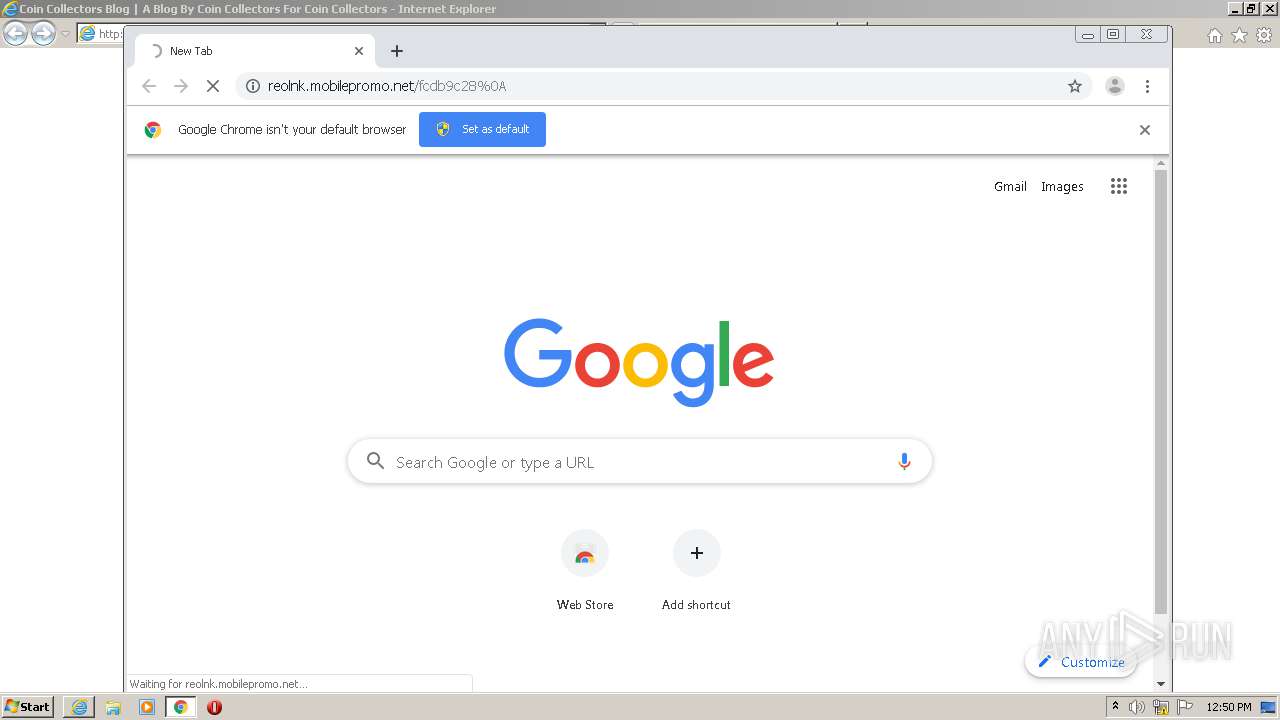
| URL: | http://reolnk.mobilepromo.net/fcdb9c28%0A |
| Full analysis: | https://app.any.run/tasks/28c931fc-64bc-4706-b77c-9add235c59ce |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 11:49:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 260F25753B8181E2828A51039660B76D |
| SHA1: | F2FCAD1B8BF435F78564302EA6B673CDB3161C40 |
| SHA256: | BDB18A98CE99A21C978DD22A5D403B5D407E416C7AB5BAC85B239AAECFCE8AFF |
| SSDEEP: | 3:N1KM8jIAVWLLxACO:CMA3W/xE |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2108)
- iexplore.exe (PID: 1000)
Application launched itself
- iexplore.exe (PID: 2108)
- chrome.exe (PID: 1340)
Changes internet zones settings
- iexplore.exe (PID: 2108)
Reads internet explorer settings
- iexplore.exe (PID: 1000)
Reads settings of System Certificates
- iexplore.exe (PID: 1000)
- chrome.exe (PID: 824)
- iexplore.exe (PID: 2108)
Creates files in the user directory
- iexplore.exe (PID: 1000)
- iexplore.exe (PID: 2108)
Drops Coronavirus (possible) decoy
- iexplore.exe (PID: 1000)
- chrome.exe (PID: 824)
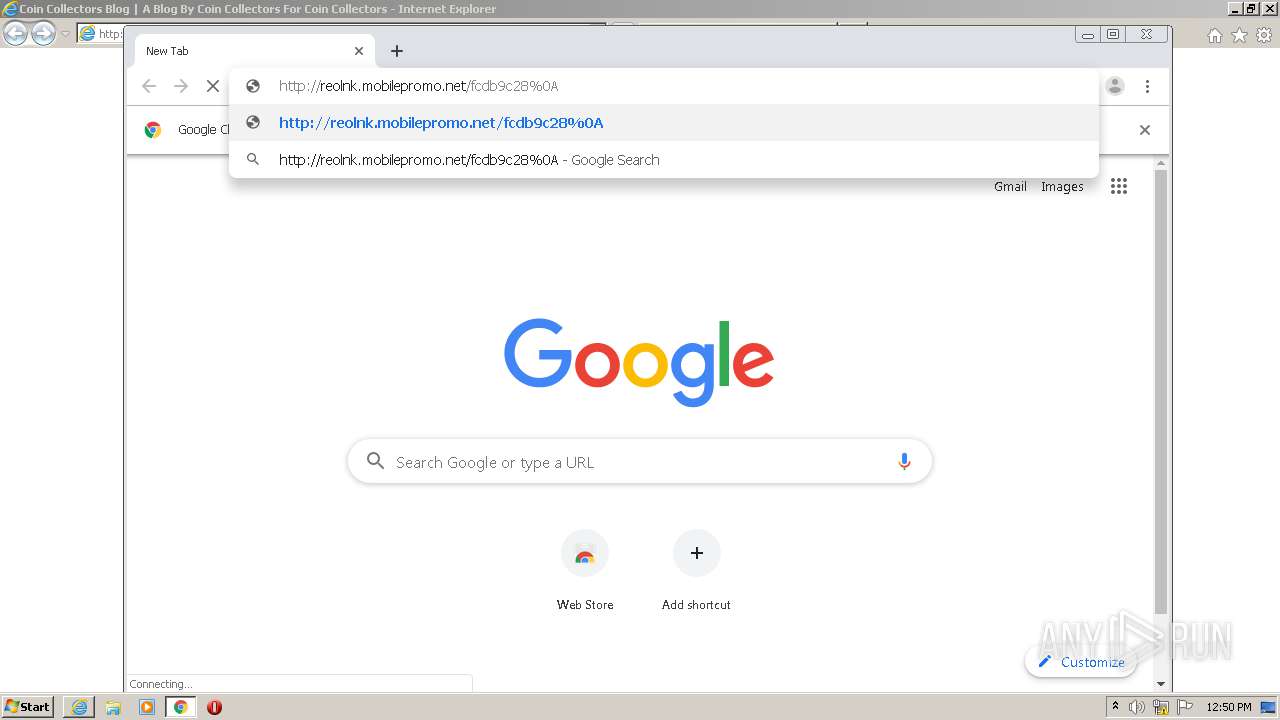
Manual execution by user
- chrome.exe (PID: 1340)
Reads the hosts file
- chrome.exe (PID: 1340)
- chrome.exe (PID: 824)
Changes settings of System certificates
- iexplore.exe (PID: 2108)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2108)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
59
Monitored processes
22
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,11622160035760612008,11365705486677823634,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=2657348416067568748 --mojo-platform-channel-handle=1628 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2108 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,11622160035760612008,11365705486677823634,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7624996072720217045 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3640 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,11622160035760612008,11365705486677823634,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=14083069562453214652 --mojo-platform-channel-handle=2248 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,11622160035760612008,11365705486677823634,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15238041325237916065 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=996,11622160035760612008,11365705486677823634,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=412045404004921044 --mojo-platform-channel-handle=1004 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,11622160035760612008,11365705486677823634,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14359838862284676042 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2520 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Internet Explorer\iexplore.exe" http://reolnk.mobilepromo.net/fcdb9c28%0A | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6c4fa9d0,0x6c4fa9e0,0x6c4fa9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 545
Read events
1 392
Write events
145
Delete events
8
Modification events
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 717042224 | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30844631 | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
130
Text files
225
Unknown types
61
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2108 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1000 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab5FE7.tmp | — | |
MD5:— | SHA256:— | |||
| 1000 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar5FE8.tmp | — | |
MD5:— | SHA256:— | |||
| 1000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\9FF67FB3141440EED32363089565AE60_6A95412D7942FF87C0DCC4EDDDB99B12 | binary | |
MD5:— | SHA256:— | |||
| 1000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9FF67FB3141440EED32363089565AE60_CCA7004767E1683D2CB9E3AFFE820C28 | der | |
MD5:— | SHA256:— | |||
| 1000 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\css[3].css | text | |
MD5:— | SHA256:— | |||
| 1000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:— | SHA256:— | |||
| 1000 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\css[2].css | text | |
MD5:— | SHA256:— | |||
| 1000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 1000 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\ZC84C5Q7.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
135
TCP/UDP connections
201
DNS requests
127
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
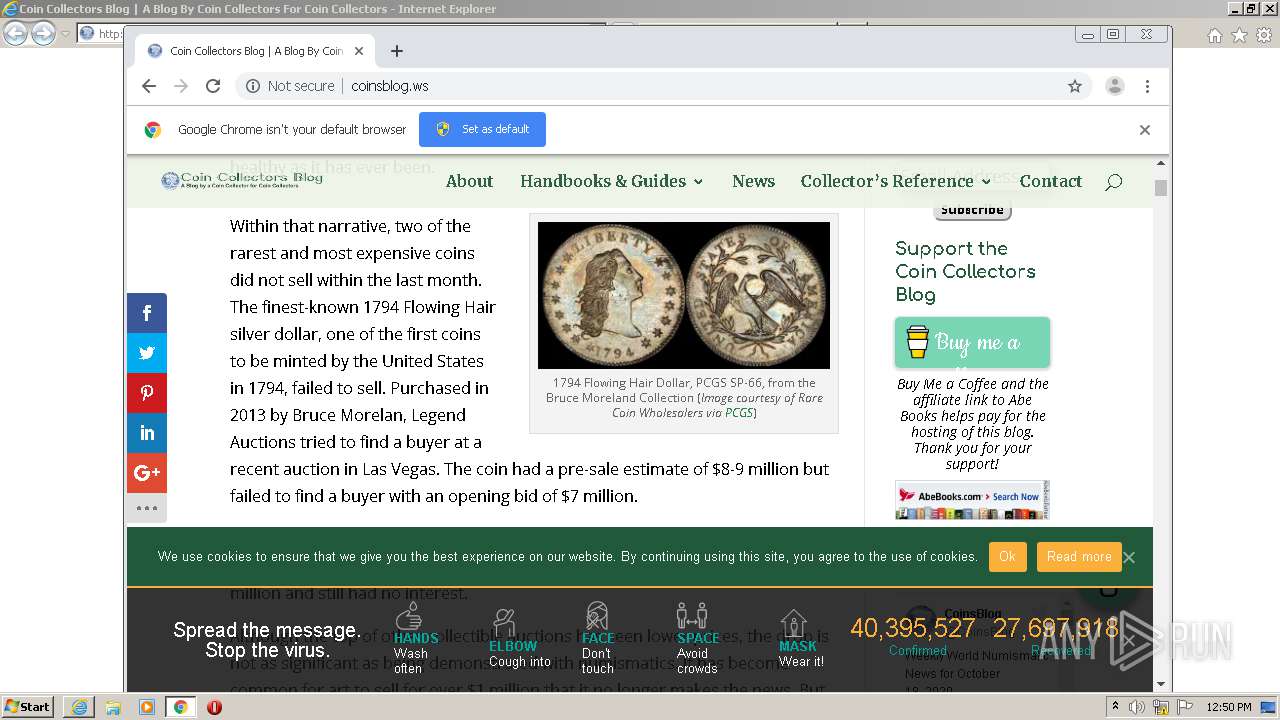
1000 | iexplore.exe | GET | 302 | 34.95.127.121:80 | http://www.ojrq.net/p/?return=http%3A%2F%2Faffiliates.abebooks.com%2Fi%2F394814%2F76930%2F2029%3Flevel%3D1%26srcref%3Dhttp%253A%252F%252Fcoinsblog.ws%252F&cid=2029&tpsync=no | US | — | — | whitelisted |
1000 | iexplore.exe | GET | 200 | 172.217.16.138:80 | http://fonts.googleapis.com/css?family=Open+Sans:300italic,400italic,600italic,700italic,800italic,400,300,600,700,800&subset=latin,latin-ext&display=swap | US | text | 394 b | whitelisted |
1000 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
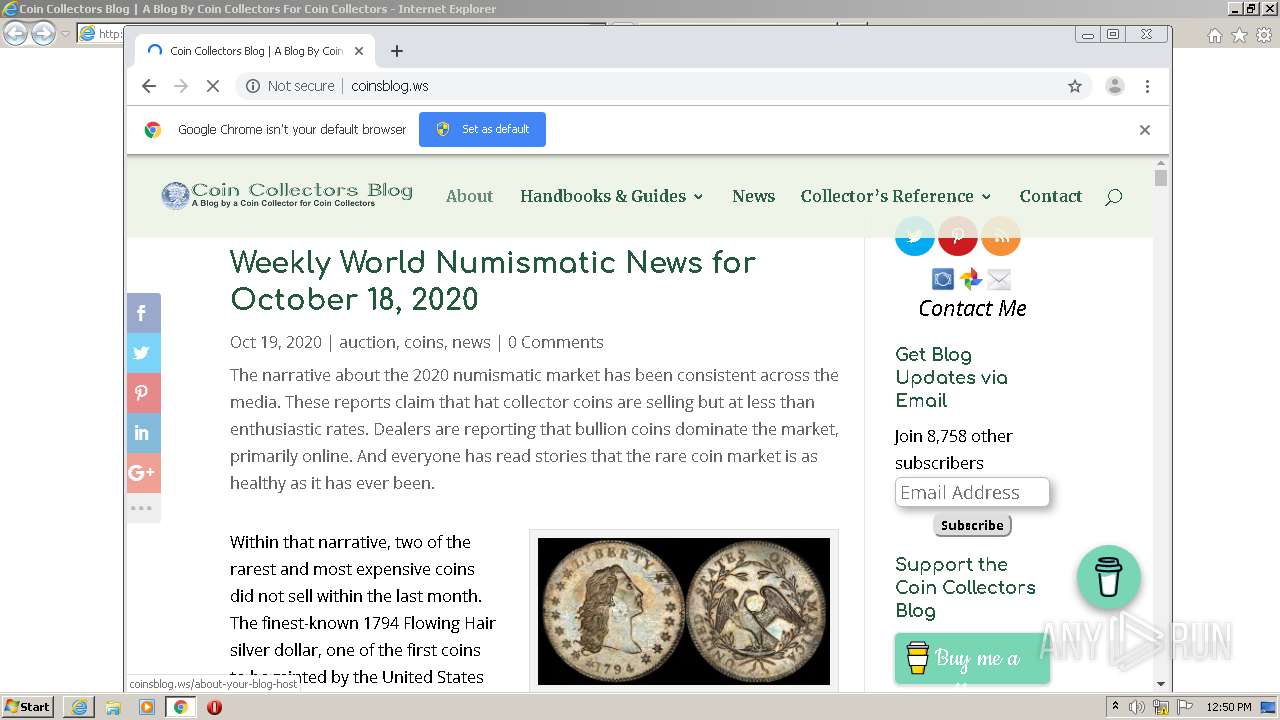
1000 | iexplore.exe | GET | 200 | 162.0.235.113:80 | http://reolnk.mobilepromo.net/fcdb9c28%0A | CA | html | 4.08 Kb | suspicious |
1000 | iexplore.exe | GET | 302 | 35.244.197.23:80 | http://affiliates.abebooks.com/i/394814/76930/2029 | US | html | 211 b | unknown |
1000 | iexplore.exe | GET | 200 | 99.86.2.112:80 | http://a.impactradius-go.com/display-ad/2029-76930 | US | image | 6.83 Kb | whitelisted |
1000 | iexplore.exe | GET | 302 | 192.64.119.175:80 | http://twittercounter.com/embed/coinsblog/ffffff/111111 | US | html | 89 b | whitelisted |
1000 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
1000 | iexplore.exe | GET | 200 | 172.217.16.138:80 | http://fonts.googleapis.com/css?family=Open+Sans:400,700 | US | text | 232 b | whitelisted |
1000 | iexplore.exe | GET | 200 | 172.217.16.138:80 | http://fonts.googleapis.com/css?family=Comfortaa:300,regular,700|Merriweather:300,300italic,regular,italic,700,700italic,900,900italic&subset=latin-ext,greek,vietnamese,cyrillic,latin,cyrillic-ext&display=swap | US | text | 436 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
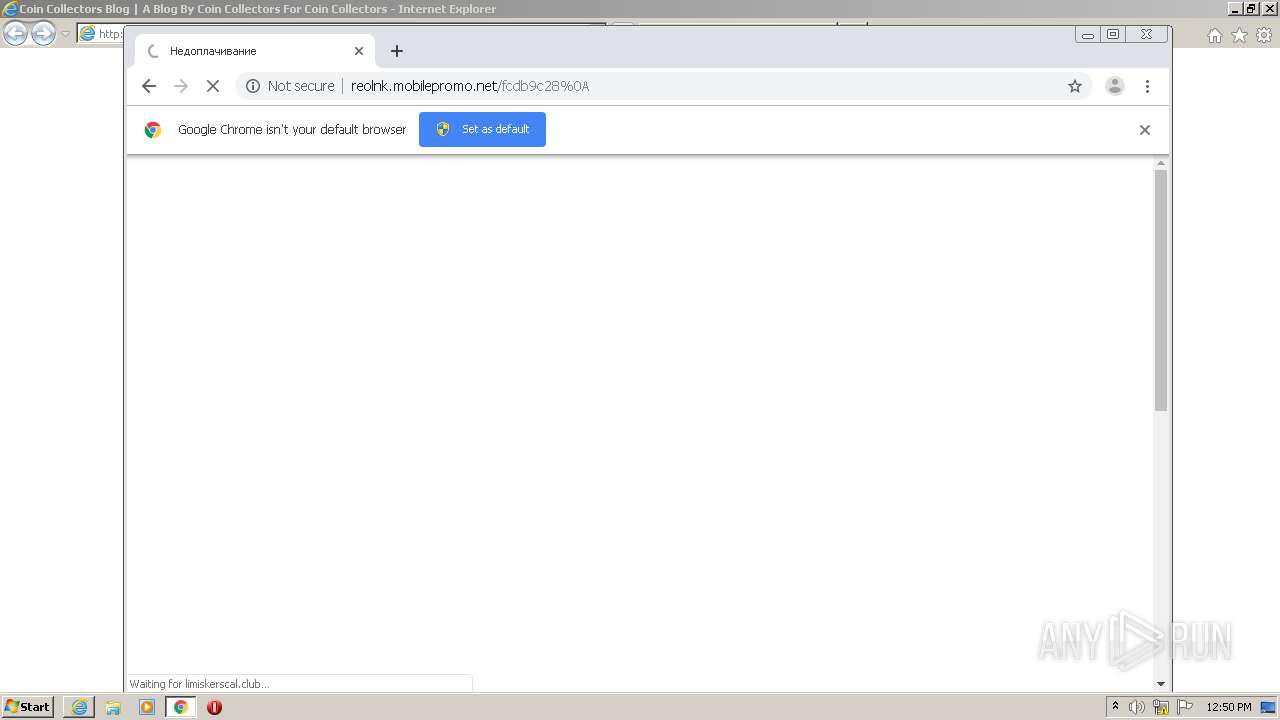
1000 | iexplore.exe | 162.0.235.113:80 | reolnk.mobilepromo.net | AirComPlus Inc. | CA | suspicious |
2108 | iexplore.exe | 162.0.235.113:80 | reolnk.mobilepromo.net | AirComPlus Inc. | CA | suspicious |
1000 | iexplore.exe | 104.27.162.220:443 | limiskerscal.club | Cloudflare Inc | US | shared |
2108 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1000 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1000 | iexplore.exe | 74.208.236.74:80 | coinsblog.ws | 1&1 Internet SE | US | malicious |
1000 | iexplore.exe | 172.217.16.138:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1000 | iexplore.exe | 104.75.88.209:80 | assets.pinterest.com | Akamai Technologies, Inc. | NL | malicious |
1000 | iexplore.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
1000 | iexplore.exe | 192.0.77.2:443 | i2.wp.com | Automattic, Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
reolnk.mobilepromo.net |
| unknown |
limiskerscal.club |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
coinsblog.ws |
| suspicious |
c0.wp.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
assets.pinterest.com |
| whitelisted |
cdnjs.buymeacoffee.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Suspicious Domain Request for Possible COVID-19 Domain M2 |
1000 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 Domain M2 |
1000 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M2 |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Suspicious Domain Request for Possible COVID-19 Domain M2 |
824 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 Domain M2 |
824 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M2 |
824 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
2108 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
1000 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
1000 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |