| download: | vcard_setup.exe |
| Full analysis: | https://app.any.run/tasks/de415a53-f238-4245-a5cd-cd3d55076bd8 |
| Verdict: | Malicious activity |
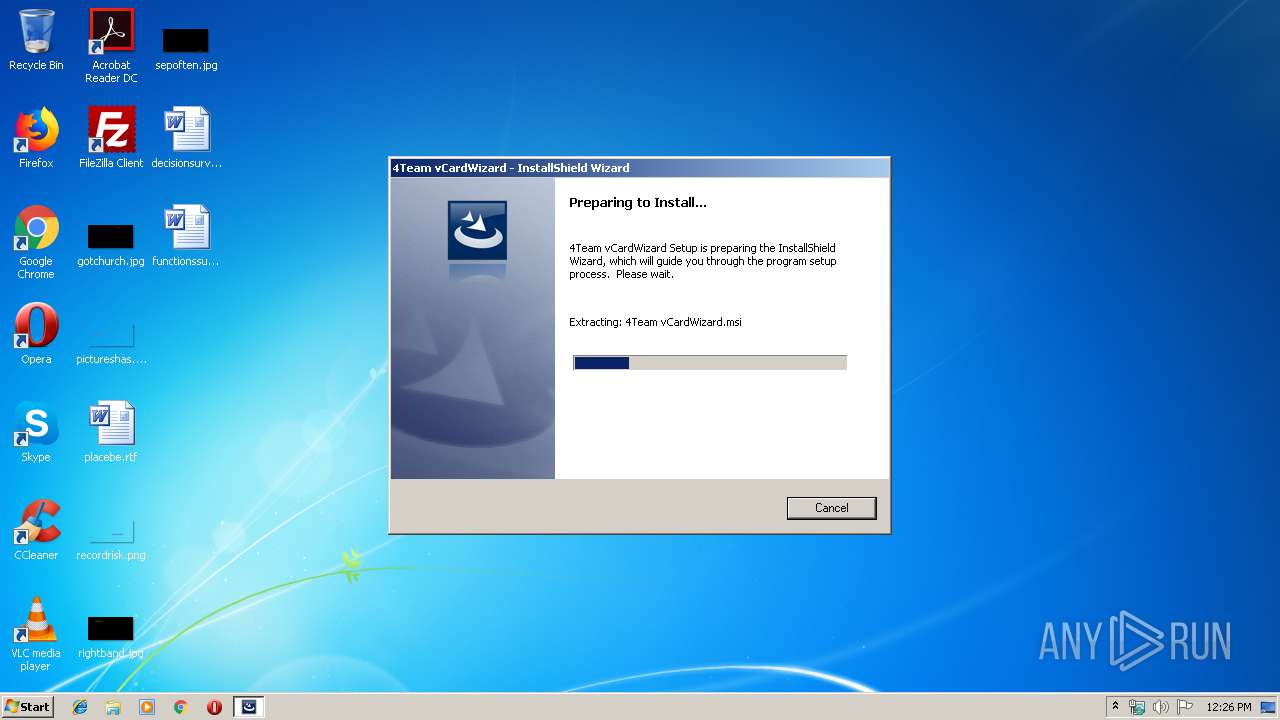
| Analysis date: | December 06, 2019, 12:26:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | CD5DEF86E5ECBD9C928BCFC3F337C4F9 |
| SHA1: | 26F3A18A0923ECDF2F21227F8DEBE8E11F0748B6 |
| SHA256: | BDA8BC02EF40459968EC8C4A350F1482C040BE8A6A19BE82E310F07681FEF0B9 |
| SSDEEP: | 393216:8Se1EjGh8fPiJz/rLsamjBzWCMyvXcKzgN:8fR8ULroamBMy/zE |
MALICIOUS
Loads dropped or rewritten executable
- vcard_setup.exe (PID: 3532)
- vCardWizardApp.exe (PID: 1152)
- 4Team-Updater.exe (PID: 2156)
Application was dropped or rewritten from another process
- vcardwizard_setup_423_x86.exe (PID: 2716)
- vCardWizardLauncher.exe (PID: 2076)
- vCardWizardLauncher.exe (PID: 776)
- vCardWizardApp.exe (PID: 1152)
- 4Team-Updater.exe (PID: 2156)
SUSPICIOUS
Executable content was dropped or overwritten
- vcard_setup.exe (PID: 3532)
- msiexec.exe (PID: 3424)
- 4Team-Updater.exe (PID: 2156)
Executed as Windows Service
- vssvc.exe (PID: 2184)
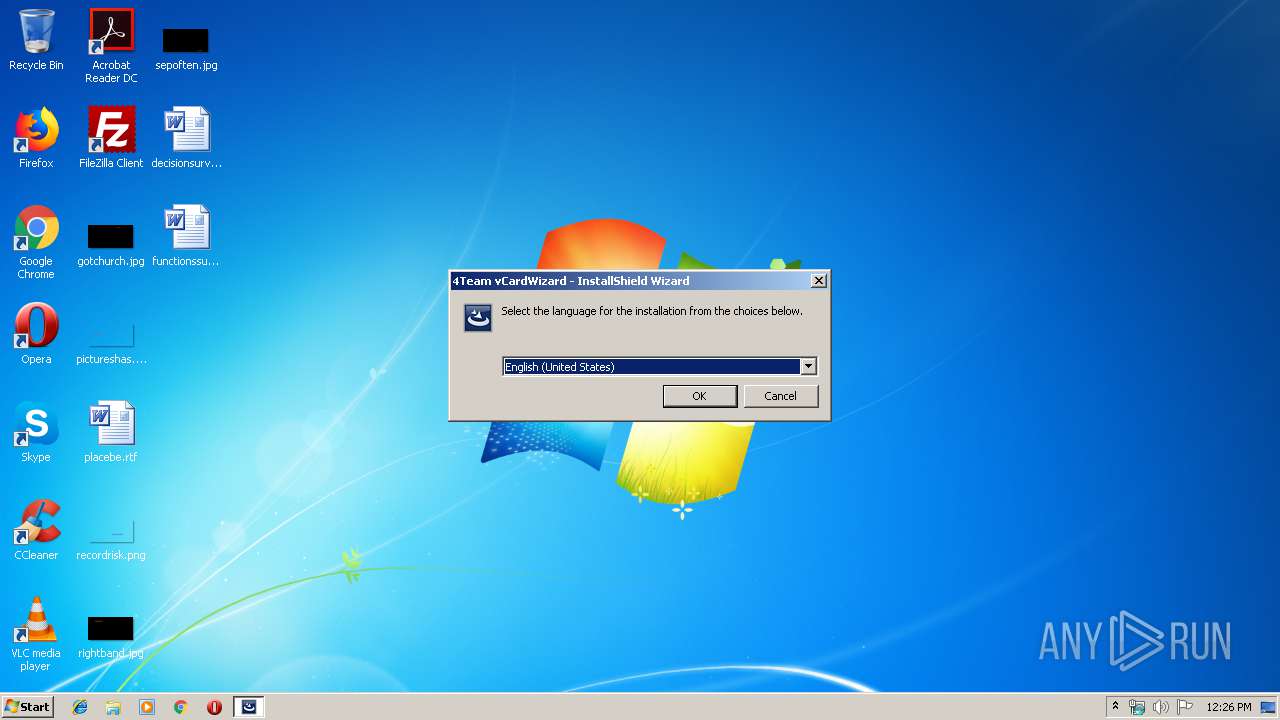
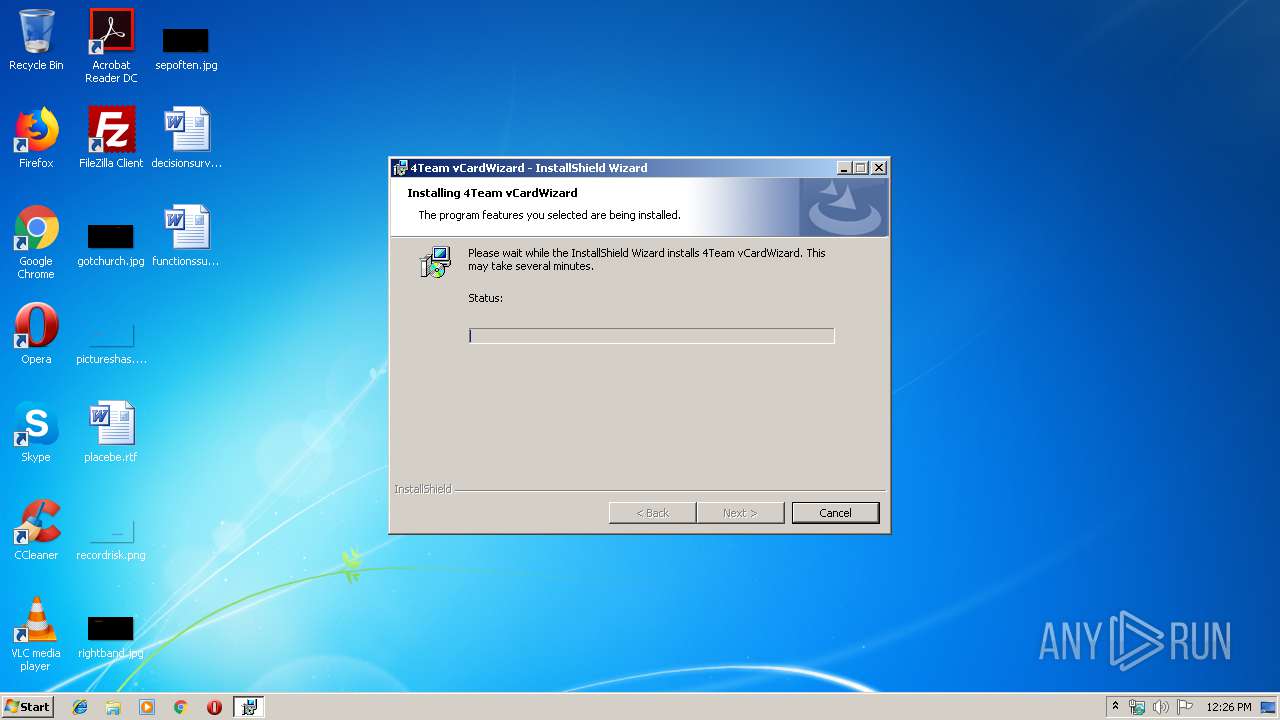
Starts Microsoft Installer
- vcardwizard_setup_423_x86.exe (PID: 2716)
Creates files in the Windows directory
- msiexec.exe (PID: 3424)
Creates files in the user directory
- msiexec.exe (PID: 3424)
- vCardWizardApp.exe (PID: 1152)
- 4Team-Updater.exe (PID: 2156)
Creates COM task schedule object
- msiexec.exe (PID: 3424)
- MsiExec.exe (PID: 3816)
Reads Microsoft Outlook installation path
- MsiExec.exe (PID: 3816)
- vCardWizardApp.exe (PID: 1152)
Creates files in the program directory
- 4Team-Updater.exe (PID: 2156)
INFO
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2332)
- MsiExec.exe (PID: 3816)
- MsiExec.exe (PID: 2916)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2184)
Searches for installed software
- msiexec.exe (PID: 3424)
Application launched itself
- msiexec.exe (PID: 3424)
Starts application with an unusual extension
- msiexec.exe (PID: 3424)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 3424)
Creates a software uninstall entry
- msiexec.exe (PID: 3424)
Reads Microsoft Office registry keys
- vCardWizardApp.exe (PID: 1152)
Creates files in the program directory
- msiexec.exe (PID: 3424)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:02 05:20:05+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 120320 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30fb |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.23.0.236 |
| ProductVersionNumber: | 4.23.0.236 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
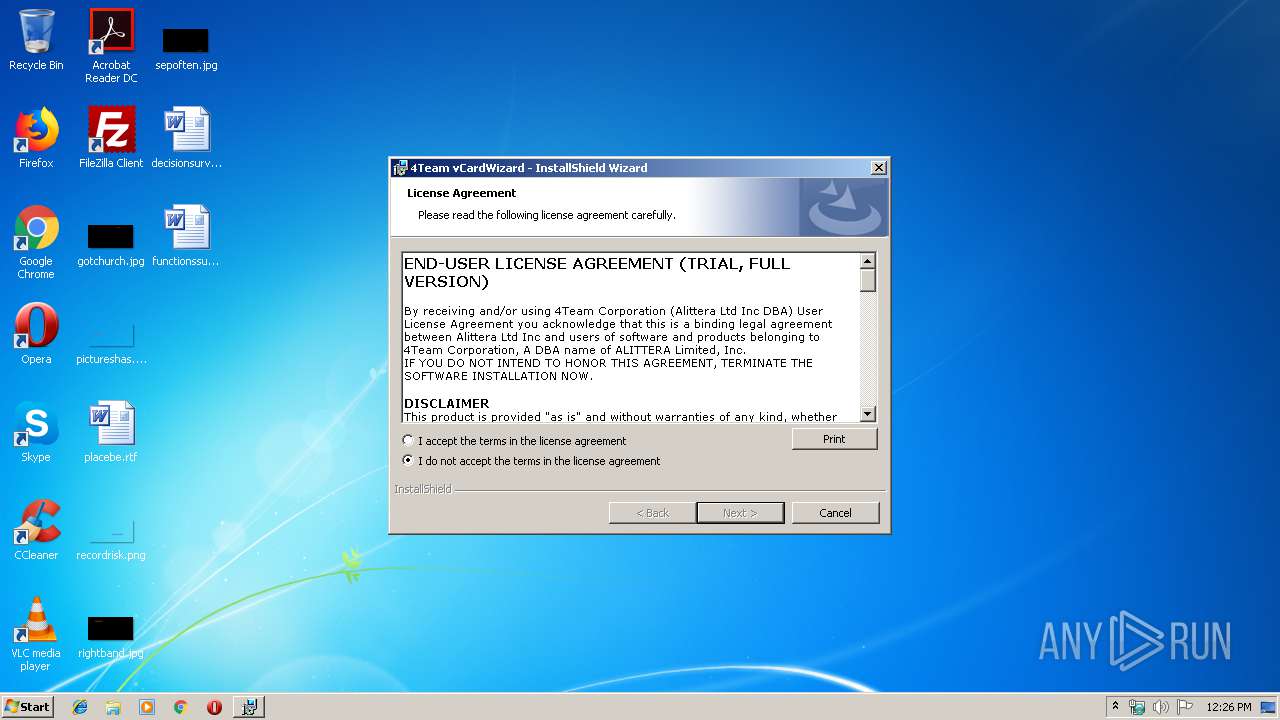
| Comments: | 4Team vCardWizard Setup |
| CompanyName: | 4Team Corporation |
| FileDescription: | 4Team vCardWizard Setup |
| FileVersion: | 4.23.0236 |
| LegalCopyright: | © 4Team Corporation |
| ProductName: | 4Team vCardWizard |
| ProductVersion: | 4.23.0236 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Apr-2016 03:20:05 |
| Detected languages: |
|
| Comments: | 4Team vCardWizard Setup |
| CompanyName: | 4Team Corporation |
| FileDescription: | 4Team vCardWizard Setup |
| FileVersion: | 4.23.0236 |
| LegalCopyright: | © 4Team Corporation |
| ProductName: | 4Team vCardWizard |
| ProductVersion: | 4.23.0236 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 02-Apr-2016 03:20:05 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005AEB | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.42231 |
.rdata | 0x00007000 | 0x00001196 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.20292 |
.data | 0x00009000 | 0x0001B038 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.04751 |
.ndata | 0x00025000 | 0x00009000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002E000 | 0x00014B20 | 0x00014C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.42256 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22372 | 947 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 7.90898 | 18045 | UNKNOWN | English - United States | RT_ICON |
3 | 5.0253 | 9640 | UNKNOWN | English - United States | RT_ICON |
4 | 5.09189 | 4264 | UNKNOWN | English - United States | RT_ICON |
5 | 5.47214 | 3752 | UNKNOWN | English - United States | RT_ICON |
6 | 6.02855 | 2216 | UNKNOWN | English - United States | RT_ICON |
7 | 3.93375 | 1384 | UNKNOWN | English - United States | RT_ICON |
8 | 5.31538 | 1128 | UNKNOWN | English - United States | RT_ICON |
9 | 3.33823 | 744 | UNKNOWN | English - United States | RT_ICON |
10 | 2.86523 | 296 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
50
Monitored processes
14
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 776 | "C:\Program Files\4Team Corporation\vCardWizard\vCardWizardLauncher.exe" | C:\Program Files\4Team Corporation\vCardWizard\vCardWizardLauncher.exe | — | MSIEXEC.EXE | |||||||||||
User: admin Company: 4Team Corporation Integrity Level: MEDIUM Description: vCardWizardLauncher Exit code: 4294967295 Version: 1.1.0.16 Modules
| |||||||||||||||
| 892 | "C:\Windows\Installer\MSI4C68.tmp" | C:\Windows\Installer\MSI4C68.tmp | — | msiexec.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 920 | "C:\Windows\Installer\MSI2D91.tmp" "C:\Program Files\4Team Corporation\vCardWizard\" | C:\Windows\Installer\MSI2D91.tmp | — | msiexec.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1152 | "C:\Program Files\4Team Corporation\vCardWizard\vCardWizardApp.exe" -Splash 393610 | C:\Program Files\4Team Corporation\vCardWizard\vCardWizardApp.exe | — | vCardWizardLauncher.exe | |||||||||||
User: admin Company: 4Team Corporation Integrity Level: MEDIUM Description: vCard Wizard Exit code: 0 Version: 4.23.236.0 Modules
| |||||||||||||||
| 2076 | "C:\Program Files\4Team Corporation\vCardWizard\vCardWizardLauncher.exe" PostInstallEvent2GoogleAnalytics | C:\Program Files\4Team Corporation\vCardWizard\vCardWizardLauncher.exe | MSIEXEC.EXE | ||||||||||||
User: admin Company: 4Team Corporation Integrity Level: MEDIUM Description: vCardWizardLauncher Exit code: 0 Version: 1.1.0.16 Modules
| |||||||||||||||
| 2156 | "C:\Program Files\4Team Corporation\4Team-Updater\4Team-Updater.exe" | C:\Program Files\4Team Corporation\4Team-Updater\4Team-Updater.exe | MSIEXEC.EXE | ||||||||||||
User: admin Company: 4Team Corporation Integrity Level: MEDIUM Description: Auto-Updater Exit code: 0 Version: 1.30.69.0 Modules
| |||||||||||||||
| 2184 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2332 | C:\Windows\system32\MsiExec.exe -Embedding D08EA5868C03AAD9E985CE8171A0340E C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2716 | "C:\Users\admin\AppData\Local\Temp\vcardwizard_setup_423_x86.exe" | C:\Users\admin\AppData\Local\Temp\vcardwizard_setup_423_x86.exe | — | vcard_setup.exe | |||||||||||
User: admin Company: 4Team Corporation Integrity Level: MEDIUM Description: Setup Launcher Unicode Exit code: 0 Version: 4.23.0236 Modules
| |||||||||||||||
| 2916 | C:\Windows\system32\MsiExec.exe -Embedding CFFCA4A4E1385624658C24C2C0D07DDB | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 015
Read events
1 850
Write events
2 151
Delete events
14
Modification events
| (PID) Process: | (3532) vcard_setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3532) vcard_setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (4044) MSIEXEC.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4044) MSIEXEC.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\p2pcollab.dll,-8042 |
Value: Peer to Peer Trust | |||
| (PID) Process: | (4044) MSIEXEC.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\qagentrt.dll,-10 |
Value: System Health Authentication | |||
| (PID) Process: | (4044) MSIEXEC.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dnsapi.dll,-103 |
Value: Domain Name System (DNS) Server Trust | |||
| (PID) Process: | (4044) MSIEXEC.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-843 |
Value: BitLocker Drive Encryption | |||
| (PID) Process: | (4044) MSIEXEC.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-844 |
Value: BitLocker Data Recovery Agent | |||
| (PID) Process: | (3424) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000C23C3C7030ACD501600D0000EC060000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3424) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000C23C3C7030ACD501600D0000EC060000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
51
Suspicious files
11
Text files
154
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2716 | vcardwizard_setup_423_x86.exe | C:\Users\admin\AppData\Local\Temp\~CDBA.tmp | — | |
MD5:— | SHA256:— | |||
| 2716 | vcardwizard_setup_423_x86.exe | C:\Users\admin\AppData\Local\Temp\~CDBB.tmp | — | |
MD5:— | SHA256:— | |||
| 2716 | vcardwizard_setup_423_x86.exe | C:\Users\admin\AppData\Local\Temp\_isCDDC..dll | — | |
MD5:— | SHA256:— | |||
| 2716 | vcardwizard_setup_423_x86.exe | C:\Users\admin\AppData\Local\Temp\_isCE2B..dll | — | |
MD5:— | SHA256:— | |||
| 2716 | vcardwizard_setup_423_x86.exe | C:\Users\admin\AppData\Local\Temp\_isCE6A..dll | — | |
MD5:— | SHA256:— | |||
| 2716 | vcardwizard_setup_423_x86.exe | C:\Users\admin\AppData\Local\Temp\_isCE9A..dll | — | |
MD5:— | SHA256:— | |||
| 2716 | vcardwizard_setup_423_x86.exe | C:\Users\admin\AppData\Local\Temp\_isCEAB..dll | — | |
MD5:— | SHA256:— | |||
| 2716 | vcardwizard_setup_423_x86.exe | C:\Users\admin\AppData\Local\Temp\{4264CF71-E9DC-41F7-A968-E0F42BC23946}\4Team vCardWizard.msi | — | |
MD5:— | SHA256:— | |||
| 2716 | vcardwizard_setup_423_x86.exe | C:\Users\admin\AppData\Local\Downloaded Installations\{C862275C-D071-401F-BD78-9903F24018B8}\4Team vCardWizard.msi | — | |
MD5:— | SHA256:— | |||
| 2716 | vcardwizard_setup_423_x86.exe | C:\Users\admin\AppData\Local\Temp\~D061.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
3
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2156 | 4Team-Updater.exe | GET | 200 | 104.131.135.195:80 | http://d.4team.biz/files/Lib4Updates_13076.zip_x86 | US | compressed | 4.05 Mb | suspicious |
2156 | 4Team-Updater.exe | POST | 200 | 192.145.233.177:80 | http://ws.4team.biz/l4u/checkversion | US | text | 155 b | suspicious |
2076 | vCardWizardLauncher.exe | POST | 200 | 172.217.18.174:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2076 | vCardWizardLauncher.exe | 172.217.18.174:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
2156 | 4Team-Updater.exe | 192.145.233.177:80 | ws.4team.biz | InMotion Hosting, Inc. | US | unknown |
2156 | 4Team-Updater.exe | 104.131.135.195:80 | d.4team.biz | Digital Ocean, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google-analytics.com |
| whitelisted |
ws.4team.biz |
| suspicious |
d.4team.biz |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
Process | Message |
|---|---|
4Team-Updater.exe | [12/06/2019 12:27:32] Log type "Information": Application started.
|
4Team-Updater.exe | [12/06/2019 12:27:32] Log type "Information": Writing defaul StartDelay value to registry.
|
4Team-Updater.exe | [12/06/2019 12:27:32] Log type "Warning": Failed to parse StartDelay from the registry, assuming default value - 1
|
4Team-Updater.exe | [12/06/2019 12:27:32] Log type "Information": Writing defaul CheckInterval value to registry.
|
4Team-Updater.exe | [12/06/2019 12:27:32] Log type "Warning": Failed to parse CheckInterval from the registry, assuming default value - 1
|
4Team-Updater.exe | [12/06/2019 12:27:32] Log type "Warning": Failed to parse ReminderInterval from the registry, assuming default value - 90
|
4Team-Updater.exe | [12/06/2019 12:27:32] Log type "Information": Writing defaul ReminderInterval value to registry.
|