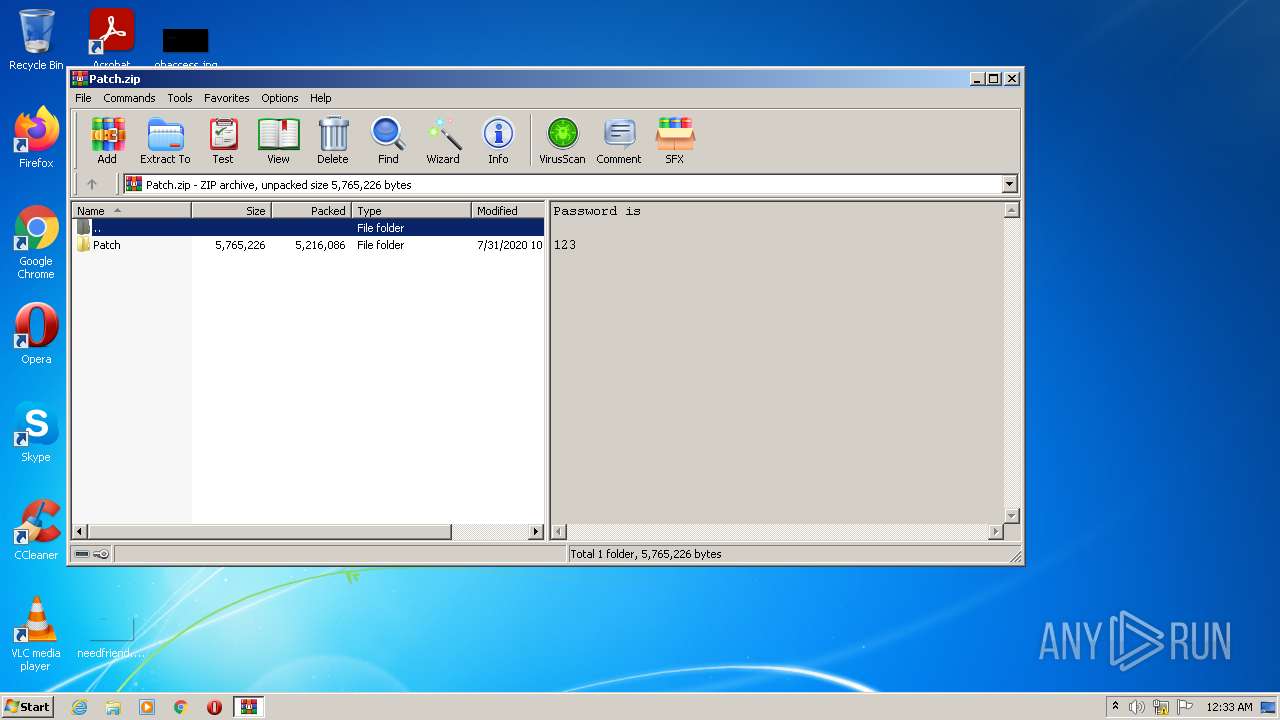
| File name: | Patch.zip |
| Full analysis: | https://app.any.run/tasks/80946883-ee75-41fe-bc0a-4049bd97407c |
| Verdict: | Malicious activity |
| Analysis date: | January 25, 2022, 00:33:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | B57F0A510A83CDA98F1A35F47908F29E |
| SHA1: | 291FDED7A3DDE86A94376744BF58FFC0294EC7E3 |
| SHA256: | BD4F1214354EF3FE196AF58D53E44945440E850A0673CB0BE701E91FFABDB99A |
| SSDEEP: | 98304:sxzEgUHZazzPkuw96Pu2GyA1S5JZMQaxCFfnhjHxCUGhPrJl3IC5gPdJ:sx0a3IEPu2bAAhn/hzxotxIdJ |
MALICIOUS
Application was dropped or rewritten from another process
- Patch32.exe (PID: 3840)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 3268)
- Patch32.exe (PID: 3840)
Reads the computer name
- WinRAR.exe (PID: 3268)
- Patch32.exe (PID: 3840)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3268)
- Patch32.exe (PID: 3840)
Drops a file with too old compile date
- WinRAR.exe (PID: 3268)
- Patch32.exe (PID: 3840)
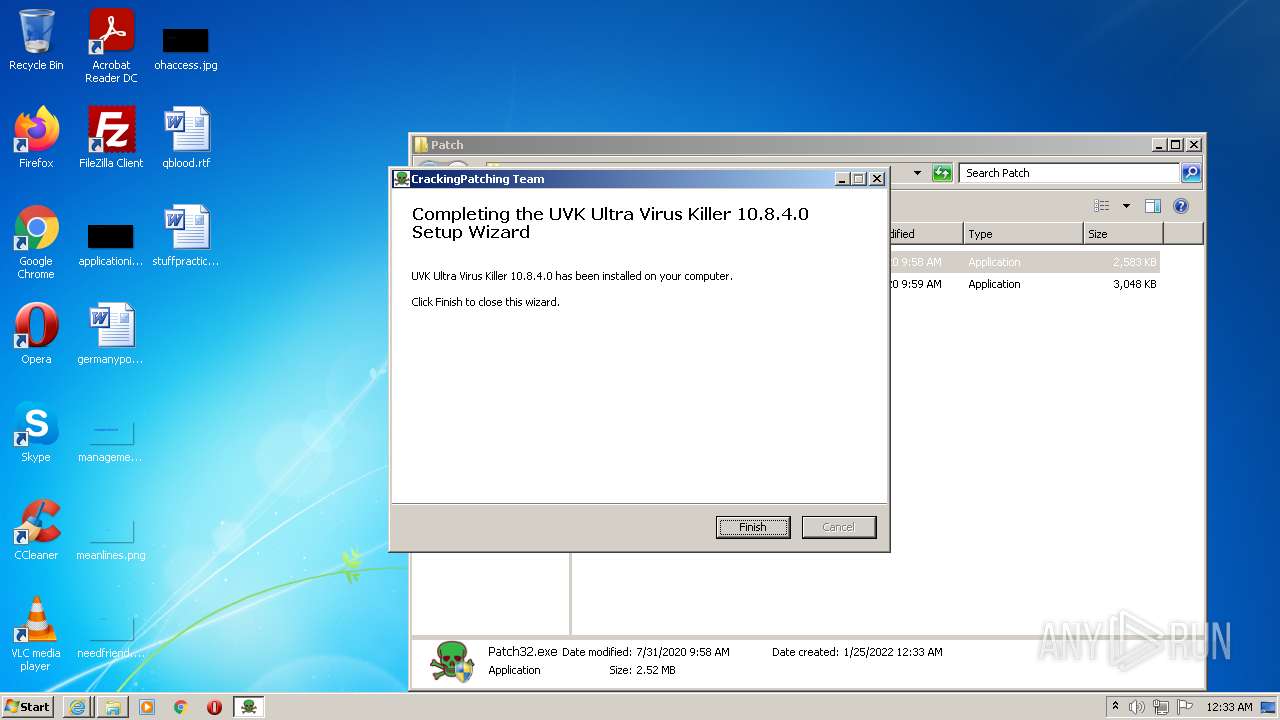
Creates a directory in Program Files
- Patch32.exe (PID: 3840)
Creates files in the program directory
- Patch32.exe (PID: 3840)
Creates a software uninstall entry
- Patch32.exe (PID: 3840)
Starts Internet Explorer
- Patch32.exe (PID: 3840)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2680)
- iexplore.exe (PID: 3664)
INFO
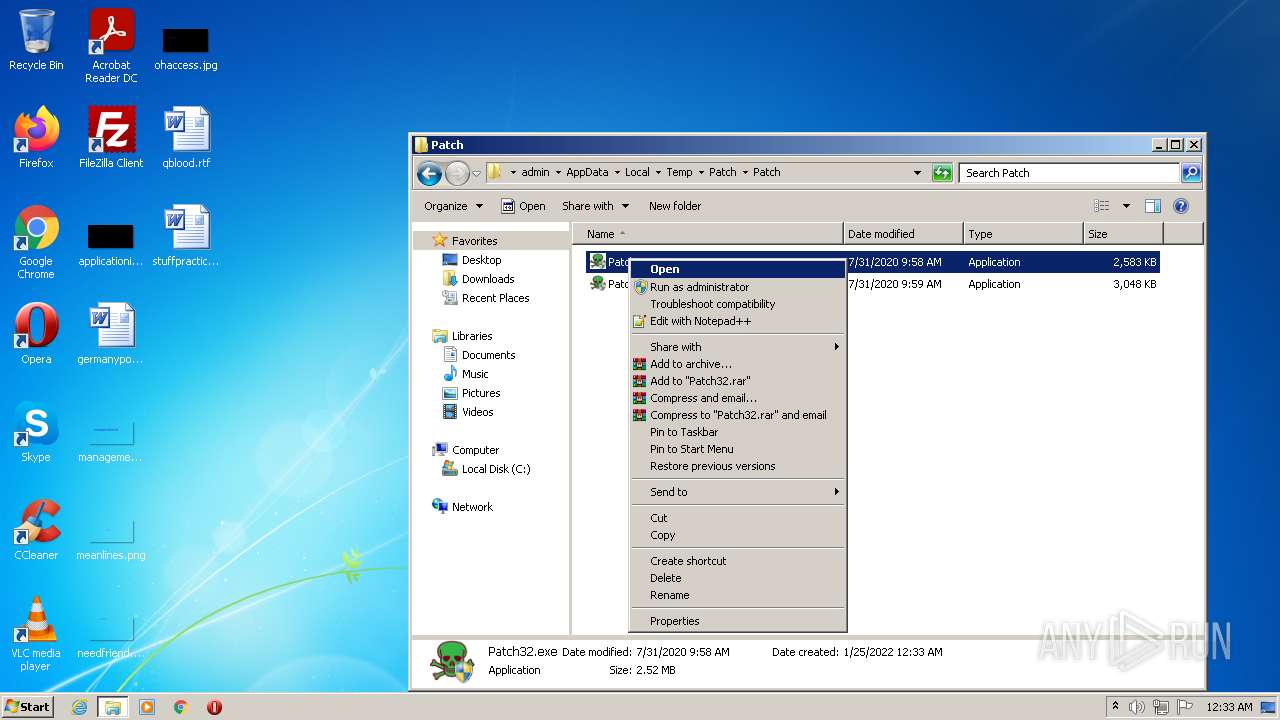
Manual execution by user
- Patch32.exe (PID: 3840)
Reads the computer name
- iexplore.exe (PID: 3804)
- iexplore.exe (PID: 1408)
- iexplore.exe (PID: 2680)
- iexplore.exe (PID: 3664)
Checks supported languages
- iexplore.exe (PID: 3804)
- iexplore.exe (PID: 1408)
- iexplore.exe (PID: 2680)
- iexplore.exe (PID: 3664)
Changes internet zones settings
- iexplore.exe (PID: 3804)
- iexplore.exe (PID: 1408)
Application launched itself
- iexplore.exe (PID: 3804)
- iexplore.exe (PID: 1408)
Reads internet explorer settings
- iexplore.exe (PID: 2680)
- iexplore.exe (PID: 3664)
Checks Windows Trust Settings
- iexplore.exe (PID: 3664)
- iexplore.exe (PID: 2680)
- iexplore.exe (PID: 3804)
- iexplore.exe (PID: 1408)
Changes settings of System certificates
- iexplore.exe (PID: 2680)
Reads settings of System Certificates
- iexplore.exe (PID: 3664)
- iexplore.exe (PID: 2680)
- iexplore.exe (PID: 1408)
- iexplore.exe (PID: 3804)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2680)
Creates files in the user directory
- iexplore.exe (PID: 3664)
- iexplore.exe (PID: 2680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
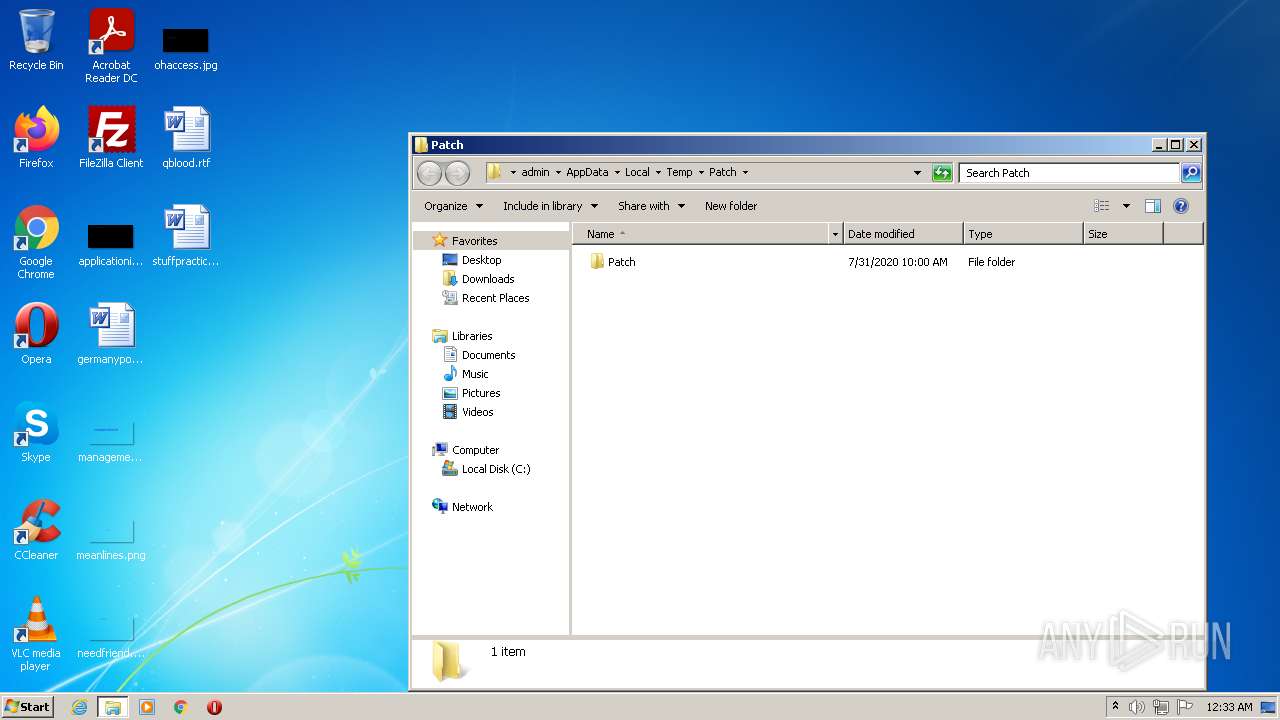
| ZipFileName: | Patch/ |
|---|---|
| ZipUncompressedSize: | - |
| ZipCompressedSize: | - |
| ZipCRC: | 0x00000000 |
| ZipModifyDate: | 2020:07:31 10:00:10 |
| ZipCompression: | None |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 10 |
Total processes
48
Monitored processes
6
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
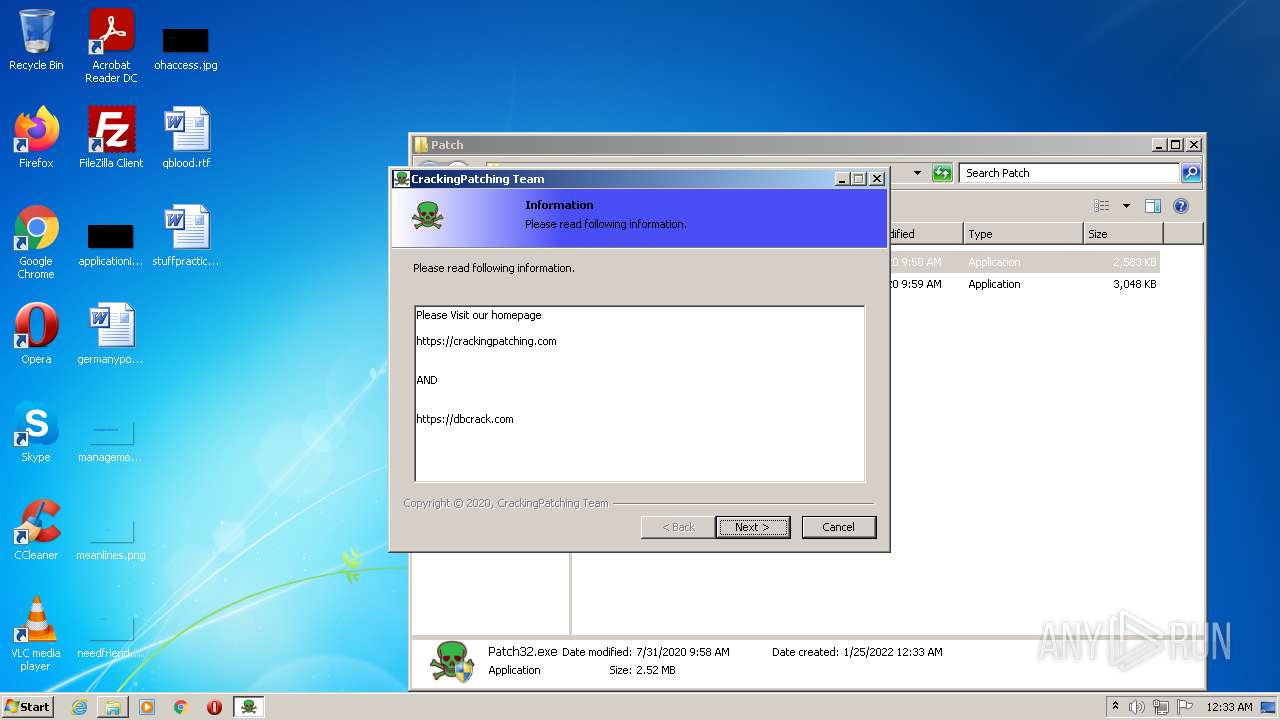
| 1408 | "C:\Program Files\Internet Explorer\iexplore.exe" https://crackingpatching.com/2019/08/idm-crack.html | C:\Program Files\Internet Explorer\iexplore.exe | Patch32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2680 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1408 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
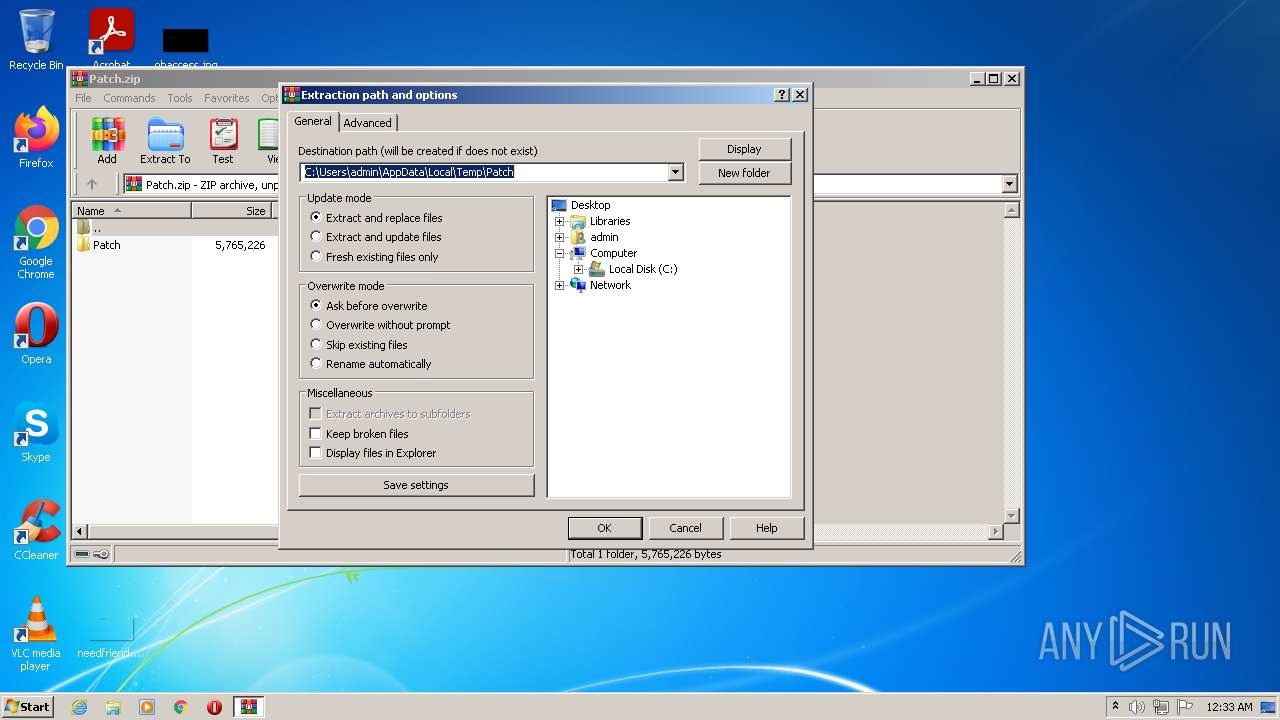
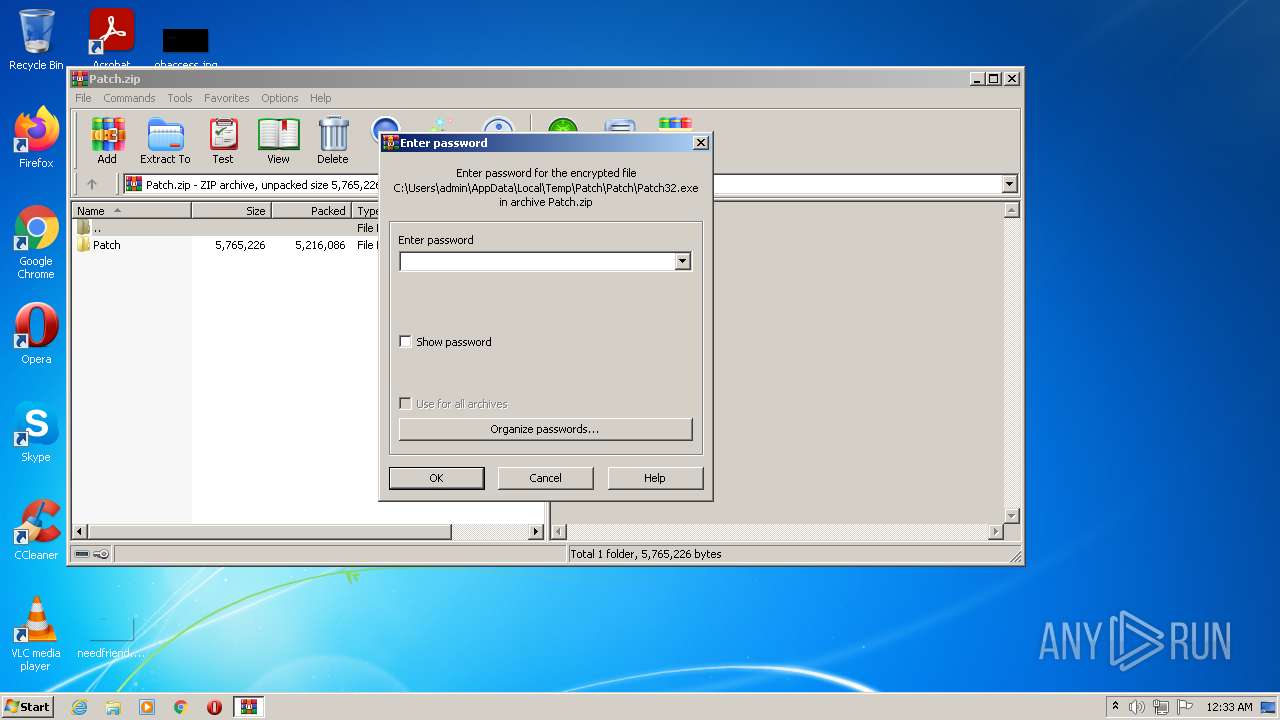
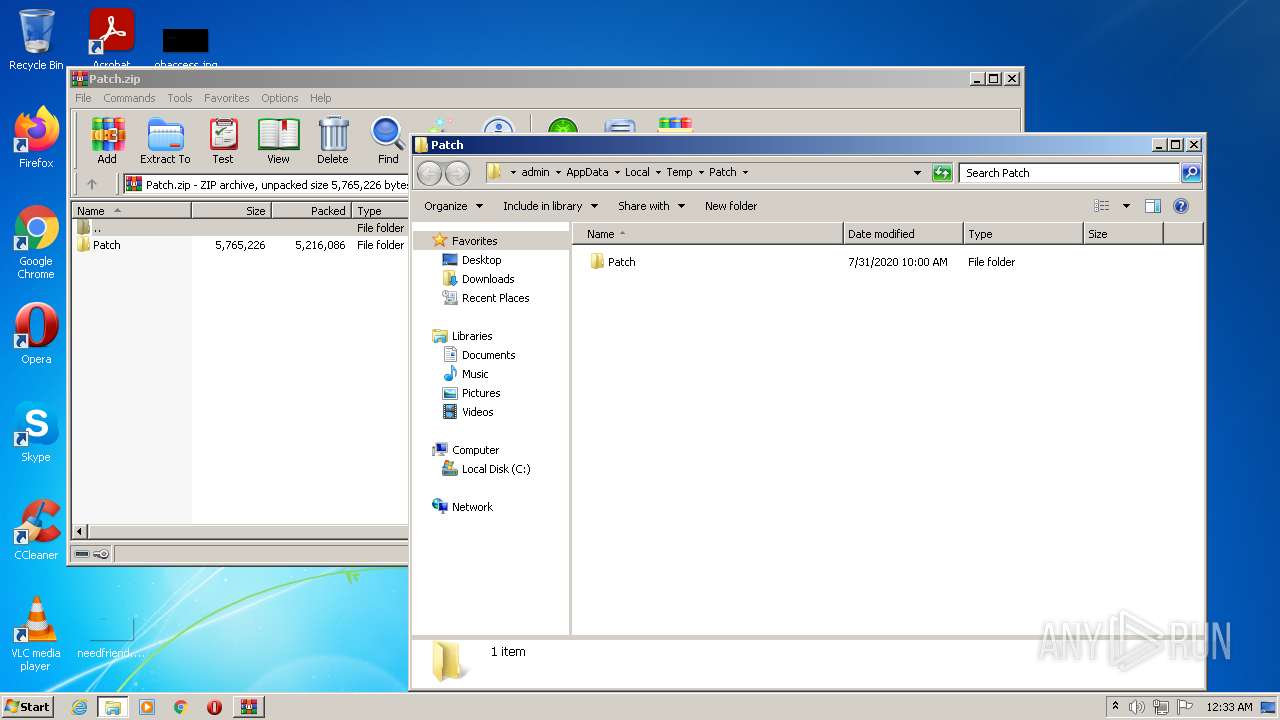
| 3268 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Patch.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3664 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3804 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3804 | "C:\Program Files\Internet Explorer\iexplore.exe" https://crackingpatching.com/ | C:\Program Files\Internet Explorer\iexplore.exe | Patch32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
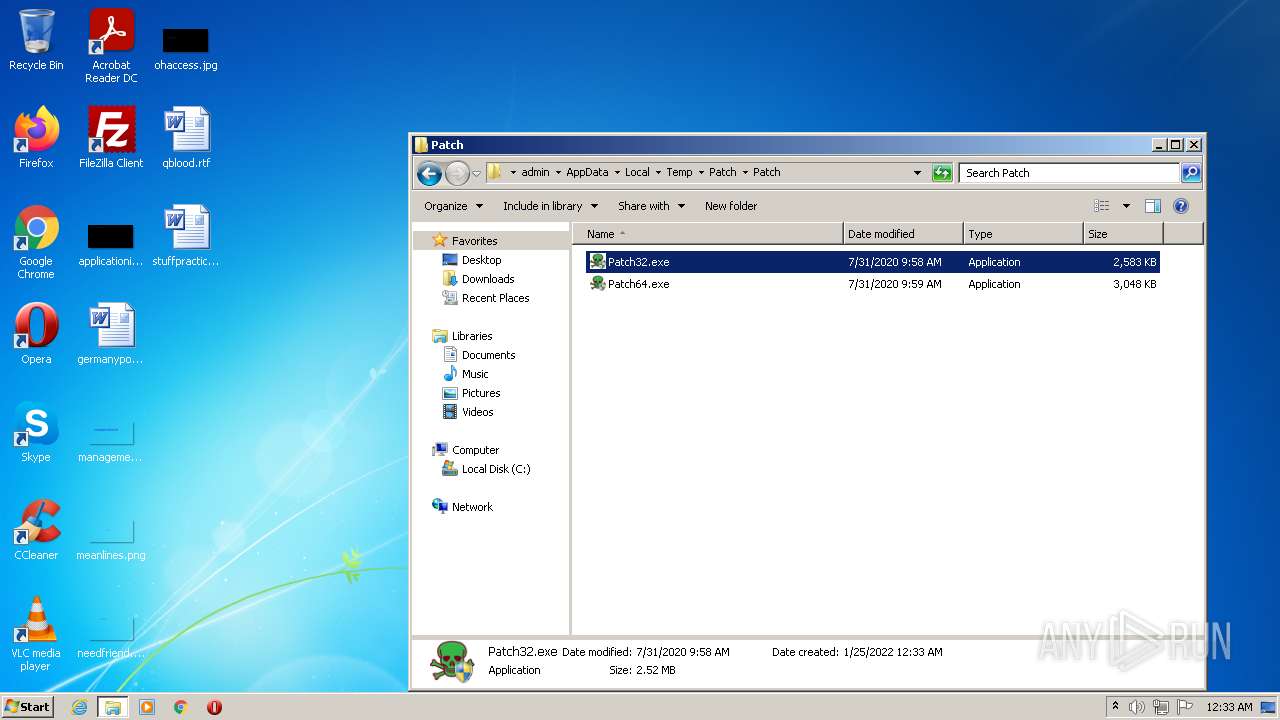
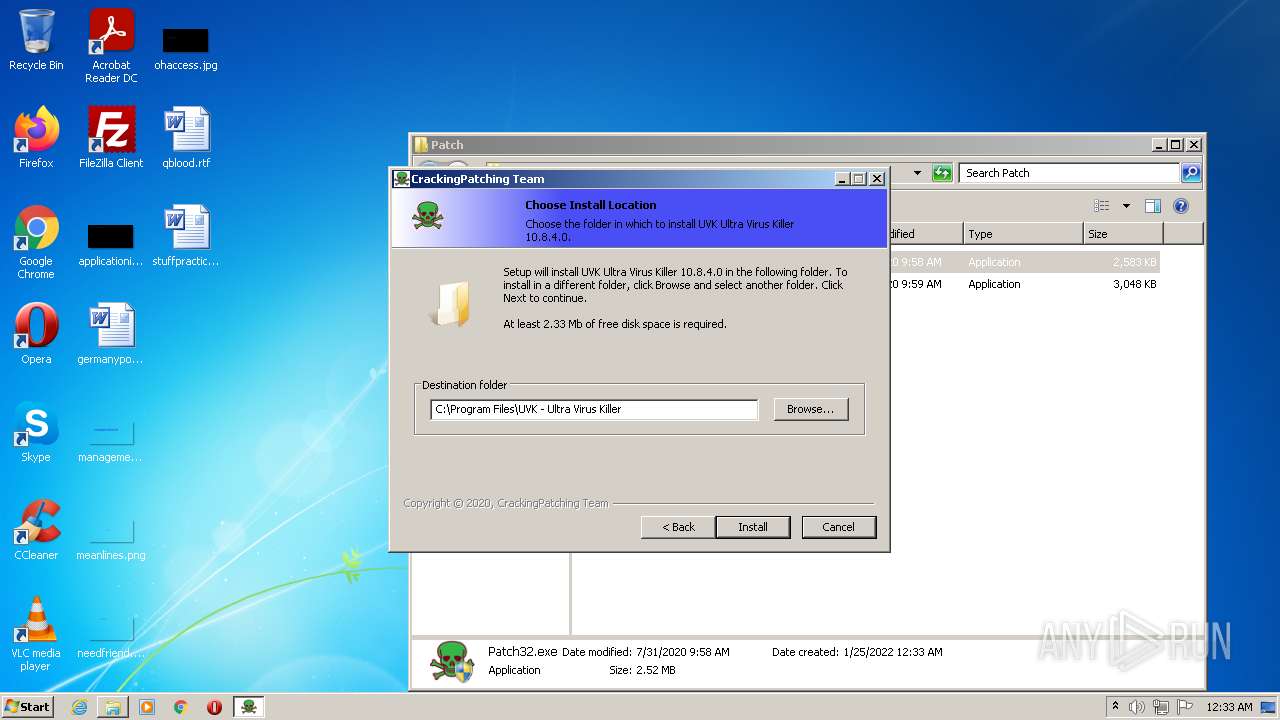
| 3840 | "C:\Users\admin\AppData\Local\Temp\Patch\Patch\Patch32.exe" | C:\Users\admin\AppData\Local\Temp\Patch\Patch\Patch32.exe | Explorer.EXE | ||||||||||||
User: admin Company: Crackingpatching.com Team Integrity Level: HIGH Description: UVK Ultra Virus Killer 10.8.4.0 1.0.0 Installation Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
Total events
32 934
Read events
32 212
Write events
700
Delete events
22
Modification events
| (PID) Process: | (3268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3268) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Patch.zip | |||
| (PID) Process: | (3268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
4
Suspicious files
30
Text files
139
Unknown types
23
Dropped files
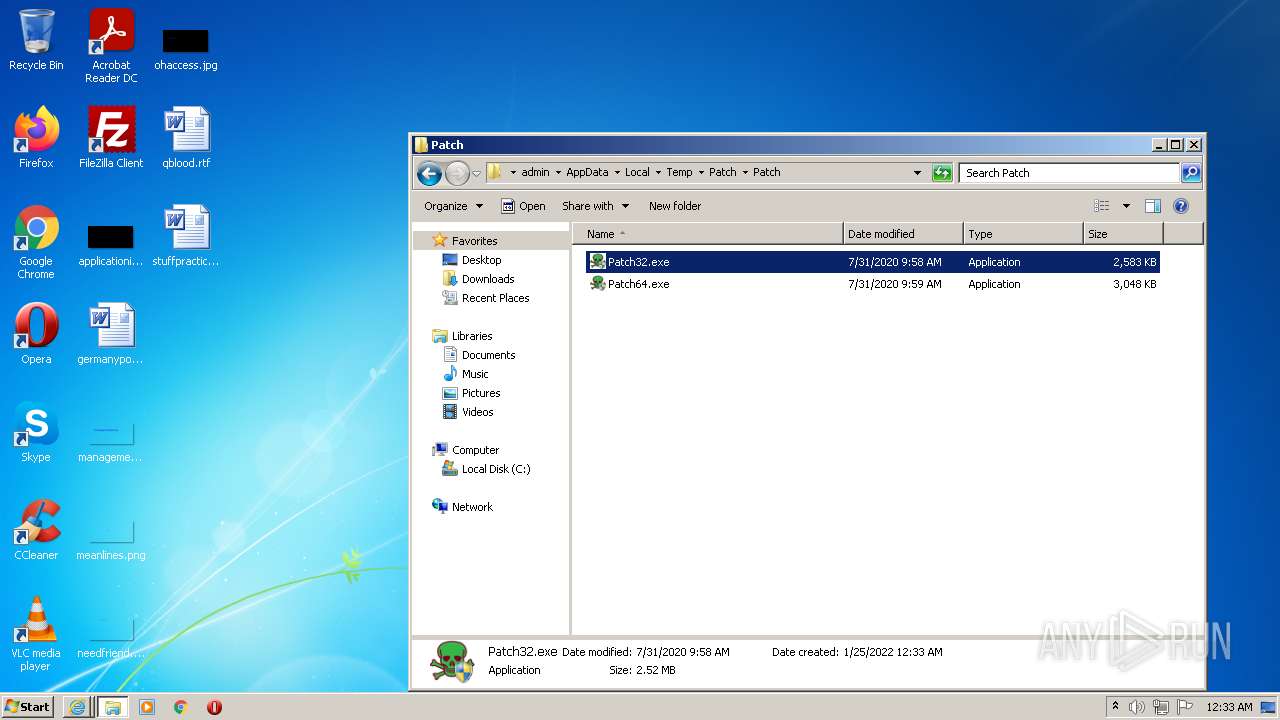
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3840 | Patch32.exe | C:\Users\admin\AppData\Local\Temp\$inst\2.tmp | compressed | |
MD5:— | SHA256:— | |||
| 3268 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Patch\Patch\Patch32.exe | executable | |
MD5:— | SHA256:— | |||
| 3268 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Patch\Patch\Patch64.exe | executable | |
MD5:— | SHA256:— | |||
| 3840 | Patch32.exe | C:\Users\admin\AppData\Local\Temp\$inst\temp_0.tmp | compressed | |
MD5:— | SHA256:— | |||
| 3840 | Patch32.exe | C:\Program Files\Internet Download Manager\UVK Ultra Virus Killer 10.8.4.0 Patch Uninstalle.ini | ini | |
MD5:— | SHA256:— | |||
| 3804 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\High\Active\RecoveryStore.{77339A6B-7D76-11EC-A20C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3840 | Patch32.exe | C:\Program Files\UVK - Ultra Virus Killer\UVK_en.exe | executable | |
MD5:— | SHA256:— | |||
| 2680 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 2680 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\idm-crack-patch[1].htm | html | |
MD5:— | SHA256:— | |||
| 1408 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\High\Active\RecoveryStore.{77313811-7D76-11EC-A20C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
151
DNS requests
58
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1408 | iexplore.exe | GET | 304 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | — | — | whitelisted |
2680 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
2680 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
2680 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
2680 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEA85iIsHH624nUw0F8EXTag%3D | US | der | 471 b | whitelisted |
3664 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.68 Kb | whitelisted |
3664 | iexplore.exe | GET | 200 | 216.58.214.3:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
2680 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3664 | iexplore.exe | GET | 200 | 216.58.214.3:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEEFKxQHtEPcBCgAAAAErfHU%3D | US | der | 471 b | whitelisted |
3664 | iexplore.exe | GET | 200 | 216.58.214.3:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQD0HrJV5UaPhAoAAAABK4HO | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2680 | iexplore.exe | 192.0.77.2:443 | i2.wp.com | Automattic, Inc | US | suspicious |
2680 | iexplore.exe | 157.240.214.11:443 | connect.facebook.net | — | US | unknown |
2680 | iexplore.exe | 142.250.179.142:443 | apis.google.com | Google Inc. | US | whitelisted |
2680 | iexplore.exe | 199.232.148.157:443 | platform.twitter.com | — | US | unknown |
2680 | iexplore.exe | 192.0.76.3:443 | stats.wp.com | Automattic, Inc | US | suspicious |
2680 | iexplore.exe | 104.18.30.182:80 | ocsp.comodoca.com | Cloudflare Inc | US | suspicious |
1408 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2680 | iexplore.exe | 104.18.31.182:80 | ocsp.comodoca.com | Cloudflare Inc | US | unknown |
3804 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2680 | iexplore.exe | 216.58.208.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crackingpatching.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
c0.wp.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
i2.wp.com |
| whitelisted |
i1.wp.com |
| whitelisted |