| File name: | Monoxidex86.exe |
| Full analysis: | https://app.any.run/tasks/a9cc2e7a-07d5-4981-8fa4-f148b7daa93b |
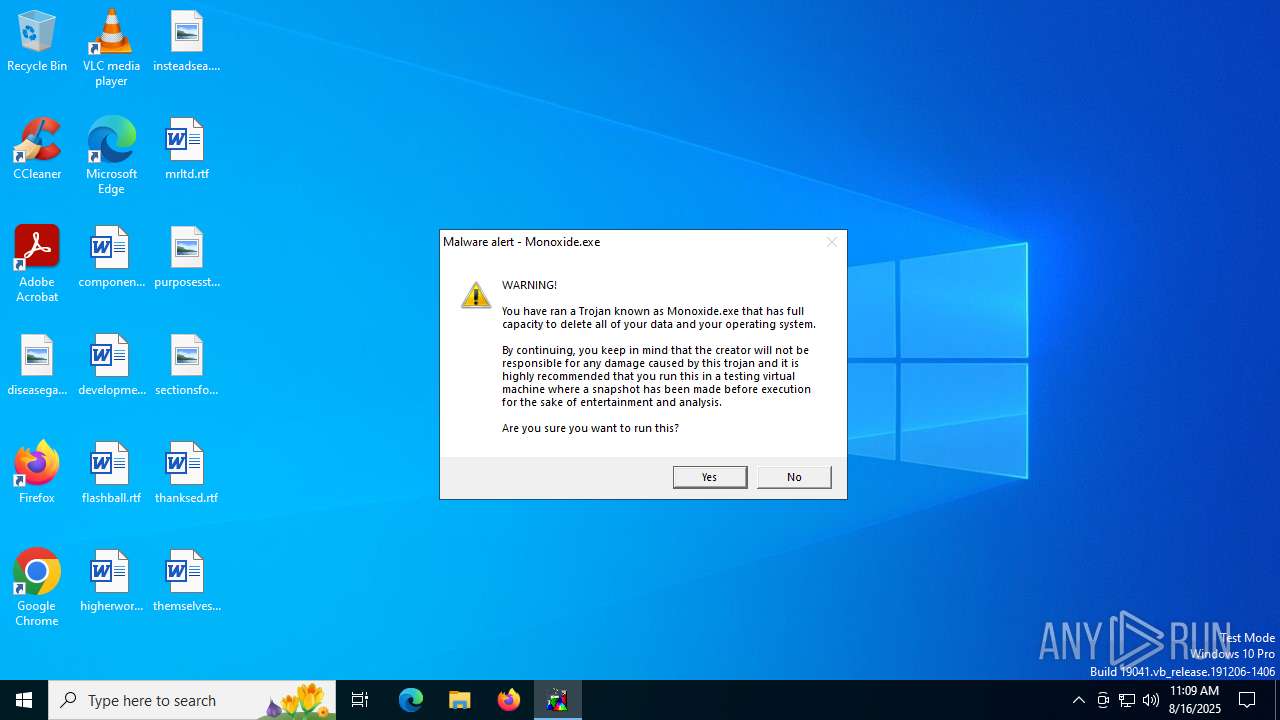
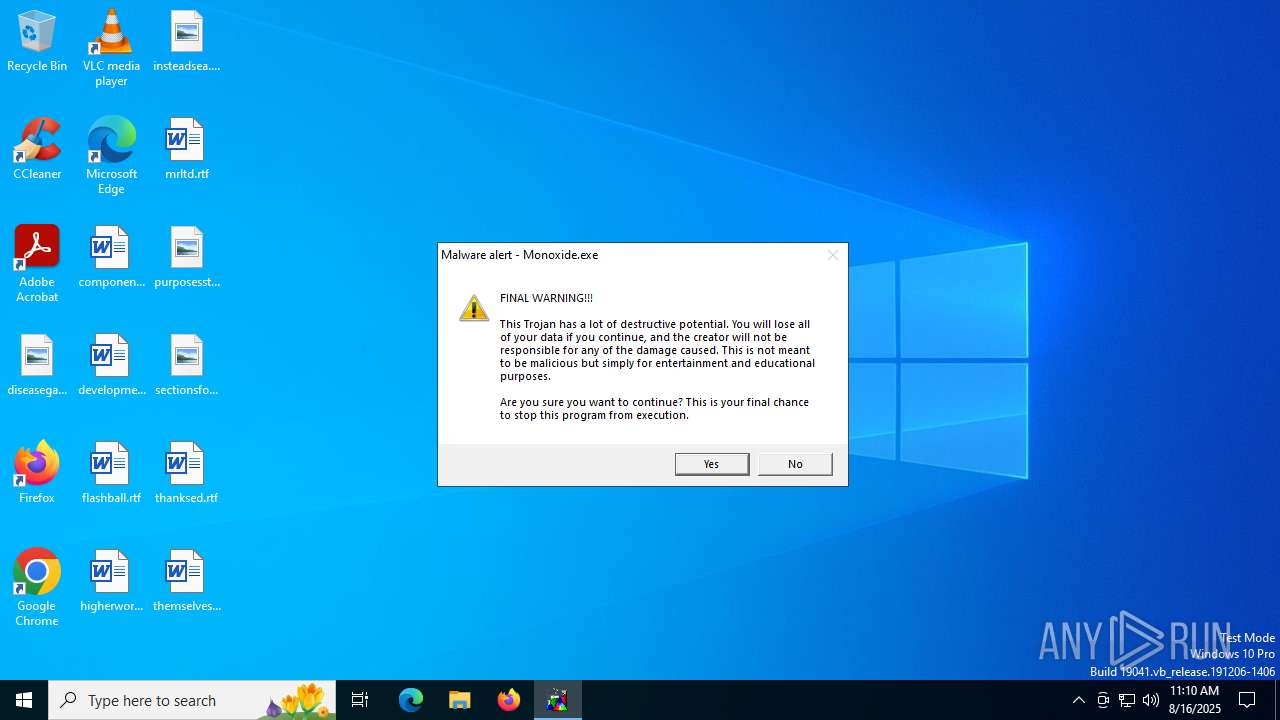
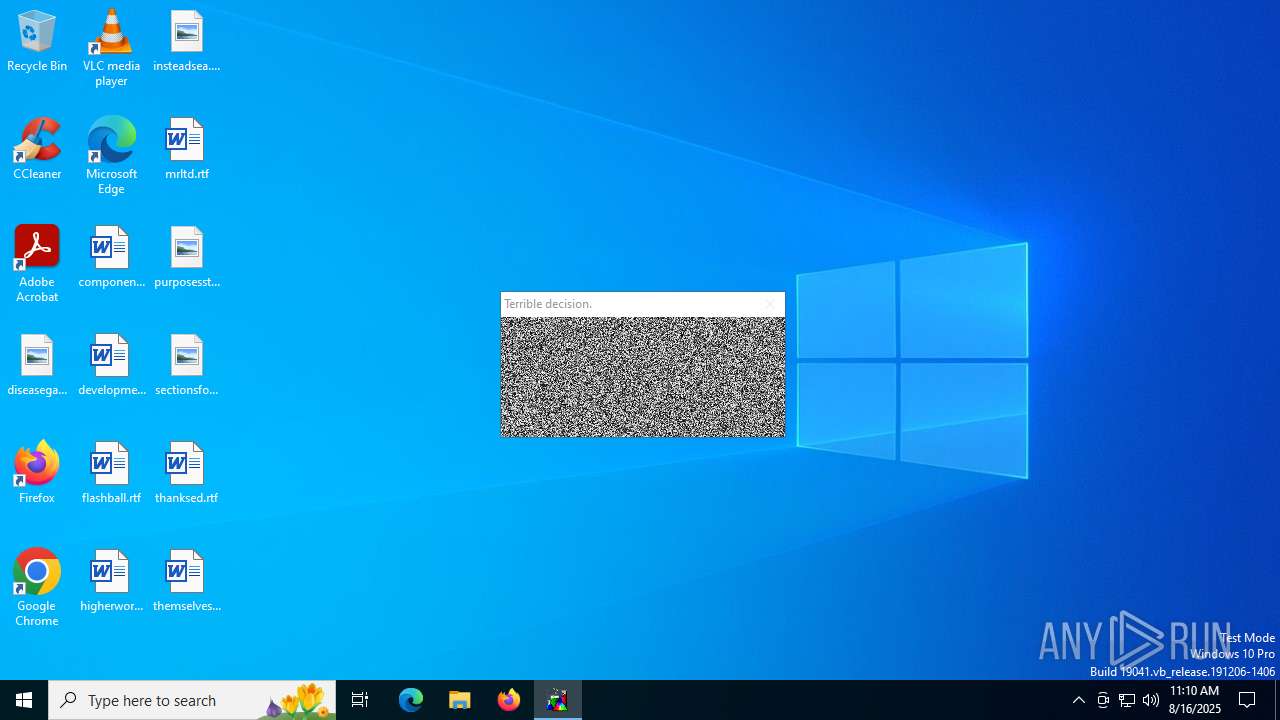
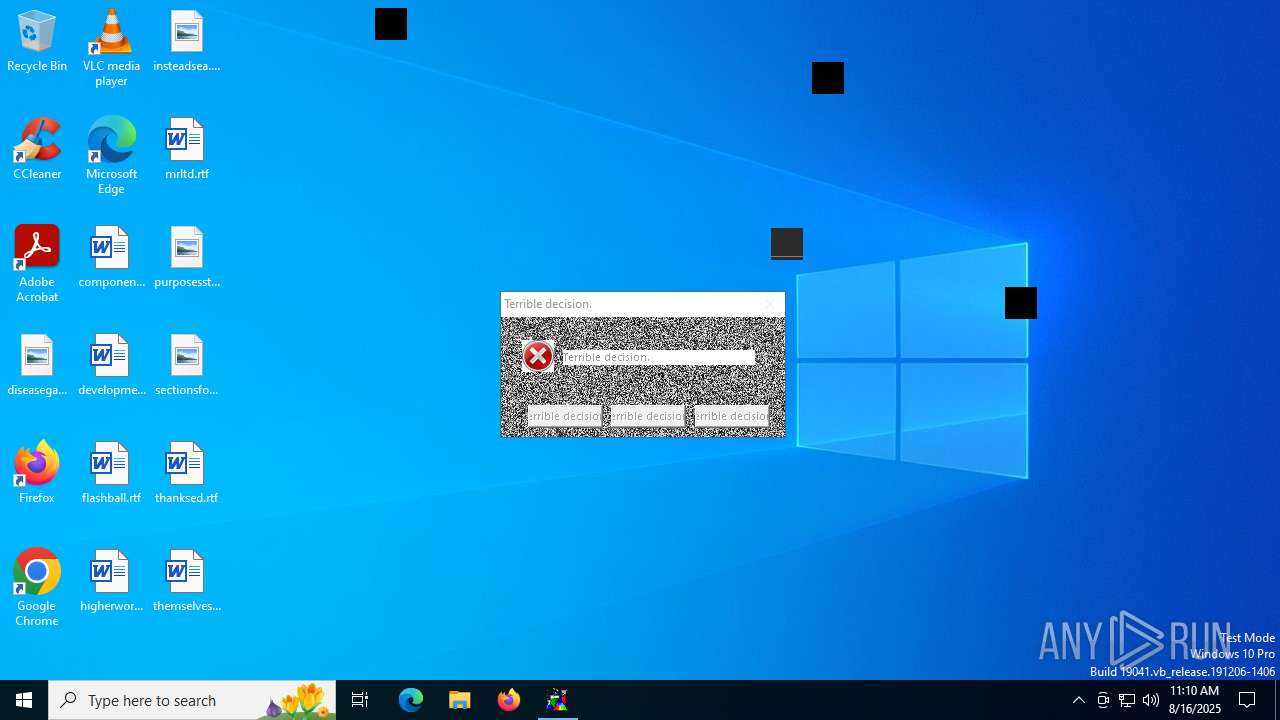
| Verdict: | Malicious activity |
| Analysis date: | August 16, 2025, 11:09:35 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 5C378B11848AC59704C2000B4E711C30 |
| SHA1: | 6A46C53FD89B1F66D3FDAB7653181E8A3E56D418 |
| SHA256: | BD764FE2F9734D5AC56933CE68DF0A175BFA98DC0266AE3CD3A5C963267EA77E |
| SSDEEP: | 6144:bJuMc7iv8+gsg058LvD47vlOi9E3AAqgmlB:sKgX0MivlOi9E3AAqzlB |
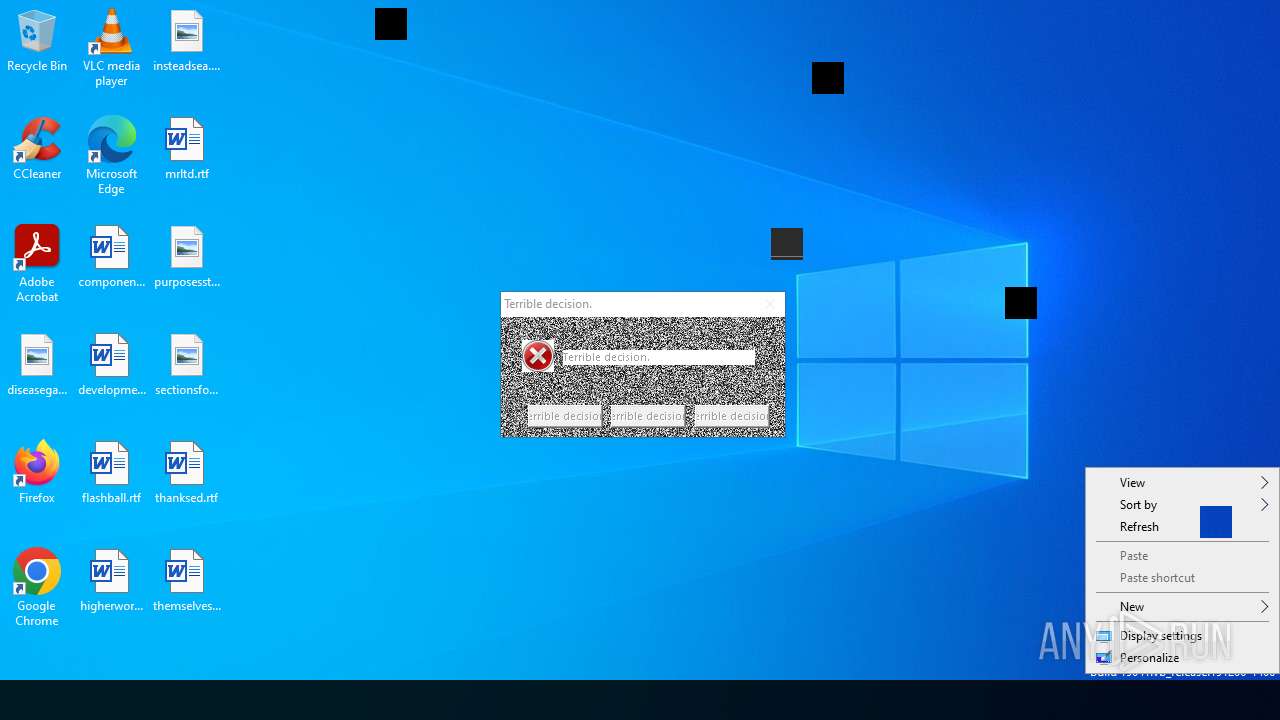
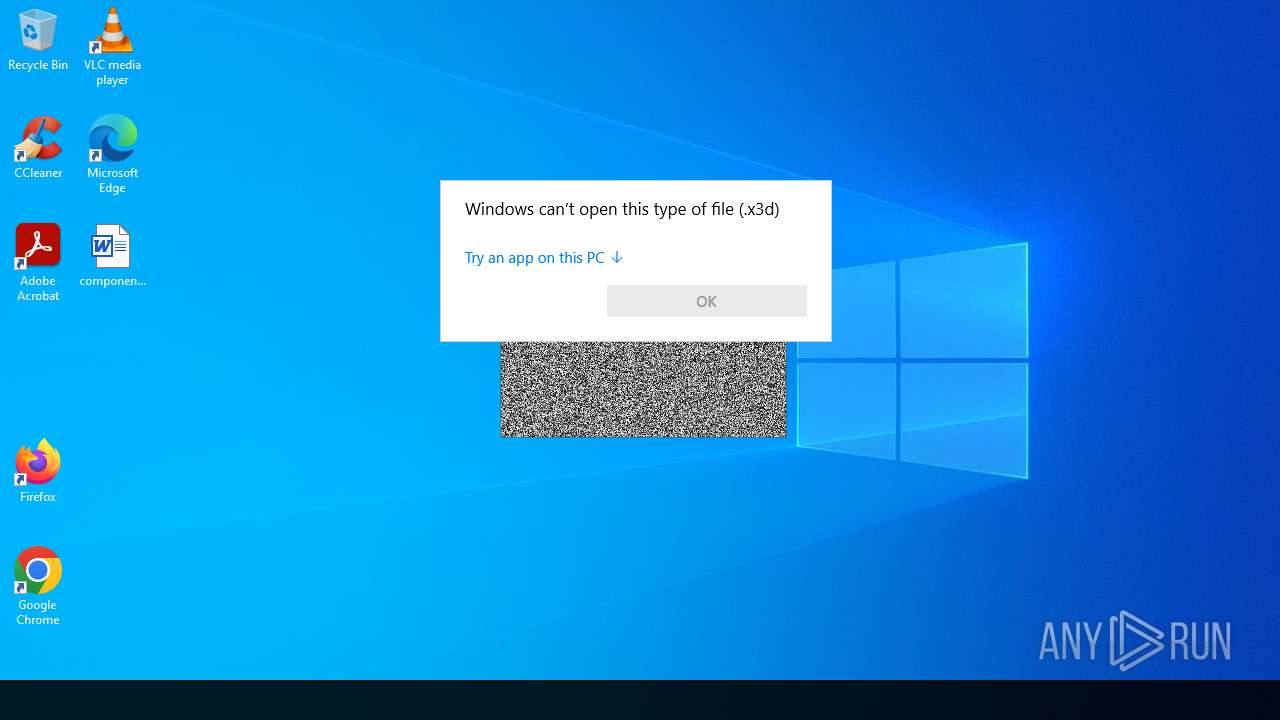
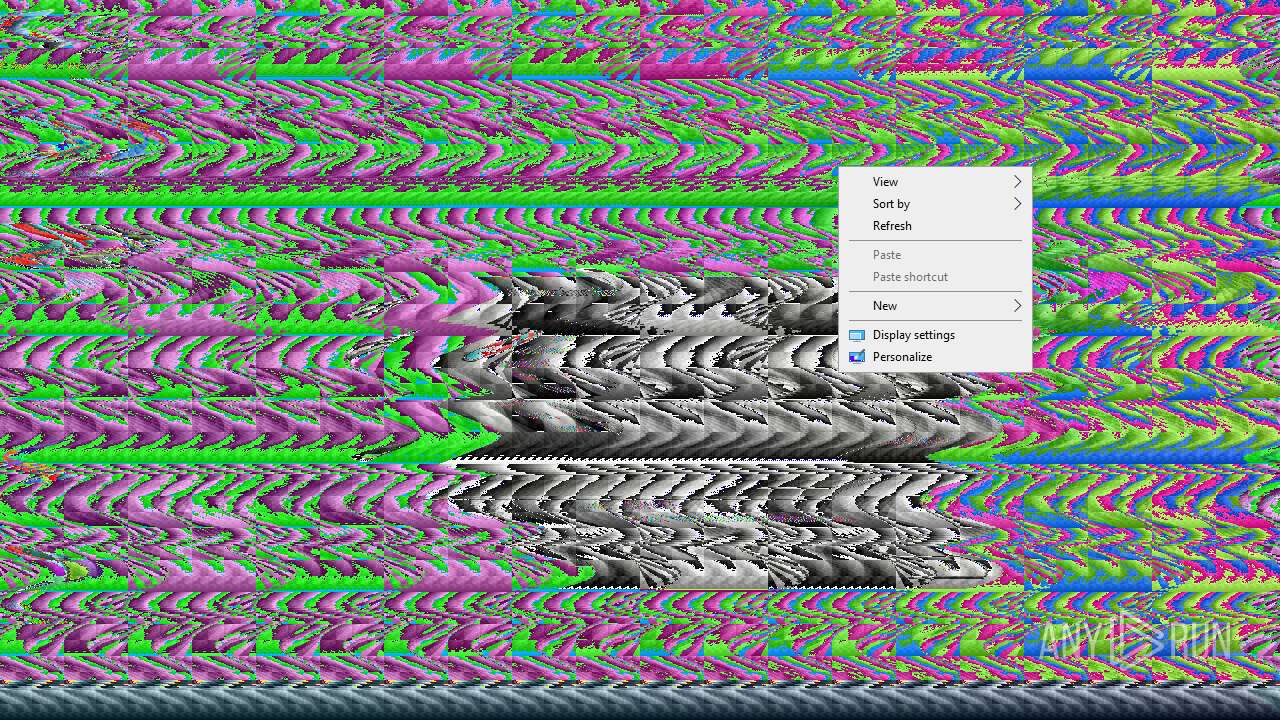
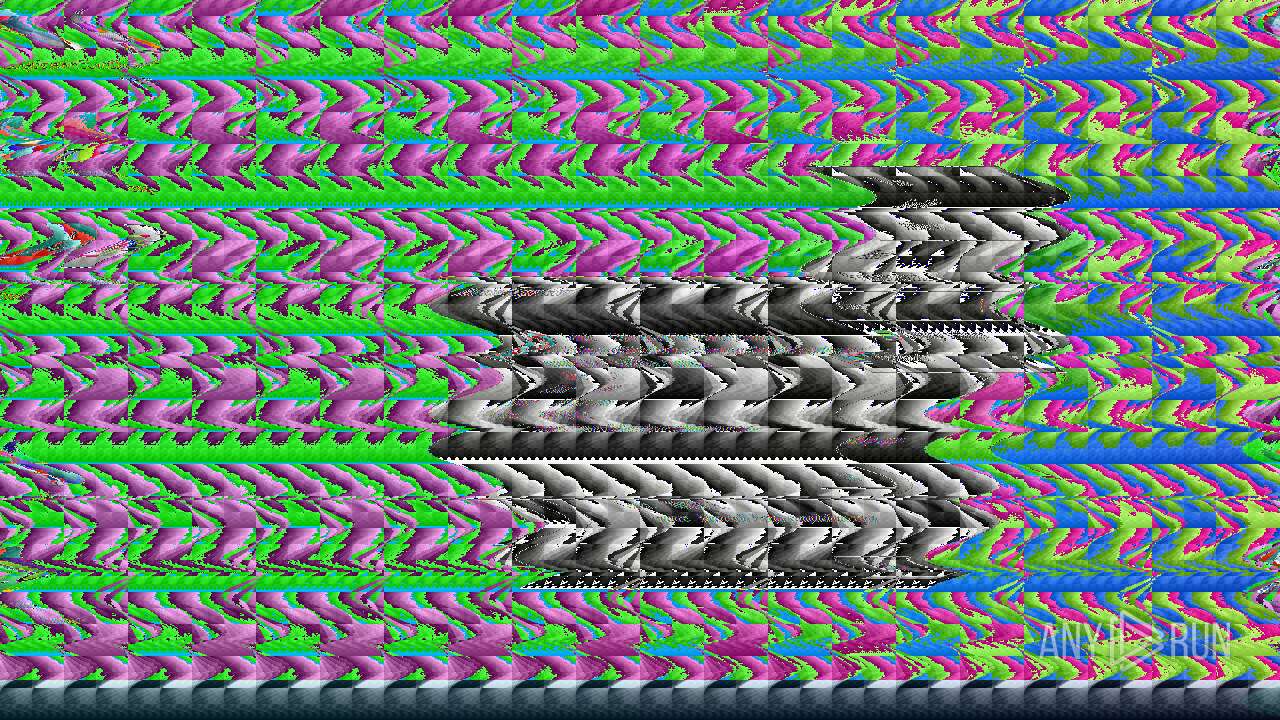
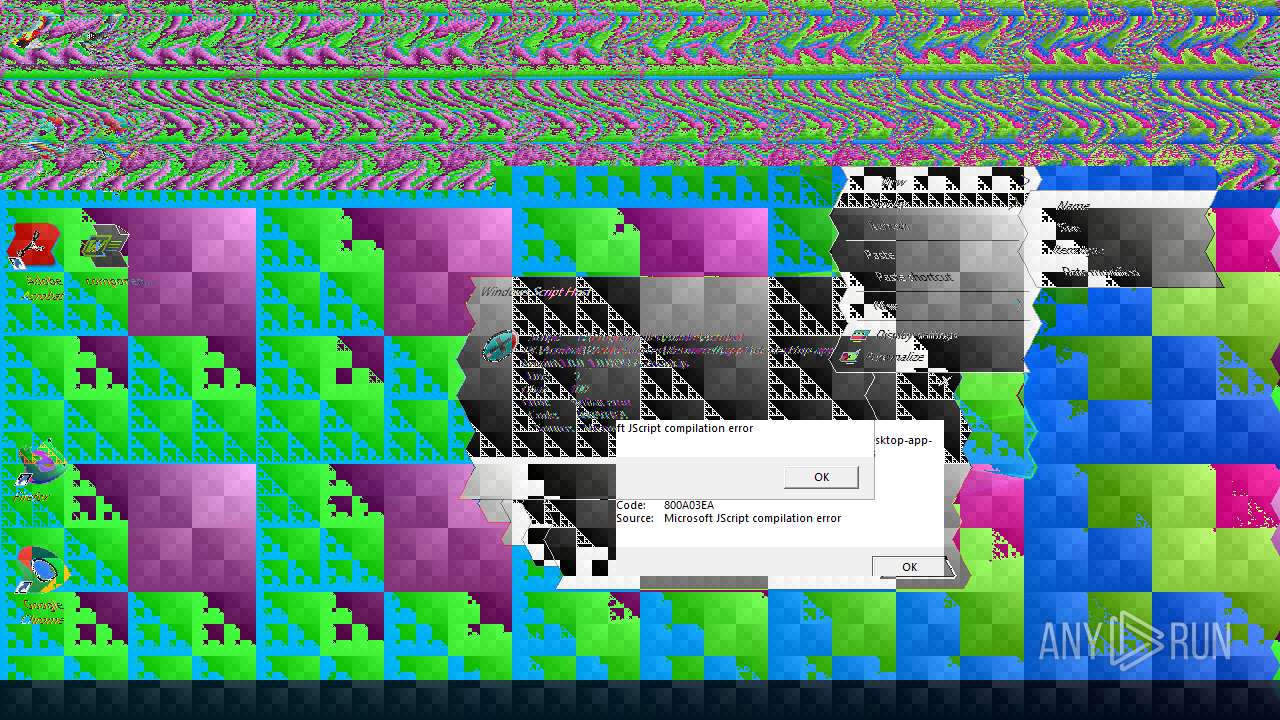
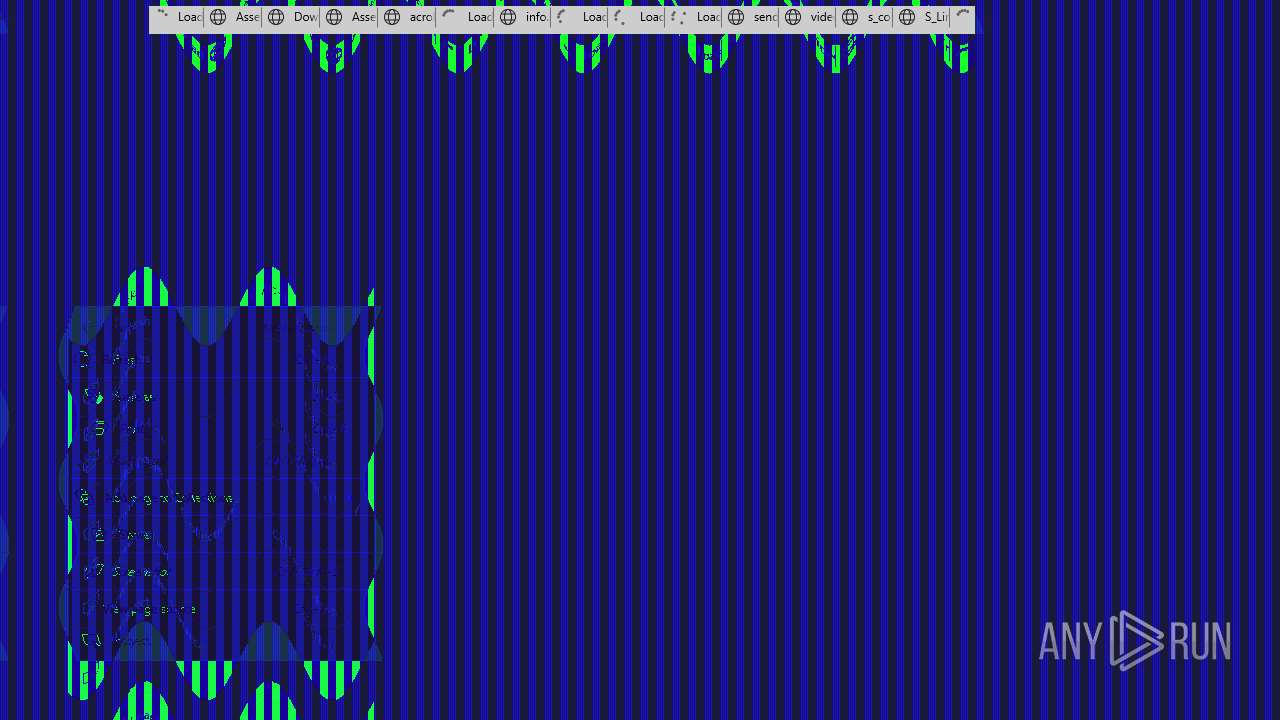
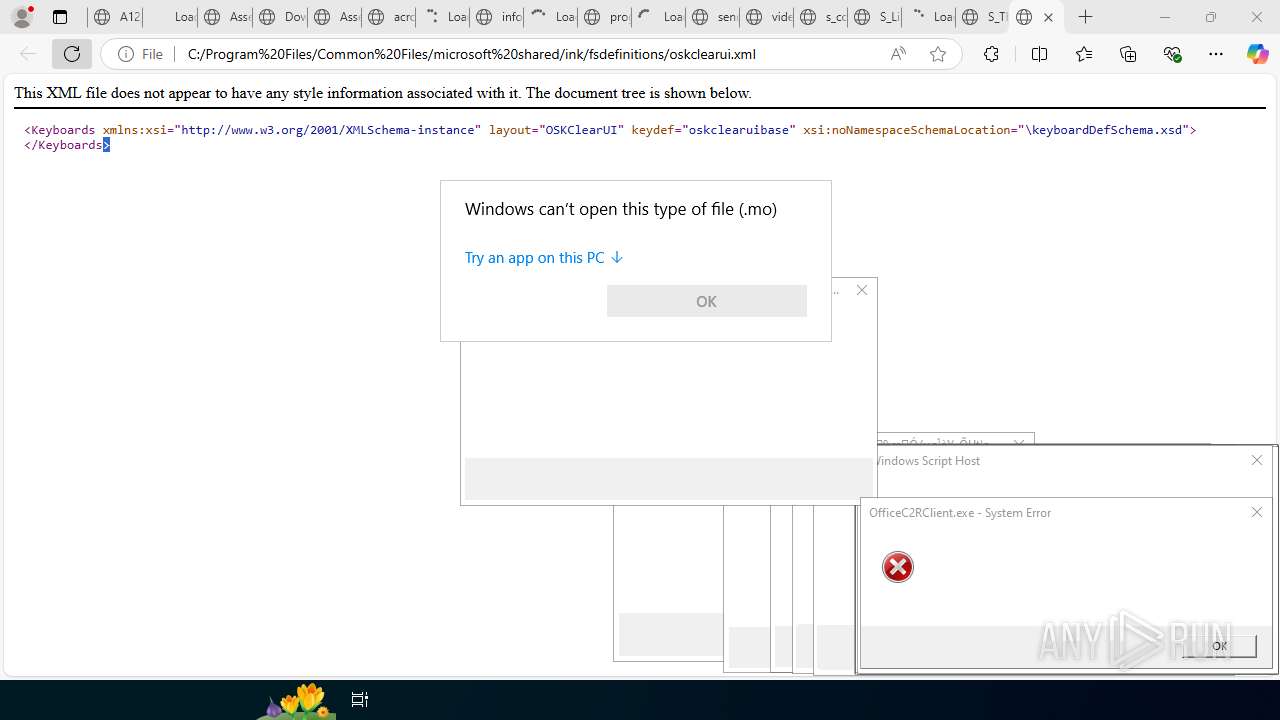
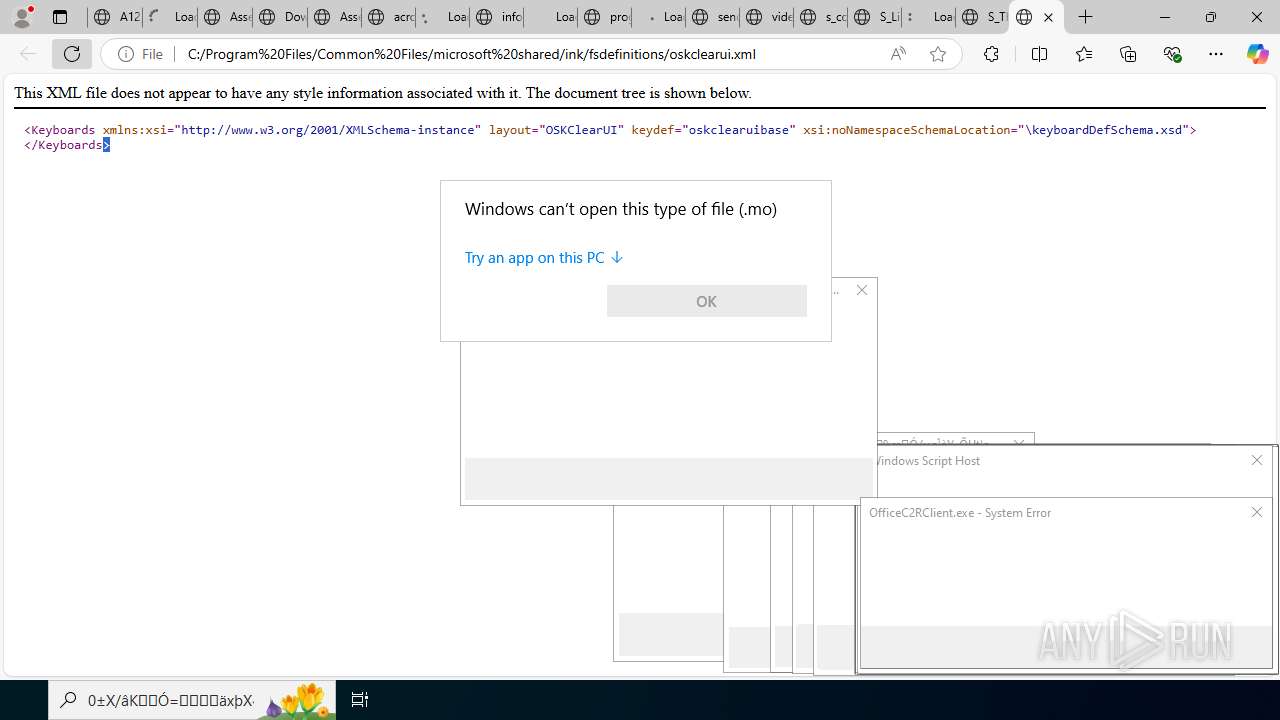
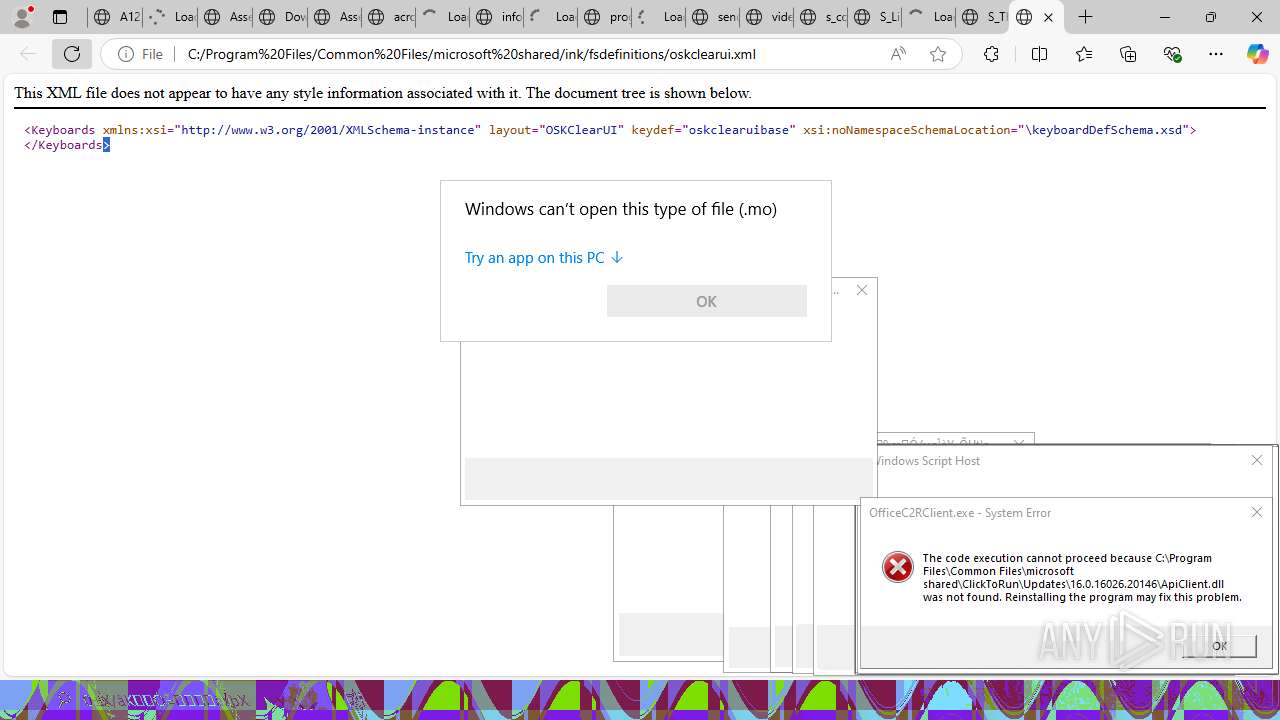
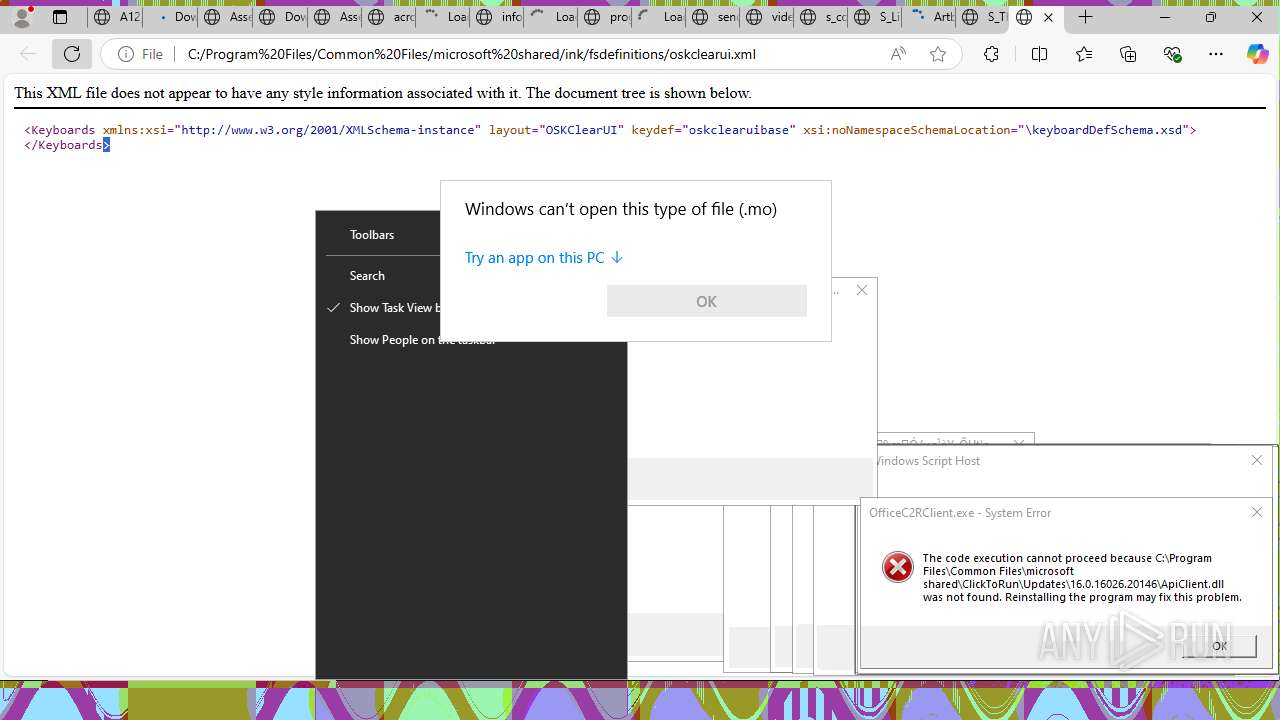
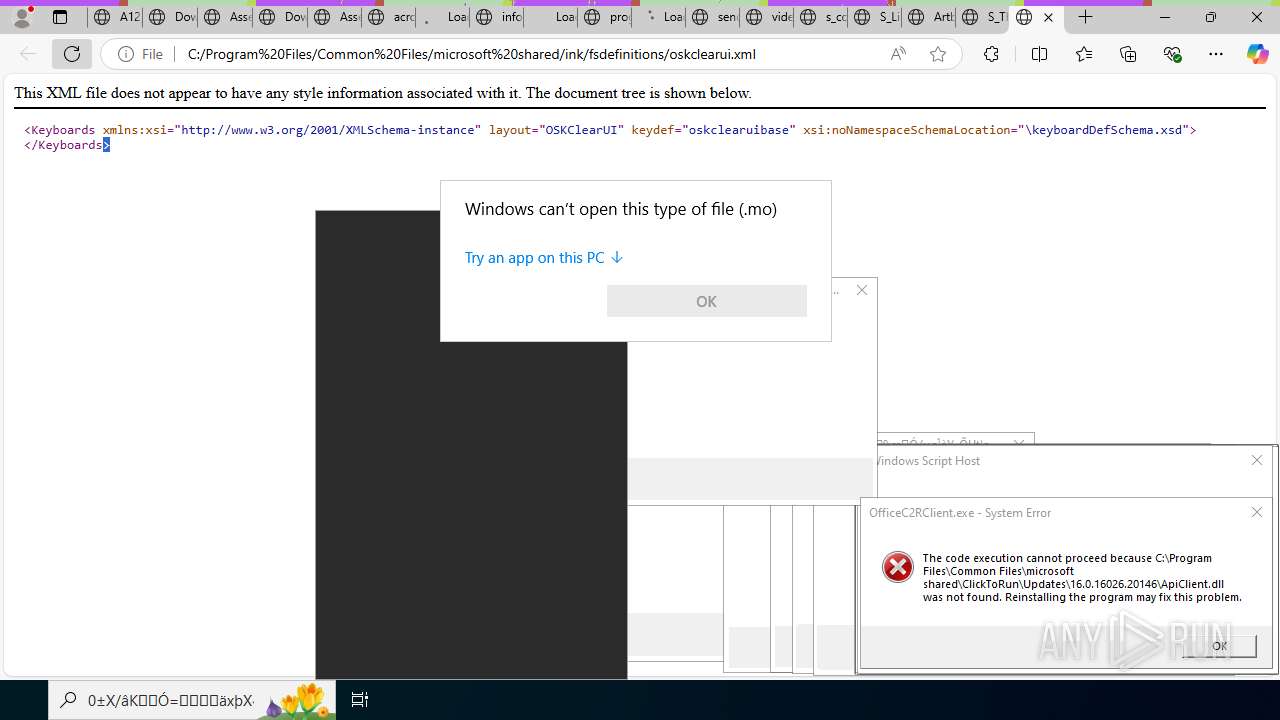
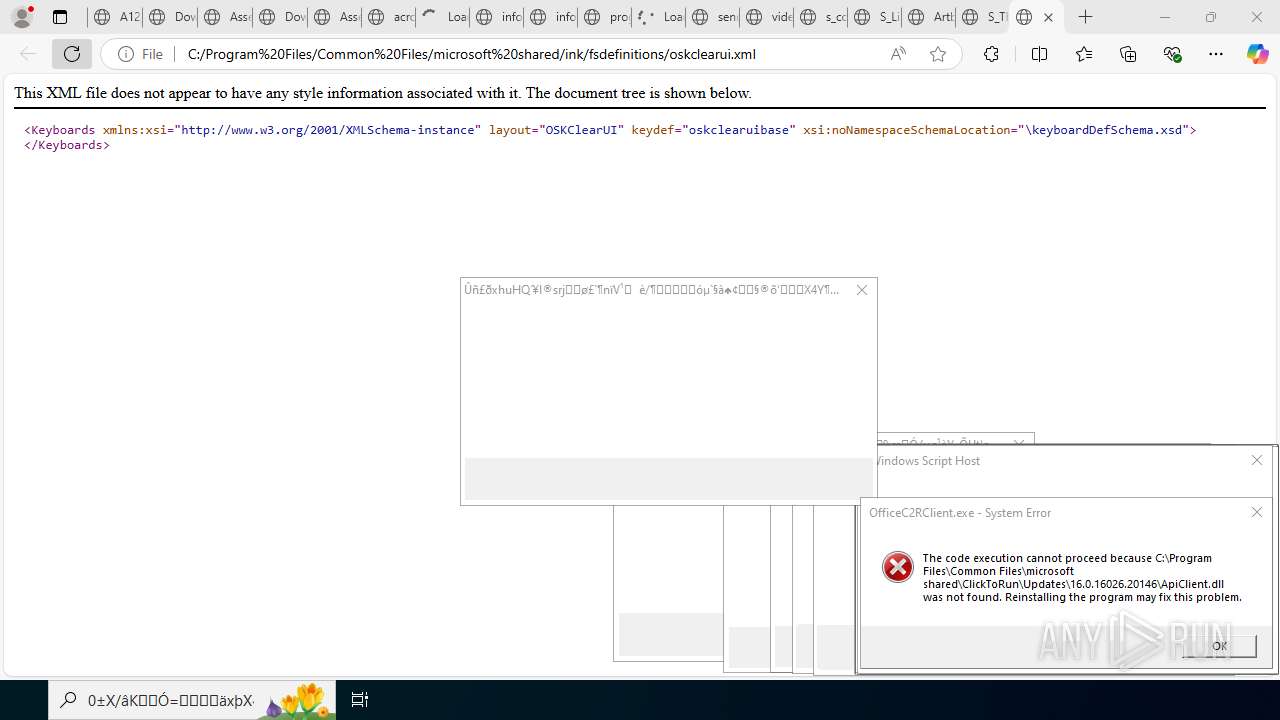
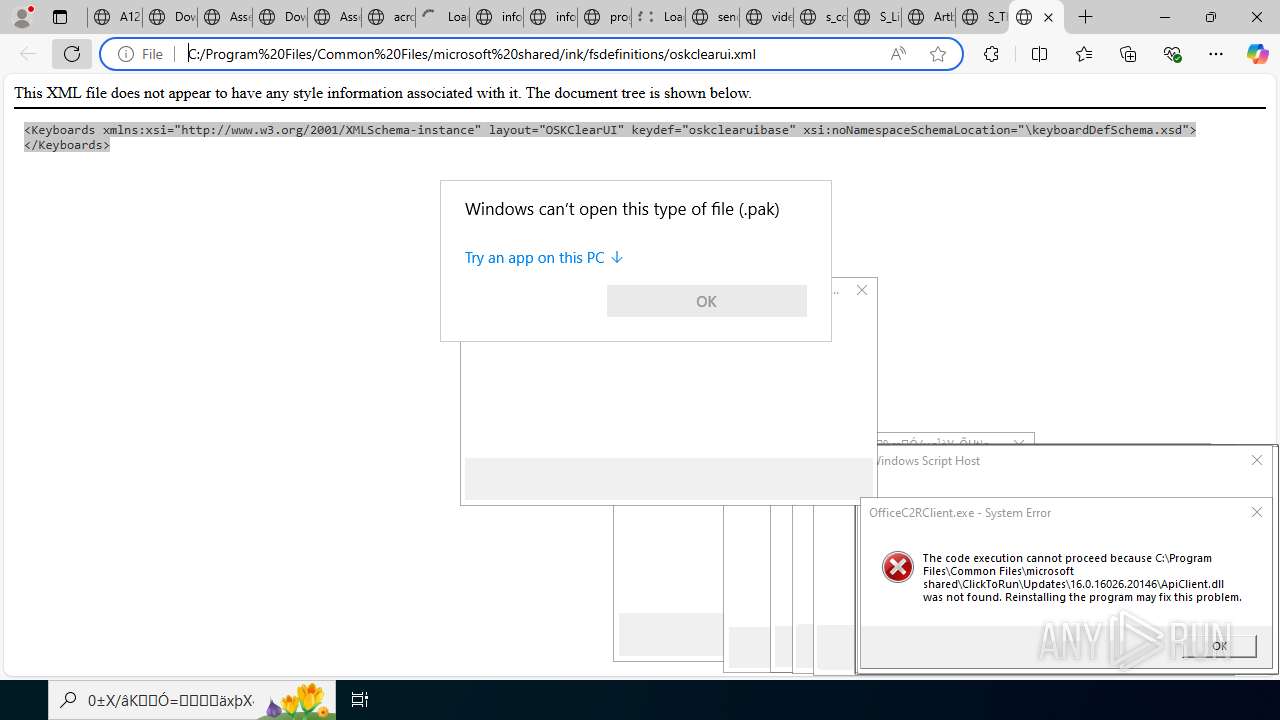
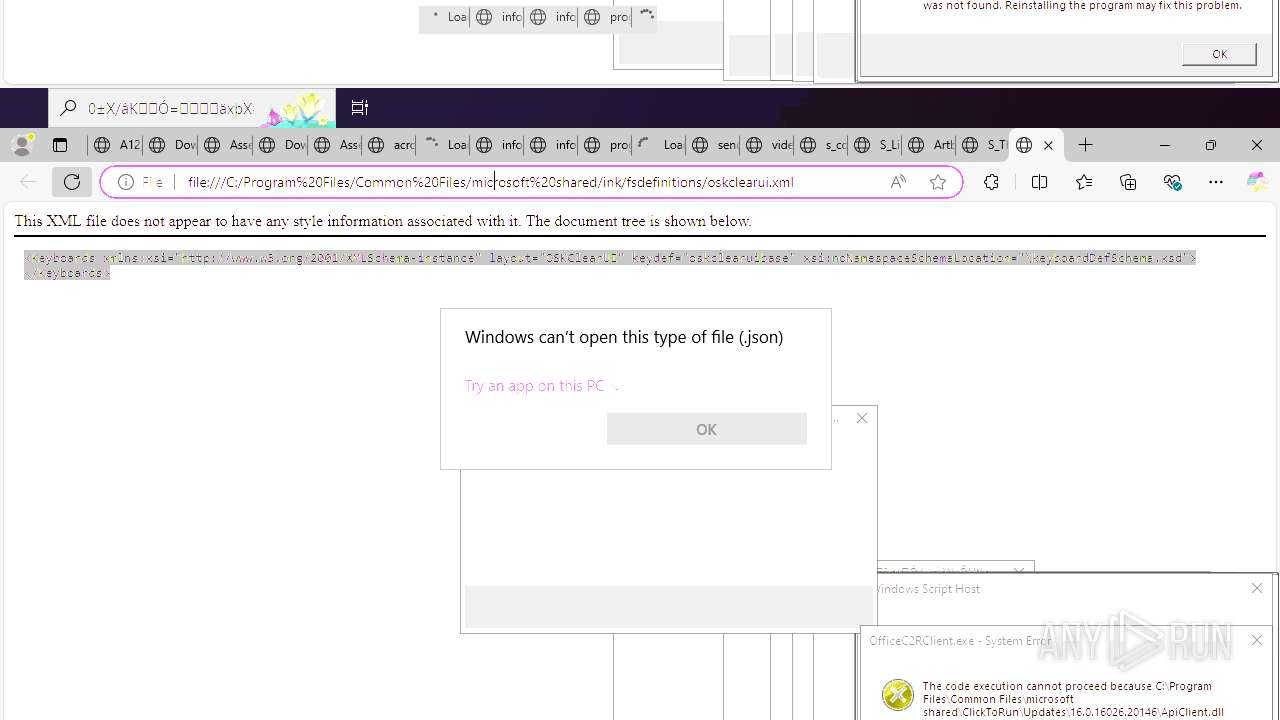
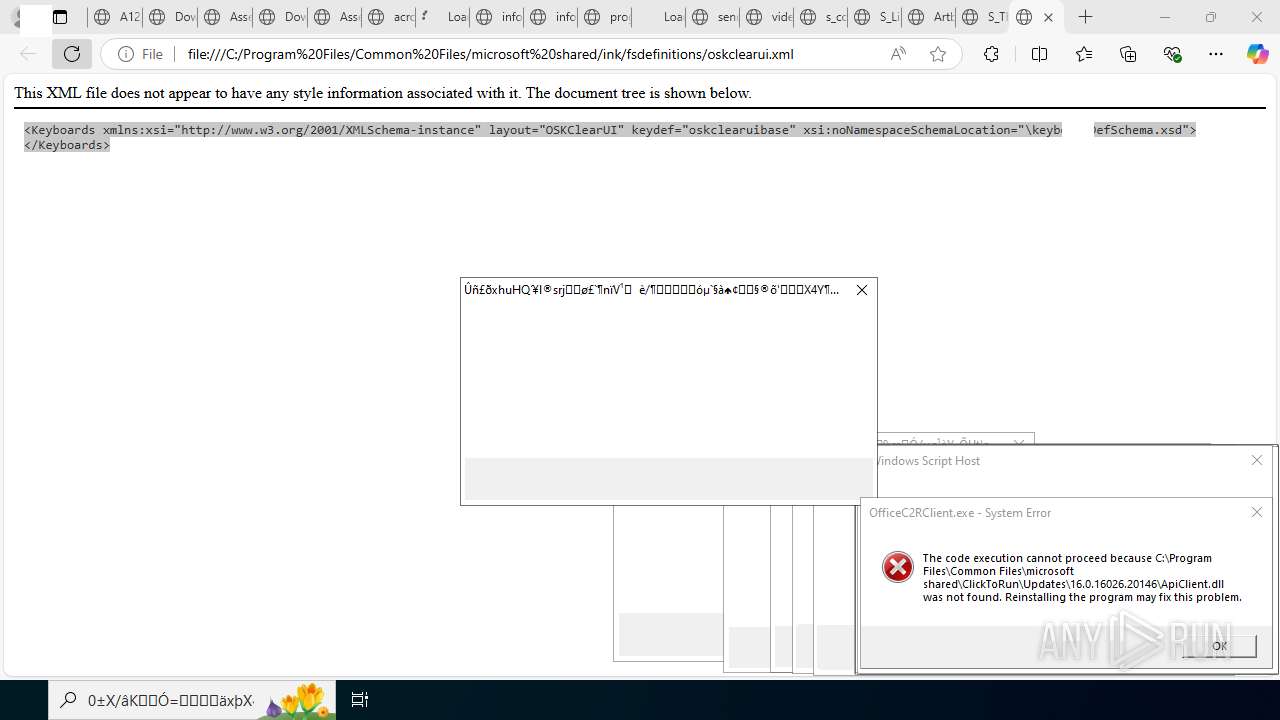
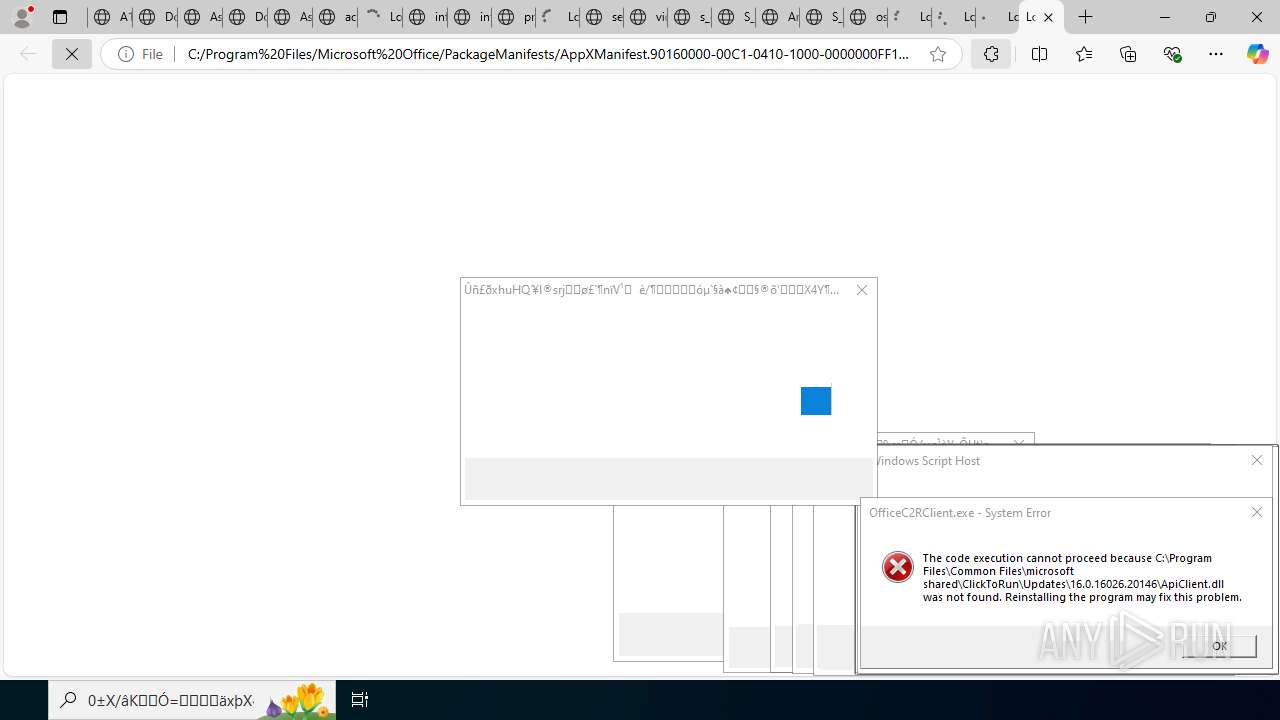
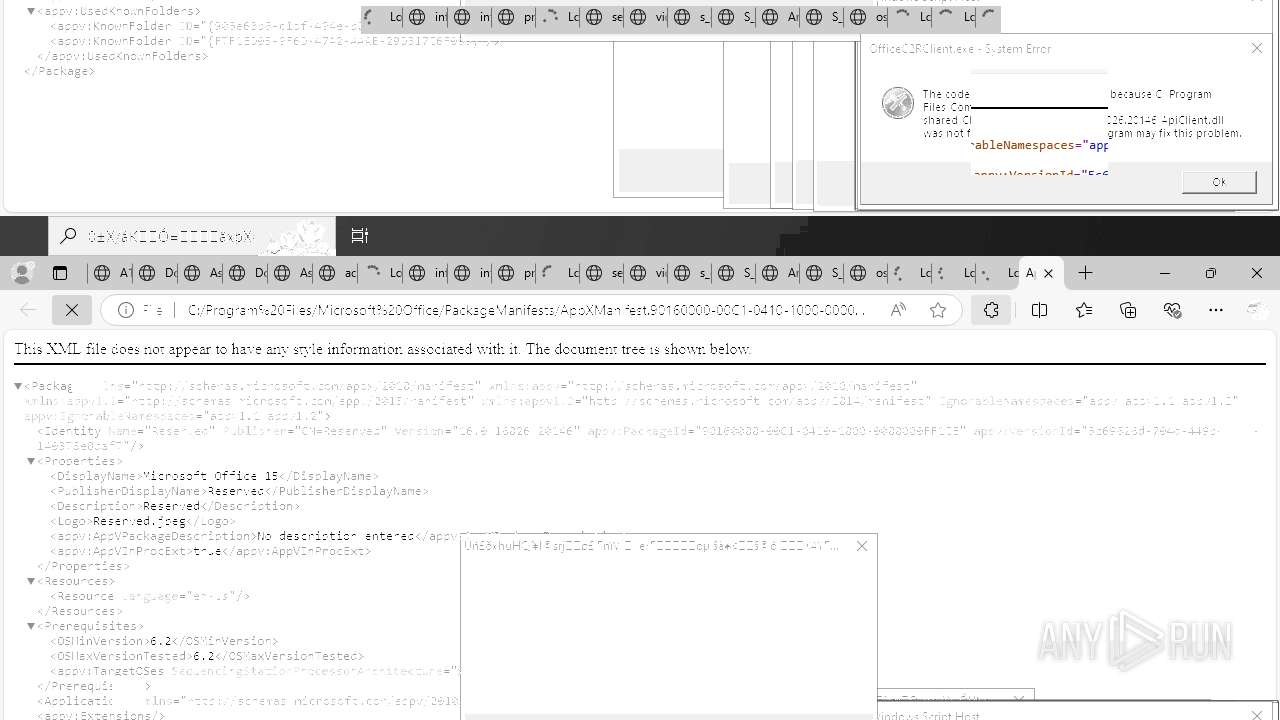
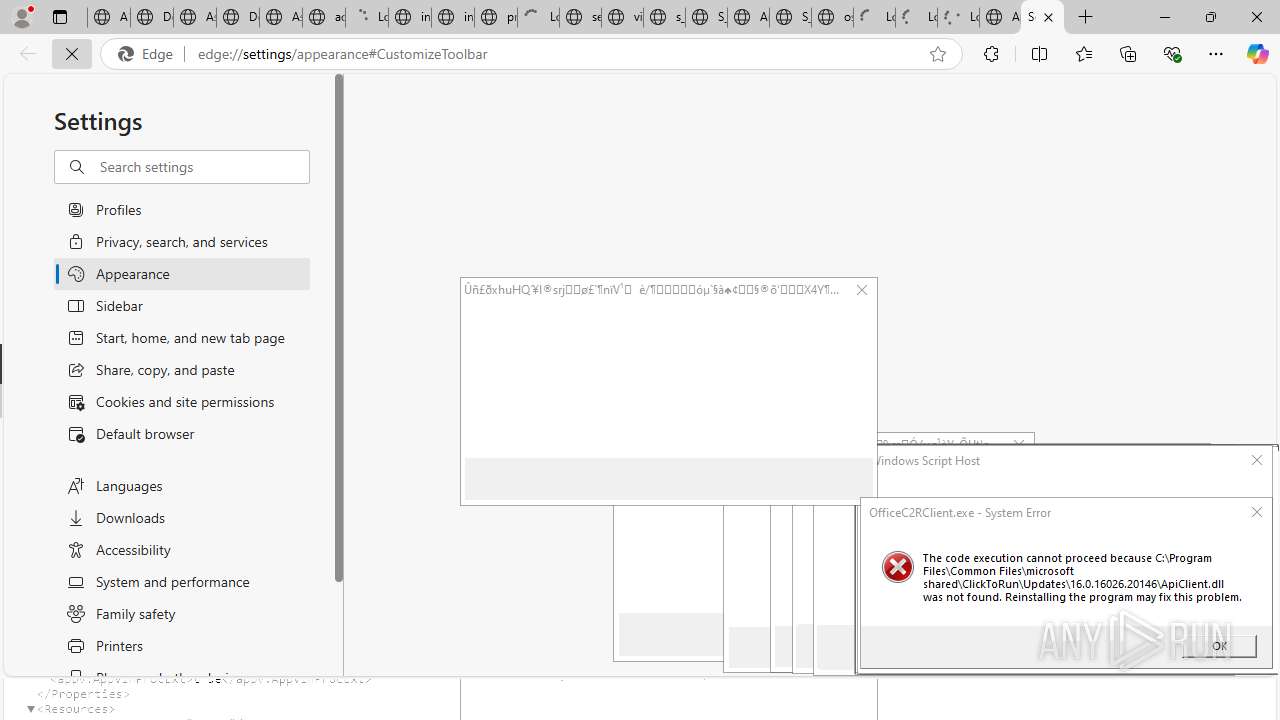
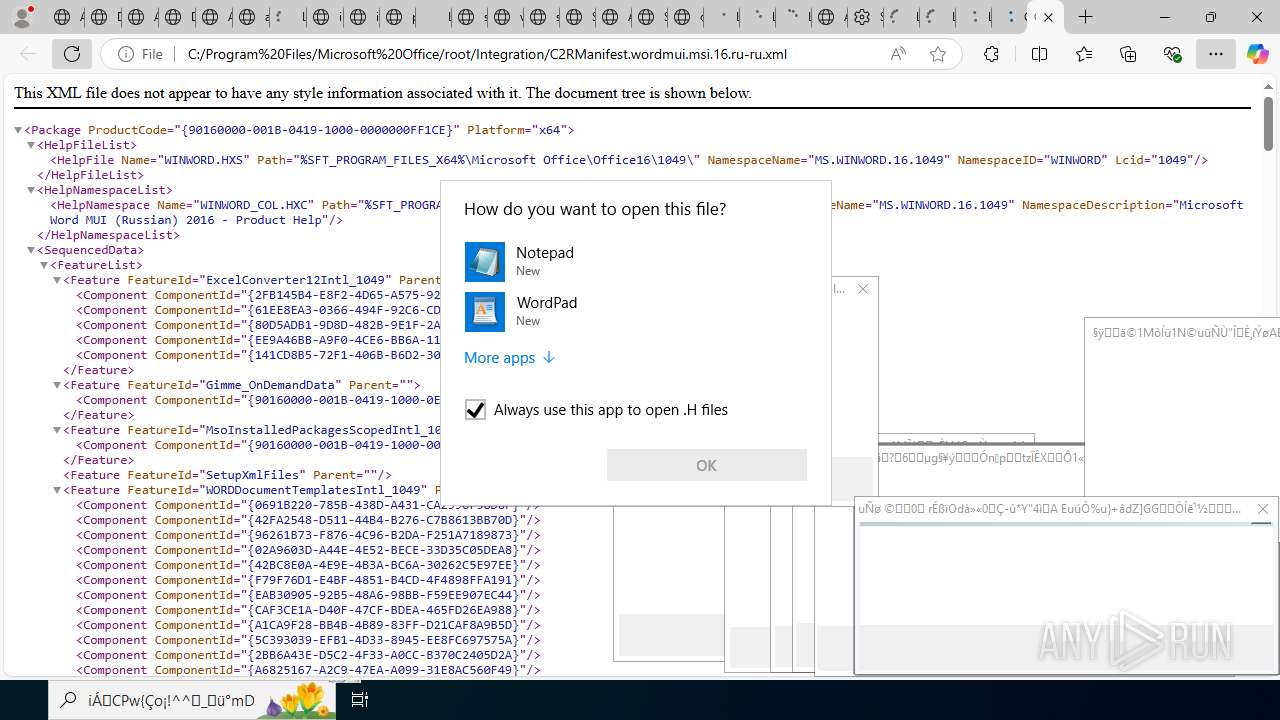
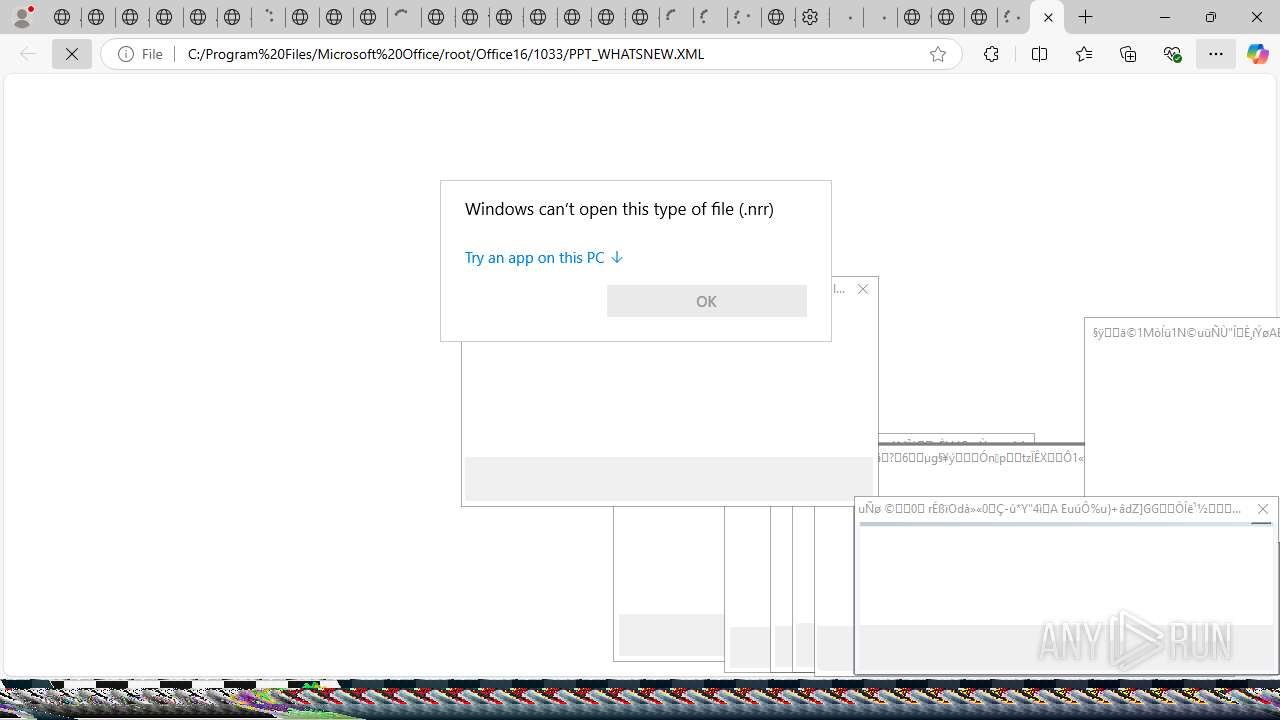
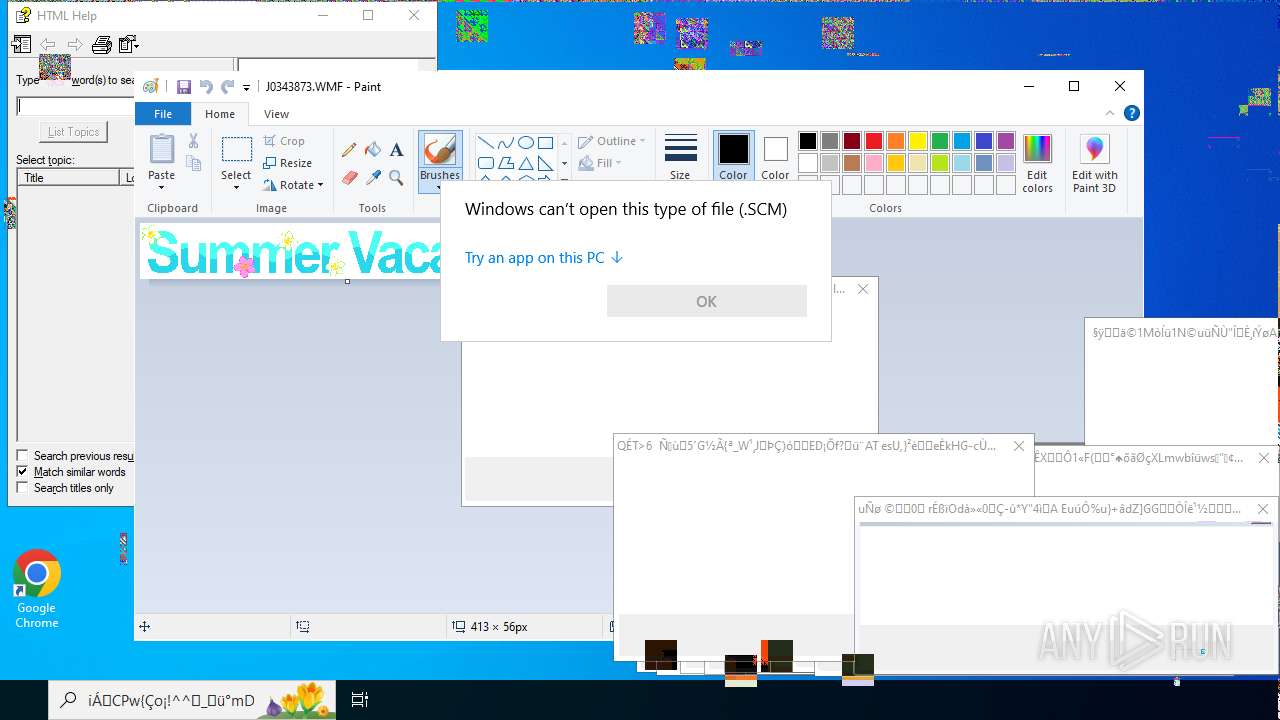
MALICIOUS
Monoxide mutex has been found
- 萩鬊搙鐌骜龾丿翘瑟躍憌澬毕圍暼苤.exe (PID: 4456)
SUSPICIOUS
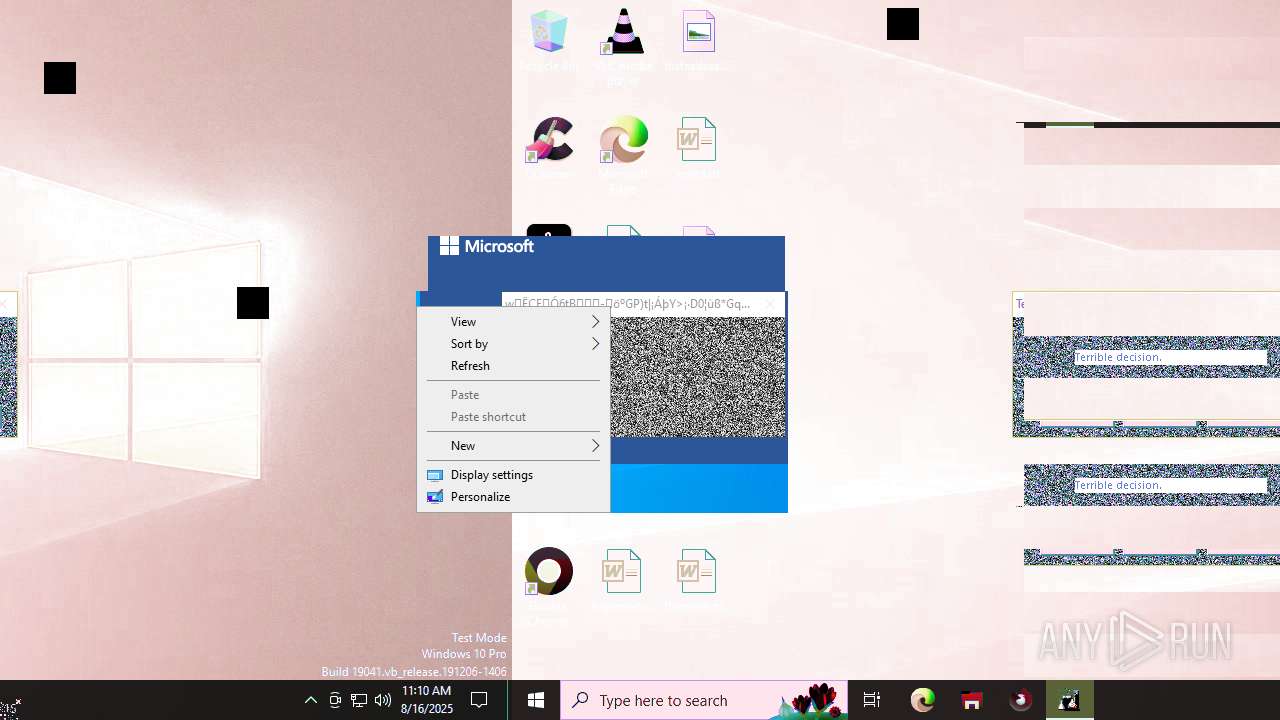
Starts itself from another location
- Monoxidex86.exe (PID: 7032)
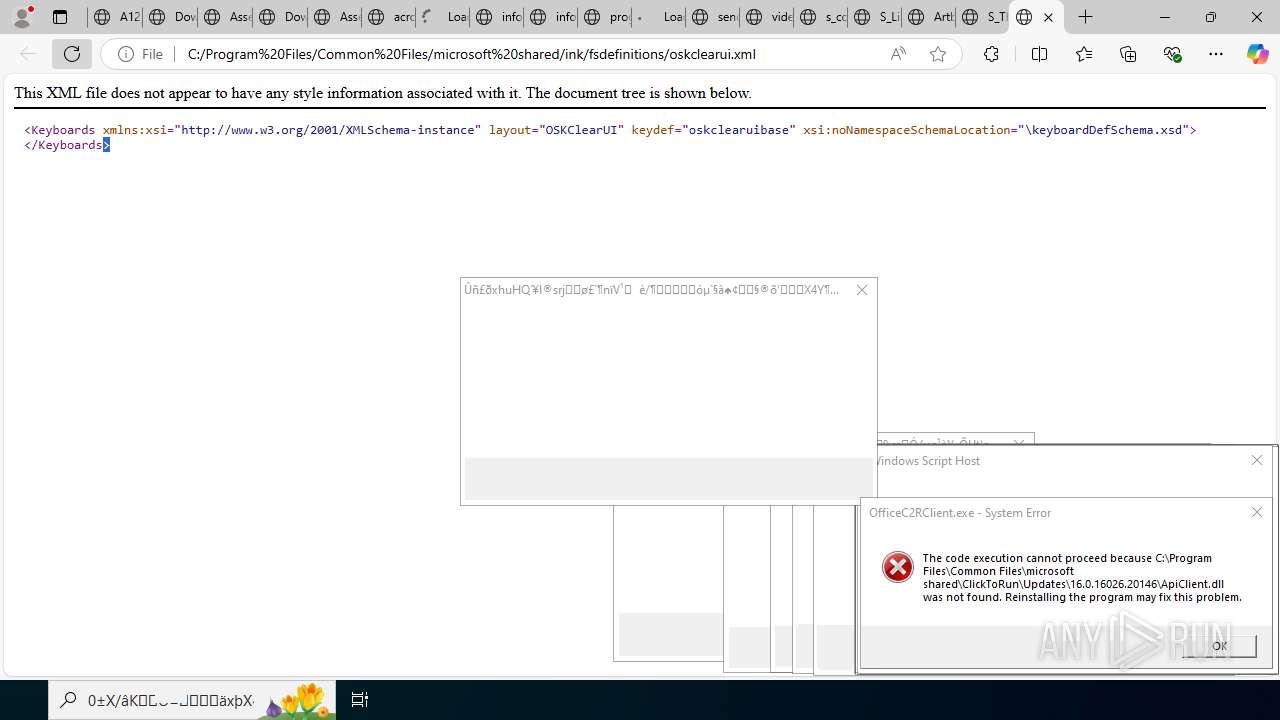
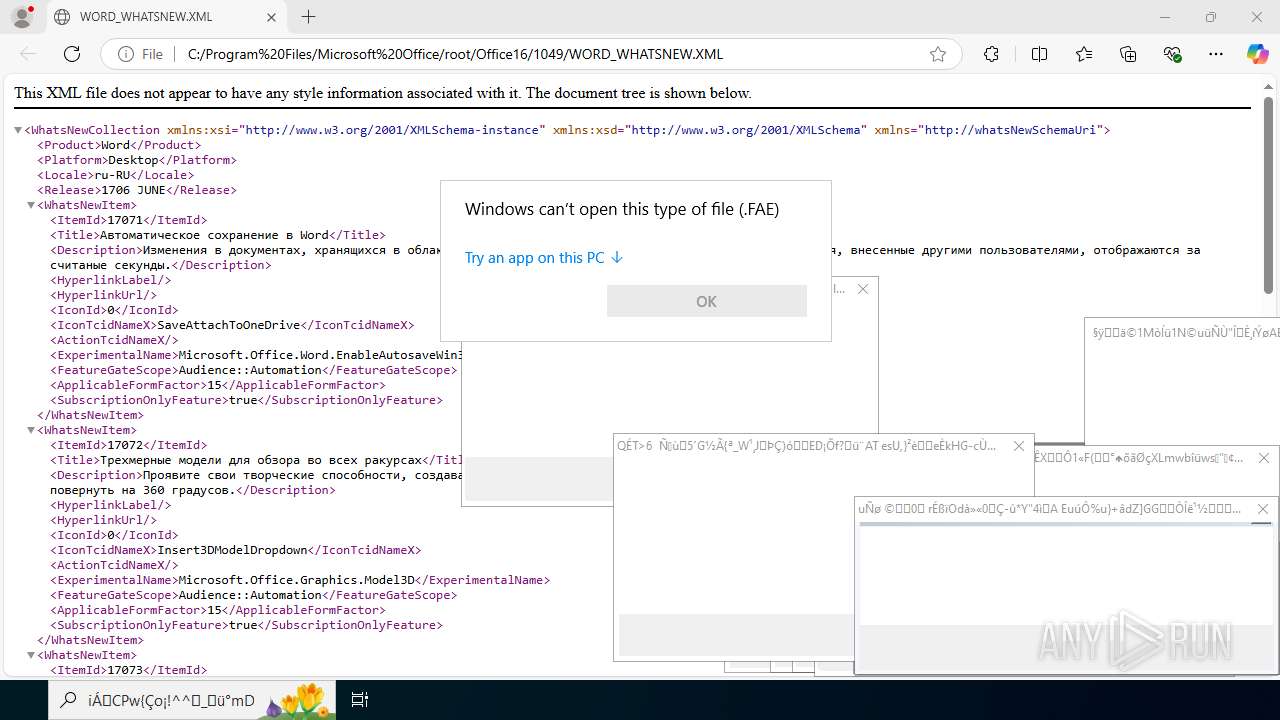
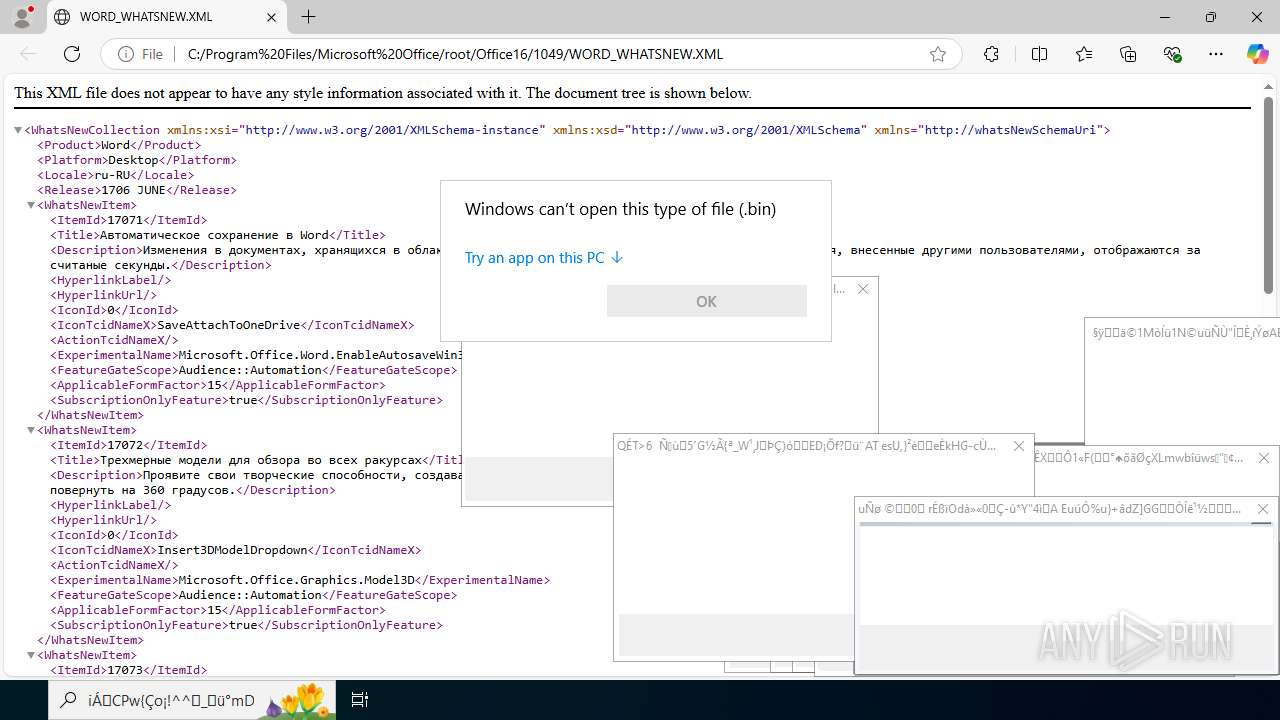
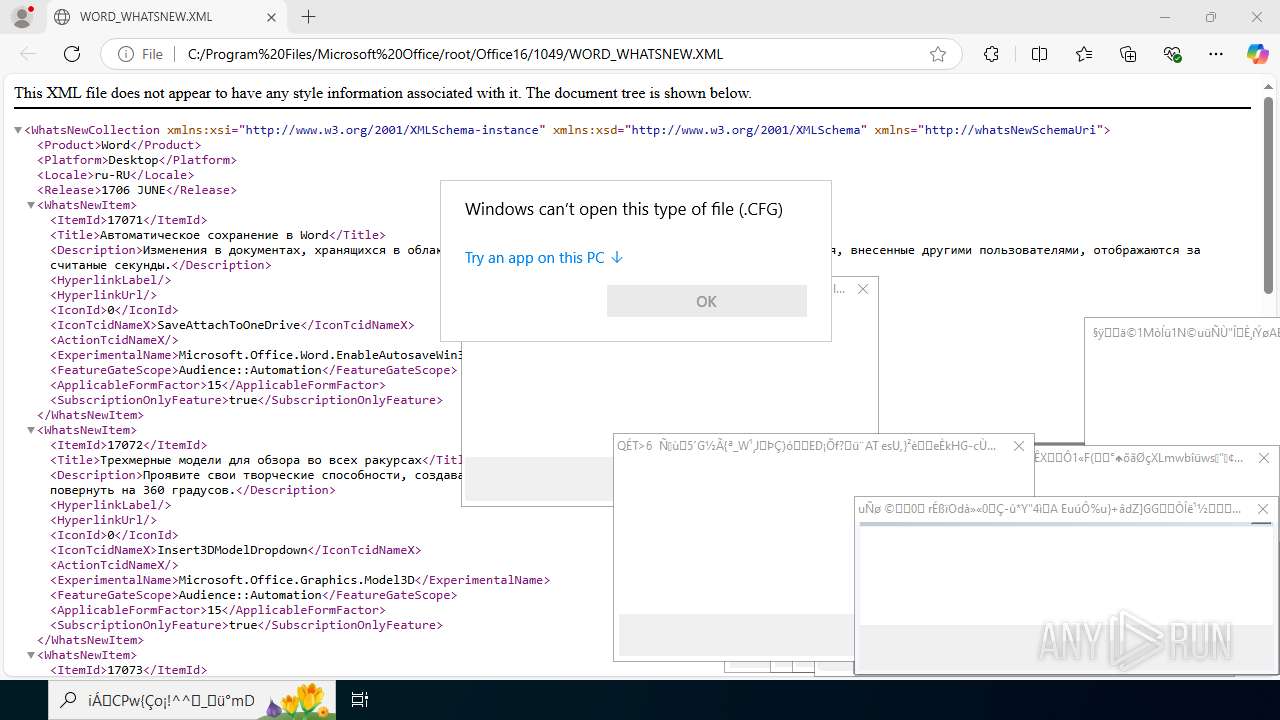
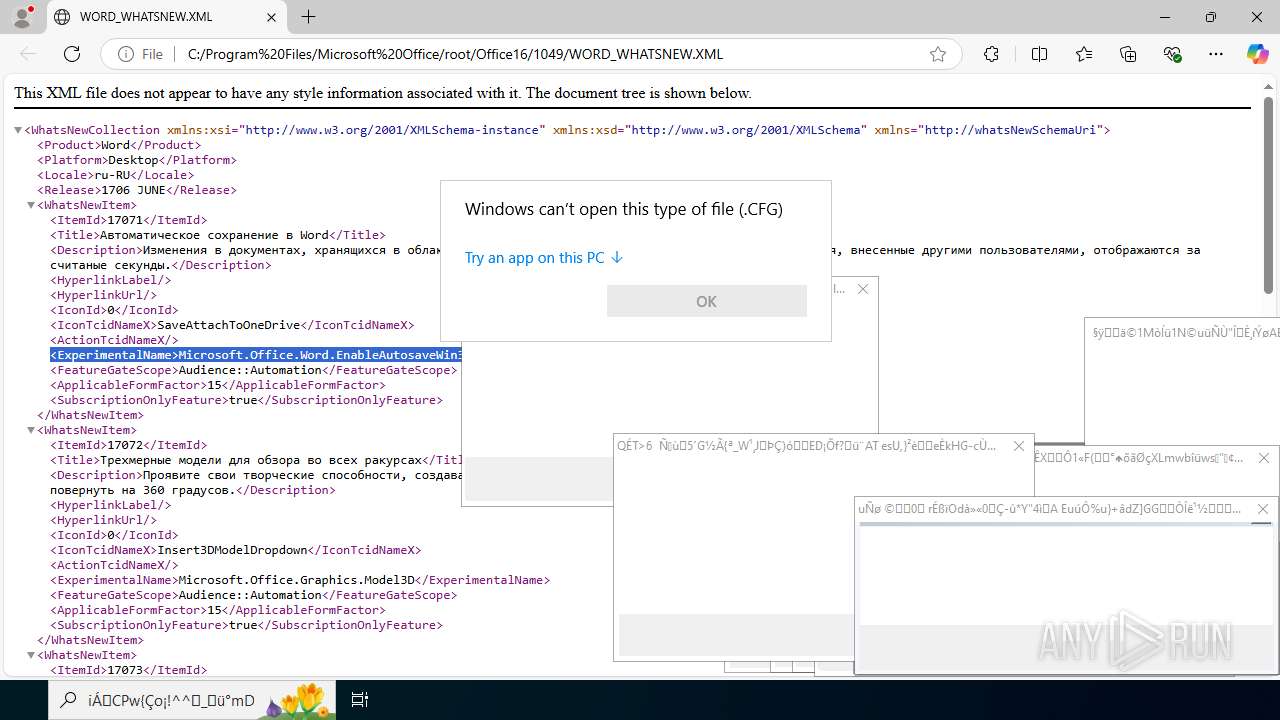
Executable content was dropped or overwritten
- Monoxidex86.exe (PID: 7032)
Creates file in the systems drive root
- 萩鬊搙鐌骜龾丿翘瑟躍憌澬毕圍暼苤.exe (PID: 4456)
Reads security settings of Internet Explorer
- 萩鬊搙鐌骜龾丿翘瑟躍憌澬毕圍暼苤.exe (PID: 4456)
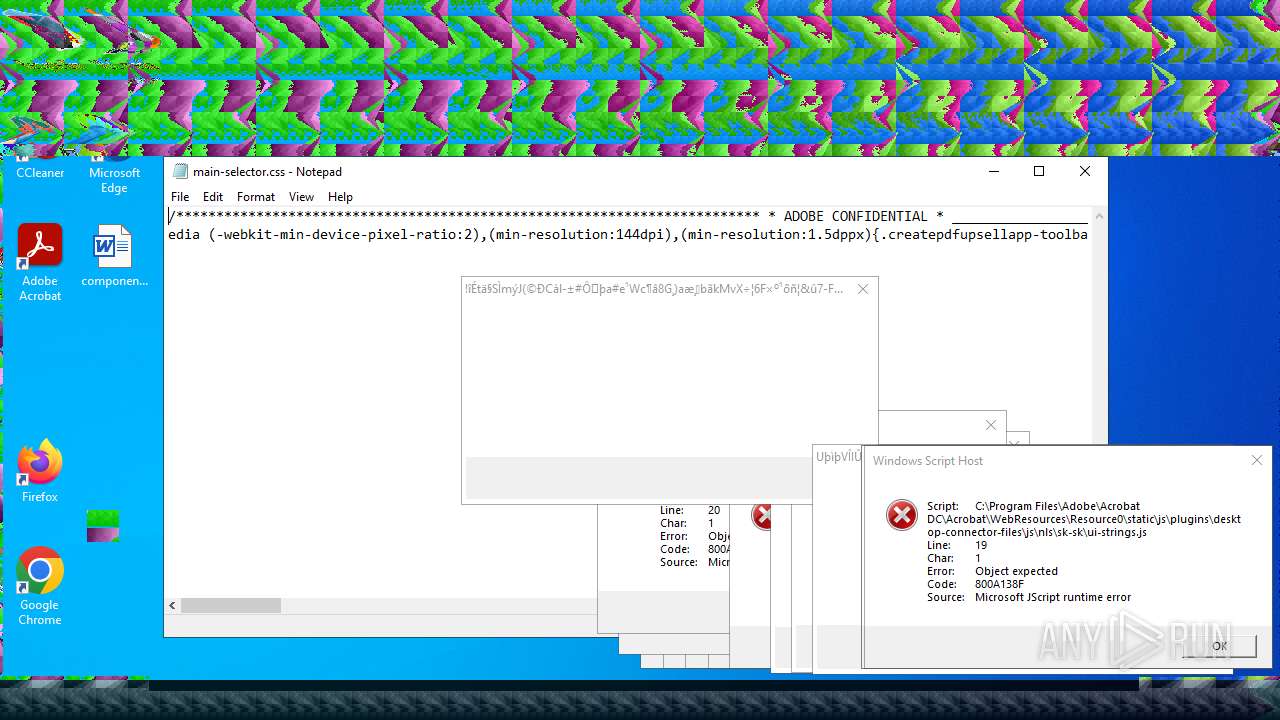
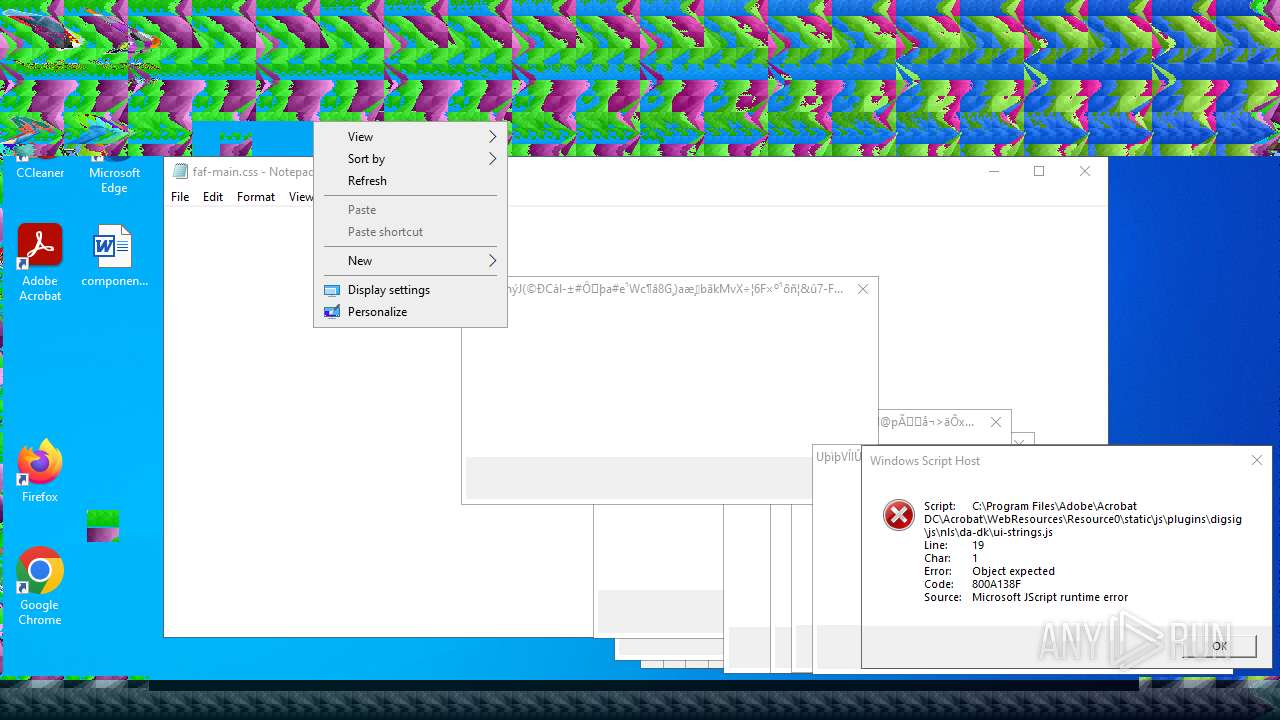
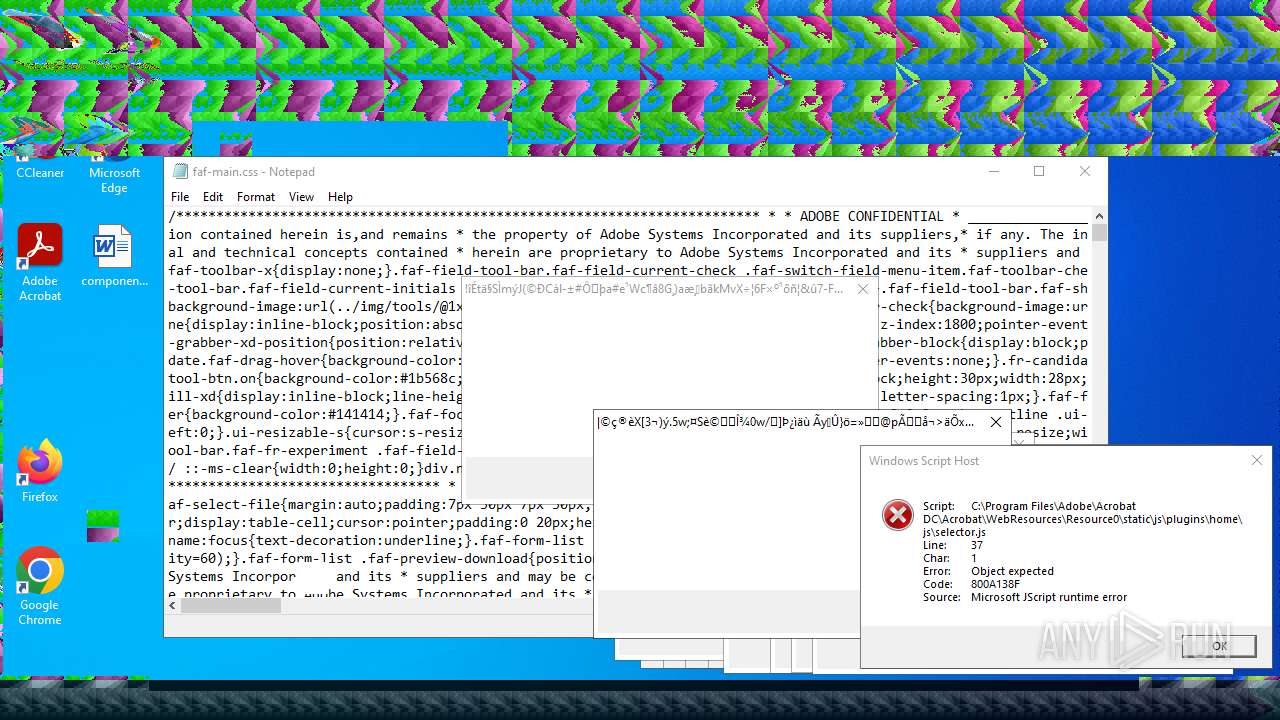
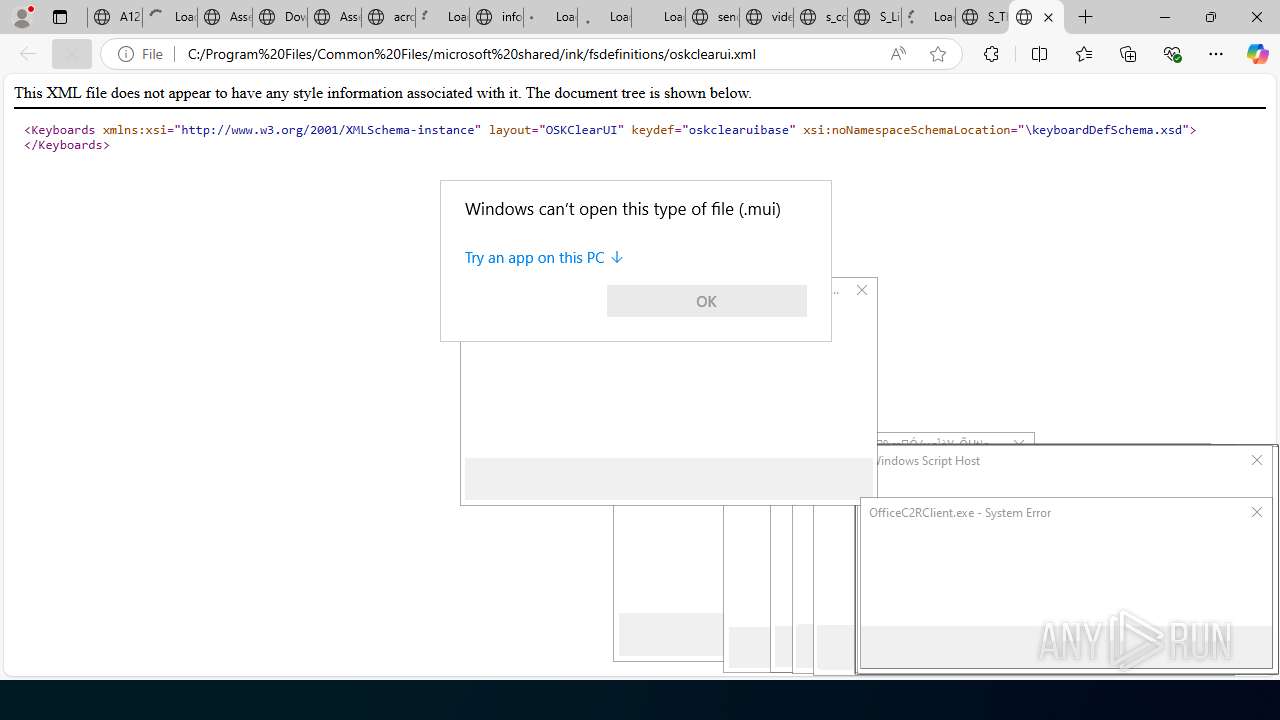
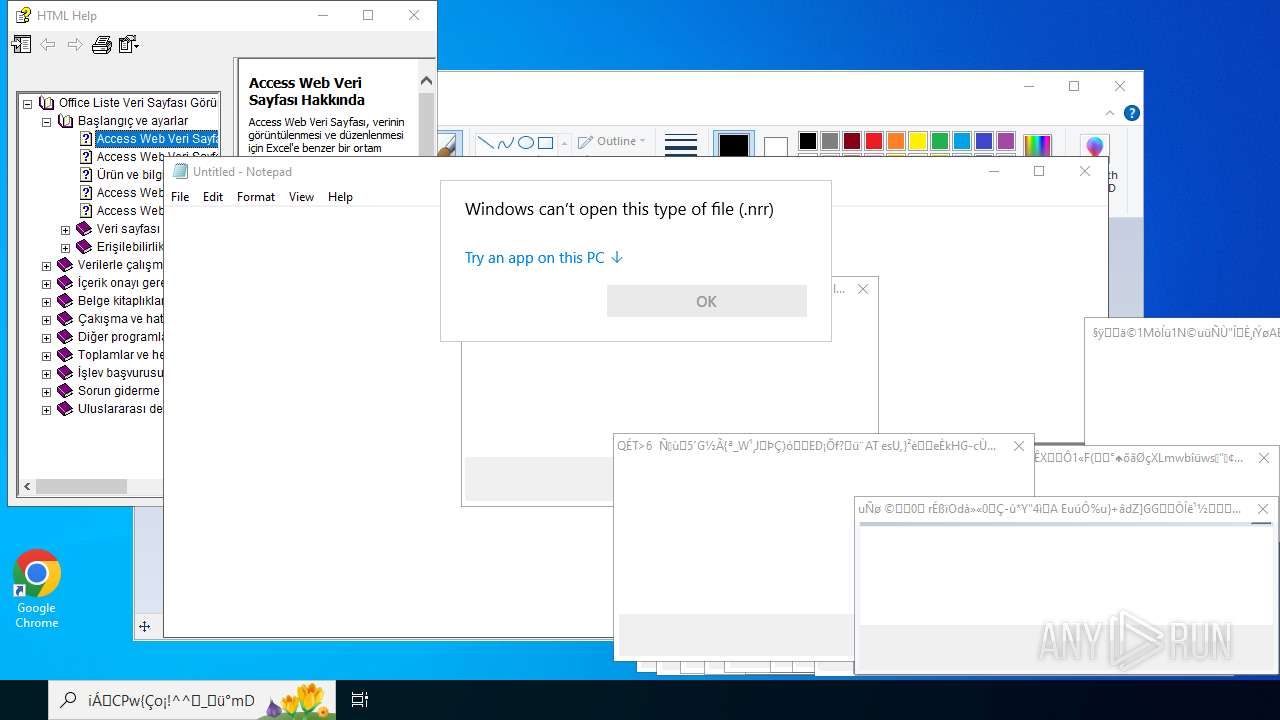
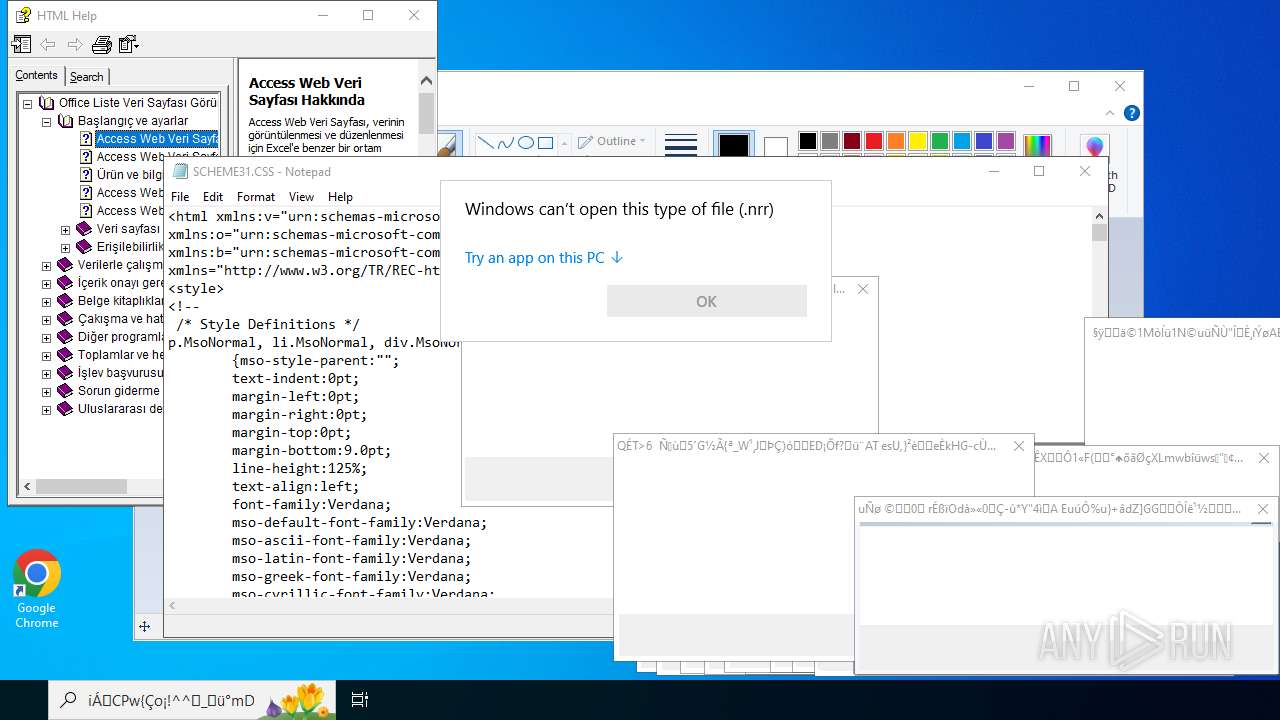
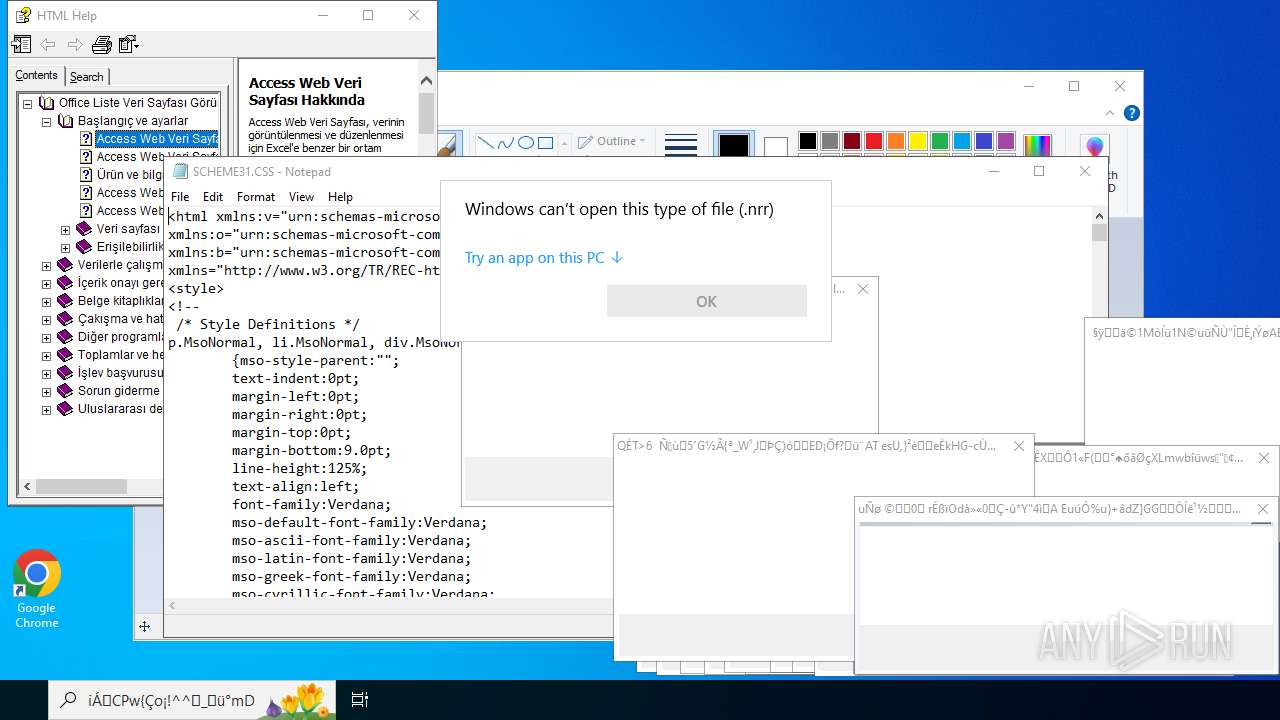
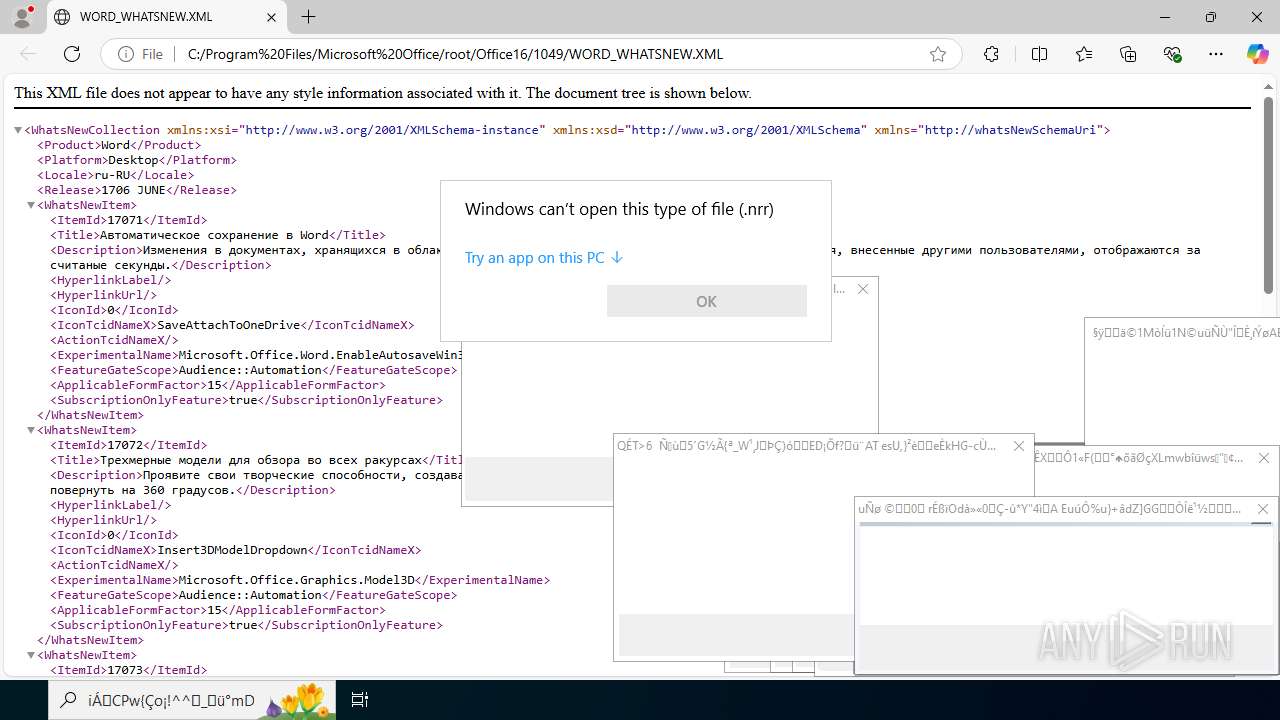
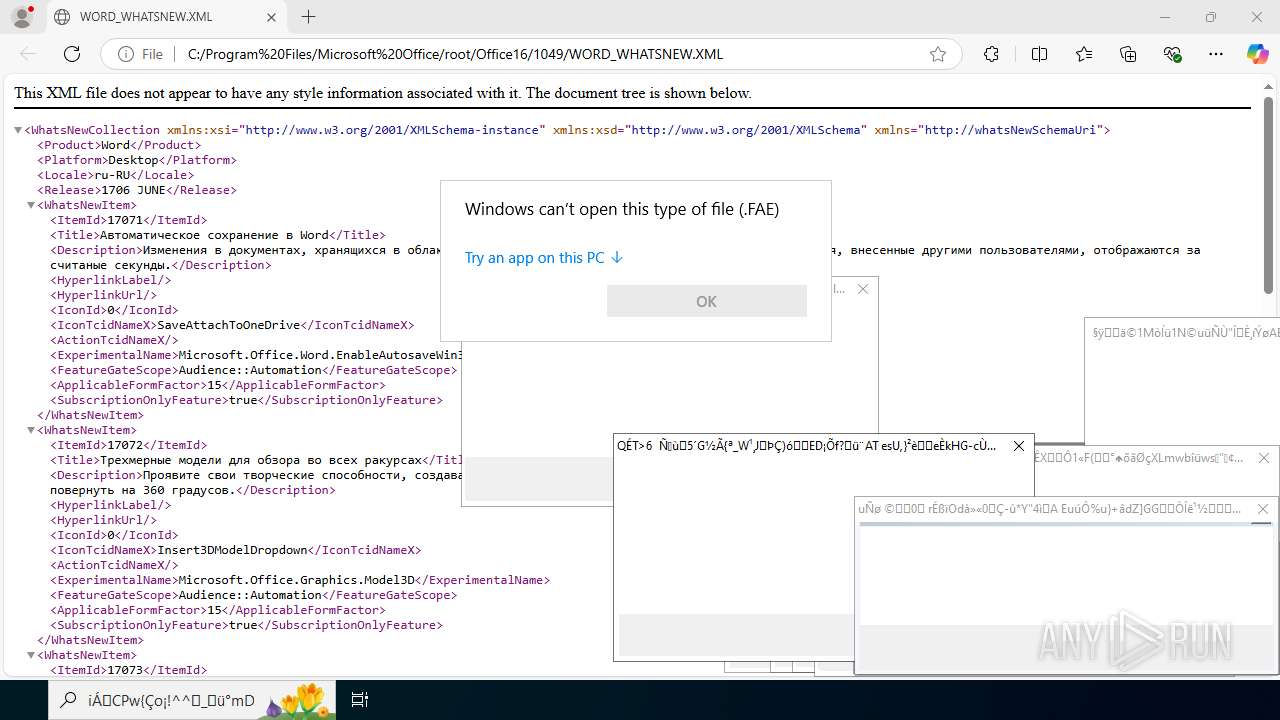
The process executes JS scripts
- 萩鬊搙鐌骜龾丿翘瑟躍憌澬毕圍暼苤.exe (PID: 4456)
There is functionality for taking screenshot (YARA)
- 萩鬊搙鐌骜龾丿翘瑟躍憌澬毕圍暼苤.exe (PID: 4456)
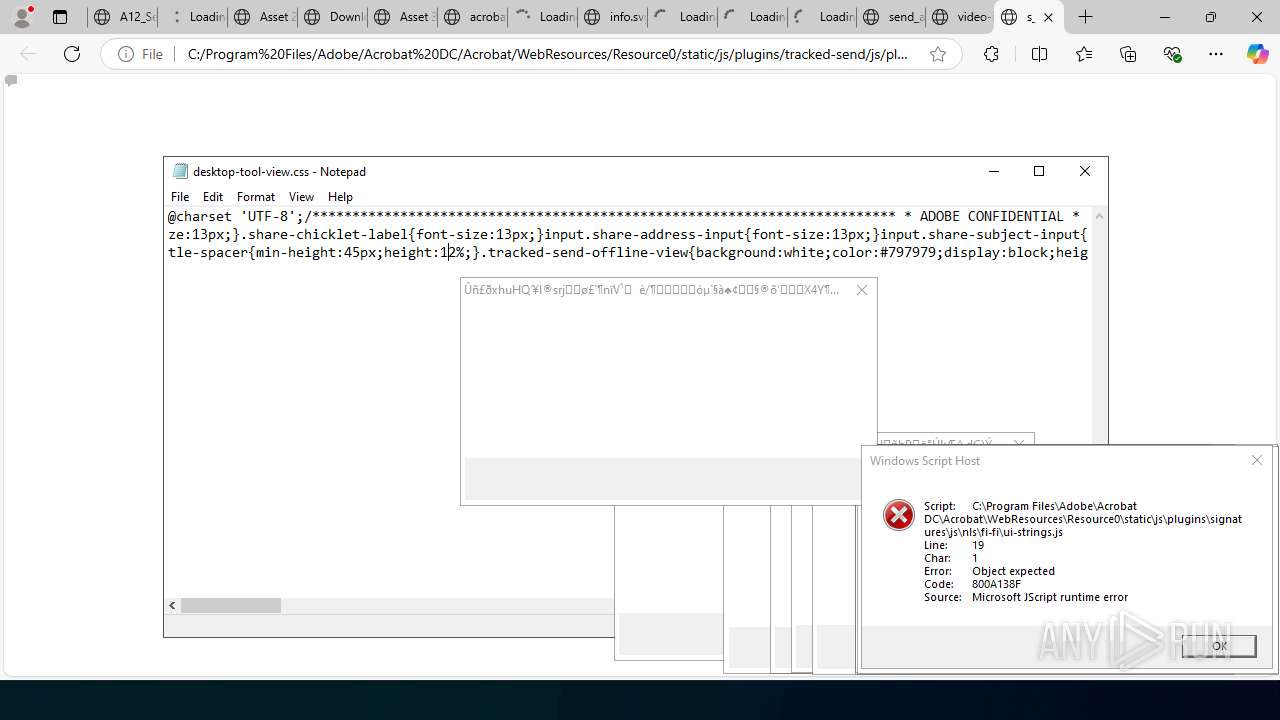
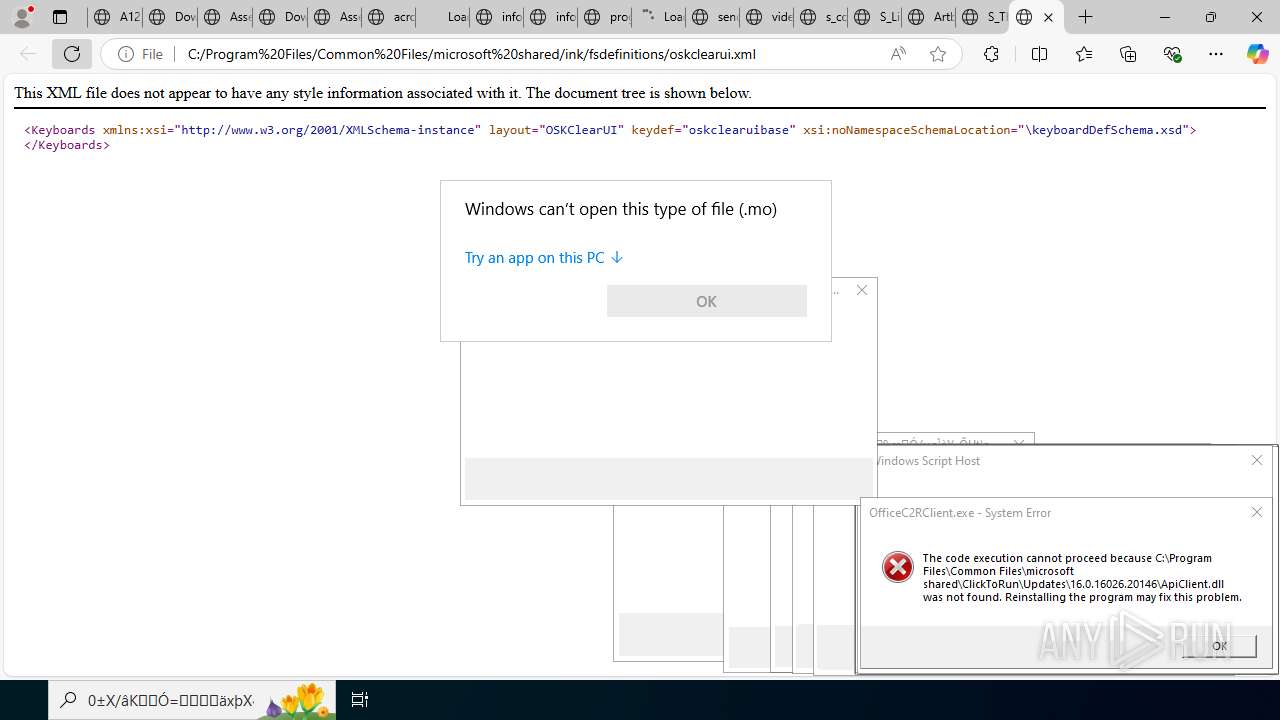
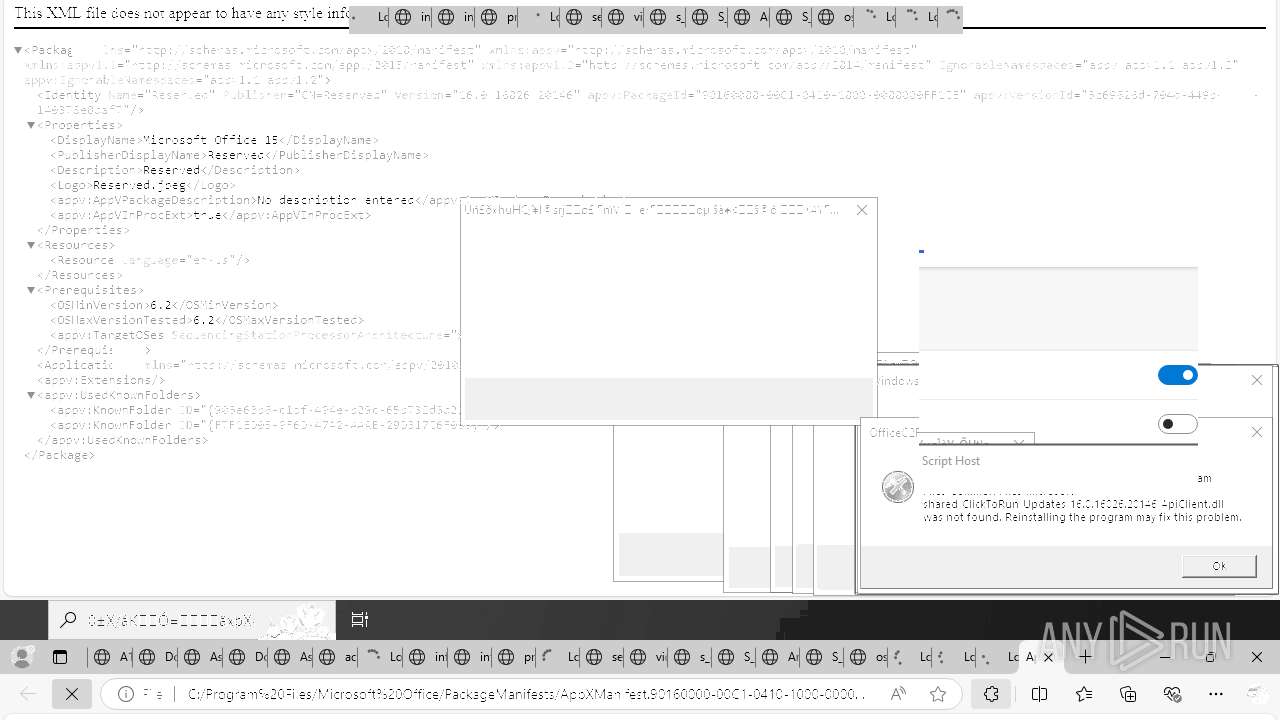
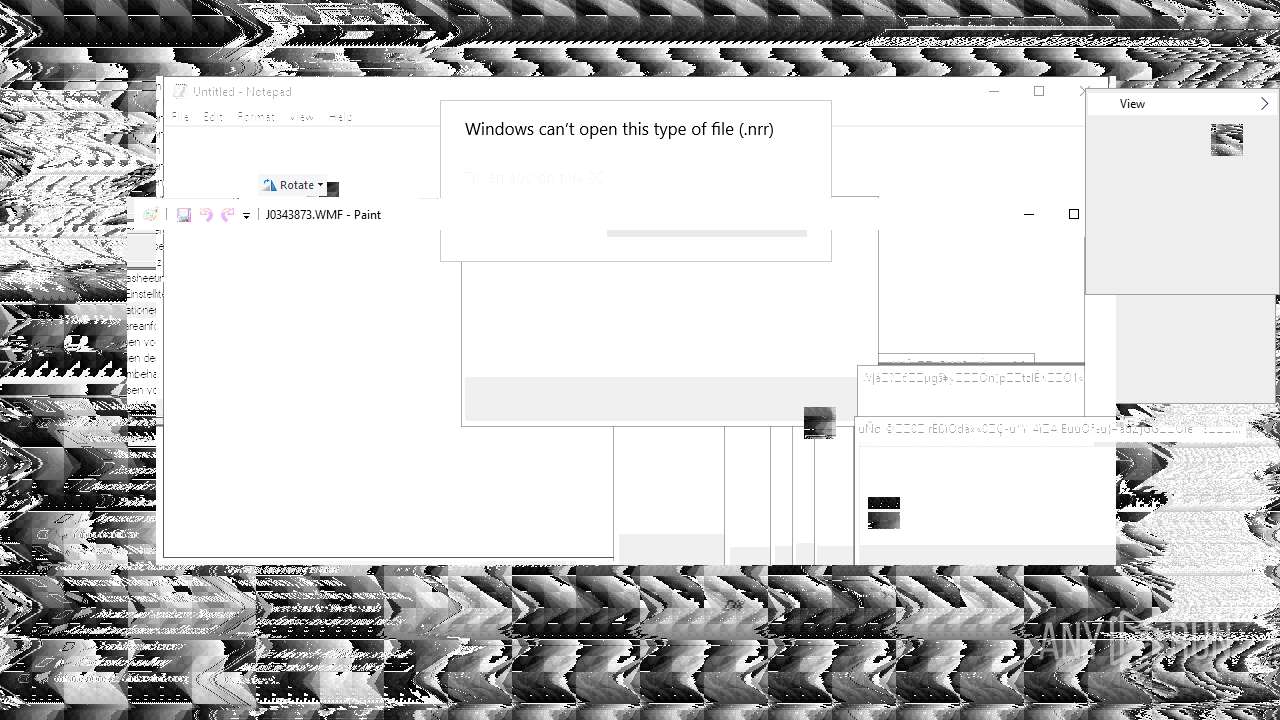
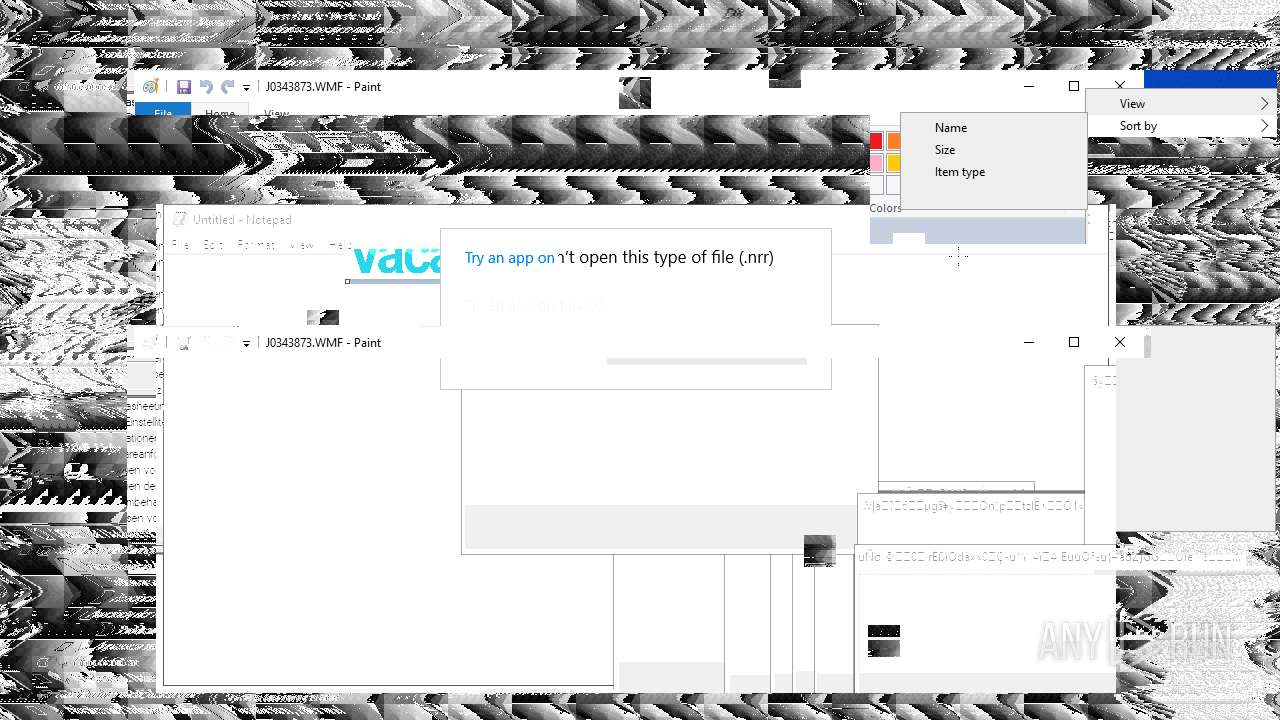
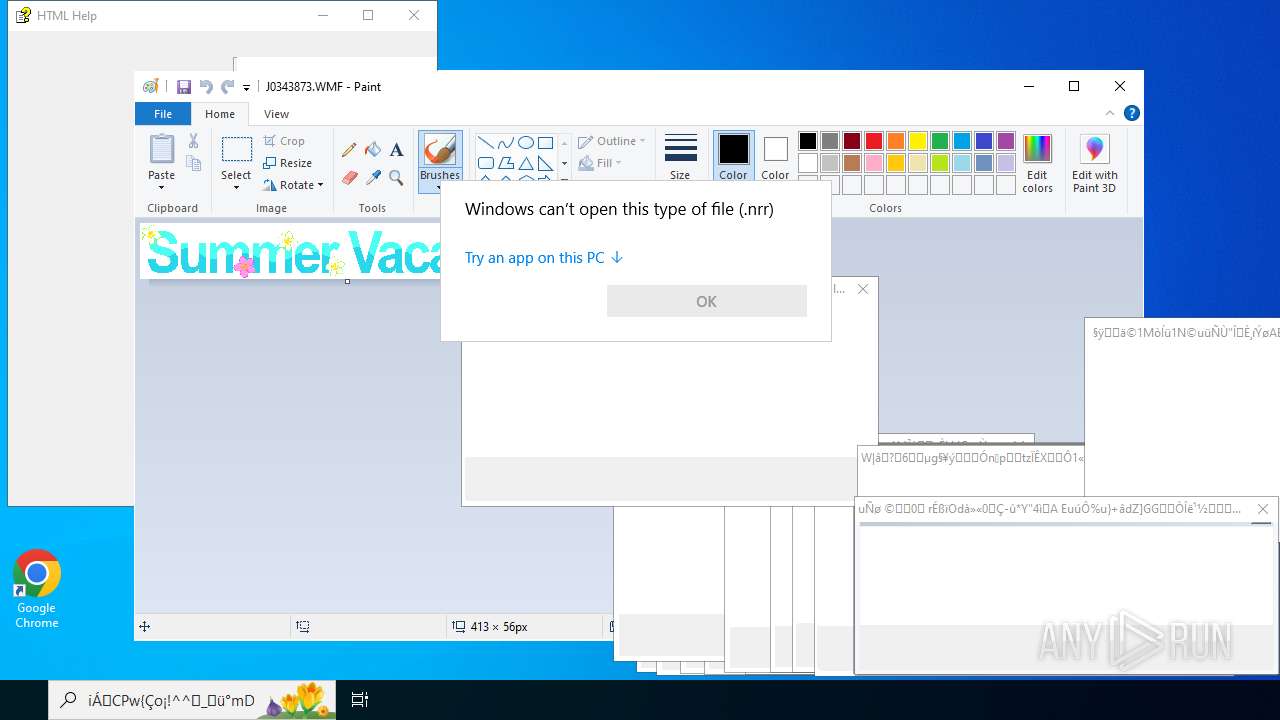
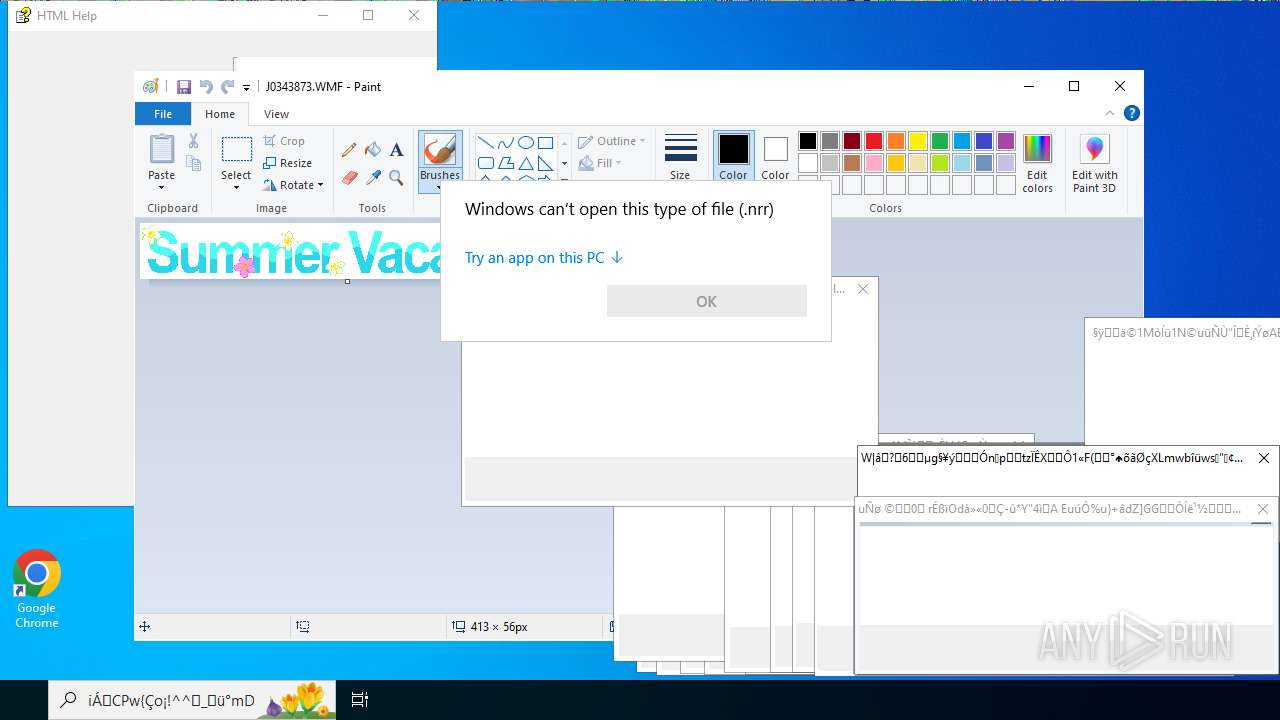
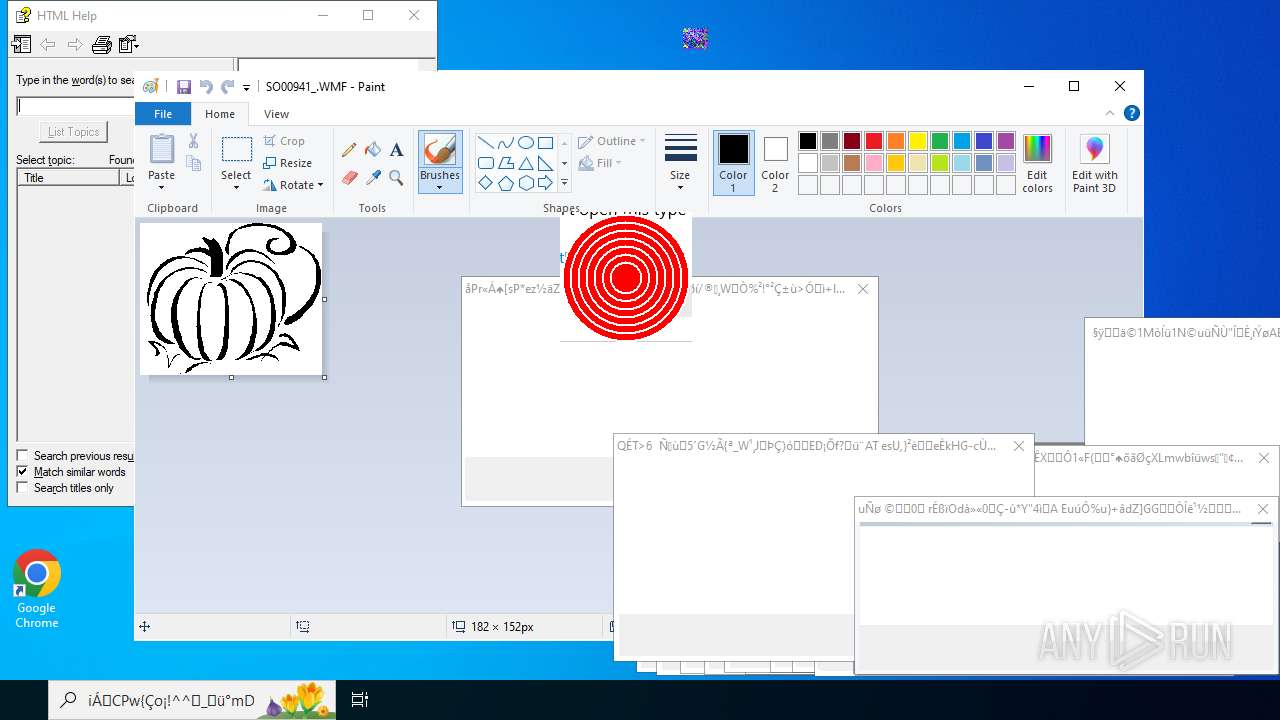
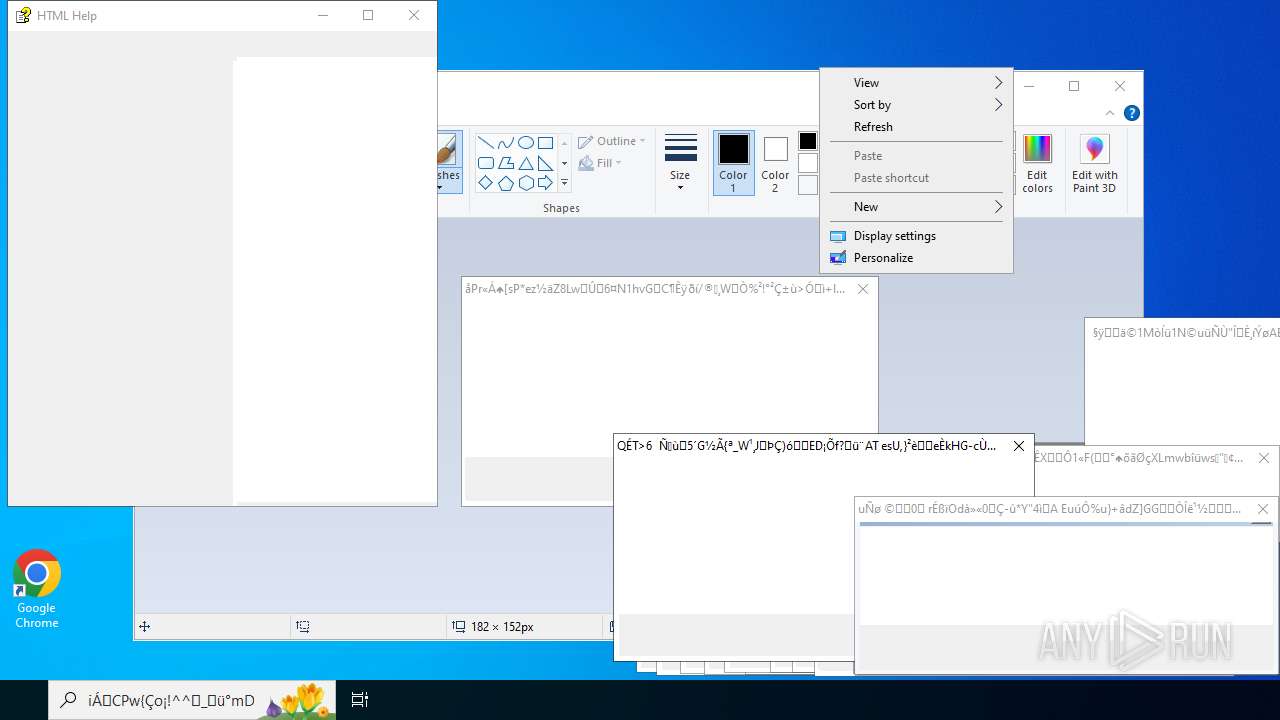
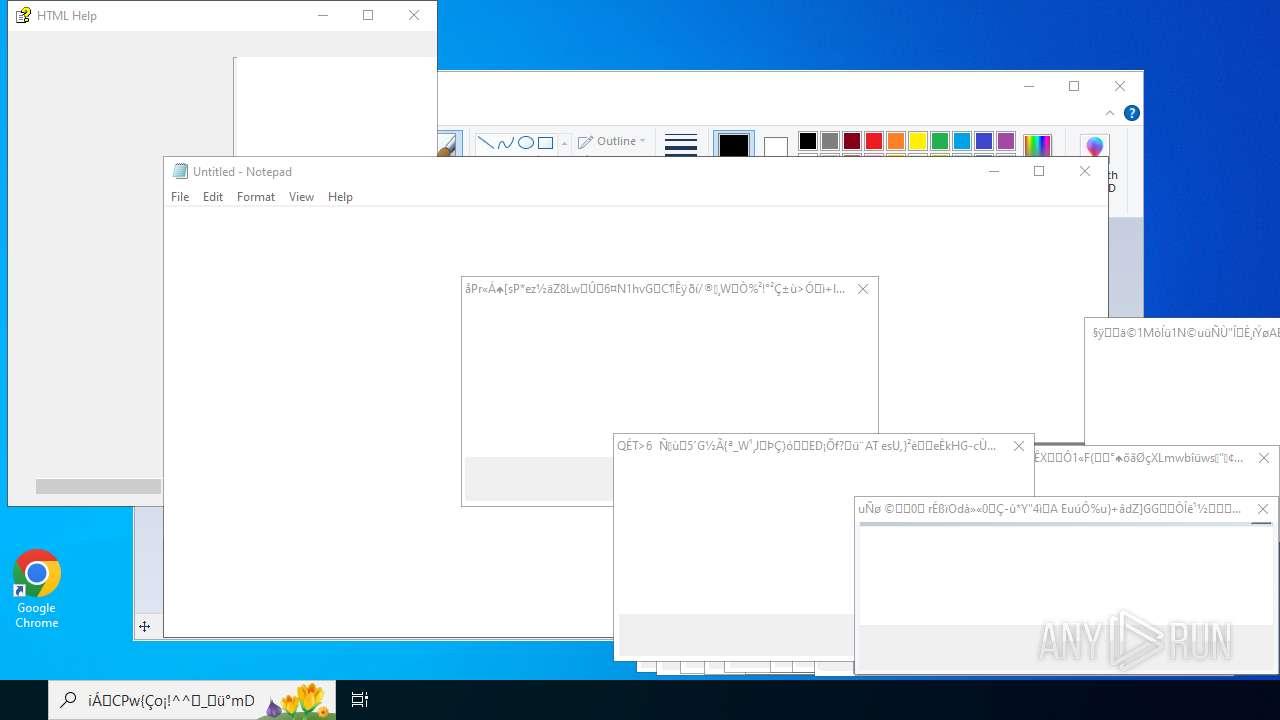
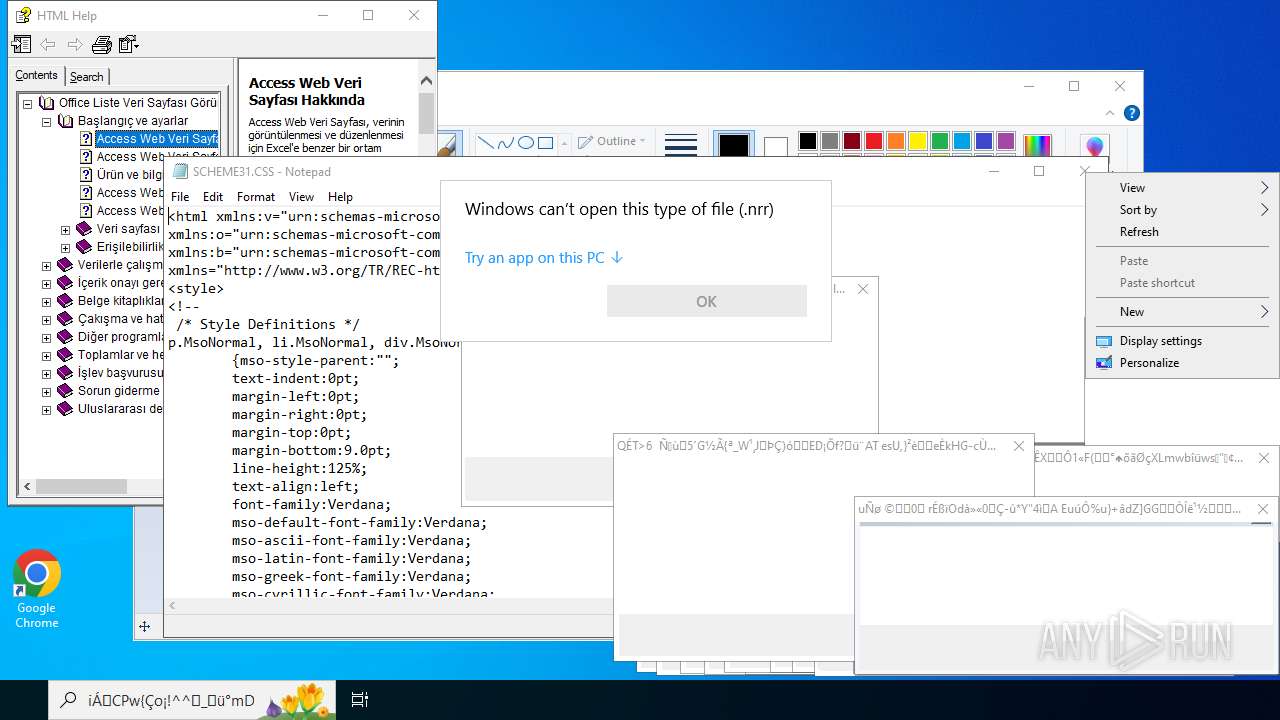
Start notepad (likely ransomware note)
- 萩鬊搙鐌骜龾丿翘瑟躍憌澬毕圍暼苤.exe (PID: 4456)
Checks for Java to be installed
- java.exe (PID: 11736)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 4700)
Application launched itself
- msiexec.exe (PID: 4700)
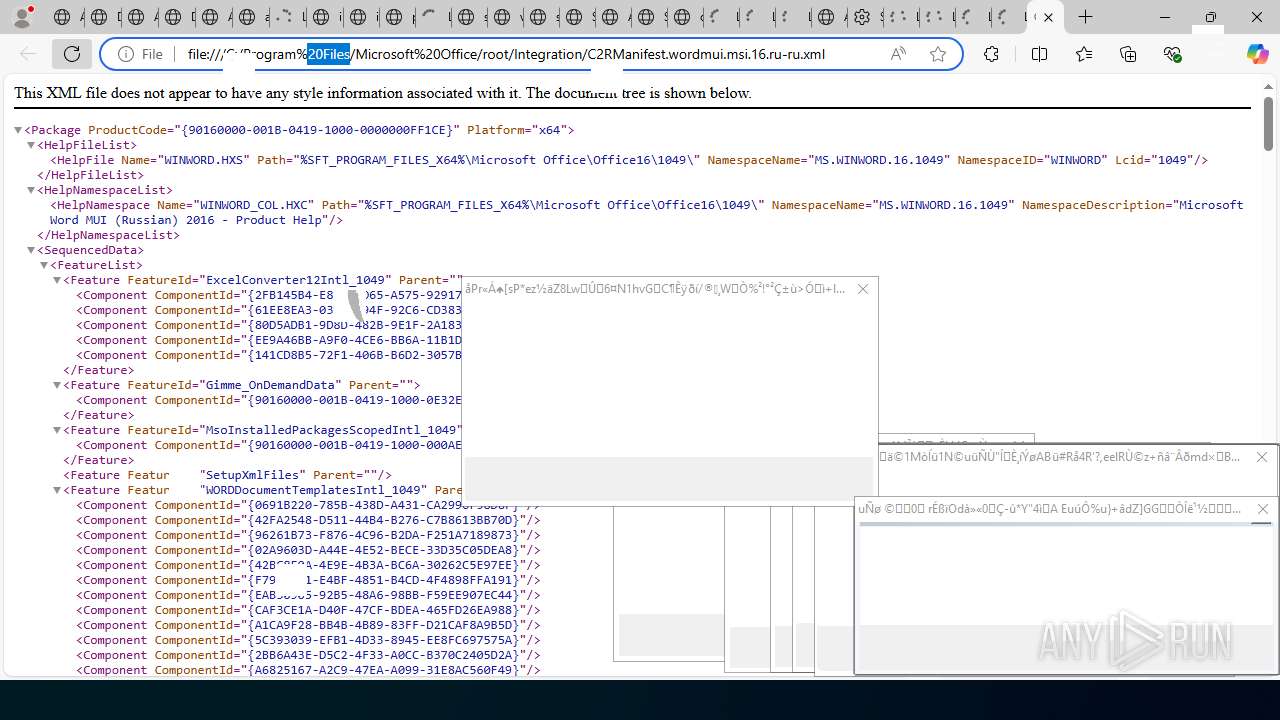
Process drops legitimate windows executable
- msiexec.exe (PID: 4700)
Reads Internet Explorer settings
- hh.exe (PID: 3656)
- hh.exe (PID: 15048)
- hh.exe (PID: 14692)
- hh.exe (PID: 8020)
Reads Microsoft Outlook installation path
- hh.exe (PID: 3656)
- hh.exe (PID: 15048)
- hh.exe (PID: 14692)
- hh.exe (PID: 8020)
Executes application which crashes
- 萩鬊搙鐌骜龾丿翘瑟躍憌澬毕圍暼苤.exe (PID: 4456)
INFO
Create files in a temporary directory
- Monoxidex86.exe (PID: 7032)
- hh.exe (PID: 3656)
- hh.exe (PID: 14692)
- hh.exe (PID: 15048)
- hh.exe (PID: 8020)
Reads the computer name
- 萩鬊搙鐌骜龾丿翘瑟躍憌澬毕圍暼苤.exe (PID: 4456)
- InspectorOfficeGadget.exe (PID: 11360)
- identity_helper.exe (PID: 11292)
- elevation_service.exe (PID: 8280)
- msiexec.exe (PID: 4700)
- msiexec.exe (PID: 8104)
- msiexec.exe (PID: 9432)
- identity_helper.exe (PID: 14276)
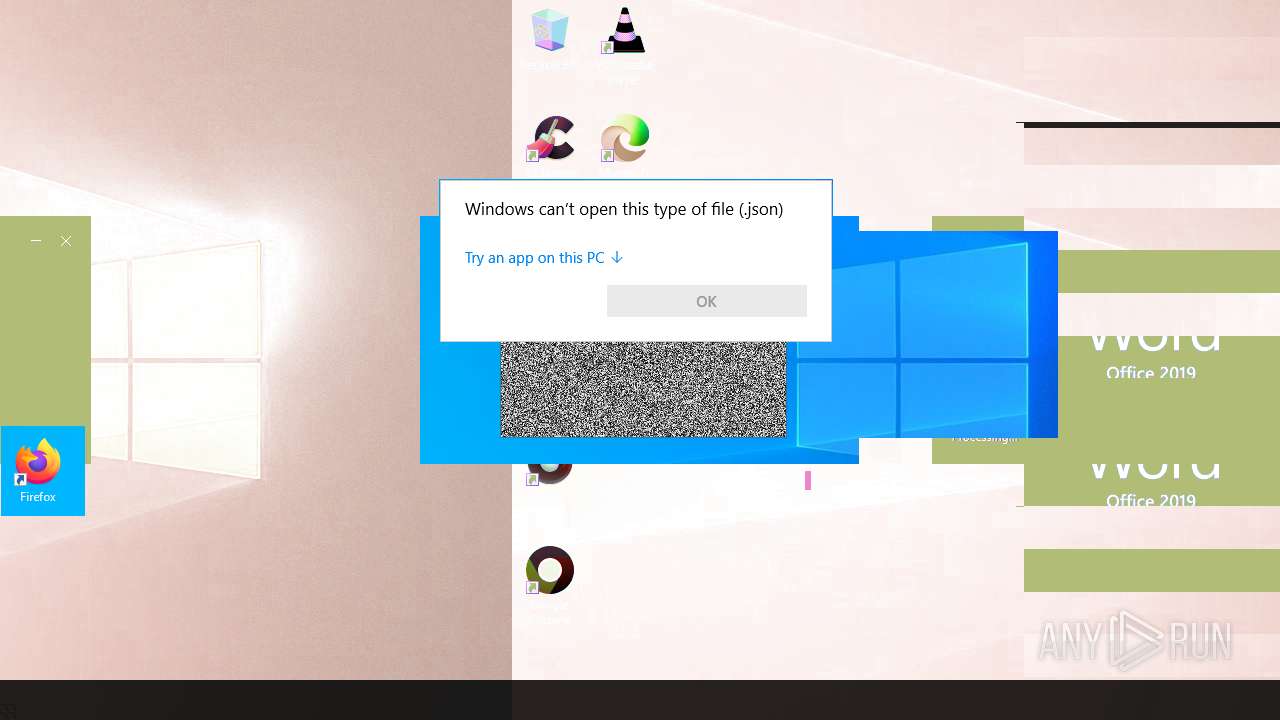
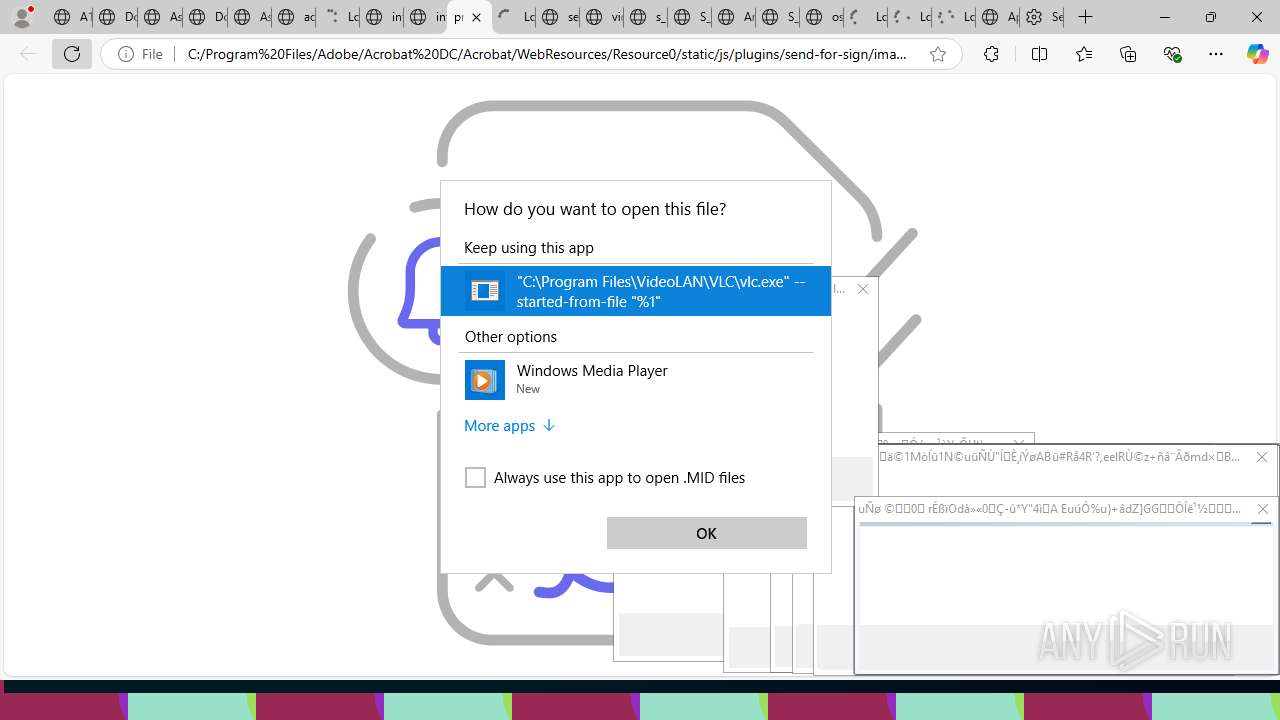
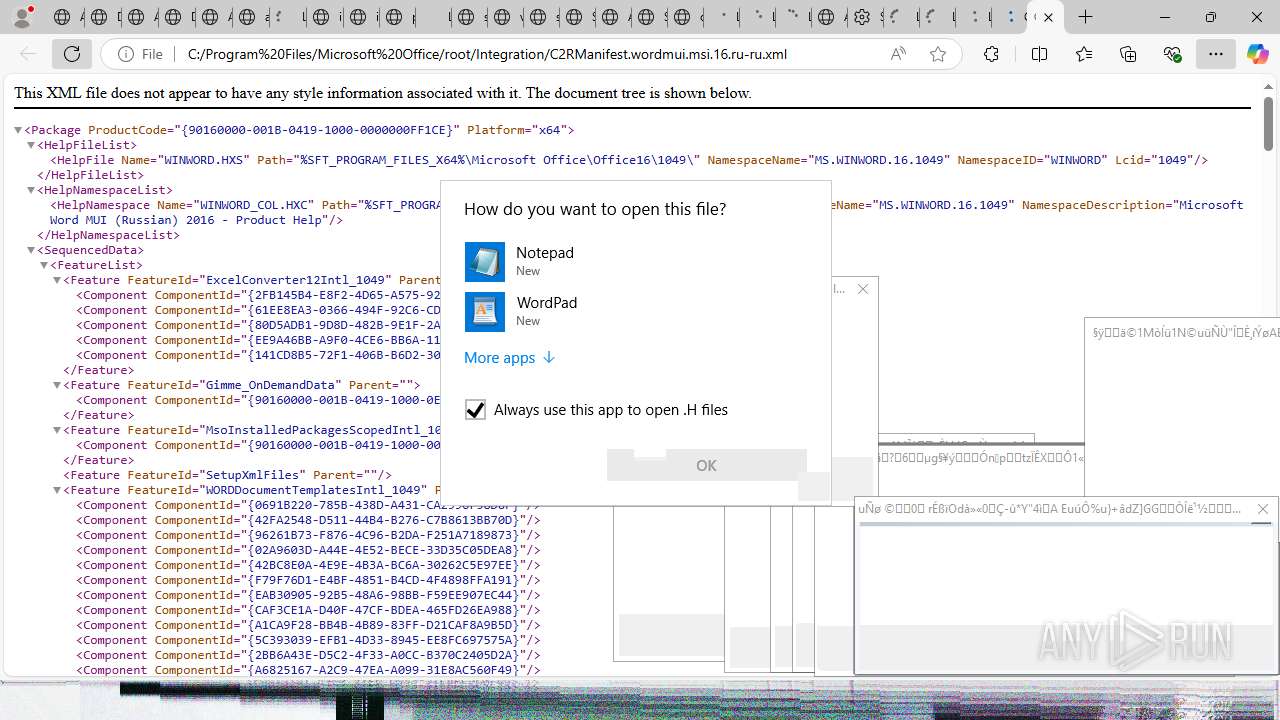
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 7124)
- OpenWith.exe (PID: 5552)
- OpenWith.exe (PID: 304)
- OpenWith.exe (PID: 7020)
- OpenWith.exe (PID: 5456)
- OpenWith.exe (PID: 3580)
- OpenWith.exe (PID: 9760)
- OpenWith.exe (PID: 7292)
- OpenWith.exe (PID: 11604)
- OpenWith.exe (PID: 11784)
- OpenWith.exe (PID: 11876)
- OpenWith.exe (PID: 11984)
- OpenWith.exe (PID: 12248)
- OpenWith.exe (PID: 12056)
- OpenWith.exe (PID: 12112)
- OpenWith.exe (PID: 11472)
- OpenWith.exe (PID: 7292)
- OpenWith.exe (PID: 11904)
- OpenWith.exe (PID: 2992)
- OpenWith.exe (PID: 12040)
- OpenWith.exe (PID: 8040)
- OpenWith.exe (PID: 3880)
- OpenWith.exe (PID: 6348)
- OpenWith.exe (PID: 9148)
- OpenWith.exe (PID: 12248)
- OpenWith.exe (PID: 12004)
- OpenWith.exe (PID: 1948)
- OpenWith.exe (PID: 11808)
- OpenWith.exe (PID: 8028)
- OpenWith.exe (PID: 12140)
- OpenWith.exe (PID: 12452)
- OpenWith.exe (PID: 12128)
- OpenWith.exe (PID: 11404)
- OpenWith.exe (PID: 11064)
- OpenWith.exe (PID: 13376)
- OpenWith.exe (PID: 14636)
- OpenWith.exe (PID: 15080)
- OpenWith.exe (PID: 14216)
- OpenWith.exe (PID: 14680)
- OpenWith.exe (PID: 9568)
- OpenWith.exe (PID: 15232)
- OpenWith.exe (PID: 13608)
- OpenWith.exe (PID: 9392)
- OpenWith.exe (PID: 14560)
- OpenWith.exe (PID: 3640)
- OpenWith.exe (PID: 8496)
- OpenWith.exe (PID: 14852)
- OpenWith.exe (PID: 11276)
- OpenWith.exe (PID: 8504)
- OpenWith.exe (PID: 8772)
- OpenWith.exe (PID: 9064)
- OpenWith.exe (PID: 9364)
- OpenWith.exe (PID: 10012)
- OpenWith.exe (PID: 10984)
- OpenWith.exe (PID: 5900)
- OpenWith.exe (PID: 11772)
- OpenWith.exe (PID: 10436)
- OpenWith.exe (PID: 12452)
- OpenWith.exe (PID: 2288)
- OpenWith.exe (PID: 13432)
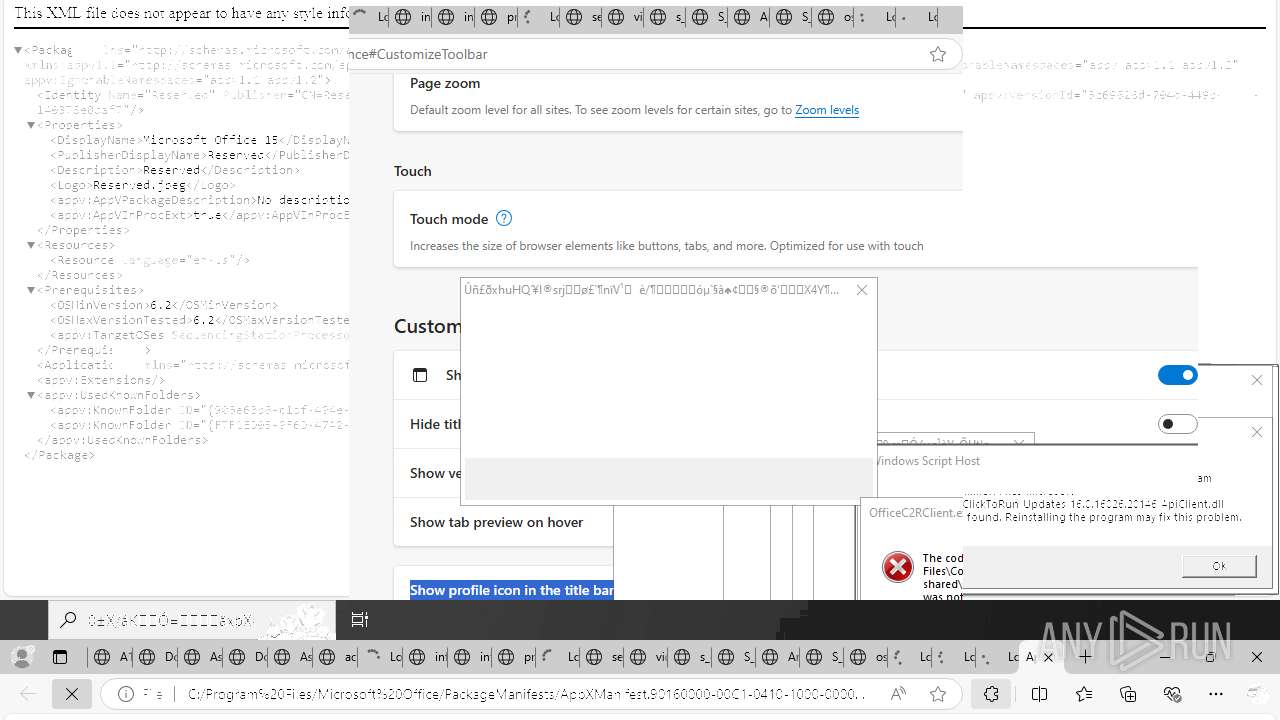
Application launched itself
- msedge.exe (PID: 620)
- msedge.exe (PID: 4576)
- msedge.exe (PID: 4320)
- msedge.exe (PID: 868)
- msedge.exe (PID: 6016)
- msedge.exe (PID: 6332)
- msedge.exe (PID: 440)
- msedge.exe (PID: 304)
- msedge.exe (PID: 4120)
- msedge.exe (PID: 3852)
- msedge.exe (PID: 6240)
- msedge.exe (PID: 2692)
- msedge.exe (PID: 864)
- msedge.exe (PID: 7956)
- msedge.exe (PID: 7972)
- msedge.exe (PID: 8300)
- msedge.exe (PID: 8388)
- msedge.exe (PID: 8336)
- msedge.exe (PID: 7492)
- msedge.exe (PID: 432)
- msedge.exe (PID: 9272)
- msedge.exe (PID: 9956)
- msedge.exe (PID: 10020)
- msedge.exe (PID: 2276)
- msedge.exe (PID: 9940)
- msedge.exe (PID: 9660)
- msedge.exe (PID: 9376)
- msedge.exe (PID: 10352)
- msedge.exe (PID: 10376)
- msedge.exe (PID: 11144)
- msedge.exe (PID: 10936)
- msedge.exe (PID: 6732)
- msedge.exe (PID: 10376)
- msedge.exe (PID: 10000)
- msedge.exe (PID: 9784)
- msedge.exe (PID: 11524)
- msedge.exe (PID: 11904)
- msedge.exe (PID: 12256)
- msedge.exe (PID: 8316)
- msedge.exe (PID: 4120)
- msedge.exe (PID: 13996)
- msedge.exe (PID: 14260)
- msedge.exe (PID: 14076)
- msedge.exe (PID: 14112)
- msedge.exe (PID: 14184)
- msedge.exe (PID: 14460)
- msedge.exe (PID: 7496)
- msedge.exe (PID: 5400)
- msedge.exe (PID: 14876)
Process checks computer location settings
- 萩鬊搙鐌骜龾丿翘瑟躍憌澬毕圍暼苤.exe (PID: 4456)
Checks supported languages
- Monoxidex86.exe (PID: 7032)
- 萩鬊搙鐌骜龾丿翘瑟躍憌澬毕圍暼苤.exe (PID: 4456)
- InspectorOfficeGadget.exe (PID: 11360)
- elevation_service.exe (PID: 8280)
- java.exe (PID: 11736)
- identity_helper.exe (PID: 11292)
- msiexec.exe (PID: 4700)
- msiexec.exe (PID: 9432)
- msiexec.exe (PID: 8104)
- identity_helper.exe (PID: 14276)
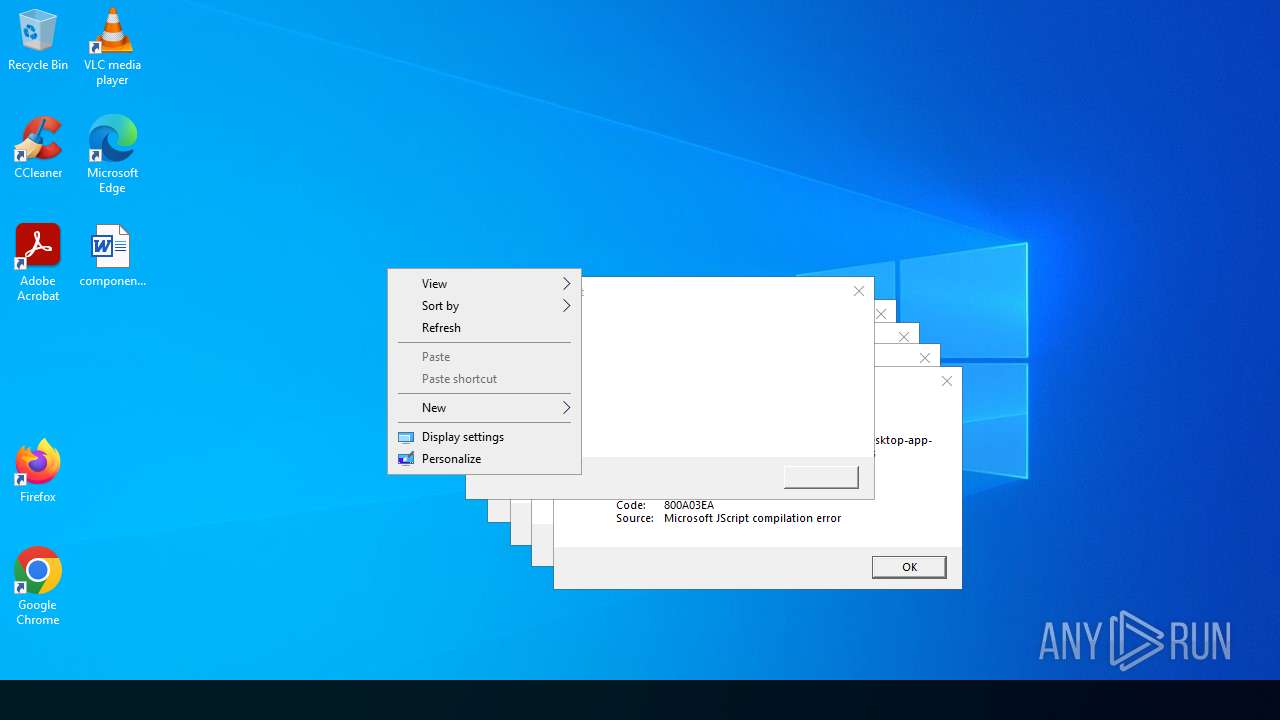
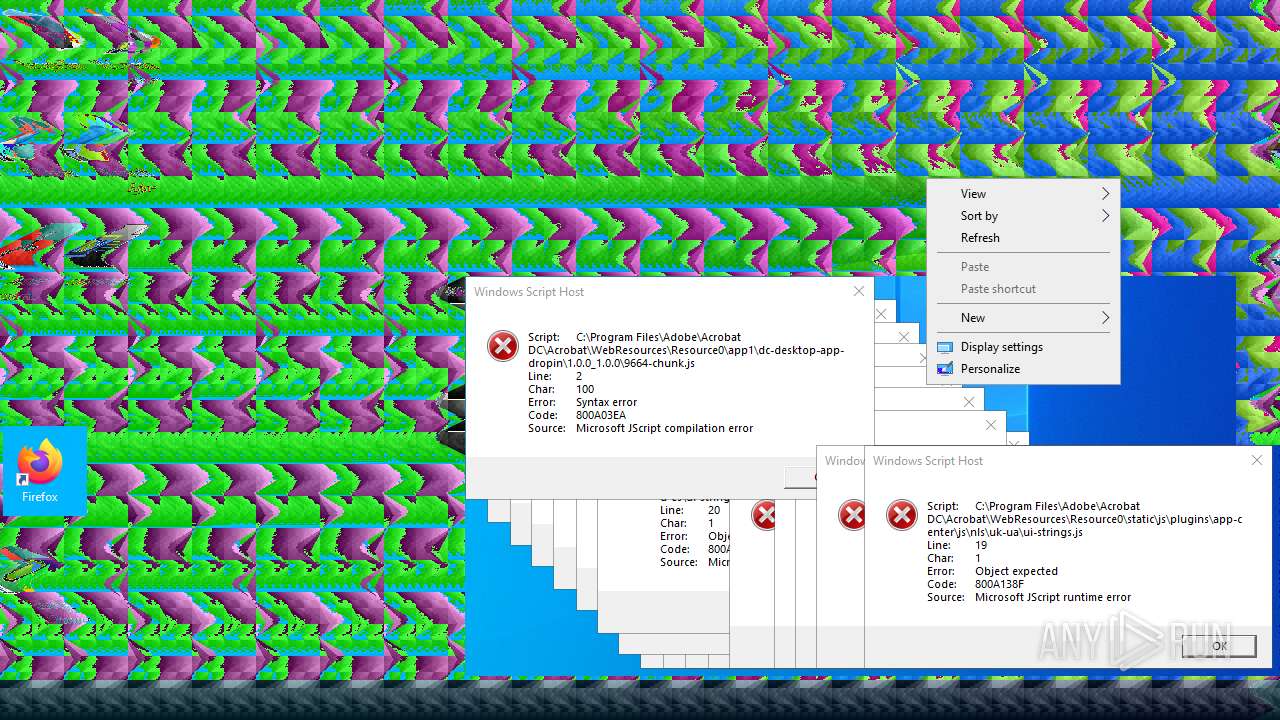
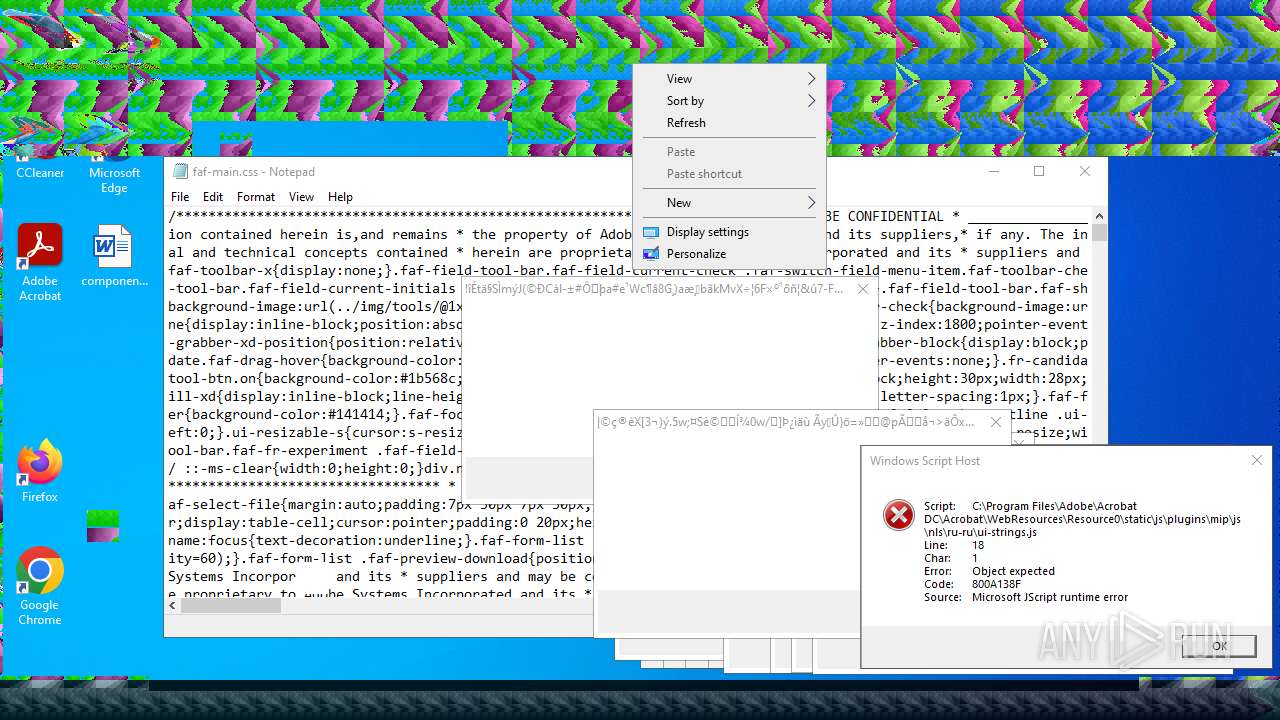
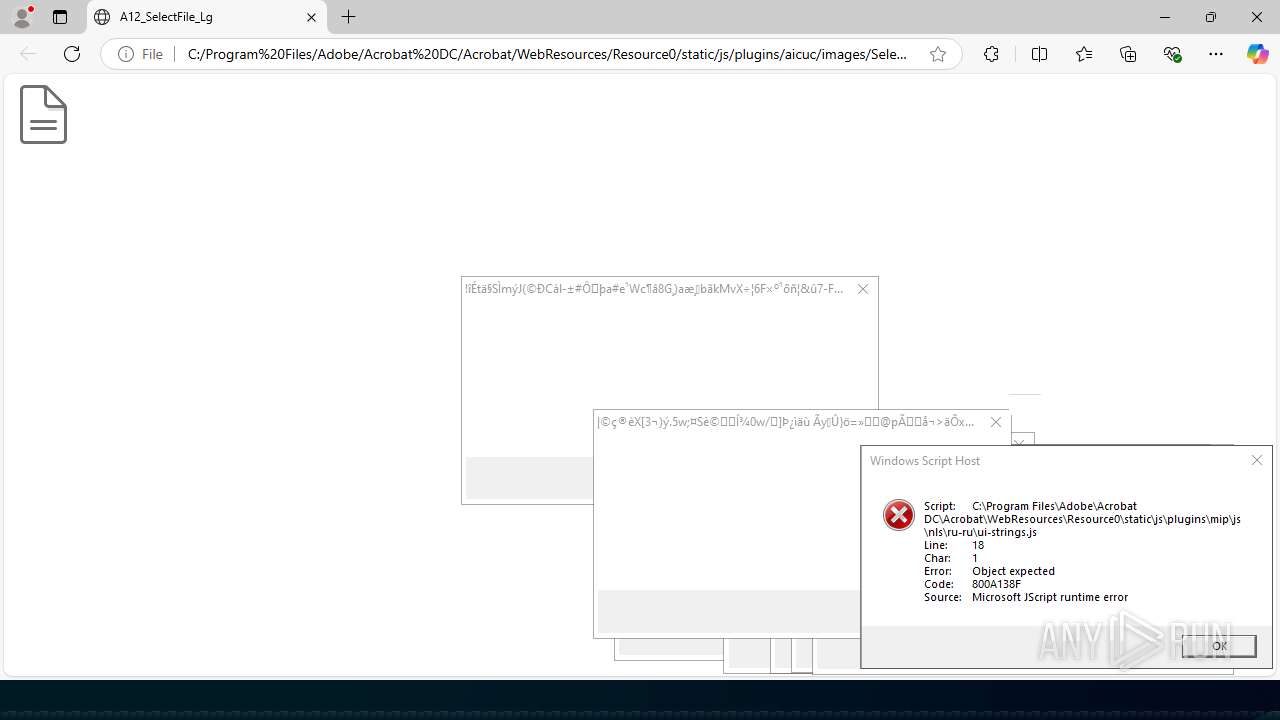
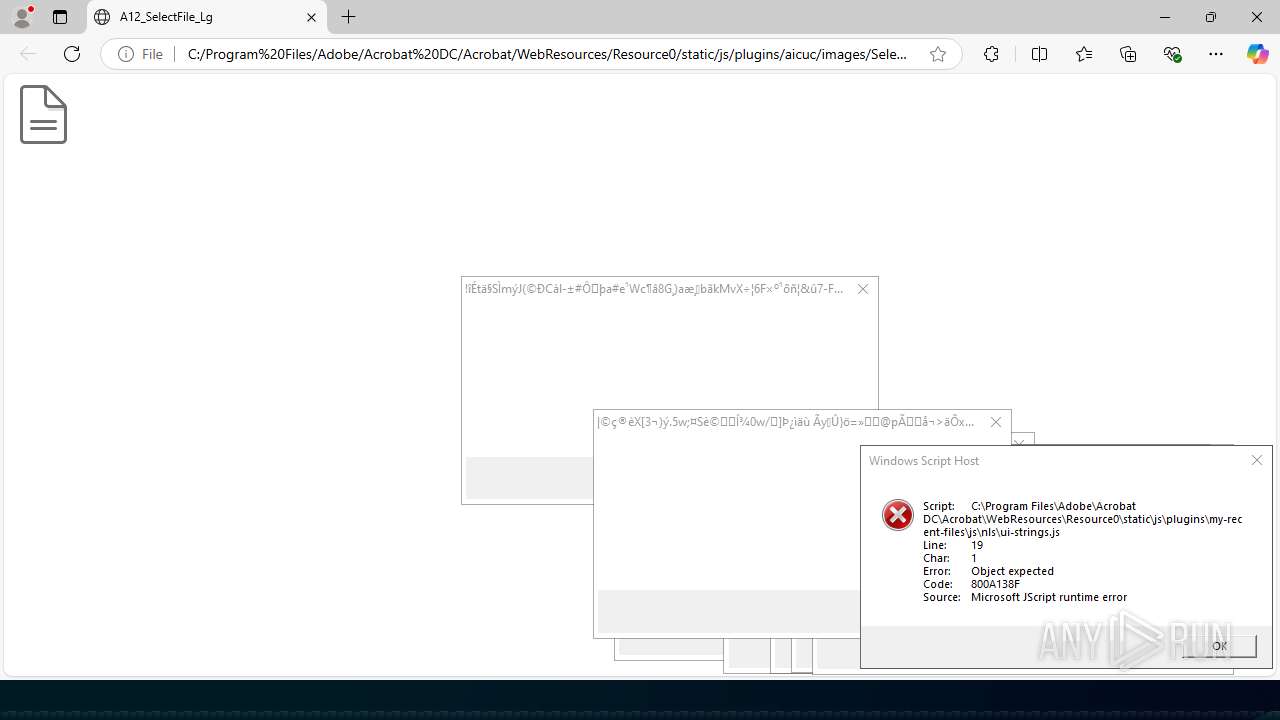
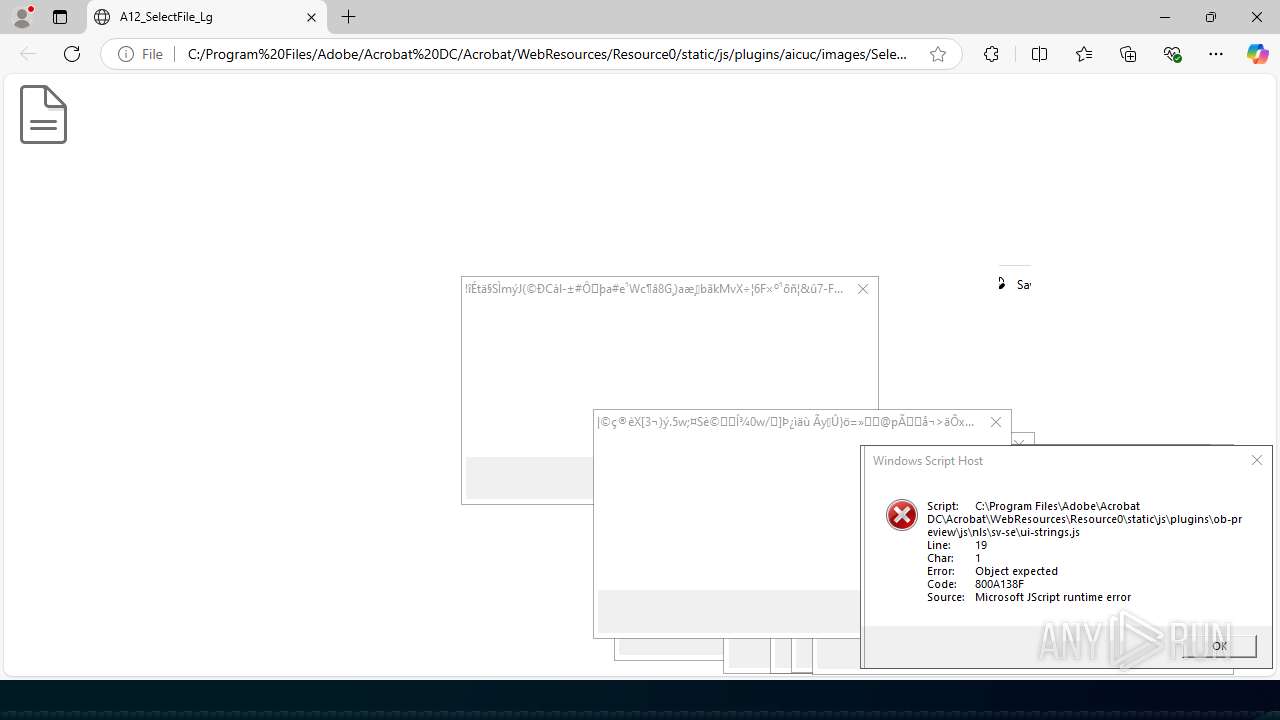
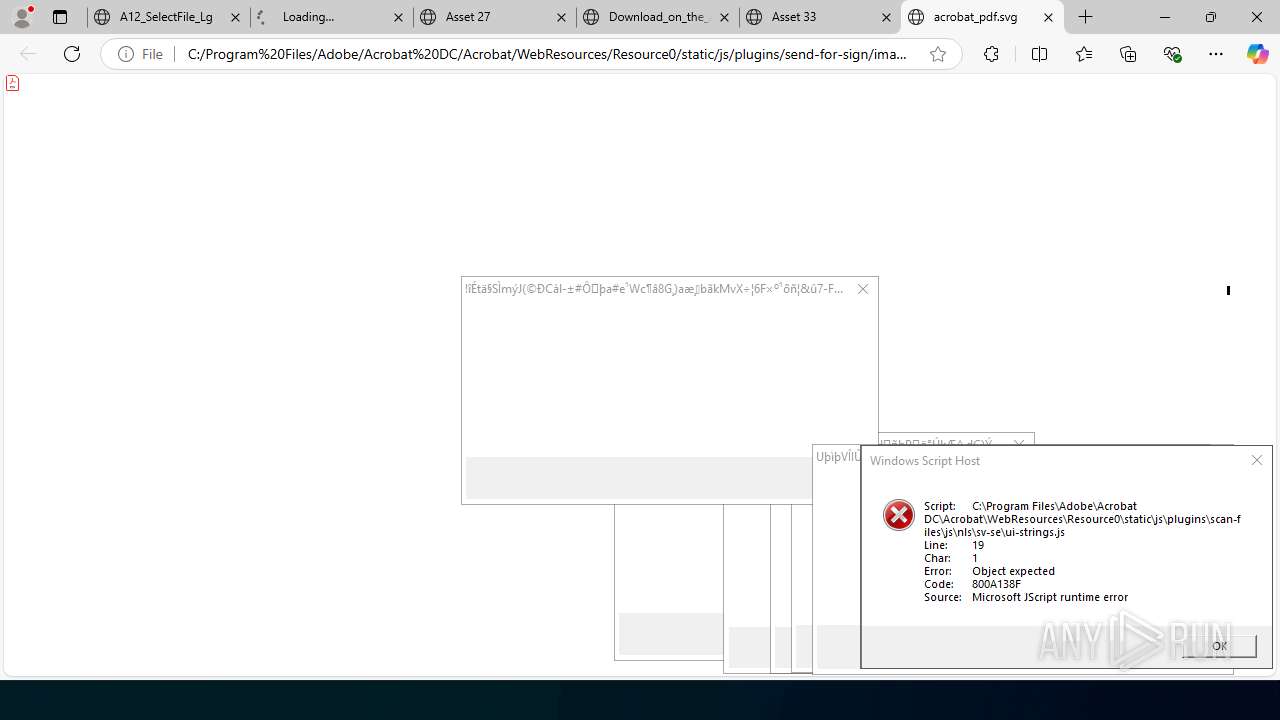
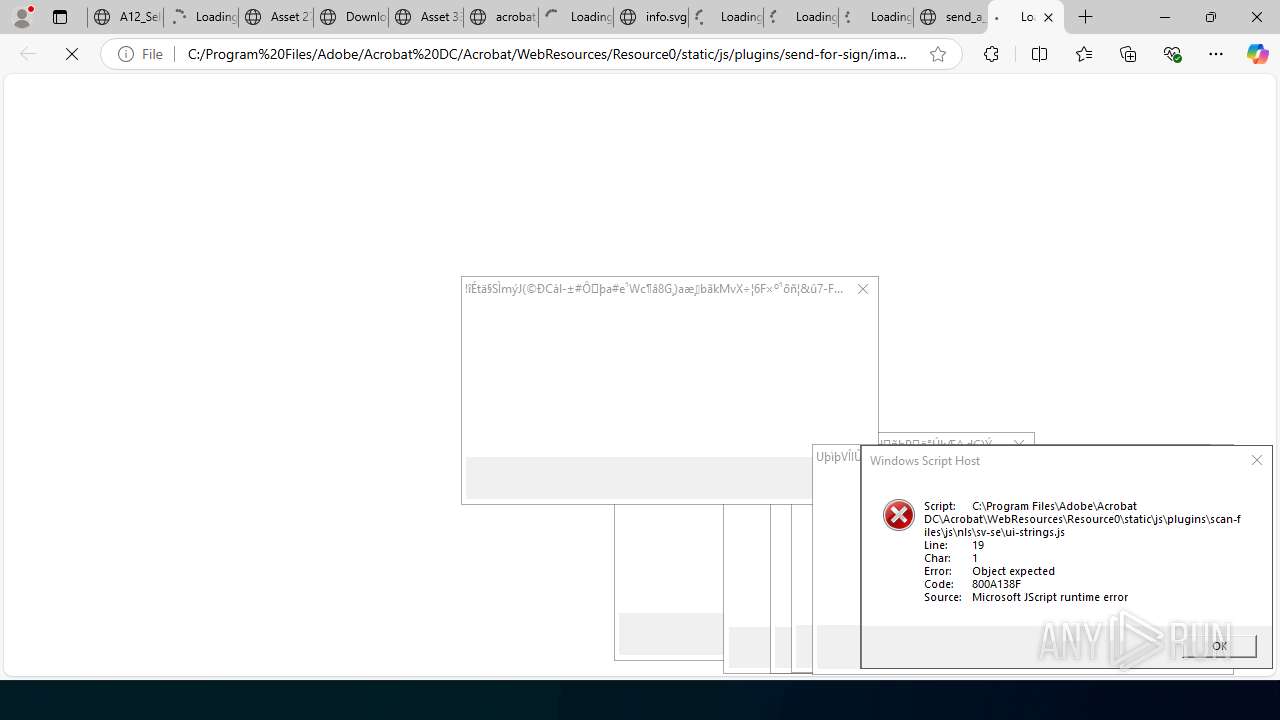
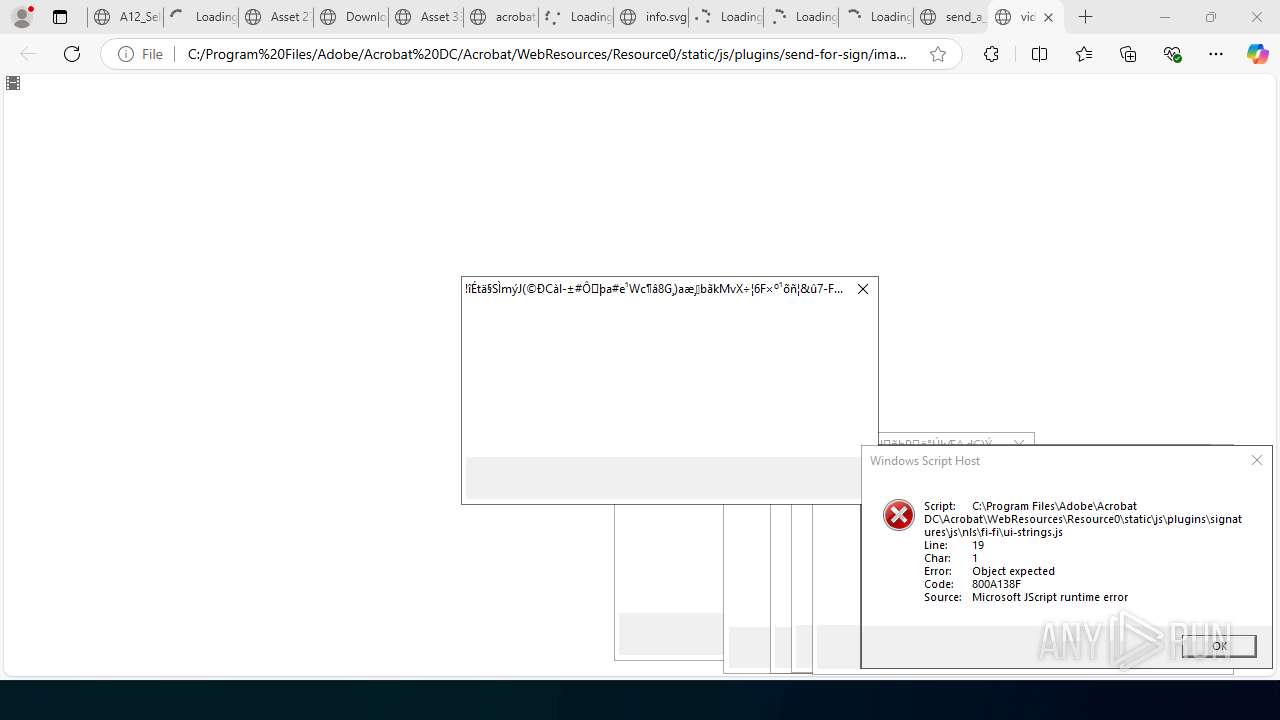
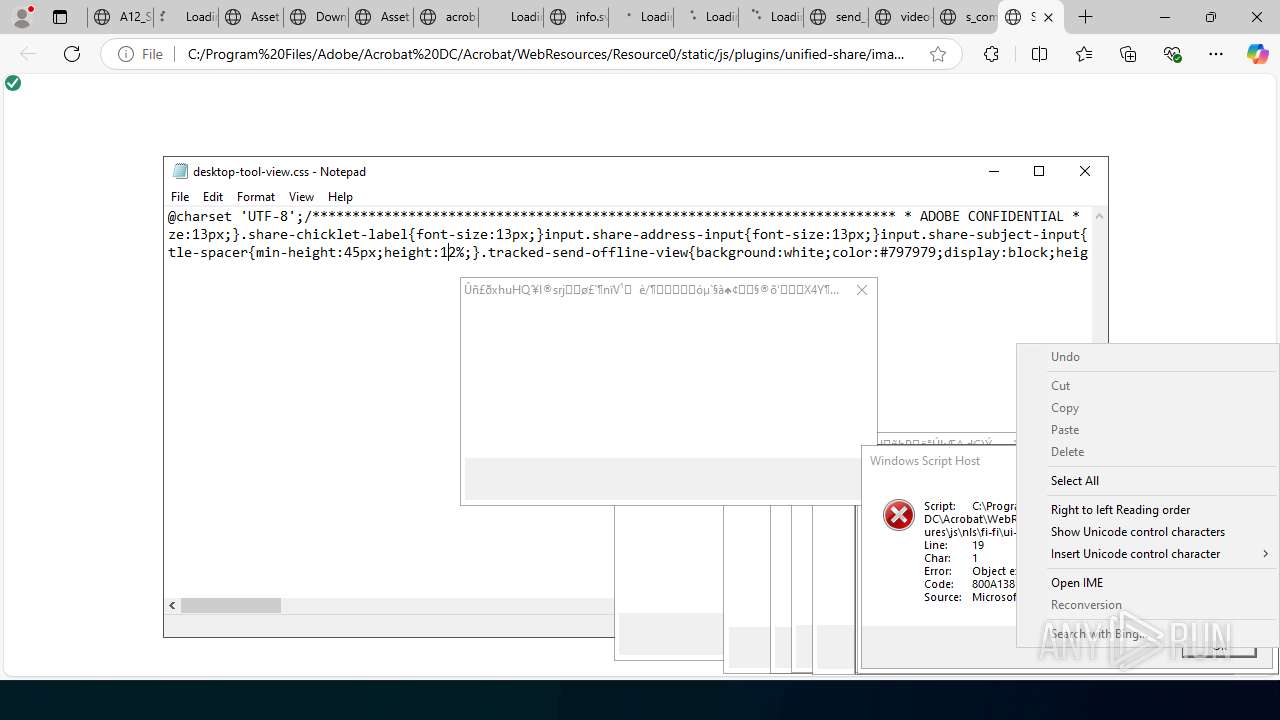
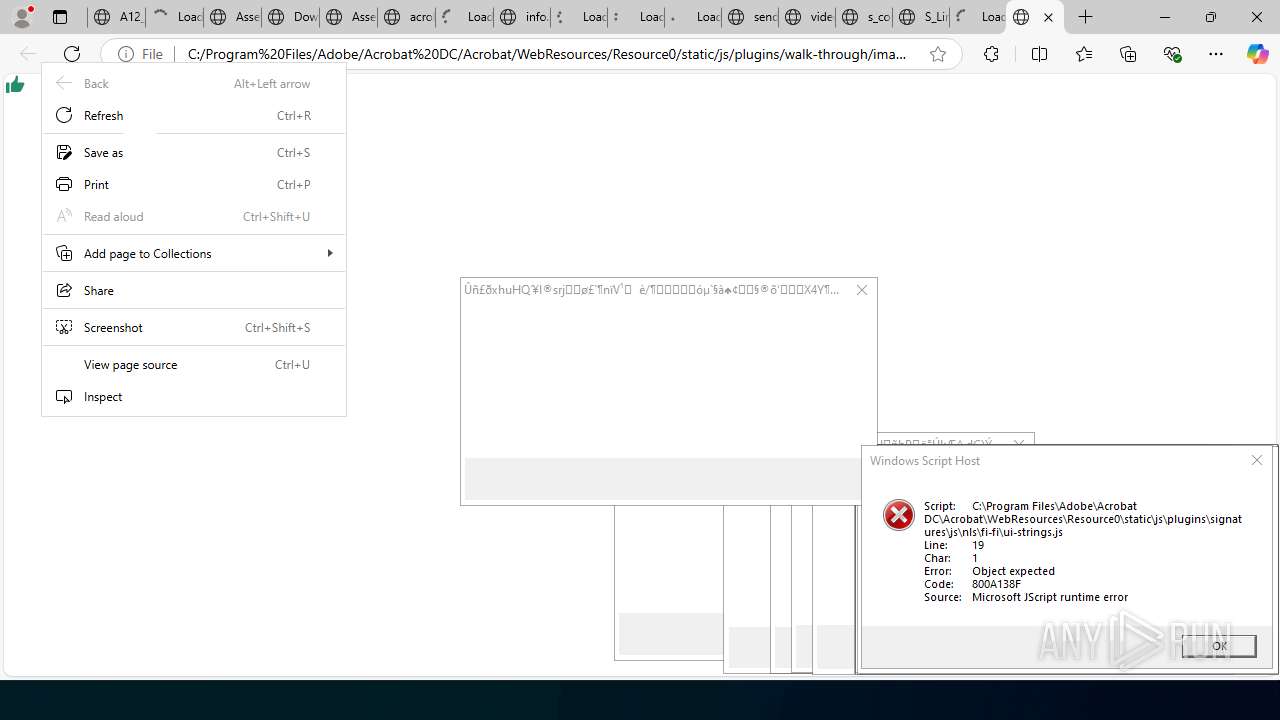
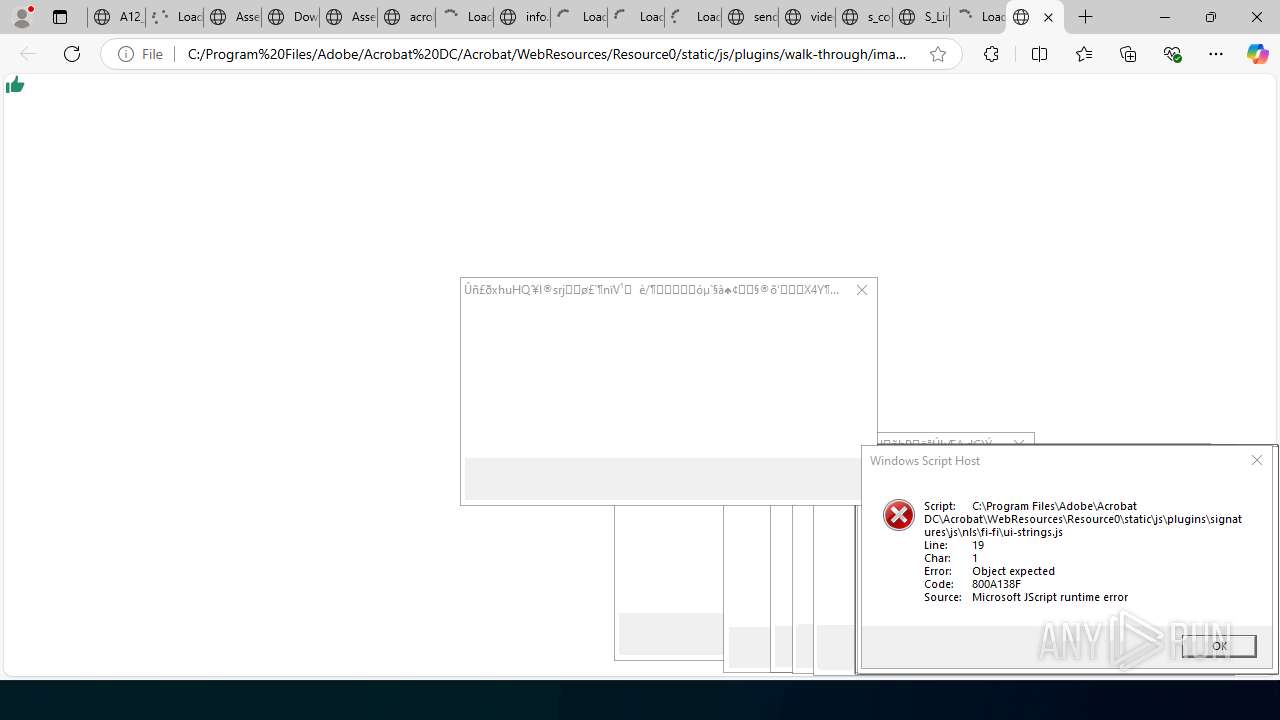
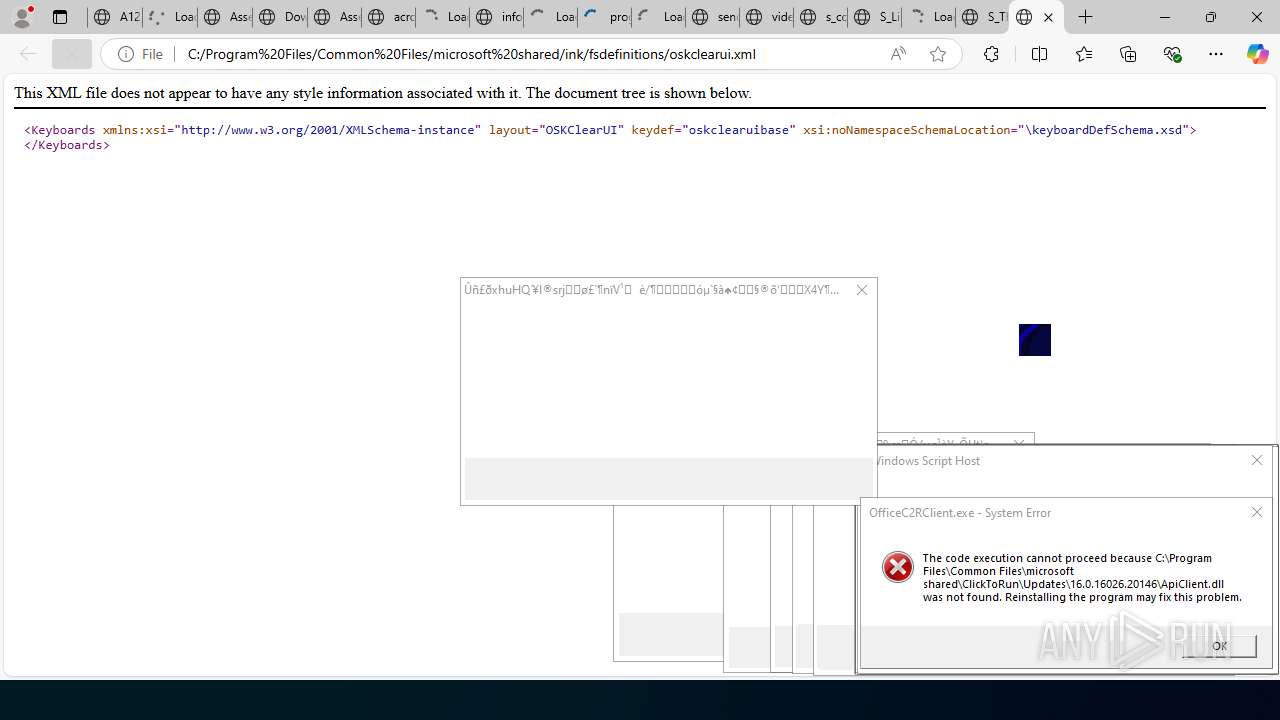
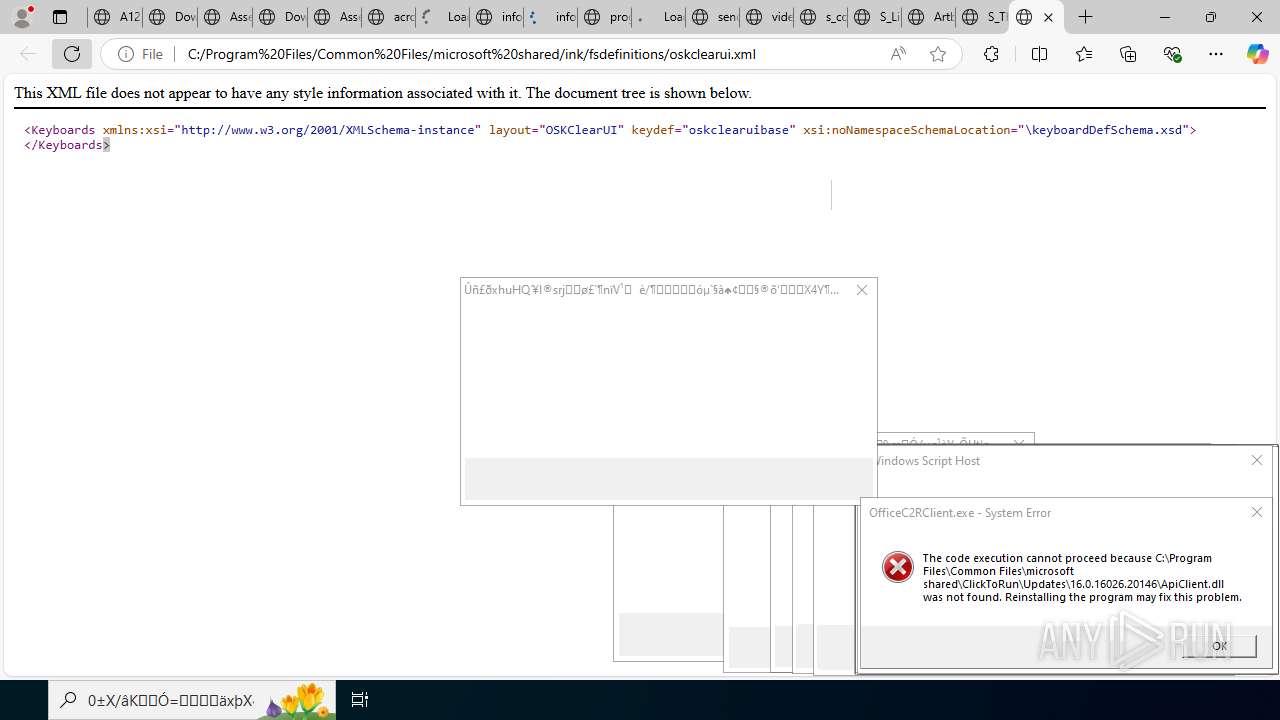
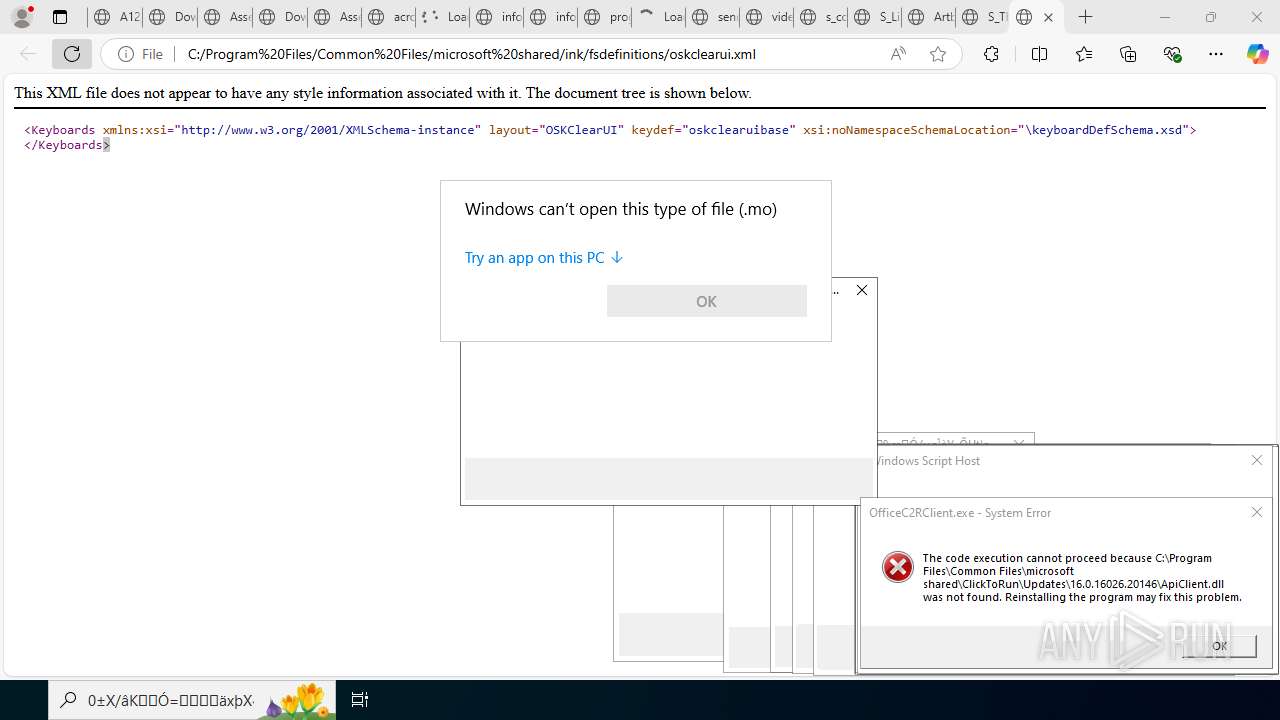
JScript runtime error (SCRIPT)
- wscript.exe (PID: 6036)
- wscript.exe (PID: 1324)
- wscript.exe (PID: 7192)
- wscript.exe (PID: 7624)
- wscript.exe (PID: 7596)
- wscript.exe (PID: 7752)
- wscript.exe (PID: 7516)
- wscript.exe (PID: 7780)
- wscript.exe (PID: 7892)
- wscript.exe (PID: 7700)
- wscript.exe (PID: 3788)
- wscript.exe (PID: 8088)
- wscript.exe (PID: 7860)
- wscript.exe (PID: 7528)
- wscript.exe (PID: 1800)
- wscript.exe (PID: 3844)
- wscript.exe (PID: 7696)
- wscript.exe (PID: 7364)
- wscript.exe (PID: 7348)
- wscript.exe (PID: 6240)
- wscript.exe (PID: 3688)
- wscript.exe (PID: 1136)
- wscript.exe (PID: 6876)
- wscript.exe (PID: 7724)
- wscript.exe (PID: 7980)
- wscript.exe (PID: 8212)
- wscript.exe (PID: 8444)
- wscript.exe (PID: 8236)
- wscript.exe (PID: 8520)
- wscript.exe (PID: 8636)
- wscript.exe (PID: 8980)
- wscript.exe (PID: 7212)
- wscript.exe (PID: 8836)
- wscript.exe (PID: 8304)
- wscript.exe (PID: 8100)
- wscript.exe (PID: 8164)
- wscript.exe (PID: 8180)
- wscript.exe (PID: 8188)
- wscript.exe (PID: 9664)
- wscript.exe (PID: 8400)
- wscript.exe (PID: 9536)
- wscript.exe (PID: 9728)
- wscript.exe (PID: 9608)
- wscript.exe (PID: 9688)
- wscript.exe (PID: 9384)
- wscript.exe (PID: 10220)
- wscript.exe (PID: 9296)
- wscript.exe (PID: 3972)
- wscript.exe (PID: 10880)
- wscript.exe (PID: 10964)
- wscript.exe (PID: 11216)
- wscript.exe (PID: 10796)
- wscript.exe (PID: 11068)
- wscript.exe (PID: 10560)
- wscript.exe (PID: 10716)
- wscript.exe (PID: 10680)
- wscript.exe (PID: 10484)
- wscript.exe (PID: 9856)
Manual execution by a user
- msedge.exe (PID: 7504)
- msedge.exe (PID: 7492)
- msedge.exe (PID: 14876)
Reads security settings of Internet Explorer
- notepad.exe (PID: 7688)
- notepad.exe (PID: 4664)
- notepad.exe (PID: 9920)
- notepad.exe (PID: 10844)
- notepad.exe (PID: 10888)
- notepad.exe (PID: 10380)
- notepad.exe (PID: 10420)
- notepad.exe (PID: 11236)
- notepad.exe (PID: 5684)
- notepad.exe (PID: 10352)
- notepad.exe (PID: 10184)
- notepad.exe (PID: 7304)
- HelpPane.exe (PID: 14288)
- hh.exe (PID: 3656)
- notepad.exe (PID: 14616)
- notepad.exe (PID: 14520)
- notepad.exe (PID: 14548)
- notepad.exe (PID: 14956)
- notepad.exe (PID: 15140)
- notepad.exe (PID: 15252)
- notepad.exe (PID: 15208)
- notepad.exe (PID: 13812)
- notepad.exe (PID: 14484)
- notepad.exe (PID: 11568)
- notepad.exe (PID: 14300)
- notepad.exe (PID: 4512)
- notepad.exe (PID: 15012)
- hh.exe (PID: 15048)
- hh.exe (PID: 14692)
- notepad.exe (PID: 2228)
- notepad.exe (PID: 15332)
- notepad.exe (PID: 14376)
- notepad.exe (PID: 14072)
- notepad.exe (PID: 14348)
- notepad.exe (PID: 12332)
- notepad.exe (PID: 32)
- notepad.exe (PID: 8952)
- notepad.exe (PID: 15084)
- hh.exe (PID: 8020)
- notepad.exe (PID: 11560)
- notepad.exe (PID: 12512)
- notepad.exe (PID: 8232)
- notepad.exe (PID: 9044)
- notepad.exe (PID: 12024)
- notepad.exe (PID: 10132)
- notepad.exe (PID: 9200)
- notepad.exe (PID: 12616)
Reads the machine GUID from the registry
- InspectorOfficeGadget.exe (PID: 11360)
- msiexec.exe (PID: 4700)
- HelpPane.exe (PID: 14288)
Reads Environment values
- identity_helper.exe (PID: 11292)
- identity_helper.exe (PID: 14276)
Checks proxy server information
- slui.exe (PID: 5468)
- hh.exe (PID: 3656)
- hh.exe (PID: 15048)
- hh.exe (PID: 8020)
- hh.exe (PID: 14692)
Reads the software policy settings
- slui.exe (PID: 5468)
- msiexec.exe (PID: 4700)
- HelpPane.exe (PID: 14288)
Executable content was dropped or overwritten
- msiexec.exe (PID: 4700)
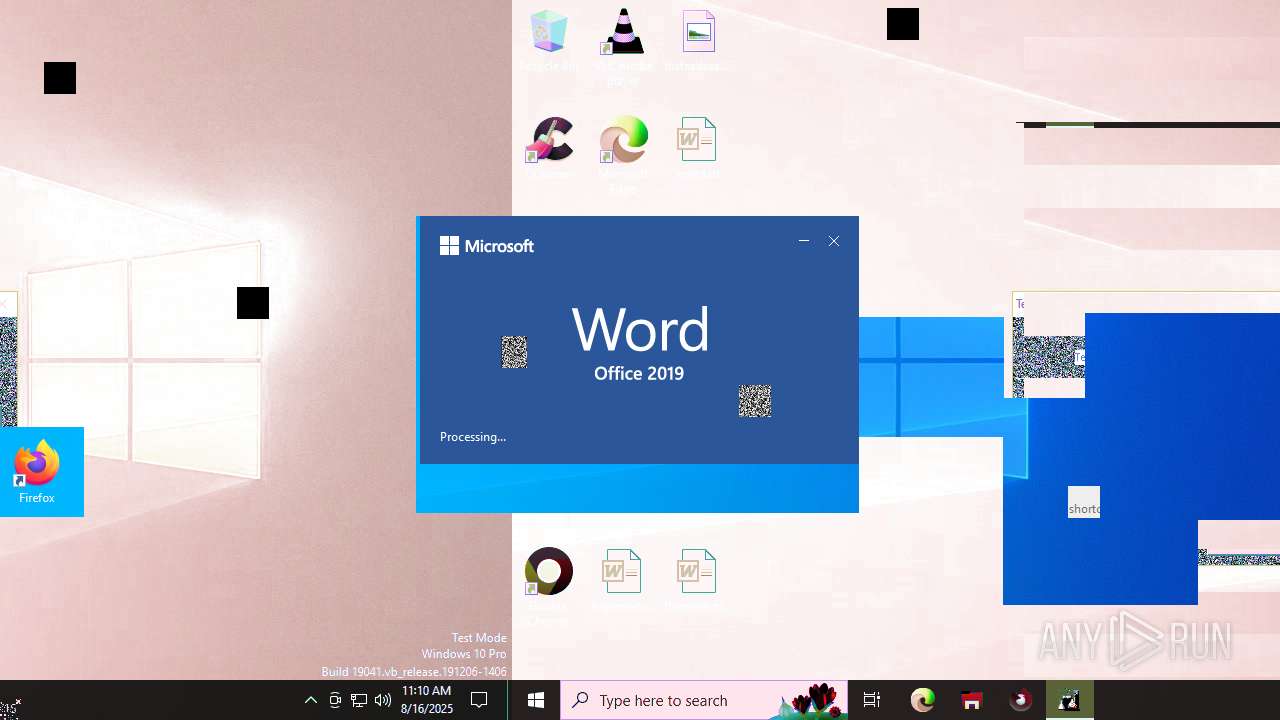
The sample compiled with french language support
- msiexec.exe (PID: 4700)
The sample compiled with english language support
- msiexec.exe (PID: 4700)
Creates a software uninstall entry
- msiexec.exe (PID: 4700)
Creates files or folders in the user directory
- hh.exe (PID: 3656)
- hh.exe (PID: 15048)
- hh.exe (PID: 8020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:06:09 12:22:35+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.29 |
| CodeSize: | 83456 |
| InitializedDataSize: | 232448 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7712 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
580
Monitored processes
426
Malicious processes
2
Suspicious processes
4
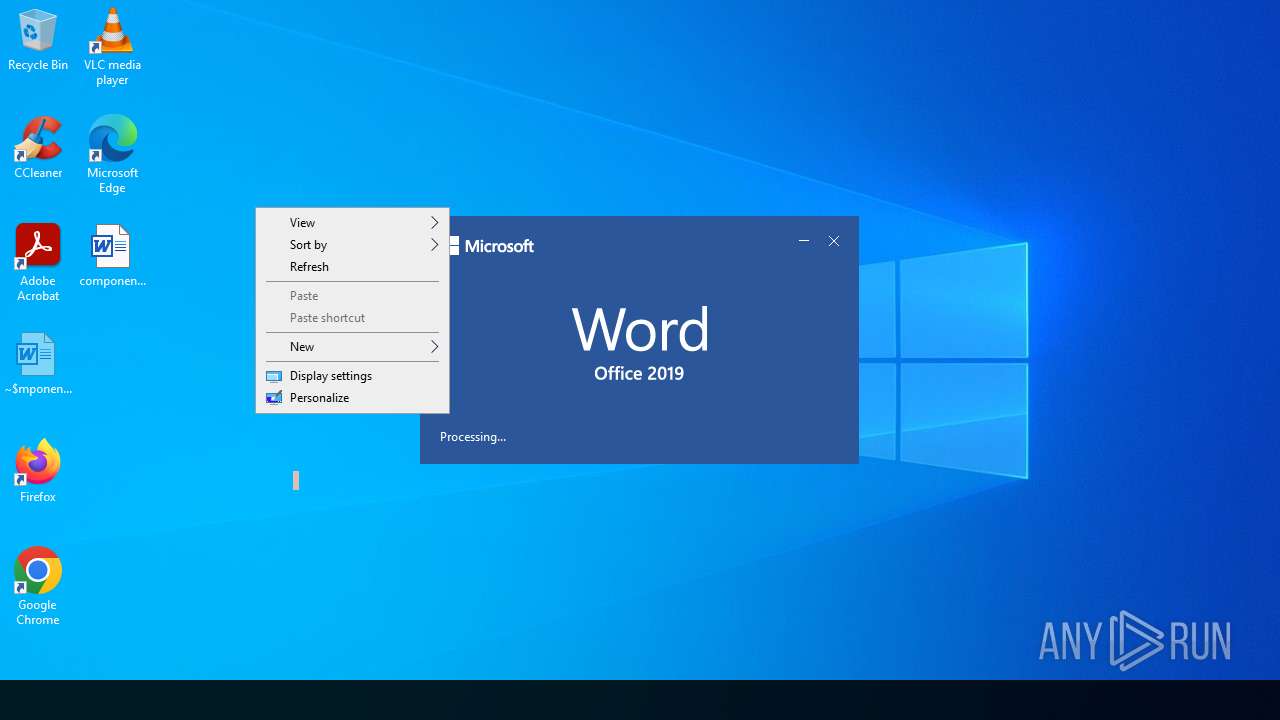
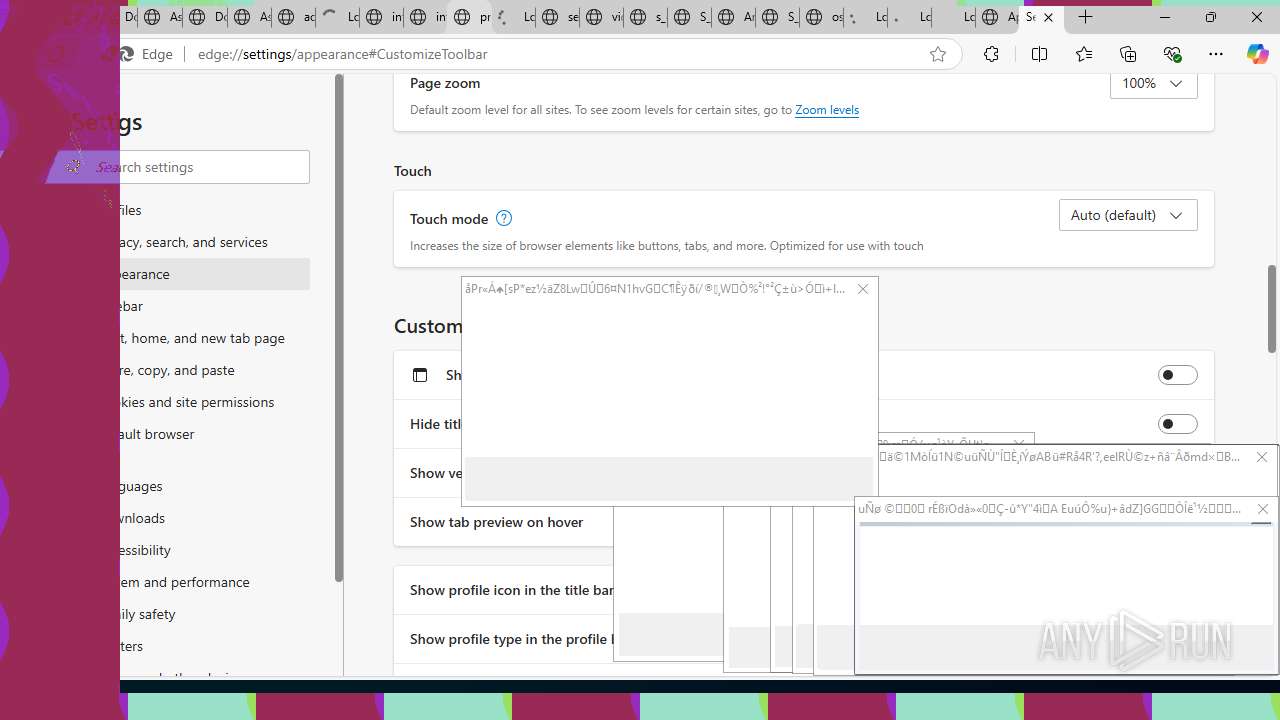
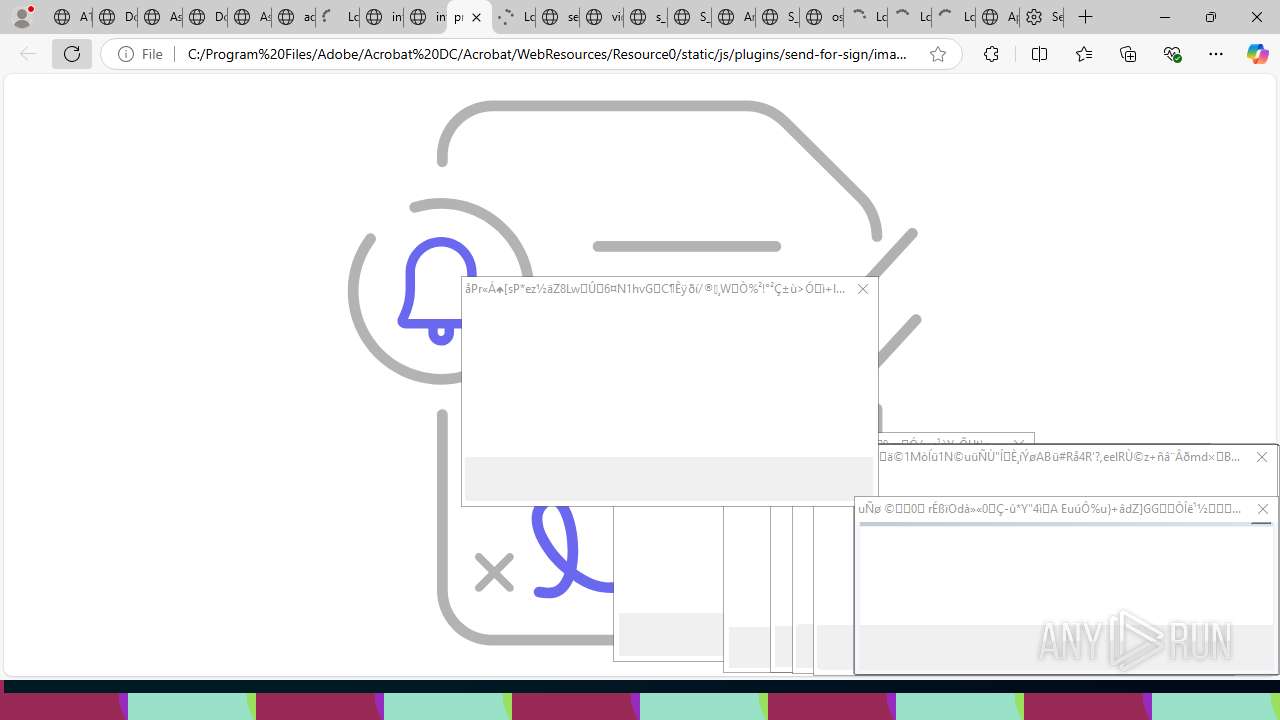
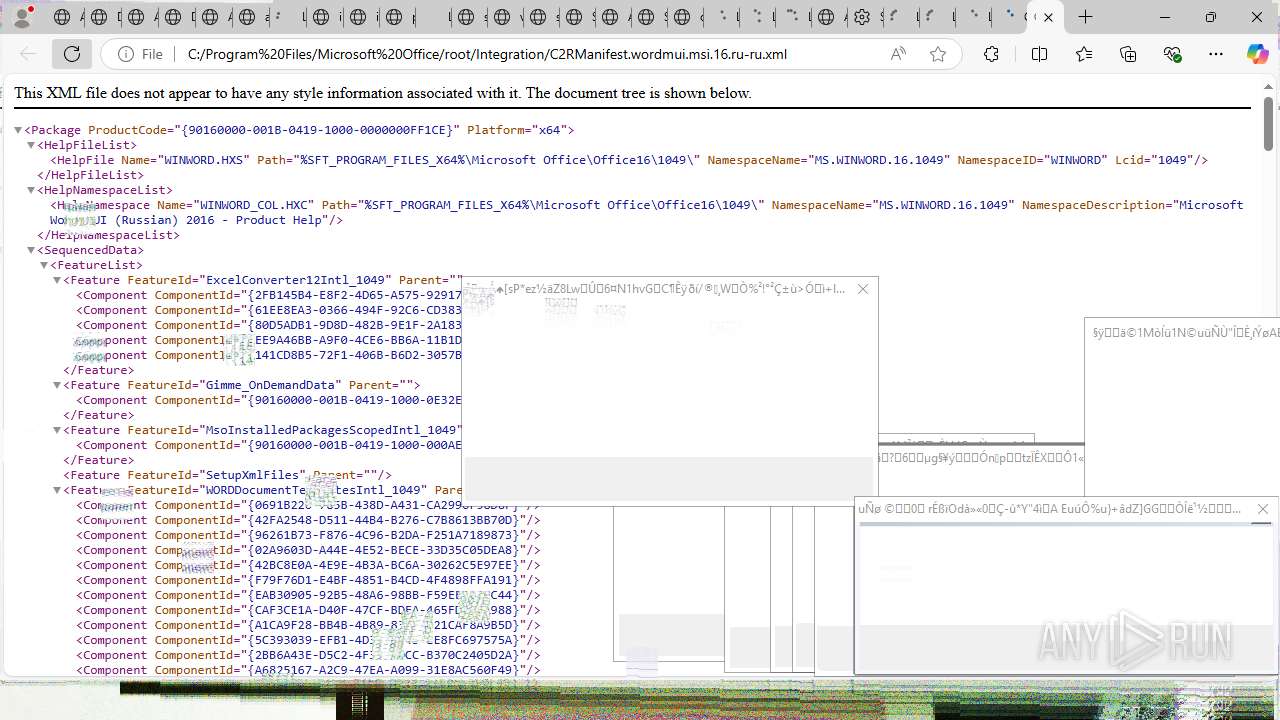
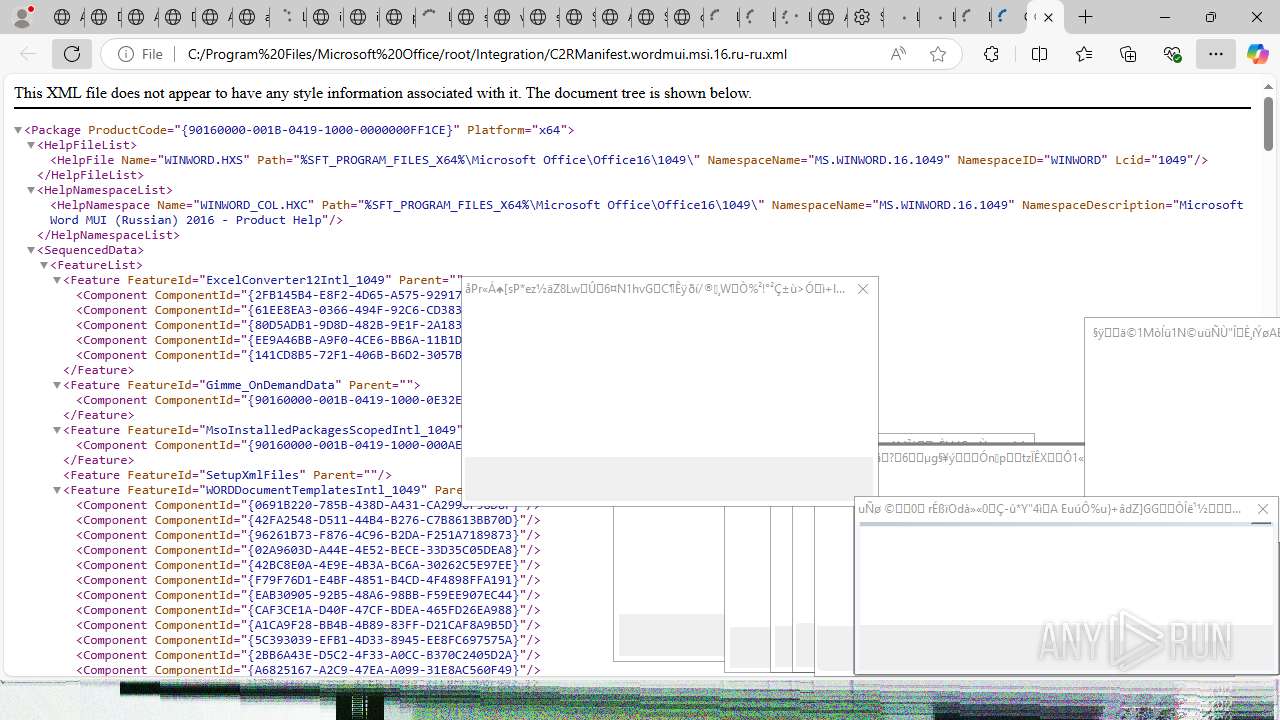
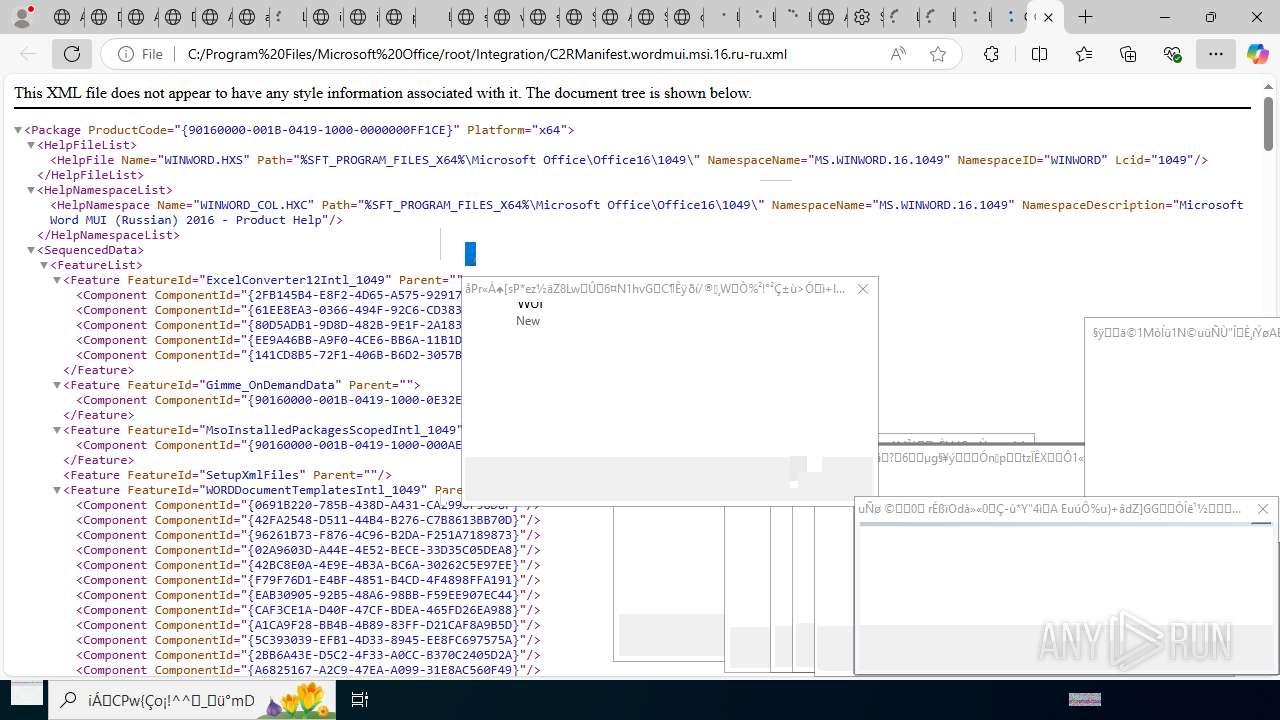
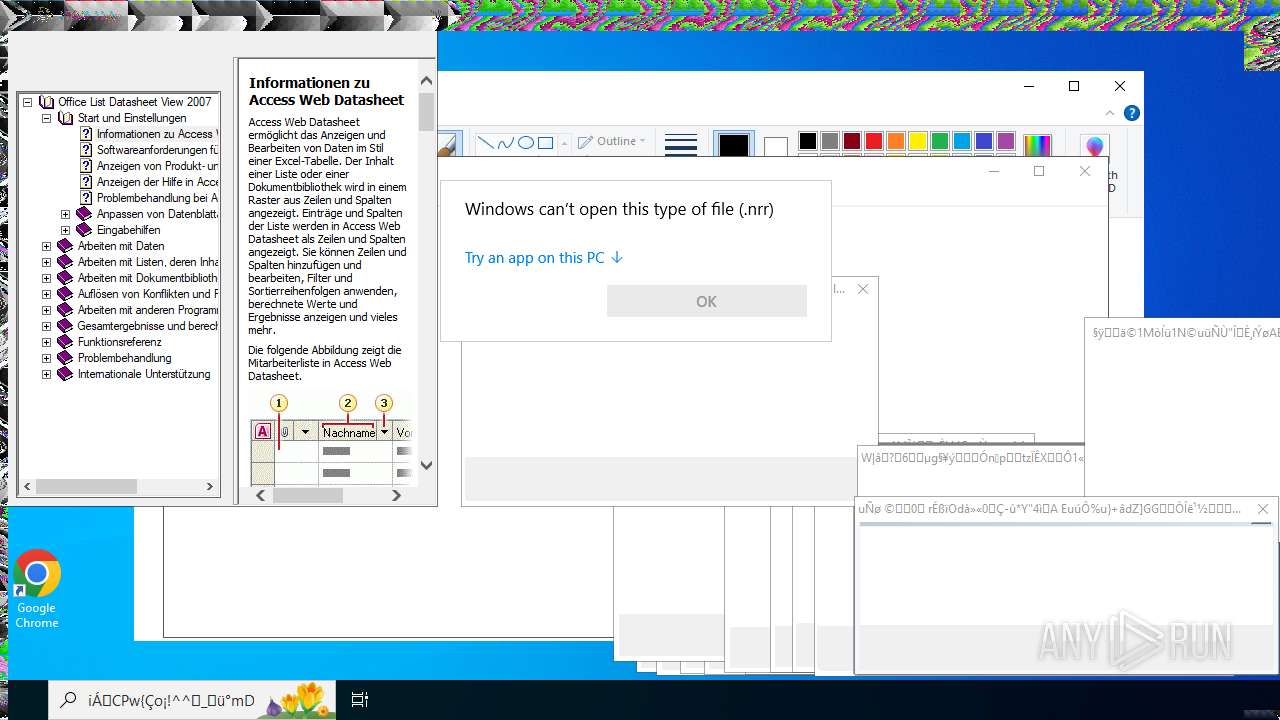
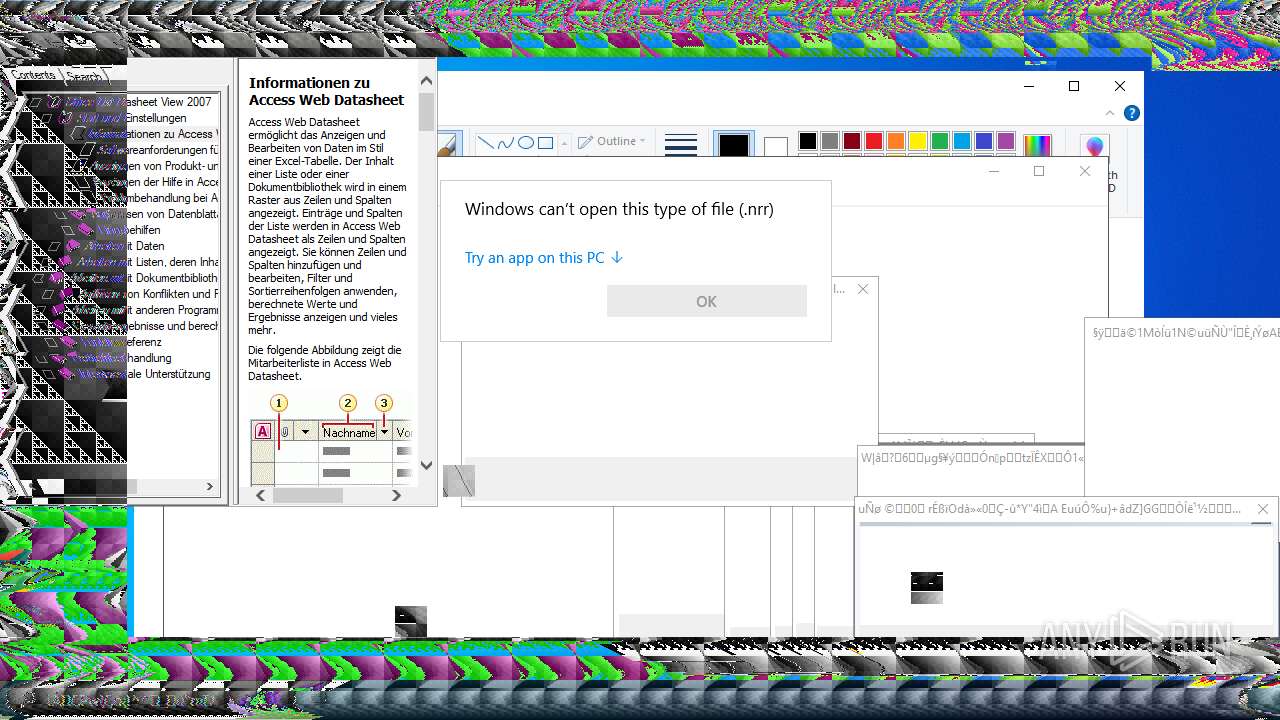
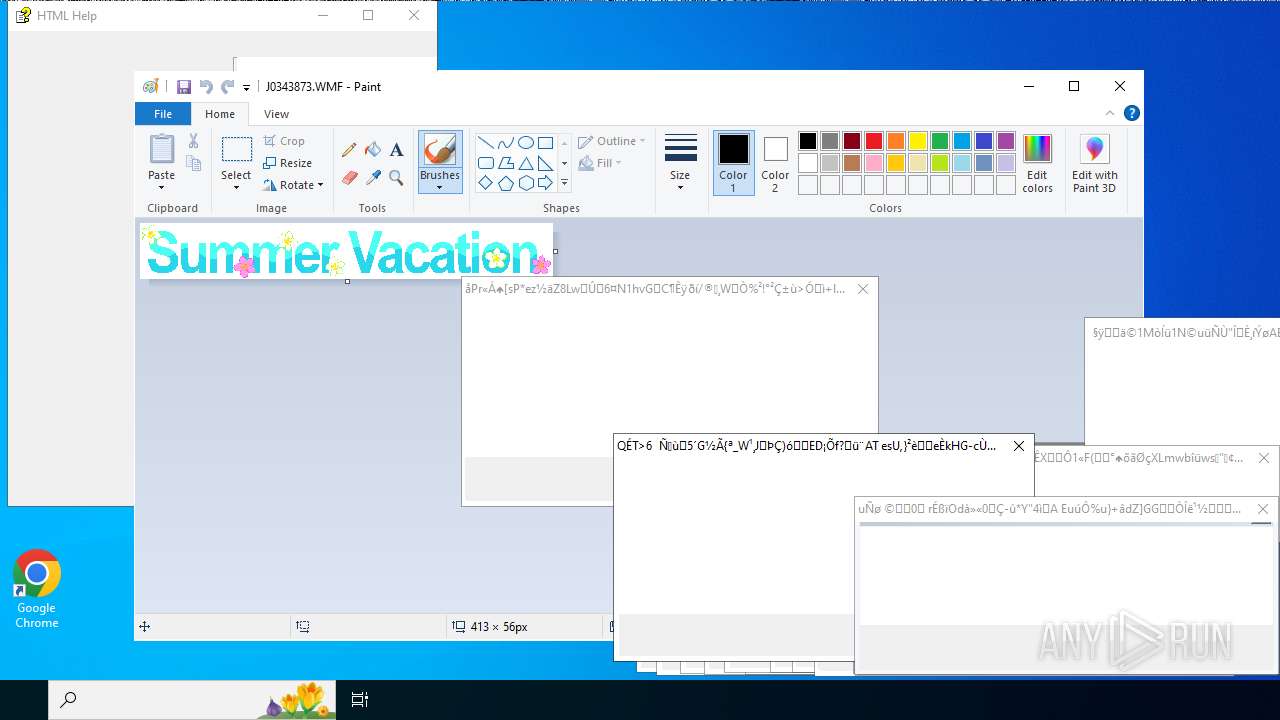
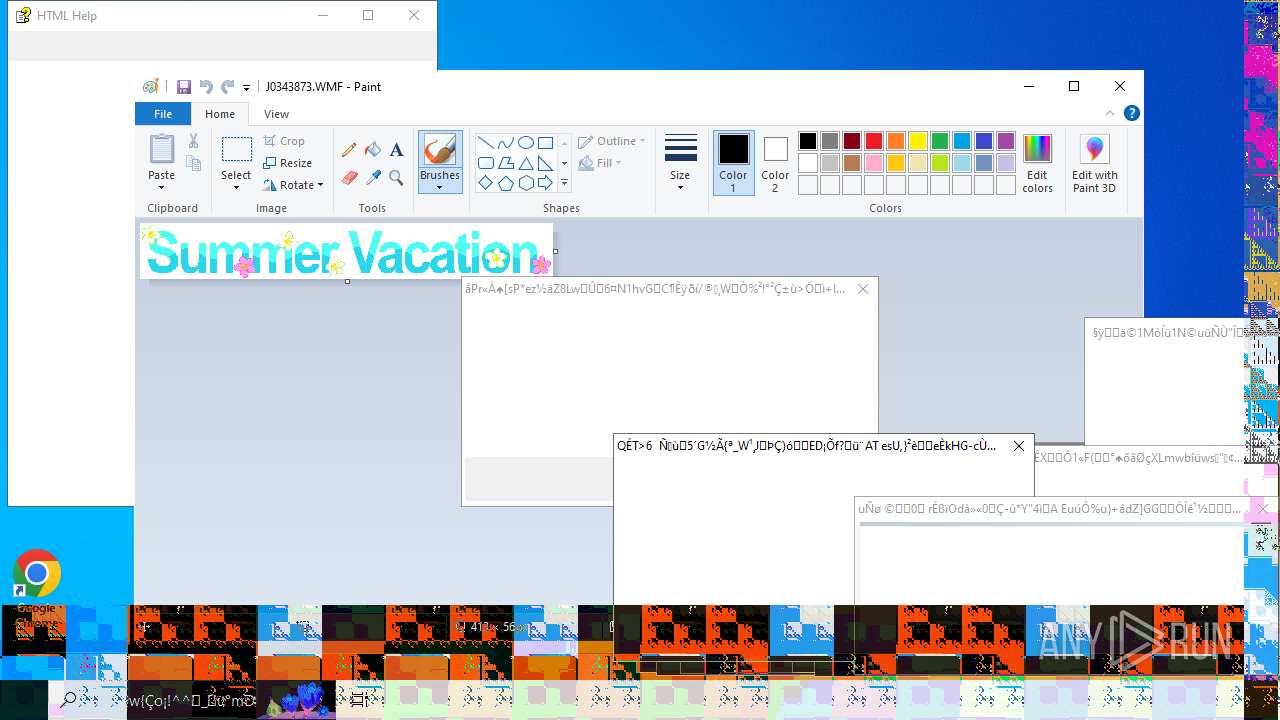
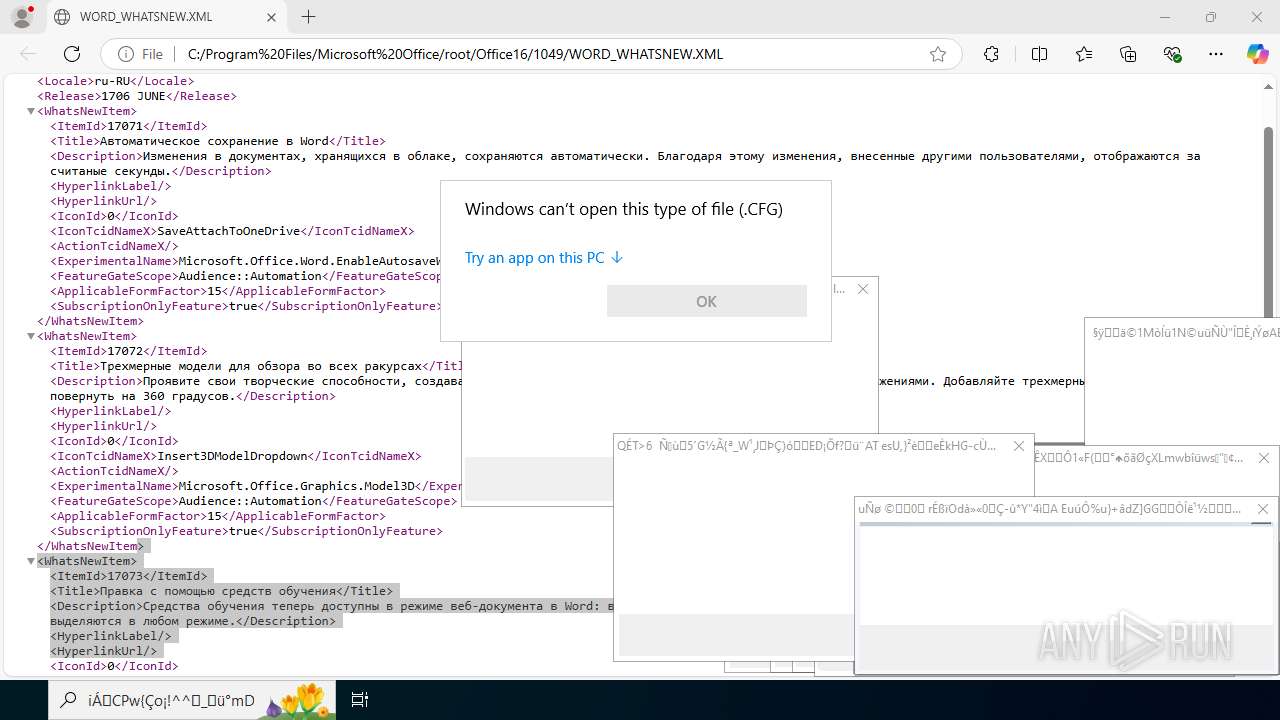
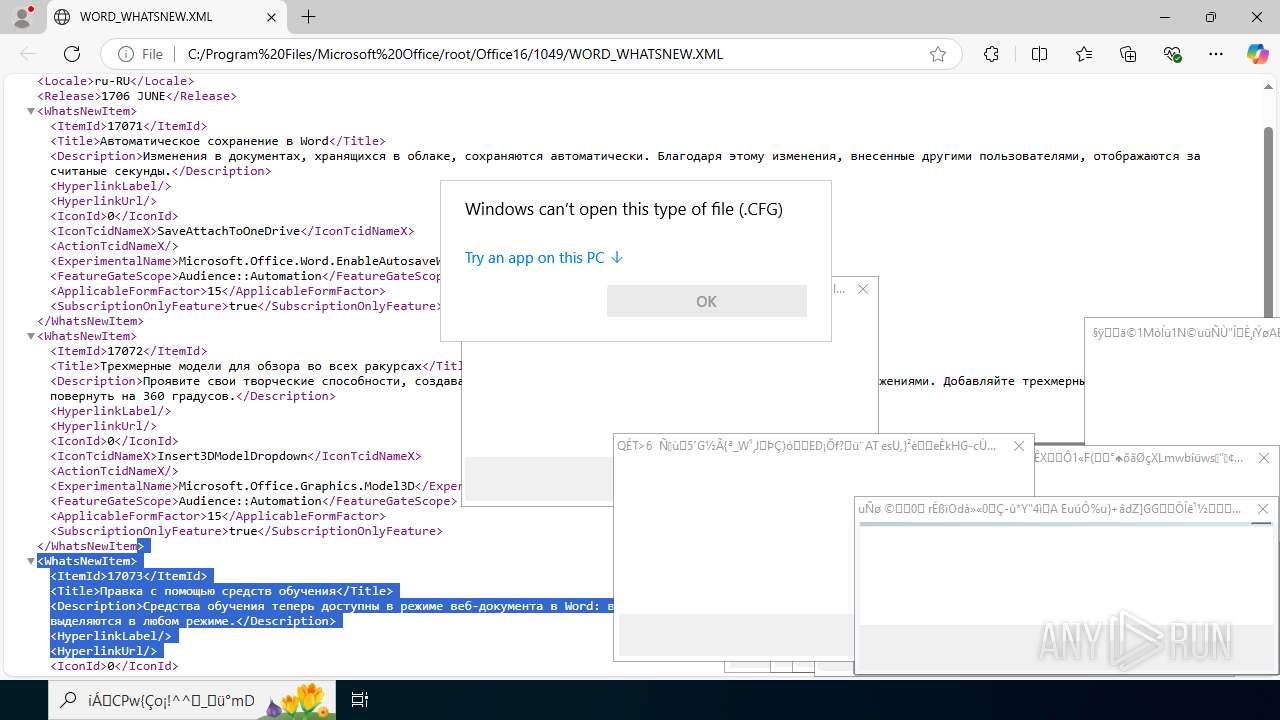
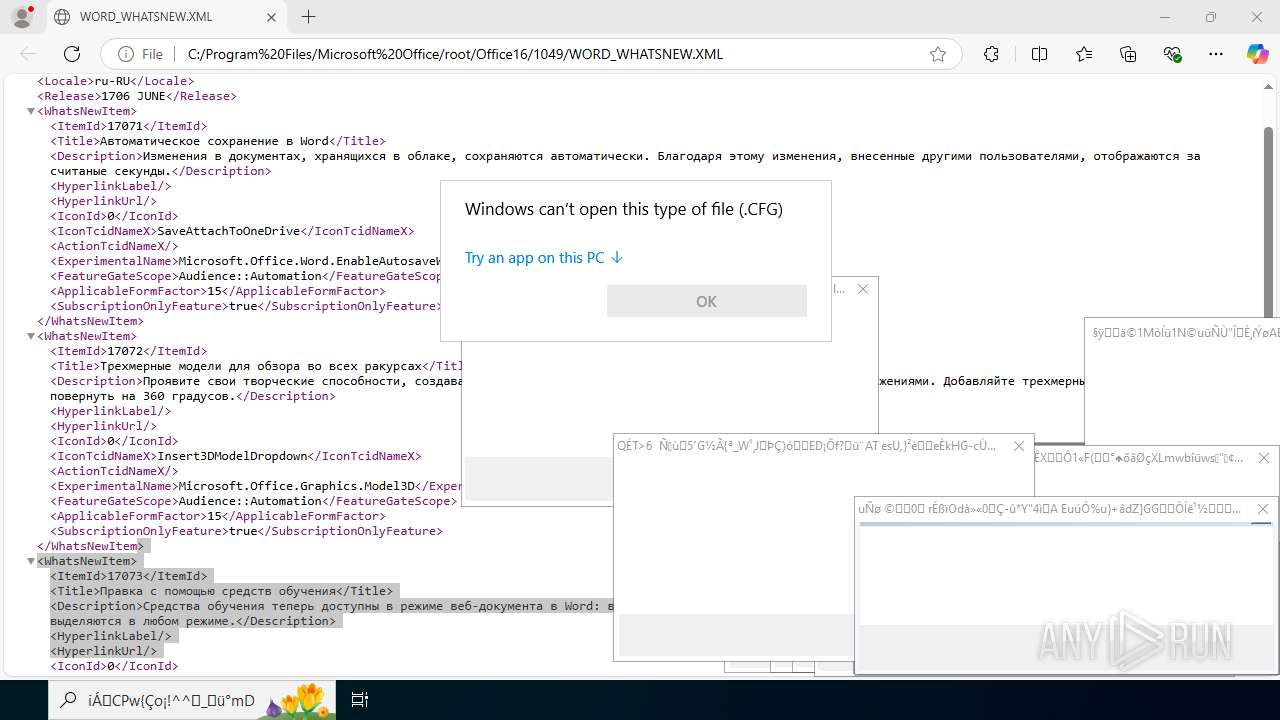
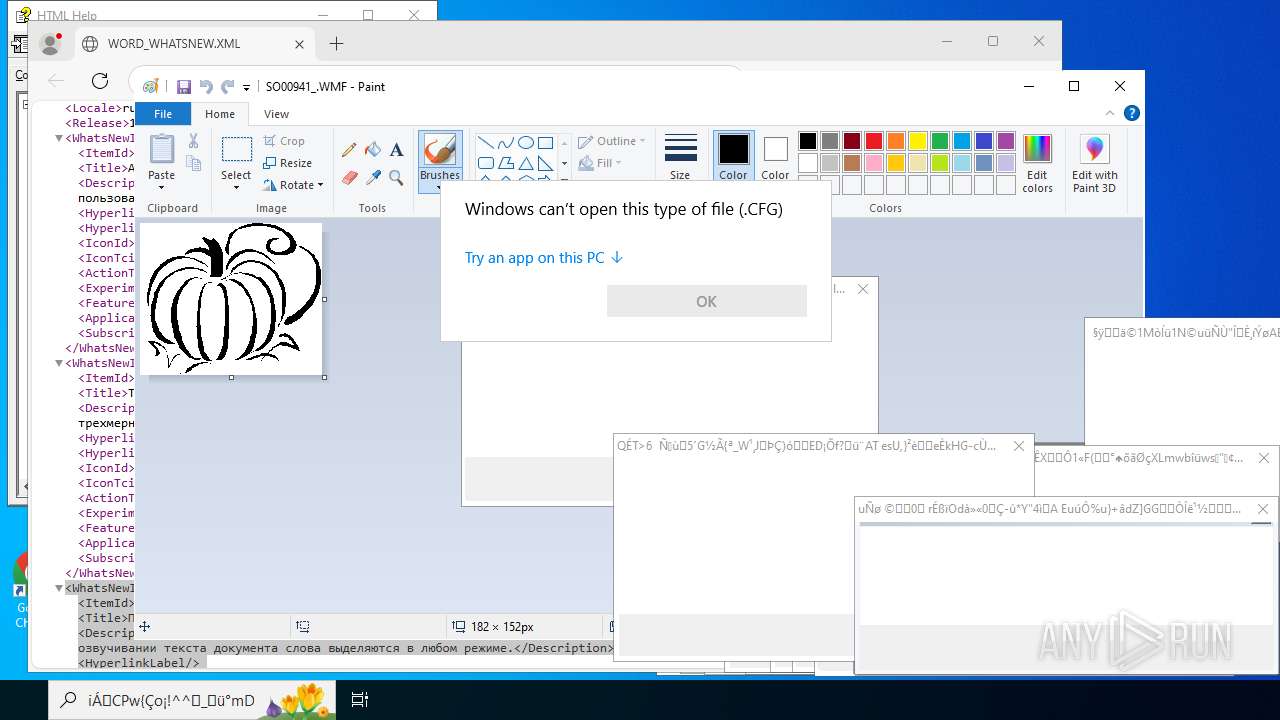
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Program Files\Microsoft Office\root\Office16\1049\PUBFTSCM\SCHEME36.CSS | C:\Windows\SysWOW64\notepad.exe | — | 萩鬊搙鐌骜龾丿翘瑟躍憌澬毕圍暼苤.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --edge-skip-compat-layer-relaunch --single-argument C:\Program Files\Adobe\Acrobat DC\Acrobat\WebResources\Resource0\static\js\plugins\send-for-sign\images\themes\dark\progressive_AddSigner_img2.svg | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 304 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 304 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument C:\Program Files\Adobe\Acrobat DC\Acrobat\WebResources\Resource0\static\images\themes\dark\s_listview_selected.svg | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | 萩鬊搙鐌骜龾丿翘瑟躍憌澬毕圍暼苤.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 432 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument C:\Program Files\Adobe\Acrobat DC\Acrobat\WebResources\Resource0\static\js\plugins\on-boarding\images\themeless\Localized_images\fi-fi\AppStore_icon.svg | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | 萩鬊搙鐌骜龾丿翘瑟躍憌澬毕圍暼苤.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 440 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument C:\Program Files\Adobe\Acrobat DC\Acrobat\WebResources\Resource0\static\images\themes\dark\S_IlluError_136x136.svg | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | 萩鬊搙鐌骜龾丿翘瑟躍憌澬毕圍暼苤.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 512 | "C:\Users\admin\Desktop\Monoxidex86.exe" | C:\Users\admin\Desktop\Monoxidex86.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 544 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=43 --always-read-main-dll --field-trial-handle=11524,i,10318310735837249034,6961392296791217459,262144 --variations-seed-version --mojo-platform-channel-handle=11688 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 620 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument C:\Program Files\Adobe\Acrobat DC\Acrobat\WebResources\Resource0\OWP\default\images\chevron-next.svg | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | 萩鬊搙鐌骜龾丿翘瑟躍憌澬毕圍暼苤.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
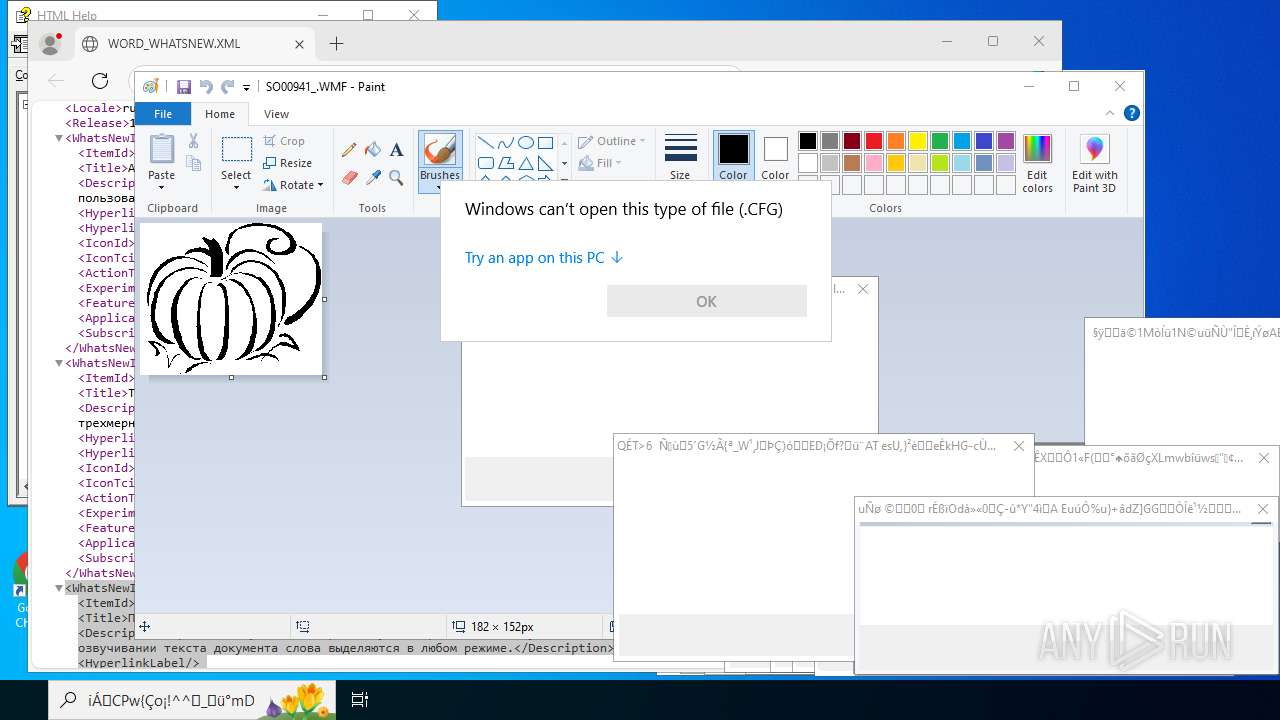
| 620 | "C:\WINDOWS\system32\mspaint.exe" "C:\Program Files\Microsoft Office\root\MEDIA\JPOSTWIZ\J0330657.WMF" | C:\Windows\SysWOW64\mspaint.exe | — | 萩鬊搙鐌骜龾丿翘瑟躍憌澬毕圍暼苤.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Paint Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
177 581
Read events
176 625
Write events
911
Delete events
45
Modification events
| (PID) Process: | (4456) 萩鬊搙鐌骜龾丿翘瑟躍憌澬毕圍暼苤.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rtf\OpenWithProgids |
| Operation: | write | Name: | Word.RTF.8 |
Value: | |||
| (PID) Process: | (4700) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 0 |
Value: 017012000000001000B24E9A3E02000000000000000600000000000000 | |||
| (PID) Process: | (4700) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 1 | |||
| (PID) Process: | (4700) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 1 | |||
| (PID) Process: | (4700) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 1 | |||
| (PID) Process: | (4700) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 1 | |||
| (PID) Process: | (4700) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 1 | |||
| (PID) Process: | (4700) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 1 | |||
| (PID) Process: | (4700) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ko-kr |
Value: 1 | |||
| (PID) Process: | (4700) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | pt-br |
Value: 1 | |||
Executable files
6
Suspicious files
457
Text files
156
Unknown types
130
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4700 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntities.bin | text | |
MD5:CC90D669144261B198DEAD45AA266572 | SHA256:89C701EEFF939A44F28921FD85365ECD87041935DCD0FE0BAF04957DA12C9899 | |||
| 7032 | Monoxidex86.exe | C:\Users\admin\AppData\Local\Temp\萩鬊搙鐌骜龾丿翘瑟躍憌澬毕圍暼苤.exe | executable | |
MD5:5C378B11848AC59704C2000B4E711C30 | SHA256:BD764FE2F9734D5AC56933CE68DF0A175BFA98DC0266AE3CD3A5C963267EA77E | |||
| 4700 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\9E6E7FDE-DDC8-4D97-834B-F979D77A8586 | xml | |
MD5:D5AB065E67EA3E3DA999CD2D0664D41B | SHA256:13C1C72449EAB582422FBAF9053F8C6AECB4269EA74E45B5C3D3B5FAB4A12D48 | |||
| 7032 | Monoxidex86.exe | C:\Users\admin\AppData\Local\Temp\萩鬊搙鐌骜龾丿翘瑟躍憌澬毕圍暼苤.txt | binary | |
MD5:001BE798AB33F13E4D048AA3444CEE31 | SHA256:3A5F0DC57A9F4125531BFD4ED54FAEB3EF0CBB0B77110608E4A79FEBCAD70CBF | |||
| 4700 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:E5791D875BB29B5A40938CB8036FB356 | SHA256:A8A526601A435A54DDC49CBF1045CAF2B8C3B6213226CDA850A981AC578D131A | |||
| 4700 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_0FB9553B978E7F00C6B2309507DEB64A | binary | |
MD5:76B5E3C21DCBEBBBB05F6923616DC61D | SHA256:F2B1415D9BA5CAEB4CAF16F4E9C4D24AA7C29714507F567E649229A70DFEE797 | |||
| 4700 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_0FB9553B978E7F00C6B2309507DEB64A | der | |
MD5:A4833401A89A87D44674DC969D3078E9 | SHA256:6B53B1AE3AB500E770F8802E28DB128707FAF6237598688D077F36658BDA8EE6 | |||
| 4700 | WINWORD.EXE | C:\Users\admin\Desktop\~$mponentscheap.rtf | pgc | |
MD5:68A8990F2A7DFF50D9A09957D118A55E | SHA256:8FEAA49A5EDA5E13F67EDAB0E01356AB31FF7667D64968F5EFACFD42417DED29 | |||
| 4700 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | ini | |
MD5:5B55494A04FF40AC7DC2F54AF46517D5 | SHA256:4CC46B724728B0DE87EF9A04F7DBF4F61A369AA7268601230C14241B876EC3E6 | |||
| 4700 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntitiesUpdated.bin | text | |
MD5:F683D454CDEC6F4B1C678B440C6989D4 | SHA256:B814559F3B483EBC370223189C8EA8E086B0EA340C823378BB9B03438C4FD22A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
88
DNS requests
87
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
11008 | svchost.exe | GET | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1755807595&P2=404&P3=2&P4=OGQjEYe6IOTKPU6S9oUBTVTKThiA6QsVpDrgUp%2fcizrjZjNhMizO0%2bYa6zhVvd9wOv8mZPdB7yrYux6TrBNq0A%3d%3d | US | binary | 2.98 Kb | whitelisted |
11008 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/550117a4-8c0f-4d0d-8ff8-7c3caccb0e8a?P1=1755811207&P2=404&P3=2&P4=PdBy8qftMSGAqlr7jOy463Zqjwhflcwla6032lMQKssvJAxLQgNa5n6r%2fRZNZr3mXpBw4jIWZvKA9r64i6w4MQ%3d%3d | US | binary | 2.98 Kb | whitelisted |
11008 | svchost.exe | GET | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/550117a4-8c0f-4d0d-8ff8-7c3caccb0e8a?P1=1755811207&P2=404&P3=2&P4=PdBy8qftMSGAqlr7jOy463Zqjwhflcwla6032lMQKssvJAxLQgNa5n6r%2fRZNZr3mXpBw4jIWZvKA9r64i6w4MQ%3d%3d | US | binary | 6.24 Kb | whitelisted |
2460 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
1268 | svchost.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.15:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
4724 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
4724 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 420 b | whitelisted |
4700 | WINWORD.EXE | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
4700 | WINWORD.EXE | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6312 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2460 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2460 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 23.216.77.15:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
Process | Message |
|---|---|
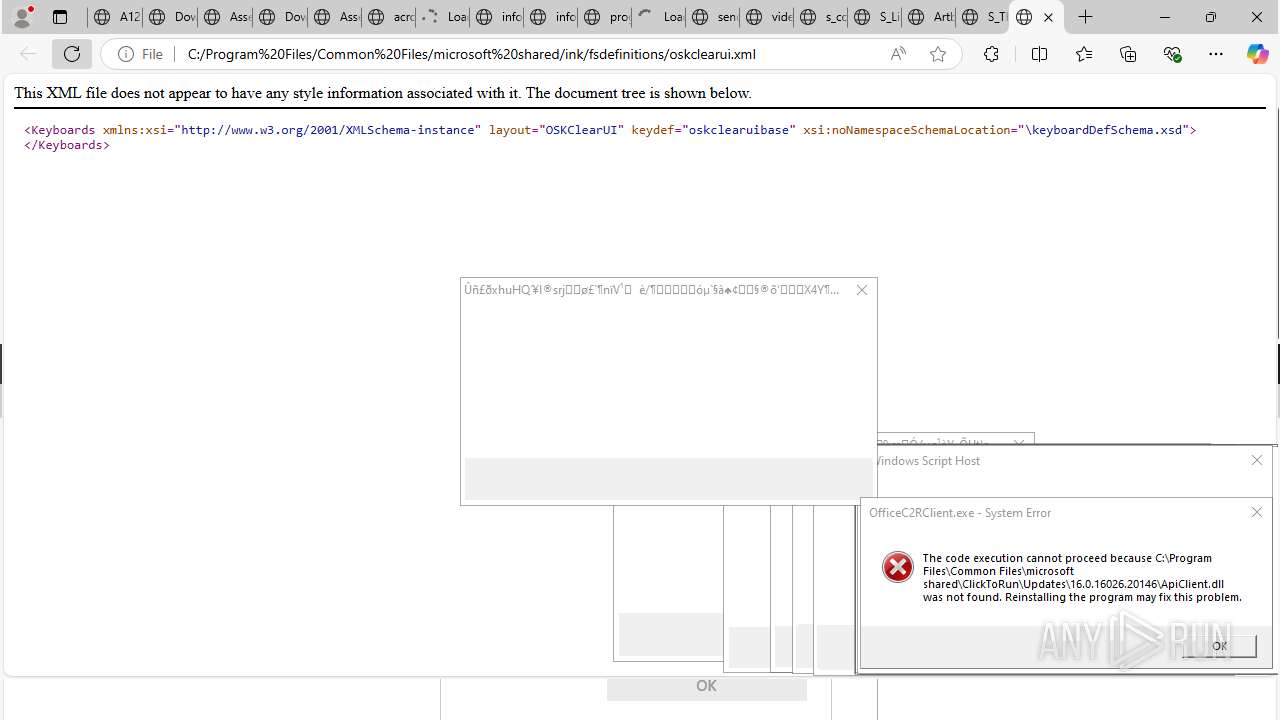
elevation_service.exe | [0816/111129.542:ERROR:service.cc(225)] Failed to connect to the service control manager: The service process could not connect to the service controller. (0x427)
|