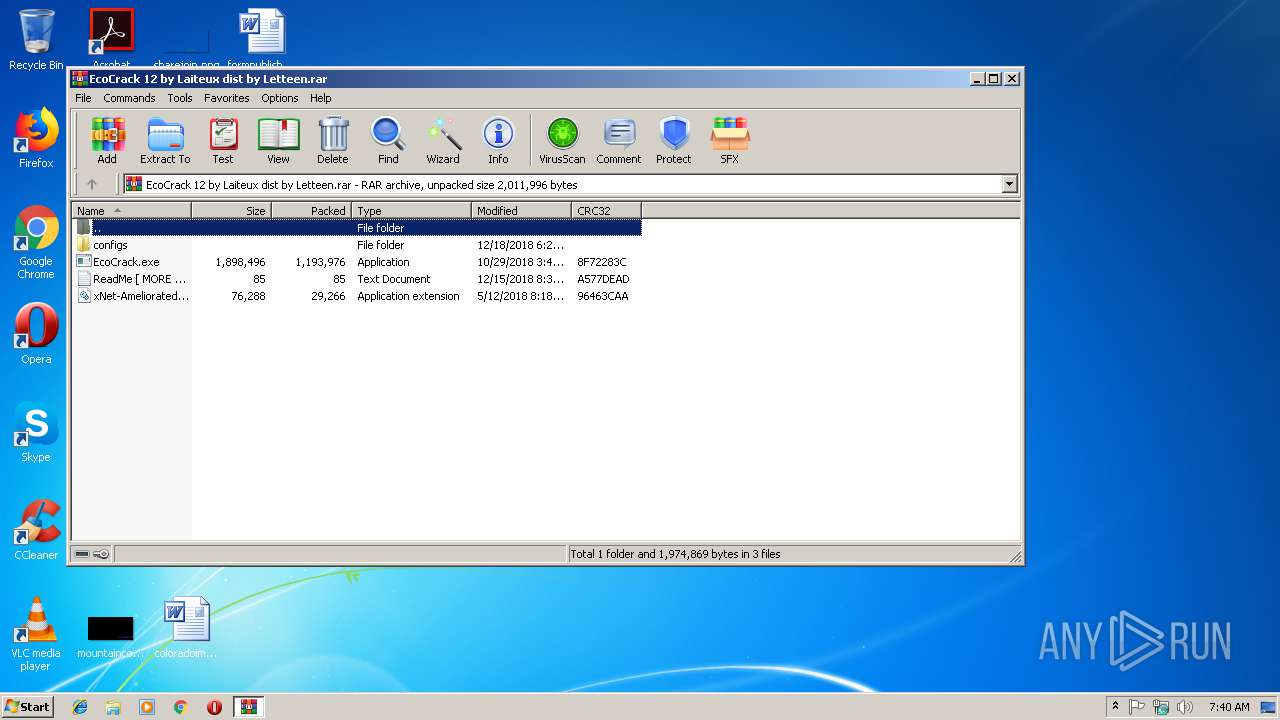
| 2708 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\EcoCrack 12 by Laiteux dist by Letteen.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2776 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2640 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
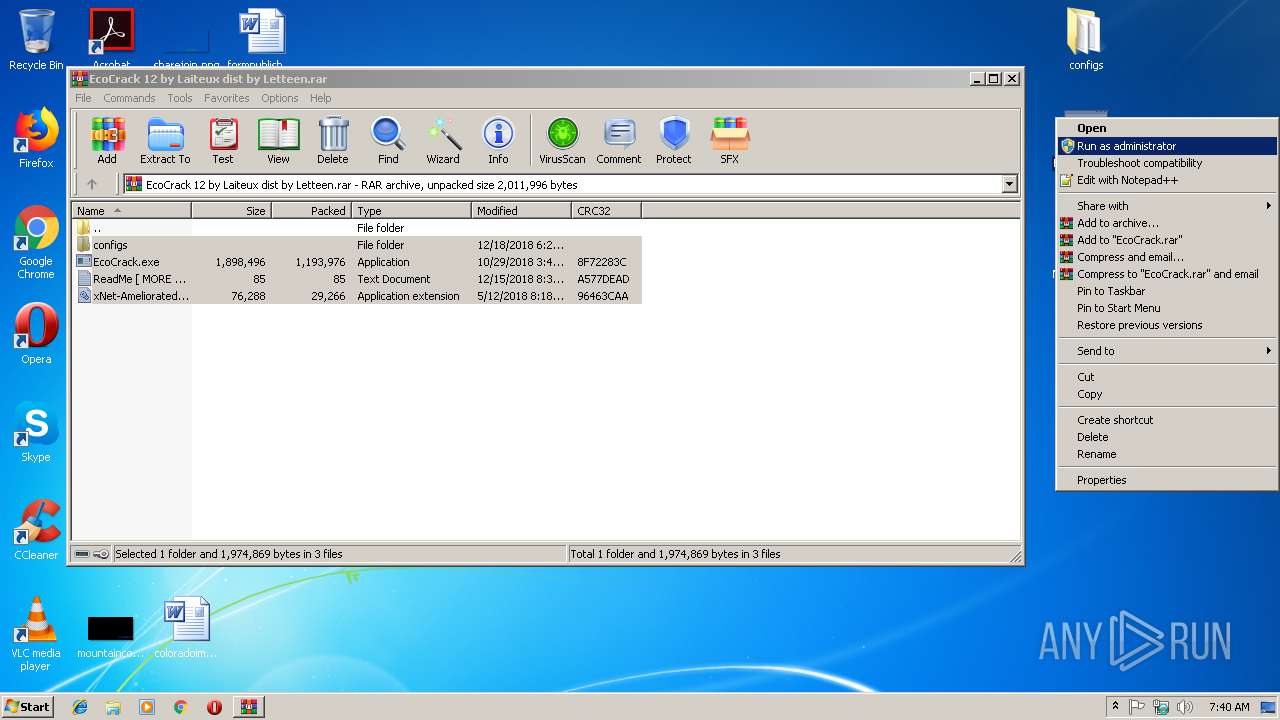
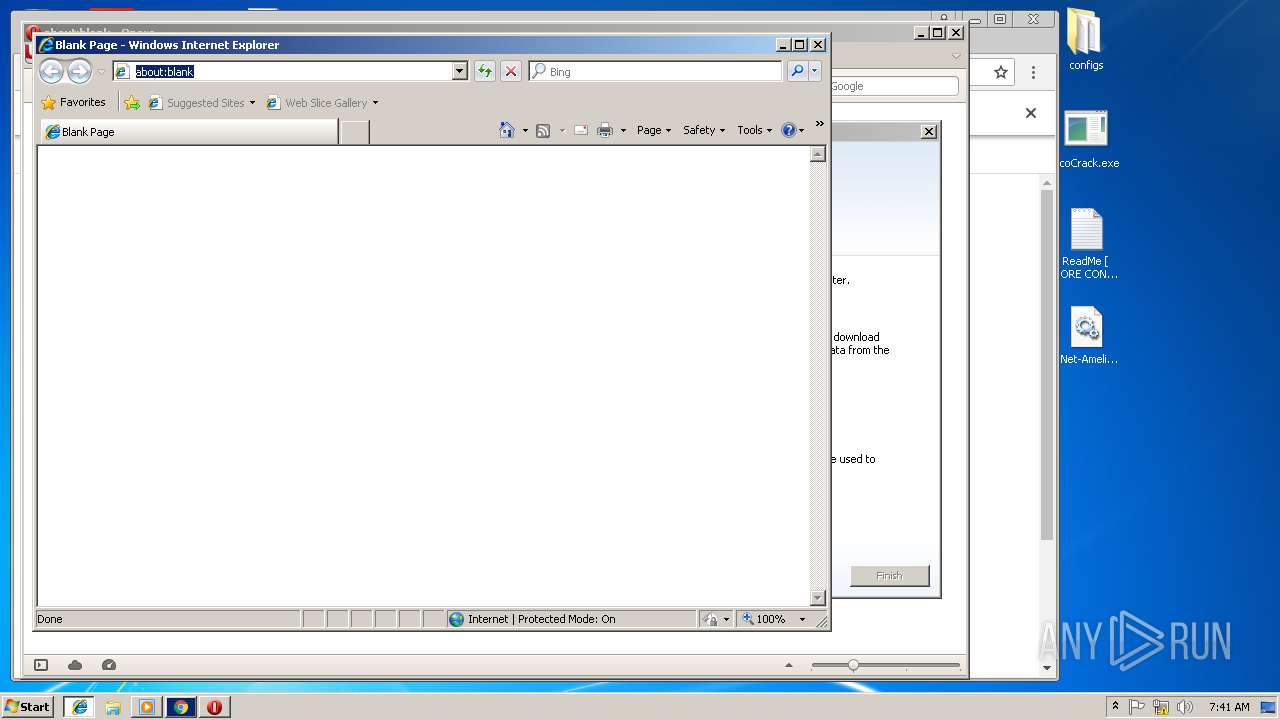
| 2800 | "C:\Users\admin\Desktop\EcoCrack.exe" | C:\Users\admin\Desktop\EcoCrack.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: EcoCrack Exit code: 3221225786 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
2 388
Read events
2 006
Write events
371
Delete events
11
Modification events
| (PID) Process: | (2708) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2708) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2708) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2708) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\EcoCrack 12 by Laiteux dist by Letteen.rar | |||
| (PID) Process: | (2708) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2708) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2708) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2708) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1932) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1932) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
Executable files
2
Suspicious files
75
Text files
121
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
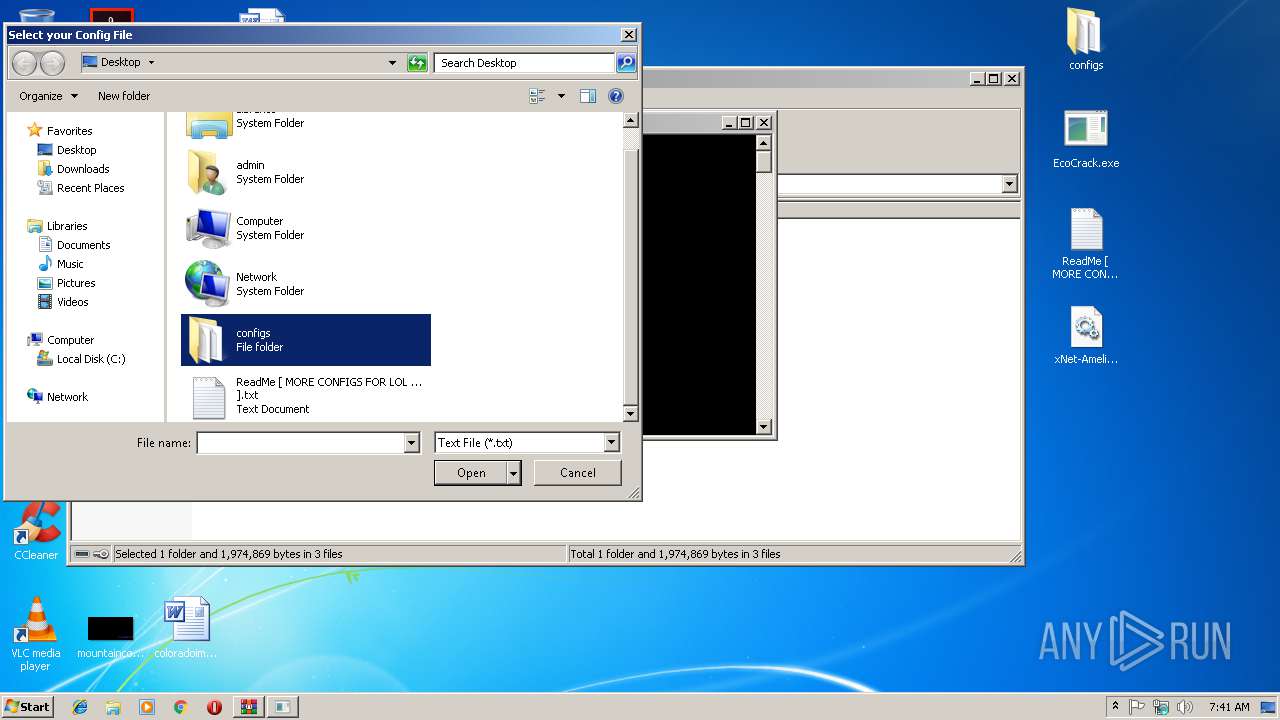
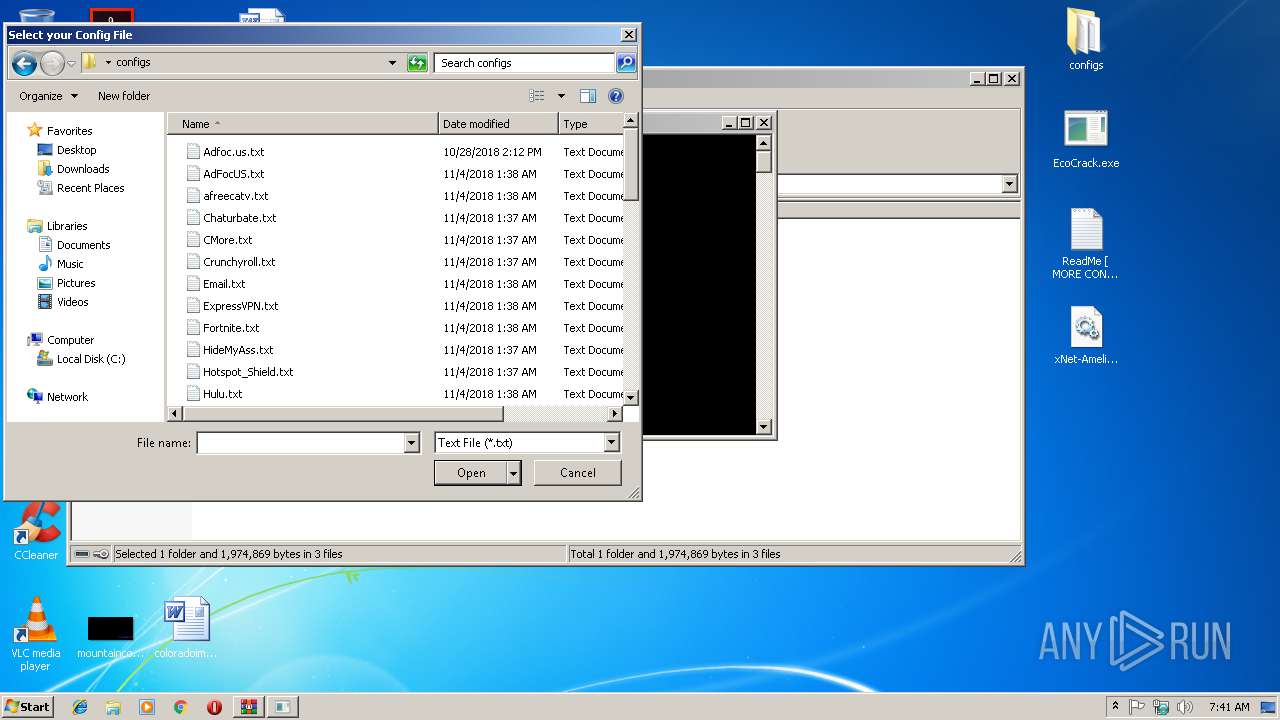
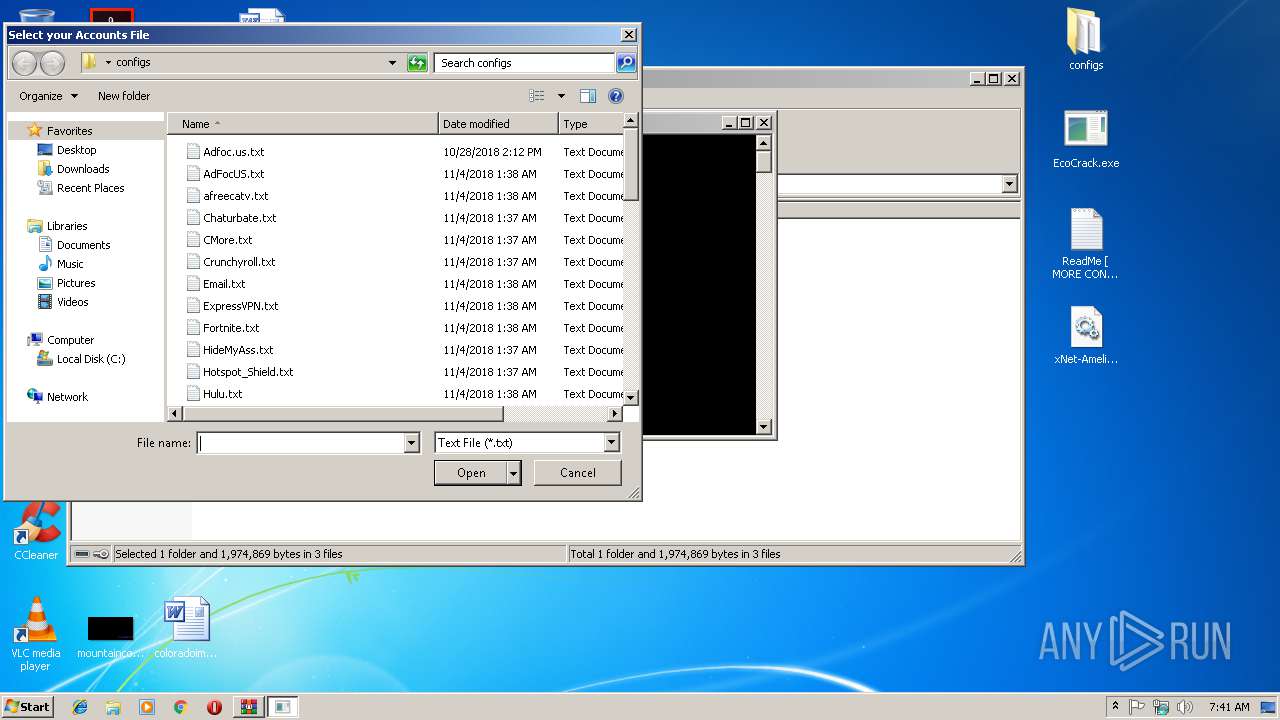
| 2708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2708.35895\configs\AdFocUS.txt | text | |
MD5:— | SHA256:— | |||
| 2708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2708.35895\configs\Email.txt | text | |
MD5:— | SHA256:— | |||
| 2708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2708.35895\configs\Crunchyroll.txt | text | |
MD5:— | SHA256:— | |||
| 2708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2708.35895\configs\IPVanish.txt | text | |
MD5:— | SHA256:— | |||
| 2708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2708.35895\configs\ExpressVPN.txt | text | |
MD5:— | SHA256:— | |||
| 2708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2708.35895\configs\Hotspot_Shield.txt | html | |
MD5:— | SHA256:— | |||
| 2708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2708.35895\configs\afreecatv.txt | text | |
MD5:— | SHA256:— | |||
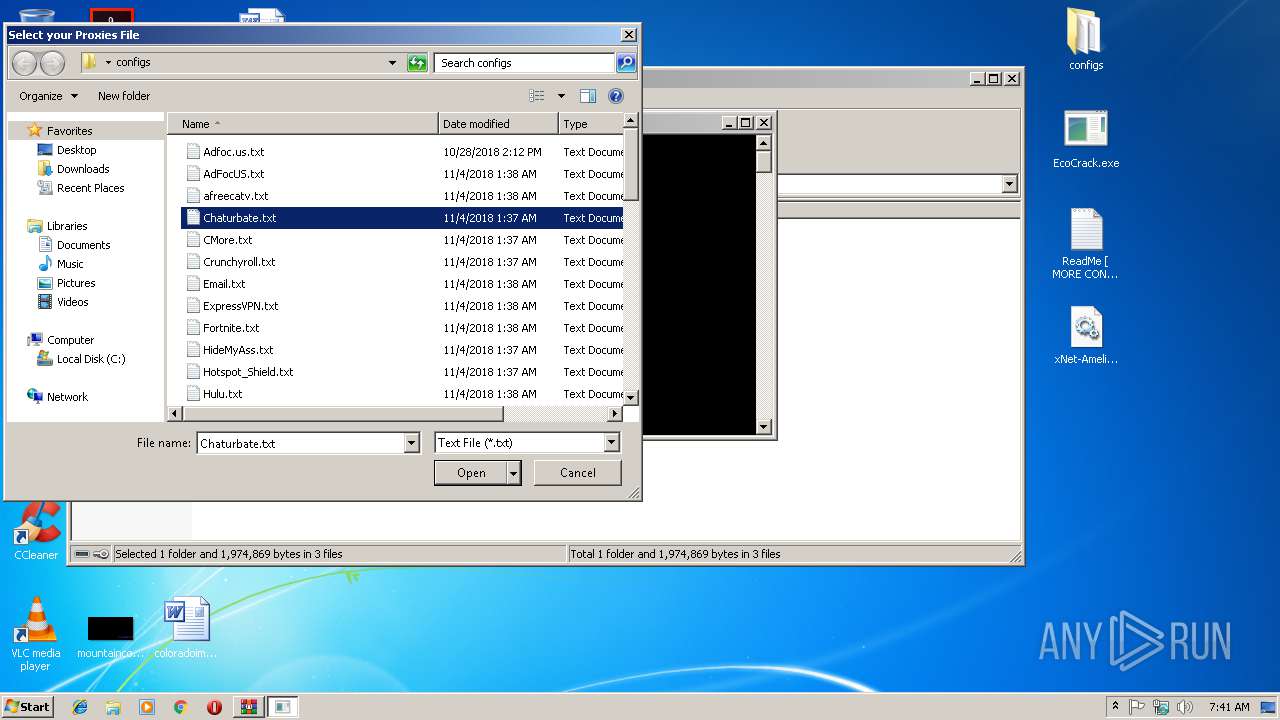
| 2708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2708.35895\configs\Chaturbate.txt | html | |
MD5:— | SHA256:— | |||
| 2708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2708.35895\configs\League_of_Legends_BR.txt | text | |
MD5:— | SHA256:— | |||
| 2708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2708.35895\configs\CMore.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
16
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3576 | opera.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAOXQPQlVpLtFek%2BmcpabOk%3D | US | der | 471 b | whitelisted |
3576 | opera.exe | GET | 200 | 66.225.197.197:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 543 b | whitelisted |
2640 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2800 | EcoCrack.exe | 104.20.209.21:443 | pastebin.com | Cloudflare Inc | US | shared |
2508 | chrome.exe | 216.58.215.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2508 | chrome.exe | 172.217.168.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2508 | chrome.exe | 172.217.168.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
3576 | opera.exe | 82.145.215.40:443 | certs.opera.com | Opera Software AS | — | whitelisted |
2508 | chrome.exe | 172.217.168.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3576 | opera.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3576 | opera.exe | 66.225.197.197:80 | crl4.digicert.com | CacheNetworks, Inc. | US | whitelisted |
2508 | chrome.exe | 172.217.20.100:443 | www.google.com | Google Inc. | US | whitelisted |
2640 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |
www.google.de |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
certs.opera.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |