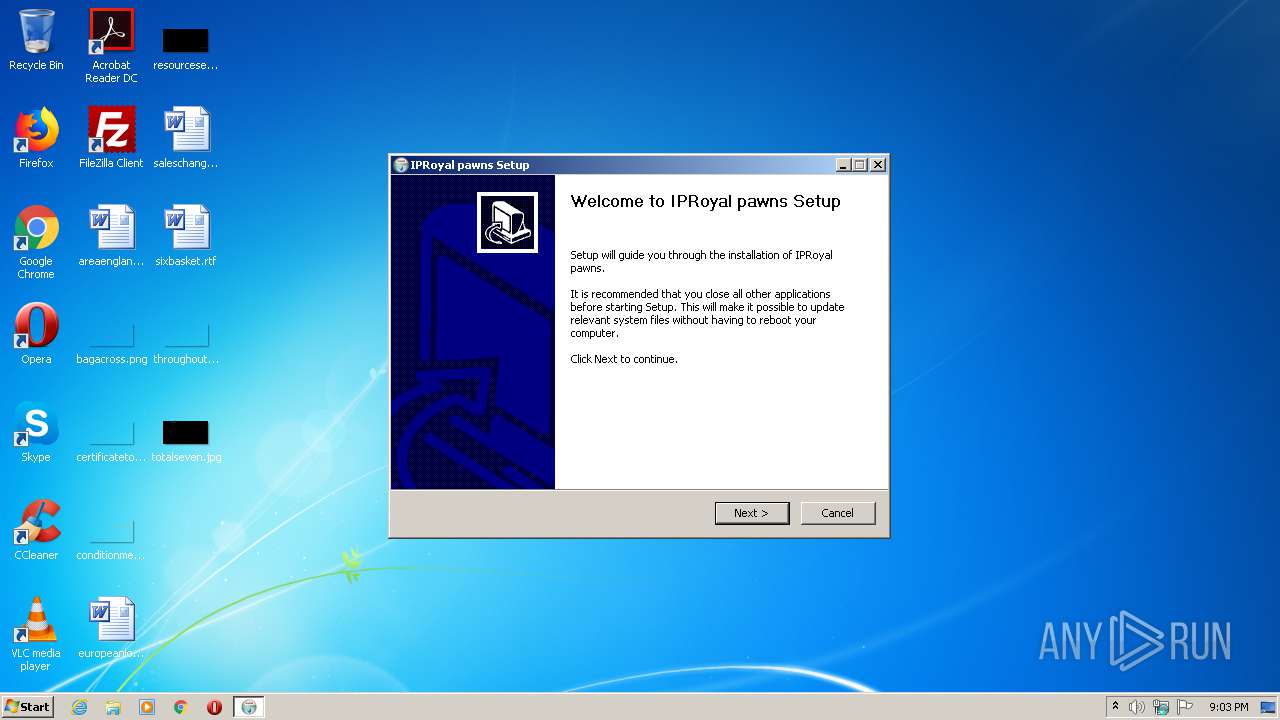
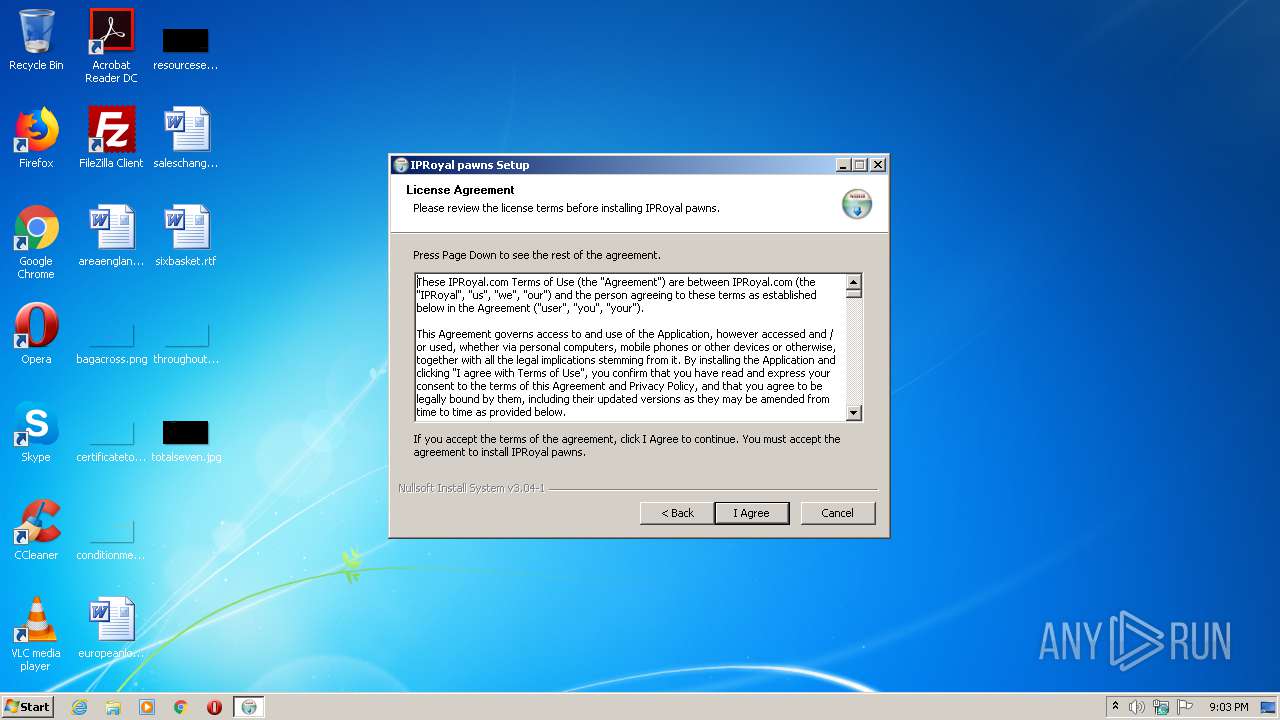
| File name: | IPRoyalPawnsSetup (1).exe |
| Full analysis: | https://app.any.run/tasks/7254924a-4ca0-48b9-8140-f485df3daaa3 |
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2021, 21:02:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | C0EBE33354922A211F0BF3CA2C84361D |
| SHA1: | 33A2DEA1147045EA8BF38FD35F5FA994F5800BE0 |
| SHA256: | BD9CE67BC48E56017F34D46718767723DC427EE8648E3EF585D6BF1606C0B253 |
| SSDEEP: | 196608:mK+zAtulFVzw4FLELUUIuIsFdSuZEd9sVecPr59wXW6DIZ1rBZwpe2f:mXguljzL1ELFIuIsbSAA9slVcPD21rDG |
MALICIOUS
Application was dropped or rewritten from another process
- iproyal_pawns.exe (PID: 3592)
Changes settings of System certificates
- iproyal_pawns.exe (PID: 3592)
SUSPICIOUS
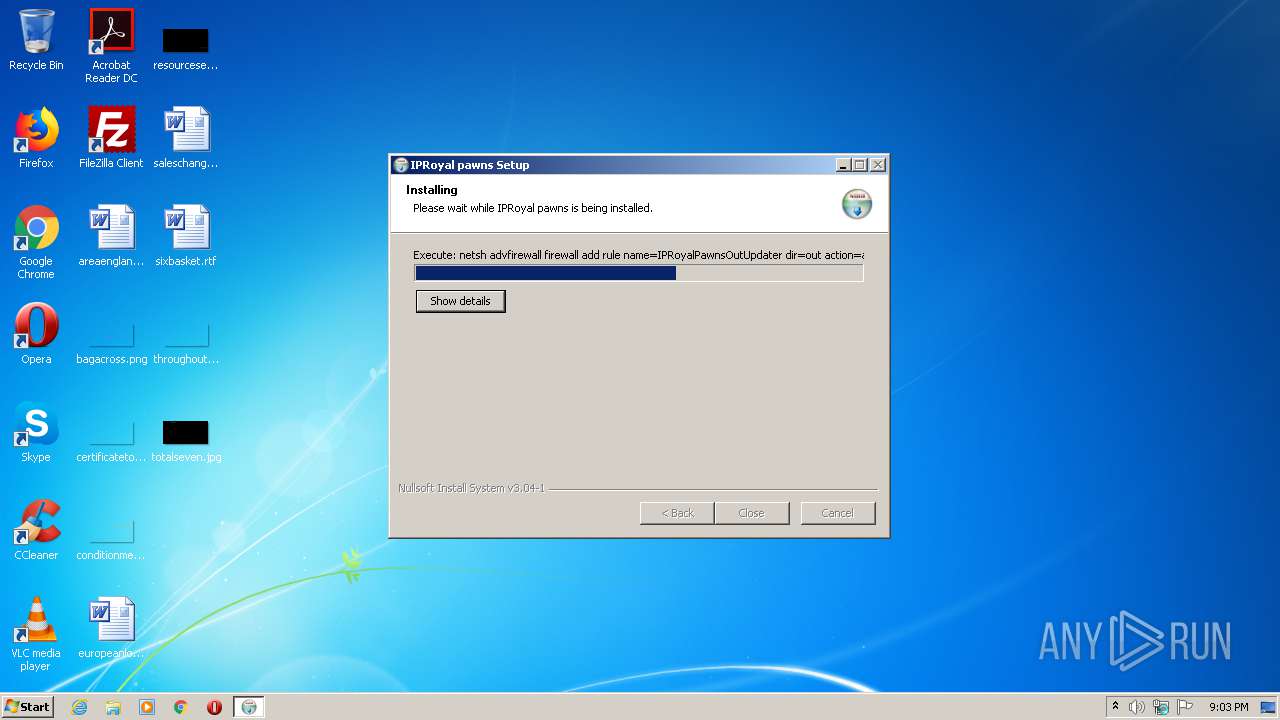
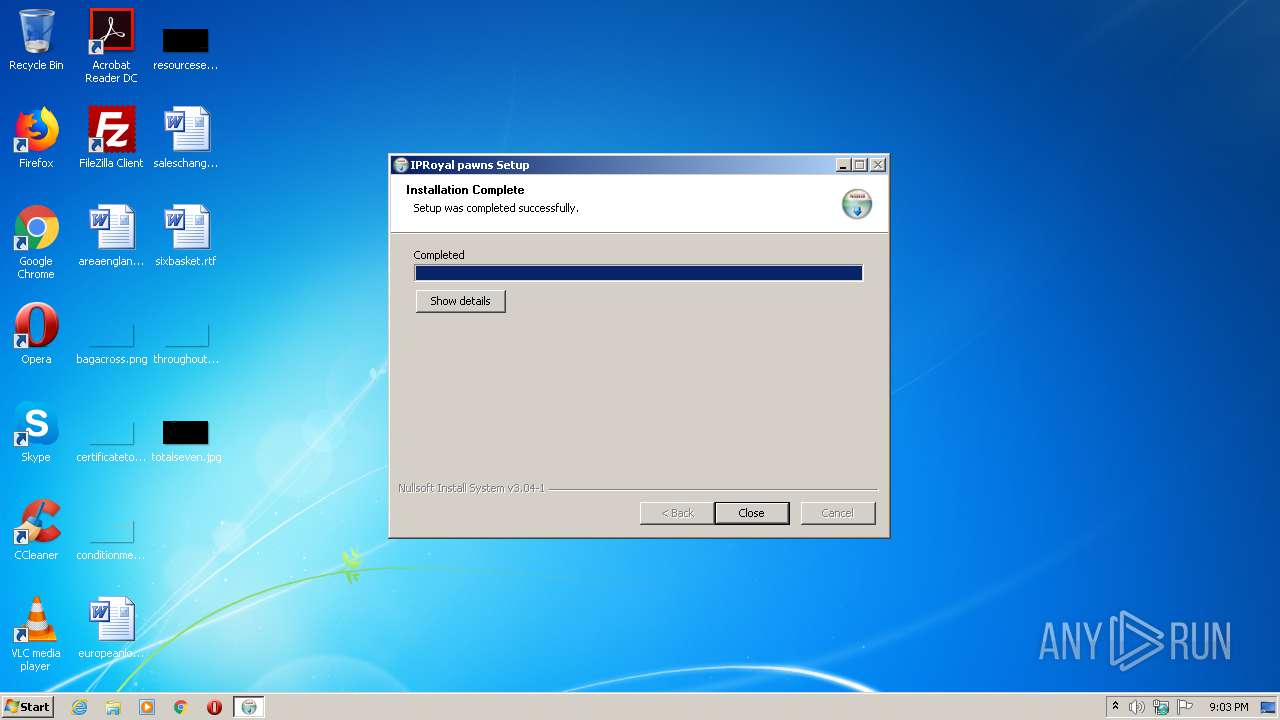
Executable content was dropped or overwritten
- IPRoyalPawnsSetup (1).exe (PID: 2276)
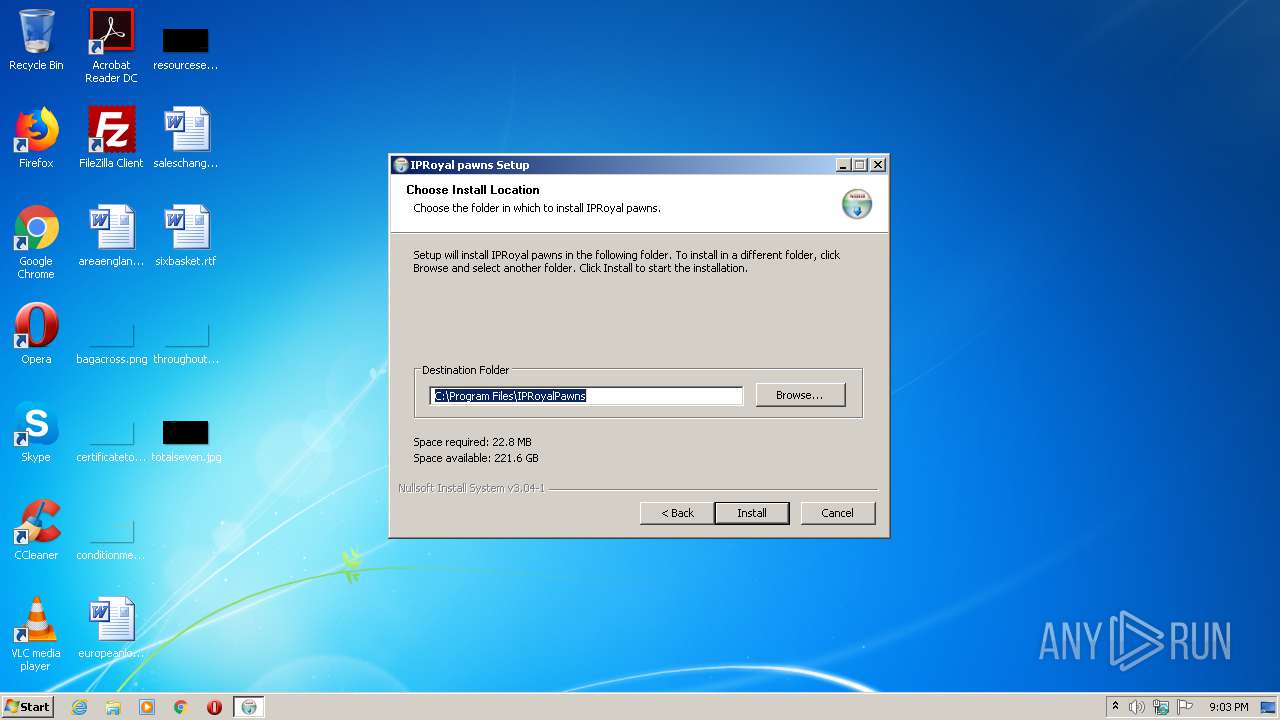
Creates files in the program directory
- IPRoyalPawnsSetup (1).exe (PID: 2276)
Creates a directory in Program Files
- IPRoyalPawnsSetup (1).exe (PID: 2276)
Drops a file with a compile date too recent
- IPRoyalPawnsSetup (1).exe (PID: 2276)
Drops a file that was compiled in debug mode
- IPRoyalPawnsSetup (1).exe (PID: 2276)
Drops a file with too old compile date
- IPRoyalPawnsSetup (1).exe (PID: 2276)
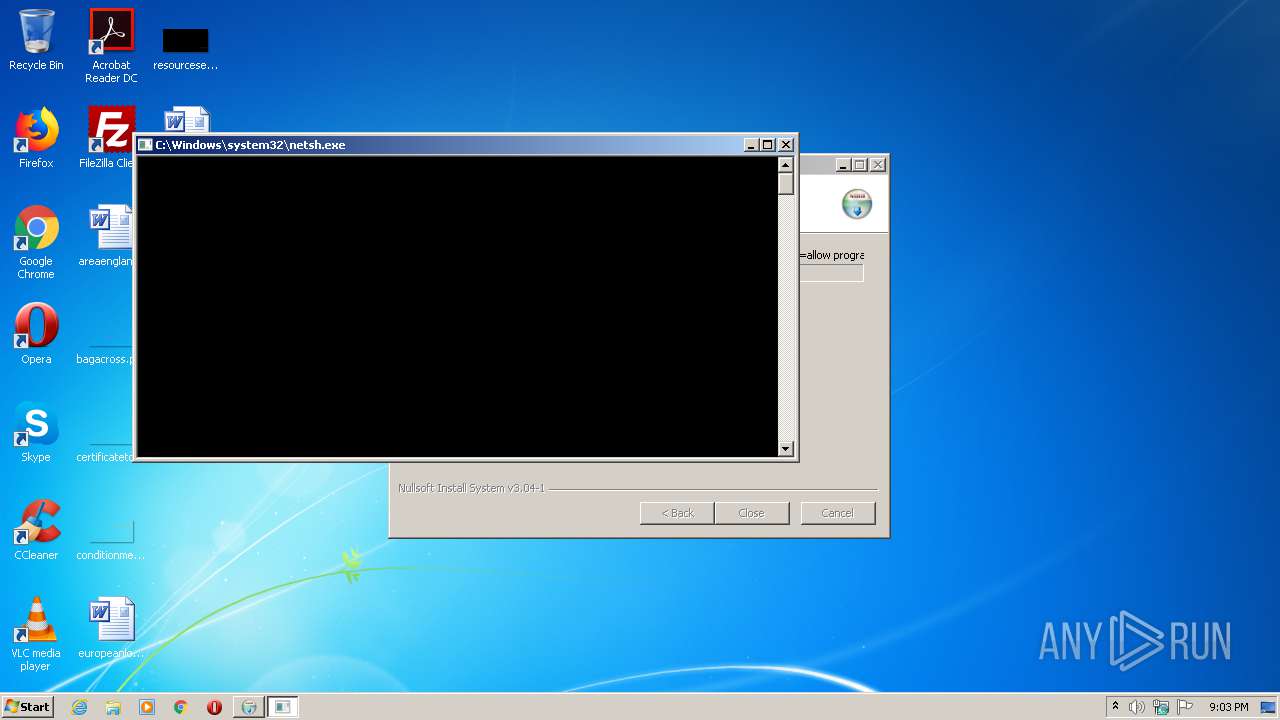
Uses NETSH.EXE for network configuration
- IPRoyalPawnsSetup (1).exe (PID: 2276)
Uses ICACLS.EXE to modify access control list
- IPRoyalPawnsSetup (1).exe (PID: 2276)
Adds / modifies Windows certificates
- iproyal_pawns.exe (PID: 3592)
Creates files in the user directory
- iproyal_pawns.exe (PID: 3592)
INFO
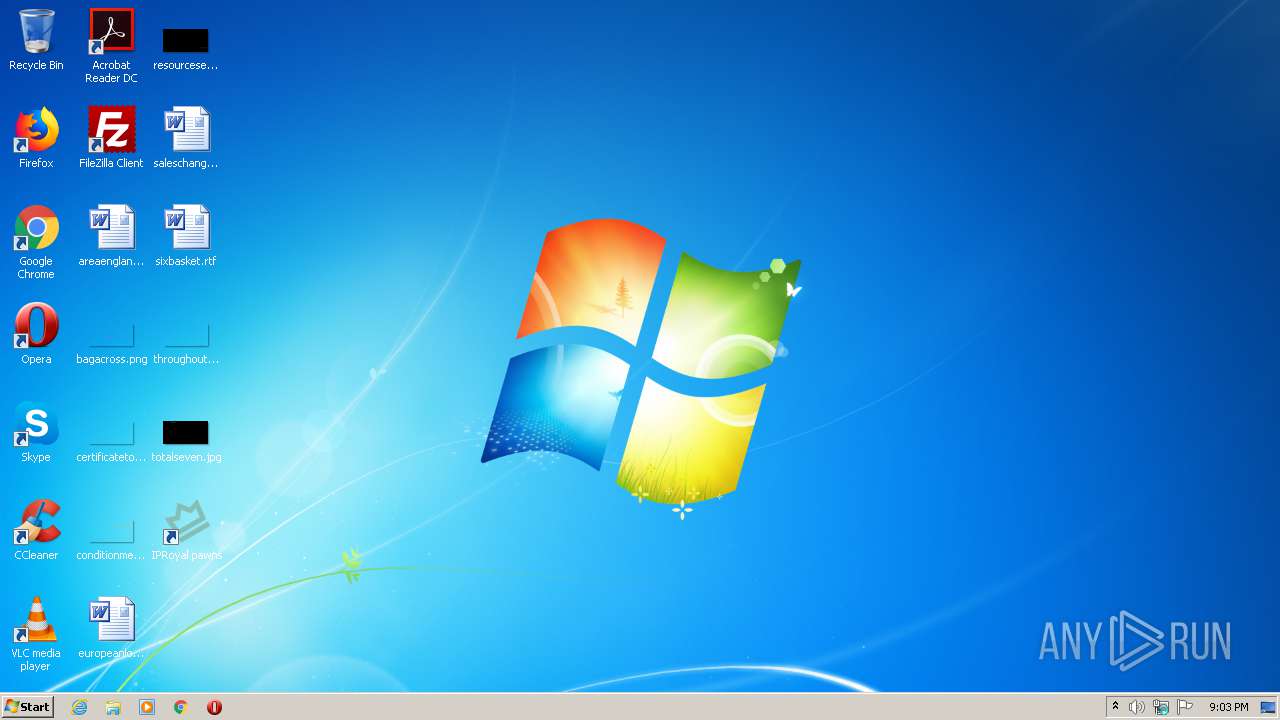
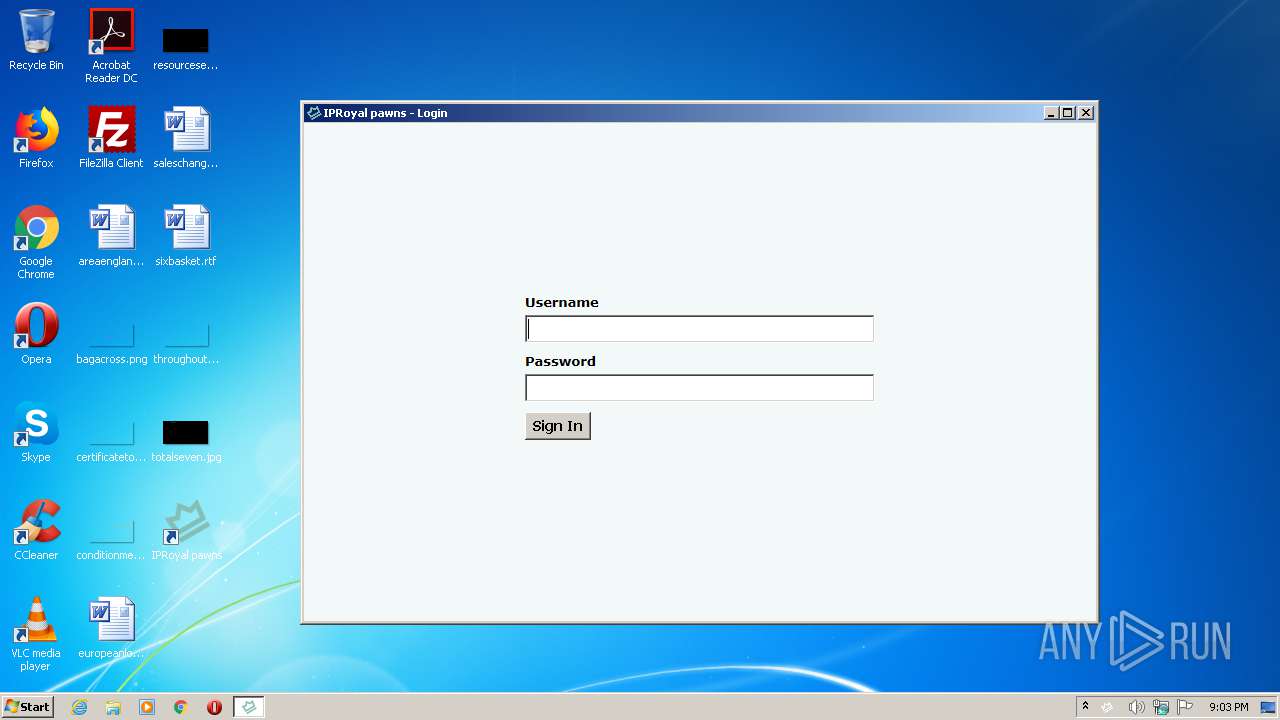
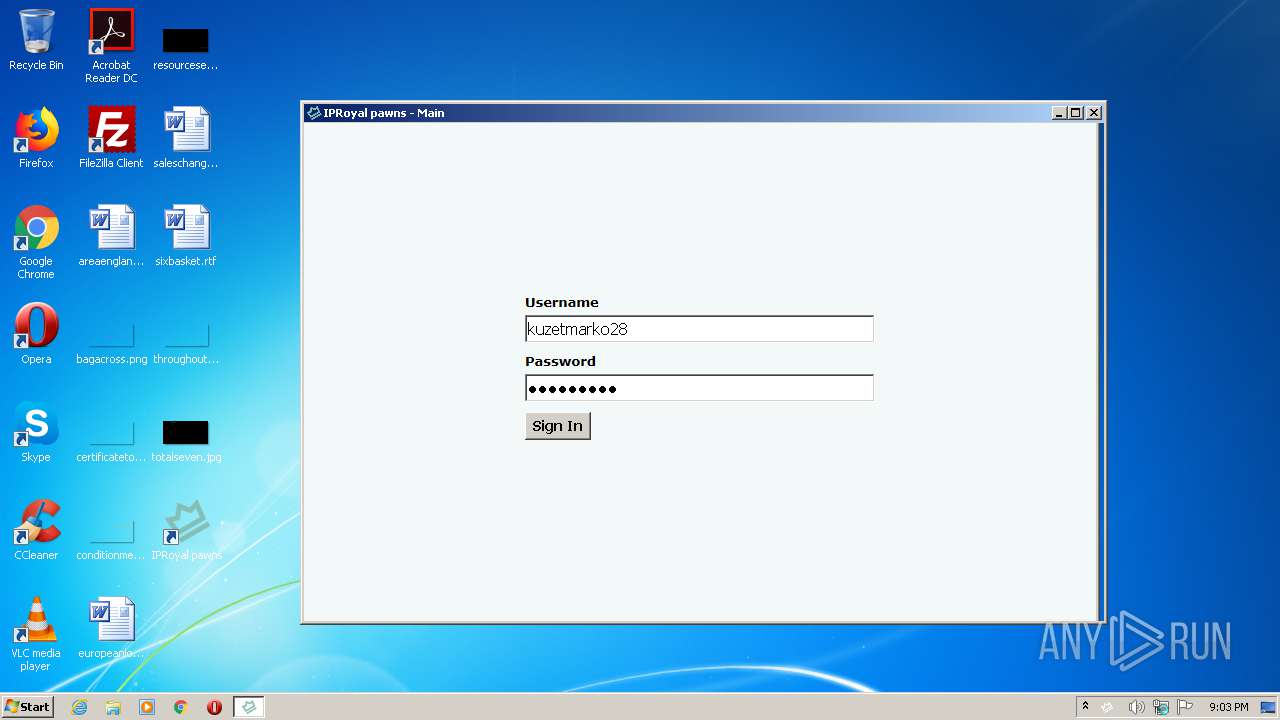
Manual execution by user
- iproyal_pawns.exe (PID: 3592)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:01:07 10:13:04+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.31 |
| CodeSize: | 36352 |
| InitializedDataSize: | 38912 |
| UninitializedDataSize: | 152064 |
| EntryPoint: | 0x413e |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Jan-2019 09:13:04 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 07-Jan-2019 09:13:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00008D2C | 0x00008E00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.05248 |
.data | 0x0000A000 | 0x000000C8 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.42508 |
.rdata | 0x0000B000 | 0x00006CE8 | 0x00006E00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.2447 |
.bss | 0x00012000 | 0x00025200 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00038000 | 0x00001354 | 0x00001400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.34575 |
.ndata | 0x0003A000 | 0x00014000 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0004E000 | 0x00004CD0 | 0x00004E00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.75359 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29735 | 1068 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.9993 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 6.24459 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 5.01502 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 6.16057 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 3.34146 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 3.04232 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.6691 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.71374 | 356 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.DLL |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
55
Monitored processes
9
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | icacls "C:\Program Files\IPRoyalPawns\iproyal_pawns.exe" /grant *S-1-5-32-545:(R,W) | C:\Windows\system32\icacls.exe | — | IPRoyalPawnsSetup (1).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1076 | "C:\Users\admin\AppData\Local\Temp\IPRoyalPawnsSetup (1).exe" | C:\Users\admin\AppData\Local\Temp\IPRoyalPawnsSetup (1).exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2276 | "C:\Users\admin\AppData\Local\Temp\IPRoyalPawnsSetup (1).exe" | C:\Users\admin\AppData\Local\Temp\IPRoyalPawnsSetup (1).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2424 | netsh advfirewall firewall add rule name=IPRoyalPawnsOut dir=out action=allow program="C:\Program Files\IPRoyalPawns\iproyal_pawns.exe" enable=yes profile=public,private | C:\Windows\system32\netsh.exe | — | IPRoyalPawnsSetup (1).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2496 | netsh advfirewall firewall add rule name=IPRoyalPawnsOutUpdater dir=out action=allow program="C:\Program Files\IPRoyalPawns\updater.exe" enable=yes profile=public,private | C:\Windows\system32\netsh.exe | — | IPRoyalPawnsSetup (1).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2568 | icacls "C:\Program Files\IPRoyalPawns\updater.exe" /grant *S-1-5-32-545::(R,W) | C:\Windows\system32\icacls.exe | — | IPRoyalPawnsSetup (1).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 87 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2772 | netsh advfirewall firewall add rule name=IPRoyalPawnsIn dir=in action=allow program="C:\Program Files\IPRoyalPawns\iproyal_pawns.exe" enable=yes profile=public,private | C:\Windows\system32\netsh.exe | — | IPRoyalPawnsSetup (1).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3592 | "C:\Program Files\IPRoyalPawns\iproyal_pawns.exe" | C:\Program Files\IPRoyalPawns\iproyal_pawns.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3832 | netsh advfirewall firewall add rule name=IPRoyalPawnsInUpdater dir=in action=allow program="C:\Program Files\IPRoyalPawns\updater.exe" enable=yes profile=public,private | C:\Windows\system32\netsh.exe | — | IPRoyalPawnsSetup (1).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
562
Read events
362
Write events
198
Delete events
2
Modification events
| (PID) Process: | (2772) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2772) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (2772) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (2772) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (2772) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
| (PID) Process: | (2772) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-1 |
Value: IPsec Relying Party | |||
| (PID) Process: | (2772) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-2 |
Value: Provides IPsec based enforcement for Network Access Protection | |||
| (PID) Process: | (2772) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-4 |
Value: 1.0 | |||
| (PID) Process: | (2772) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-3 |
Value: Microsoft Corporation | |||
| (PID) Process: | (2772) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\tsgqec.dll,-100 |
Value: RD Gateway Quarantine Enforcement Client | |||
Executable files
6
Suspicious files
0
Text files
3
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2276 | IPRoyalPawnsSetup (1).exe | C:\Users\admin\AppData\Local\Temp\nsi9F2F.tmp\System.dll | executable | |
MD5:DBAEF88A5991E569B0419F757950F1B7 | SHA256:487C9B44388783296736DB93BE2A1F786F6051BA4282F8DF54A4E1B94E272D56 | |||
| 2276 | IPRoyalPawnsSetup (1).exe | C:\Program Files\IPRoyalPawns\updater.exe | executable | |
MD5:EA90A9323725AB8C39DCB4BB1975F165 | SHA256:F1AF4CBA8127A5F0066E1935DF1E78919CE7CDB23405A92DFE3FBA500C7E97FE | |||
| 3592 | iproyal_pawns.exe | C:\Users\admin\AppData\Local\Temp\systray_temp_icon_178a35b2f027b31c6ad5a4f7b2c7f93a | image | |
MD5:178A35B2F027B31C6AD5A4F7B2C7F93A | SHA256:337D9CB7A1CEB00FB4A82E9100DEC20C3C1229B95DFA5DC8E397E01AAD219A84 | |||
| 3592 | iproyal_pawns.exe | C:\Users\admin\AppData\Roaming\ip_royal_paws\session | text | |
MD5:EFBB48B1B6E64552C5CFBDDC6C851D3D | SHA256:51237935CC9991D7A09AAC9CE4FD2A3AB512045582DB9B10229A8EC74CC0C6C1 | |||
| 2276 | IPRoyalPawnsSetup (1).exe | C:\Users\admin\Desktop\IPRoyal pawns.lnk | lnk | |
MD5:D5EB59D7410B4FC12BCDE61C578239C7 | SHA256:27761A34057DCE23B69B45AD12E3625346F005C4D3E9CD97267F112254F901F4 | |||
| 2276 | IPRoyalPawnsSetup (1).exe | C:\Program Files\IPRoyalPawns\sciter.dll | executable | |
MD5:4672647FD40B361D8259C454AD233A4F | SHA256:DA312829FD967BCABD705979BE4E1BF6969B626F4FE4C589AB99BA09D830EECC | |||
| 2276 | IPRoyalPawnsSetup (1).exe | C:\Program Files\IPRoyalPawns\uninstaller.exe | executable | |
MD5:7D576C125A8A8C31FD1049A886A8A11C | SHA256:A1667DF52848872D2FC1B2B0775C1FB474B8C9918250EAAD13B9201E27384A75 | |||
| 2276 | IPRoyalPawnsSetup (1).exe | C:\Program Files\IPRoyalPawns\iproyal_pawns.exe | executable | |
MD5:FD8E37432EA2D17406E5E7345830BEC7 | SHA256:A3192753B160AFA89D90FC6DA69446F2ADF25459690C48562C862B0939381AF4 | |||
| 2276 | IPRoyalPawnsSetup (1).exe | C:\Users\admin\AppData\Local\Temp\nsi9F2F.tmp\nsDialogs.dll | executable | |
MD5:B1B3911821A129B23445C829C1ACB9D8 | SHA256:79E6B77AFF2B543C547F920D54D8D3302F1FC6F6B42B3C262283E4E85D27825F | |||
| 2276 | IPRoyalPawnsSetup (1).exe | C:\Users\admin\AppData\Local\Temp\nsi9F2F.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
3
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
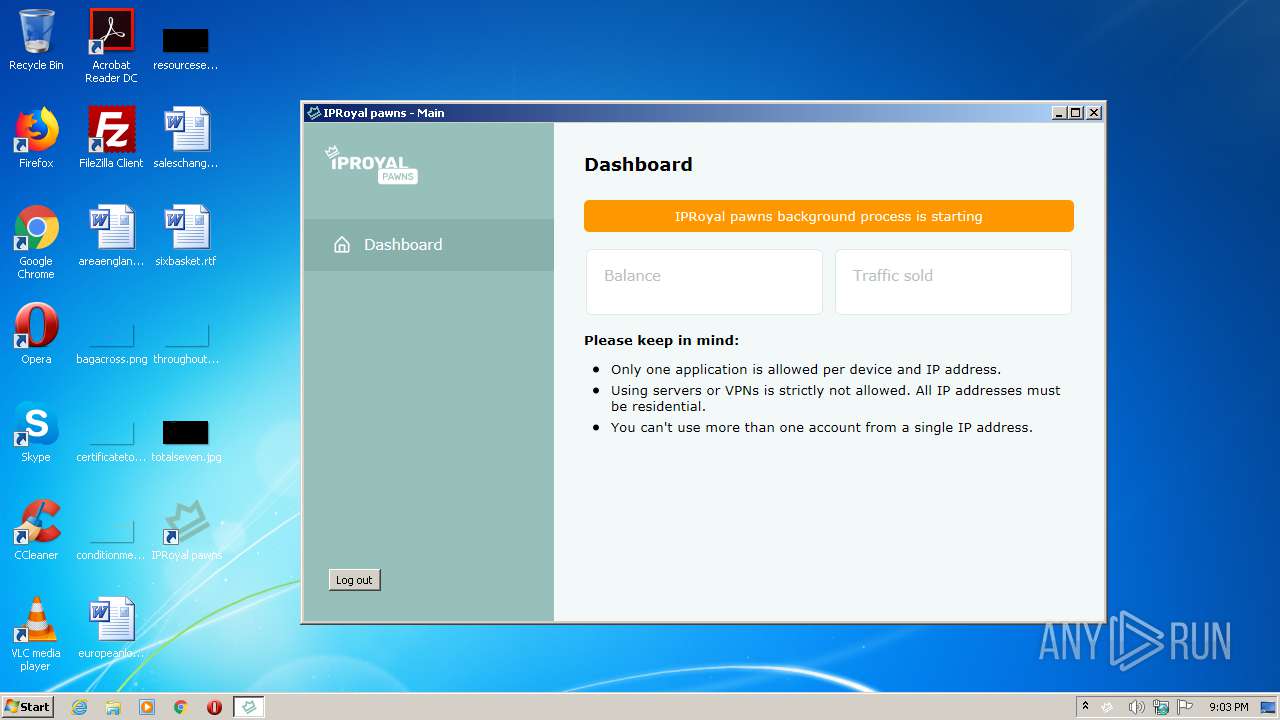
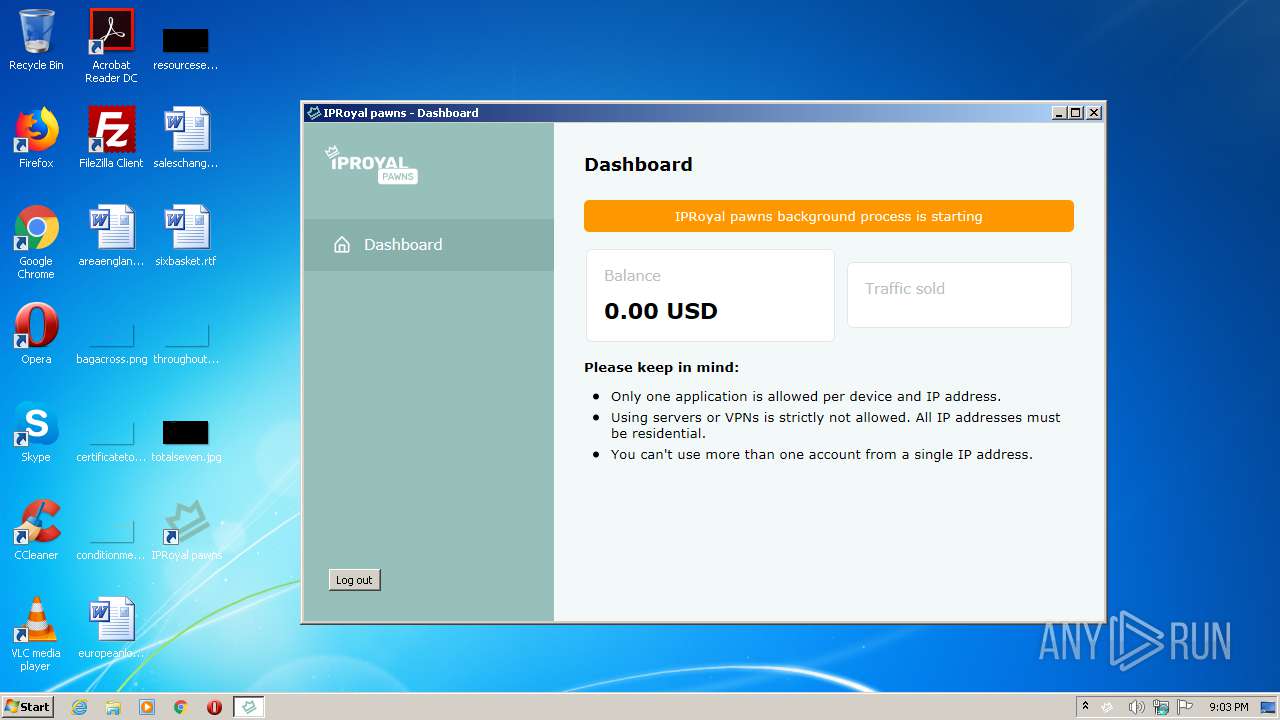
3592 | iproyal_pawns.exe | 91.239.130.49:443 | api.iproyal.com | — | — | unknown |
3592 | iproyal_pawns.exe | 91.239.130.49:7000 | api.iproyal.com | — | — | unknown |
3592 | iproyal_pawns.exe | 66.171.248.178:443 | ipv4bot.whatismyipaddress.com | Alchemy Communications, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.iproyal.com |
| unknown |
ipv4bot.whatismyipaddress.com |
| shared |
228.20.91.45.in-addr.arpa |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3592 | iproyal_pawns.exe | Potential Corporate Privacy Violation | ET POLICY Known External IP Lookup Service Domain in SNI |