| File name: | fortnite hack.exe |
| Full analysis: | https://app.any.run/tasks/e7296ae3-e7d7-44e4-bcfb-fabde5b62f93 |
| Verdict: | Malicious activity |
| Analysis date: | October 04, 2022, 23:36:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 08BB1E7FC7B5A67098E7A1B2D6F19E91 |
| SHA1: | D4DDCAF63797B44BD0FDA7029C64835213767E8E |
| SHA256: | BD9CCEE749AEC5AB8602010A0E5061E36DFDD1CC98F9941A6C4D56BDEDD226B2 |
| SSDEEP: | 768:2KsMqCXfVcWlzM9ZkiANIUQfdYLDwUzc80gmq3oP/oDb:2Kse1M9ZkiAPQ6r/0O8/of |
MALICIOUS
Changes the autorun value in the registry
- fortnite hack.exe (PID: 2988)
Actions looks like stealing of personal data
- fortnite hack.exe (PID: 2988)
Runs app for hidden code execution
- fortnite hack.exe (PID: 2988)
SUSPICIOUS
Checks supported languages
- fortnite hack.exe (PID: 2988)
- cmd.exe (PID: 3092)
Reads the computer name
- fortnite hack.exe (PID: 2988)
Starts CMD.EXE for commands execution
- fortnite hack.exe (PID: 2988)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 3092)
INFO
Checks supported languages
- WMIC.exe (PID: 3440)
Reads the computer name
- WMIC.exe (PID: 3440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (72.2) |
|---|---|---|
| .scr | | | Windows screen saver (12.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (6.4) |
| .exe | | | Win32 Executable (generic) (4.4) |
| .exe | | | Generic Win/DOS Executable (1.9) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 2039-Jan-30 07:06:20 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | - |
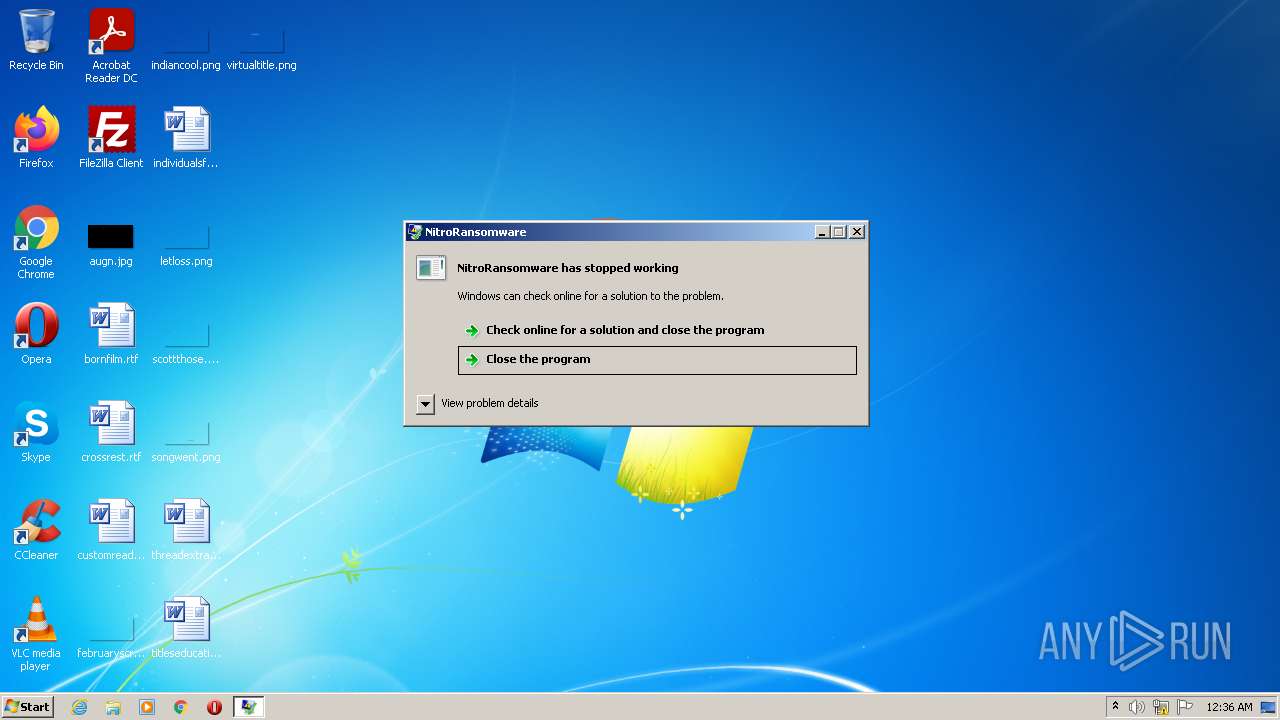
| FileDescription: | NitroRansomware |
| FileVersion: | 1.0.0.0 |
| InternalName: | NitroRansomware.exe |
| LegalCopyright: | Copyright © 2021 |
| LegalTrademarks: | - |
| OriginalFilename: | NitroRansomware.exe |
| ProductName: | NitroRansomware |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 144 |
| e_cp: | 3 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | - |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | - |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 3 |
| TimeDateStamp: | 2039-Jan-30 07:06:20 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 8192 | 60392 | 60416 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.42352 |
.rsrc | 73728 | 1500 | 1536 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.14747 |
.reloc | 81920 | 12 | 512 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.26641 | 844 | UNKNOWN | UNKNOWN | RT_VERSION |
1 (#2) | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
40
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2988 | "C:\Users\admin\AppData\Local\Temp\fortnite hack.exe" | C:\Users\admin\AppData\Local\Temp\fortnite hack.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Description: NitroRansomware Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3092 | "cmd.exe" | C:\Windows\system32\cmd.exe | — | fortnite hack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3440 | wmic csproduct get uuid | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
165
Read events
164
Write events
1
Delete events
0
Modification events
| (PID) Process: | (2988) fortnite hack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | NR |
Value: "C:\Users\admin\AppData\Local\Temp\fortnite hack.exe" | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report