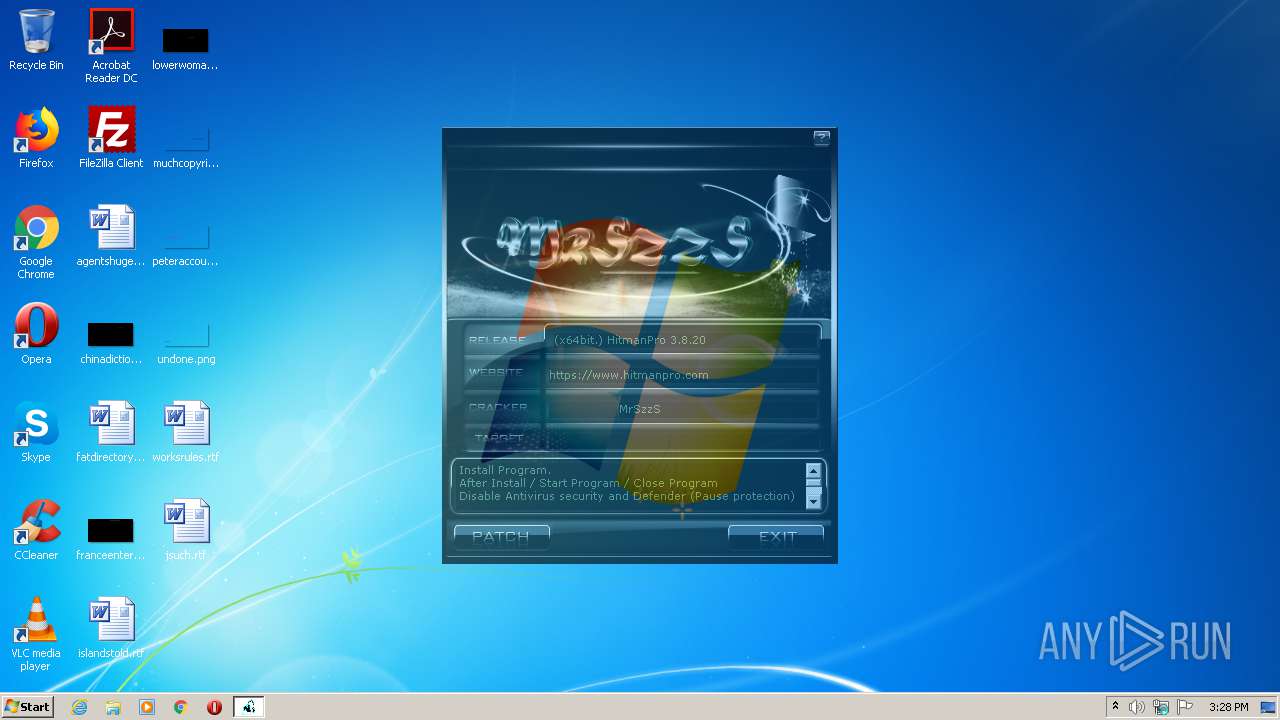
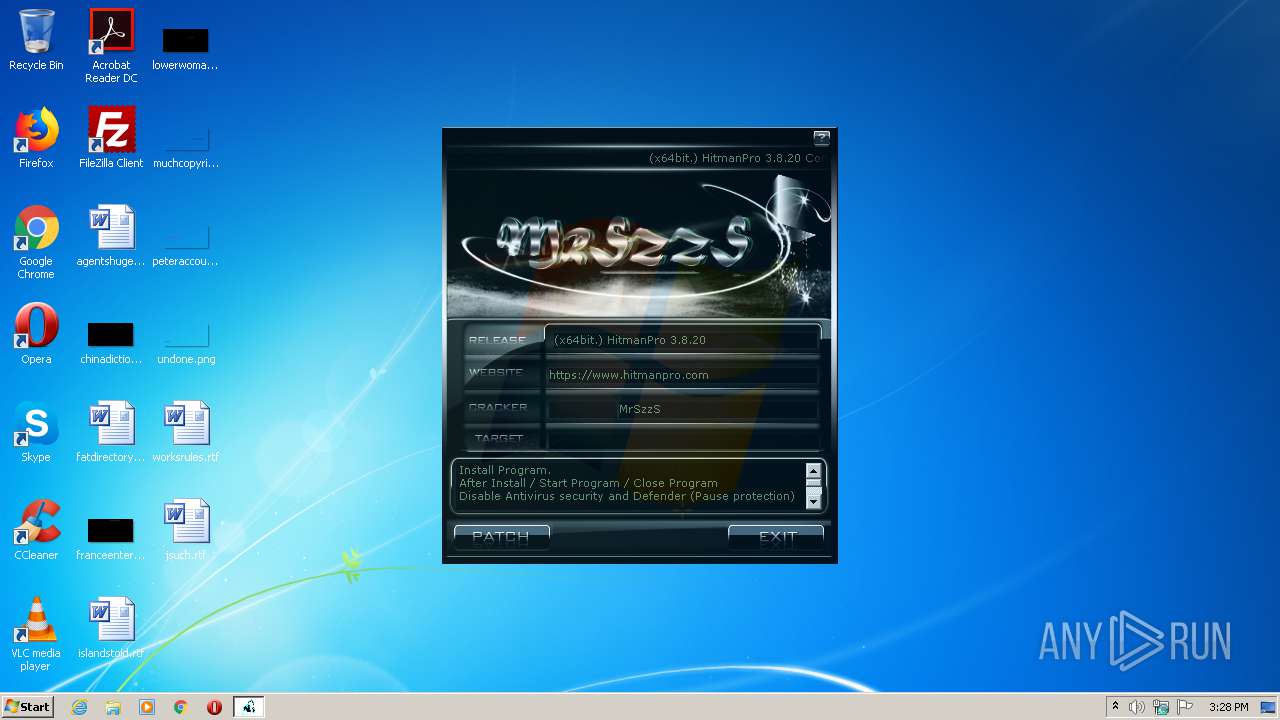
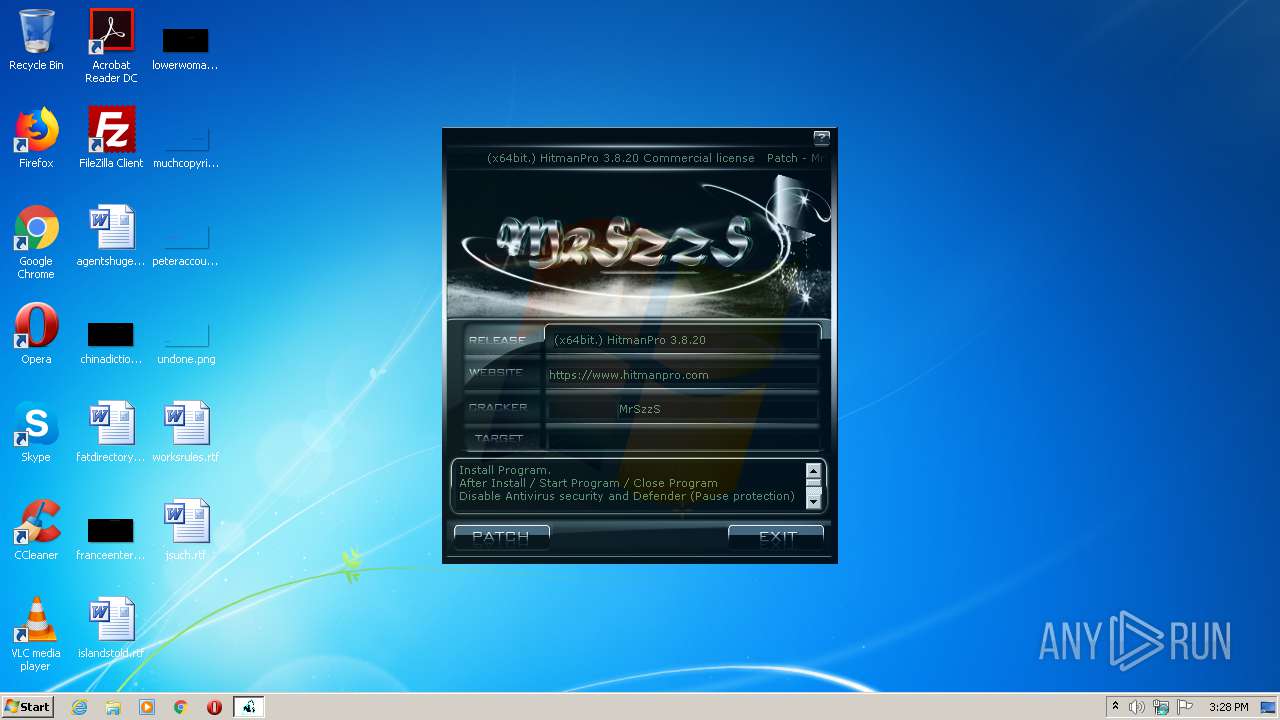
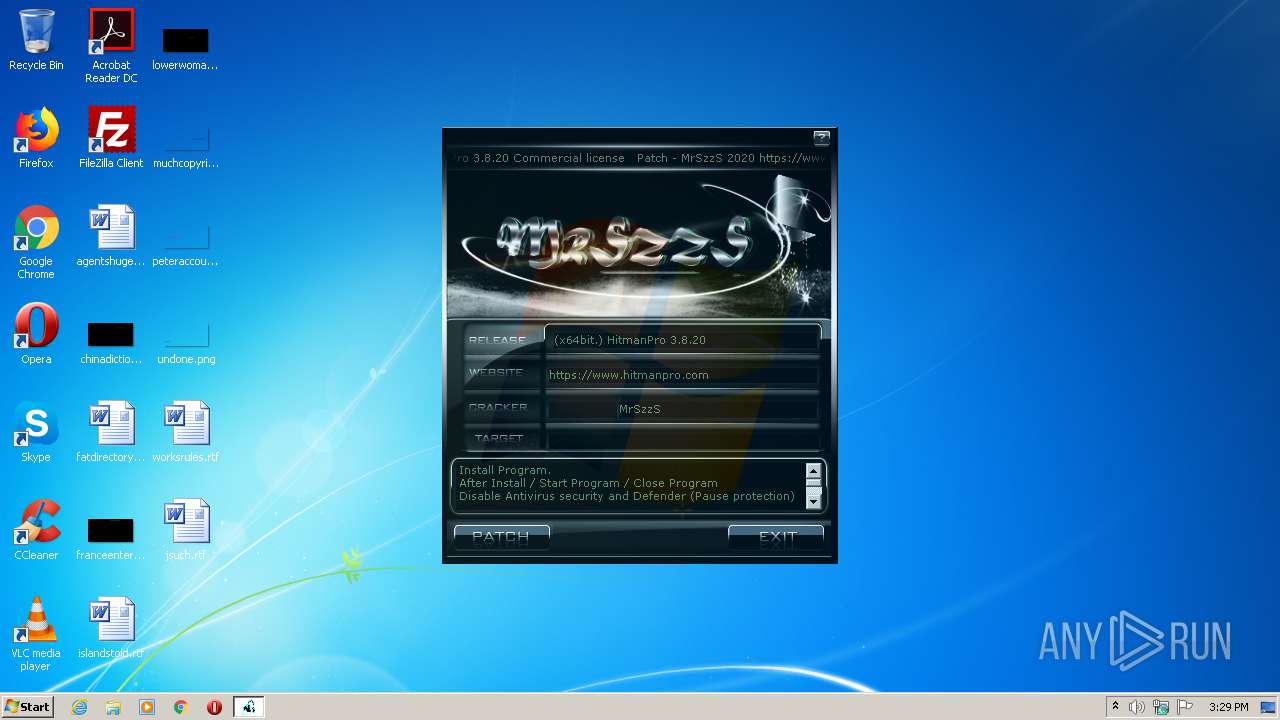
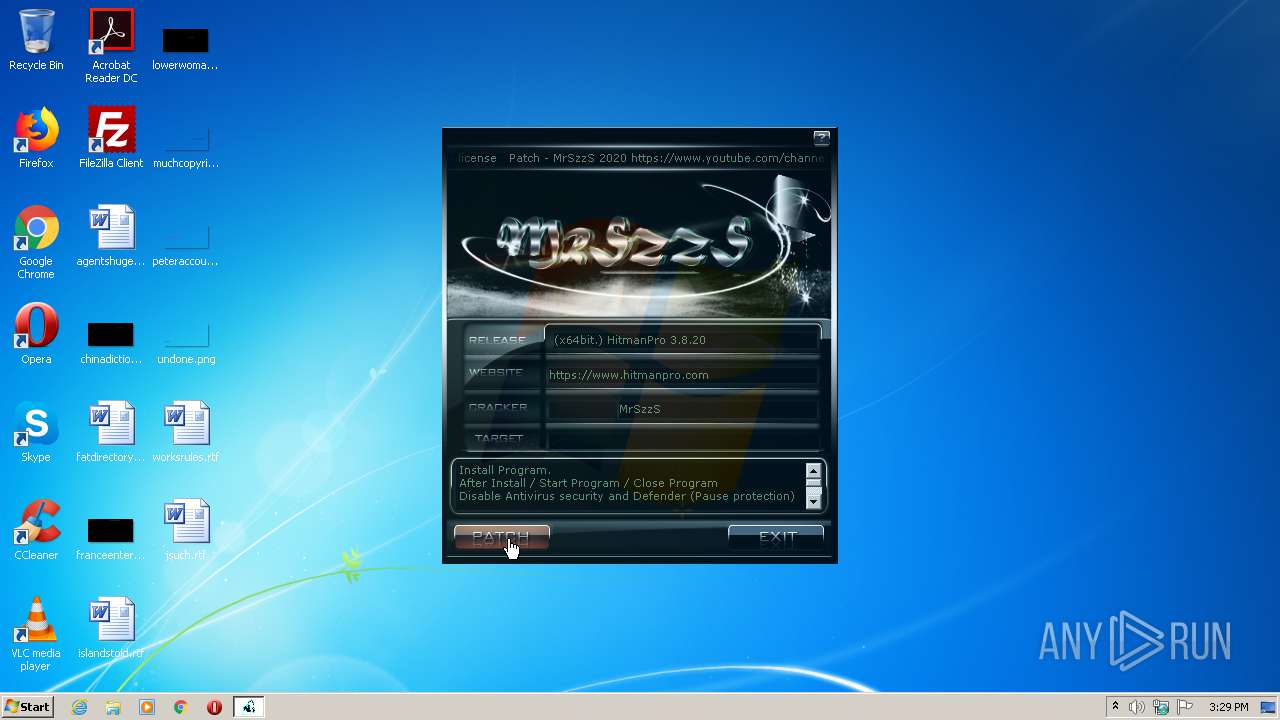
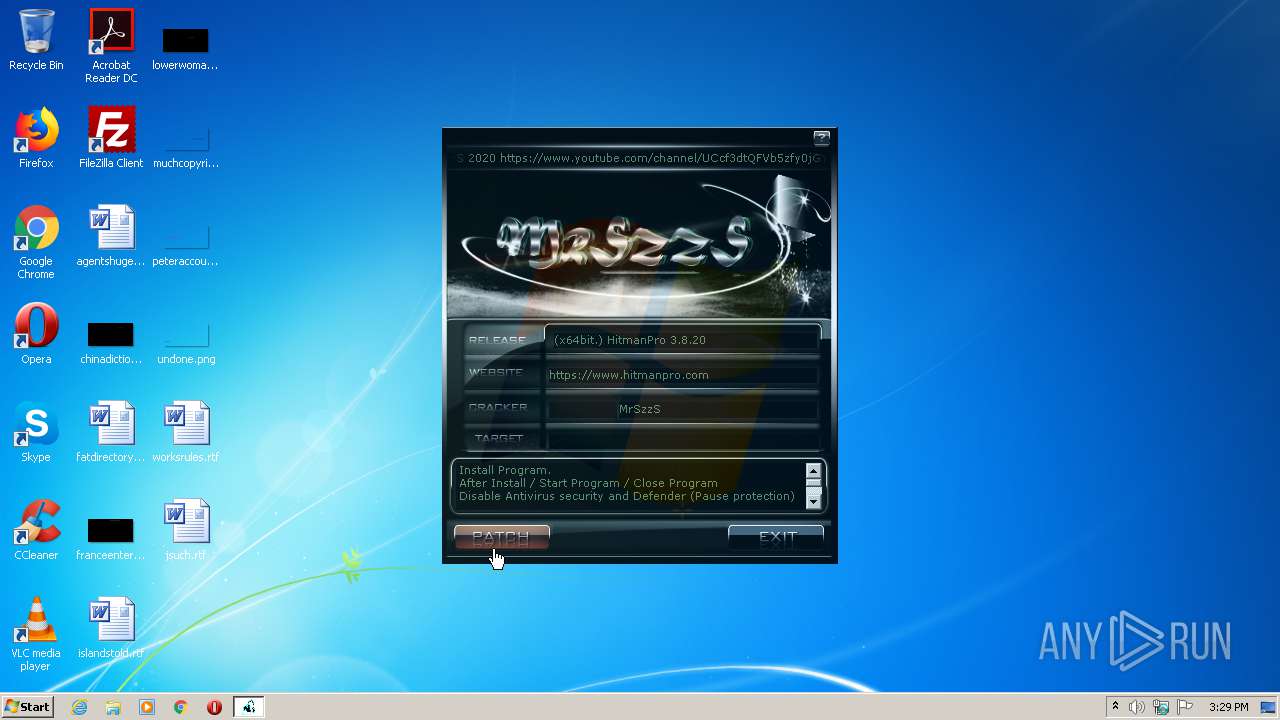
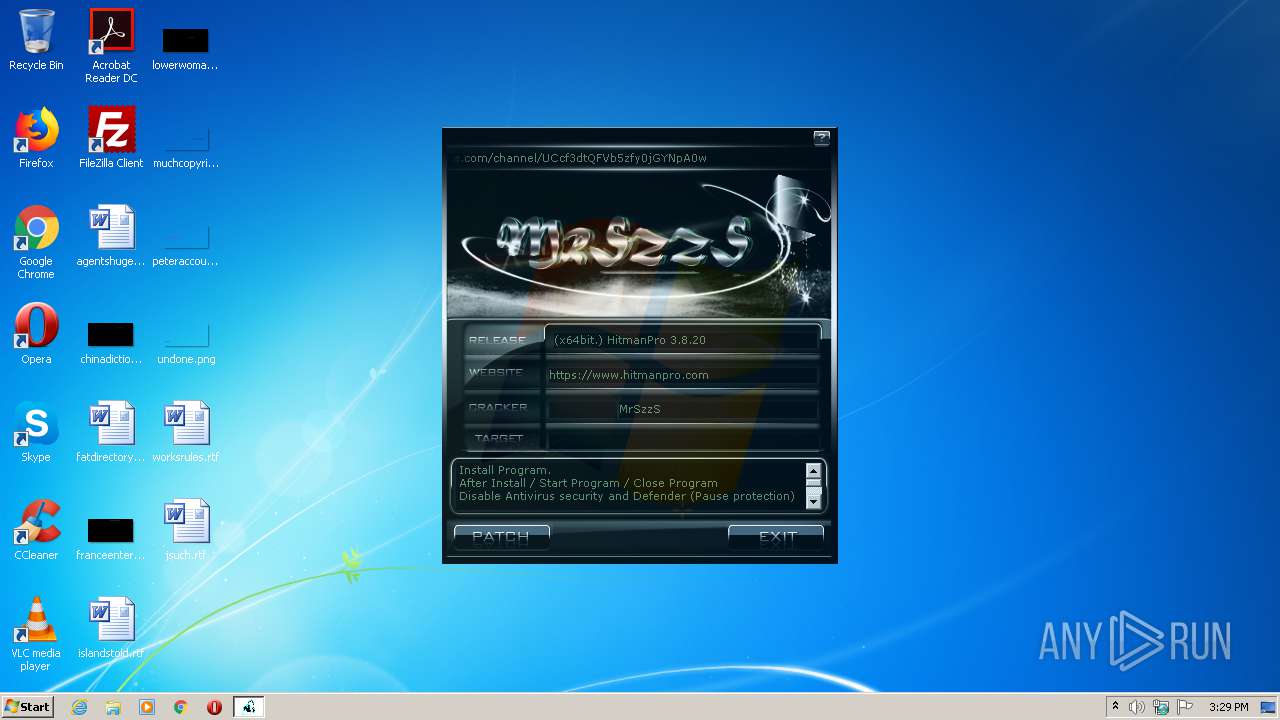
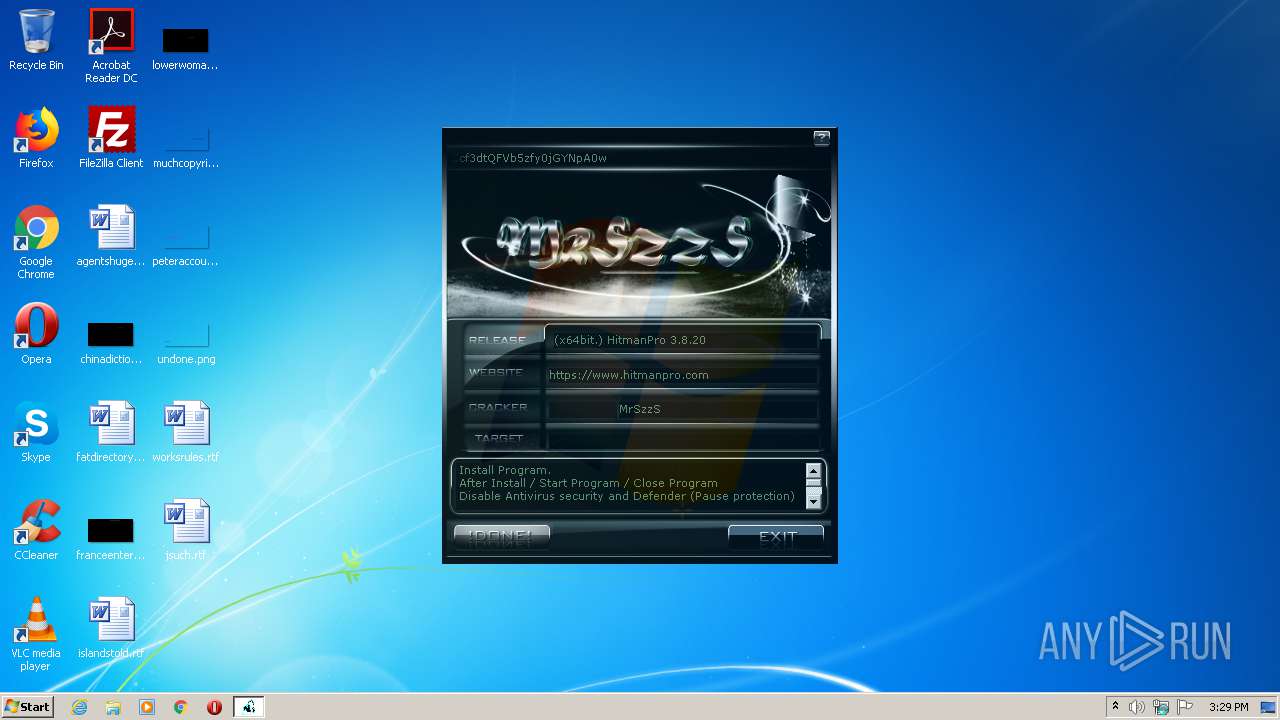
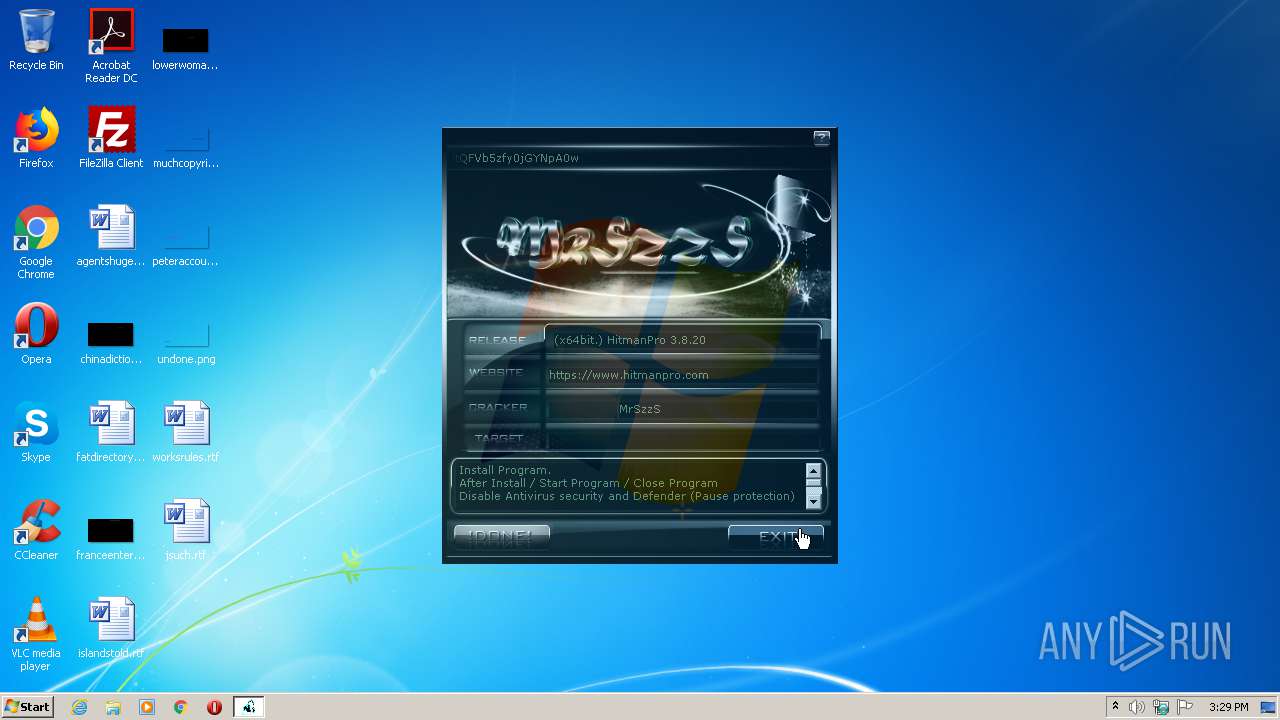
| File name: | (x64bit.).hitmanpro.3.8.20-patch.exe |
| Full analysis: | https://app.any.run/tasks/8d08d32d-33d8-4c41-b9dc-e2a3954e44e5 |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 14:28:22 |
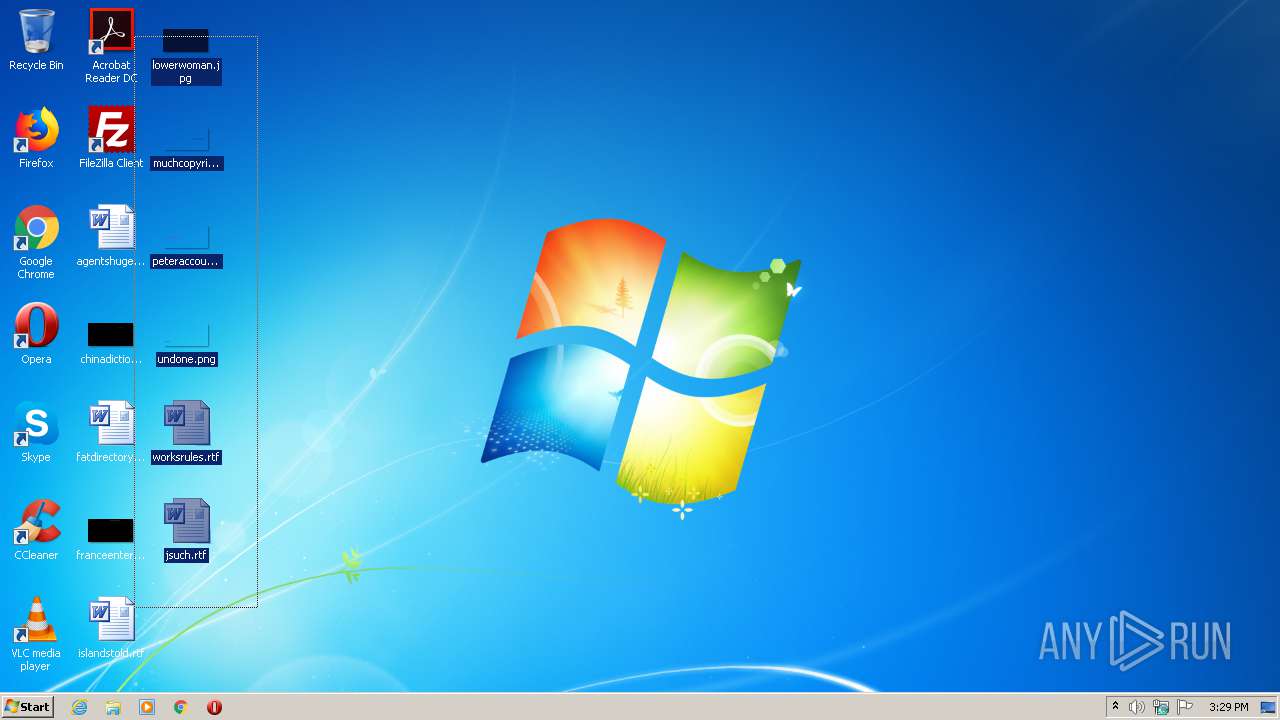
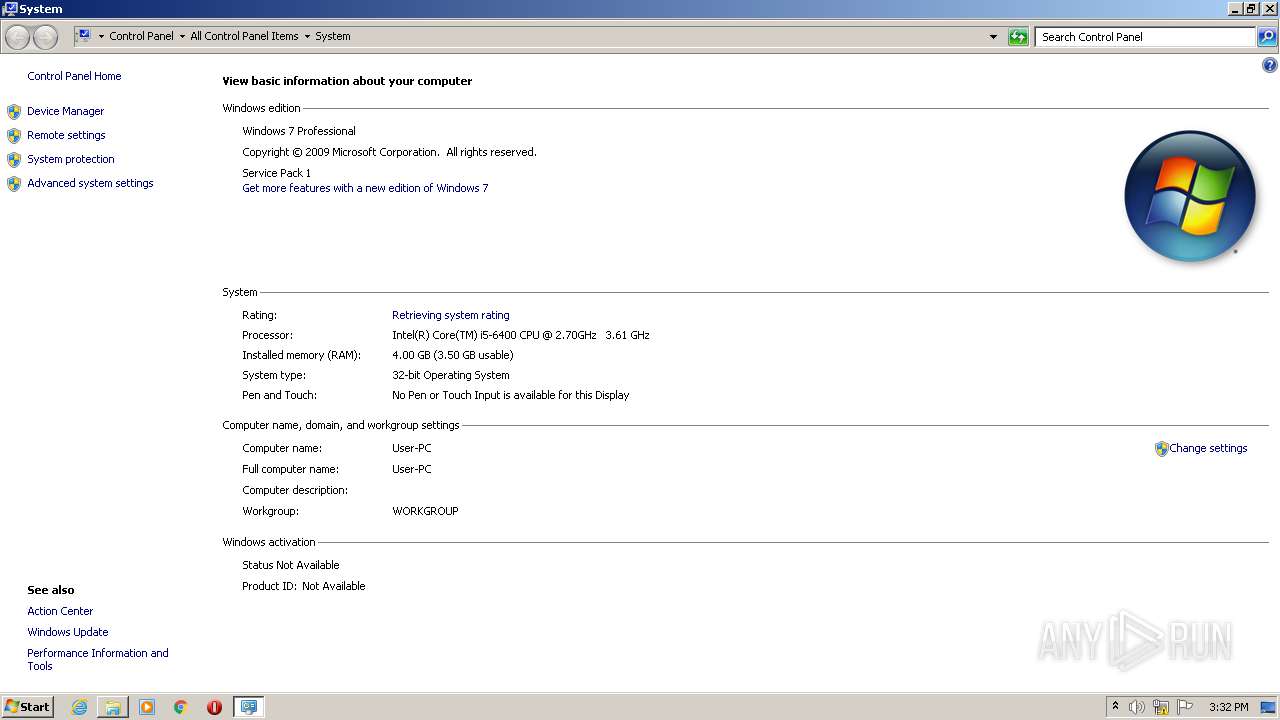
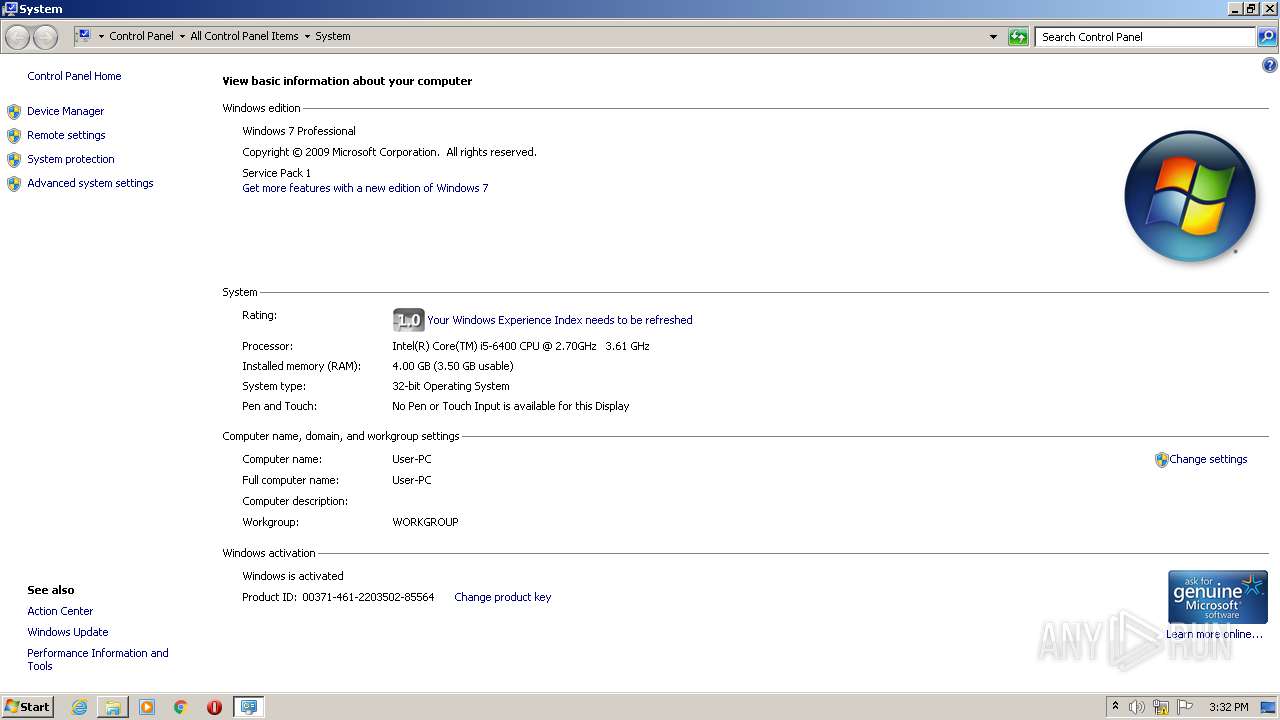
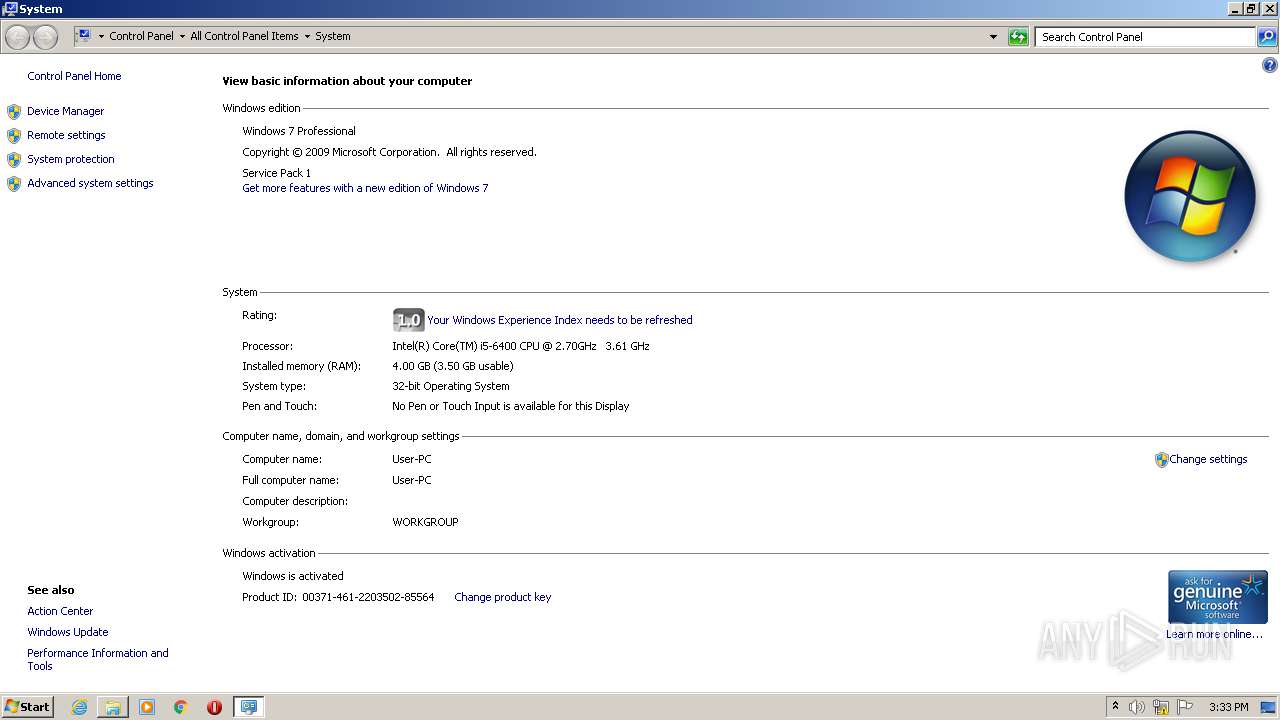
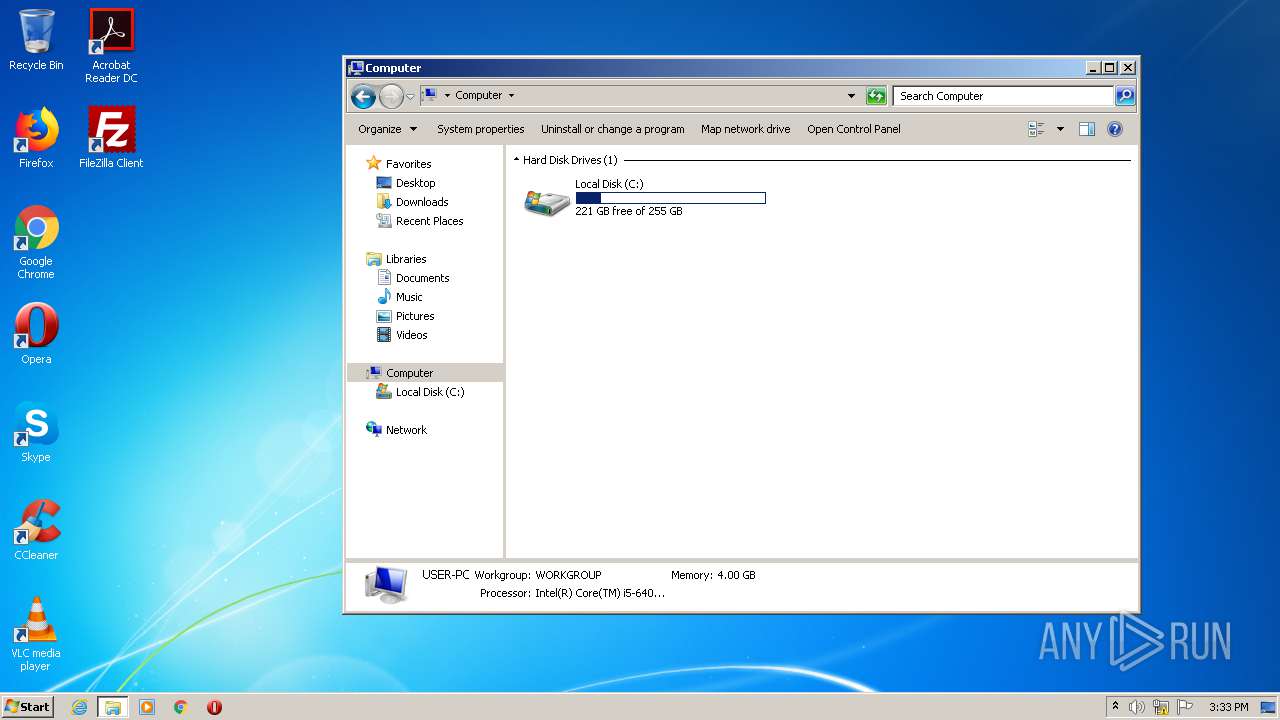
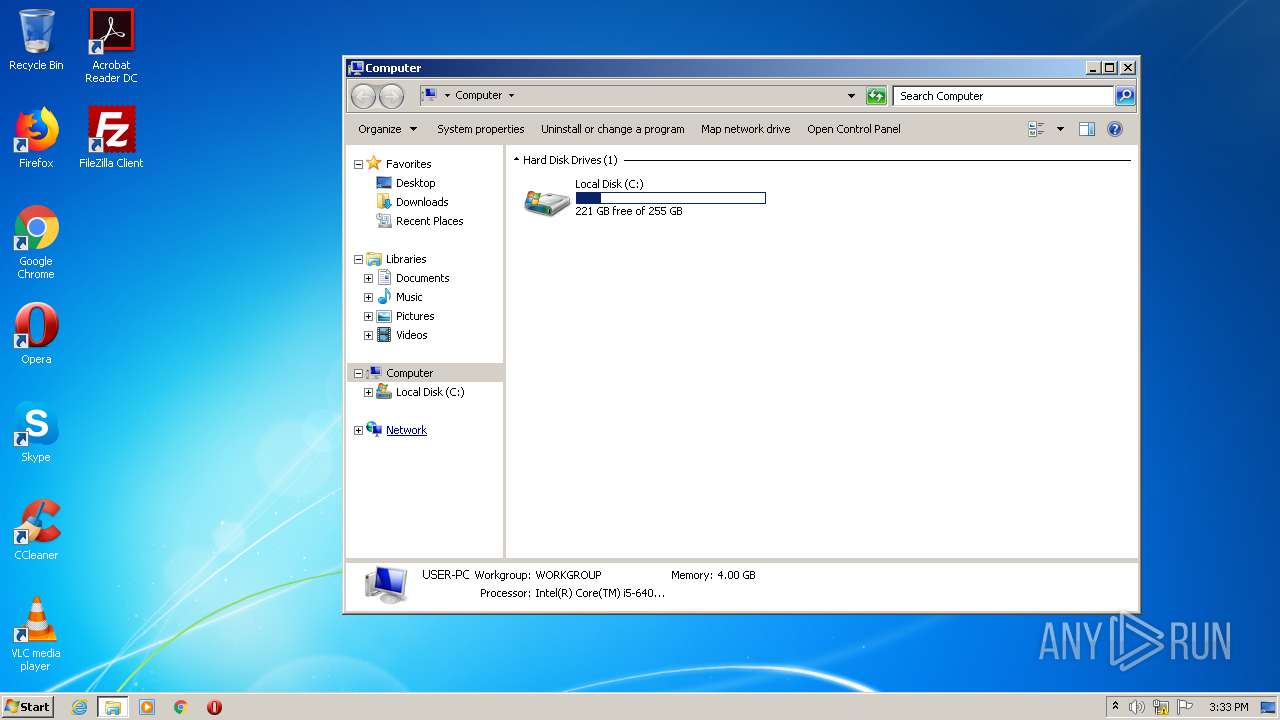
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 31629CC08F588B8E442B821FCFEE763E |
| SHA1: | 81966ADD9BA99B96732349FEC524535B0B92D29A |
| SHA256: | BD3C1A357629D64E1D50548288D0F8E3A2E87231ED2B038F3E8979C7A1E47BC1 |
| SSDEEP: | 24576:8KdnzbOzO5++lh2Fvvv9WYsHt9obcFc79K:8KNzKa57lQvvvwYs3qcGx |
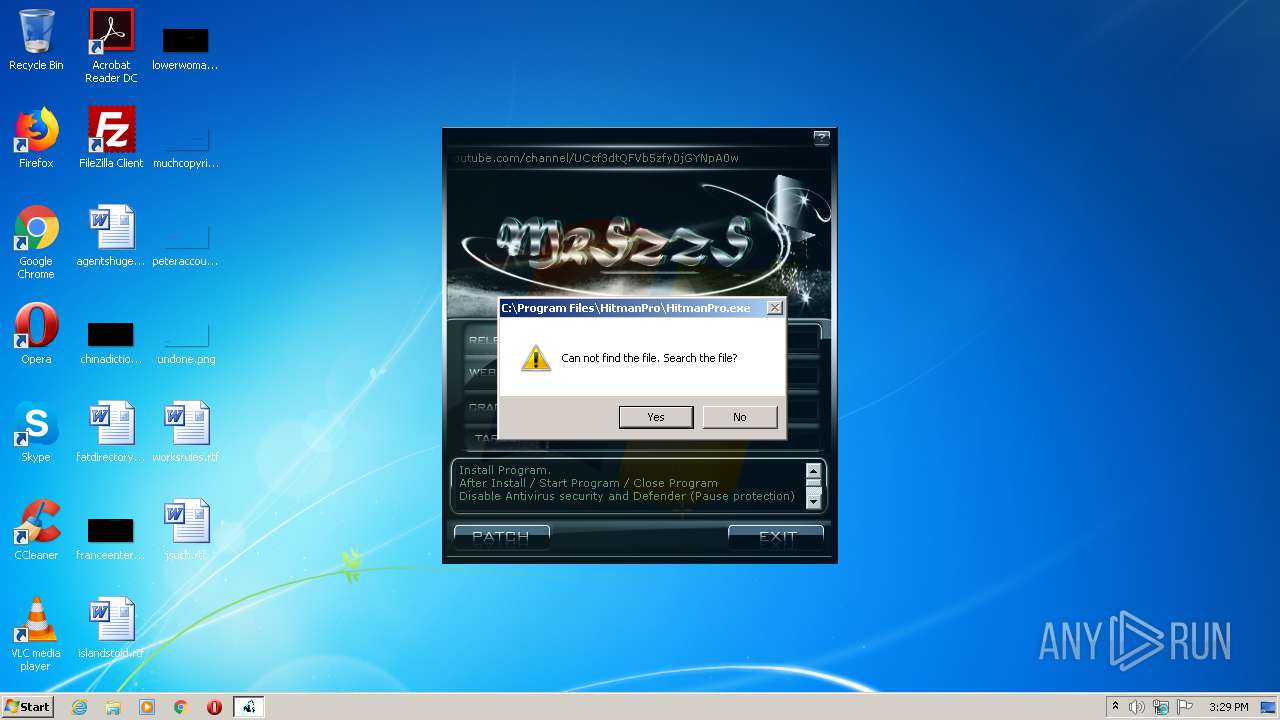
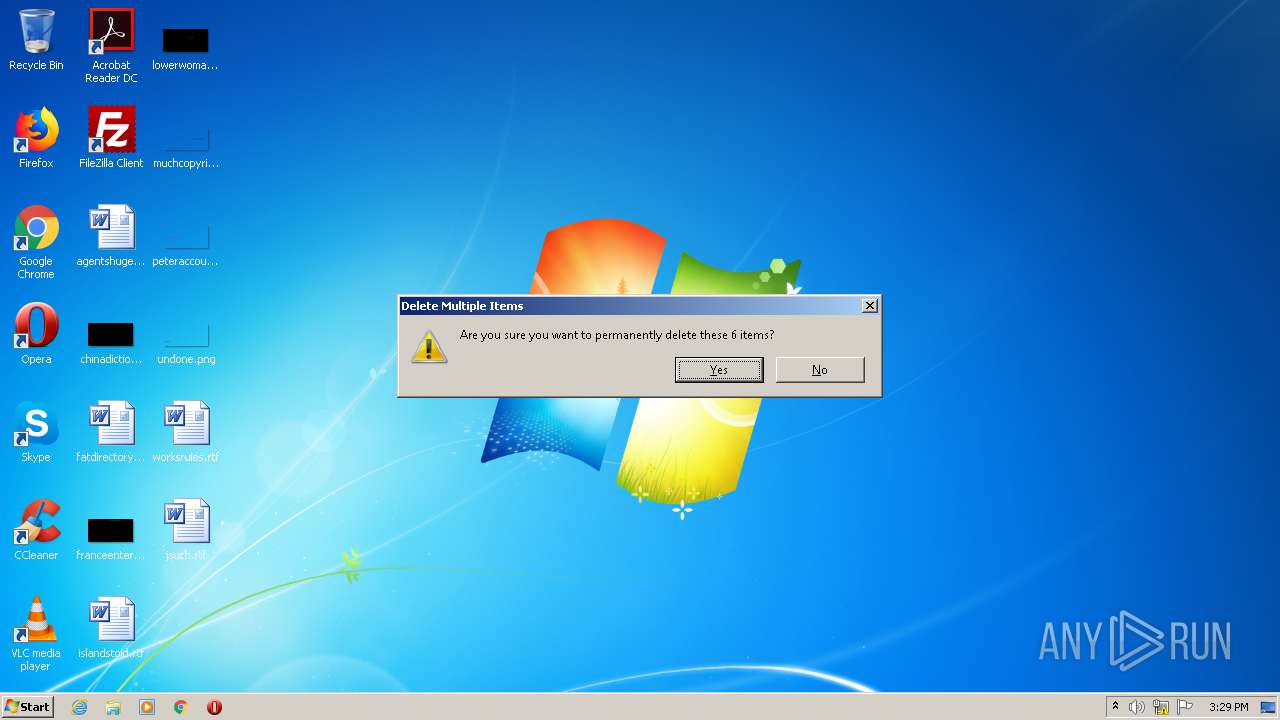
MALICIOUS
Loads dropped or rewritten executable
- (x64bit.).hitmanpro.3.8.20-patch.exe (PID: 3356)
SUSPICIOUS
Executable content was dropped or overwritten
- (x64bit.).hitmanpro.3.8.20-patch.exe (PID: 3356)
Executed via COM
- DllHost.exe (PID: 3936)
- DllHost.exe (PID: 2724)
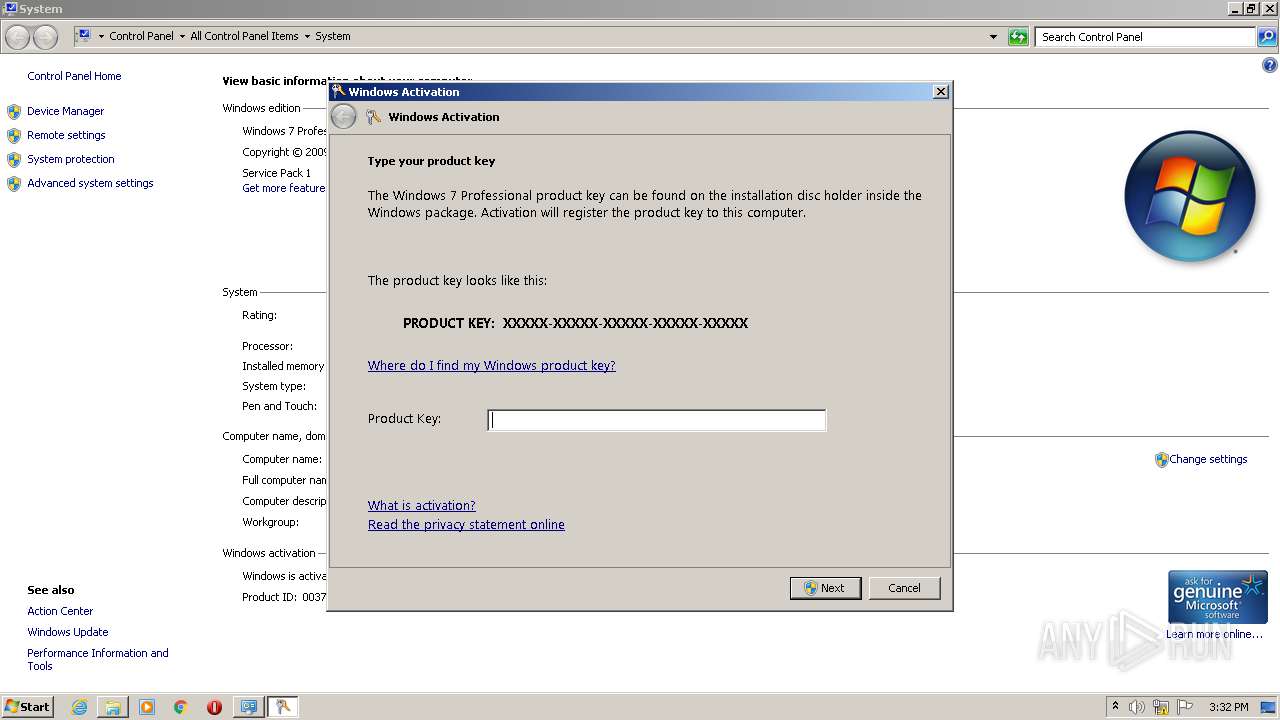
- slui.exe (PID: 2240)
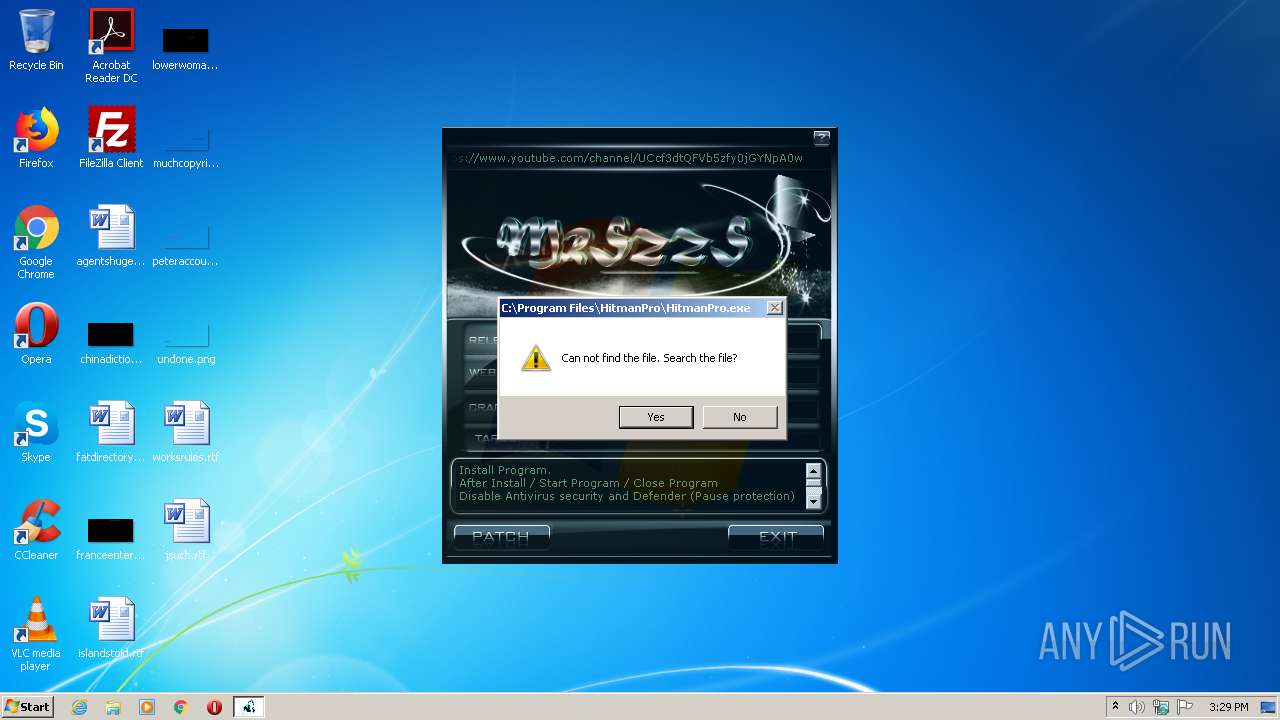
Creates files in the program directory
- (x64bit.).hitmanpro.3.8.20-patch.exe (PID: 3356)
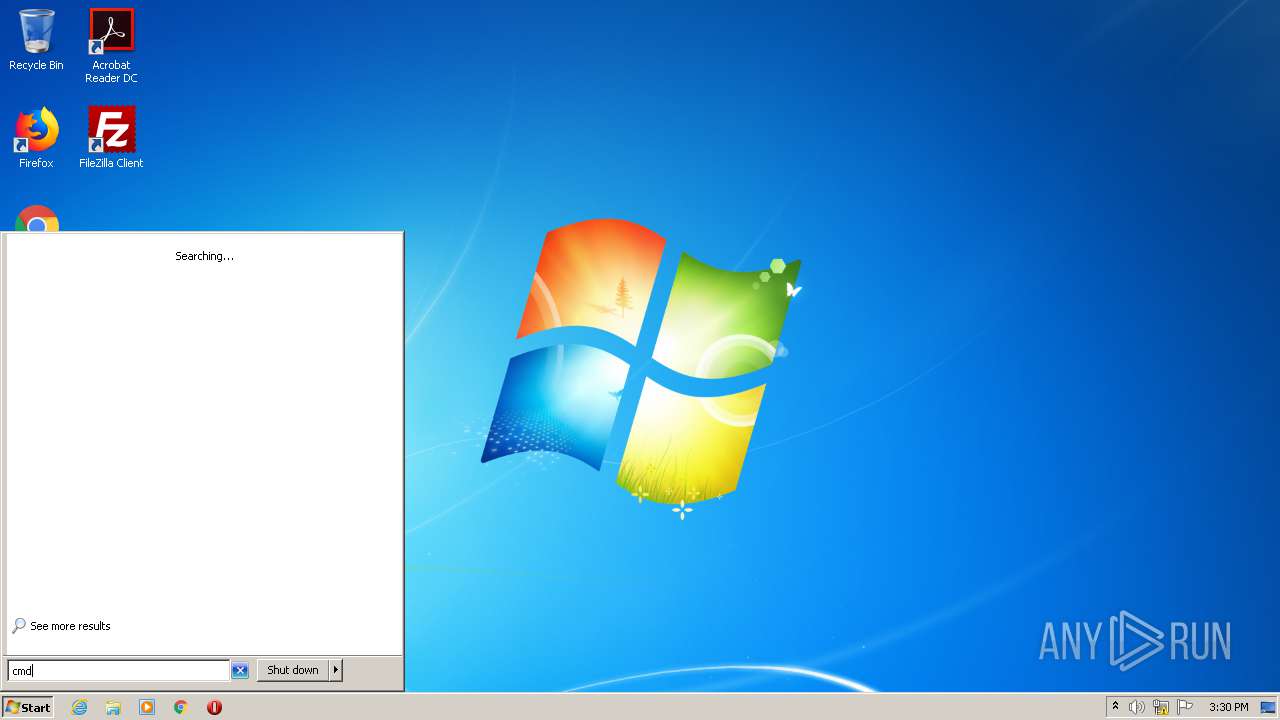
Uses IPCONFIG.EXE to discover IP address
- cmd.exe (PID: 1244)
INFO
Dropped object may contain Bitcoin addresses
- (x64bit.).hitmanpro.3.8.20-patch.exe (PID: 3356)
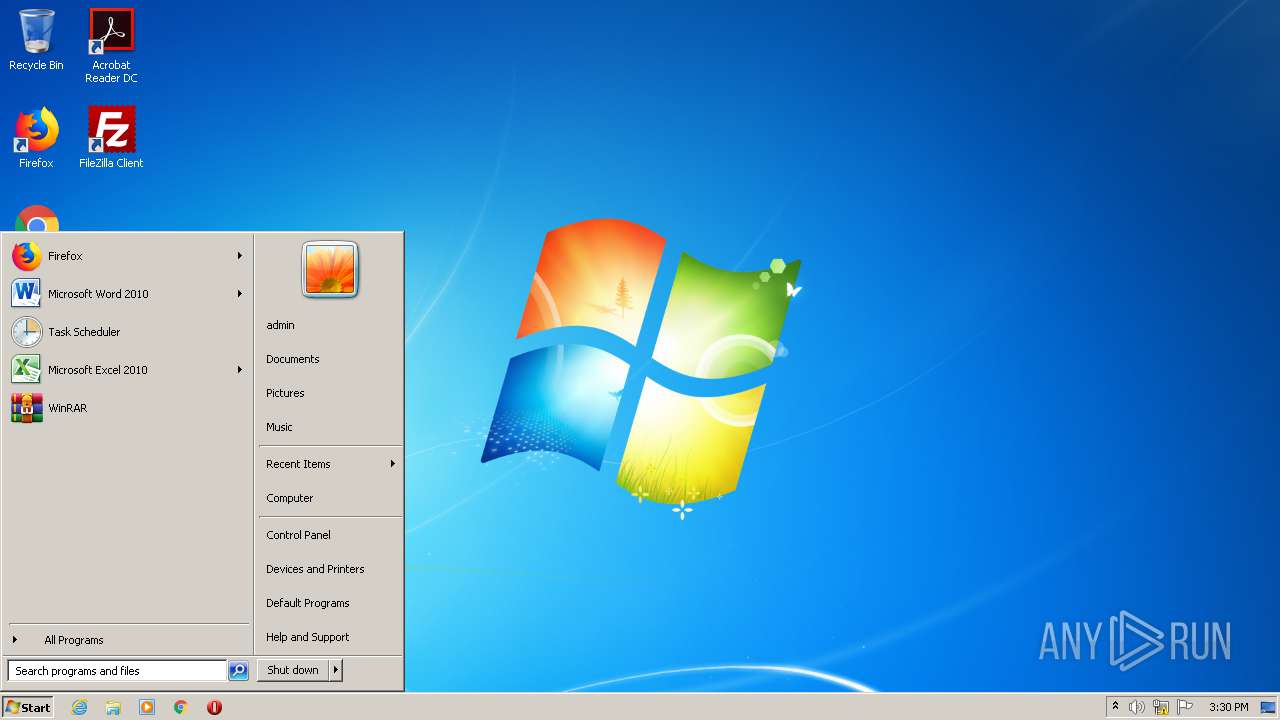
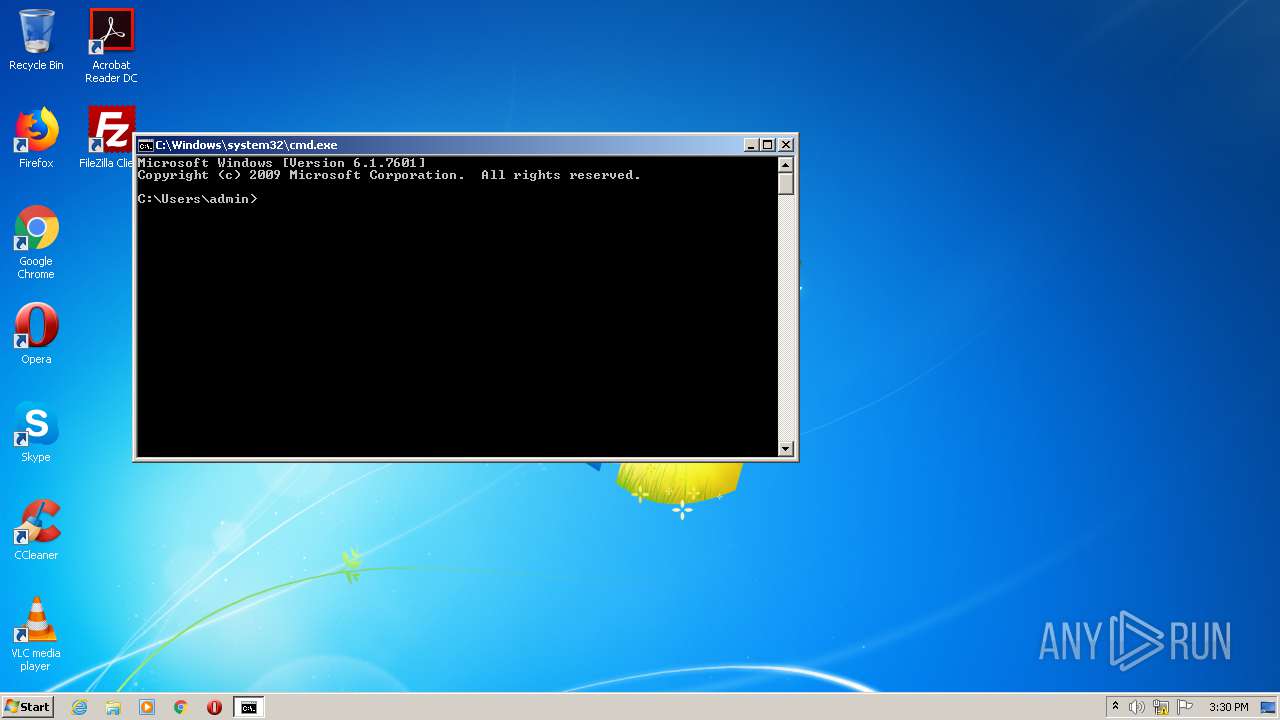
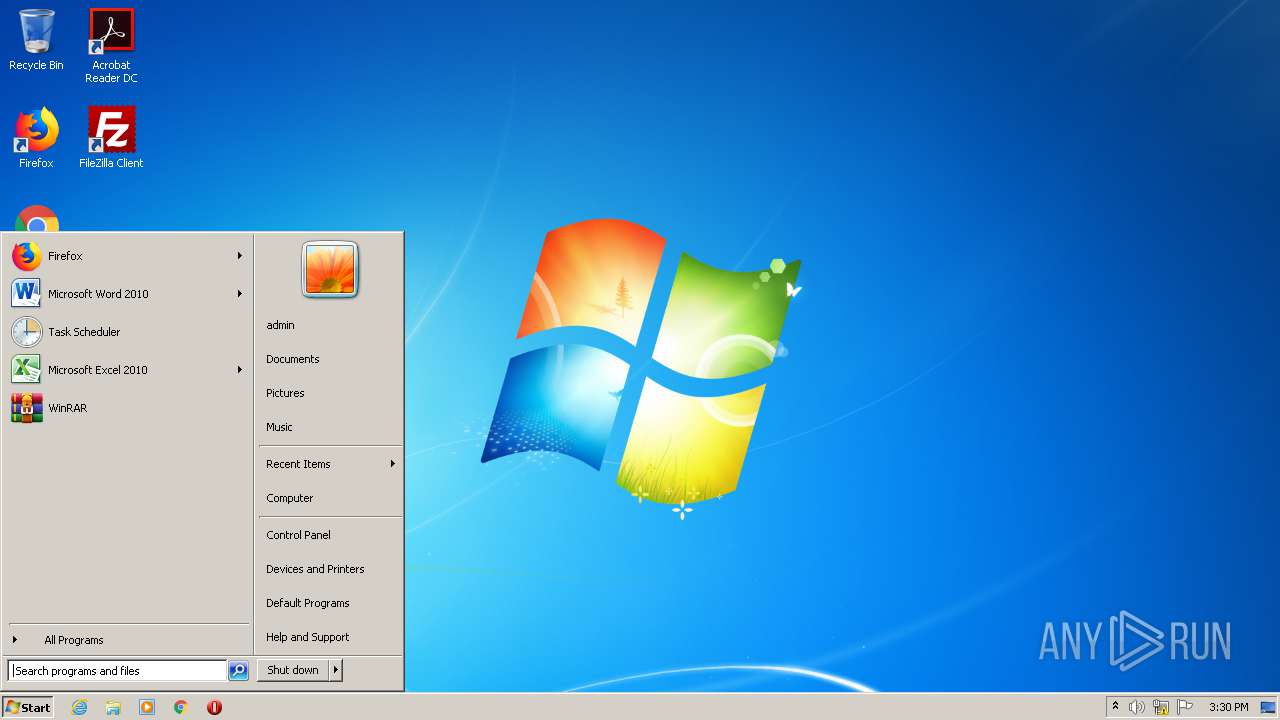
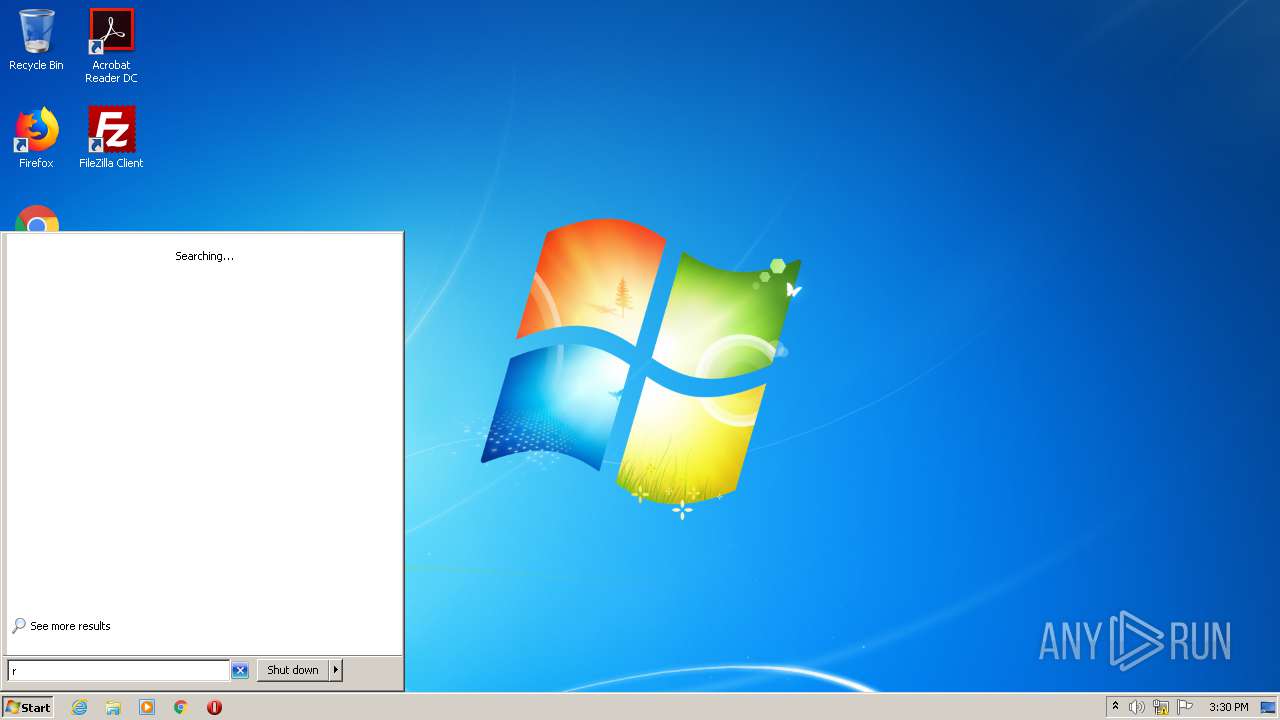
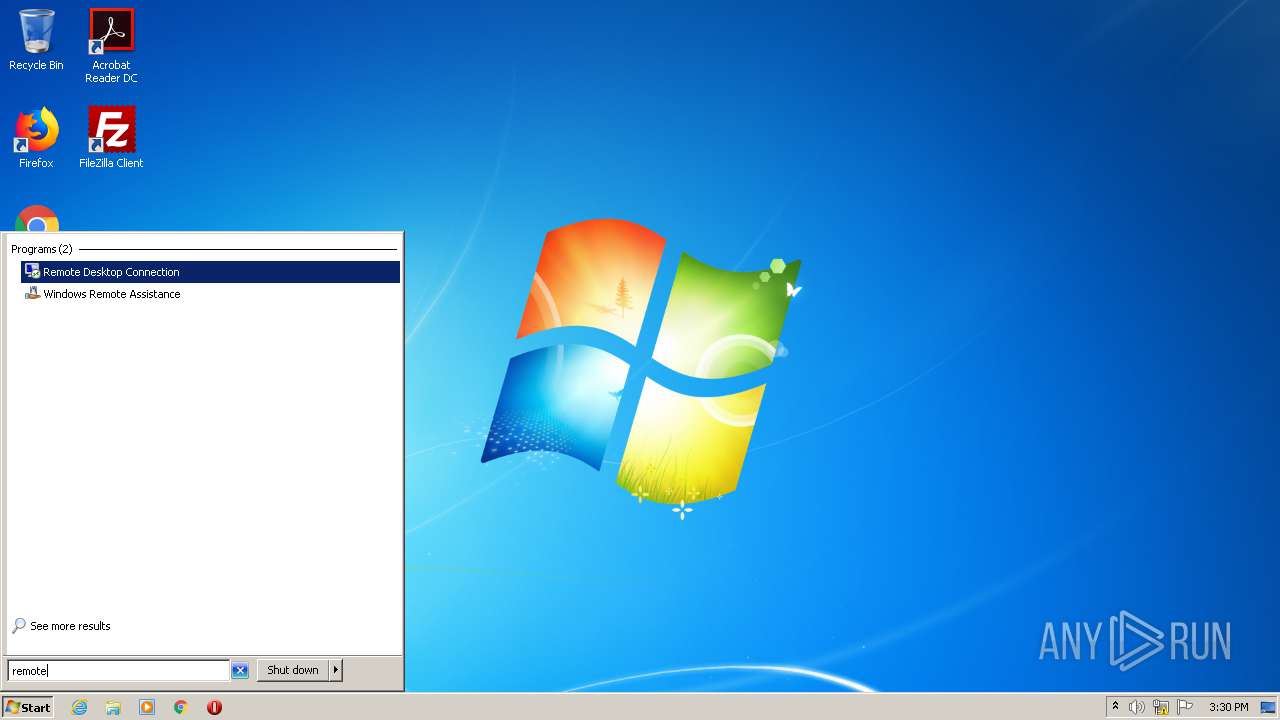
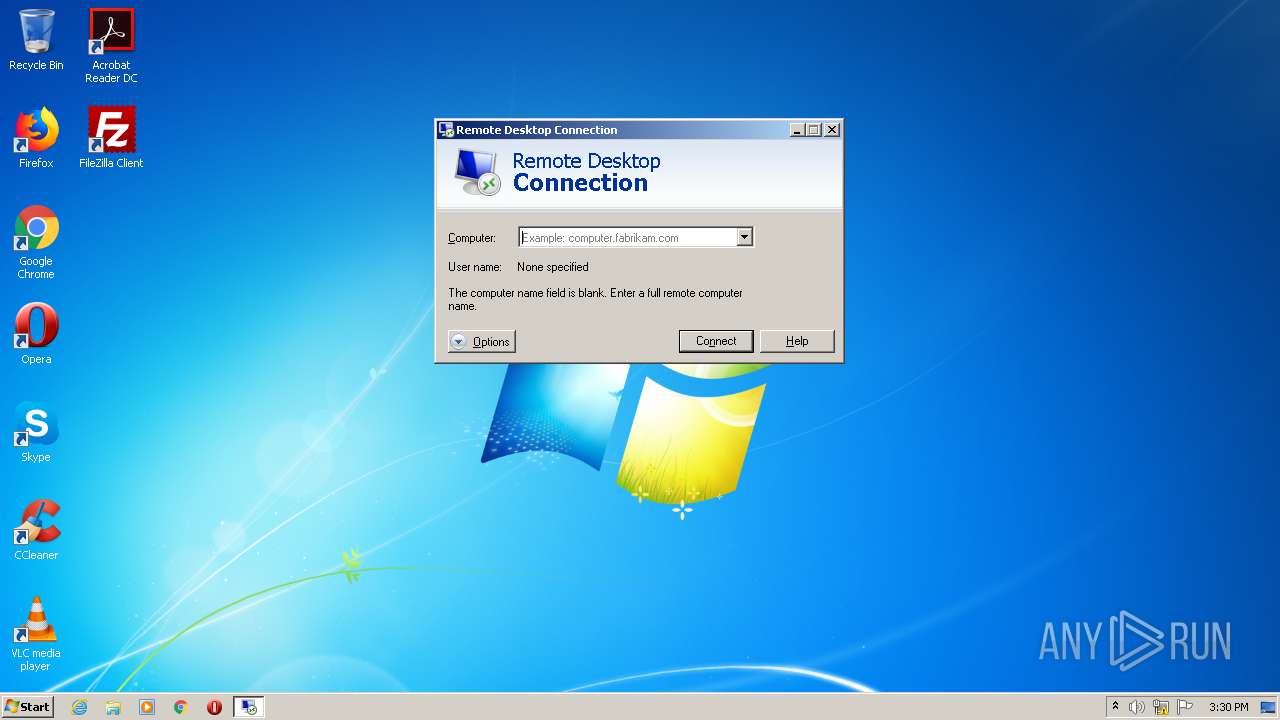
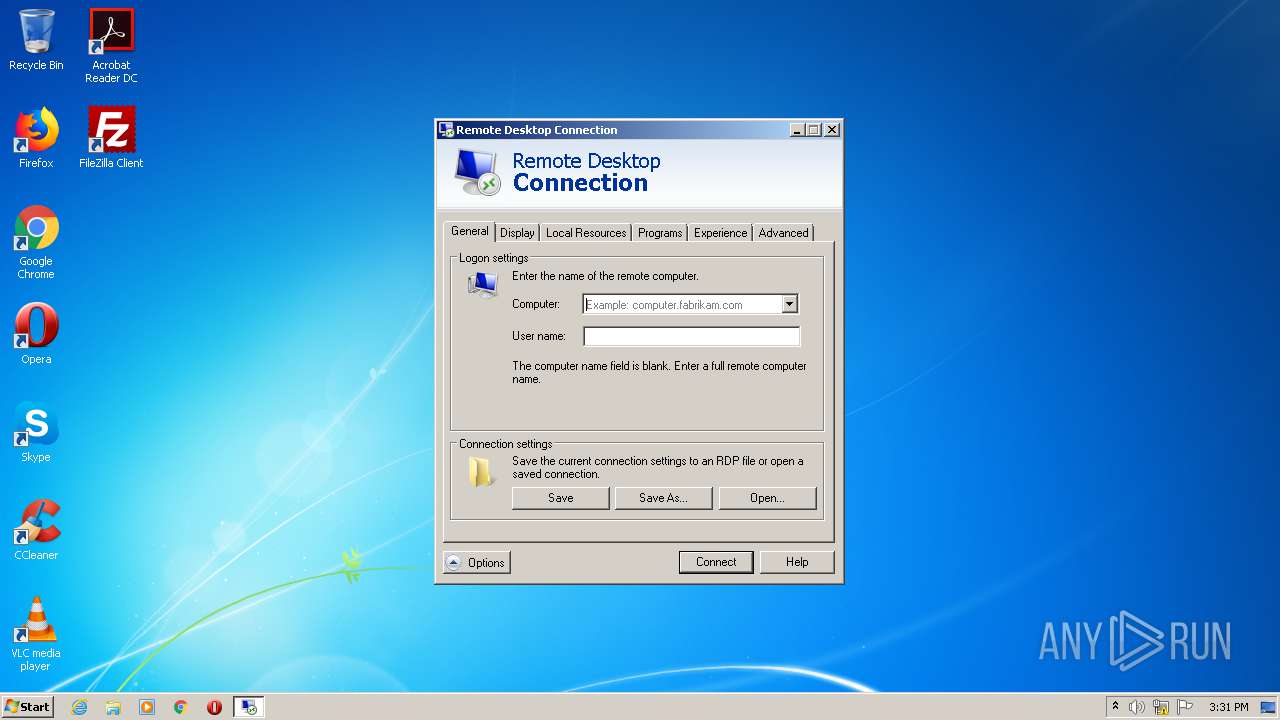
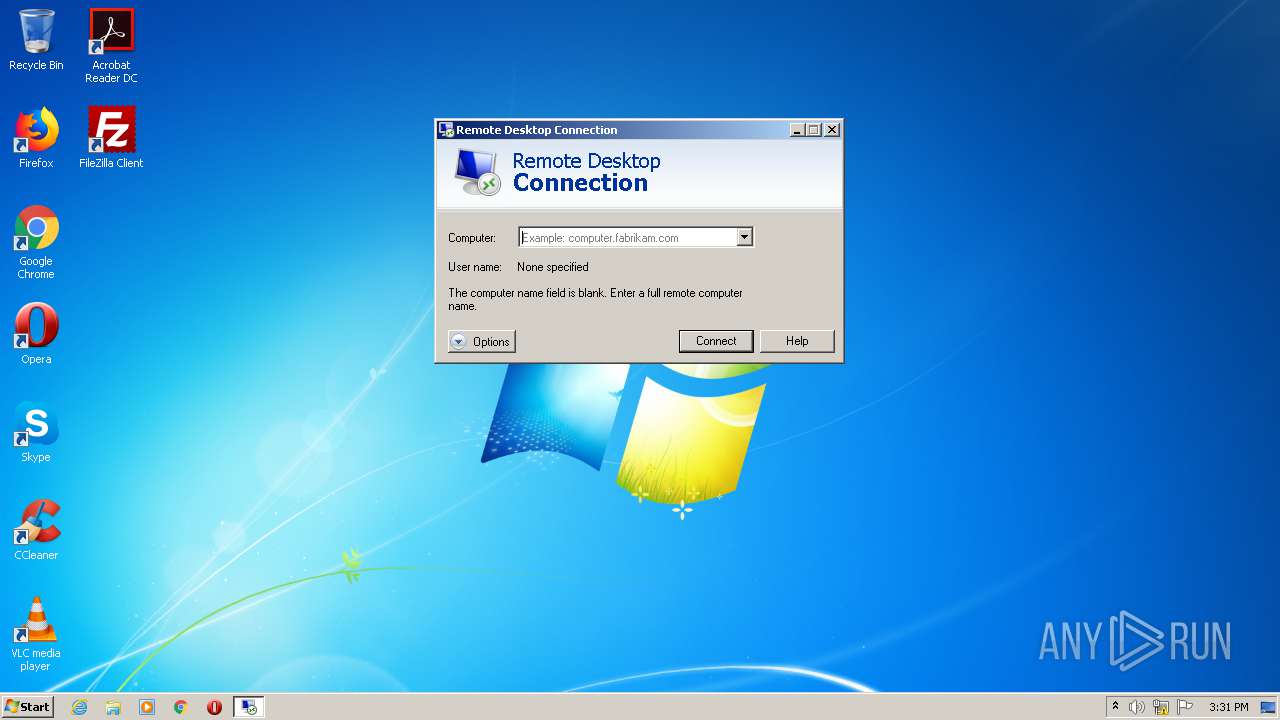
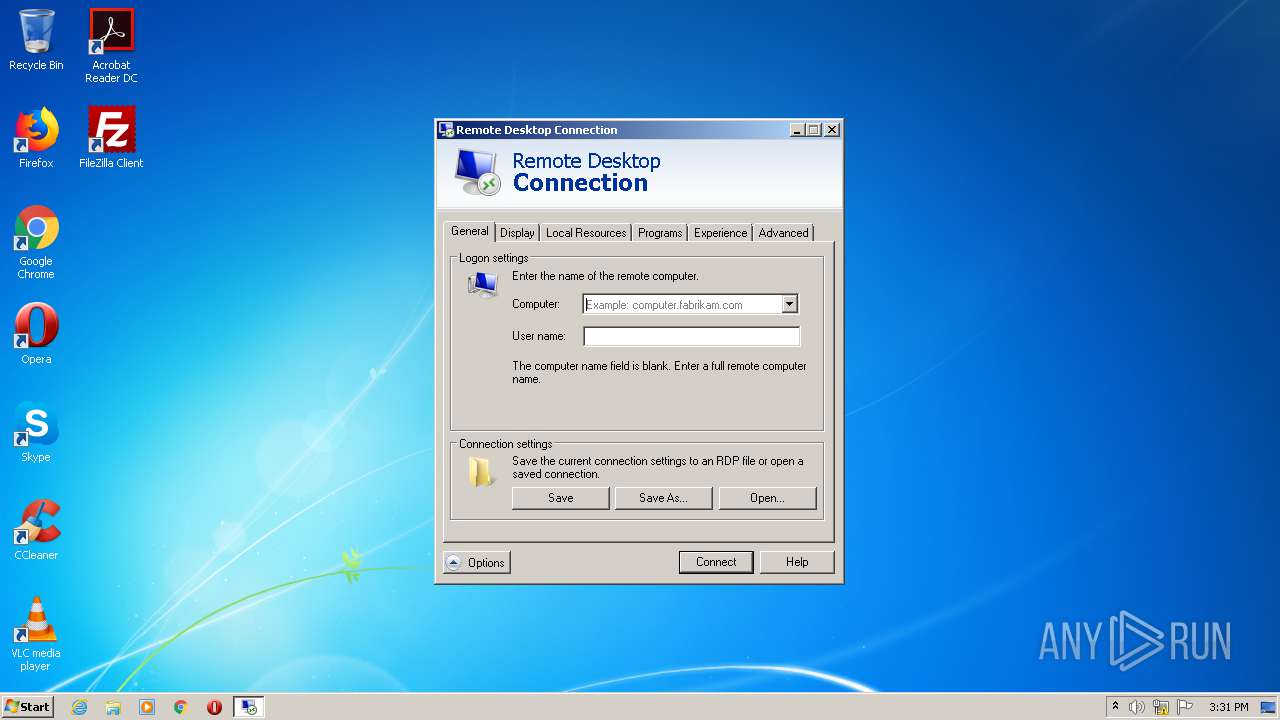
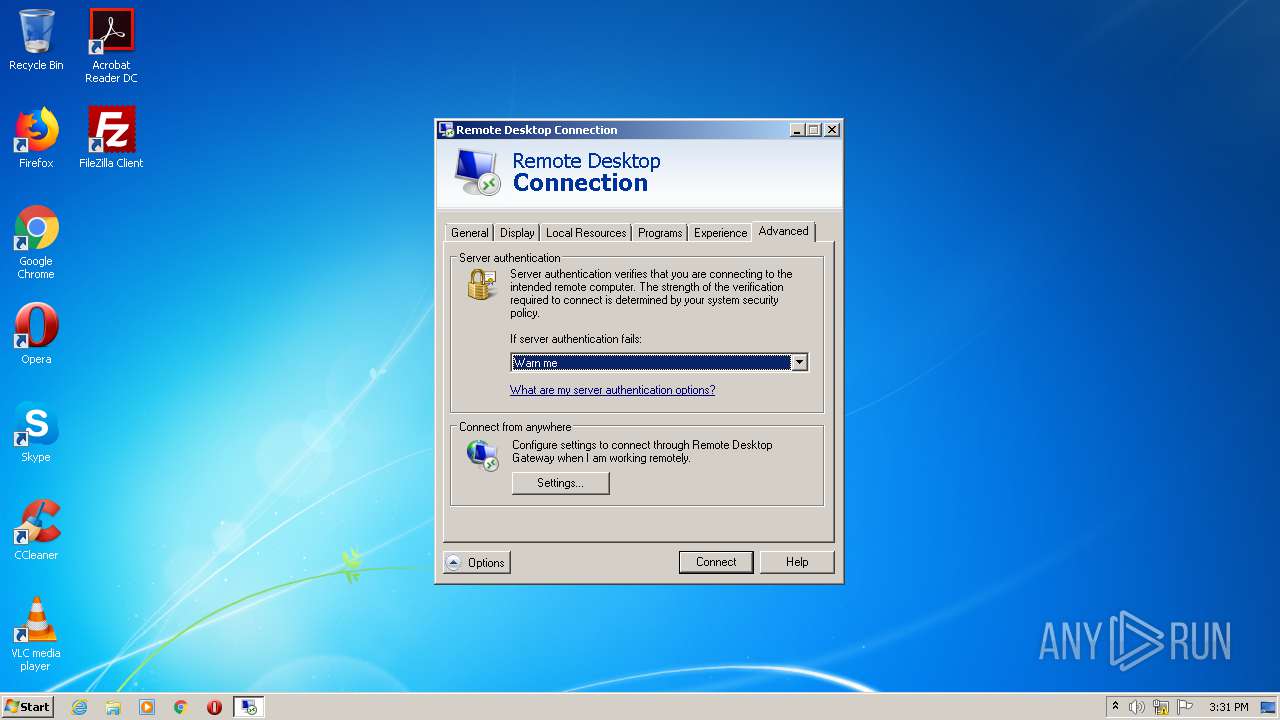
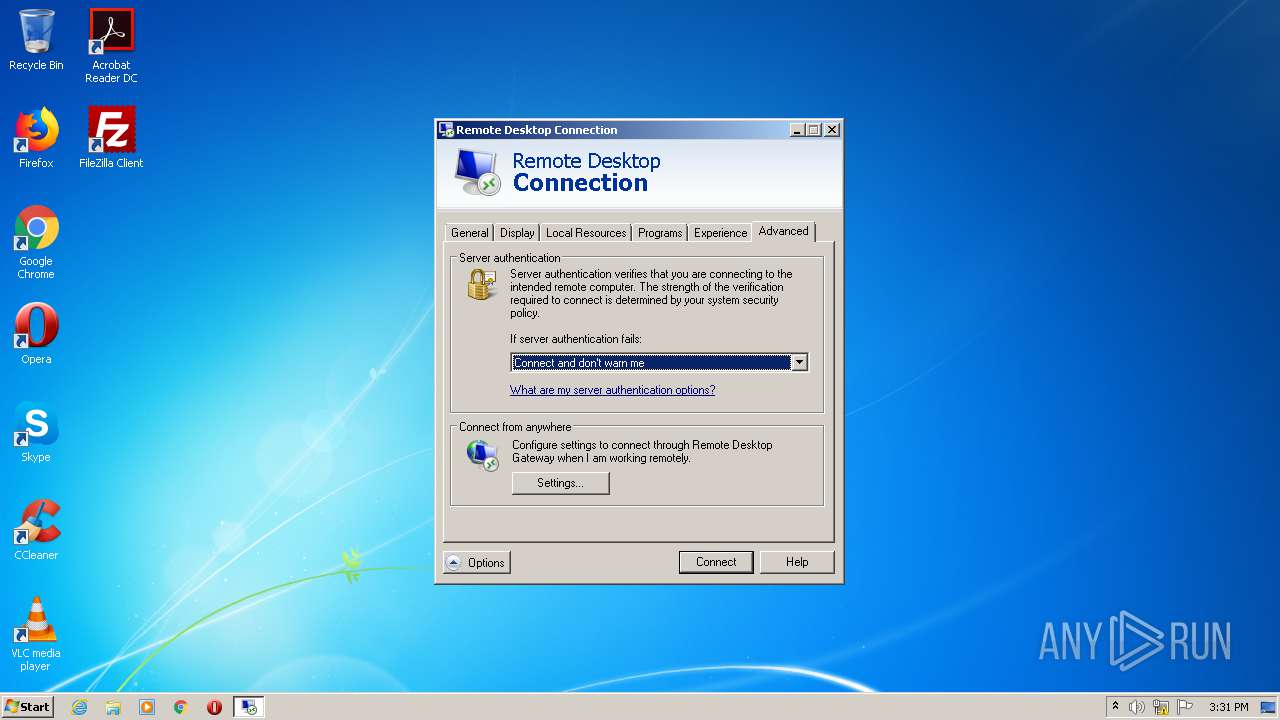
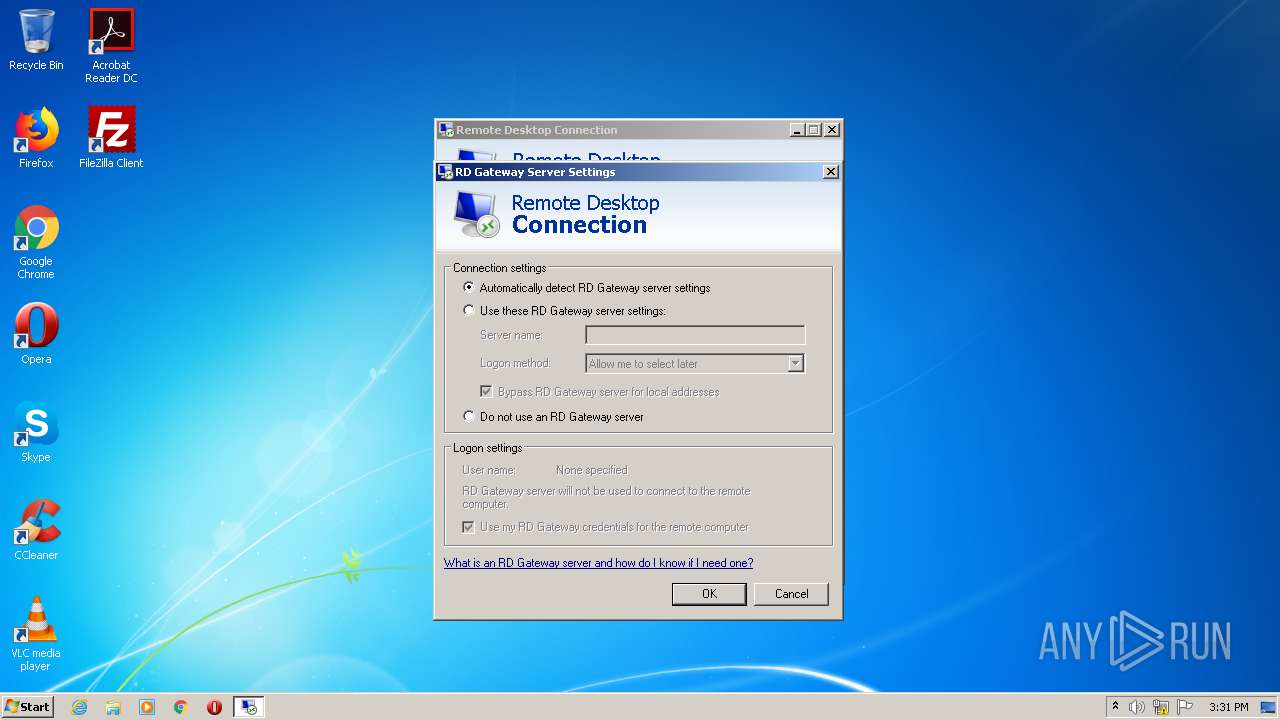
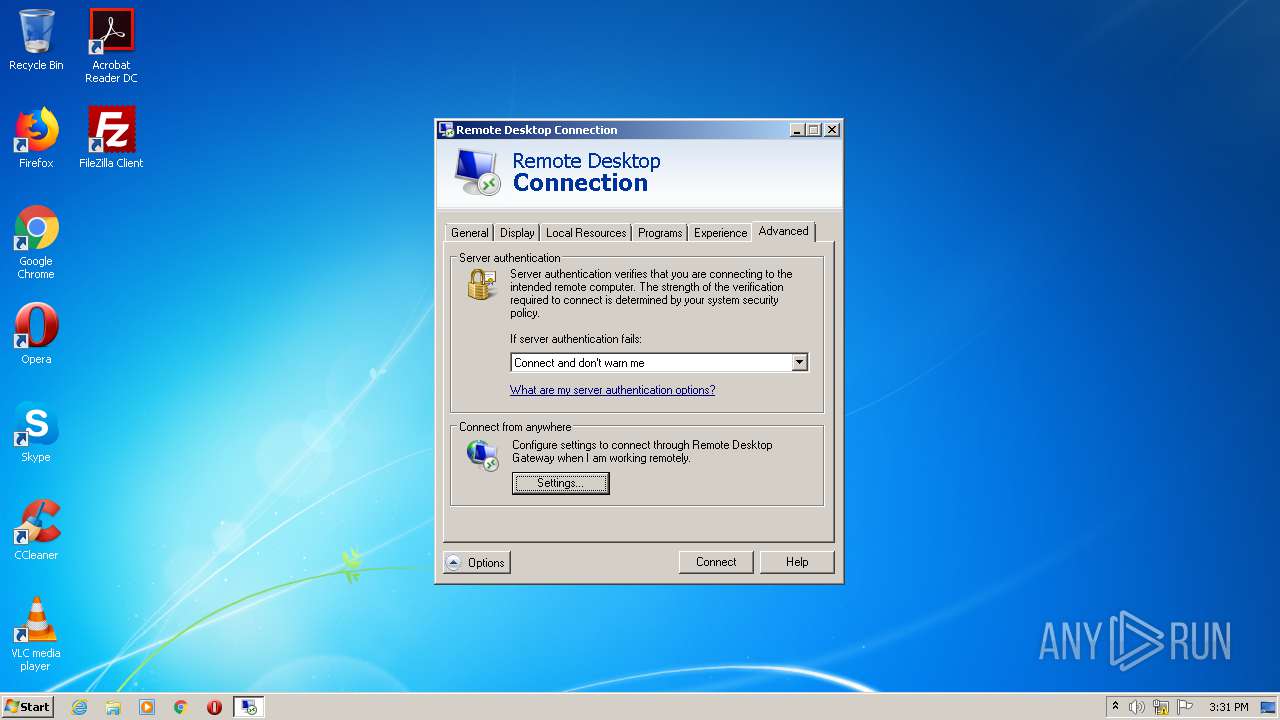
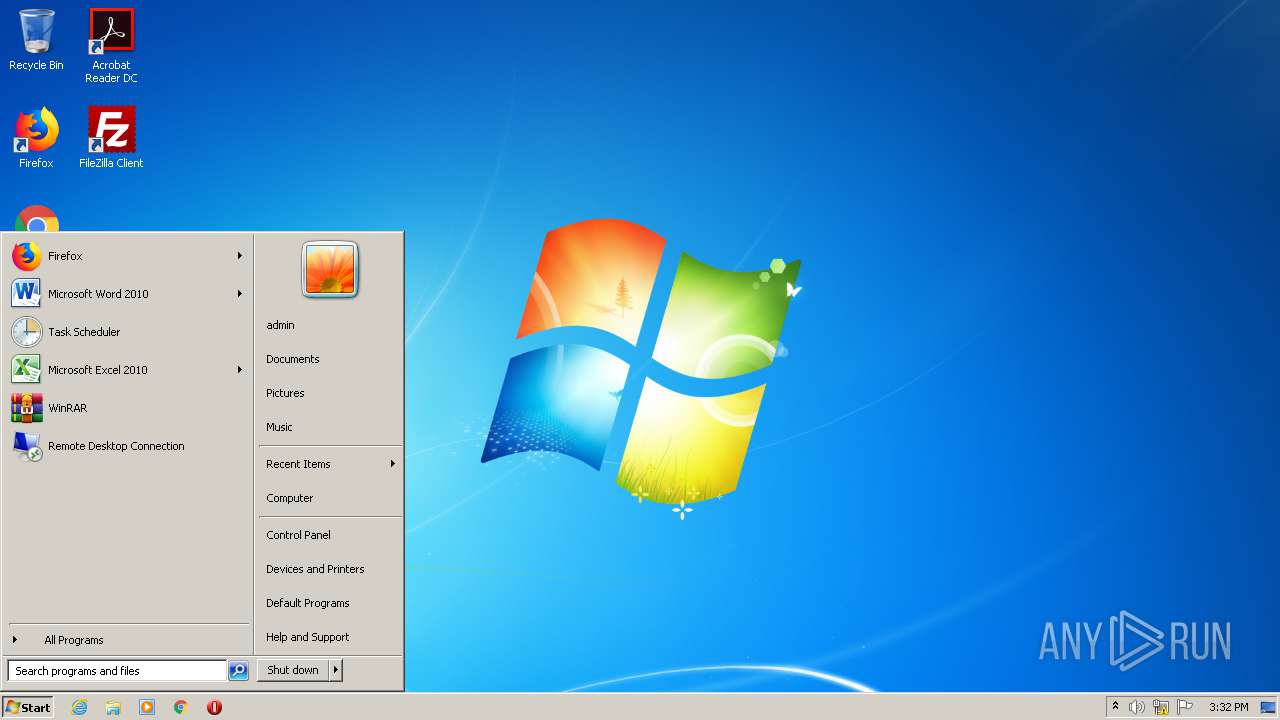
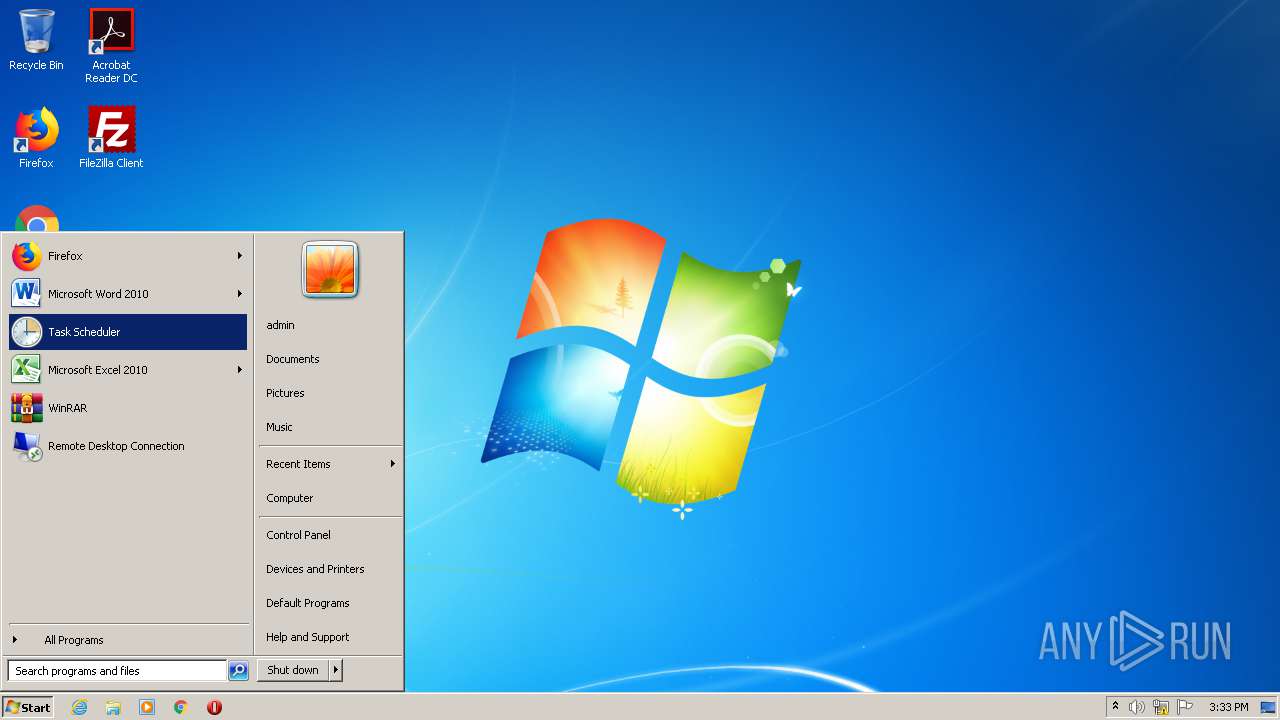
Manual execution by user
- cmd.exe (PID: 1244)
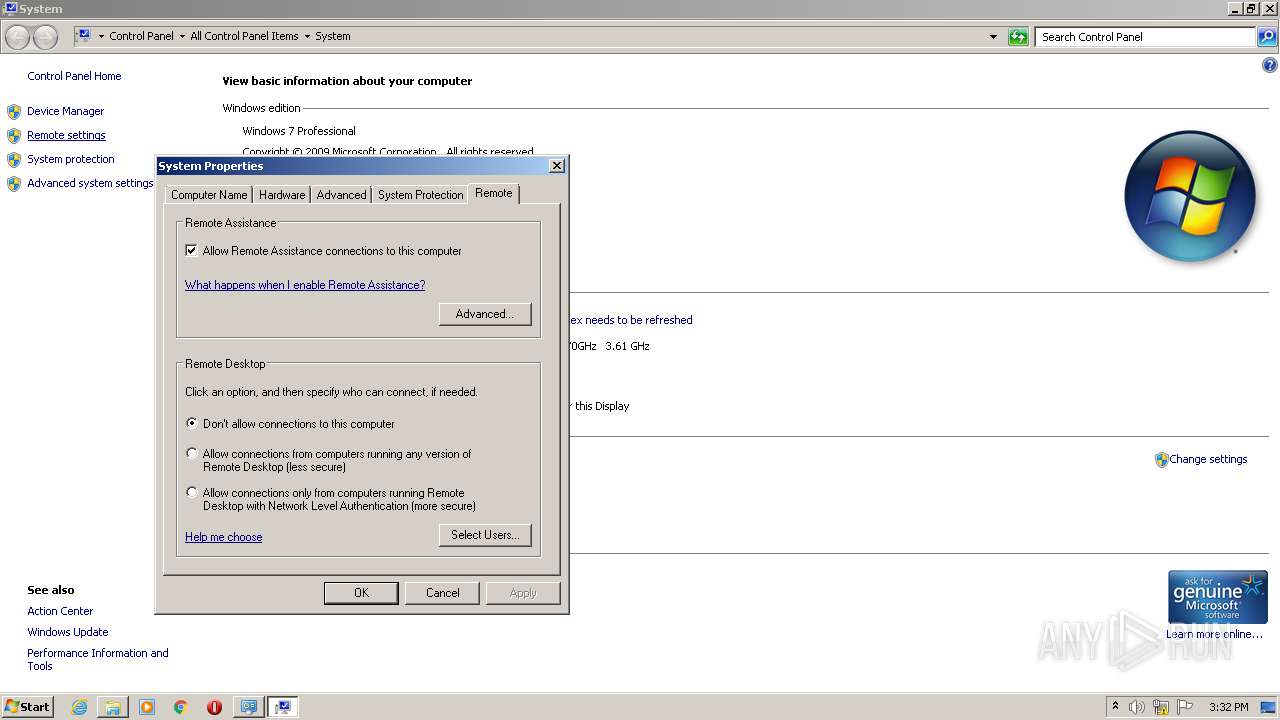
- mstsc.exe (PID: 392)
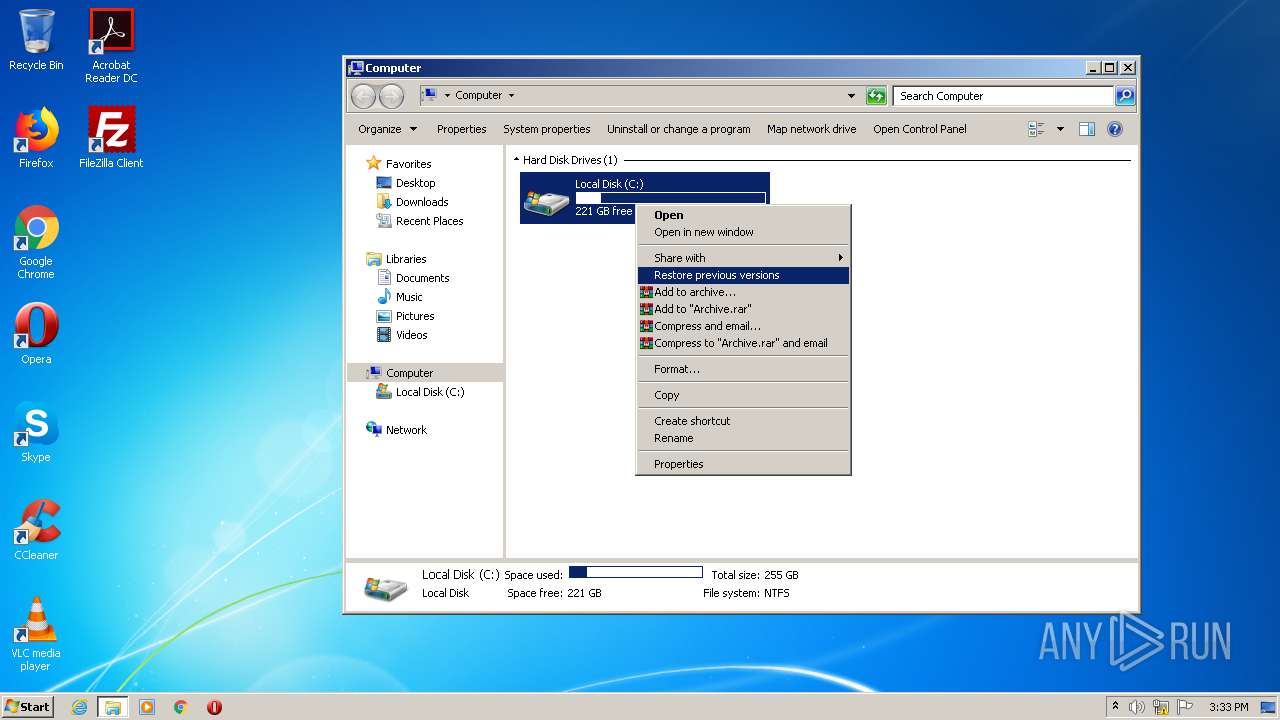
- control.exe (PID: 2028)
- slui.exe (PID: 3260)
- systempropertiesremote.exe (PID: 1208)
- systempropertiesremote.exe (PID: 3200)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:12:21 21:59:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 512 |
| InitializedDataSize: | 846848 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x102b |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Dec-2012 20:59:46 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 21-Dec-2012 20:59:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000001F6 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.06408 |
.rdata | 0x00002000 | 0x000001D8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.27064 |
.data | 0x00003000 | 0x00000034 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.568988 |
.rsrc | 0x00004000 | 0x000CE478 | 0x000CE600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99259 |
.reloc | 0x000D3000 | 0x00000052 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.736046 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.85663 | 898 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
500 | 1.91924 | 20 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
DLL | 7.99978 | 834048 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
kernel32.dll |
Total processes
60
Monitored processes
12
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 392 | "C:\Windows\system32\mstsc.exe" | C:\Windows\system32\mstsc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Remote Desktop Connection Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1208 | "C:\Windows\system32\systempropertiesremote.exe" | C:\Windows\system32\systempropertiesremote.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: System Remote Settings Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1244 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1920 | "C:\Users\admin\AppData\Local\Temp\(x64bit.).hitmanpro.3.8.20-patch.exe" | C:\Users\admin\AppData\Local\Temp\(x64bit.).hitmanpro.3.8.20-patch.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2028 | "C:\Windows\System32\control.exe" SYSTEM | C:\Windows\System32\control.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Control Panel Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2120 | ipconfig | C:\Windows\system32\ipconfig.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2240 | C:\Windows\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2724 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3200 | "C:\Windows\system32\systempropertiesremote.exe" | C:\Windows\system32\systempropertiesremote.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: System Remote Settings Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3260 | "C:\Windows\System32\slui.exe" 0x03 | C:\Windows\System32\slui.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
755
Read events
719
Write events
35
Delete events
1
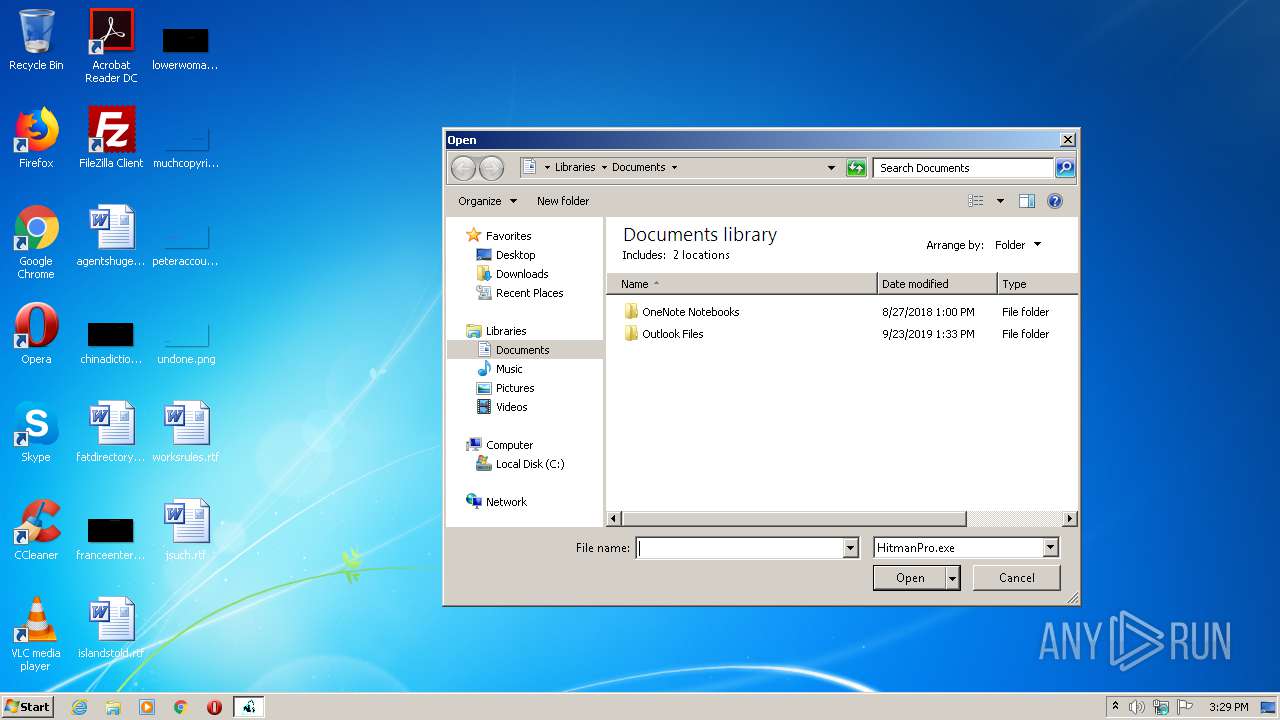
Modification events
| (PID) Process: | (3356) (x64bit.).hitmanpro.3.8.20-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3356) (x64bit.).hitmanpro.3.8.20-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 02000000010000000B00000000000000070000000A000000090000000800000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3356) (x64bit.).hitmanpro.3.8.20-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (3356) (x64bit.).hitmanpro.3.8.20-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (3356) (x64bit.).hitmanpro.3.8.20-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (3356) (x64bit.).hitmanpro.3.8.20-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3356) (x64bit.).hitmanpro.3.8.20-patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | 2 |
Value: 28007800360034006200690074002E0029002E006800690074006D0061006E00700072006F002E0033002E0038002E00320030002D00700061007400630068002E00650078006500000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000BA0100007F0000003A0400005F020000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (3356) (x64bit.).hitmanpro.3.8.20-patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | delete value | Name: | 2 |
Value: 28007800360034006200690074002E0029002E006800690074006D0061006E00700072006F002E0033002E0038002E00320030002D00700061007400630068002E00650078006500000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000BA0100007F0000003A0400005F020000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (3356) (x64bit.).hitmanpro.3.8.20-patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | 2 |
Value: 28007800360034006200690074002E0029002E006800690074006D0061006E00700072006F002E0033002E0038002E00320030002D00700061007400630068002E0065007800650000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000BA0100007F000000460300003402000000000000000000000000000000000000BA0100007F0000003A0400005F020000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (3356) (x64bit.).hitmanpro.3.8.20-patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | MRUListEx |
Value: 020000000100000000000000FFFFFFFF | |||
Executable files
2
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3356 | (x64bit.).hitmanpro.3.8.20-patch.exe | C:\Users\admin\AppData\Local\Temp\bassmod.dll | executable | |
MD5:780D14604D49E3C634200C523DEF8351 | SHA256:844EB66A10B848D3A71A8C63C35F0A01550A46D2FF8503E2CA8947978B03B4D2 | |||
| 3356 | (x64bit.).hitmanpro.3.8.20-patch.exe | C:\ProgramData\HitmanPro\HitmanPro.key | text | |
MD5:6E8E7A058CBAF8053631EFD975CEB488 | SHA256:F2169431A31C1E7492188F64983A8384E8300626E3341FB97AAE4796840F3447 | |||
| 3356 | (x64bit.).hitmanpro.3.8.20-patch.exe | C:\ProgramData\HitmanPro\HitmanPro.lic | text | |
MD5:C4516E3DC19FD7D269ABED9047110CC8 | SHA256:0EDACCA48903D878539143BAA10A57F3F1787ACB855C0C9AEFA199A48860D97A | |||
| 3356 | (x64bit.).hitmanpro.3.8.20-patch.exe | C:\Users\admin\AppData\Local\Temp\dup2patcher.dll | executable | |
MD5:279346B106AE80AAE76A46FEA16CA01C | SHA256:9349B0F0850E6618A31F754AB8BE50BBFA038E589B4ECF26370D239D597C6FF5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report