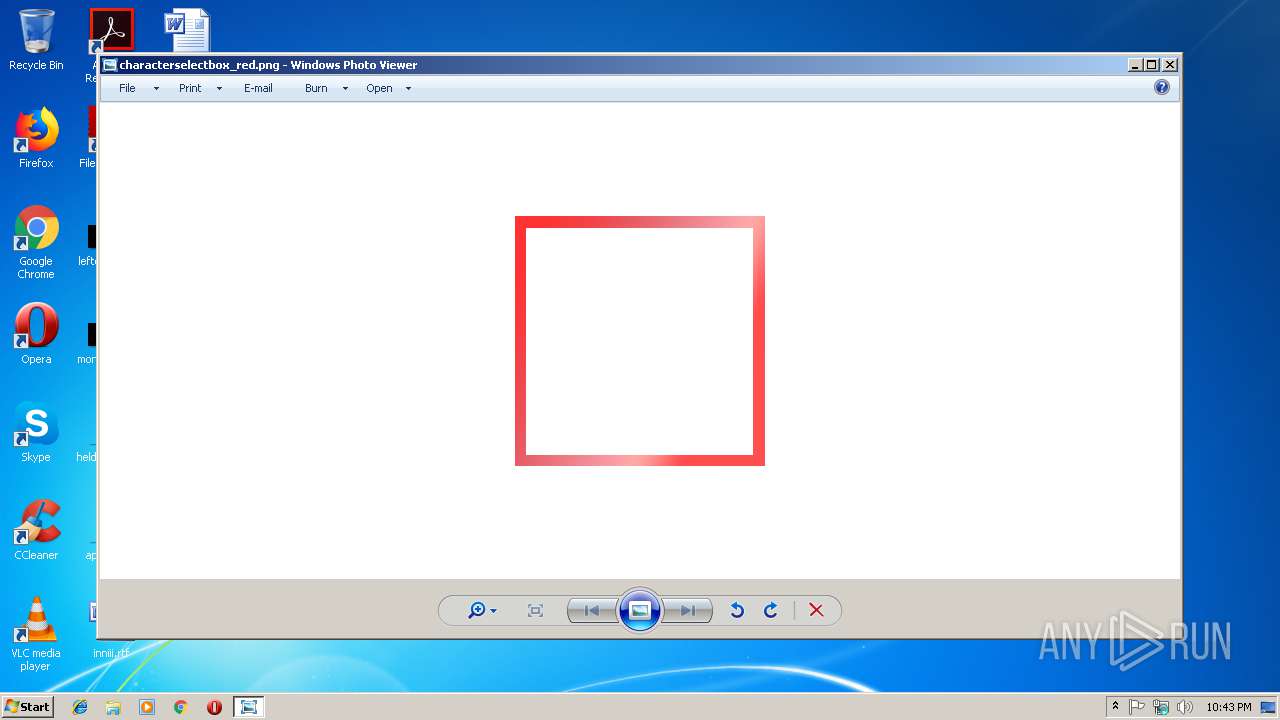
| File name: | characterselectbox_red.png |
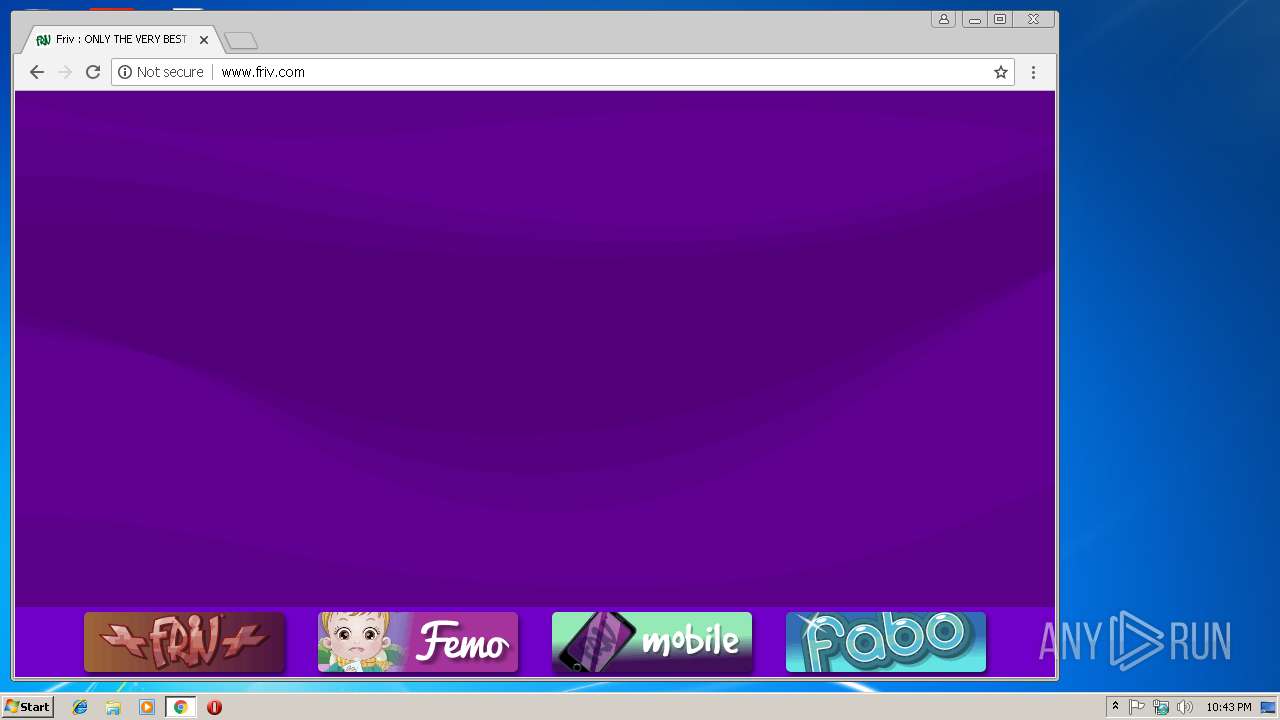
| Full analysis: | https://app.any.run/tasks/02cf6e27-a39e-414d-84c4-33e2d135be2a |
| Verdict: | No threats detected |
| Analysis date: | March 10, 2019, 22:42:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | image/png |
| File info: | PNG image data, 250 x 250, 8-bit/color RGBA, non-interlaced |
| MD5: | C4A5ADBD94CCF37F523F817EDA9ED5EF |
| SHA1: | 18622DFE71AB08781BF3EFDA8682BE56047C0EE3 |
| SHA256: | BD4E61B27EAC5BBFFD78EF8B65649523BAA56E356791377CC87800FE1EAA9A23 |
| SSDEEP: | 192:NS0tKg9E05TvAT4Sa0P2ua1E5E7l3re+14hWt7QtVW5Z4La/1RwneJXv4y6asJHN:LXE05Qa0+uYE5uRfovr+DweJ/4Ostt |
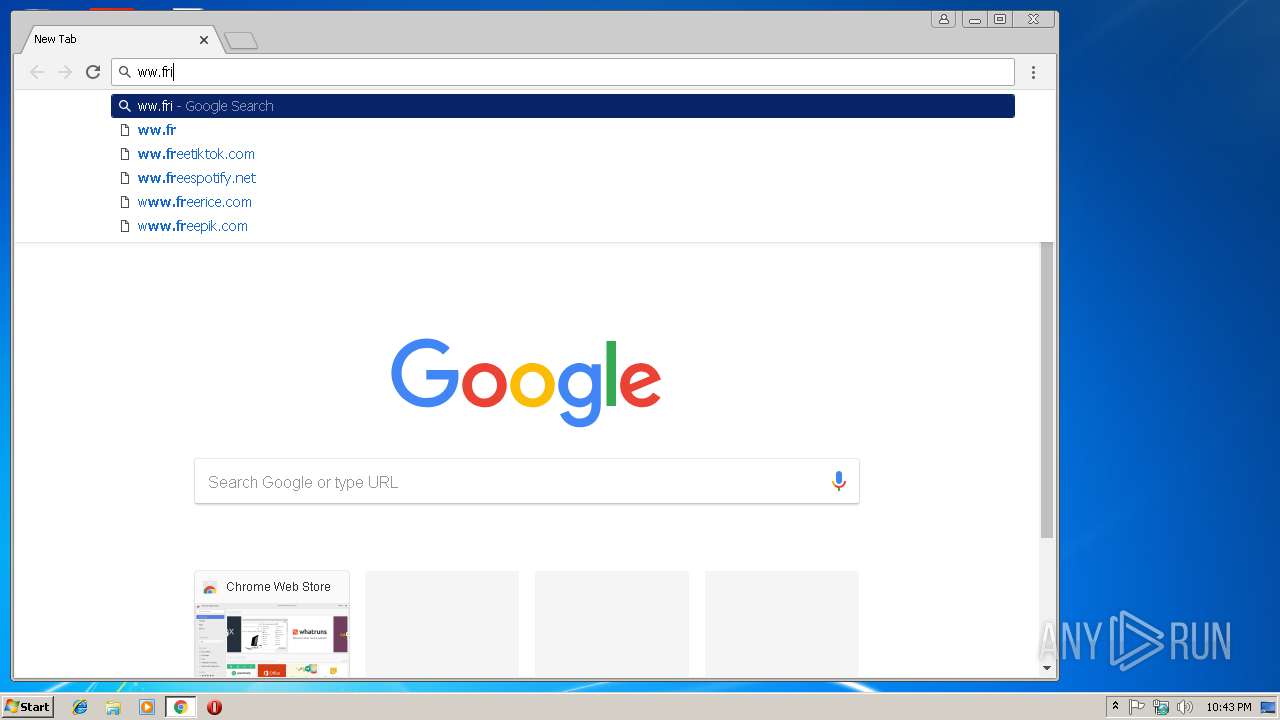
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 3388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .png | | | Portable Network Graphics (100) |
|---|
EXIF
PNG
| ImageWidth: | 250 |
|---|---|
| ImageHeight: | 250 |
| BitDepth: | 8 |
| ColorType: | RGB with Alpha |
| Compression: | Deflate/Inflate |
| Filter: | Adaptive |
| Interlace: | Noninterlaced |
| PixelsPerUnitX: | 11811 |
| PixelsPerUnitY: | 11811 |
| PixelUnits: | meters |
| ProfileName: | Photoshop ICC profile |
| WhitePointX: | 0.31269 |
| WhitePointY: | 0.32899 |
| RedX: | 0.63999 |
| RedY: | 0.33001 |
| GreenX: | 0.3 |
| GreenY: | 0.6 |
| BlueX: | 0.15 |
| BlueY: | 0.05999 |
ICC_Profile
| ProfileCMMType: | Lino |
|---|---|
| ProfileVersion: | 2.1.0 |
| ProfileClass: | Display Device Profile |
| ColorSpaceData: | RGB |
| ProfileConnectionSpace: | XYZ |
| ProfileDateTime: | 1998:02:09 06:49:00 |
| ProfileFileSignature: | acsp |
| PrimaryPlatform: | Microsoft Corporation |
| CMMFlags: | Not Embedded, Independent |
| DeviceManufacturer: | IEC |
| DeviceModel: | sRGB |
| DeviceAttributes: | Reflective, Glossy, Positive, Color |
| RenderingIntent: | Media-Relative Colorimetric |
| ConnectionSpaceIlluminant: | 0.9642 1 0.82491 |
| ProfileCreator: | HP |
| ProfileID: | - |
| ProfileCopyright: | Copyright (c) 1998 Hewlett-Packard Company |
| ProfileDescription: | sRGB IEC61966-2.1 |
| MediaWhitePoint: | 0.95045 1 1.08905 |
| MediaBlackPoint: | 0 0 0 |
| RedMatrixColumn: | 0.43607 0.22249 0.01392 |
| GreenMatrixColumn: | 0.38515 0.71687 0.09708 |
| BlueMatrixColumn: | 0.14307 0.06061 0.7141 |
| DeviceMfgDesc: | IEC http://www.iec.ch |
| DeviceModelDesc: | IEC 61966-2.1 Default RGB colour space - sRGB |
| ViewingCondDesc: | Reference Viewing Condition in IEC61966-2.1 |
| ViewingCondIlluminant: | 19.6445 20.3718 16.8089 |
| ViewingCondSurround: | 3.92889 4.07439 3.36179 |
| ViewingCondIlluminantType: | D50 |
| Luminance: | 76.03647 80 87.12462 |
| MeasurementObserver: | CIE 1931 |
| MeasurementBacking: | 0 0 0 |
| MeasurementGeometry: | Unknown |
| MeasurementFlare: | 0.999% |
| MeasurementIlluminant: | D65 |
| Technology: | Cathode Ray Tube Display |
| RedTRC: | (Binary data 2060 bytes, use -b option to extract) |
| GreenTRC: | (Binary data 2060 bytes, use -b option to extract) |
| BlueTRC: | (Binary data 2060 bytes, use -b option to extract) |
Composite
| ImageSize: | 250x250 |
|---|---|
| Megapixels: | 0.062 |
Total processes
43
Monitored processes
14
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=936,12190147897766461488,17008527792136362475,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=94D7482B4F76274FB40F35B6A73A0074 --mojo-platform-channel-handle=3864 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f6000b0,0x6f6000c0,0x6f6000cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=936,12190147897766461488,17008527792136362475,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3889326AB7F25256F2D6FEB8E8019BB5 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3889326AB7F25256F2D6FEB8E8019BB5 --renderer-client-id=6 --mojo-platform-channel-handle=3572 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=936,12190147897766461488,17008527792136362475,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=63E7D68B4CFF1982E3F90E719D2ED0E6 --mojo-platform-channel-handle=908 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2692 | "C:\Windows\System32\rundll32.exe" "C:\Program Files\Windows Photo Viewer\PhotoViewer.dll", ImageView_Fullscreen C:\Users\admin\AppData\Local\Temp\characterselectbox_red.png | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=936,12190147897766461488,17008527792136362475,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=9B38B3DEDED450C77DF69C6FAE25F263 --mojo-platform-channel-handle=3716 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=936,12190147897766461488,17008527792136362475,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=38F236D2DDD001B18EB7DB979E6FE1F0 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=38F236D2DDD001B18EB7DB979E6FE1F0 --renderer-client-id=9 --mojo-platform-channel-handle=2156 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3396 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=936,12190147897766461488,17008527792136362475,131072 --enable-features=PasswordImport --service-pipe-token=13A5E91F5EEA5000D4D43B5A81B76B6F --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13A5E91F5EEA5000D4D43B5A81B76B6F --renderer-client-id=3 --mojo-platform-channel-handle=2120 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
533
Read events
489
Write events
41
Delete events
3
Modification events
| (PID) Process: | (2692) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: rundll32.exe | |||
| (PID) Process: | (2692) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Photo Viewer\Viewer |
| Operation: | write | Name: | MainWndPos |
Value: 6000000034000000A00400008002000000000000 | |||
| (PID) Process: | (3388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3388-13196731386735500 |
Value: 259 | |||
| (PID) Process: | (3388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3388) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
65
Text files
79
Unknown types
46
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5d34cf39-7c71-4349-a1c9-4b180d7c6351.tmp | — | |
MD5:— | SHA256:— | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\266d8d2a-76ce-4bdf-bccd-c215592eefce.tmp | — | |
MD5:— | SHA256:— | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\e6622492fa163609ddd4212f54512baa07929ed3\caecb3bd-7969-4305-84d6-3a376453ec73\index-dir\temp-index | — | |
MD5:— | SHA256:— | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF19a435.TMP | text | |
MD5:— | SHA256:— | |||
| 3388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
33
DNS requests
19
Threats
1
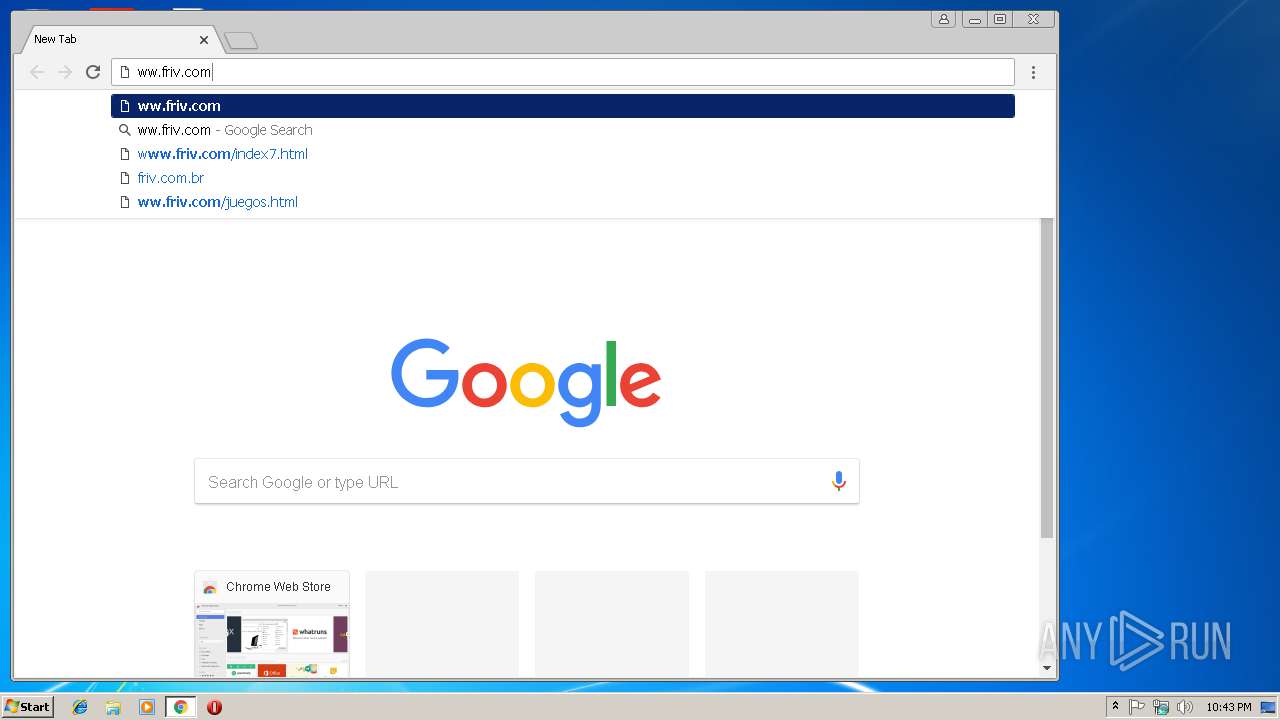
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
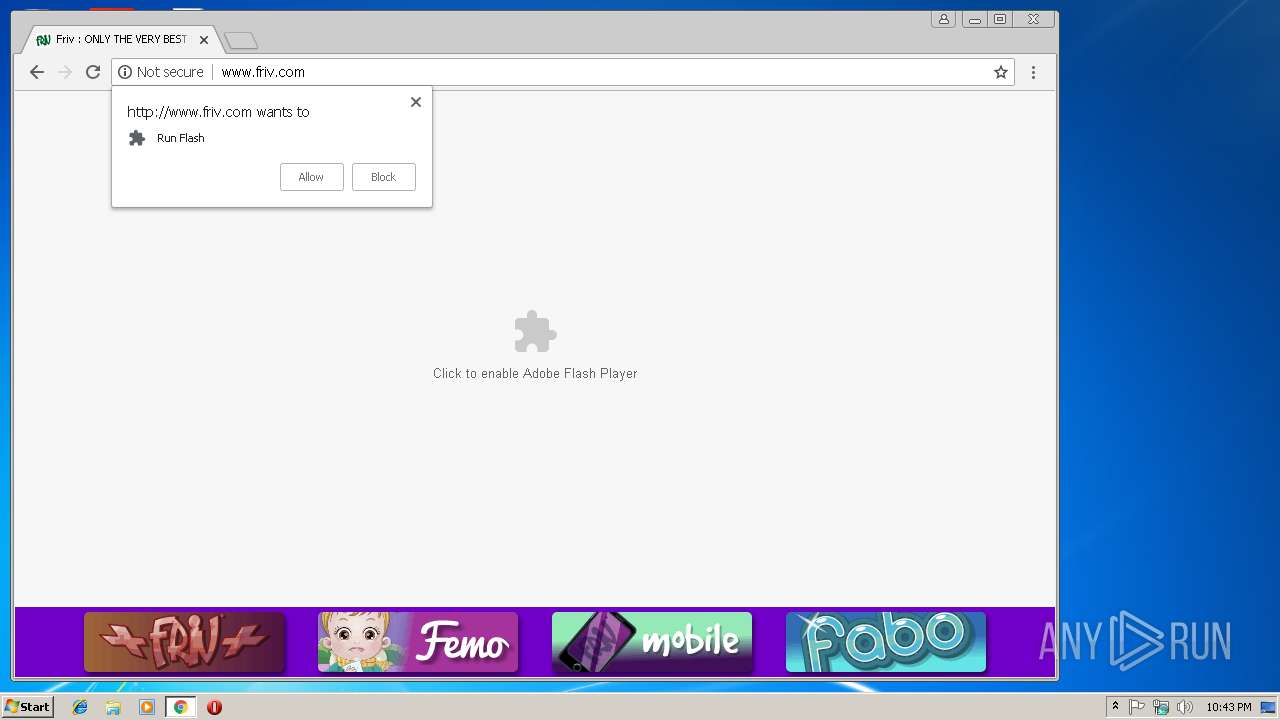
3388 | chrome.exe | GET | 307 | 67.202.94.93:80 | http://whos.amung.us/widget/eo13ecc3rv14/ | US | — | — | whitelisted |
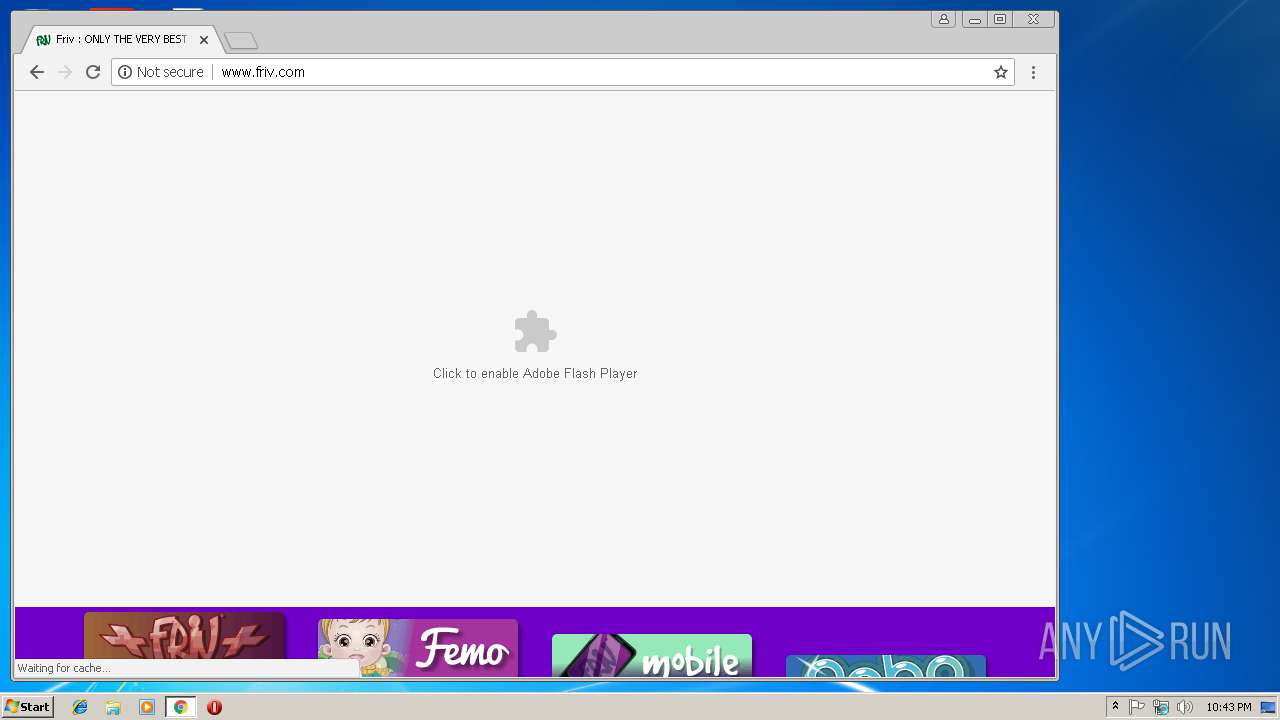
3388 | chrome.exe | GET | 200 | 75.126.39.117:80 | http://www.friv.com/menu/start.html?it=normal | US | html | 2.73 Kb | suspicious |
3388 | chrome.exe | GET | 200 | 75.126.39.117:80 | http://www.friv.com/menu/friv.js | US | text | 9.73 Kb | suspicious |
3388 | chrome.exe | GET | 200 | 75.126.39.117:80 | http://www.friv.com/menu/zeropage.html?it=normal | US | html | 1.29 Kb | suspicious |
3388 | chrome.exe | GET | 200 | 75.126.39.117:80 | http://www.friv.com/assets/gfx/bb/bbFrivPlusMin.png | US | image | 4.49 Kb | suspicious |
3388 | chrome.exe | GET | 302 | 192.64.119.83:80 | http://ww.friv.com/ | US | html | 43 b | malicious |
3388 | chrome.exe | GET | 200 | 75.126.39.117:80 | http://www.friv.com/assets/gfx/bb/bbFaboMin.png | US | image | 4.98 Kb | suspicious |
3388 | chrome.exe | GET | 200 | 75.126.39.117:80 | http://www.friv.com/favicon.ico | US | image | 3.55 Kb | suspicious |
3388 | chrome.exe | GET | 200 | 75.126.39.117:80 | http://www.friv.com/ | US | html | 1.12 Kb | suspicious |
3388 | chrome.exe | GET | 200 | 75.126.39.117:80 | http://www.friv.com/assets/gfx/bb/bbFemoBHGSMin.png | US | image | 4.39 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3388 | chrome.exe | 172.217.16.163:443 | www.google.de | Google Inc. | US | whitelisted |
3388 | chrome.exe | 216.58.205.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3388 | chrome.exe | 216.58.210.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3388 | chrome.exe | 64.233.184.94:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3388 | chrome.exe | 192.64.119.83:80 | ww.friv.com | Namecheap, Inc. | US | malicious |
3388 | chrome.exe | 172.217.16.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3388 | chrome.exe | 75.126.39.117:80 | www.friv.com | SoftLayer Technologies Inc. | US | suspicious |
3388 | chrome.exe | 31.13.90.6:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
3388 | chrome.exe | 31.13.90.36:443 | www.facebook.com | Facebook, Inc. | IE | whitelisted |
3388 | chrome.exe | 185.225.208.133:80 | widgets.amung.us | — | — | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.de |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.nl |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
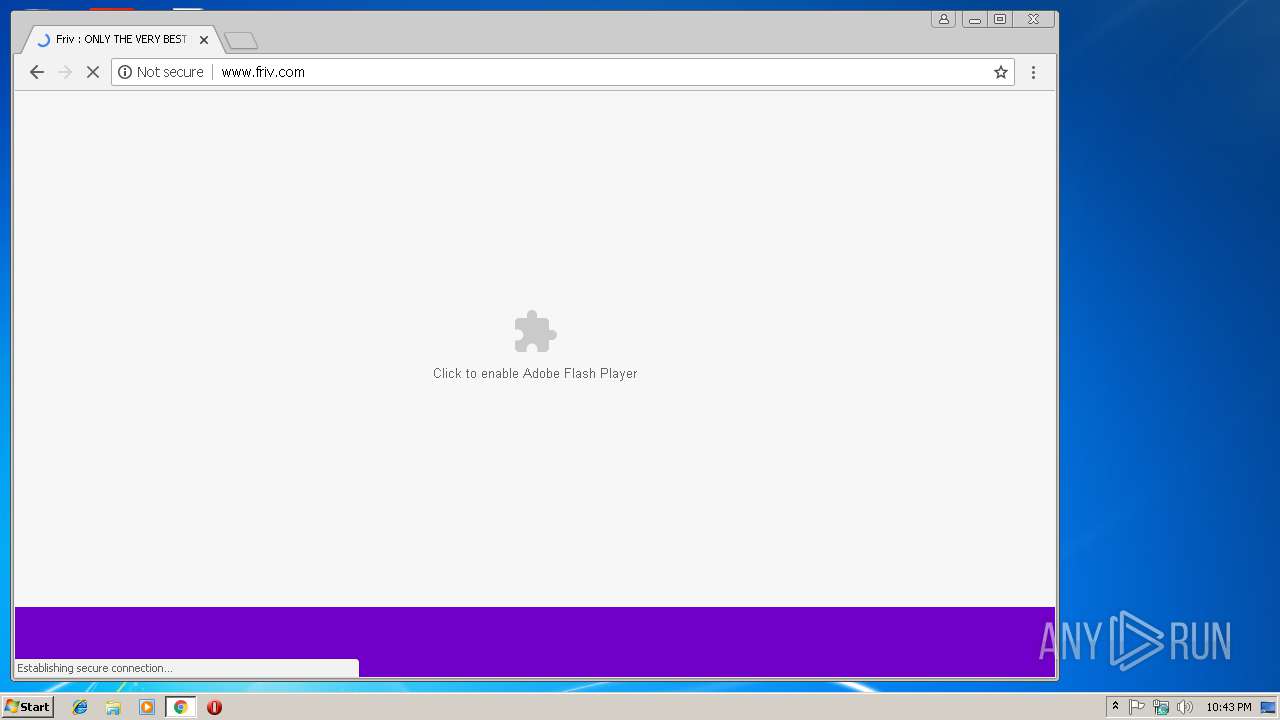
Threats
PID | Process | Class | Message |
|---|---|---|---|
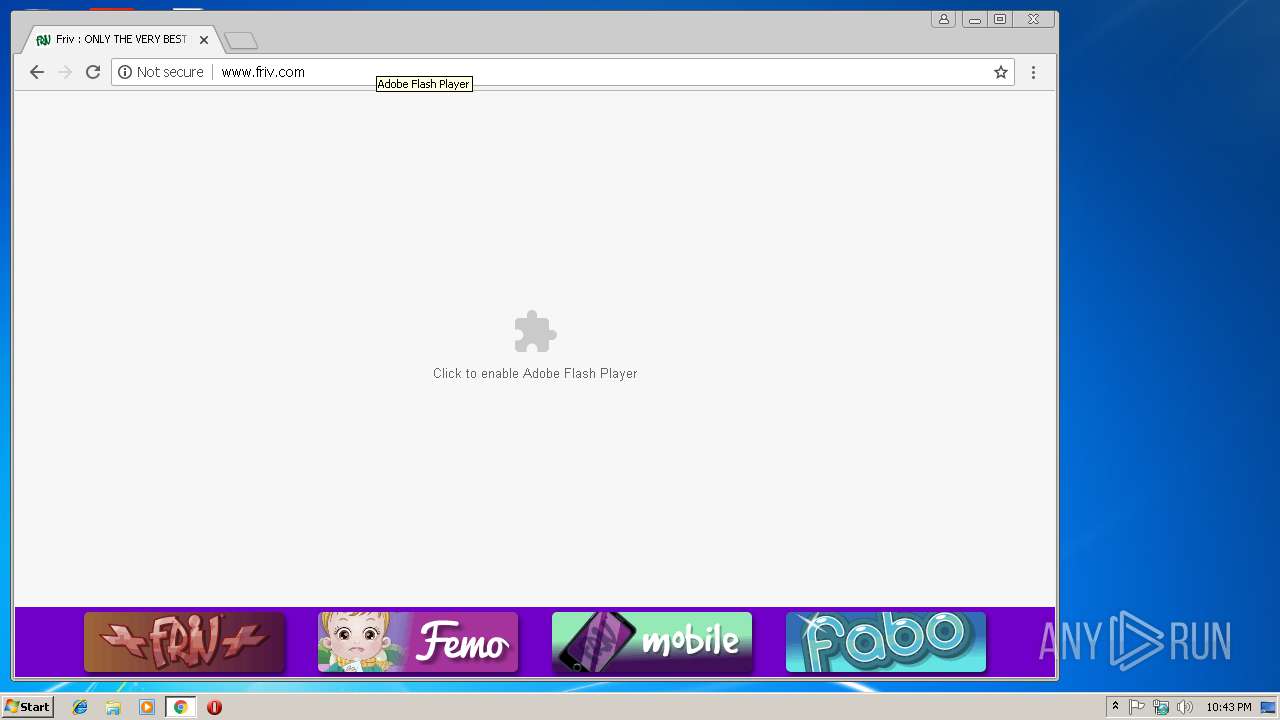
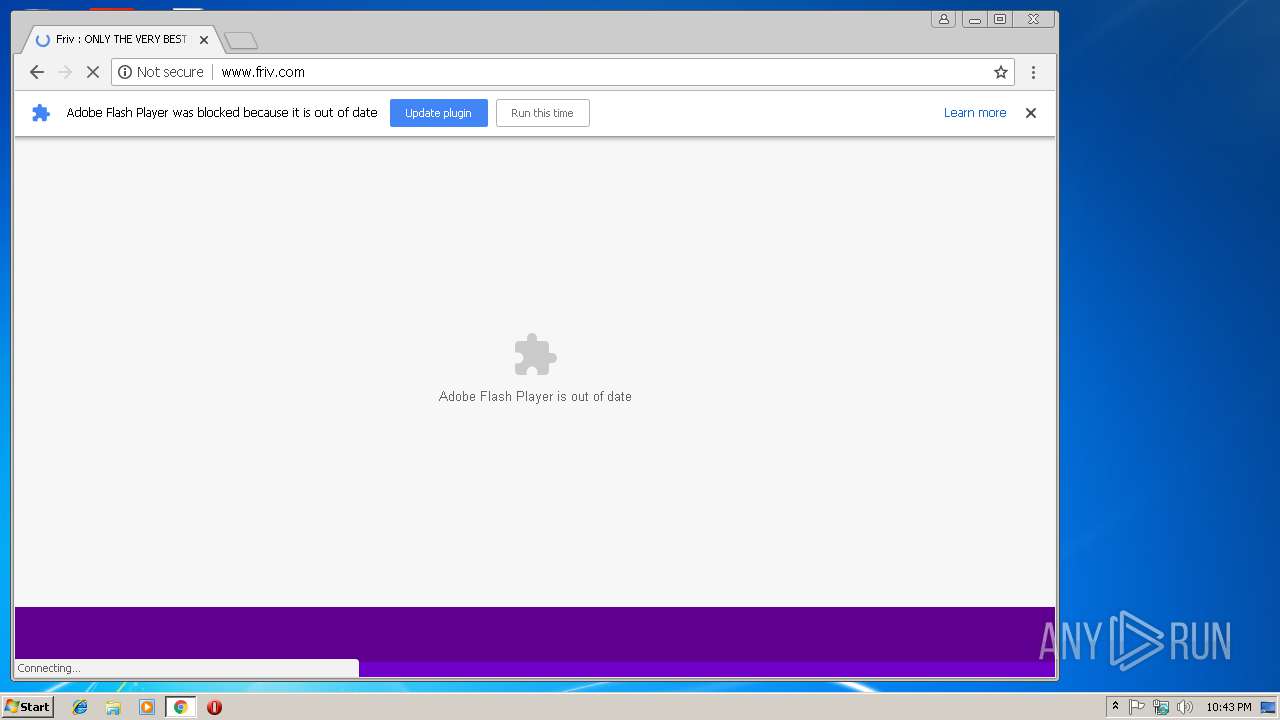
3388 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Outdated Flash Version M2 |