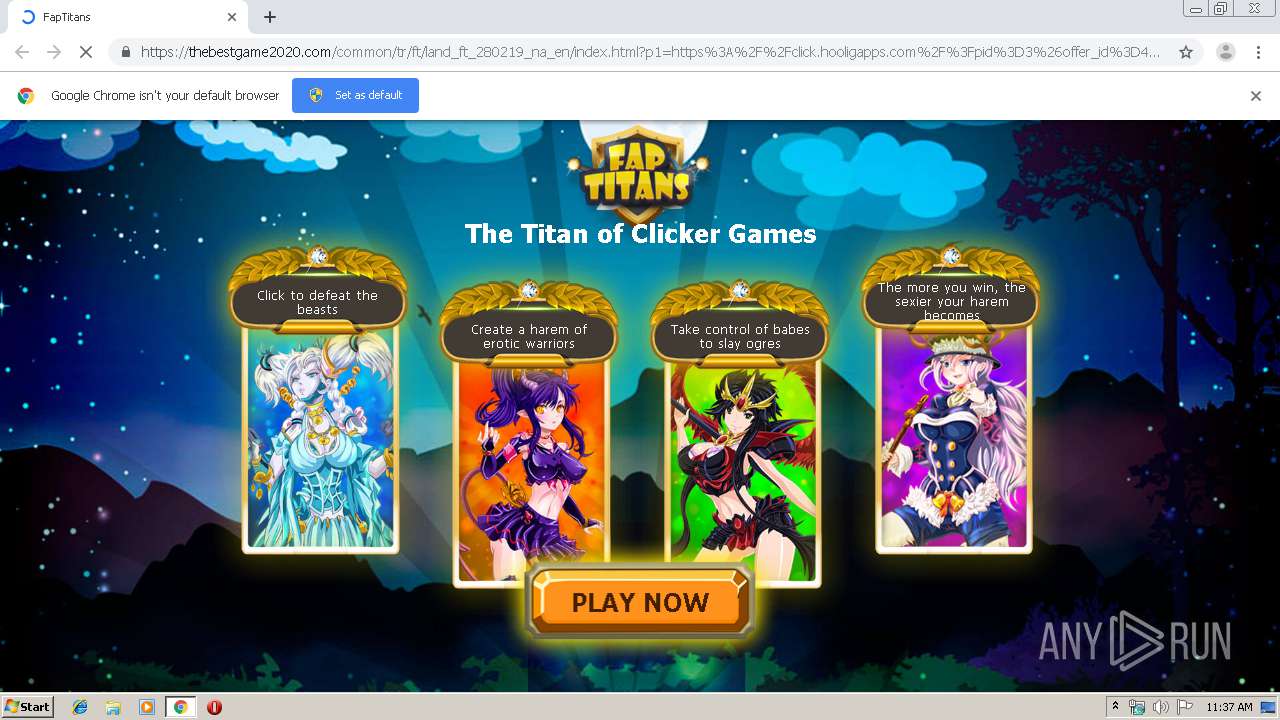
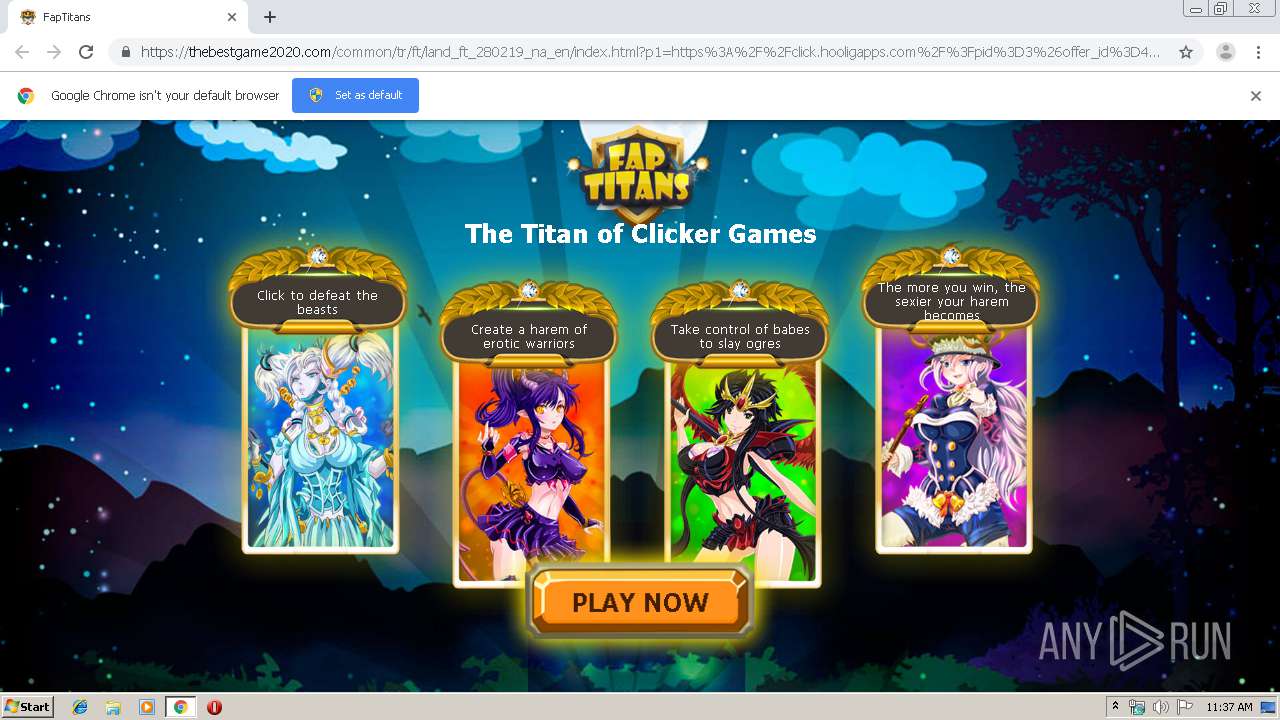
| URL: | https://thebestgame2020.com/common/tr/ft/land_ft_280219_na_en/index.html?p1=https%3A%2F%2Fclick.hooligapps.com%2F%3Fpid%3D3%26offer_id%3D4%26sub1%3Dpu_fill%26ref_id%3DVjN8MTUxMjY0NTZ8MTk3MjE1NHwxNzE2OTAzfDE1NzY4NDE2MDN8NDczODcyNGMtYmY3MS00MjVhLTkzOTMtMThlYTgzOWI3MzAwfDg4LjI1NS4yMTkuMjE4fDl8c2g9YThlYTY4NGU3YTdhNDZkNmM0MTViNDFkNTUyNWFlZjhlYTY5YzY0ODlmYzdmMzJlZTBiODhhYTVjNzVjYzAxMDhmY2JlYTk0Mzc0NDExOGQyZWE3NGJiYjJiNmEwMDE3MzYxODY4ZmNhY2JlMGQ1NGYyOGI5YzkxMjllYWUxZDVjMzNmMzY1MGUyNTI4N2Y1fGE2MzNhY2RkZjFhMzAwMjVmZDA3MDE4OGNjYTU0MTQ4%26sub2%3D15126456 |
| Full analysis: | https://app.any.run/tasks/6d8b33b3-defe-4f6e-b027-63e54a0295bf |
| Verdict: | Malicious activity |
| Analysis date: | December 20, 2019, 11:37:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F8858C707796DB56A8981113B6ECBD0C |
| SHA1: | D2FF915B5BFFE8B39446E6B47556F80A9D84D36C |
| SHA256: | BDA6F20EDDD7FC9C59704270254880B1926C7640D25440558870C15F56324B0F |
| SSDEEP: | 12:2dRmRhN+aLGQy7r468742qQaiPReCOypSec1Gohd+yVaQkrgLg:2ehN+uxy7r4H7zqQppoygf4ohs3QkMg |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2800)
INFO
Reads the hosts file
- chrome.exe (PID: 2800)
- chrome.exe (PID: 3920)
Application launched itself
- chrome.exe (PID: 2800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
65
Monitored processes
30
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11766088510570779760 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1320 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16056220601583326040 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2268 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11664012776412915056 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4800 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6224822346379896998 --mojo-platform-channel-handle=2664 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5348268167141594219 --mojo-platform-channel-handle=3424 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17350126623899972954 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2436 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1798142278524452916 --mojo-platform-channel-handle=488 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2972232877733382986 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2584 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10029259087848213218 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3996 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15986735836433362633 --mojo-platform-channel-handle=4632 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
657
Read events
555
Write events
97
Delete events
5
Modification events
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2800-13221315440858250 |
Value: 259 | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
39
Text files
267
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f85db092-fa88-4654-ba5e-c12821c4c4f4.tmp | — | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF39991e.TMP | text | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF3998df.TMP | text | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF3998df.TMP | text | |
MD5:— | SHA256:— | |||
| 2800 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF39996c.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
53
DNS requests
55
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
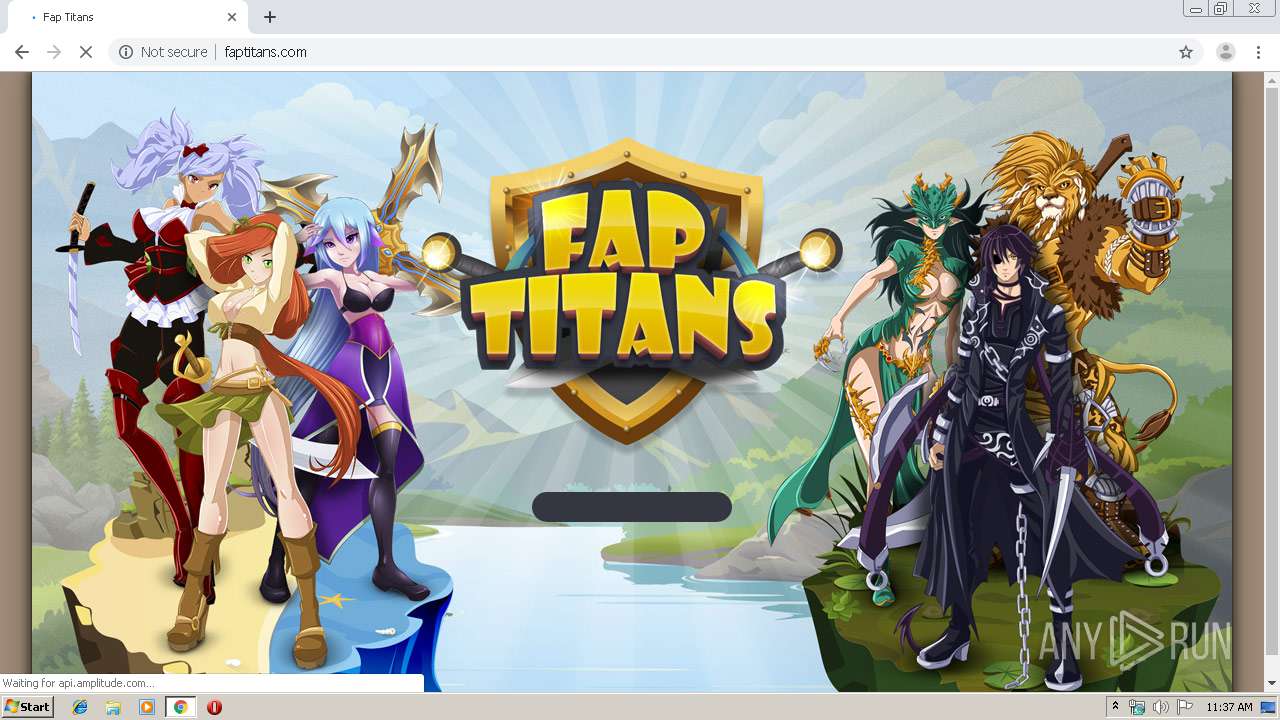
3920 | chrome.exe | GET | — | 204.155.159.29:80 | http://faptitans.com/ | US | — | — | suspicious |
3920 | chrome.exe | GET | 302 | 204.155.159.29:80 | http://faptitans.com/?haff_pid=3&haff_oid=4&haff_cid=474a000001060e07&haff_sub1=pu_fill&haff_sub2=15126456&haff_sub3= | US | — | — | suspicious |
3920 | chrome.exe | GET | 302 | 204.155.159.29:80 | http://faptitans.com/start/ | US | — | — | suspicious |
3920 | chrome.exe | GET | 302 | 204.155.159.29:80 | http://faptitans.com/?haff_pid=3&haff_oid=4&haff_cid=474a000001060e29&haff_sub1=pu_fill&haff_sub2=15126456&haff_sub3= | US | — | — | suspicious |
3920 | chrome.exe | GET | 302 | 172.217.16.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
3920 | chrome.exe | GET | 302 | 172.217.16.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 509 b | whitelisted |
3920 | chrome.exe | GET | 200 | 104.28.7.206:80 | http://lostincunt.space/iframe/5aa68ab8700?iframe&xapp=faptitans&xuid=149484729&time=3666.677490234375 | US | html | 525 b | malicious |
3920 | chrome.exe | GET | 200 | 104.28.7.206:80 | http://lostincunt.space/bnr/4/6c0/7667c7/6c07667c7783b0b5872769cdab24494e.jpg | US | image | 28.8 Kb | malicious |
3920 | chrome.exe | POST | 200 | 204.155.159.29:80 | http://faptitans.com/api/ | US | text | 63 b | suspicious |
3920 | chrome.exe | GET | 200 | 204.155.159.29:80 | http://faptitans.com/ | US | html | 5.74 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3920 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3920 | chrome.exe | 104.27.137.29:443 | thebestgame2020.com | Cloudflare Inc | US | unknown |
3920 | chrome.exe | 104.18.32.151:443 | hentaifap.land | Cloudflare Inc | US | malicious |
3920 | chrome.exe | 204.155.147.176:443 | ln.gamesrevenue.com | WZ Communications Inc. | US | suspicious |
3920 | chrome.exe | 77.88.21.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
3920 | chrome.exe | 172.217.16.164:443 | www.google.com | Google Inc. | US | whitelisted |
3920 | chrome.exe | 173.194.164.153:80 | r3---sn-4g5edne6.gvt1.com | Google Inc. | US | whitelisted |
3920 | chrome.exe | 172.217.16.129:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3920 | chrome.exe | 173.194.187.7:80 | r2---sn-4g5e6ns6.gvt1.com | Google Inc. | US | whitelisted |
3920 | chrome.exe | 104.27.167.200:443 | click.hooligapps.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
thebestgame2020.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ln.gamesrevenue.com |
| suspicious |
hentaifap.land |
| malicious |
mc.yandex.ru |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |