| download: | fwlink |
| Full analysis: | https://app.any.run/tasks/9a64892d-983a-42bb-ae1b-7b2b16fc8060 |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2019, 17:58:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A18F62282B6285E8634012838A93BEC0 |
| SHA1: | F0B63C943FCF9DAF5CC25F2FC2549B5E44C92681 |
| SHA256: | BD63CC660D1A3E6C672E8FCEE4601368E301B59203CFD9D97235F6AB0AD77269 |
| SSDEEP: | 24576:qUAsBeZYyYoMGYVl2JjLefH0QcLS35ZO/bDuoBD+L3IquLaOKqBDO+7pBgdaBpZp:1edMfQWfUQcG5ZsVD43IpXvFBz7 |
MALICIOUS
Loads dropped or rewritten executable
- fwlink.exe (PID: 3368)
Changes the autorun value in the registry
- adksetup.exe (PID: 2612)
SUSPICIOUS
Executable content was dropped or overwritten
- fwlink.exe (PID: 3368)
- fwlink.exe (PID: 1728)
- adksetup.exe (PID: 2612)
Creates files in the program directory
- fwlink.exe (PID: 3368)
- adksetup.exe (PID: 2612)
Starts itself from another location
- fwlink.exe (PID: 3368)
Executed as Windows Service
- vssvc.exe (PID: 1888)
Searches for installed software
- adksetup.exe (PID: 2612)
Creates a software uninstall entry
- adksetup.exe (PID: 2612)
Reads Internet Cache Settings
- fwlink.exe (PID: 3368)
INFO
Dropped object may contain Bitcoin addresses
- fwlink.exe (PID: 3368)
Low-level read access rights to disk partition
- vssvc.exe (PID: 1888)
Reads settings of System Certificates
- fwlink.exe (PID: 3368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:05:04 00:56:03+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.13 |
| CodeSize: | 303616 |
| InitializedDataSize: | 403456 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2e33e |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 10.1.18362.1 |
| ProductVersionNumber: | 10.1.18362.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Microsoft Corporation |
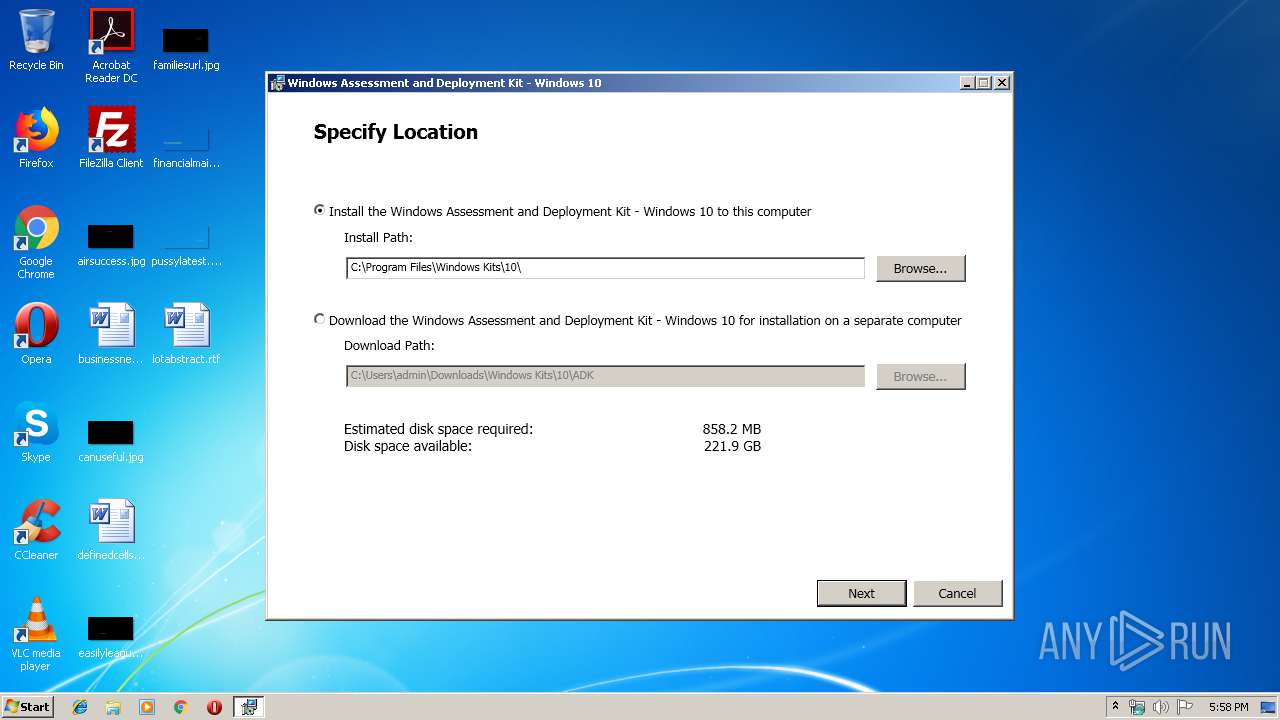
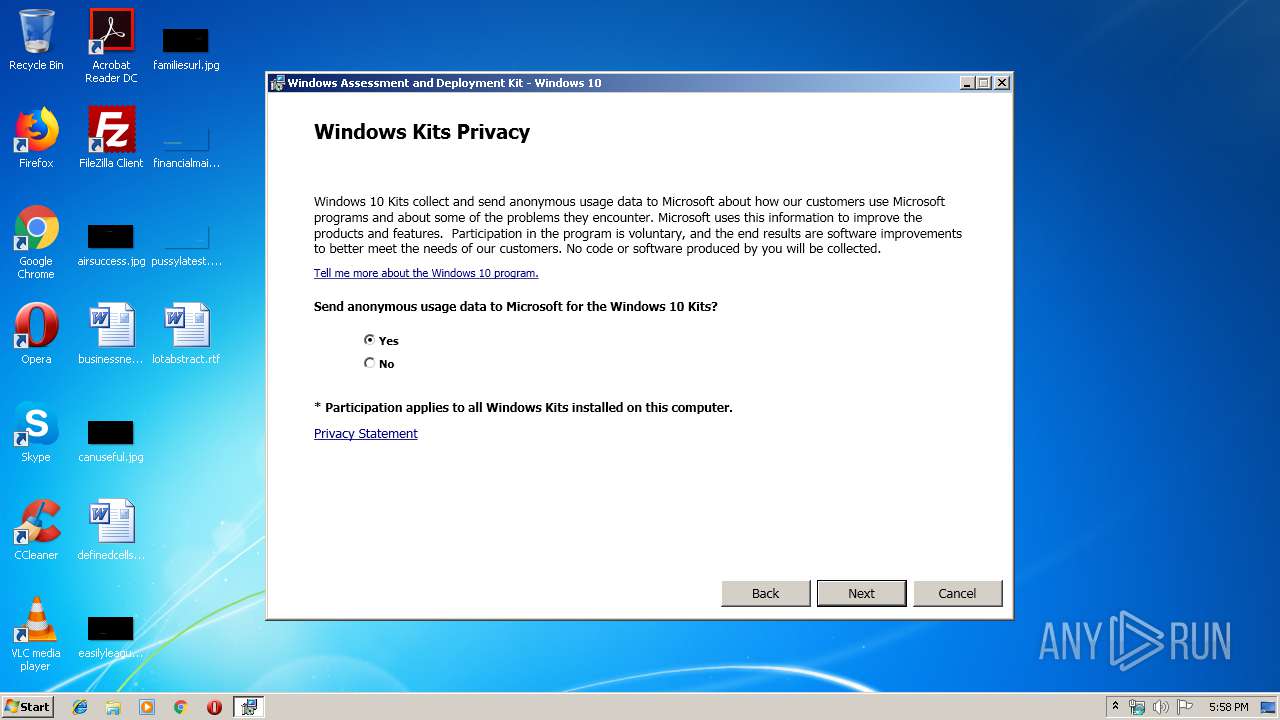
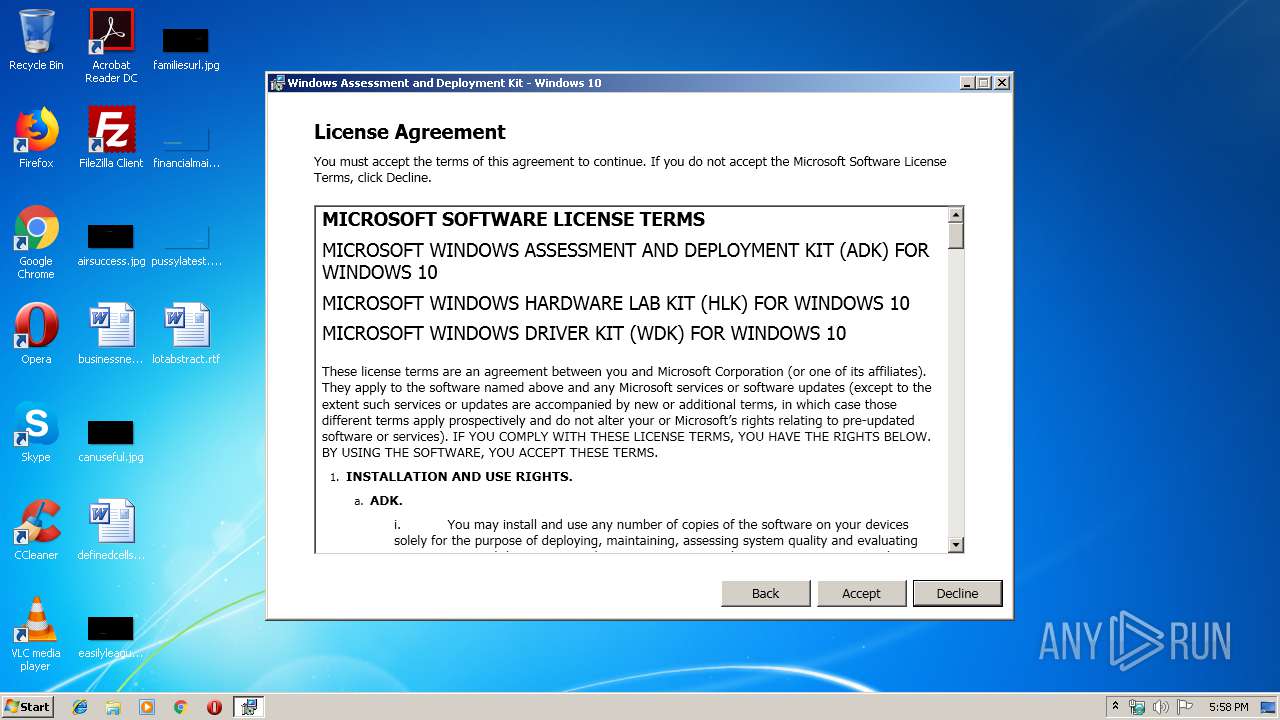
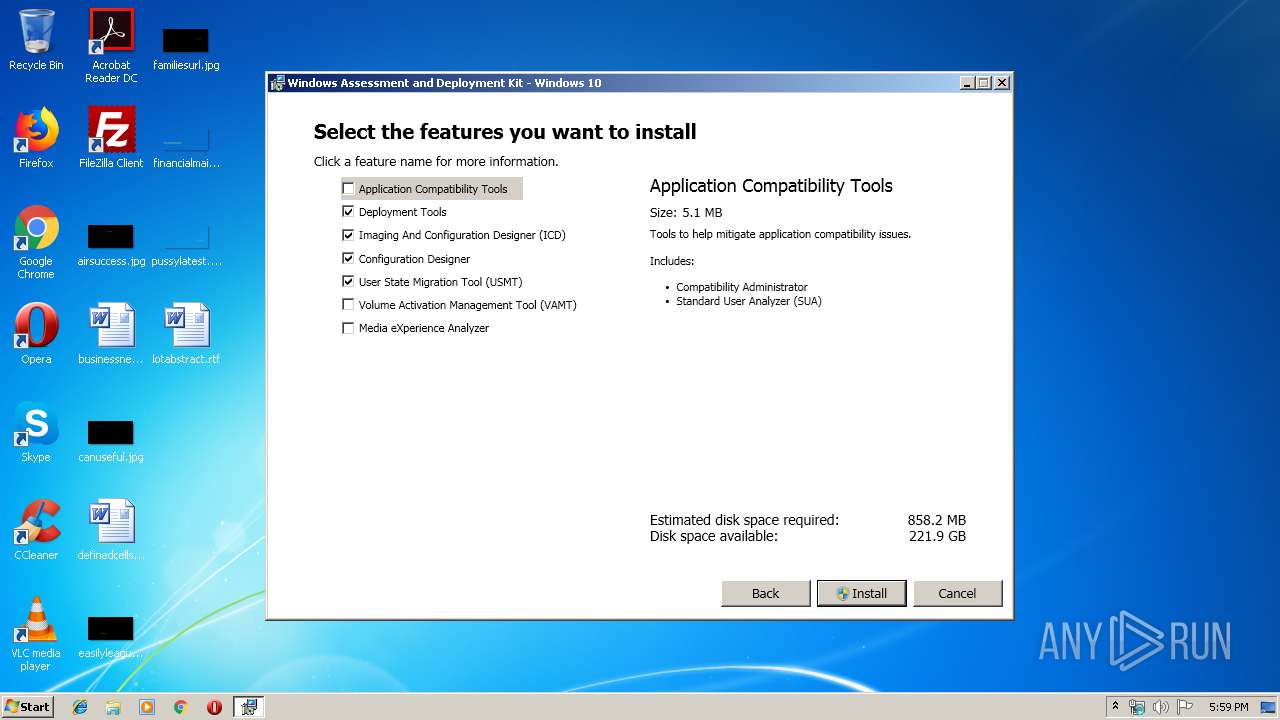
| FileDescription: | Windows Assessment and Deployment Kit - Windows 10 |
| FileVersion: | 10.1.18362.1 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Microsoft Corporation. All rights reserved. |
| OriginalFileName: | adksetup.exe |
| ProductName: | Windows Assessment and Deployment Kit - Windows 10 |
| ProductVersion: | 10.1.18362.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-May-2018 22:56:03 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Windows Assessment and Deployment Kit - Windows 10 |
| FileVersion: | 10.1.18362.1 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Microsoft Corporation. All rights reserved. |
| OriginalFilename: | adksetup.exe |
| ProductName: | Windows Assessment and Deployment Kit - Windows 10 |
| ProductVersion: | 10.1.18362.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 03-May-2018 22:56:03 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0004A1D7 | 0x0004A200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55637 |
.rdata | 0x0004C000 | 0x0001F5D0 | 0x0001F600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.13906 |
.data | 0x0006C000 | 0x0000172C | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.17124 |
.wixburn8 | 0x0006E000 | 0x00000038 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.520588 |
.rsrc | 0x0006F000 | 0x0003E500 | 0x0003E600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.94804 |
.reloc | 0x000AE000 | 0x00003E04 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.71441 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.30829 | 1234 | Latin 1 / Western European | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
Cabinet.dll (delay-loaded) |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
41
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1728 | "C:\Users\admin\AppData\Local\Temp\fwlink.exe" | C:\Users\admin\AppData\Local\Temp\fwlink.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Assessment and Deployment Kit - Windows 10 Exit code: 0 Version: 10.1.18362.1 Modules
| |||||||||||||||
| 1888 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2612 | "C:\Users\admin\AppData\Local\Temp\{4224D00F-07FB-41E5-A968-E0F4032C2B46}\.be\adksetup.exe" -q -burn.elevated BurnPipe.{85845F1F-78E8-479D-98B0-2697D1CD2109} {23CB631E-B816-4553-9390-45190F32B16C} 3368 | C:\Users\admin\AppData\Local\Temp\{4224D00F-07FB-41E5-A968-E0F4032C2B46}\.be\adksetup.exe | fwlink.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Assessment and Deployment Kit - Windows 10 Exit code: 0 Version: 10.1.18362.1 Modules
| |||||||||||||||
| 3368 | "C:\Users\admin\AppData\Local\Temp\{A3A27C6E-D55D-48A6-A45D-ECD3DB5D9622}\.cr\fwlink.exe" -burn.clean.room="C:\Users\admin\AppData\Local\Temp\fwlink.exe" -burn.filehandle.attached=148 -burn.filehandle.self=156 | C:\Users\admin\AppData\Local\Temp\{A3A27C6E-D55D-48A6-A45D-ECD3DB5D9622}\.cr\fwlink.exe | fwlink.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Assessment and Deployment Kit - Windows 10 Exit code: 0 Version: 10.1.18362.1 Modules
| |||||||||||||||
Total events
771
Read events
576
Write events
195
Delete events
0
Modification events
| (PID) Process: | (3368) fwlink.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: fwlink.exe | |||
| (PID) Process: | (3368) fwlink.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3368) fwlink.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2612) adksetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000009823BEDA5EACD501340A00002C0A0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2612) adksetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 40000000000000009823BEDA5EACD501340A00002C0A0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2612) adksetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 33 | |||
| (PID) Process: | (2612) adksetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 400000000000000094E23EDB5EACD501340A00002C0A0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2612) adksetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000A20946DB5EACD501340A000094050000E8030000010000000000000000000000BD49508A3E2B7144A535CEEFE406977E0000000000000000 | |||
| (PID) Process: | (1888) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000422F6CDB5EACD50160070000040A0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1888) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000422F6CDB5EACD50160070000B0060000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
23
Suspicious files
4
Text files
52
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1728 | fwlink.exe | C:\Users\admin\AppData\Local\Temp\{A3A27C6E-D55D-48A6-A45D-ECD3DB5D9622}\.cr\fwlink.exe | executable | |
MD5:— | SHA256:— | |||
| 3368 | fwlink.exe | C:\Users\admin\AppData\Local\Temp\{4224D00F-07FB-41E5-A968-E0F4032C2B46}\.ba\fr\Microsoft.Bootstrapper.Presentation.Resources.dll | executable | |
MD5:— | SHA256:— | |||
| 3368 | fwlink.exe | C:\Users\admin\AppData\Local\Temp\{4224D00F-07FB-41E5-A968-E0F4032C2B46}\.ba\BootstrapperCore.dll | executable | |
MD5:789476090439024462CF3694B8090B7D | SHA256:9C900B865AAAB23622C23E6F2EB22DFC881109351FE06F07CD7CC69C80CB55D2 | |||
| 3368 | fwlink.exe | C:\Users\admin\AppData\Local\Temp\{4224D00F-07FB-41E5-A968-E0F4032C2B46}\.ba\eula.rtf | text | |
MD5:8E1FF666E42CD7B26E0D5F8ABA48CF64 | SHA256:82ACD1CA7CA2C7FB7CAE8A9B843A28842BDCDC5263F665D3CDC82E318382B496 | |||
| 3368 | fwlink.exe | C:\Users\admin\AppData\Local\Temp\{4224D00F-07FB-41E5-A968-E0F4032C2B46}\.ba\de\eula.rtf | text | |
MD5:7B14174D4FDD33575A908B695D6E383A | SHA256:568126FA52AEE5E1146537063CD71239ADAC19EF827D50286BDBC10CAA7B0197 | |||
| 3368 | fwlink.exe | C:\Users\admin\AppData\Local\Temp\{4224D00F-07FB-41E5-A968-E0F4032C2B46}\.ba\it\eula.rtf | text | |
MD5:C2CE085B3107ED6D5C8D591D690074F9 | SHA256:6EE79BF8947AF649704CD9B24FAA8ED7F990322D0C4023186480515E6AB5C934 | |||
| 3368 | fwlink.exe | C:\Users\admin\AppData\Local\Temp\{4224D00F-07FB-41E5-A968-E0F4032C2B46}\.ba\2052\NetfxLicense.rtf | text | |
MD5:CBAEE2132EC712D552E7971D583CBB63 | SHA256:909FA52BD296594135032A9FCE58B578DEFB4F55EF6DEE9C0AB13ACB5585FED9 | |||
| 3368 | fwlink.exe | C:\Users\admin\AppData\Local\Temp\{4224D00F-07FB-41E5-A968-E0F4032C2B46}\.ba\mbapreq.wxl | xml | |
MD5:2598179319ADF312D99FC4F9379572D3 | SHA256:B3204B5CCFB0E5E7B43D8448B2B9E179423F1B139E53AA72616C498246090C3C | |||
| 3368 | fwlink.exe | C:\Users\admin\AppData\Local\Temp\{4224D00F-07FB-41E5-A968-E0F4032C2B46}\.ba\ru\eula.rtf | text | |
MD5:654651A42F717AFD72C55BDD09BF2409 | SHA256:C07684ADD35C311BFA445D1364062CA35E36C1107AB63684FAE7F7B98D6A58F2 | |||
| 3368 | fwlink.exe | C:\Users\admin\AppData\Local\Temp\{4224D00F-07FB-41E5-A968-E0F4032C2B46}\.ba\zh-HANT\eula.rtf | text | |
MD5:11557E54DB34DE7CE5190AA3B3CD462D | SHA256:D63A08884A7F4A1D211E721023A3422BB552BB8CDB9BCDAF99495490A8CA9D81 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3368 | fwlink.exe | 104.108.55.117:443 | go.microsoft.com | Akamai Technologies, Inc. | NL | unknown |
3368 | fwlink.exe | 23.210.248.197:443 | download.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
download.microsoft.com |
| whitelisted |