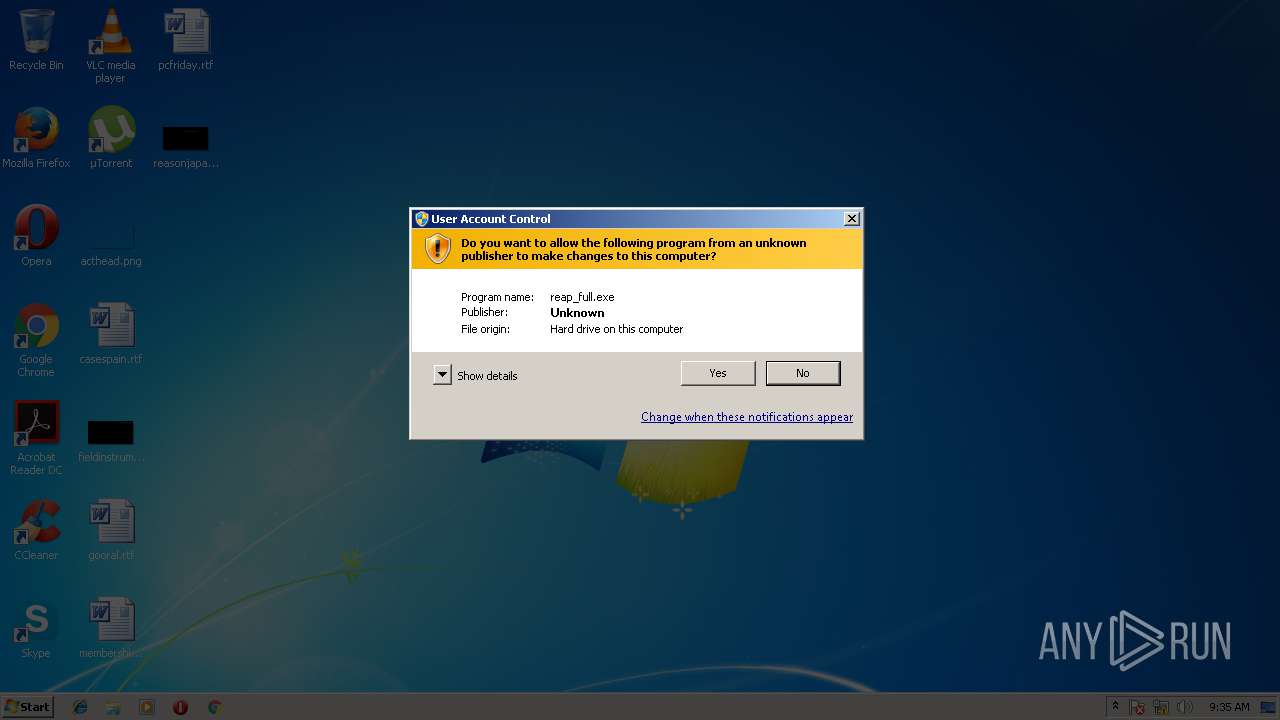
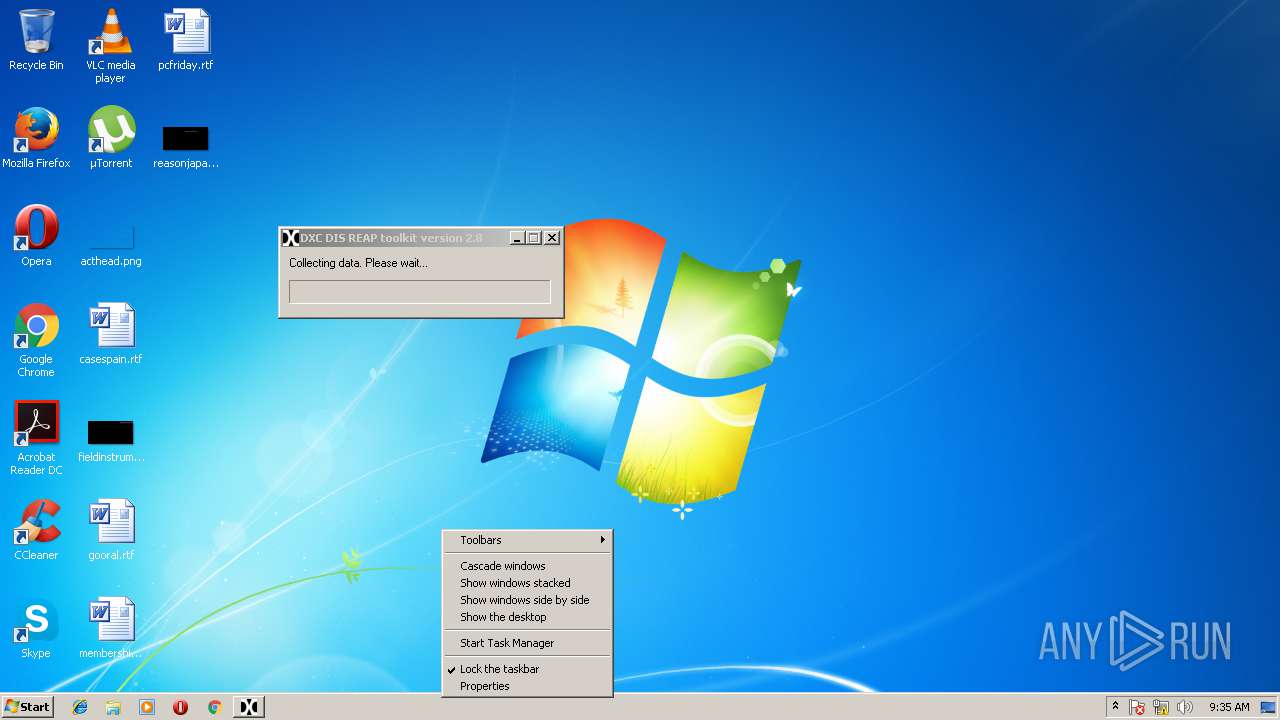
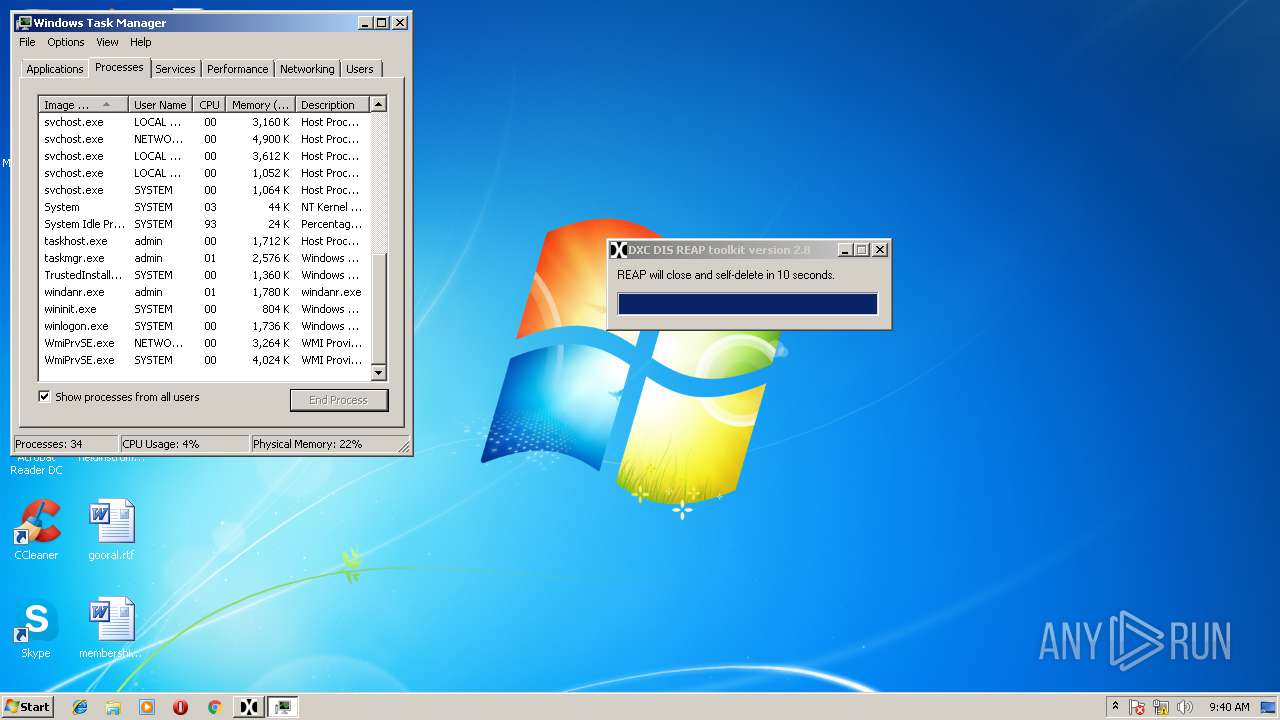
| File name: | reap_full.exe |
| Full analysis: | https://app.any.run/tasks/744c8088-b2ef-45f5-a963-edbe8f97947f |
| Verdict: | Malicious activity |
| Analysis date: | March 08, 2018, 09:35:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 05B9182F15D1CC493B48D4510BE3752A |
| SHA1: | 393FE6CCB943607C6D32EF864AA17125B9EFCCF8 |
| SHA256: | BD89643924FF274496C213164A6635B65B6DD32F95BDCA394EA8D109340955E1 |
| SSDEEP: | 196608:mj/fIutj0YsIOByx3nAxnXYadGPuPuLlEE+ZQ826A4qBy:mMutsIOBGXAVYadYlEE+p26bqB |
MALICIOUS
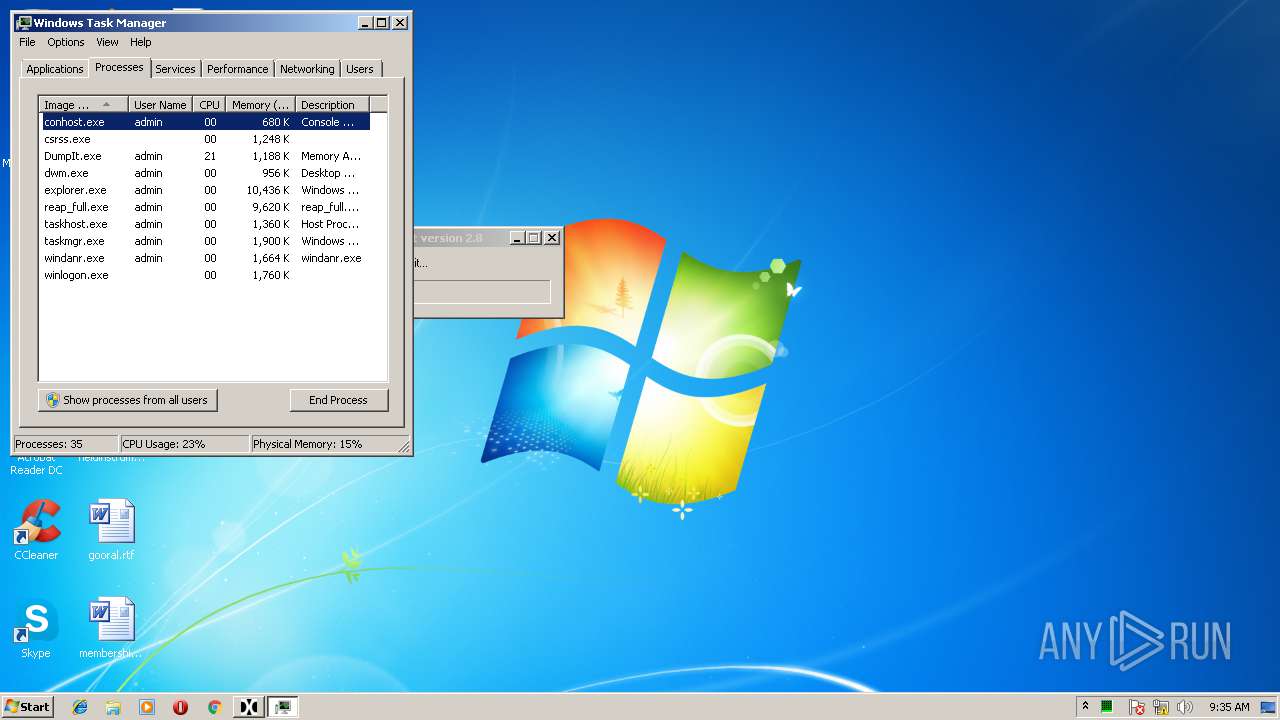
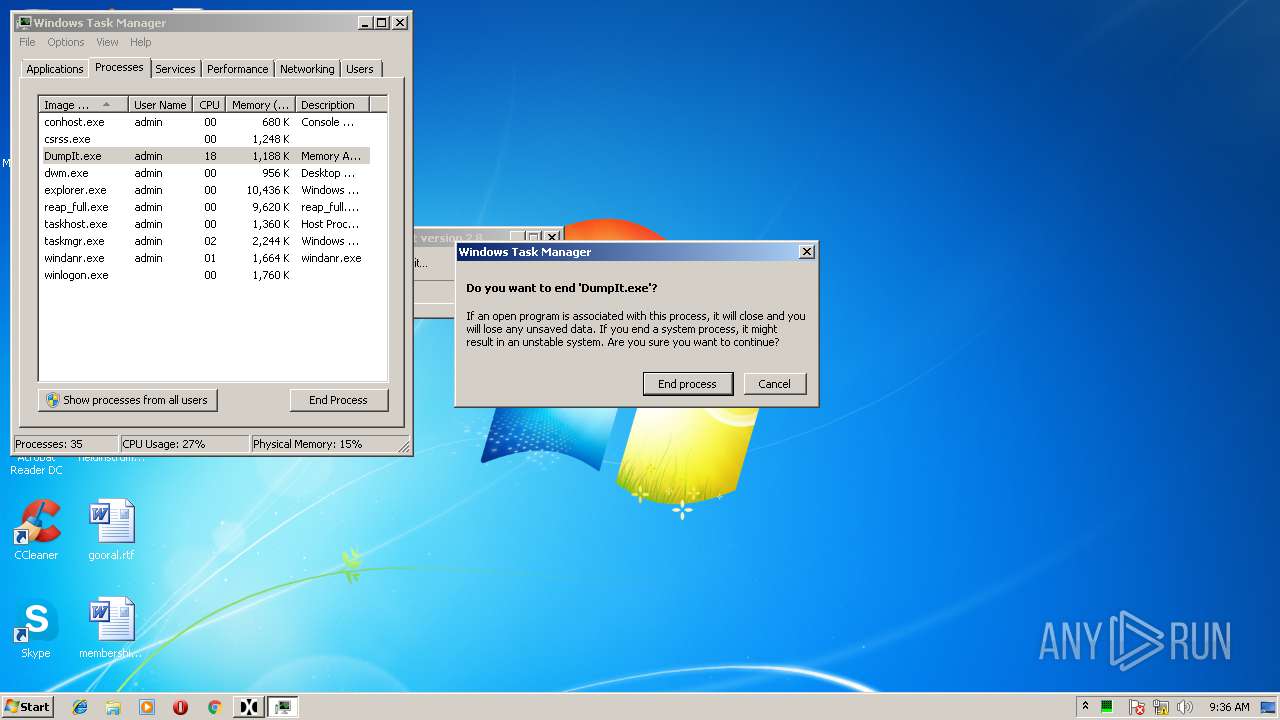
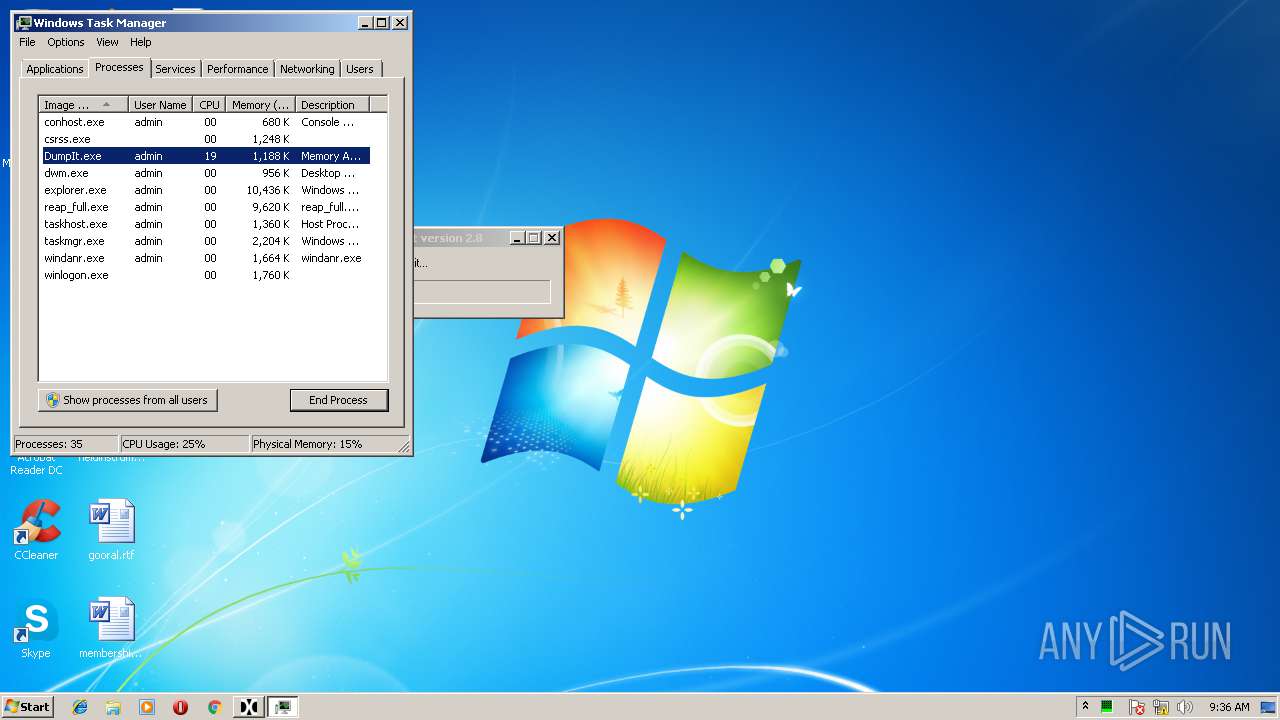
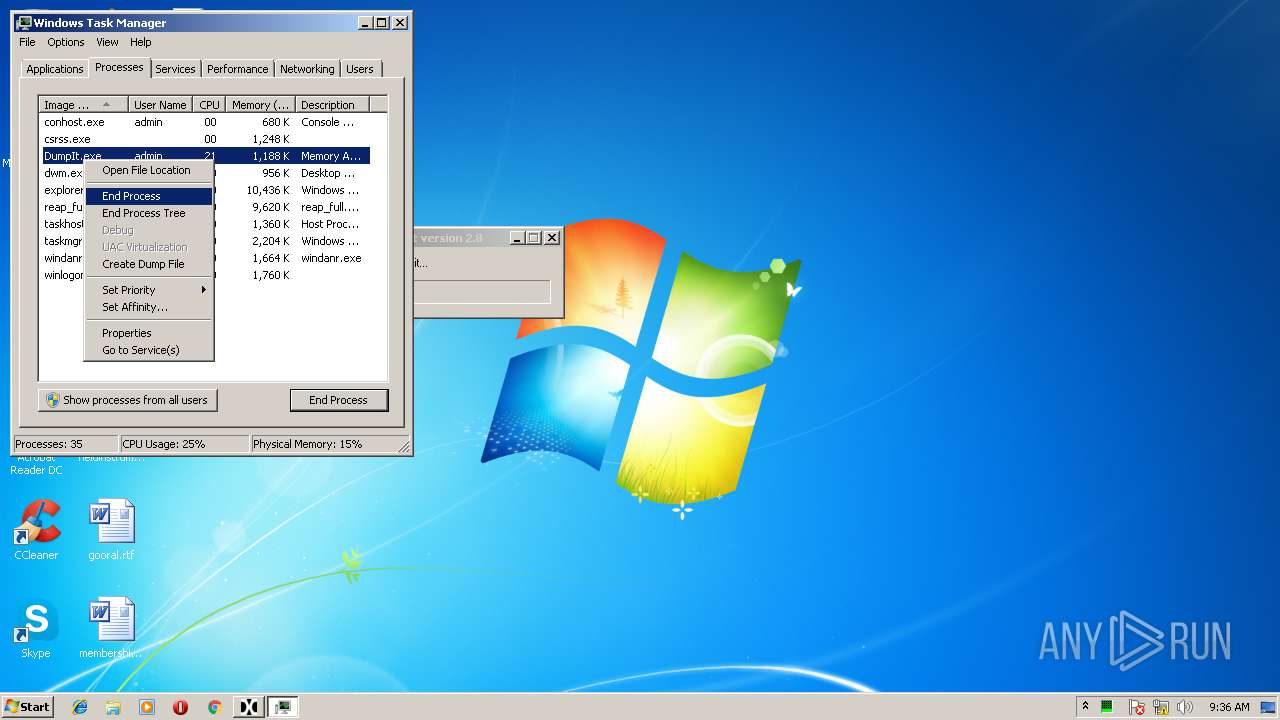
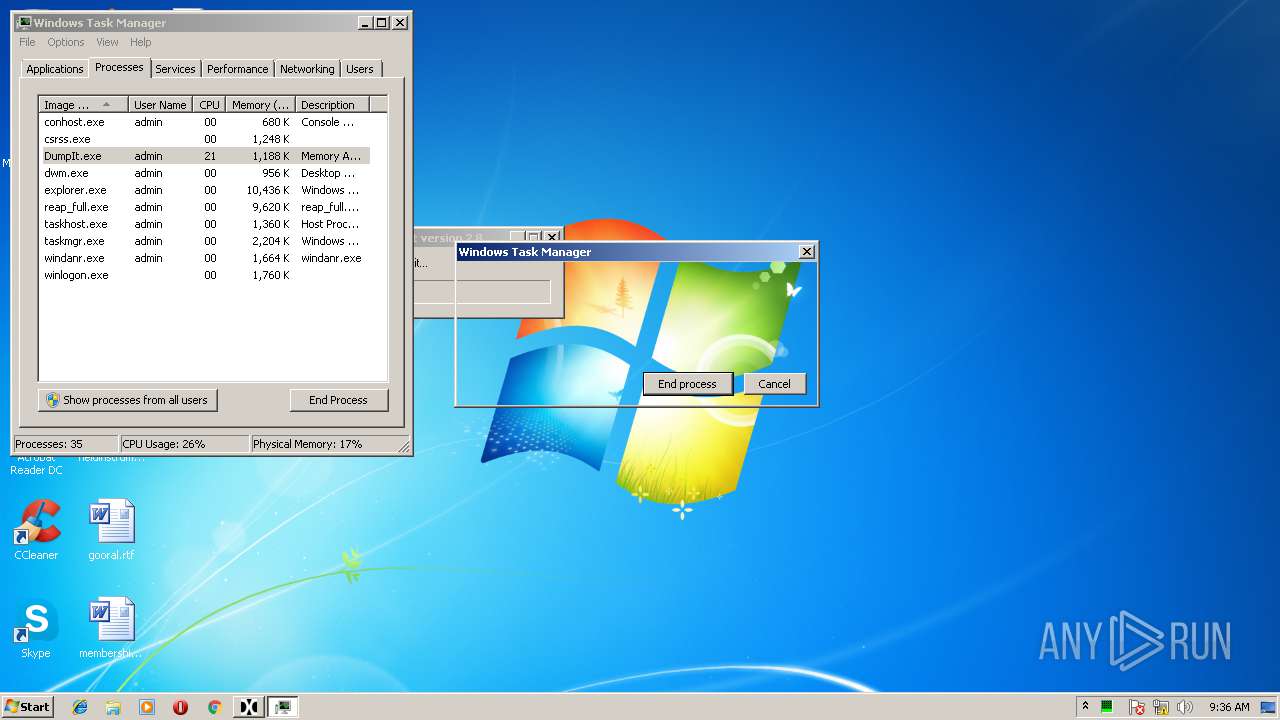
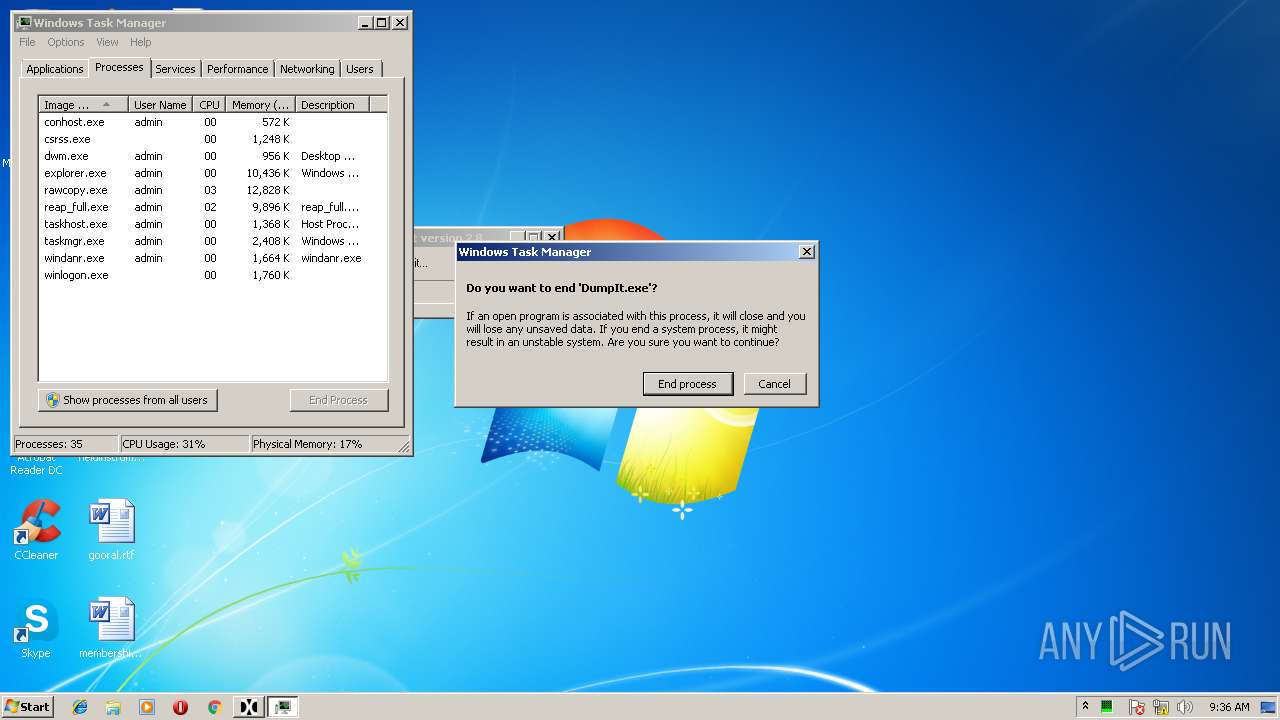
Application was dropped or rewritten from another process
- DumpIt.exe (PID: 388)
- rawcopy.exe (PID: 2300)
- rawcopy.exe (PID: 4040)
- extractusn.exe (PID: 3556)
- forecopy.exe (PID: 4072)
- NetworkOpenedFiles.exe (PID: 3000)
- pf.exe (PID: 1928)
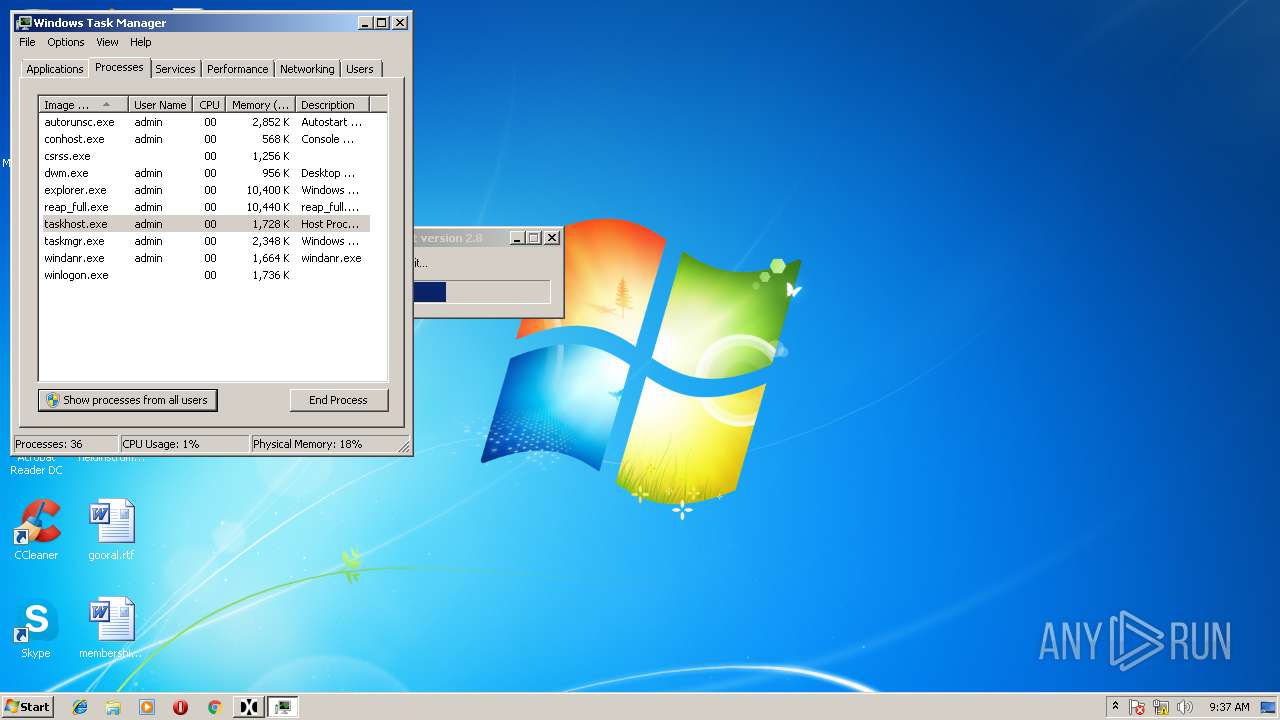
- autorunsc.exe (PID: 2140)
- usp.exe (PID: 1740)
- BrowsingHistoryView.exe (PID: 3004)
- listdlls.exe (PID: 1648)
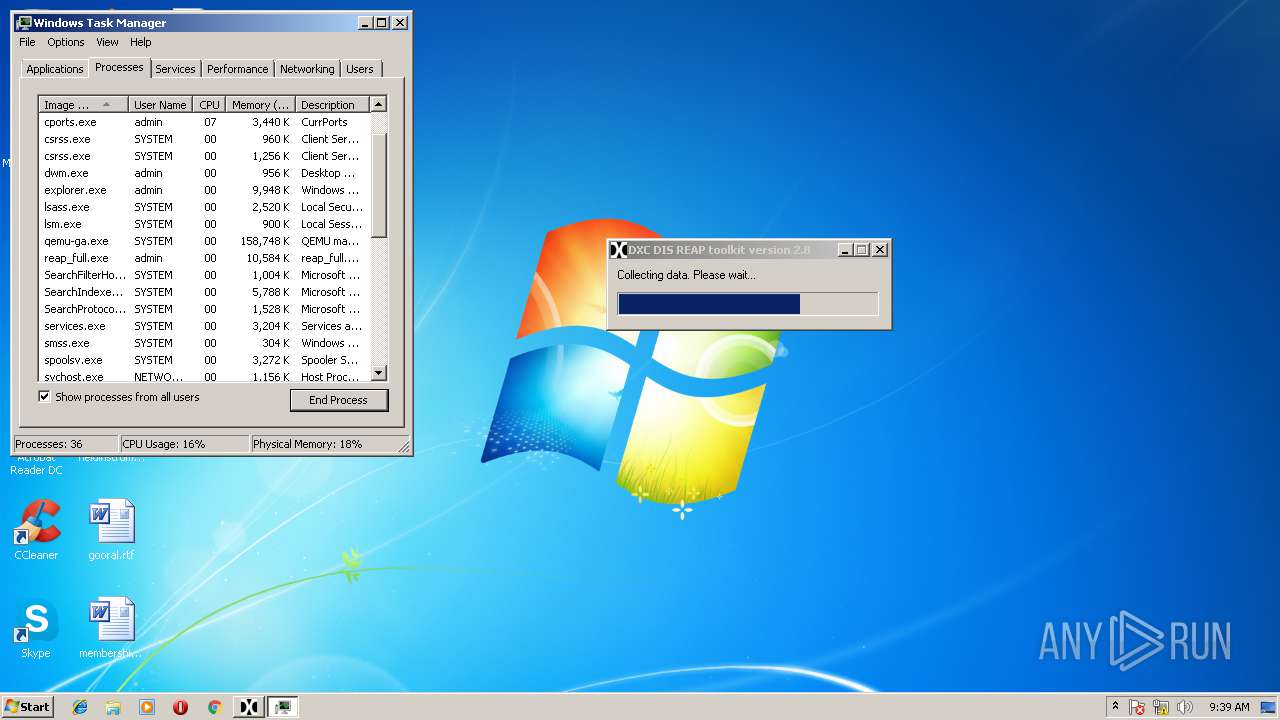
- cports.exe (PID: 3580)
- pslist.exe (PID: 3552)
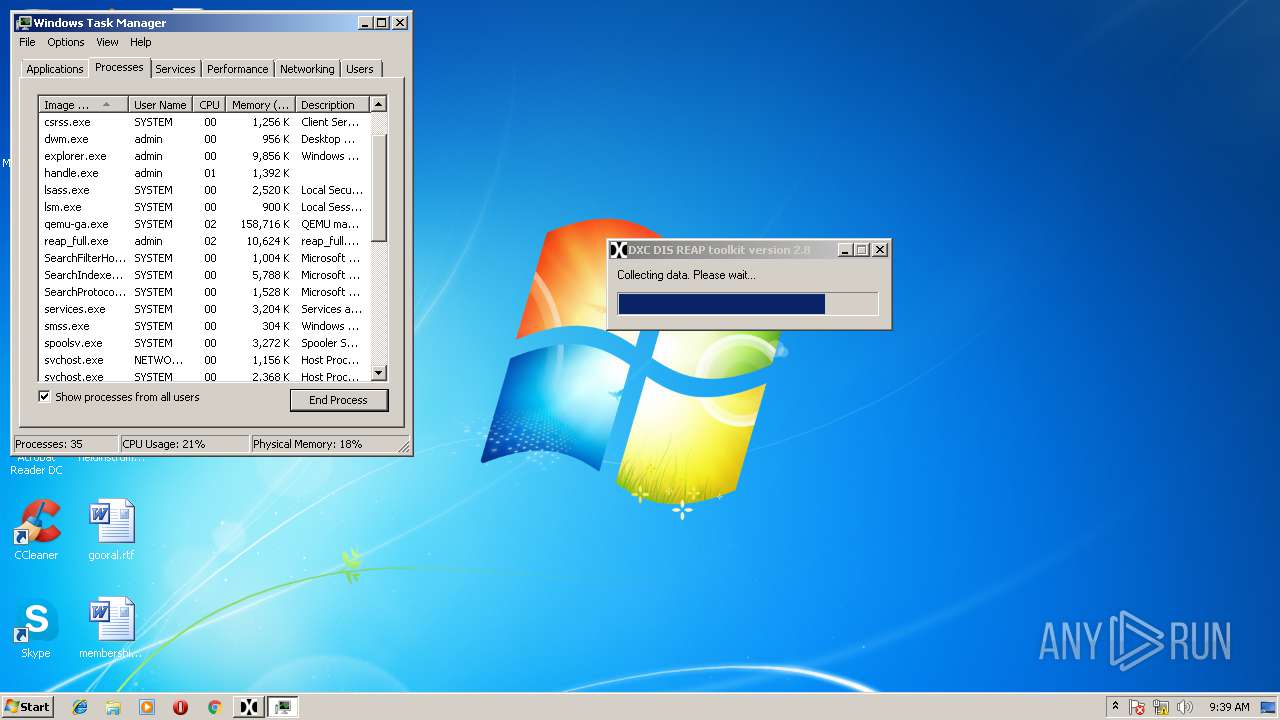
- handle.exe (PID: 2664)
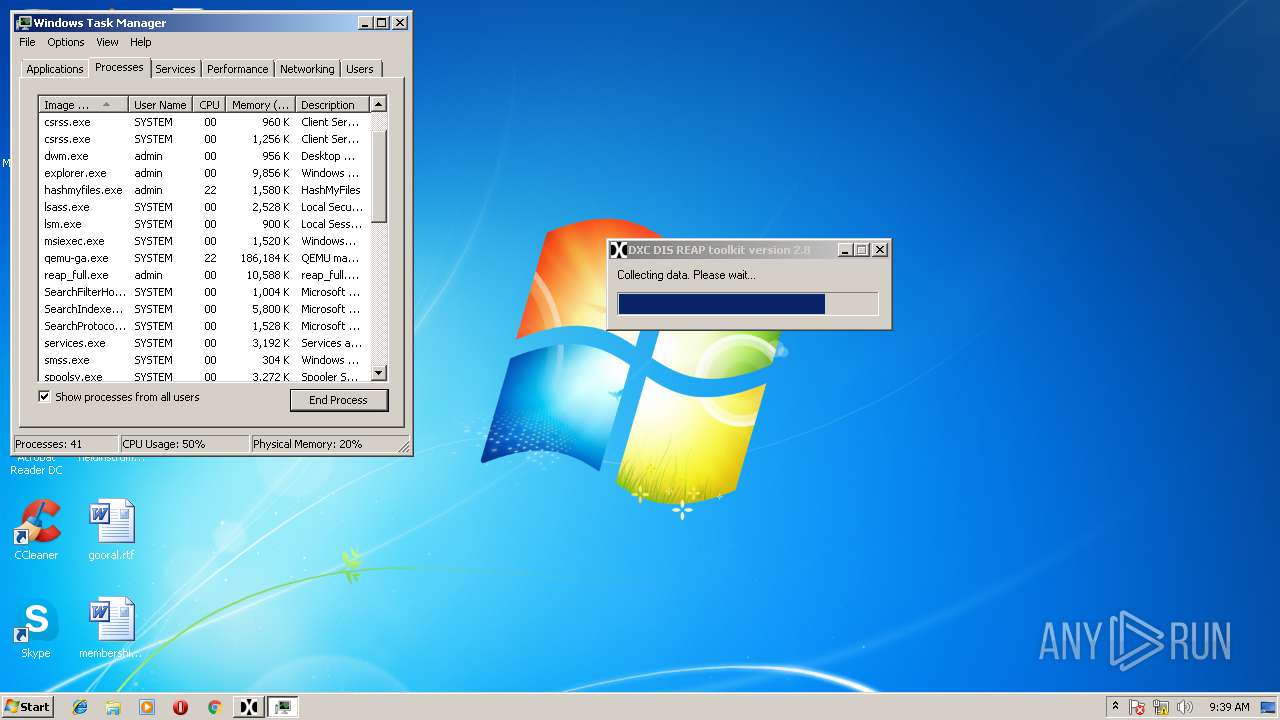
- hashmyfiles.exe (PID: 2748)
- hashmyfiles.exe (PID: 3456)
- 7za.exe (PID: 1072)
- psloggedon.exe (PID: 3308)
- pipelist.exe (PID: 236)
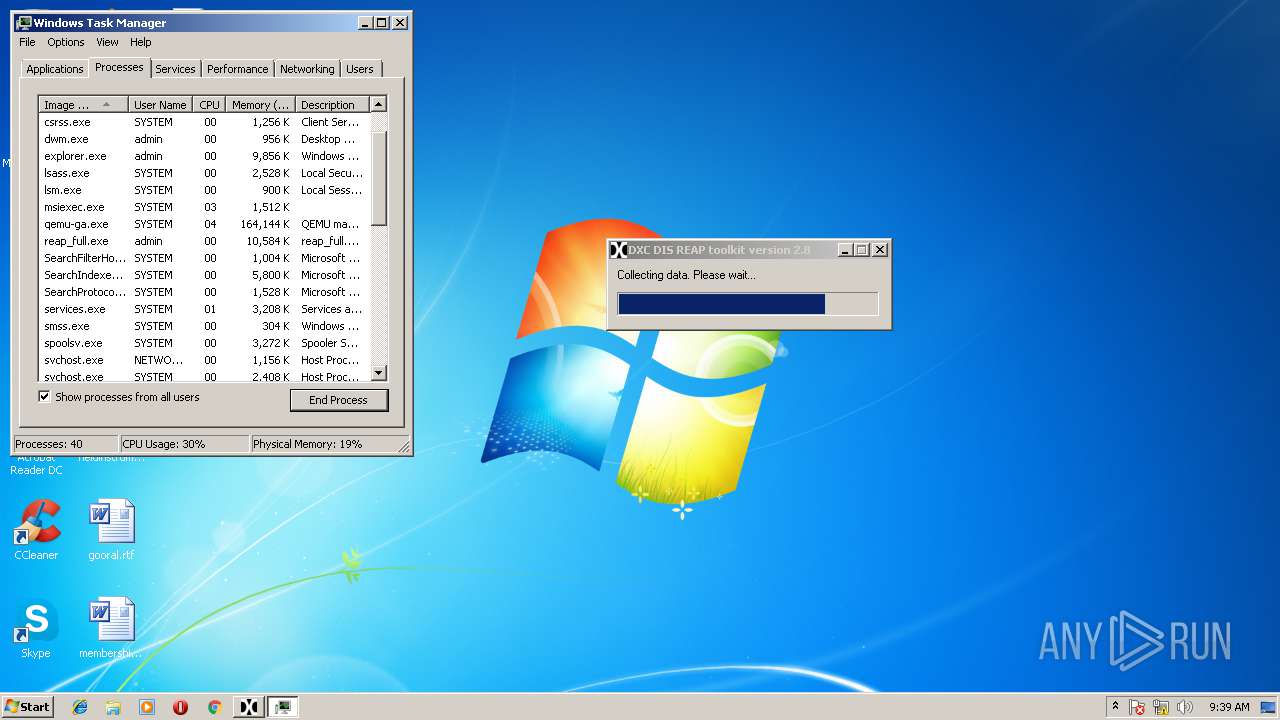
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3904)
- autorunsc.exe (PID: 2140)
- listdlls.exe (PID: 1648)
Uses Task Scheduler to run other applications
- reap_full.exe (PID: 3676)
Changes settings of System certificates
- autorunsc.exe (PID: 2140)
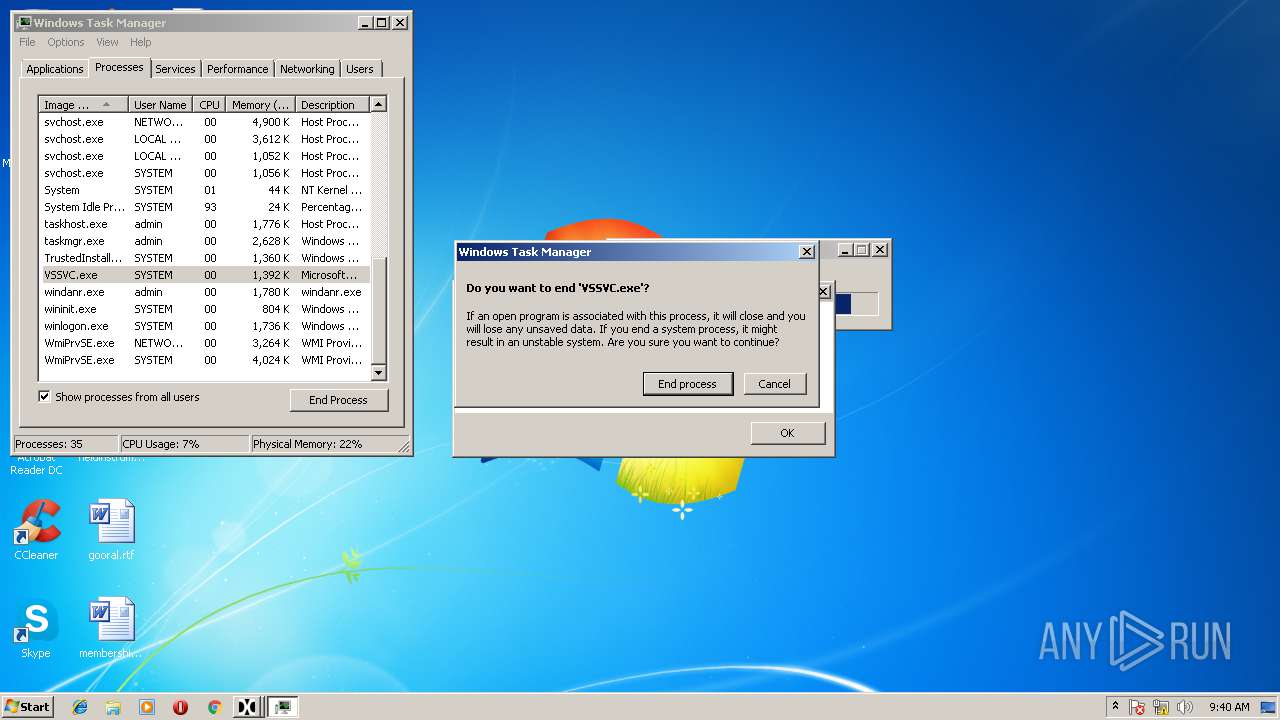
Starts VSSADMIN.EXE (used for deleting shadow copies)
- reap_full.exe (PID: 3676)
SUSPICIOUS
Creates files in the driver directory
- DumpIt.exe (PID: 388)
- handle.exe (PID: 2664)
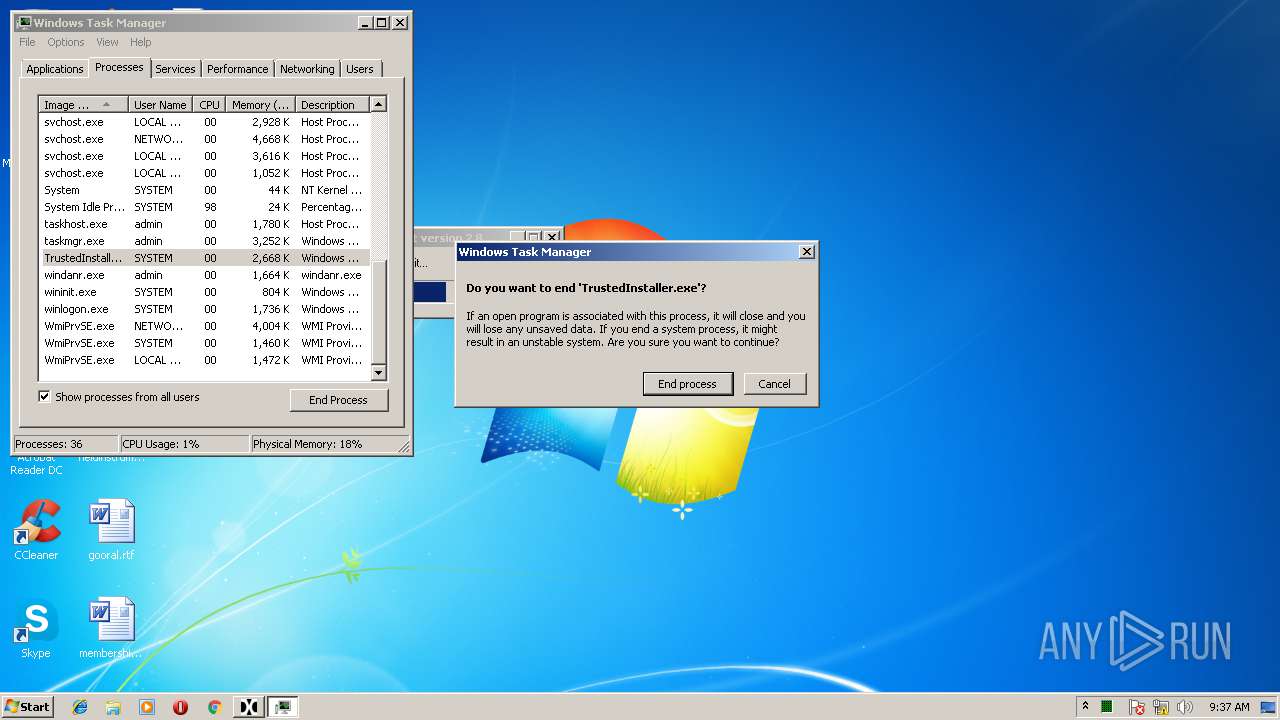
Modifies files in the system directory
- DumpIt.exe (PID: 388)
- rawcopy.exe (PID: 2300)
- rawcopy.exe (PID: 4040)
- extractusn.exe (PID: 3556)
- NetworkOpenedFiles.exe (PID: 3000)
- reap_full.exe (PID: 3676)
- pf.exe (PID: 1928)
- TrustedInstaller.exe (PID: 2528)
- BrowsingHistoryView.exe (PID: 3004)
- handle.exe (PID: 2664)
- powershell.exe (PID: 2384)
- TrustedInstaller.exe (PID: 2080)
- hashmyfiles.exe (PID: 3456)
- hashmyfiles.exe (PID: 2748)
- 7za.exe (PID: 1072)
- forecopy.exe (PID: 4072)
- cports.exe (PID: 3580)
Creates files in the Windows directory
- rawcopy.exe (PID: 2300)
- DumpIt.exe (PID: 388)
- rawcopy.exe (PID: 4040)
- extractusn.exe (PID: 3556)
- reap_full.exe (PID: 3676)
- forecopy.exe (PID: 4072)
- cmd.exe (PID: 3400)
- TrustedInstaller.exe (PID: 2528)
- BrowsingHistoryView.exe (PID: 3004)
- cports.exe (PID: 3580)
- handle.exe (PID: 2664)
- powershell.exe (PID: 2384)
- hashmyfiles.exe (PID: 2748)
- hashmyfiles.exe (PID: 3456)
- 7za.exe (PID: 1072)
- NetworkOpenedFiles.exe (PID: 3000)
Creates or modifies windows services
- DumpIt.exe (PID: 388)
- handle.exe (PID: 2664)
Removes files from Windows directory
- DumpIt.exe (PID: 388)
- reap_full.exe (PID: 3676)
- handle.exe (PID: 2664)
- 7za.exe (PID: 1072)
Starts CMD.EXE for commands execution
- reap_full.exe (PID: 3676)
- cmd.exe (PID: 3400)
- netstat.exe (PID: 3620)
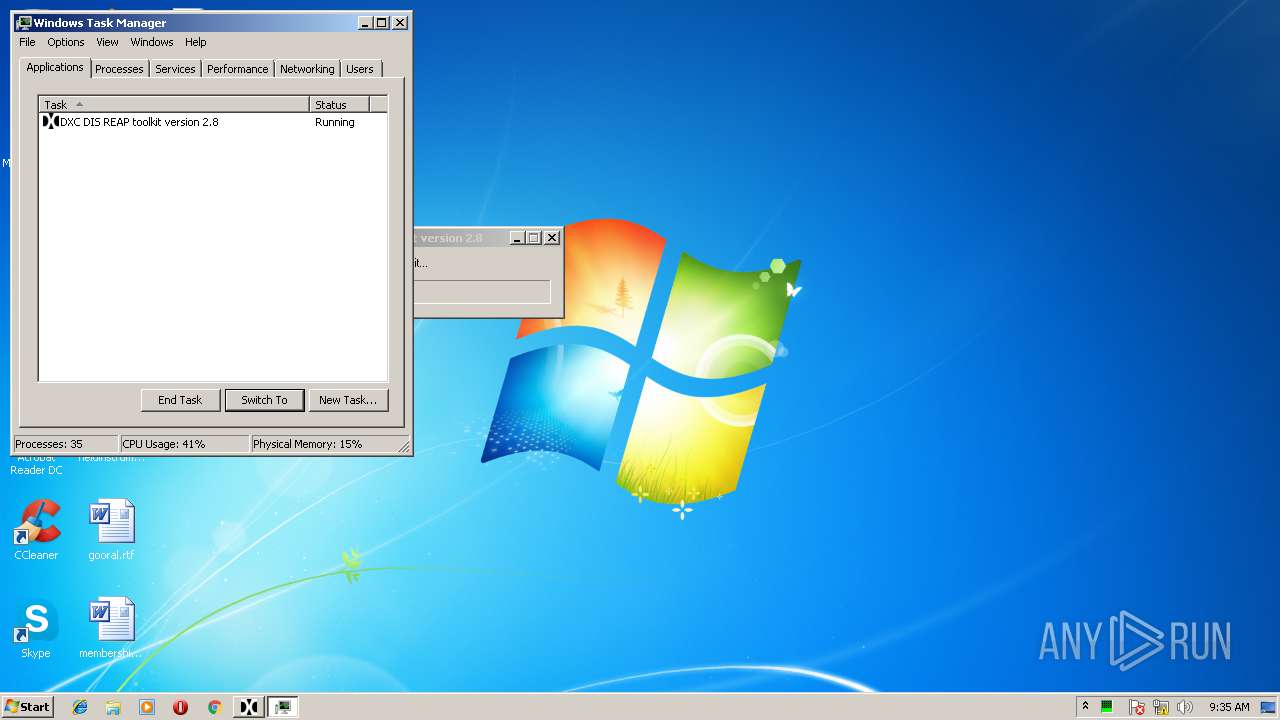
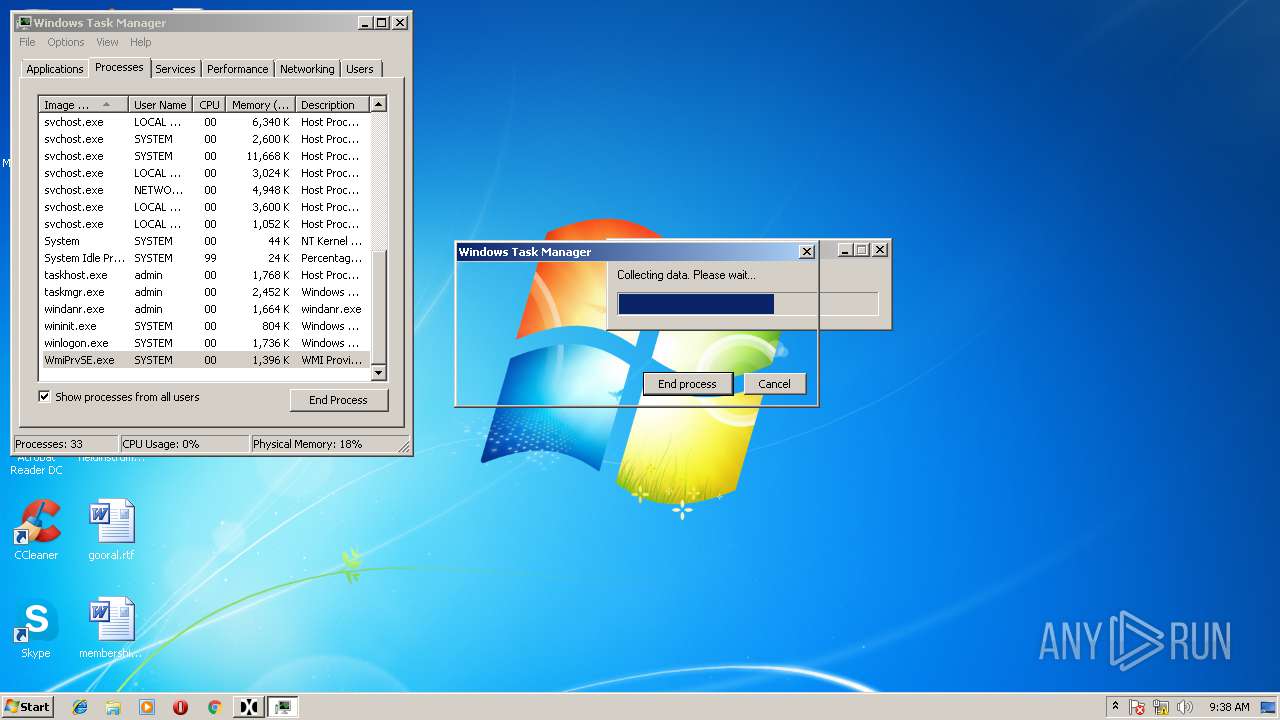
Application launched itself
- taskmgr.exe (PID: 3452)
Creates files in the user directory
- BrowsingHistoryView.exe (PID: 3004)
Adds / modifies Windows certificates
- autorunsc.exe (PID: 2140)
Uses TASKLIST.EXE to query information about running processes
- reap_full.exe (PID: 3676)
Executes PowerShell scripts
- reap_full.exe (PID: 3676)
INFO
Dropped object may contain URL's
- forecopy.exe (PID: 4072)
- autorunsc.exe (PID: 2140)
- cports.exe (PID: 3580)
- reap_full.exe (PID: 3676)
Reads settings of System Certificates
- autorunsc.exe (PID: 2140)
Dropped object may contain Bitcoin addresses
- reap_full.exe (PID: 3676)
- hashmyfiles.exe (PID: 2748)
- hashmyfiles.exe (PID: 3456)
Loads the .NET runtime environment
- powershell.exe (PID: 2384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:02:16 17:38:57+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 581120 |
| InitializedDataSize: | 10472960 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x27f4a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Feb-2018 16:38:57 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 16-Feb-2018 16:38:57 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008DD2E | 0x0008DE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67588 |
.rdata | 0x0008F000 | 0x0002E10E | 0x0002E200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.76073 |
.data | 0x000BE000 | 0x00008F74 | 0x00005200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.19881 |
.rsrc | 0x000C7000 | 0x009C26EC | 0x009C2800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99969 |
.reloc | 0x00A8A000 | 0x00007130 | 0x00007200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.78238 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.39264 | 1018 | Latin 1 / Western European | English - United Kingdom | RT_MANIFEST |
2 | 3.38607 | 1128 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
3 | 2.36962 | 4264 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
4 | 2.03429 | 9640 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
7 | 3.34702 | 1428 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
8 | 3.2817 | 1674 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
9 | 3.28849 | 1168 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
10 | 3.28373 | 1532 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
11 | 3.26322 | 1628 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
12 | 3.25812 | 1126 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
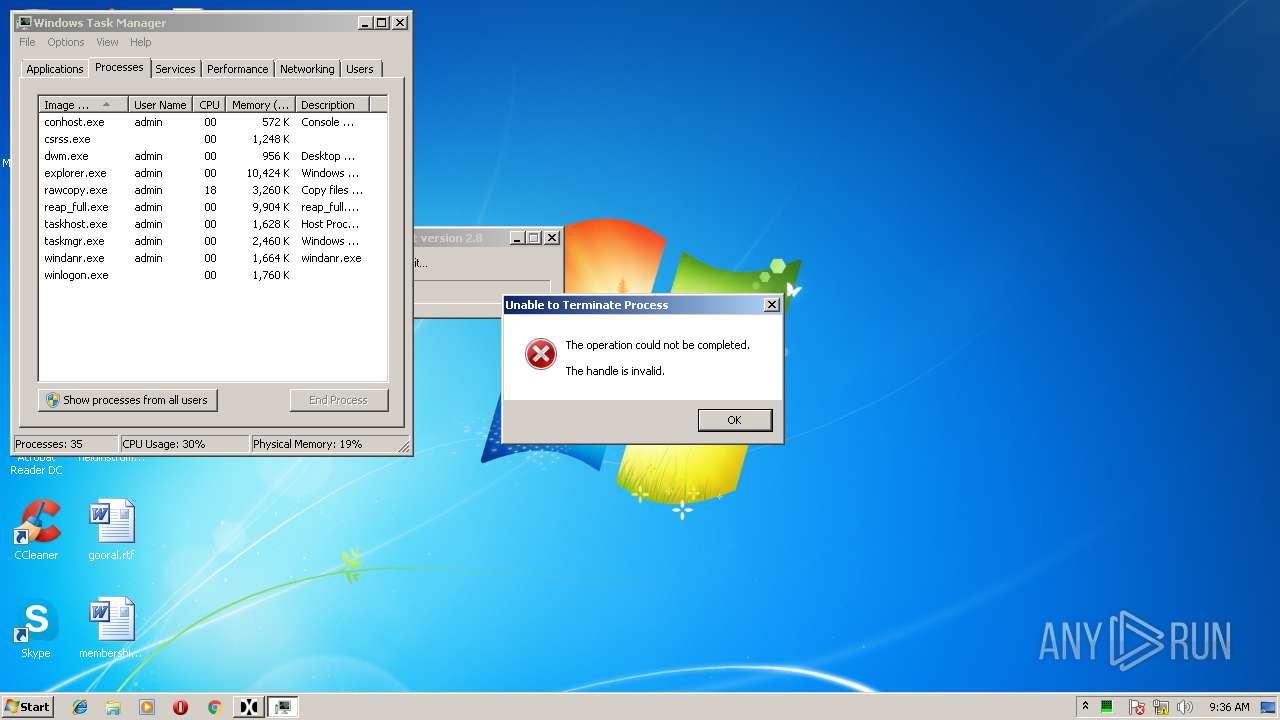
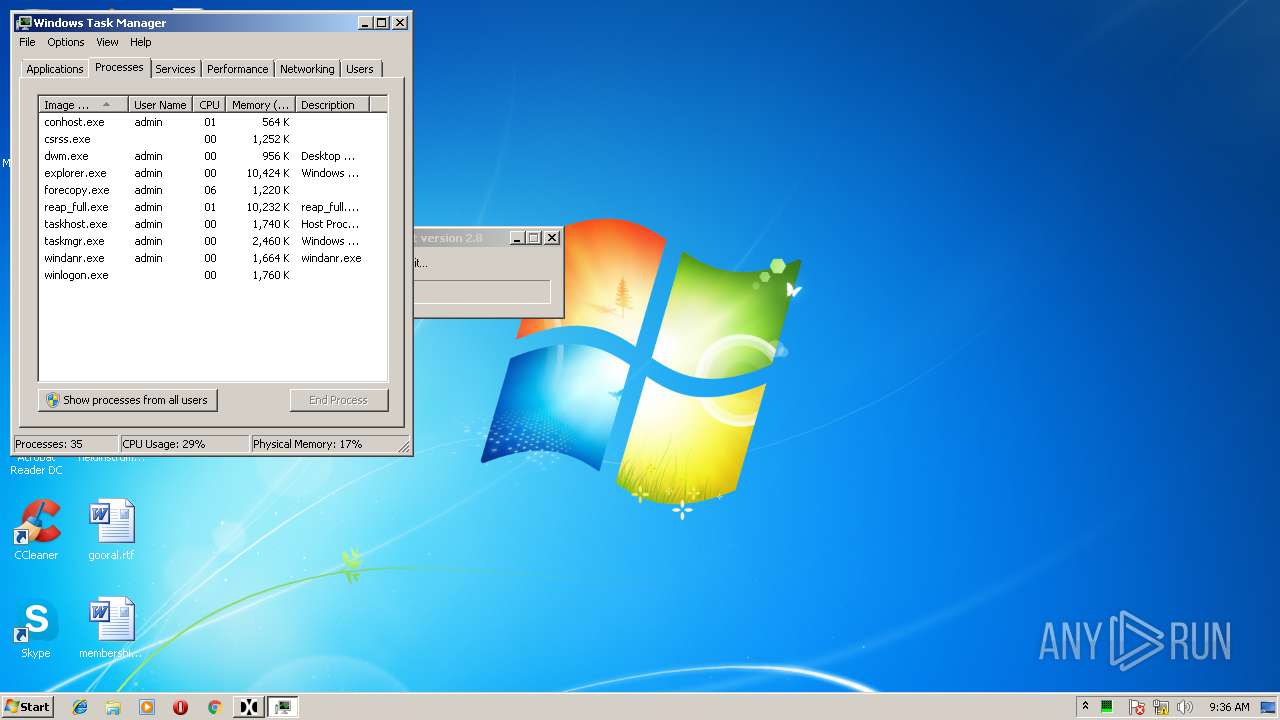
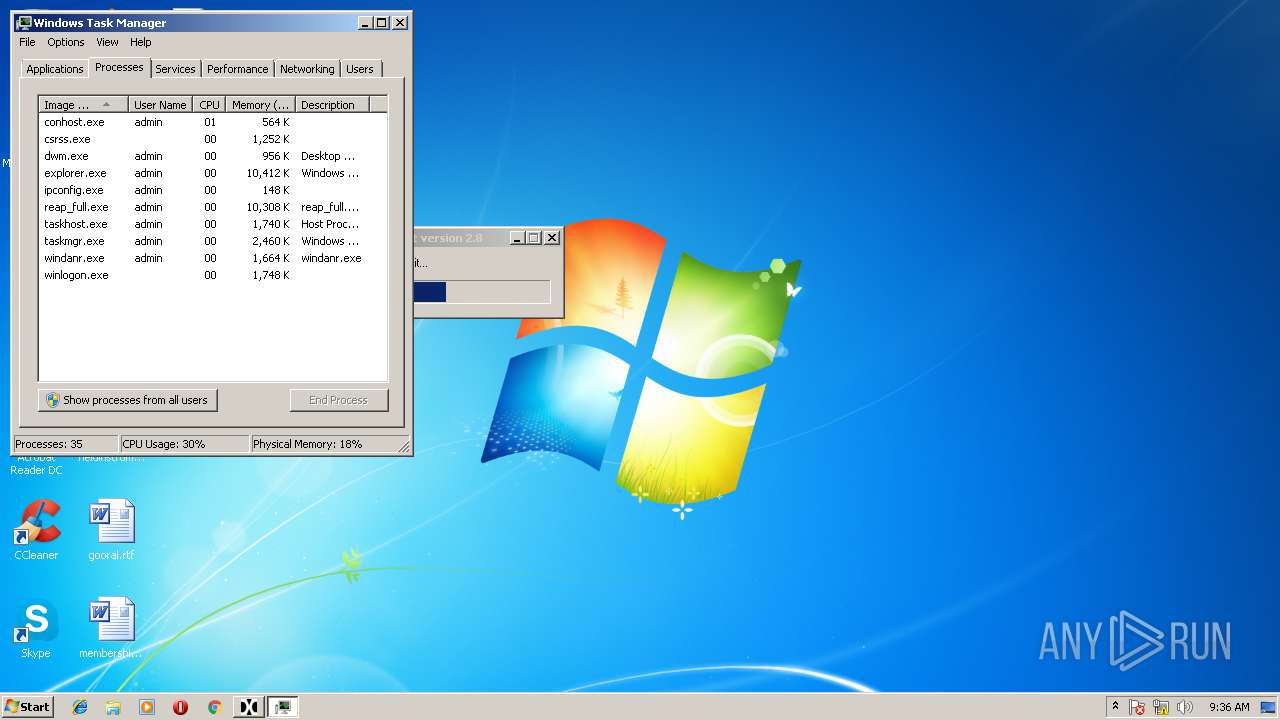
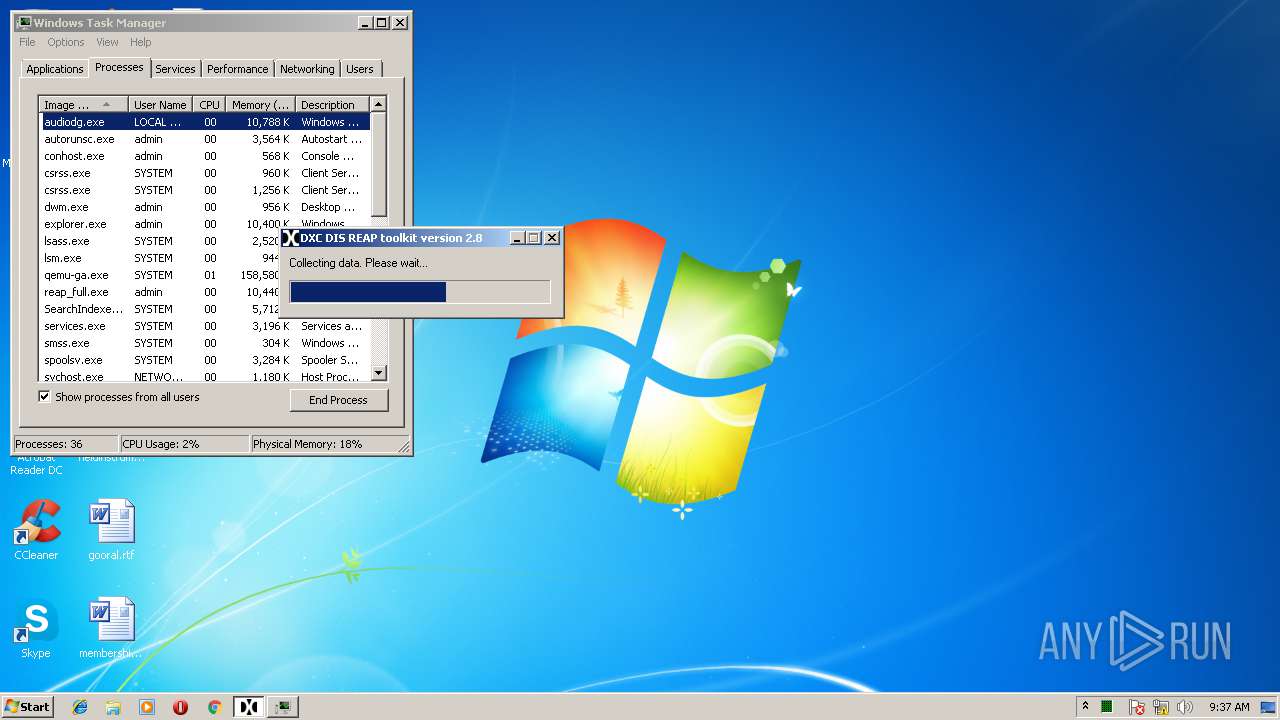
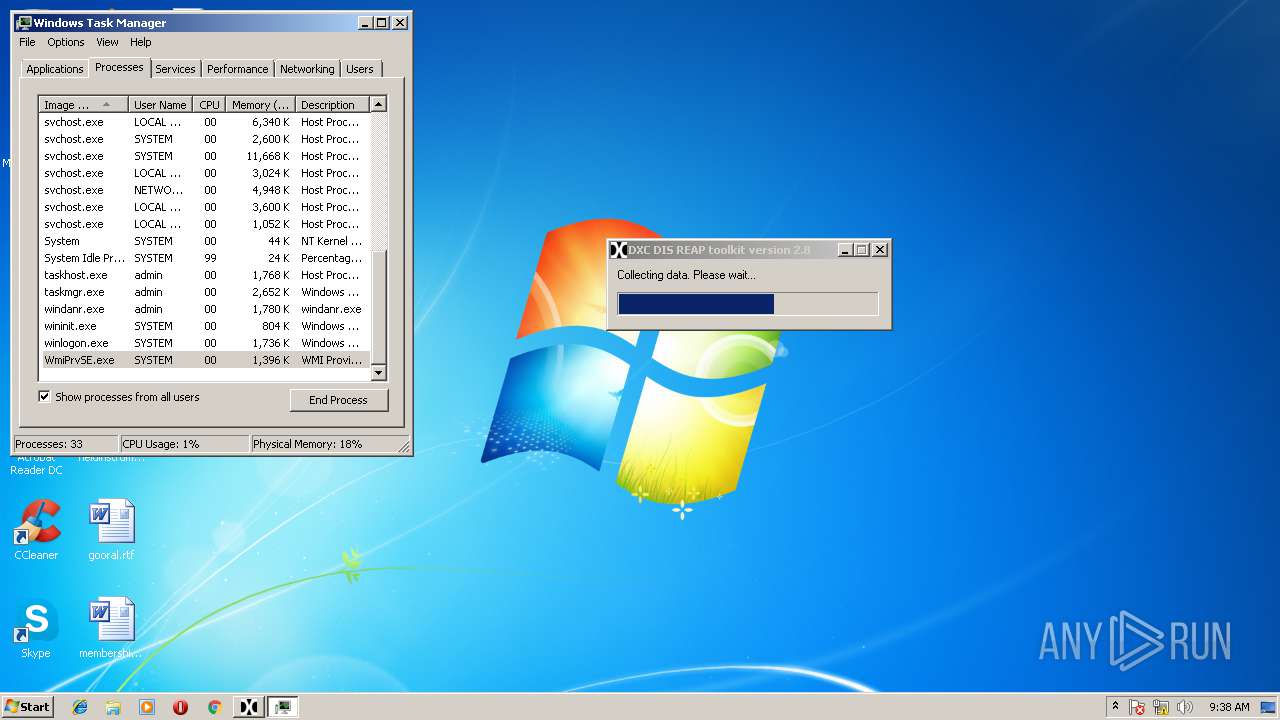
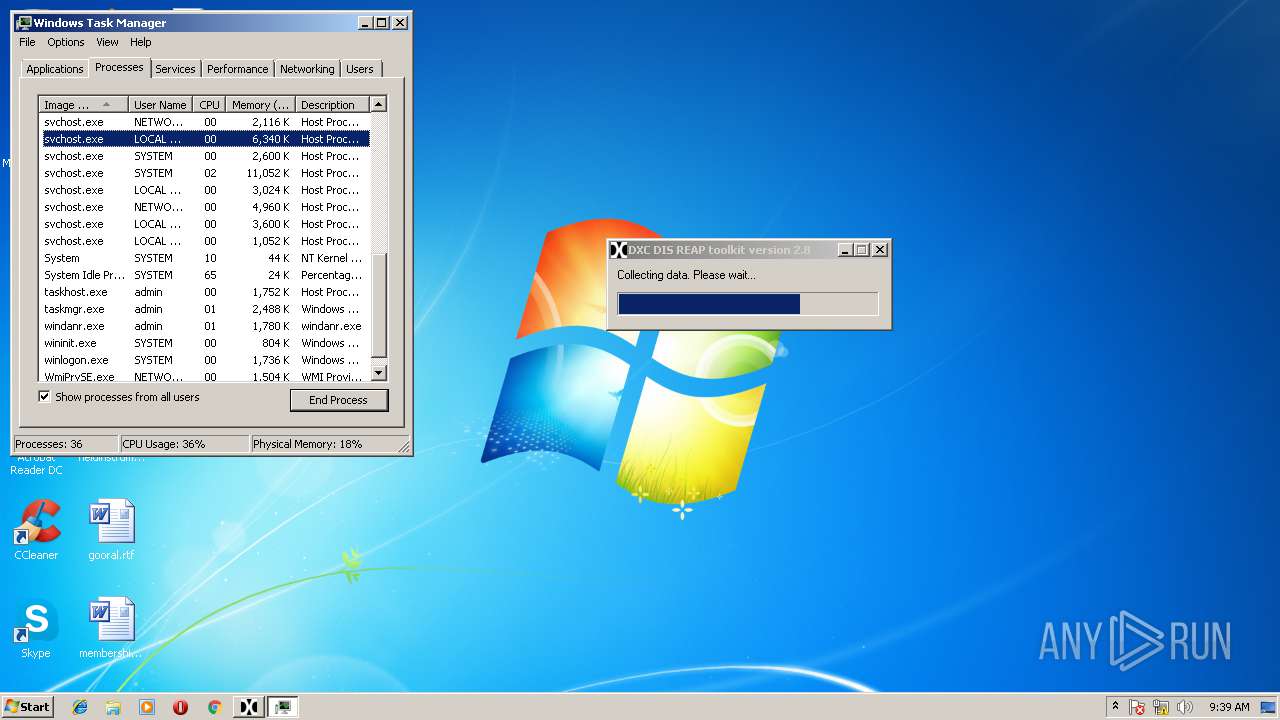
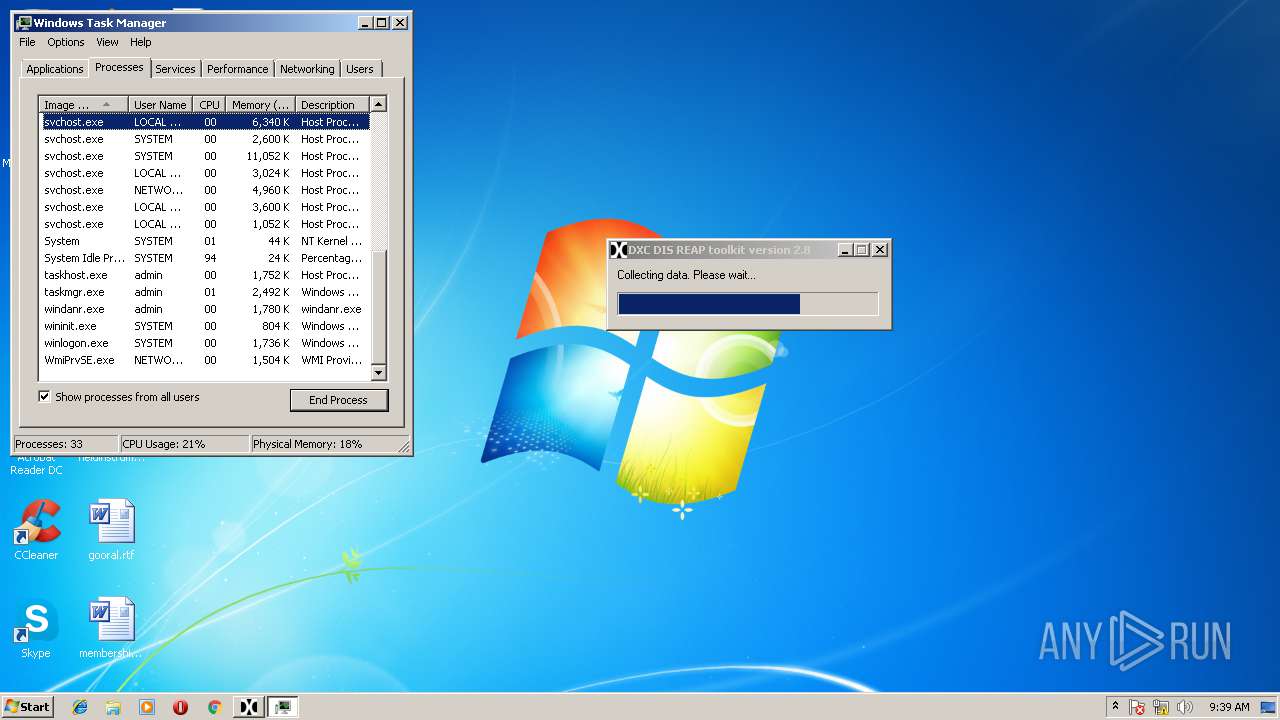
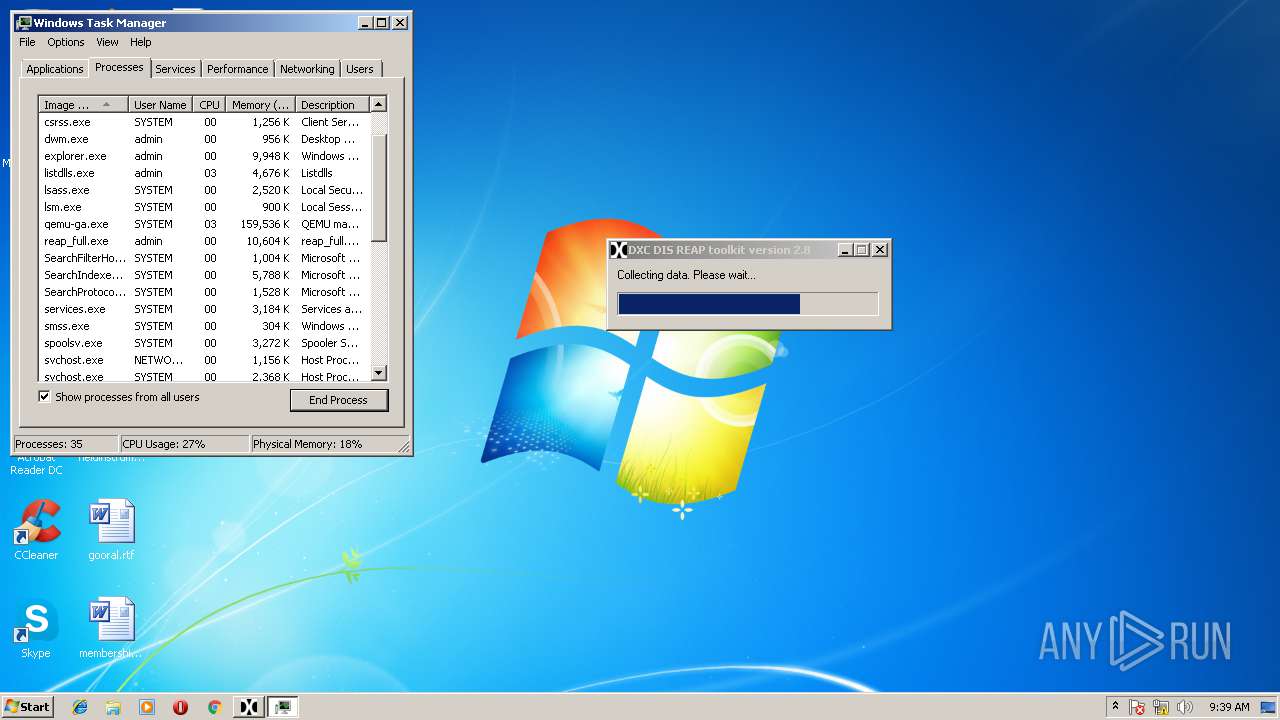
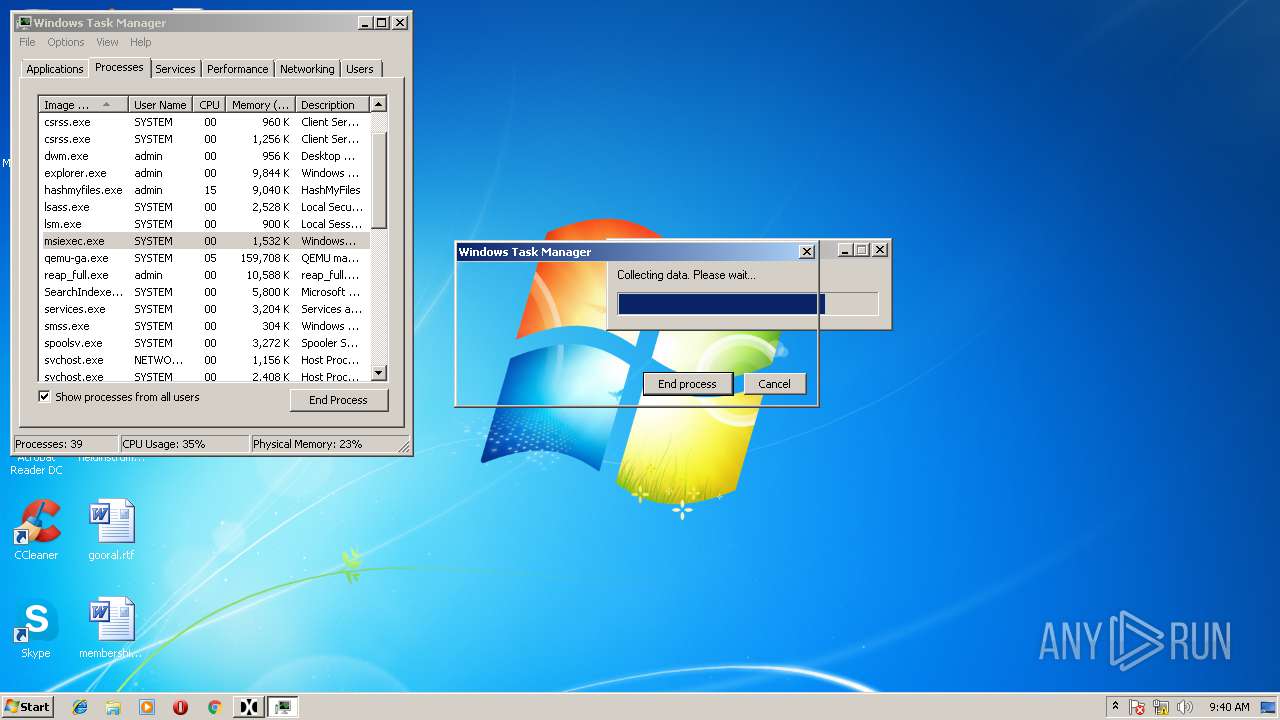
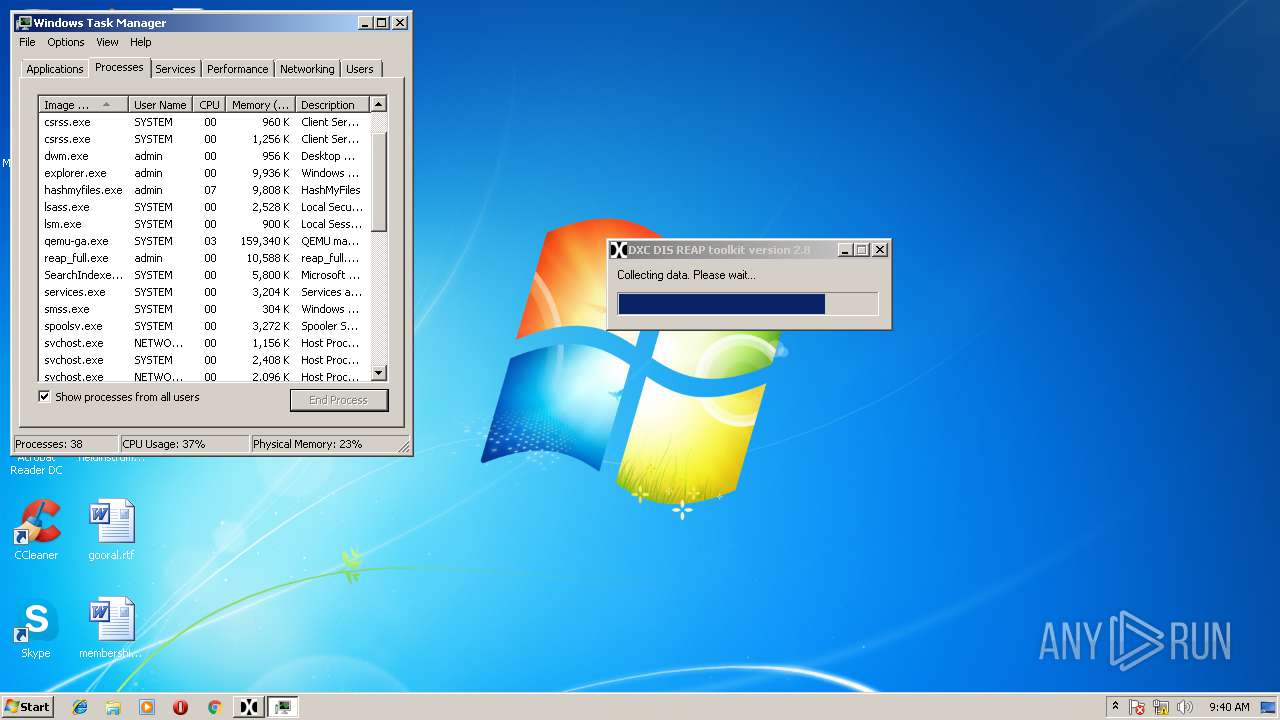
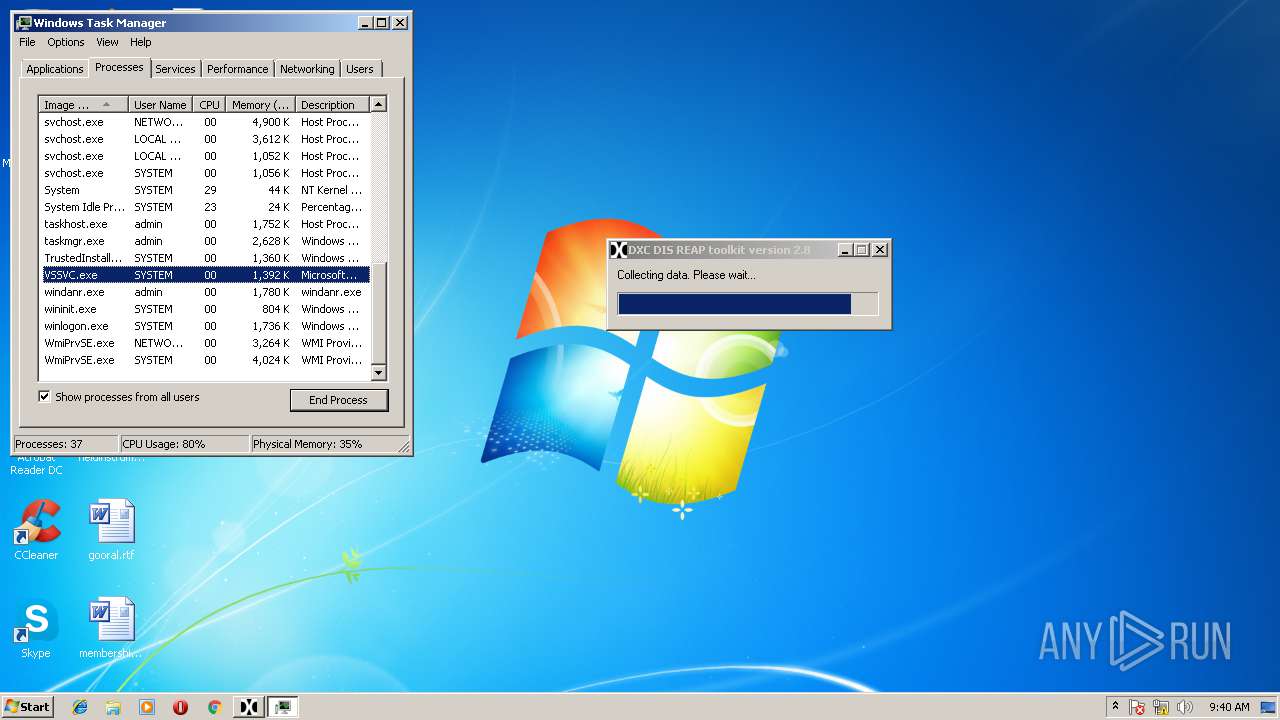
Total processes
140
Monitored processes
63
Malicious processes
11
Suspicious processes
11
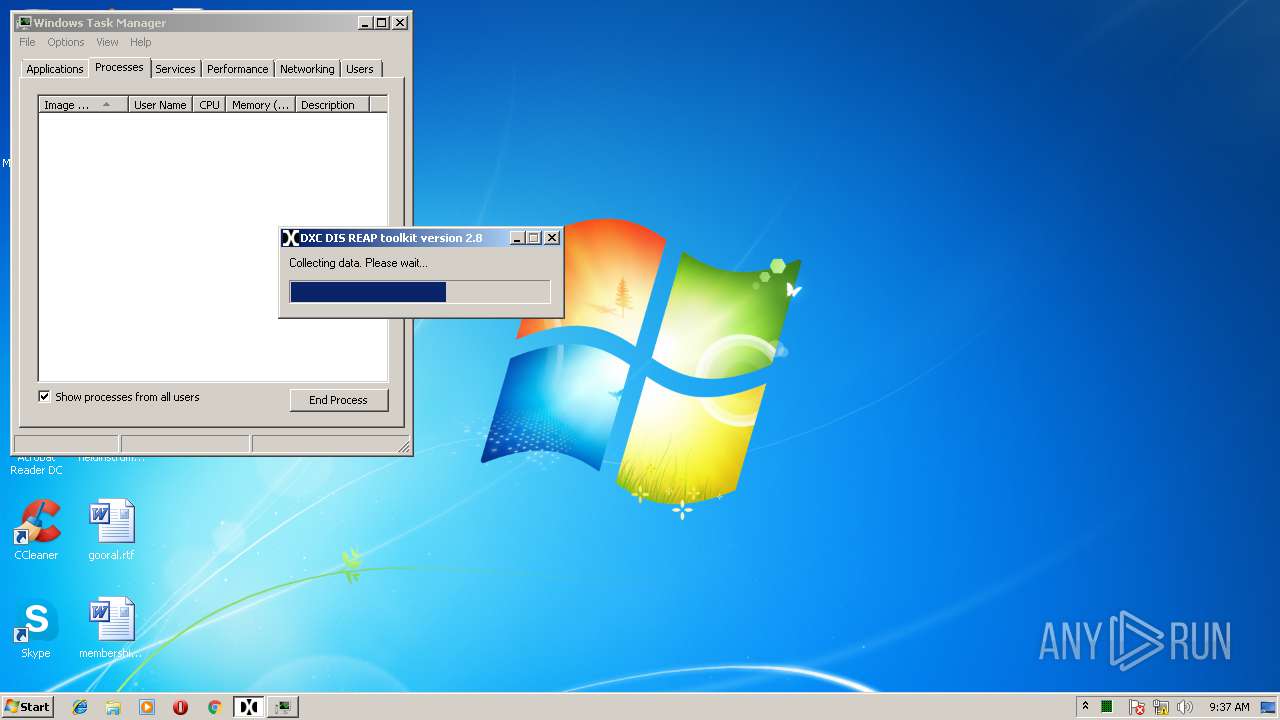
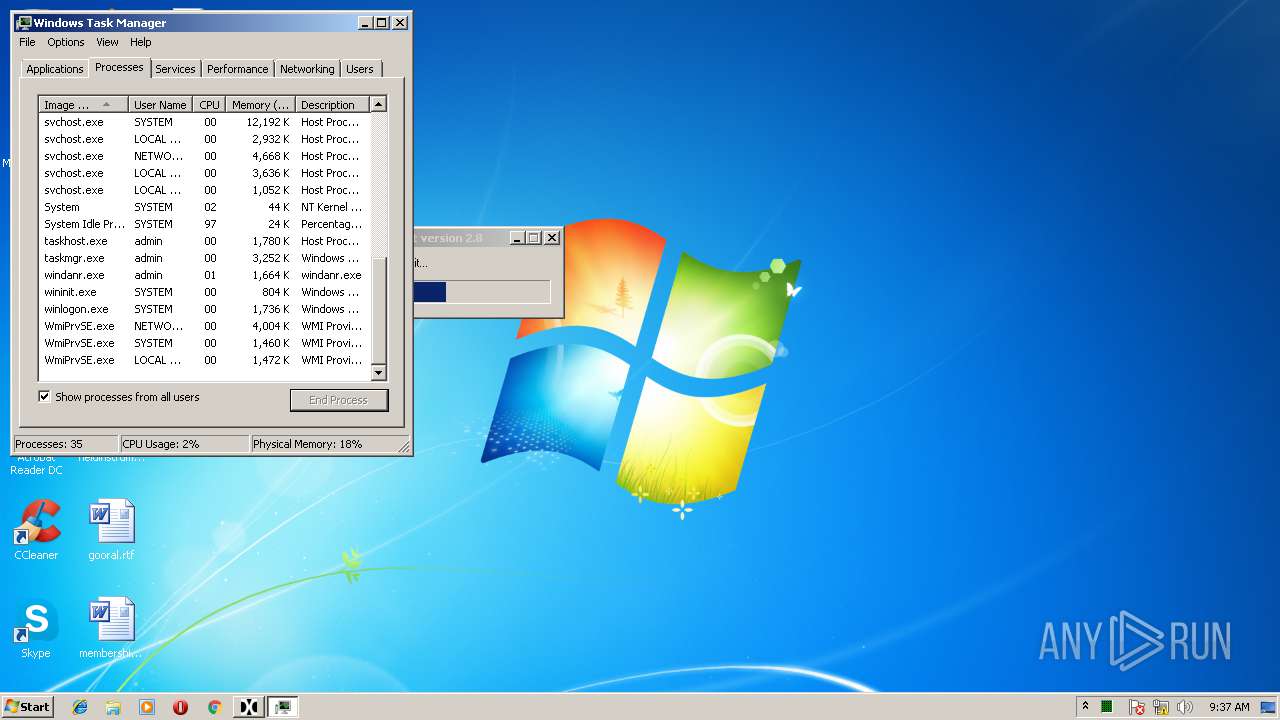
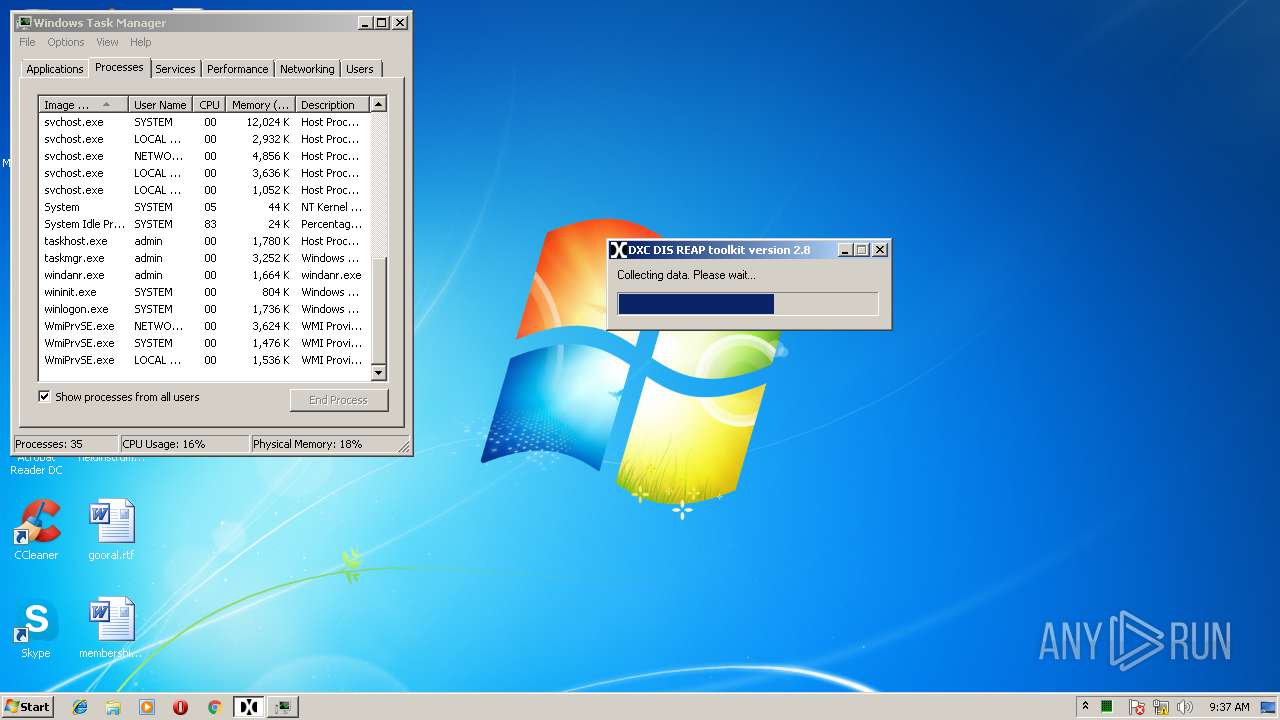
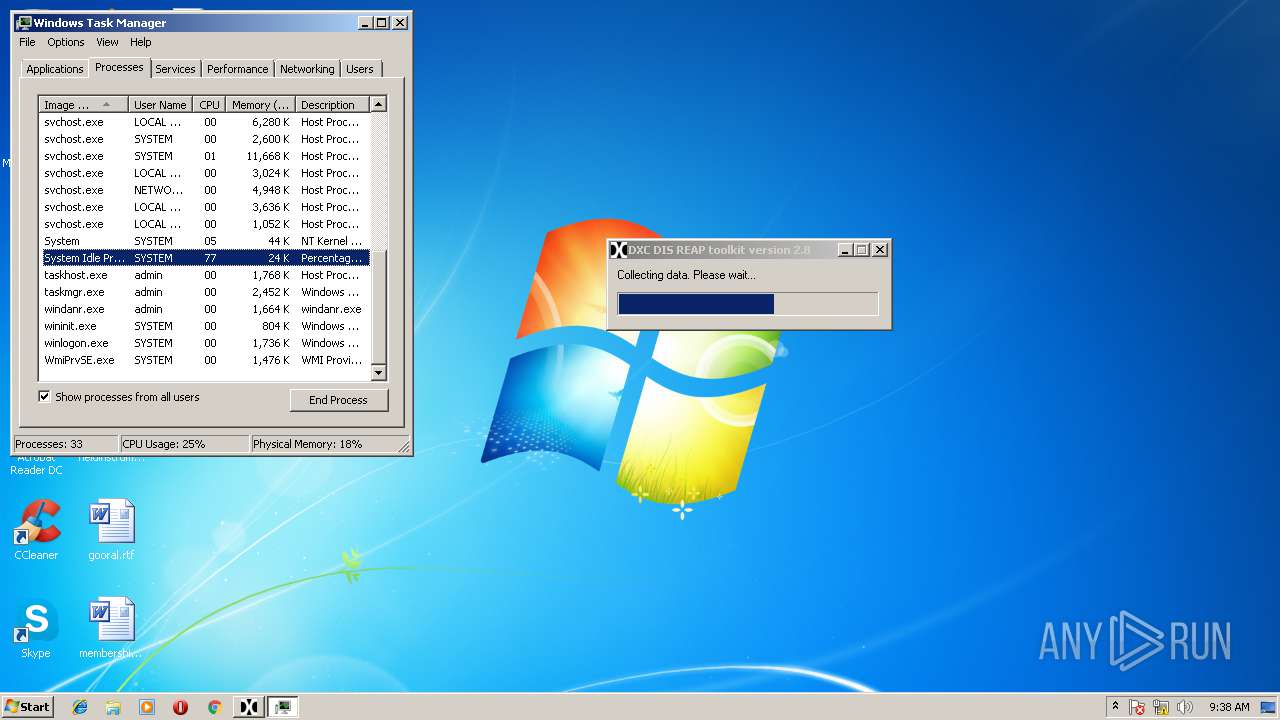
Behavior graph
Click at the process to see the details
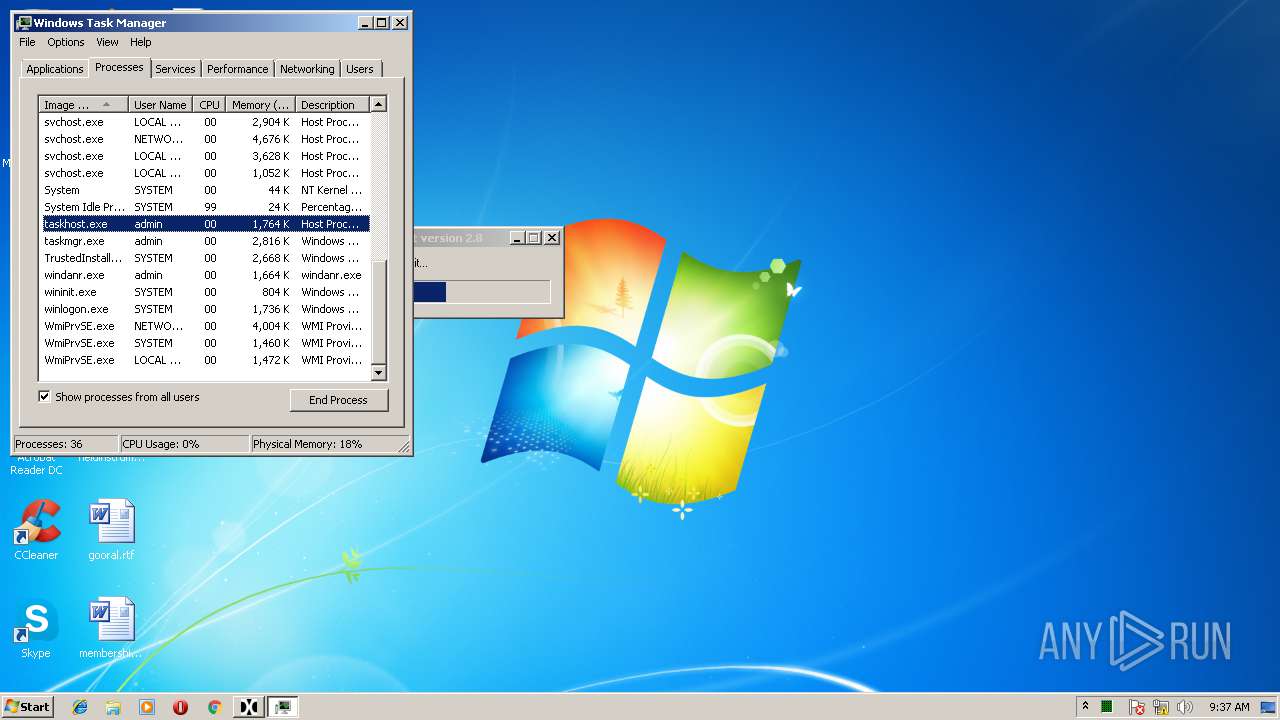
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | pipelist.exe | C:\Windows\system32\pipelist.exe | — | reap_full.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 360 | "C:\Windows\system32\klist.exe" tgt -li 0x112bf | C:\Windows\system32\klist.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Tool for managing the Kerberos ticket cache Exit code: 3221225569 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 388 | DumpIt.exe /O "C:\Windows\system32\reap_tempdir\PC.bin" /N /Q | C:\Windows\system32\DumpIt.exe | — | reap_full.exe | |||||||||||
User: admin Company: Comae Technologies FZE Integrity Level: HIGH Description: Memory Acquisition Tool Exit code: 1 Version: 3.0.0.0 Modules
| |||||||||||||||
| 660 | "C:\Windows\system32\taskmgr.exe" /1 | C:\Windows\system32\taskmgr.exe | taskmgr.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 824 | C:\Windows\system32\cmd.exe /c hashmyfiles.exe /wildcard c:\*.exe 3 /scomma "C:\Windows\system32\reap_tempdir\c_exe_hashes.csv" | C:\Windows\system32\cmd.exe | — | reap_full.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
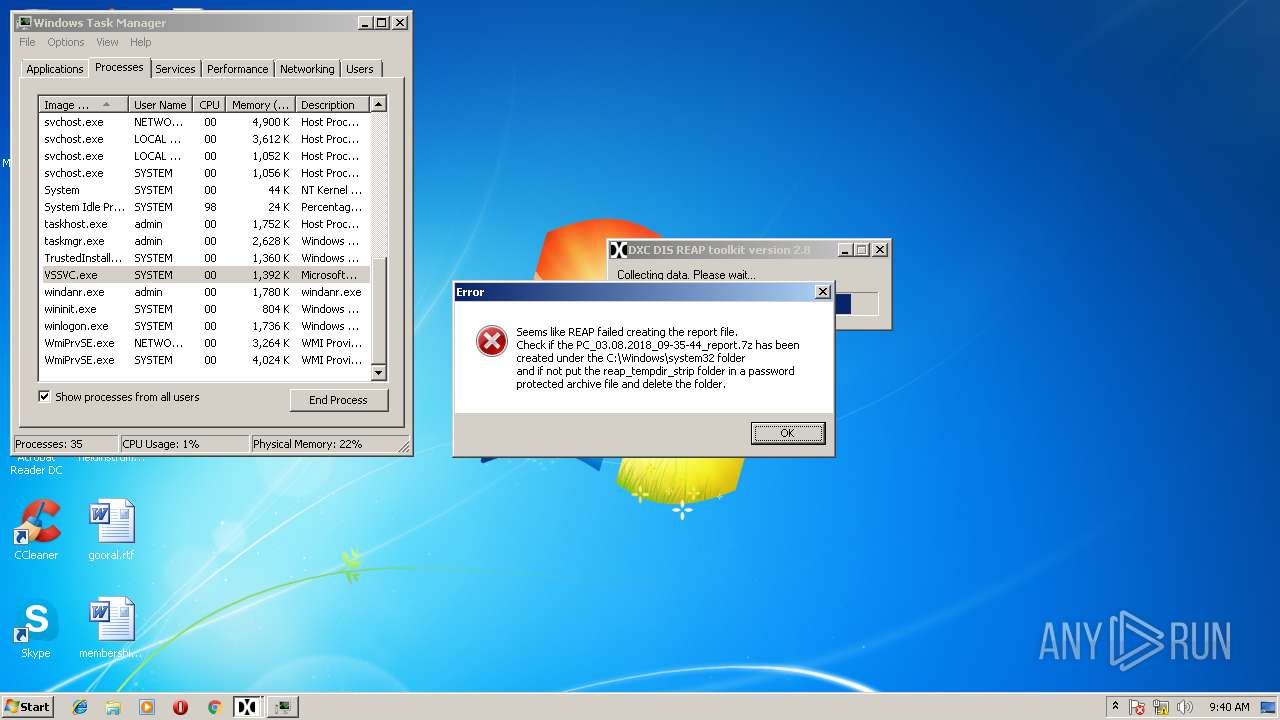
| 1072 | 7za.exe a -bsp2 -mhe -mmt -mx9 PC_03.08.2018_09-35-44_report.7z reap_tempdir -pwR~/+FxAWT.c | C:\Windows\system32\7za.exe | — | reap_full.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Standalone Console Exit code: 8 Version: 16.02 Modules
| |||||||||||||||
| 1084 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1088 | "C:\Windows\system32\klist.exe" tickets -li 0x112bf | C:\Windows\system32\klist.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Tool for managing the Kerberos ticket cache Exit code: 3221225569 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1172 | ipconfig /all | C:\Windows\system32\ipconfig.exe | — | reap_full.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1400 | arp -a | C:\Windows\system32\arp.exe | — | reap_full.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Arp Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 050
Read events
2 860
Write events
188
Delete events
2
Modification events
| (PID) Process: | (388) DumpIt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\DumpIt |
| Operation: | write | Name: | Type |
Value: 2 | |||
| (PID) Process: | (388) DumpIt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\DumpIt |
| Operation: | write | Name: | ImagePath |
Value: \??\C:\Windows\system32\Drivers\DumpIt.sys | |||
| (PID) Process: | (388) DumpIt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\DumpIt |
| Operation: | write | Name: | Start |
Value: 3 | |||
| (PID) Process: | (388) DumpIt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\DumpIt |
| Operation: | write | Name: | DependOnService |
Value: FltMgr | |||
| (PID) Process: | (388) DumpIt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\DumpIt |
| Operation: | write | Name: | Group |
Value: FSFilter Activity Monitor | |||
| (PID) Process: | (388) DumpIt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\DumpIt\Instances |
| Operation: | write | Name: | DefaultInstance |
Value: DumpIt | |||
| (PID) Process: | (388) DumpIt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\DumpIt\Instances\DumpIt |
| Operation: | write | Name: | Altitude |
Value: 389110 | |||
| (PID) Process: | (388) DumpIt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\DumpIt\Instances\DumpIt |
| Operation: | write | Name: | Flags |
Value: 0 | |||
| (PID) Process: | (3308) psloggedon.exe | Key: | HKEY_CURRENT_USER\Software\Sysinternals\PsLoggedon |
| Operation: | write | Name: | EulaAccepted |
Value: 1 | |||
| (PID) Process: | (2108) systeminfo.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
18
Suspicious files
55
Text files
97
Unknown types
170
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3676 | reap_full.exe | C:\Users\admin\AppData\Local\Temp\aut50C2.tmp | — | |
MD5:— | SHA256:— | |||
| 3676 | reap_full.exe | C:\Users\admin\AppData\Local\Temp\aut5140.tmp | — | |
MD5:— | SHA256:— | |||
| 3676 | reap_full.exe | C:\Users\admin\AppData\Local\Temp\aut516F.tmp | — | |
MD5:— | SHA256:— | |||
| 3676 | reap_full.exe | C:\Users\admin\AppData\Local\Temp\aut519F.tmp | — | |
MD5:— | SHA256:— | |||
| 3676 | reap_full.exe | C:\Users\admin\AppData\Local\Temp\aut51C0.tmp | — | |
MD5:— | SHA256:— | |||
| 3676 | reap_full.exe | C:\Users\admin\AppData\Local\Temp\aut51D0.tmp | — | |
MD5:— | SHA256:— | |||
| 3676 | reap_full.exe | C:\Users\admin\AppData\Local\Temp\aut51E1.tmp | — | |
MD5:— | SHA256:— | |||
| 388 | DumpIt.exe | C:\Windows\system32\Drivers\DumpIt.sys | — | |
MD5:— | SHA256:— | |||
| 388 | DumpIt.exe | C:\Windows\system32\reap_tempdir\PC.bin | — | |
MD5:— | SHA256:— | |||
| 3676 | reap_full.exe | C:\Windows\system32\extractusn.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
18
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.51.123.27:80 | http://ocsp.verisign.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ%2FxkCfyHfJr7GQ6M658NRZ4SHo%2FAQUCPVR6Pv%2BPT1kNnxoz1t4qN%2B5xTcCEF5t3Ic3UIKEWBT0QtHYKiU%3D | NL | der | 1.64 Kb | whitelisted |
— | — | GET | 200 | 23.51.123.27:80 | http://ocsp.verisign.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEGxZ76nhAOEO4wa6j%2BApJVk%3D | NL | der | 1.71 Kb | whitelisted |
— | — | GET | 200 | 23.51.117.163:80 | http://s1.symcb.com/pca3-g5.crl | NL | der | 712 b | whitelisted |
— | — | GET | 304 | 2.16.186.89:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.51.123.27:80 | http://ocsp.thawte.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQwF4prw9S7mCbCEHD%2Fyl6nWPkczAQUe1tFz6%2FOy3r9MZIaarbzRutXSFACEEeXTXhzpbyrDS%2BzcBkvzl4%3D | NL | der | 1.52 Kb | whitelisted |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEAQJGBtf1btmdVNDtW%2BVUAg%3D | US | der | 471 b | whitelisted |
— | — | GET | 200 | 23.51.117.163:80 | http://crl.verisign.com/pca3.crl | NL | der | 1.05 Kb | whitelisted |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAt%2BEJA8OEkP%2Bi9nmoehp7k%3D | US | der | 471 b | whitelisted |
— | — | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/WinPCA.crl | unknown | der | 530 b | whitelisted |
— | — | GET | 200 | 178.255.83.1:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | GB | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 2.16.186.89:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
— | — | 2.16.186.74:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
— | — | 23.51.117.163:80 | crl.verisign.com | Akamai Technologies, Inc. | NL | whitelisted |
— | — | 23.51.123.27:80 | ocsp.verisign.com | Akamai Technologies, Inc. | NL | whitelisted |
— | — | 178.255.83.1:80 | ocsp.usertrust.com | CCANET Limited | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
crl.verisign.com |
| whitelisted |
ocsp.verisign.com |
| whitelisted |
sf.symcd.com |
| whitelisted |
s2.symcb.com |
| whitelisted |
s1.symcb.com |
| whitelisted |
sv.symcd.com |
| shared |
sv.symcb.com |
| whitelisted |