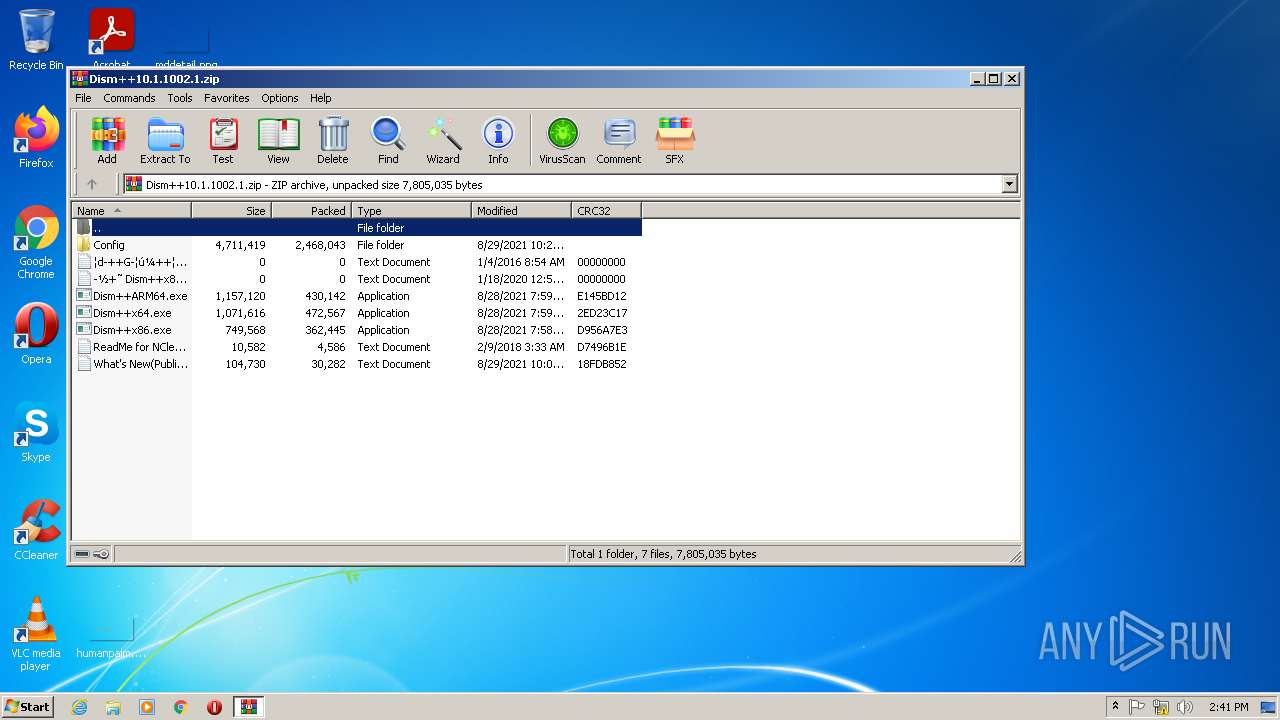
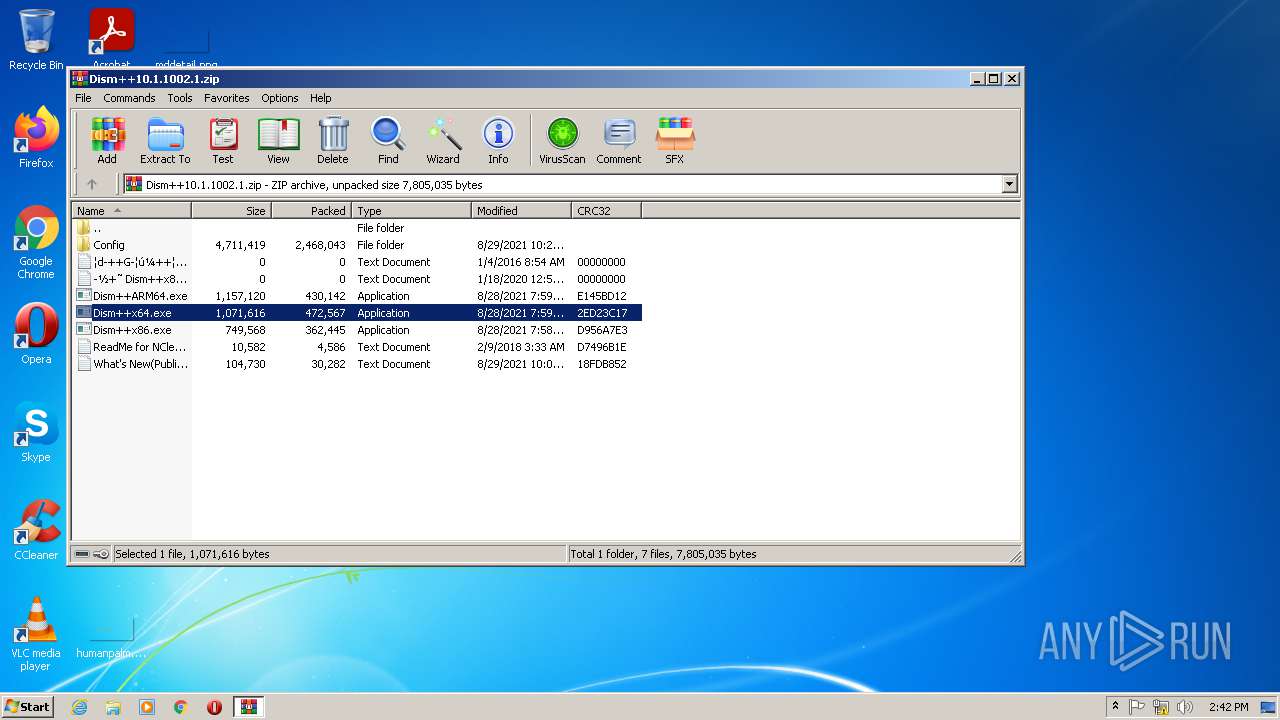
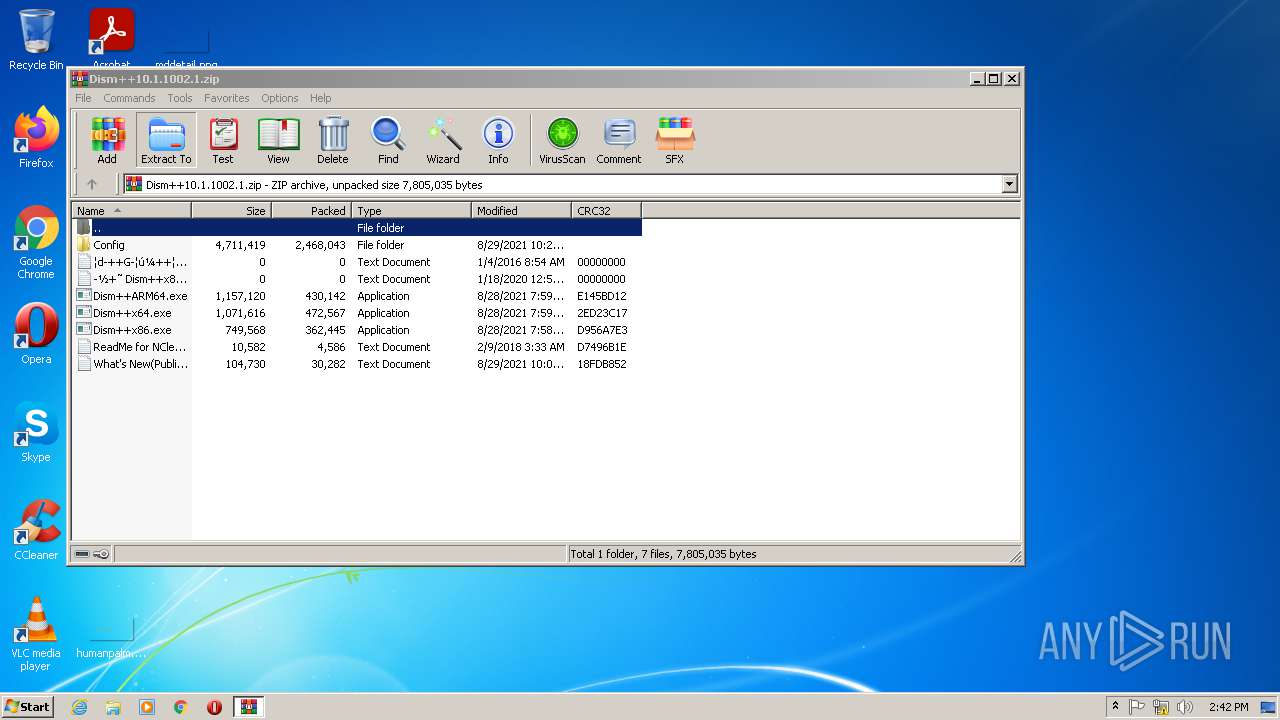
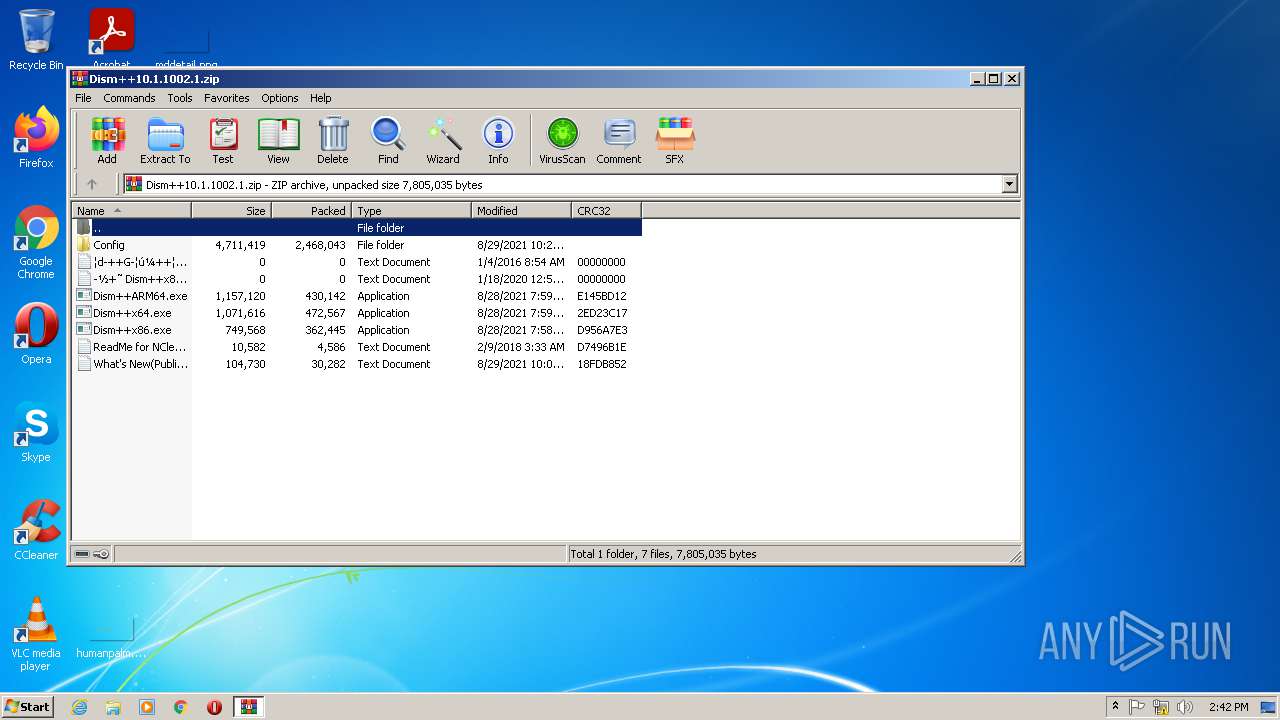
| File name: | Dism++10.1.1002.1.zip |
| Full analysis: | https://app.any.run/tasks/eecb1551-11dd-41f2-9ff4-ad2e48300a0e |
| Verdict: | Malicious activity |
| Analysis date: | October 12, 2021, 13:41:21 |
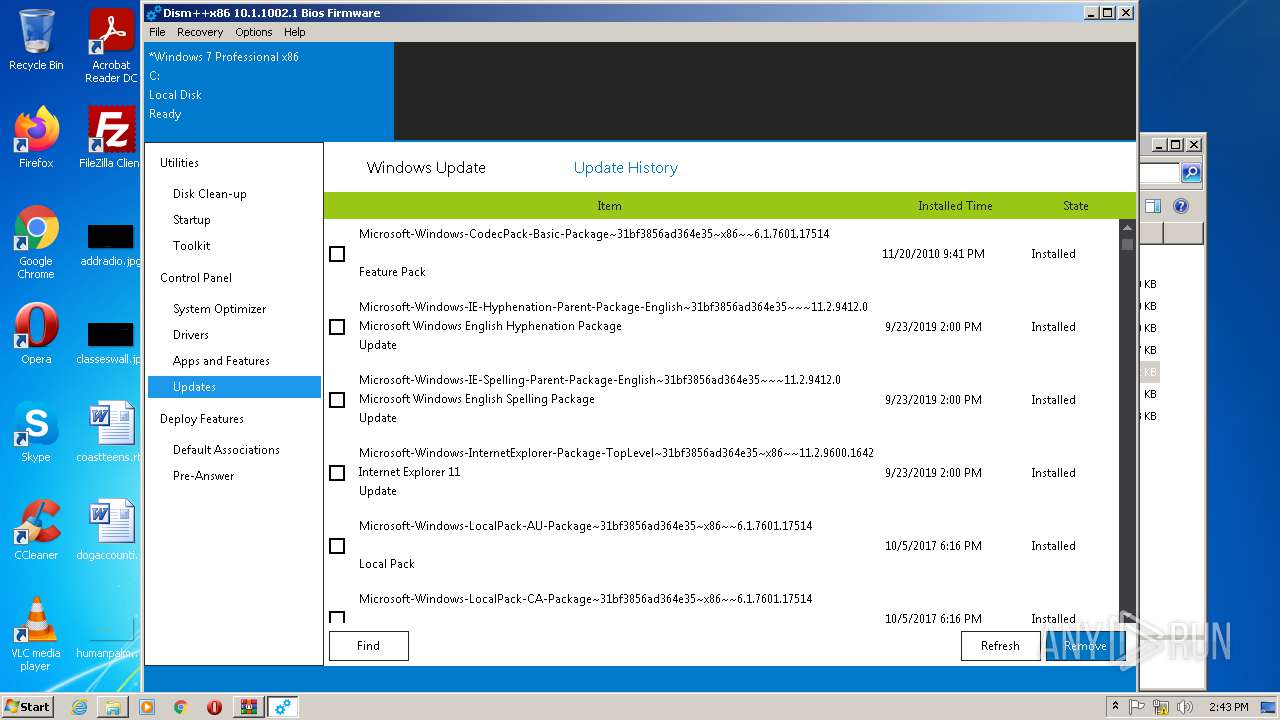
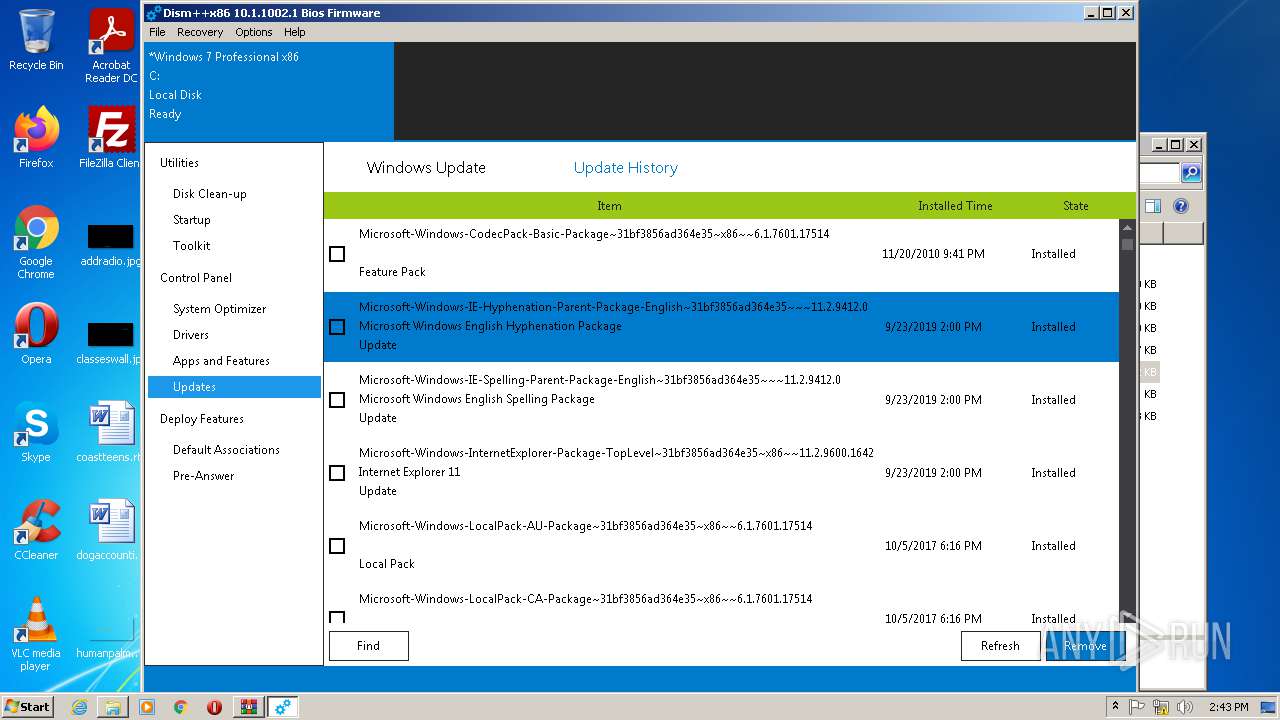
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | ABA2A40185B86EC661CA66F1B341C9DE |
| SHA1: | E1701EB9990F36EFF57837124150C91B2E491912 |
| SHA256: | BD782BA834A77661DB0B272C00AFD5377404B23CB26783507DED145F4C72F9A6 |
| SSDEEP: | 98304:EKBqv2Ch5VDy+Q8YOU6YqeYfsuK0sTILg6ixyeXmziSTPB+p:zB82KPyJf6EY0l0sUAxp2WIPB+p |
MALICIOUS
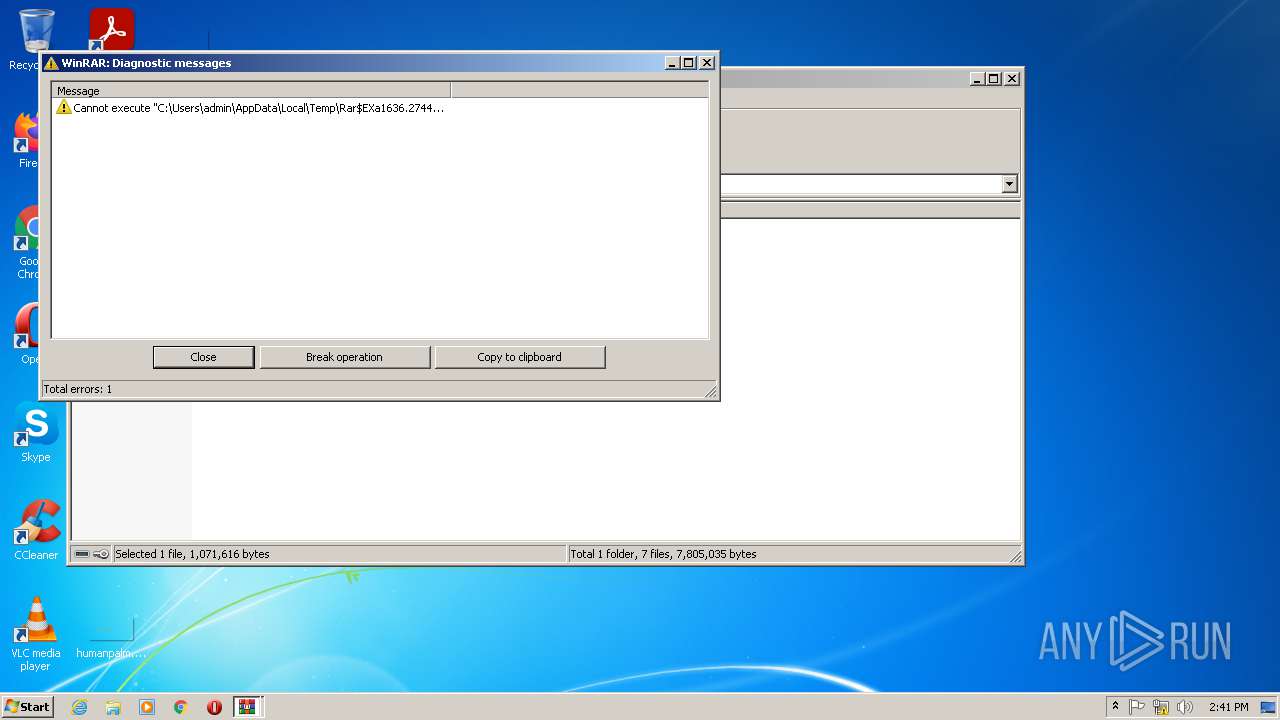
Application was dropped or rewritten from another process
- Dism++x86.exe (PID: 2100)
- Dism++x86.exe (PID: 3640)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 1472)
- Dism++x86.exe (PID: 2100)
- rundll32.exe (PID: 3028)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 1636)
- Dism++x86.exe (PID: 2100)
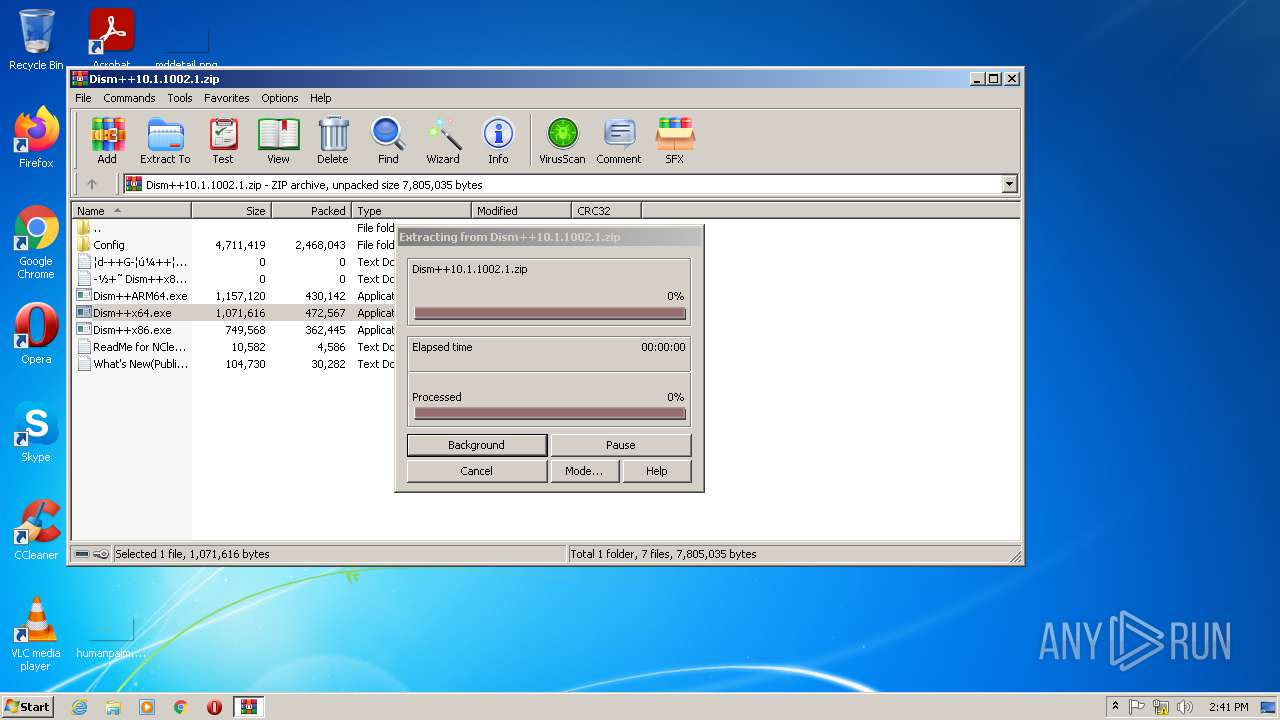
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1636)
Reads the computer name
- WinRAR.exe (PID: 1636)
- Dism++x86.exe (PID: 2100)
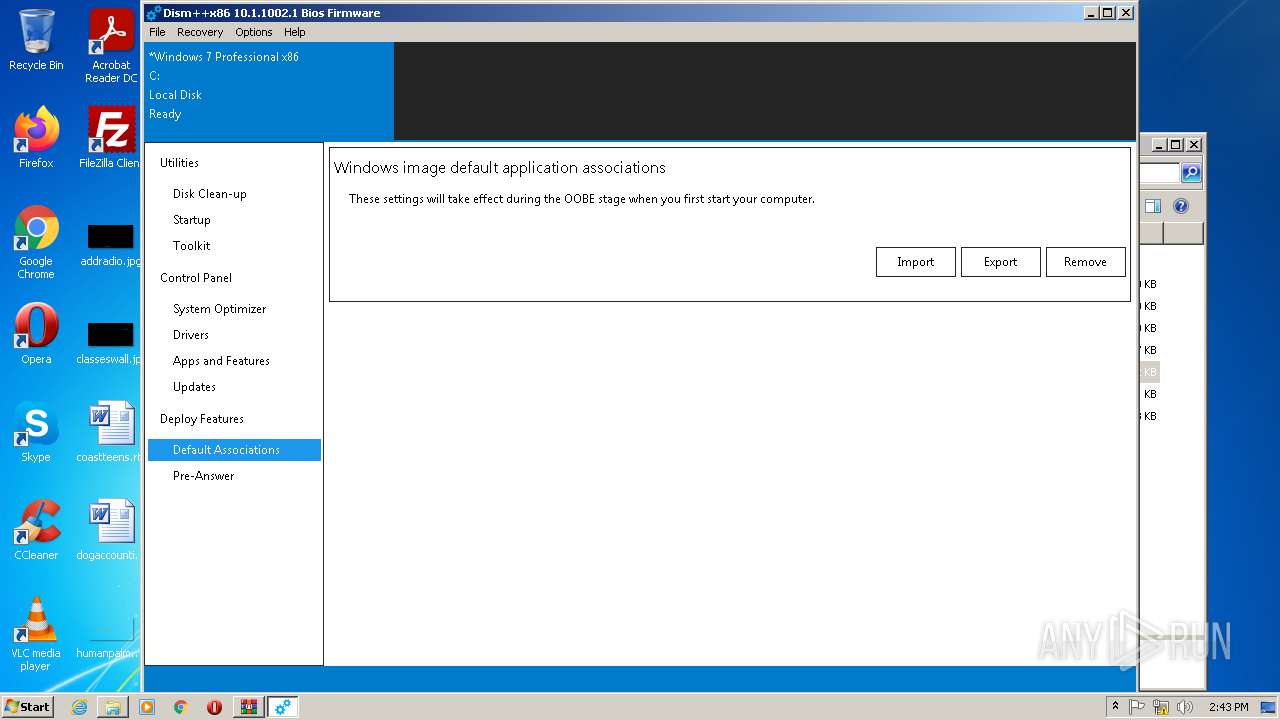
Reads default file associations for system extensions
- SearchProtocolHost.exe (PID: 1472)
Drops a file with too old compile date
- WinRAR.exe (PID: 1636)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 1636)
Removes files from Windows directory
- Dism++x86.exe (PID: 2100)
Checks Windows language
- Dism++x86.exe (PID: 2100)
Reads Environment values
- Dism++x86.exe (PID: 2100)
Uses RUNDLL32.EXE to load library
- Dism++x86.exe (PID: 2100)
INFO
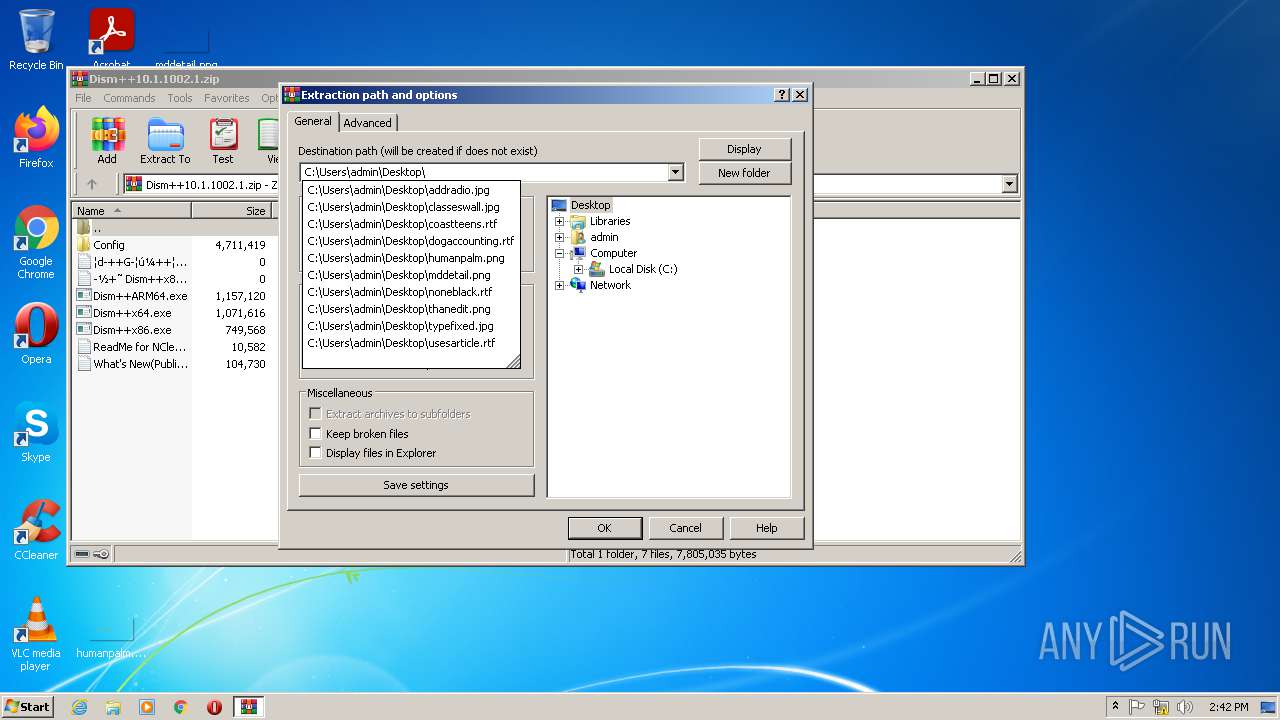
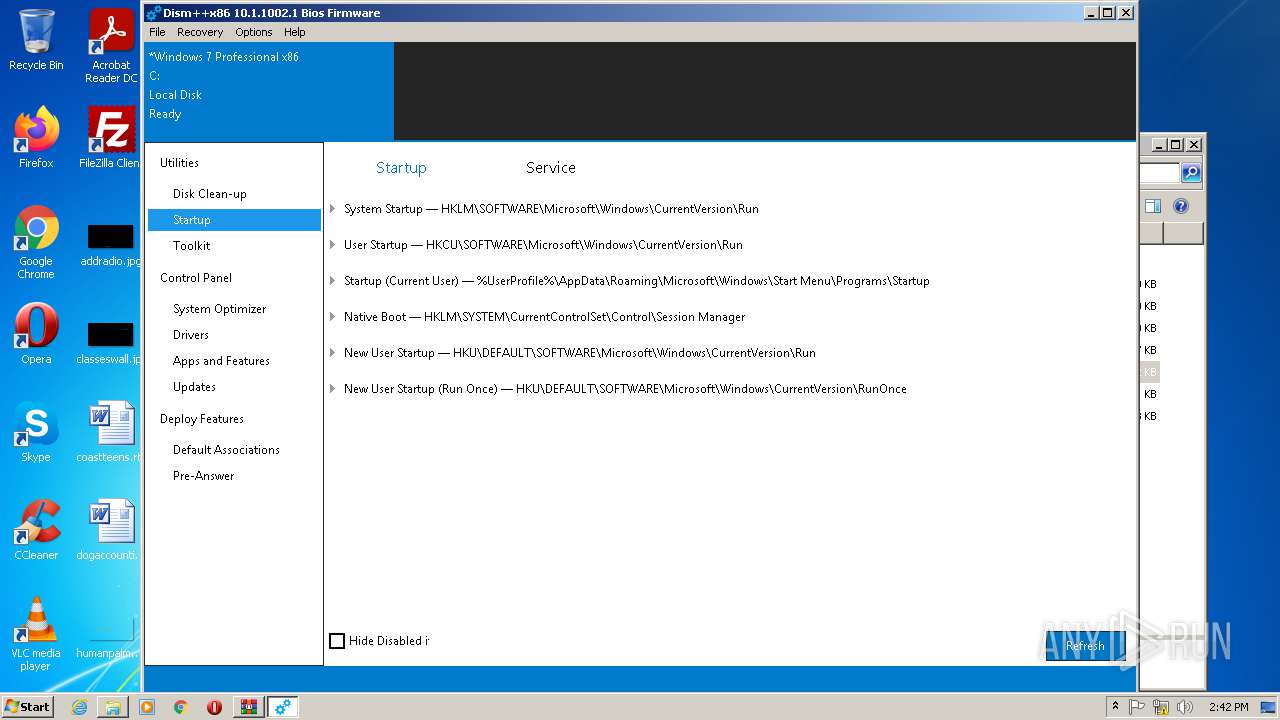
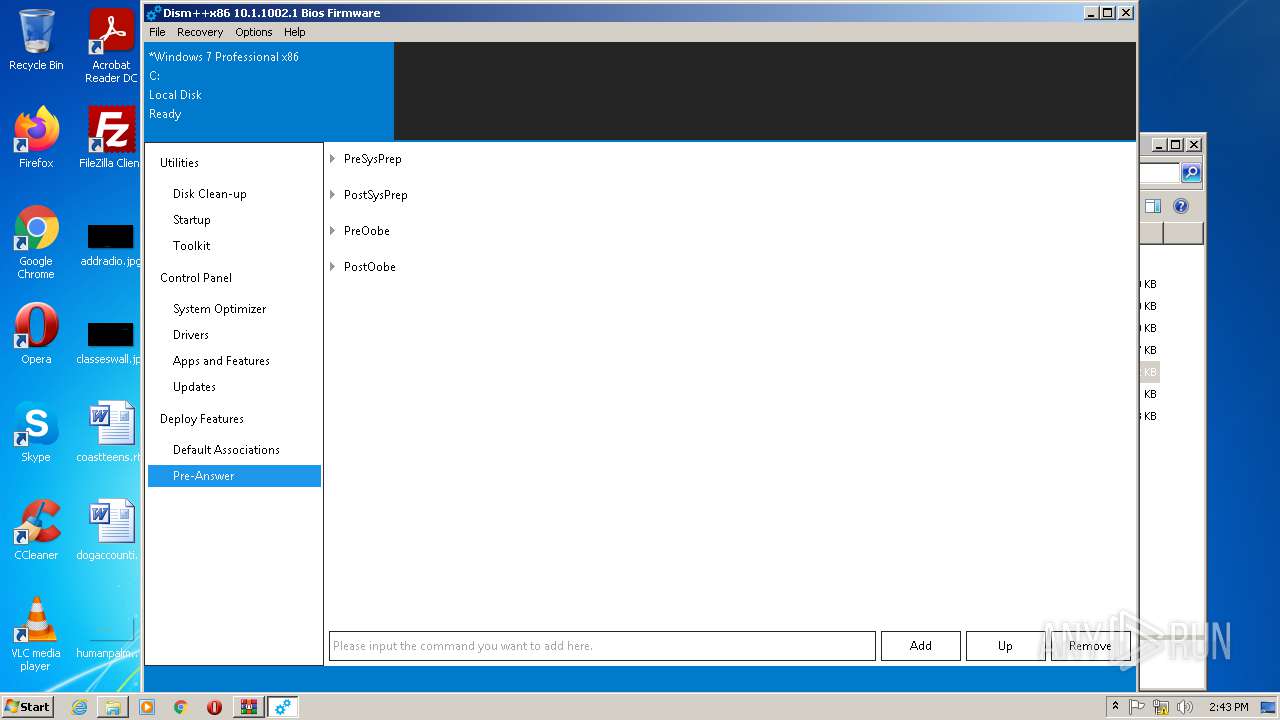
Manual execution by user
- Dism++x86.exe (PID: 3640)
- Dism++x86.exe (PID: 2100)
Reads the computer name
- rundll32.exe (PID: 3028)
Checks supported languages
- rundll32.exe (PID: 3028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2021:08:29 17:29:26 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Config/ |
Total processes
46
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1472 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
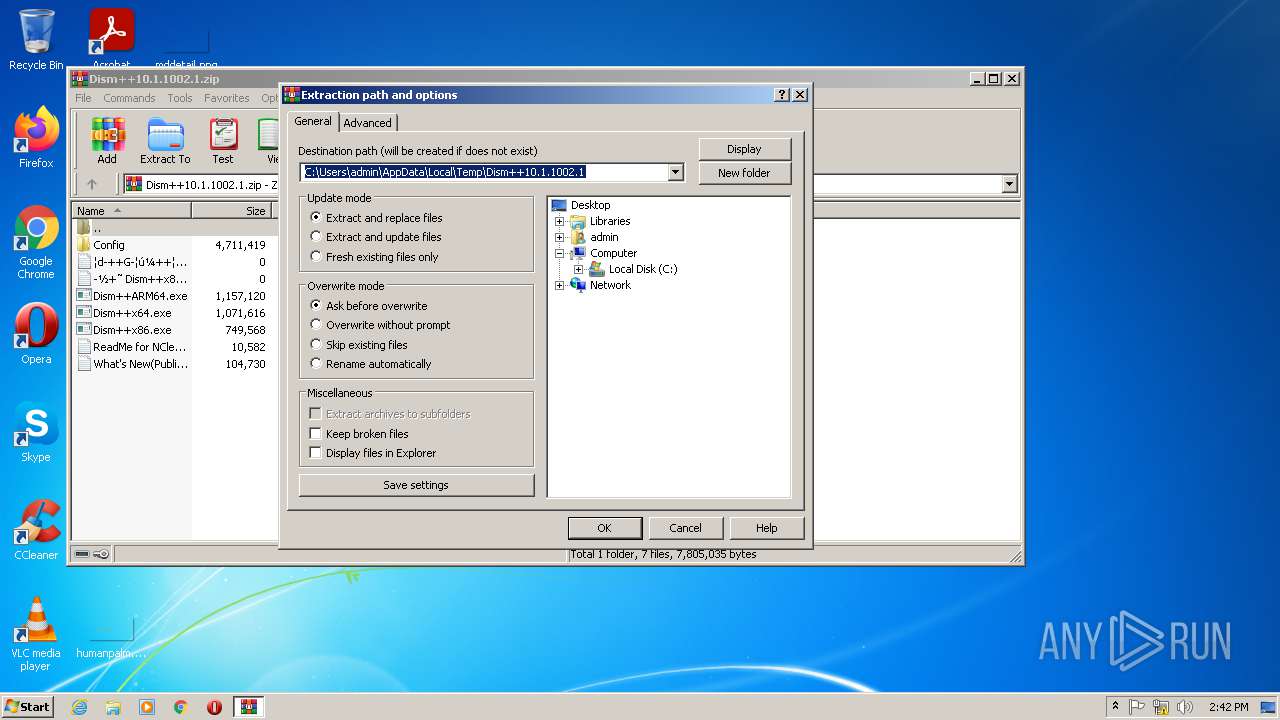
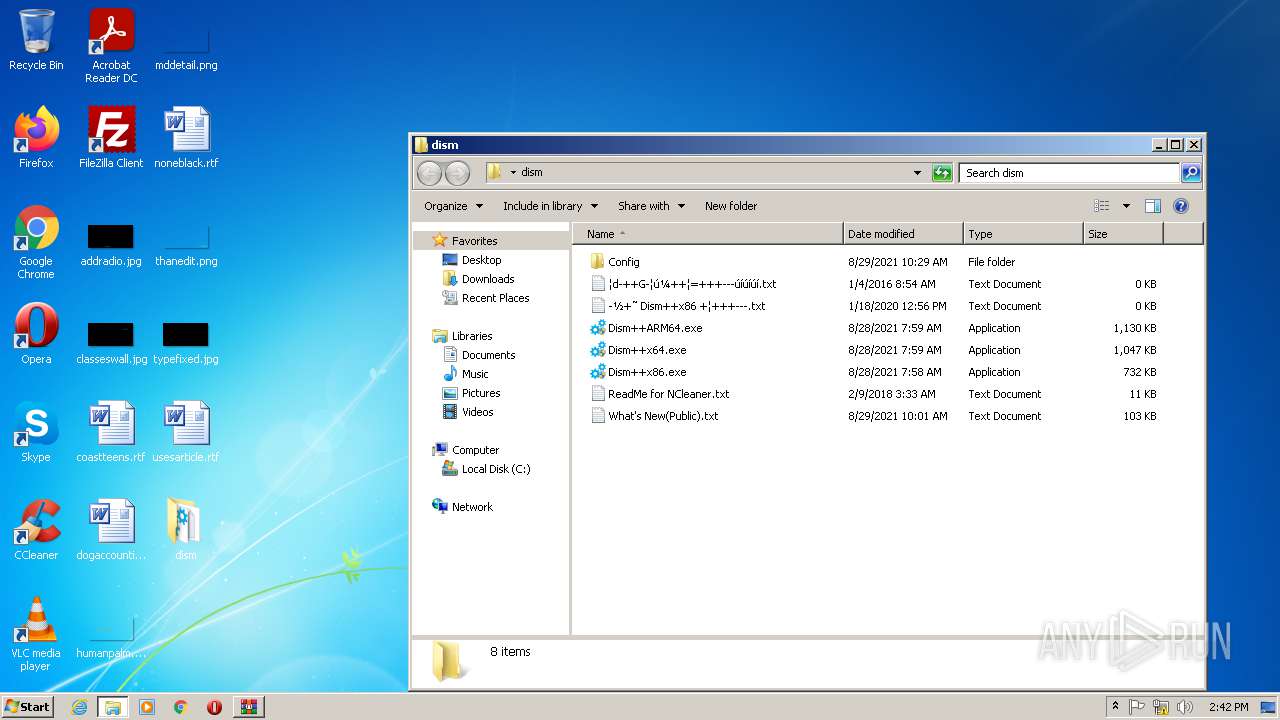
| 1636 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Dism++10.1.1002.1.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
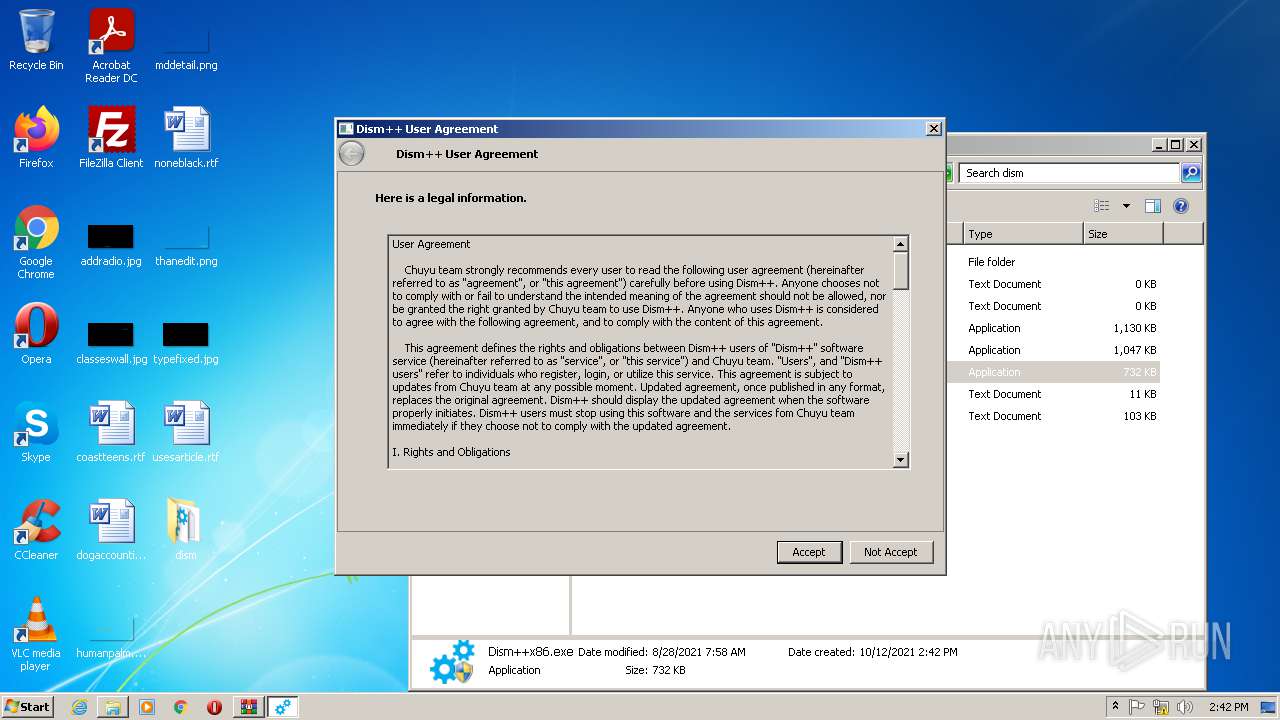
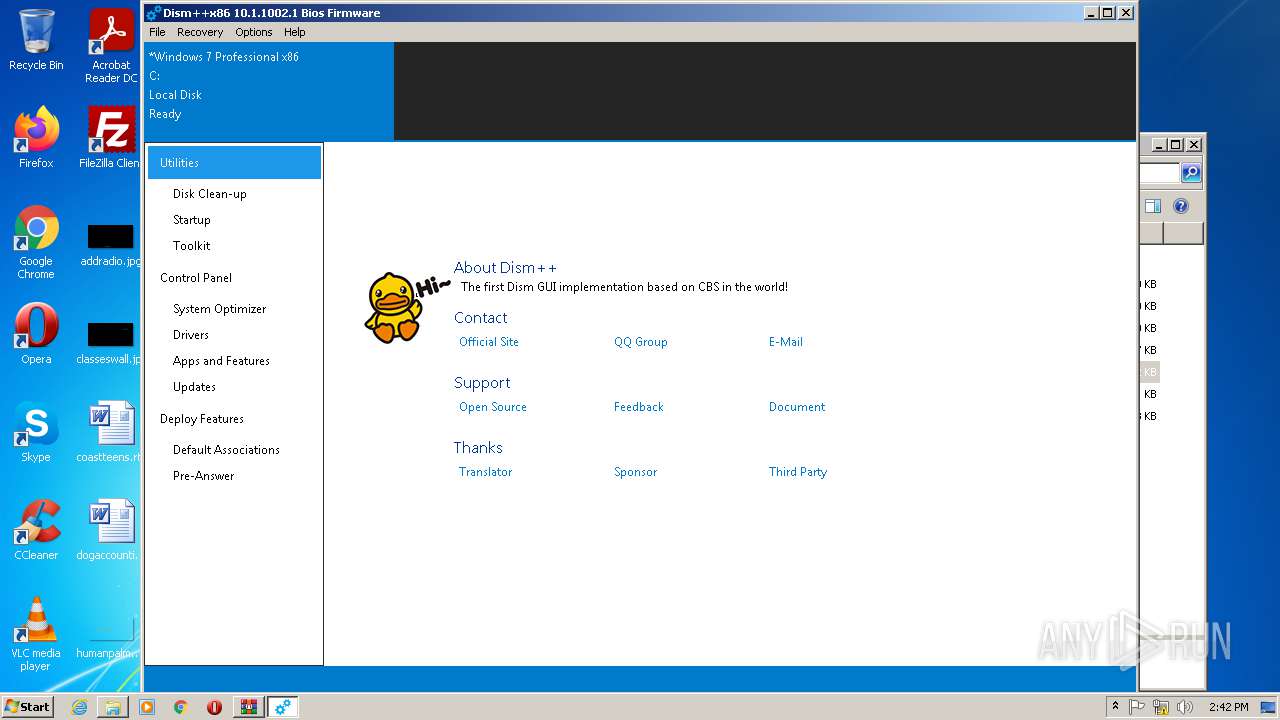
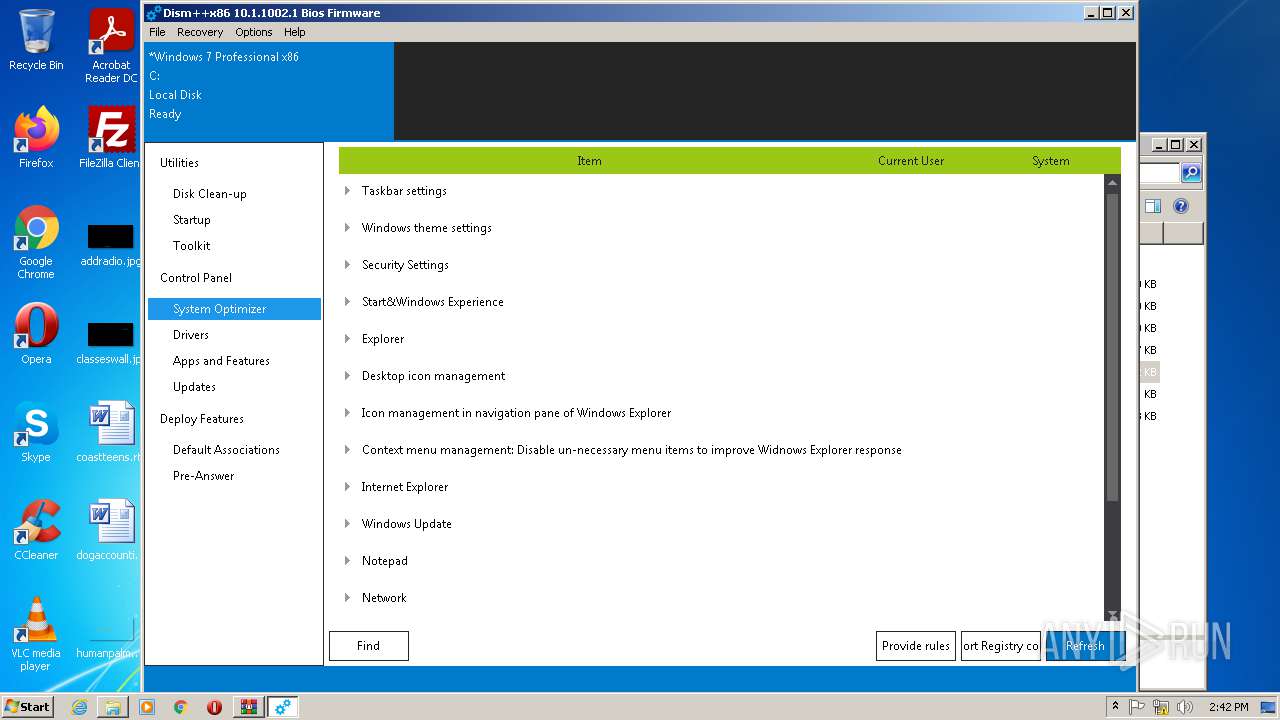
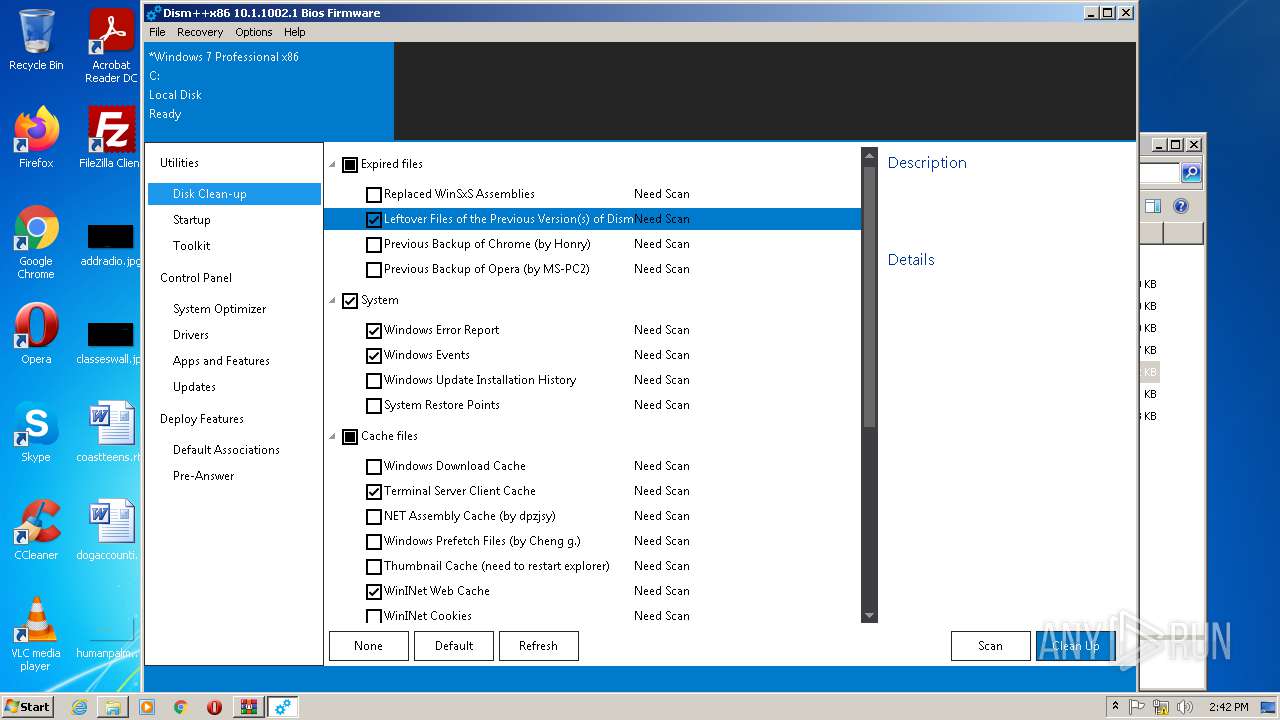
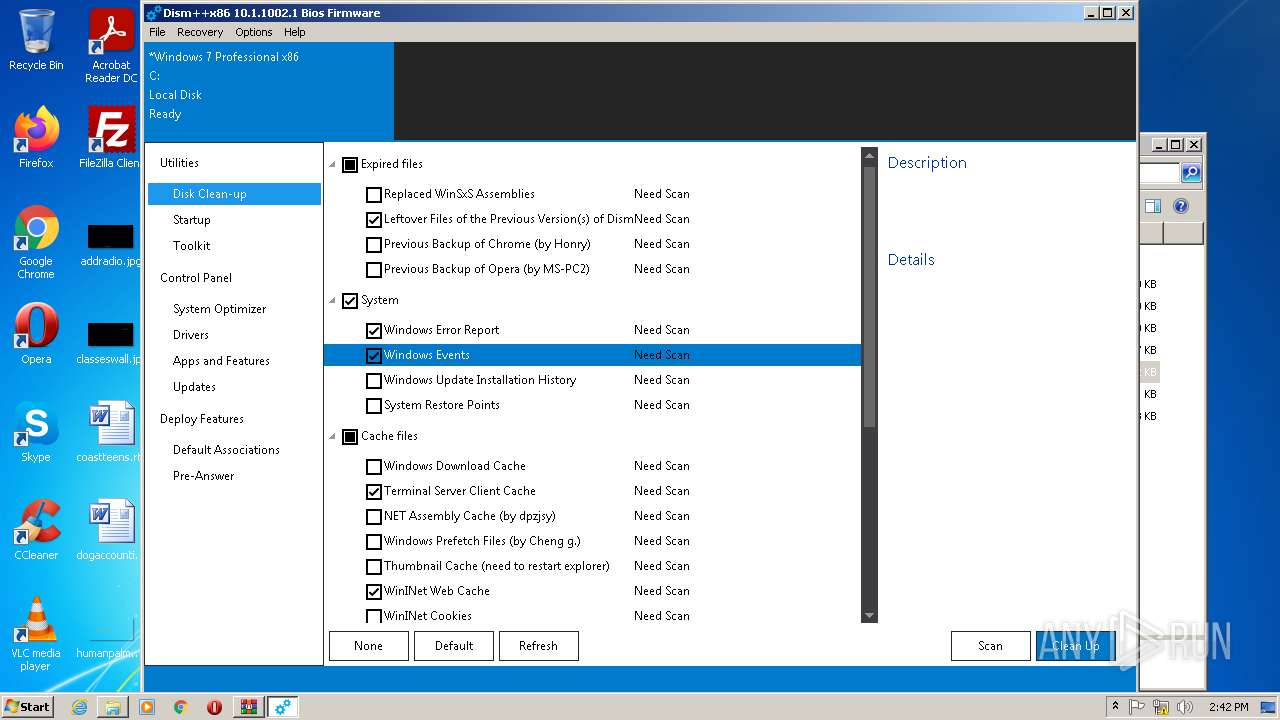
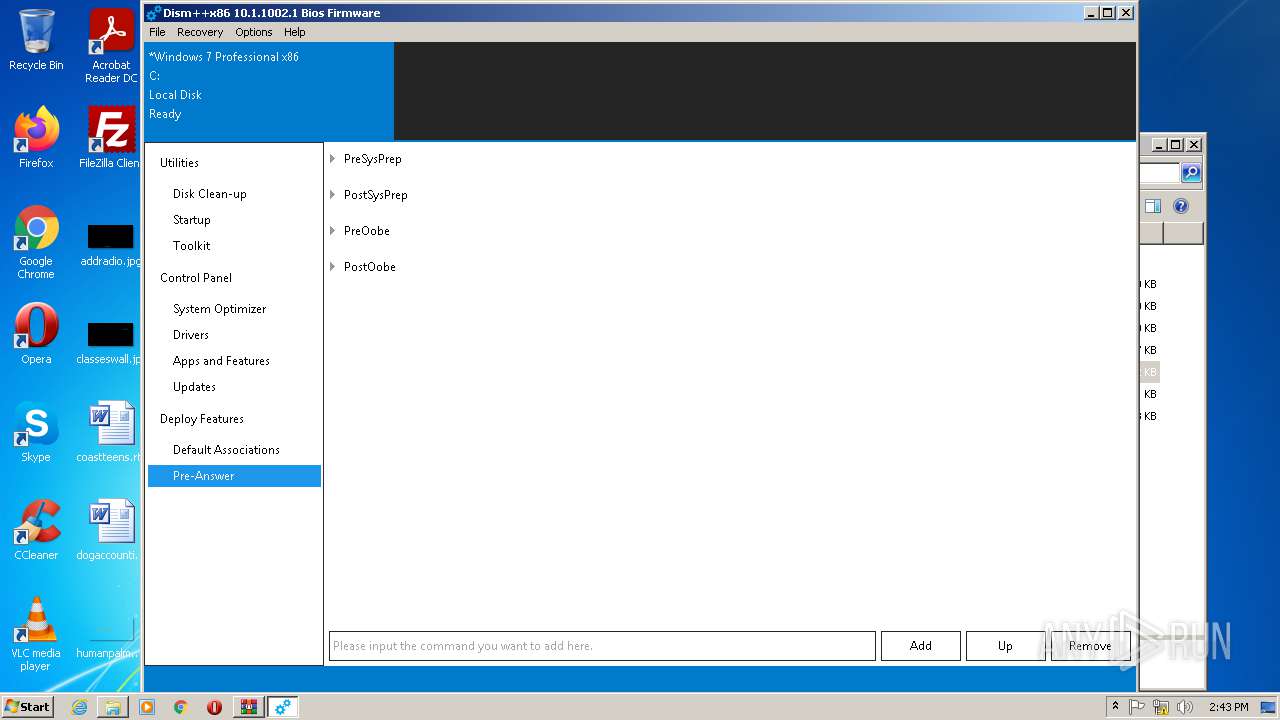
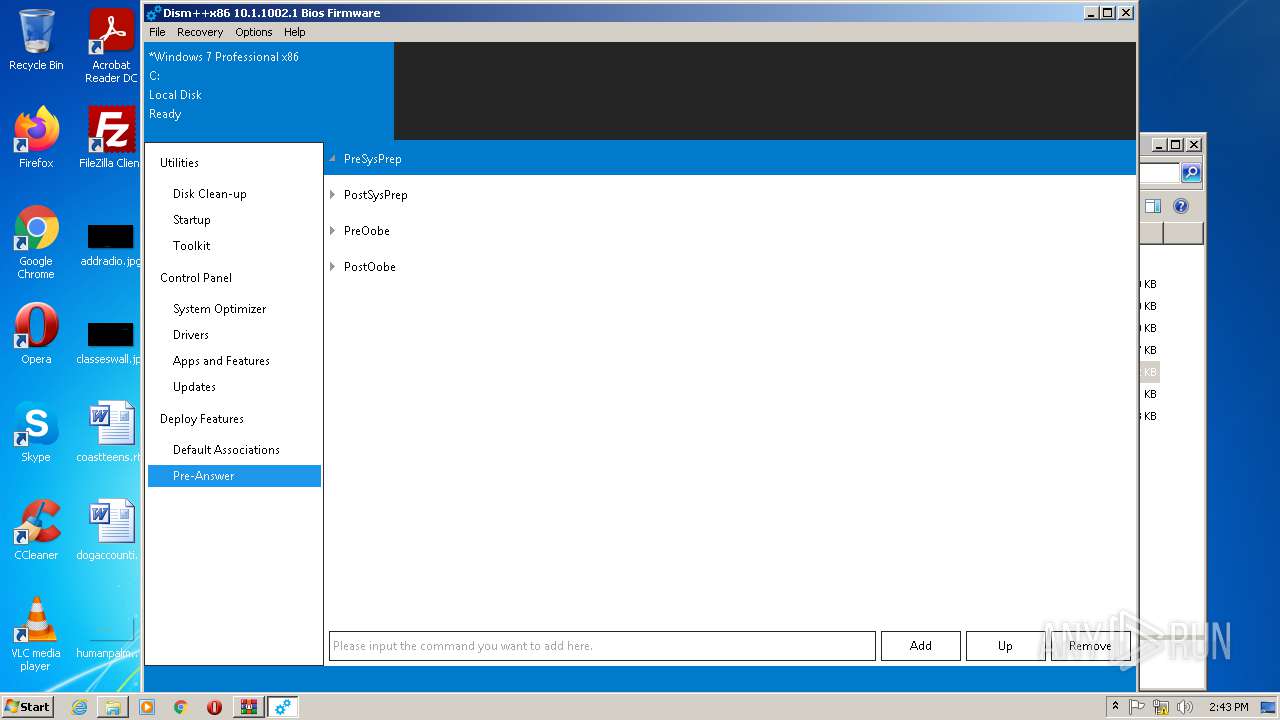
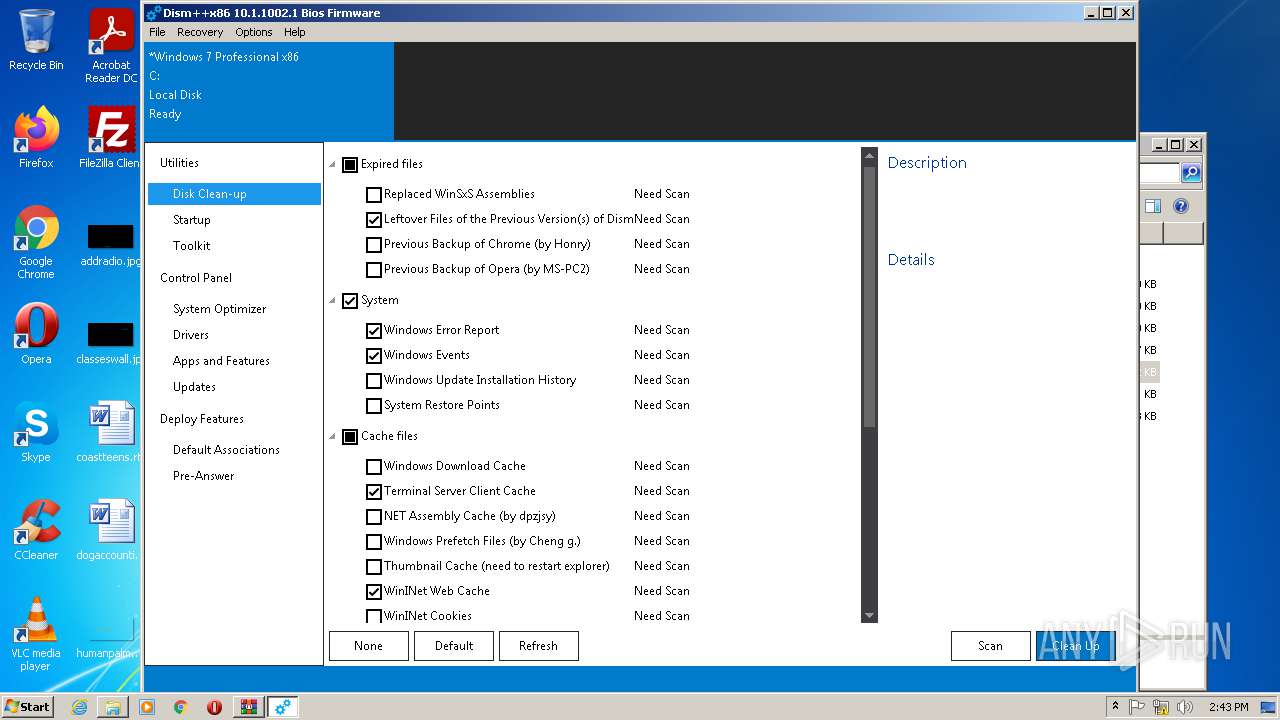
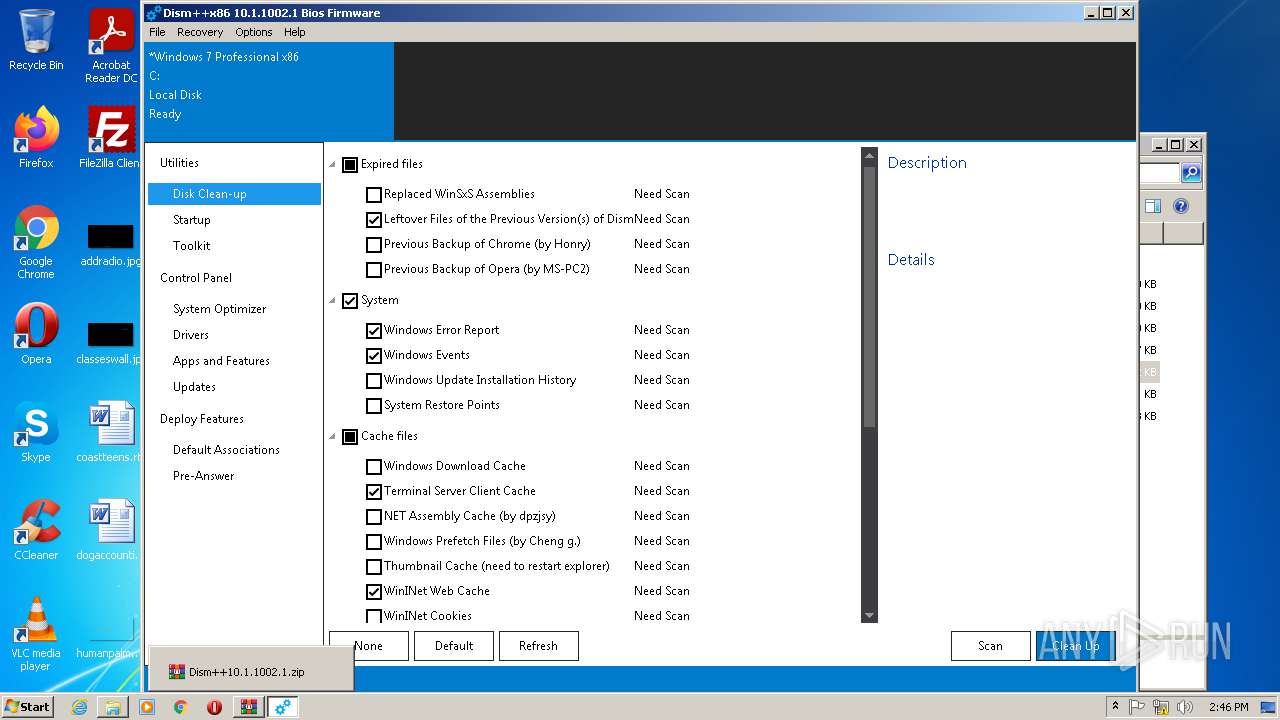
| 2100 | "C:\Users\admin\Desktop\dism\Dism++x86.exe" | C:\Users\admin\Desktop\dism\Dism++x86.exe | Explorer.EXE | ||||||||||||
User: admin Company: Chuyu Team Integrity Level: HIGH Description: Dism++??? Exit code: 0 Version: 10.1.1002.1 Modules
| |||||||||||||||
| 3028 | rundll32 "C:\Users\admin\Desktop\dism\Config\x86\CBSHost.dll",RunCbsHost {410b8549-4071-40b1-a1ed-62073e470abe} "C:" "\\?\C:\Windows\Temp\\" 000000C8 4 | C:\Windows\System32\rundll32.exe | — | Dism++x86.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3640 | "C:\Users\admin\Desktop\dism\Dism++x86.exe" | C:\Users\admin\Desktop\dism\Dism++x86.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Chuyu Team Integrity Level: MEDIUM Description: Dism++??? Exit code: 3221226540 Version: 10.1.1002.1 Modules
| |||||||||||||||
Total events
5 503
Read events
5 455
Write events
48
Delete events
0
Modification events
| (PID) Process: | (1636) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1636) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1636) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\171\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1636) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Dism++10.1.1002.1.zip | |||
| (PID) Process: | (1636) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1636) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1636) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1636) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1636) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1636) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
38
Suspicious files
39
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1636 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1636.27445\Config\Languages\bg.zip | compressed | |
MD5:D2EFE76E6991016EA78D7E65DB60A640 | SHA256:A9A1C127DF4BC6A7D420F209FD3D5BEEBD01454CF0CAFFC486D7509A9C50B7F2 | |||
| 1636 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1636.27445\Config\amd64\bcdboot.exe | executable | |
MD5:BE14BE7C8F7F0F4E397B89979CB9CF6B | SHA256:309F3ECCB0093CC6CC98F858BD3CE67B00BB810728FFB177B7BD287FB3C92B97 | |||
| 1636 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1636.27445\Config\arm64\NCleaner.dll | executable | |
MD5:6F7A31F96E95D9467F755EC806B768EC | SHA256:62BF4BCD3B3207E9BB8A4097684605A732E820968A9A8835A0F39E9BB67B26F7 | |||
| 1636 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1636.27445\Config\amd64\wofadk.sys | executable | |
MD5:FBA28D5AC166714737D1D8CDF0AEF078 | SHA256:54FBA1CC80E820B462229FCB987FB8DF2321ED85D9450F3F4A81D0982E5D289F | |||
| 1636 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1636.27445\Config\Languages\cs.zip | compressed | |
MD5:753BEC76C97EACFFB76A014DAD3A1CE7 | SHA256:41FA512672FF9627330F40F384F449D7E9516754B931E439C050340390476D97 | |||
| 1636 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1636.27445\Config\arm64\CBSHost.dll | executable | |
MD5:D81098BEC9F475C3A86E0FA38AEAA537 | SHA256:9CAEBB88BA8F4087273BDC07F37B260A15DC2C7B4058FFAC77A147ED1A27C032 | |||
| 1636 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1636.27445\Config\Languages\fr.zip | compressed | |
MD5:171BB9AE7E23A67851580C836F3854E8 | SHA256:26D49E6AE3855A7CCE6E8FAF075ECC8C06ECF3275CEE6656800856C7870ACA02 | |||
| 1636 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1636.27445\Config\Data.zip | compressed | |
MD5:C7B7C57CFDB4C76287BBE270B3337088 | SHA256:BDE45526069A31A534C1FE13289DFE9867BCFE82CE44184A0BB4FCE587494A7C | |||
| 1636 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1636.27445\Config\Languages\de.zip | compressed | |
MD5:BCFBC20C0A8F1B98BFAE74F34226C2D1 | SHA256:023247A51569A2E65156C5F4CC7BB8748FE5B6777D9FCE61CFDEFC83DADBE576 | |||
| 1636 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1636.27445\Config\default.ui.zip | compressed | |
MD5:E4B7BEF45A8F48832BA59396509DCB76 | SHA256:1A90365AC33C37EEAE4DD712F84062466C10948CF5B567574055E0B8B0F70534 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2100 | Dism++x86.exe | POST | — | 150.138.249.223:80 | http://web1612151818153.bj01.bdysite.com/chuyu-analysis/client_update.php | CN | — | — | malicious |
2100 | Dism++x86.exe | POST | — | 150.138.249.223:80 | http://web1612151818153.bj01.bdysite.com/chuyu-analysis/client_update.php | CN | — | — | malicious |
2100 | Dism++x86.exe | GET | 200 | 47.246.43.227:80 | http://update.chuyu.me/UpdateInfo.zip?t=1D7BF6F05EDD34A | US | compressed | 8.86 Kb | malicious |
2100 | Dism++x86.exe | POST | — | 150.138.249.223:80 | http://web1612151818153.bj01.bdysite.com/chuyu-analysis/client_update.php | CN | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2100 | Dism++x86.exe | 150.138.249.223:80 | web1612151818153.bj01.bdysite.com | Zhuzhou | CN | unknown |
— | — | 150.138.249.223:80 | web1612151818153.bj01.bdysite.com | Zhuzhou | CN | unknown |
2100 | Dism++x86.exe | 47.246.43.227:80 | update.chuyu.me | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
update.chuyu.me |
| malicious |
web1612151818153.bj01.bdysite.com |
| malicious |